| download: | index.html |
| Full analysis: | https://app.any.run/tasks/963c6ade-3217-4bf9-8028-b7c889802ef4 |
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2019, 02:10:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with very long lines |
| MD5: | 0C57E49887A656041F0844CD836AB9D9 |
| SHA1: | D6092B3894E090BE595DA62D3276DB8E88DEB992 |
| SHA256: | 94346E1CEE58B39865A780CA6EBF5037A55E878C463214EDB9F0C95B8AC67394 |
| SSDEEP: | 768:1Tg94DjppBudpcLnSzLATbcggHLYkL/mFVLvyaNIHwtoj1LpMtjc70Sw2SyabMU8:1bFpB8p8+UY/mF9rOjRpR9mMHC5M |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads internet explorer settings
- iexplore.exe (PID: 2760)
- iexplore.exe (PID: 3392)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2760)
Creates files in the user directory
- iexplore.exe (PID: 3392)
- iexplore.exe (PID: 2760)
Changes internet zones settings
- iexplore.exe (PID: 2216)
Changes settings of System certificates
- iexplore.exe (PID: 2760)
Application launched itself
- iexplore.exe (PID: 2216)
Reads Internet Cache Settings
- iexplore.exe (PID: 3392)
- iexplore.exe (PID: 2760)
- iexplore.exe (PID: 2216)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
EXIF
HTML
| ContentType: | text/html; charset=UTF-8 |
|---|---|
| Generator: | blogger |
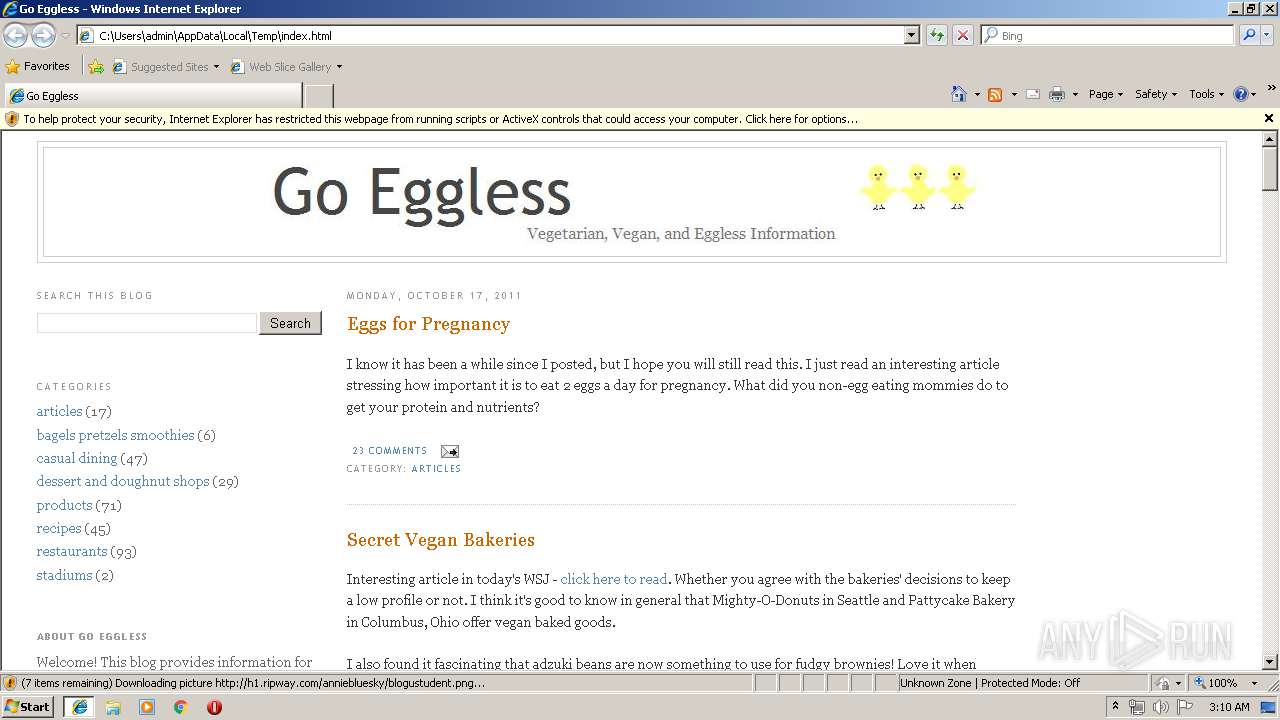
| Title: | Go Eggless |
| verifyV1: | R0FbwTJH3Y9QUCMDKkg6lzbb2b4BHMj07t5g6u6ExwY= |
Total processes
35
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2216 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\index.html | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2760 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2216 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3392 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2216 CREDAT:203009 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
705
Read events
591
Write events
110
Delete events
4
Modification events
| (PID) Process: | (2216) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2216) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2216) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2216) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2216) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2216) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000071000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2216) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {58E67E2B-66FF-11E9-A370-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2216) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2216) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (2216) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E30704000400190002000A0034006500 | |||
Executable files
0
Suspicious files
3
Text files
65
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2216 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2216 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2760 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\plusone[1].js | — | |
MD5:— | SHA256:— | |||
| 2760 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\authorization[1].css | — | |
MD5:— | SHA256:— | |||
| 2760 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@google[1].txt | text | |
MD5:— | SHA256:— | |||
| 2760 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\title2[1].jpg | image | |
MD5:— | SHA256:— | |||
| 2760 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\IMG_0045[1].JPG | image | |
MD5:— | SHA256:— | |||
| 2760 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\IMG_0043[1].jpg | image | |
MD5:— | SHA256:— | |||
| 2760 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\ErrorPageTemplate[1] | text | |
MD5:F4FE1CB77E758E1BA56B8A8EC20417C5 | SHA256:8D018639281B33DA8EB3CE0B21D11E1D414E59024C3689F92BE8904EB5779B5F | |||
| 2760 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\tools[1] | image | |
MD5:6F20BA58551E13CFD87EC059327EFFD0 | SHA256:62A7038CC42C1482D70465192318F21FC1CE0F0C737CB8804137F38A1F9D680B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
52
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3392 | iexplore.exe | GET | — | 52.203.42.164:80 | http://widget.foodieblogroll.com/?BlogID=2878 | US | — | — | unknown |
2760 | iexplore.exe | GET | — | 52.203.42.164:80 | http://widget.foodieblogroll.com/?BlogID=2878 | US | — | — | unknown |
2760 | iexplore.exe | GET | 200 | 216.58.208.33:80 | http://1.bp.blogspot.com/_7gvEO0dUECo/SNMw_ks1OXI/AAAAAAAAAGA/KupJ-ab03l4/S1600-R/title2.jpg | US | image | 9.78 Kb | whitelisted |
2760 | iexplore.exe | GET | 410 | 54.152.63.67:80 | http://www.thedailygreen.com/cm/thedailygreen/images/4u/food-additives-info-xl.jpg | US | html | 348 b | whitelisted |
2760 | iexplore.exe | GET | 200 | 216.58.208.33:80 | http://4.bp.blogspot.com/-iLPZZBr7Zho/TeMRU7QrxvI/AAAAAAAAAOE/ey7QdhH6UYM/s320/IMG_0045.JPG | US | image | 20.3 Kb | whitelisted |
2760 | iexplore.exe | GET | 200 | 216.58.208.33:80 | http://2.bp.blogspot.com/-_JyUFOcMpmU/TeMSMi9yOqI/AAAAAAAAAOU/D8VSGB9xv2U/s320/IMG_0041.jpg | US | image | 25.5 Kb | whitelisted |
2760 | iexplore.exe | GET | 200 | 216.58.208.33:80 | http://2.bp.blogspot.com/-pYkLNwDyn1I/TeMS-tQGy1I/AAAAAAAAAOc/H7OETohgaek/s320/IMG_0043.jpg | US | image | 28.5 Kb | whitelisted |
3392 | iexplore.exe | GET | 200 | 172.217.21.243:80 | http://www.goeggless.com/2011/05/mint-bistro-las-vegas.html | US | html | 12.9 Kb | malicious |
2760 | iexplore.exe | GET | 200 | 199.59.242.151:80 | http://h1.ripway.com/anniebluesky/blogustudent.png | US | html | 3.93 Kb | whitelisted |
2760 | iexplore.exe | GET | 304 | 216.58.208.33:80 | http://1.bp.blogspot.com/_7gvEO0dUECo/SNMw_ks1OXI/AAAAAAAAAGA/KupJ-ab03l4/S1600-R/title2.jpg | US | image | 9.78 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2760 | iexplore.exe | 216.58.208.33:80 | 1.bp.blogspot.com | Google Inc. | US | whitelisted |
2760 | iexplore.exe | 52.203.42.164:80 | widget.foodieblogroll.com | Amazon.com, Inc. | US | unknown |
2760 | iexplore.exe | 172.217.22.41:80 | www.blogger.com | Google Inc. | US | whitelisted |
2760 | iexplore.exe | 172.217.18.2:80 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
2760 | iexplore.exe | 199.59.242.151:80 | h1.ripway.com | Bodis, LLC | US | malicious |
2760 | iexplore.exe | 54.152.63.67:80 | www.thedailygreen.com | Amazon.com, Inc. | US | unknown |
2760 | iexplore.exe | 2.21.36.164:80 | s7.addthis.com | GTT Communications Inc. | FR | suspicious |
3392 | iexplore.exe | 172.217.21.243:80 | www.goeggless.com | Google Inc. | US | whitelisted |
2760 | iexplore.exe | 104.111.246.221:80 | banners.copyscape.com | Akamai International B.V. | NL | whitelisted |
3392 | iexplore.exe | 172.217.22.41:443 | www.blogger.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.blogger.com |
| shared |
www.bing.com |
| whitelisted |
apis.google.com |
| whitelisted |
resources.blogblog.com |
| whitelisted |
1.bp.blogspot.com |
| whitelisted |
img2.blogblog.com |
| suspicious |
img1.blogblog.com |
| suspicious |
widget.foodieblogroll.com |
| unknown |
banners.copyscape.com |
| unknown |
s7.addthis.com |
| whitelisted |