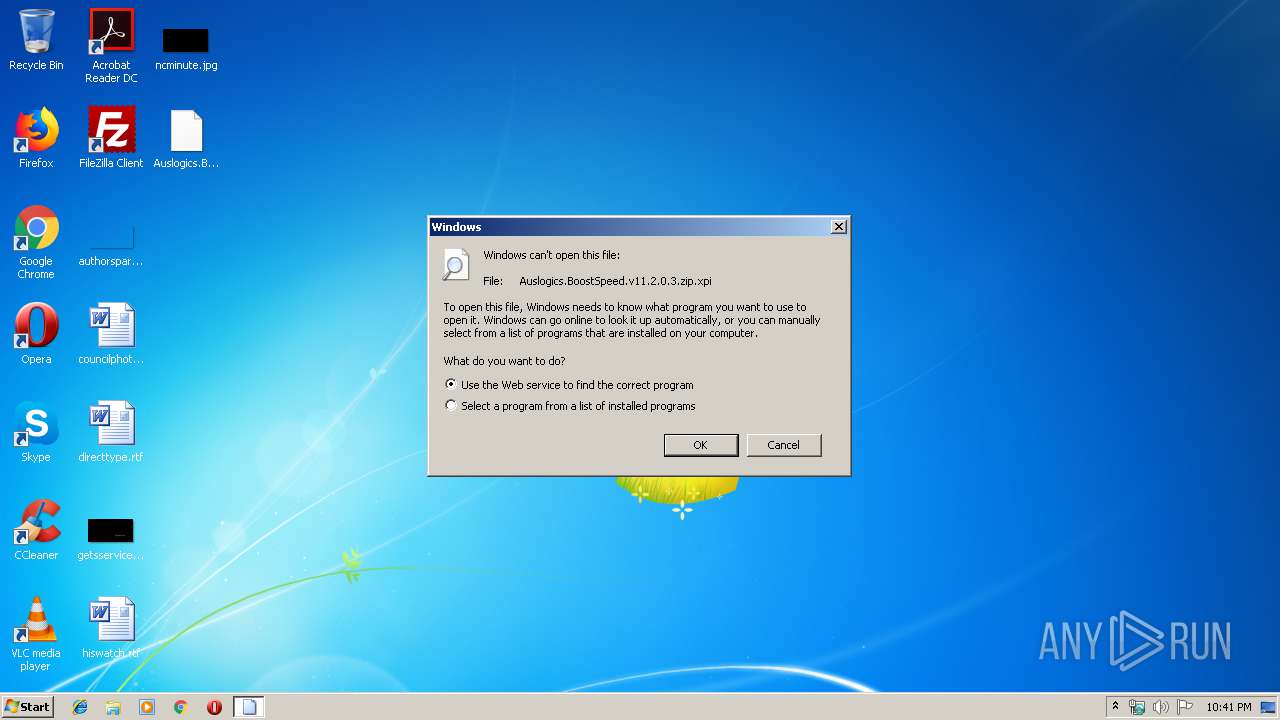
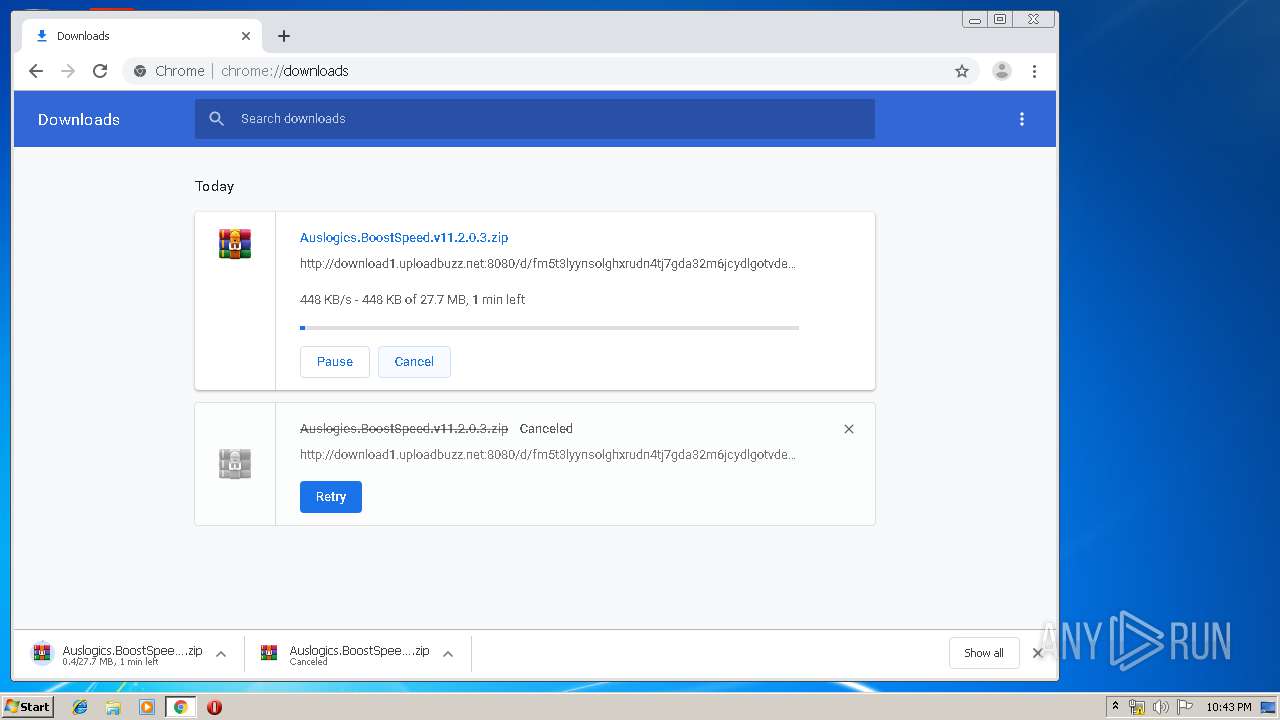
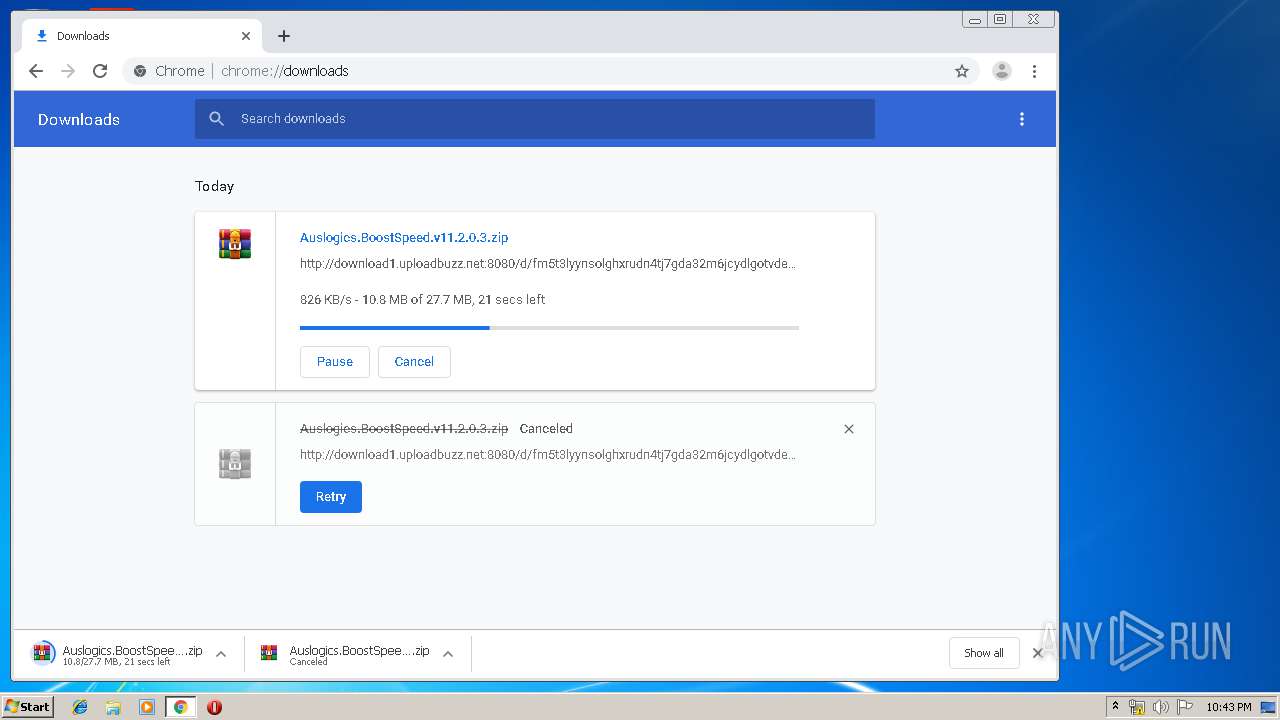
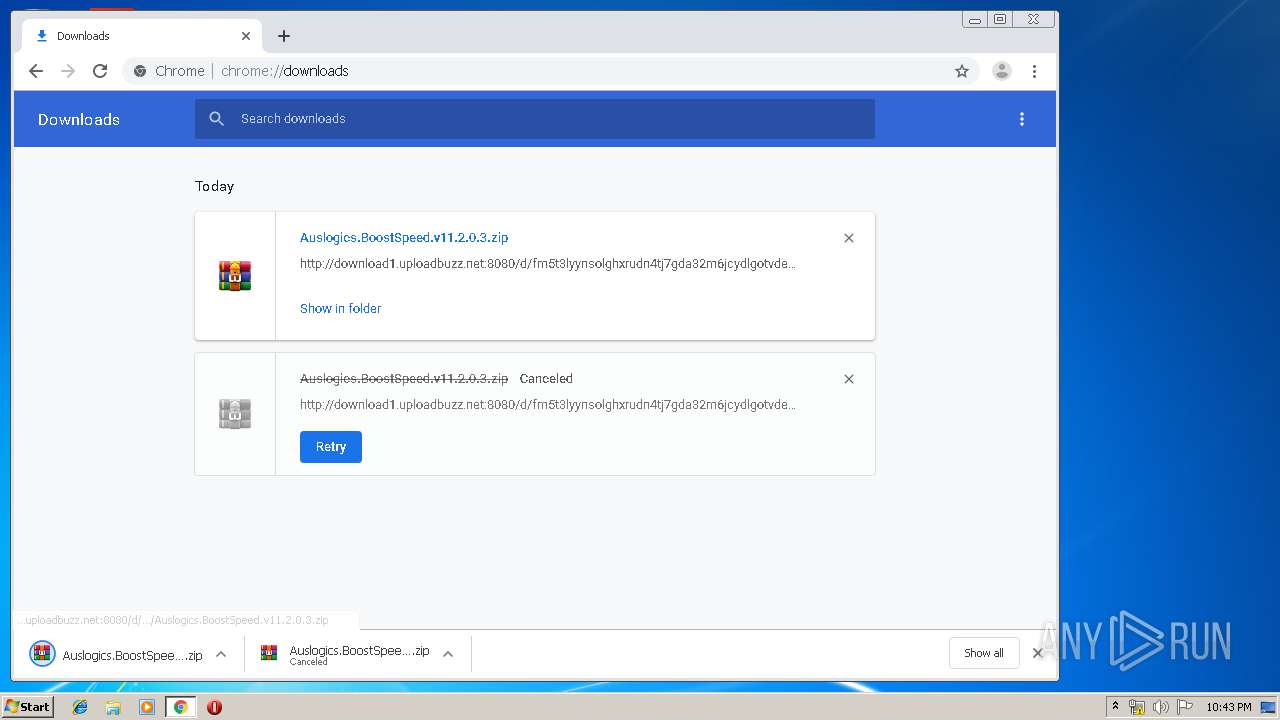
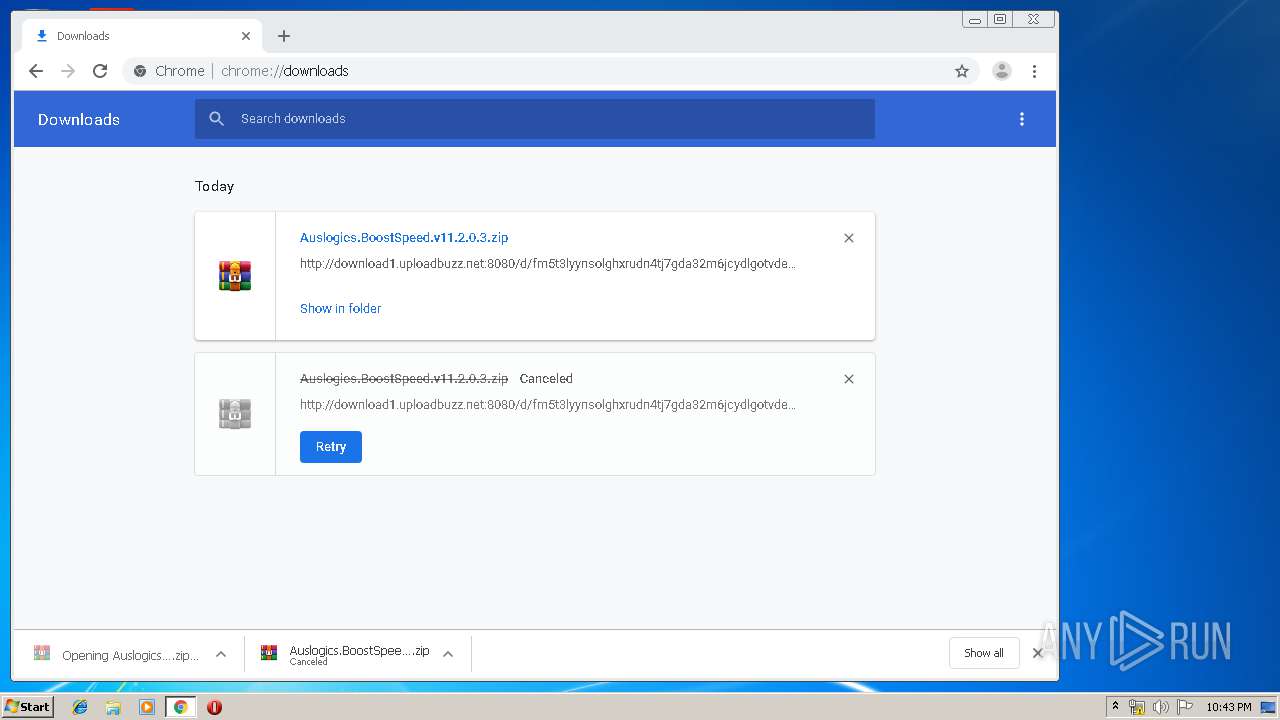
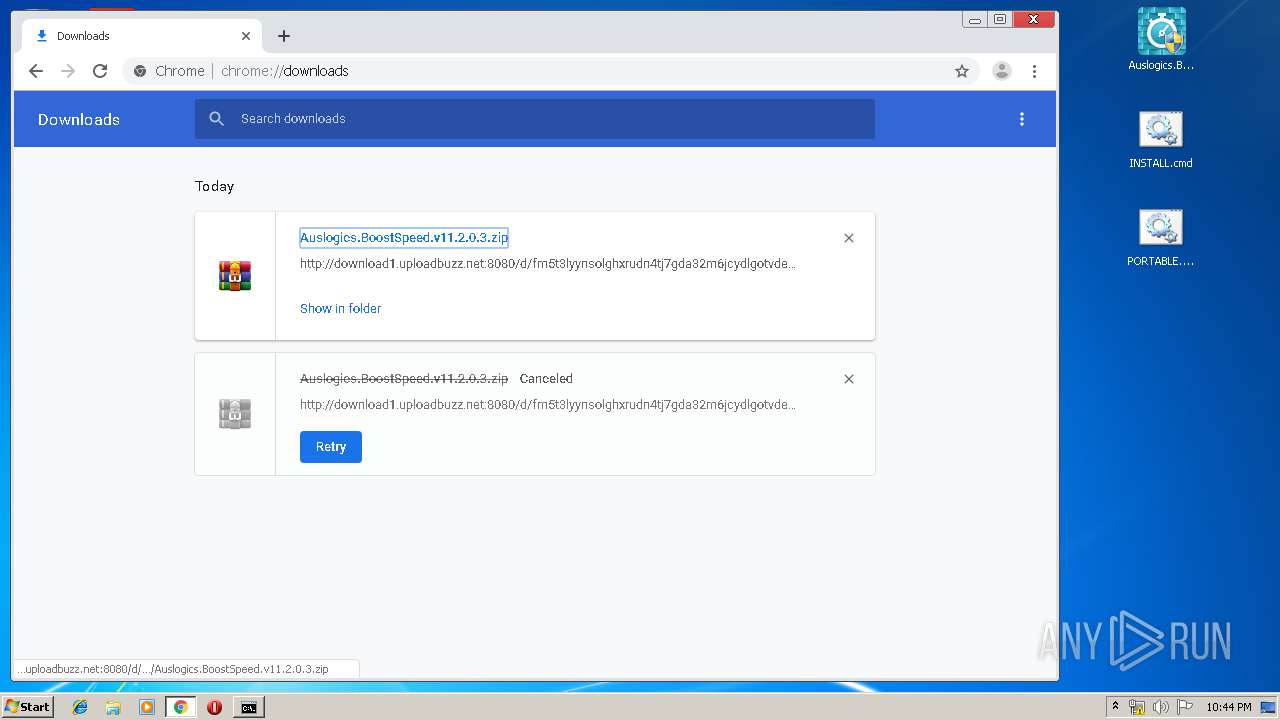
| download: | Auslogics.BoostSpeed.v11.2.0.3.zip |
| Full analysis: | https://app.any.run/tasks/1392379a-ea9c-4ab2-8fb8-6c12189bfa3f |
| Verdict: | Malicious activity |
| Analysis date: | December 02, 2019, 22:40:39 |
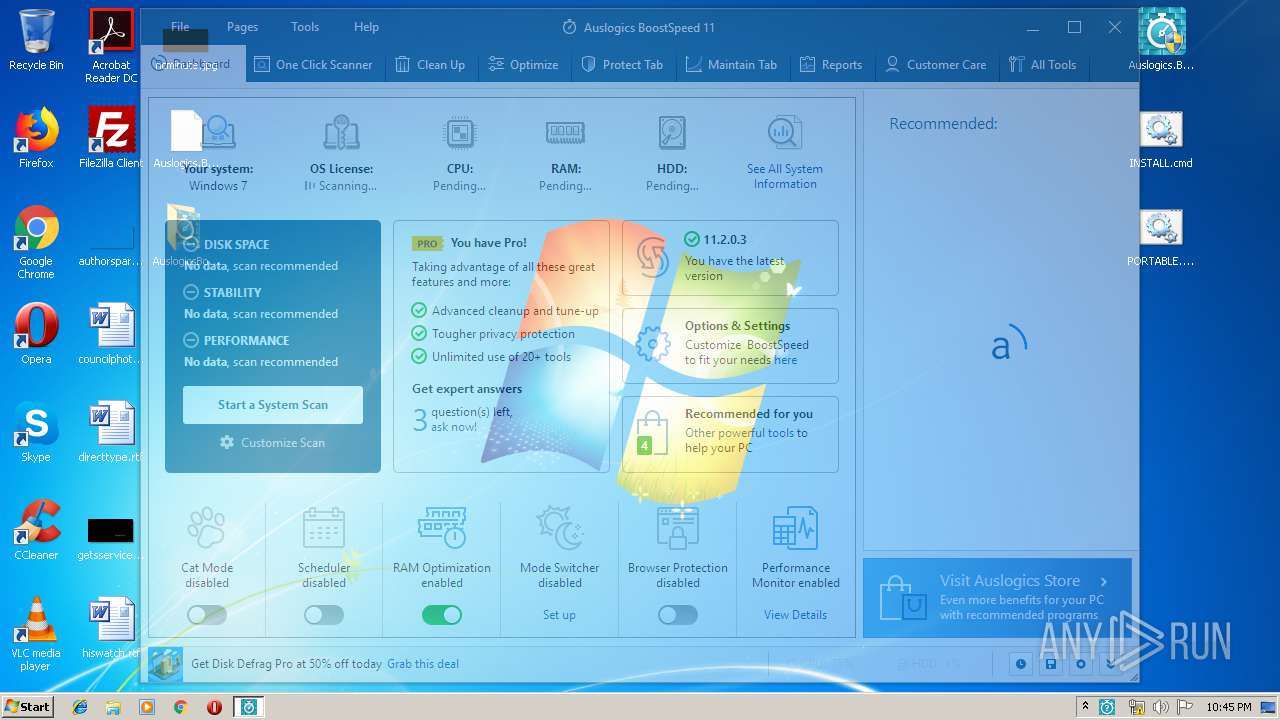
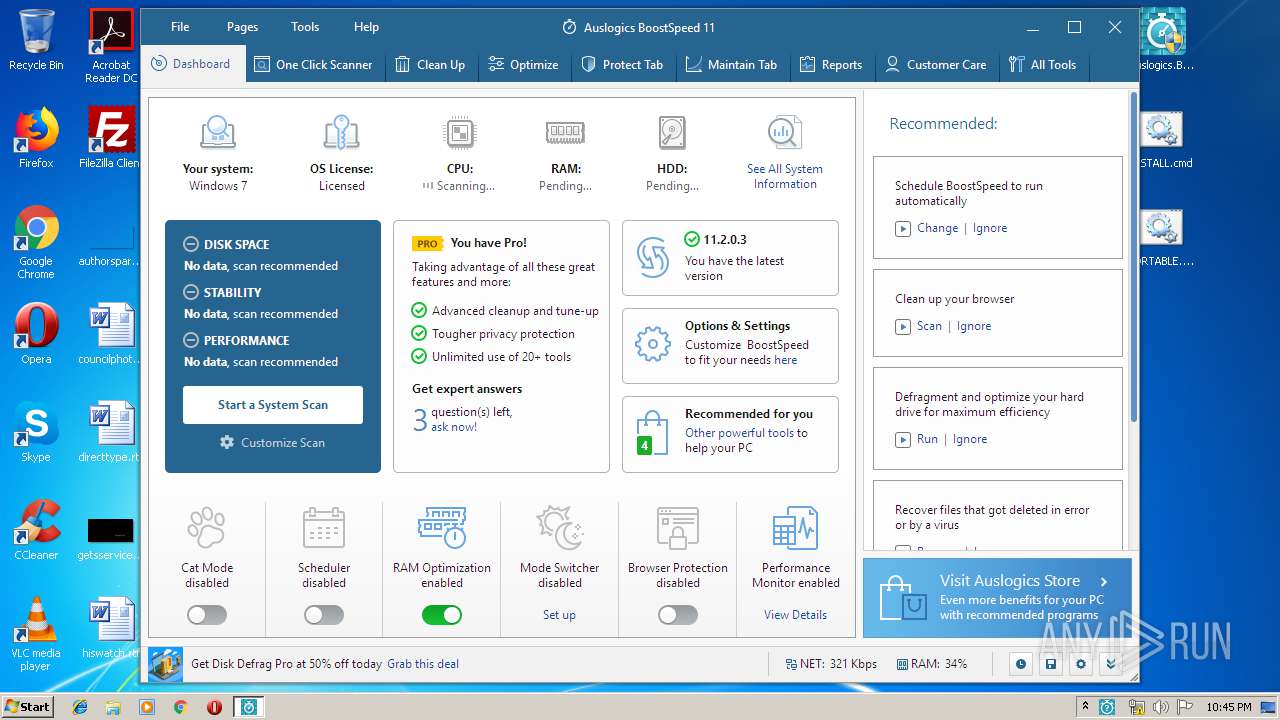
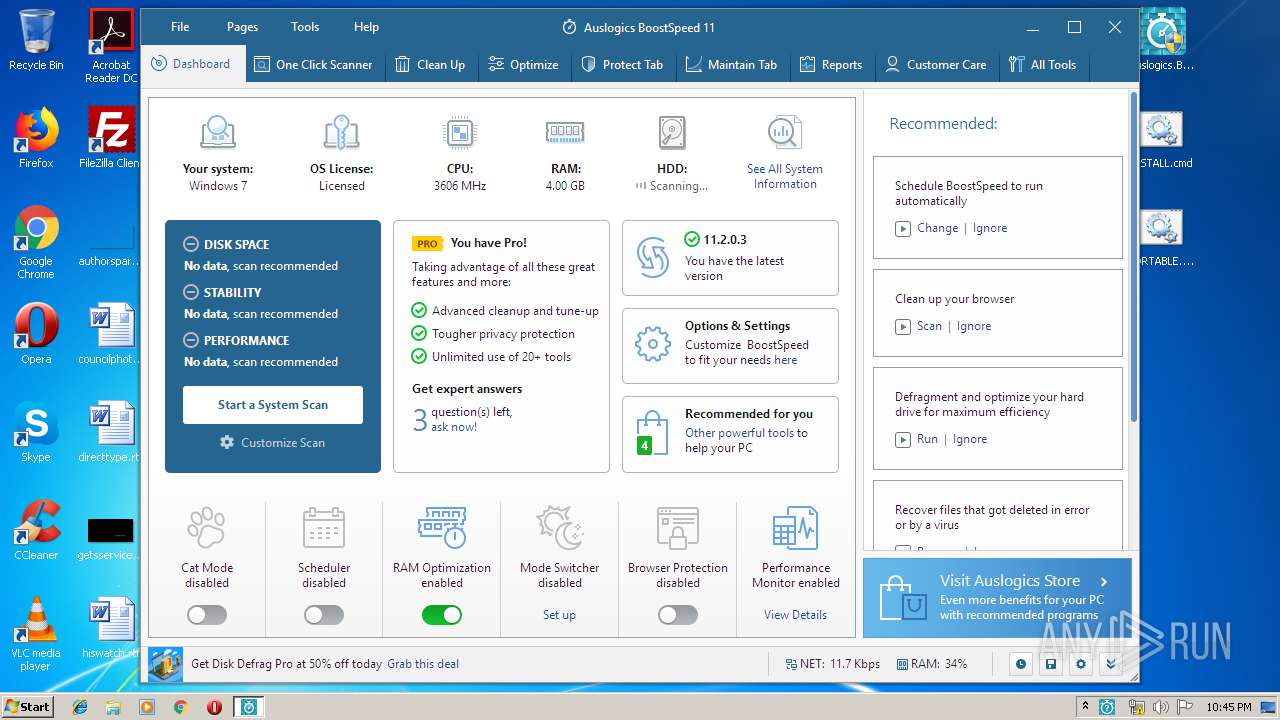
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | 1978408F4E6443D8D7B5D8FD3C92B0C9 |
| SHA1: | ADEF60584FC0417E49A989B08FD27B8C78304520 |
| SHA256: | 9429123F5DDE587D189CE92656793ADEC9A2808064896FA75F41286A848FAC87 |
| SSDEEP: | 393216:25oqBMgQBFAfnNiBeXyl886wi91H4YoQmDKQj7X/ROp8e6aVY/Nbo5XvkEw4UW:OowNivdRi9x4NQqLRM8e3cU5XsE7 |
MALICIOUS
Application was dropped or rewritten from another process
- Auslogics.BoostSpeed.v11.2.0.3.exe (PID: 3524)
- nsF84.tmp (PID: 444)
- Auslogics.BoostSpeed.v11.2.0.3.exe (PID: 1328)
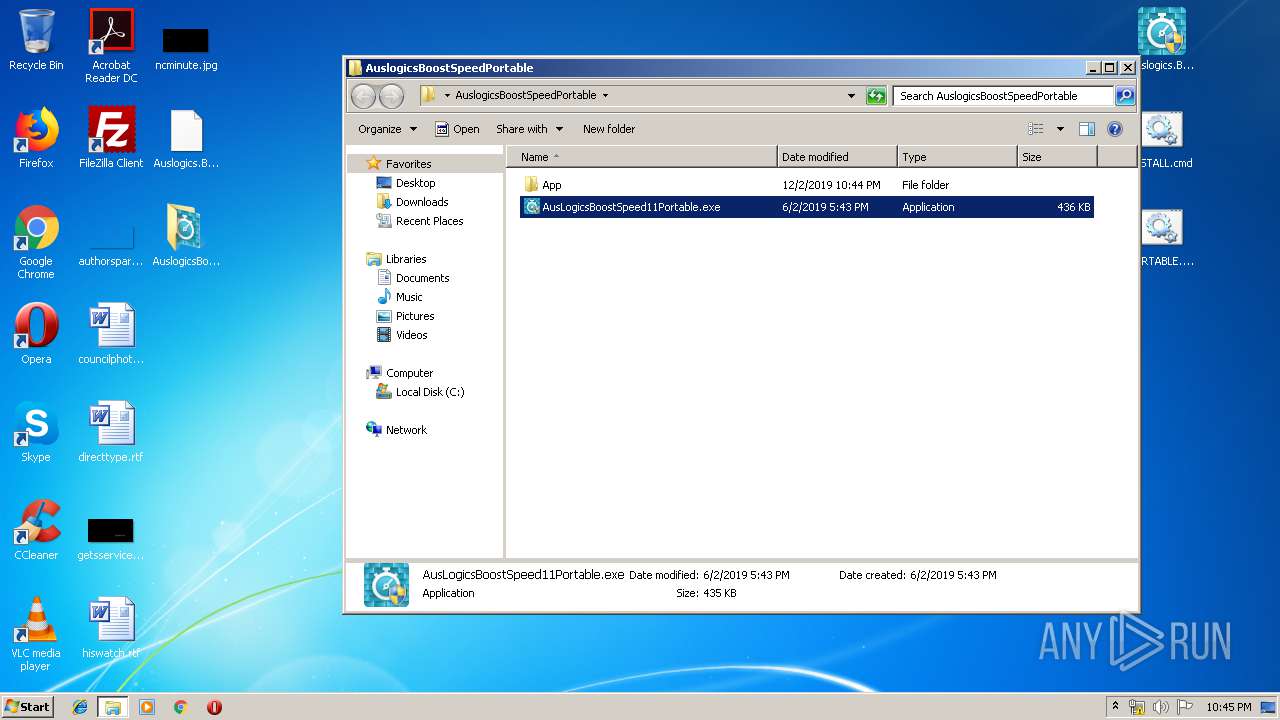
- AusLogicsBoostSpeed11Portable.exe (PID: 3712)
- tabprotect.exe (PID: 3676)
- Integrator.exe (PID: 436)
- tabdashboard.exe (PID: 2308)
- taboneclickscanner.exe (PID: 3076)
- tabcleanup.exe (PID: 1596)
- taboptimize.exe (PID: 2484)
- AusLogicsBoostSpeed11Portable.exe (PID: 2264)
- tabmaintain.exe (PID: 3856)
- tabreports.exe (PID: 2280)
- tabcarecenter.exe (PID: 2900)
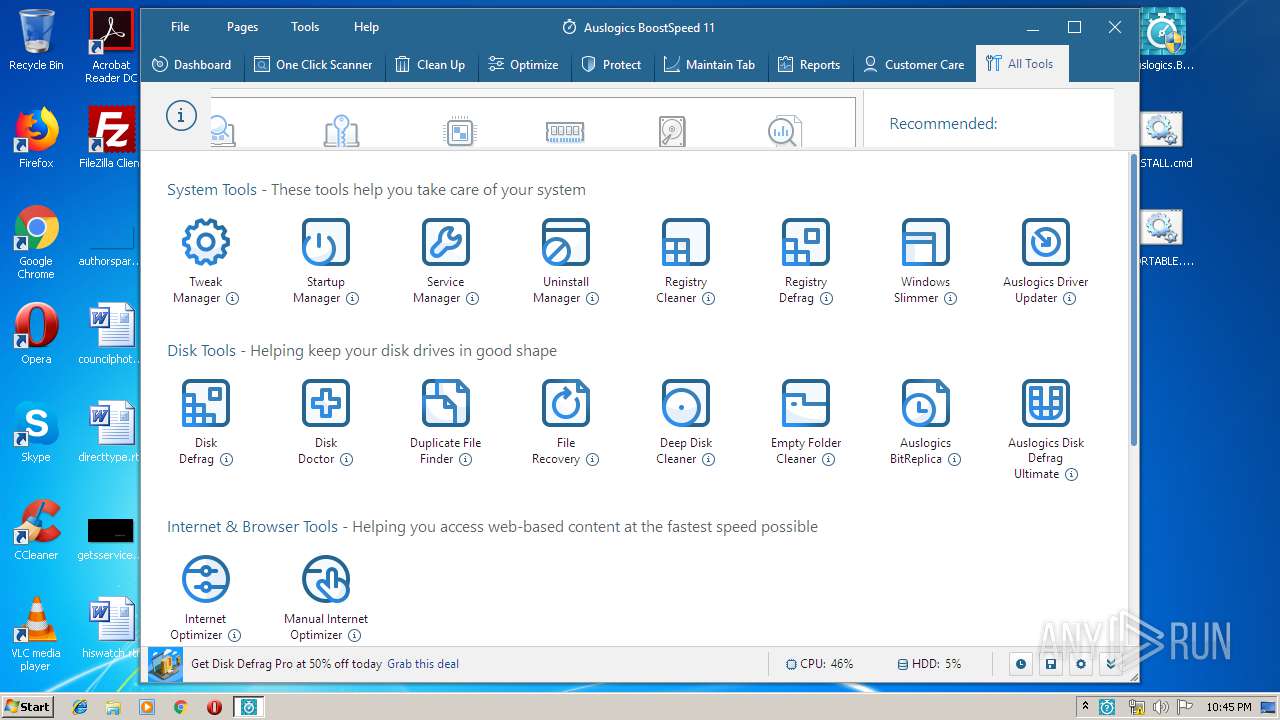
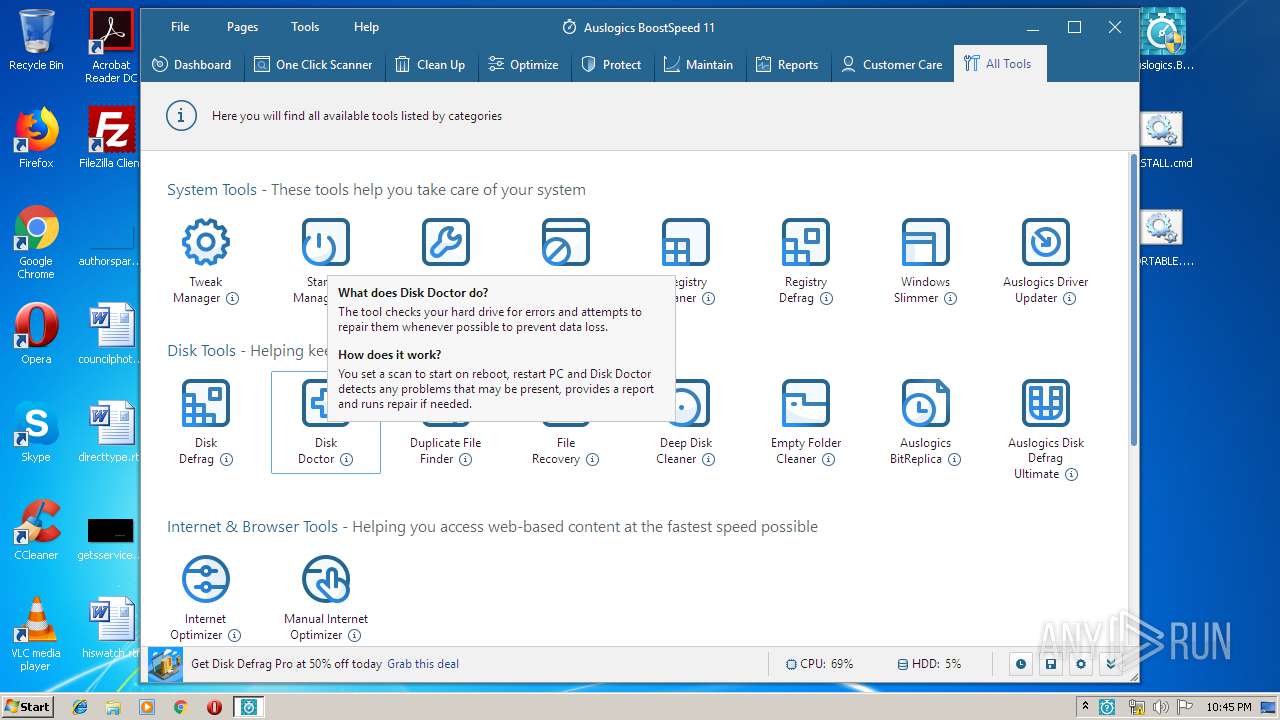
- taballtools.exe (PID: 4032)
- Auslogics.BoostSpeed.v11.2.0.3.exe (PID: 1532)
- ns13BB.tmp (PID: 3944)
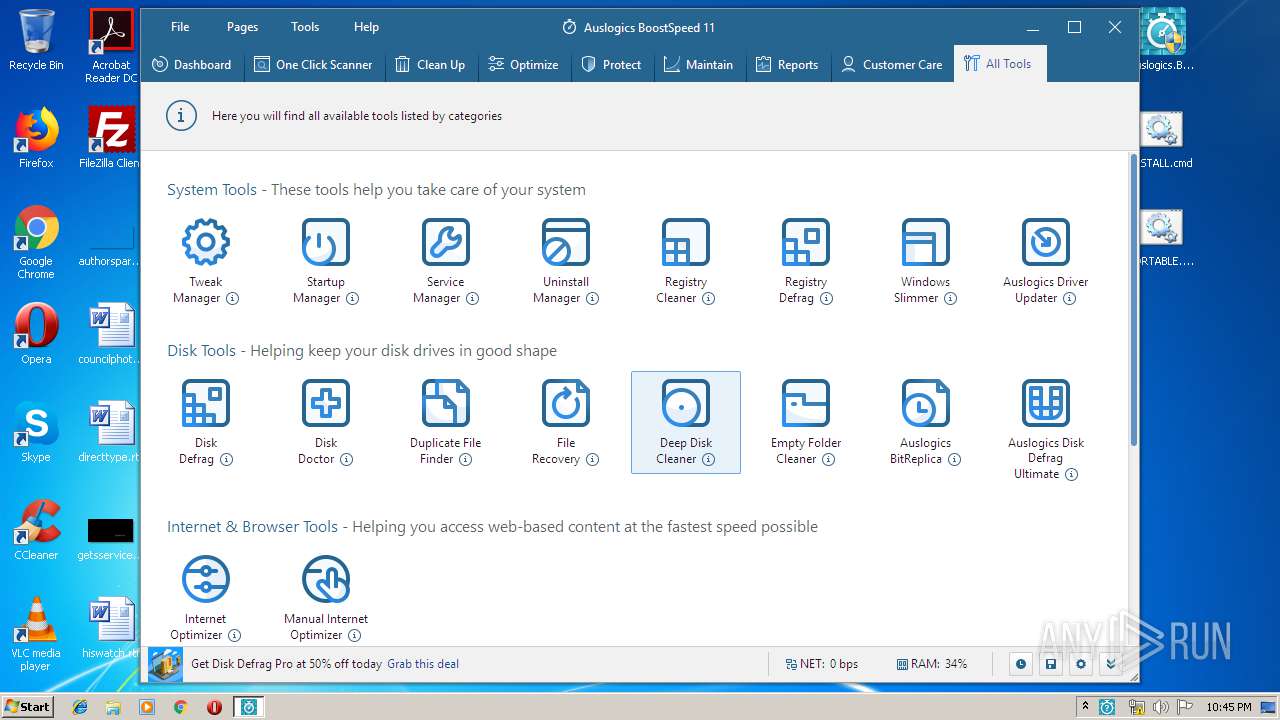
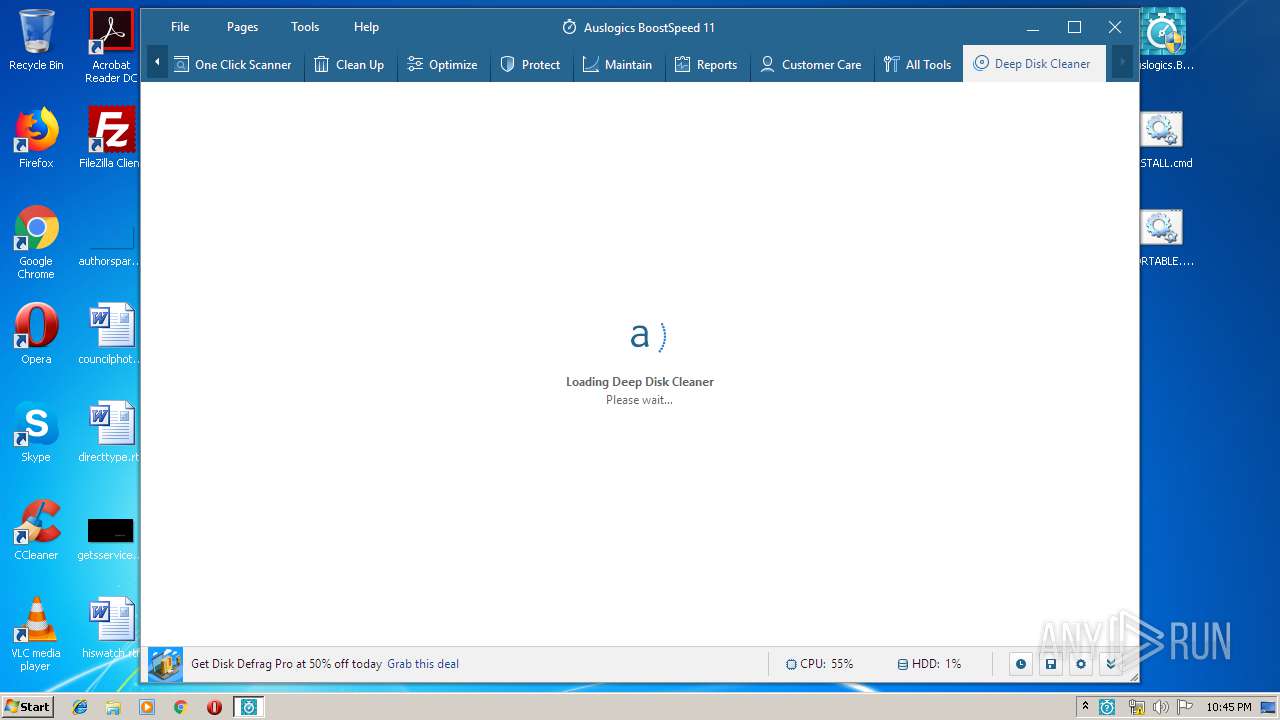
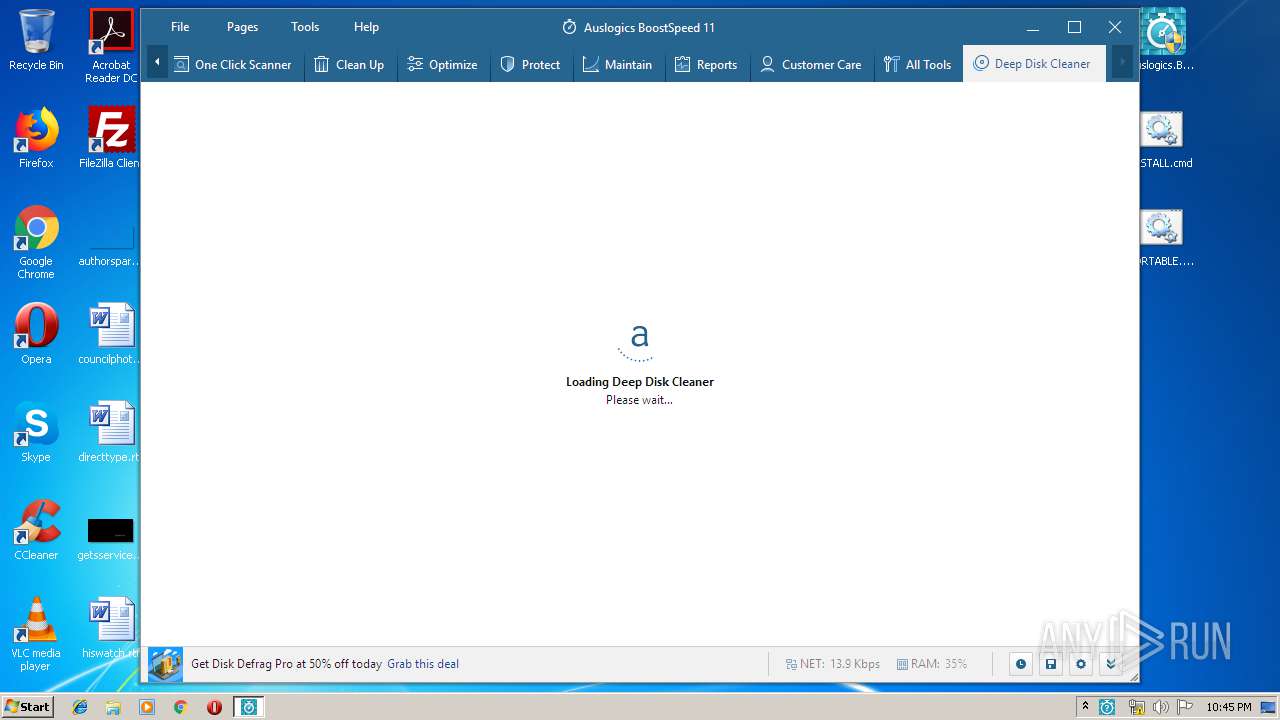
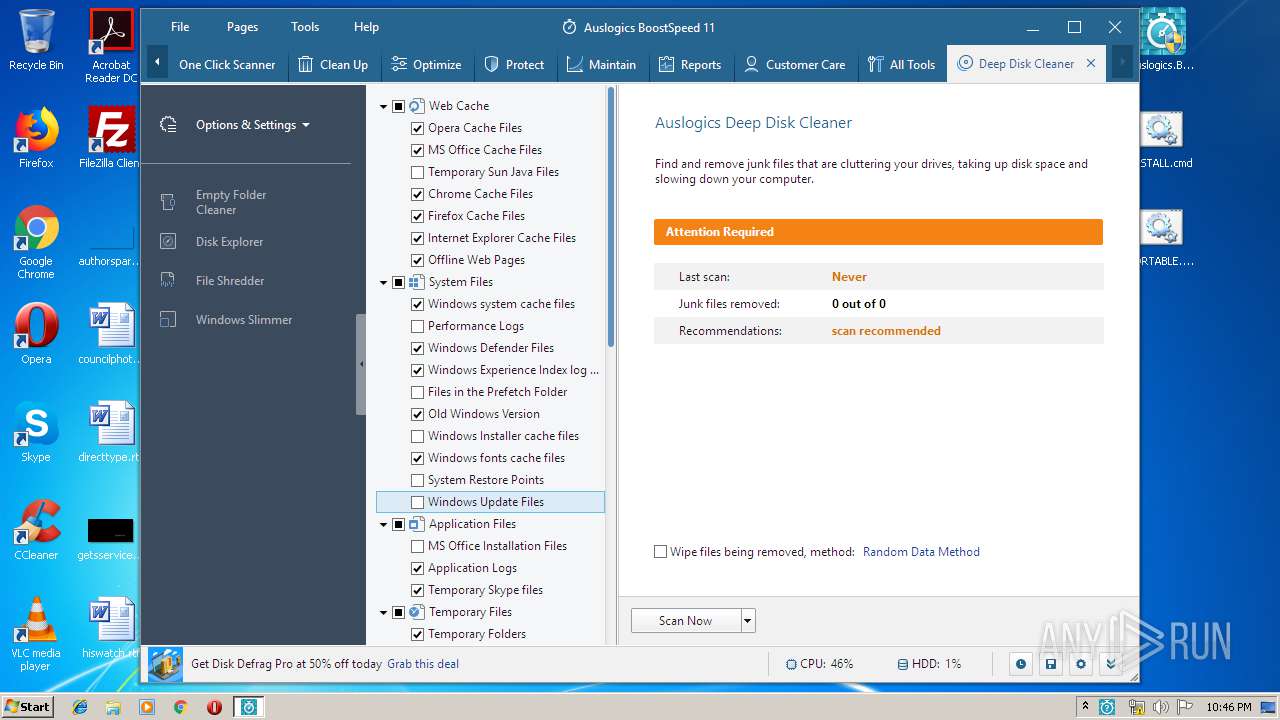
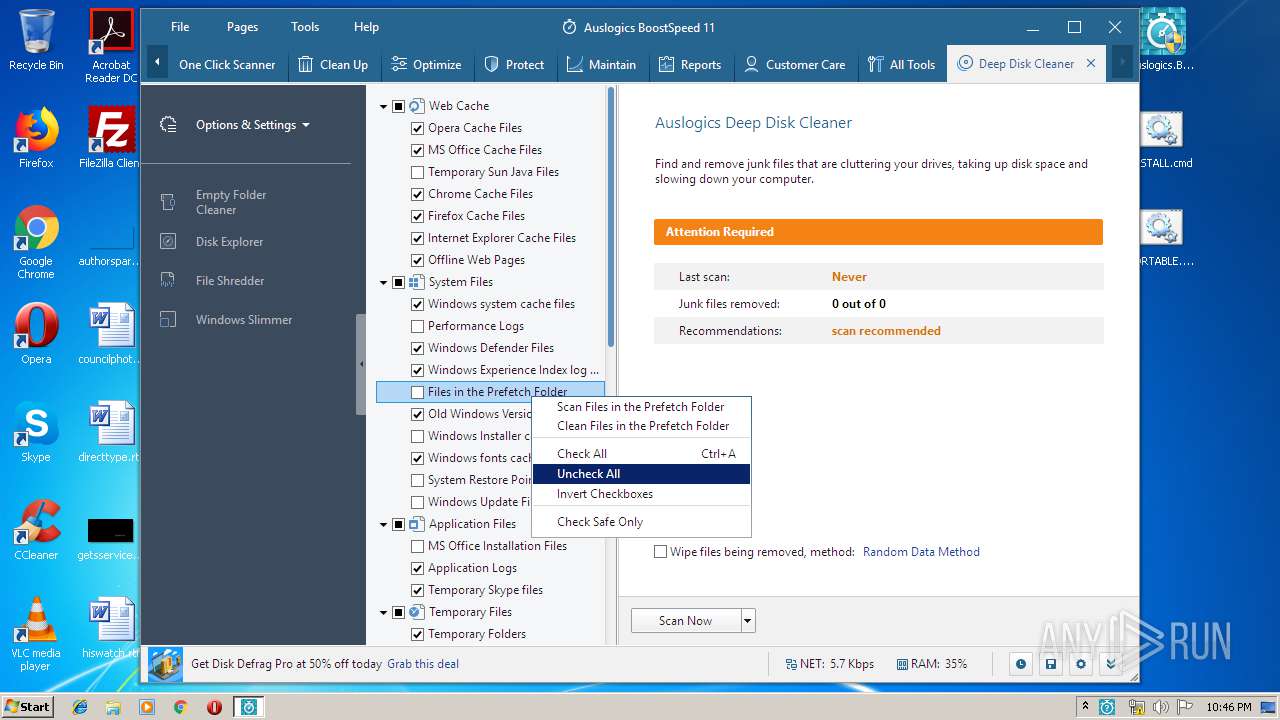
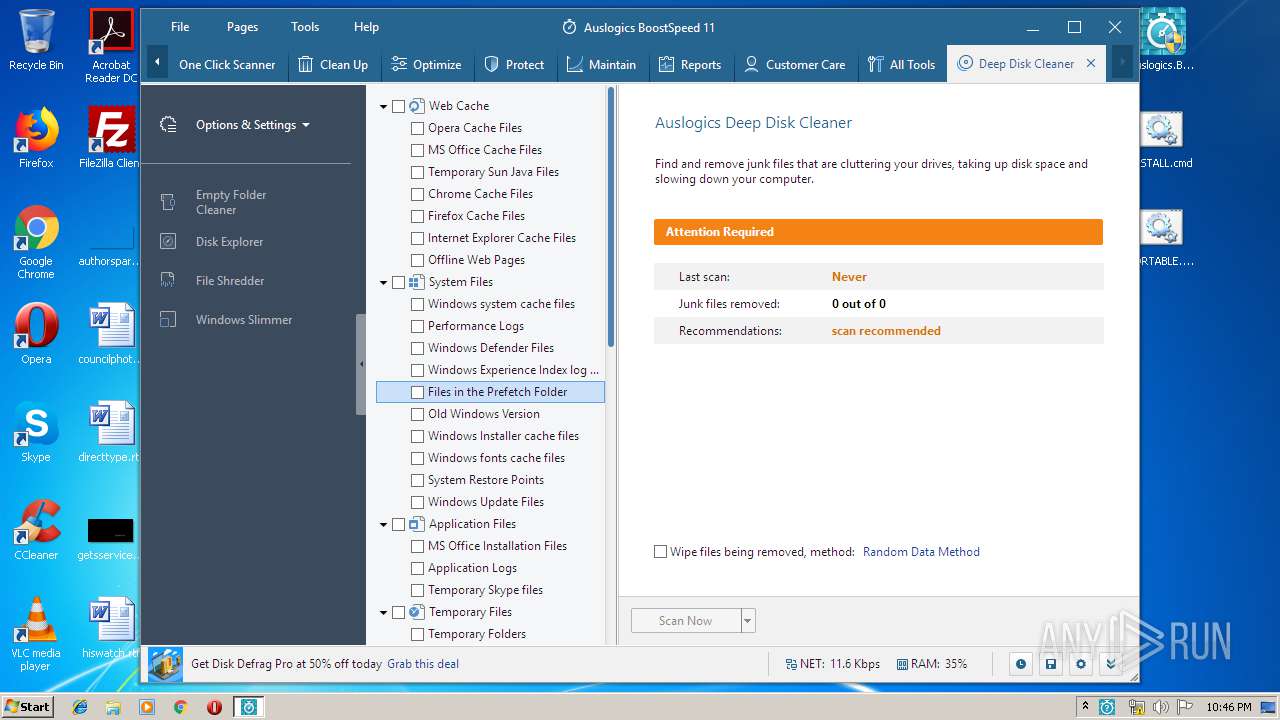
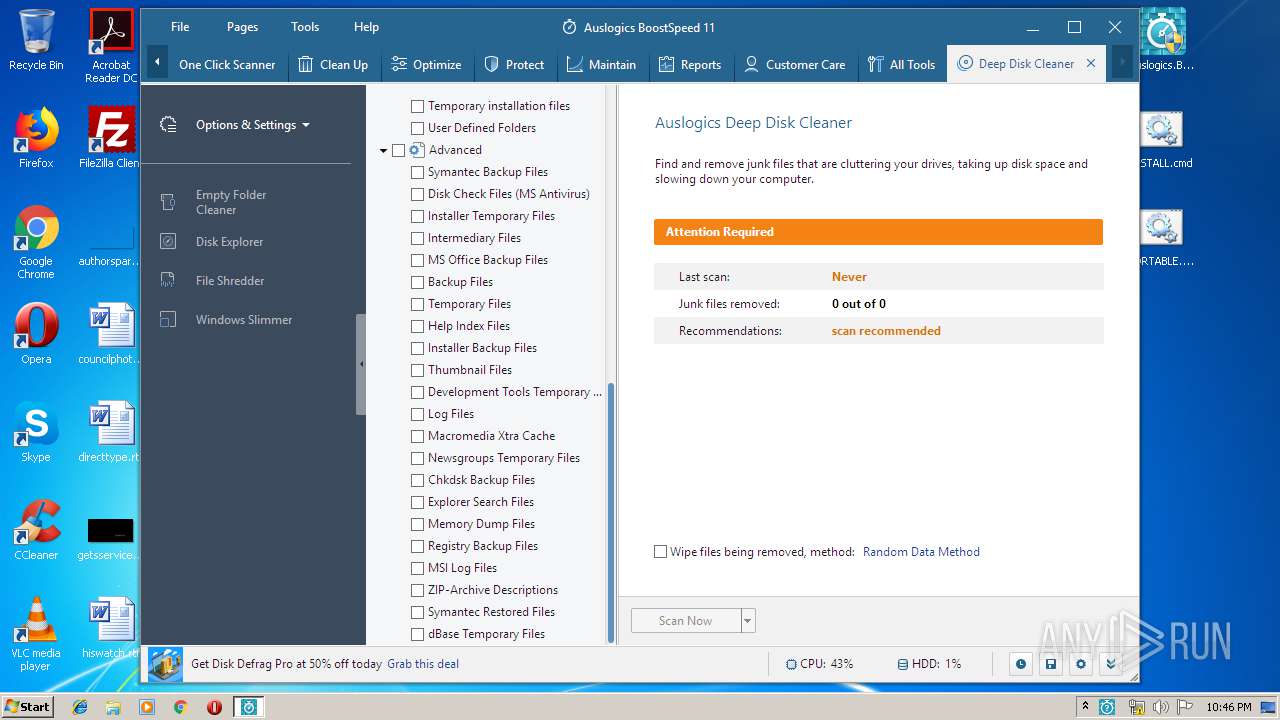
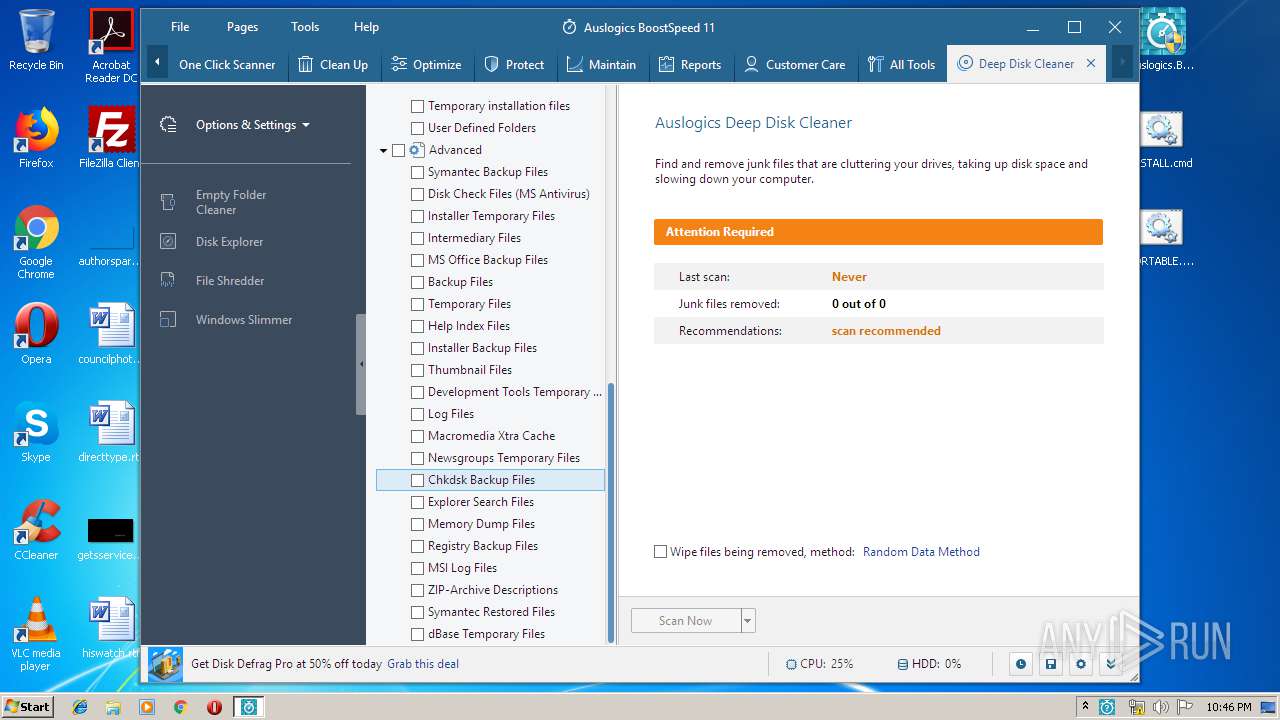
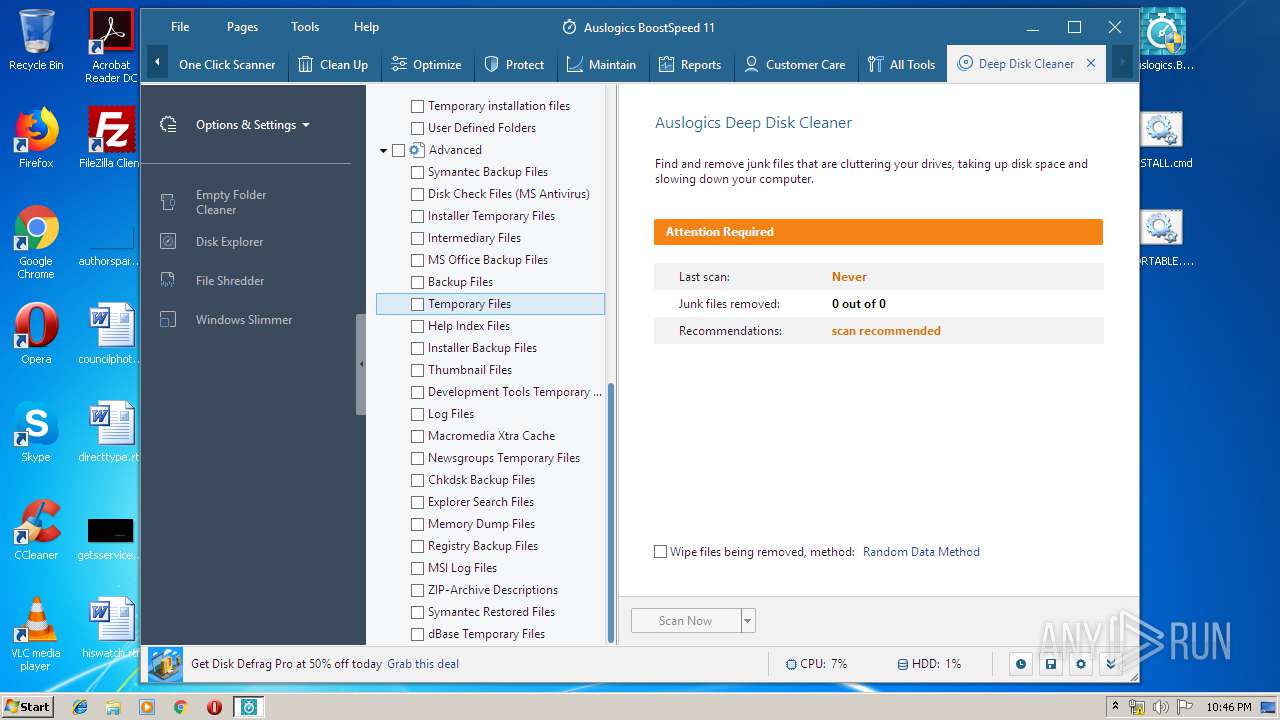
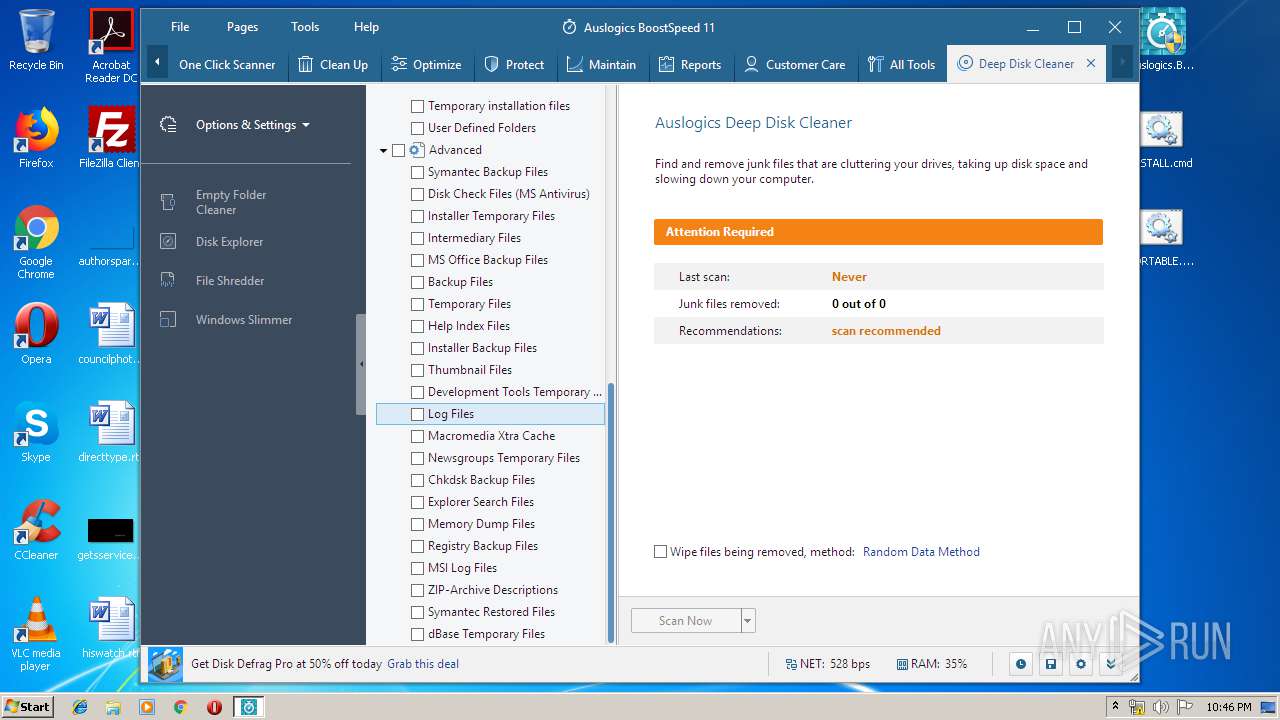
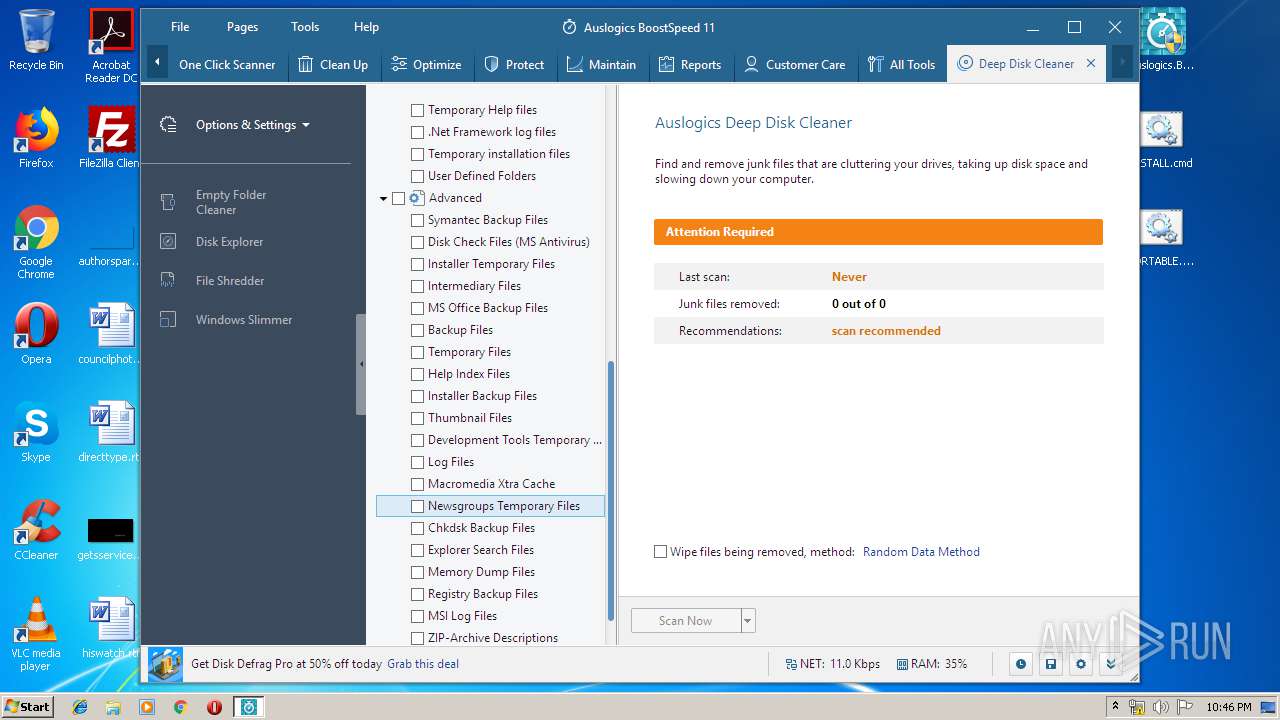
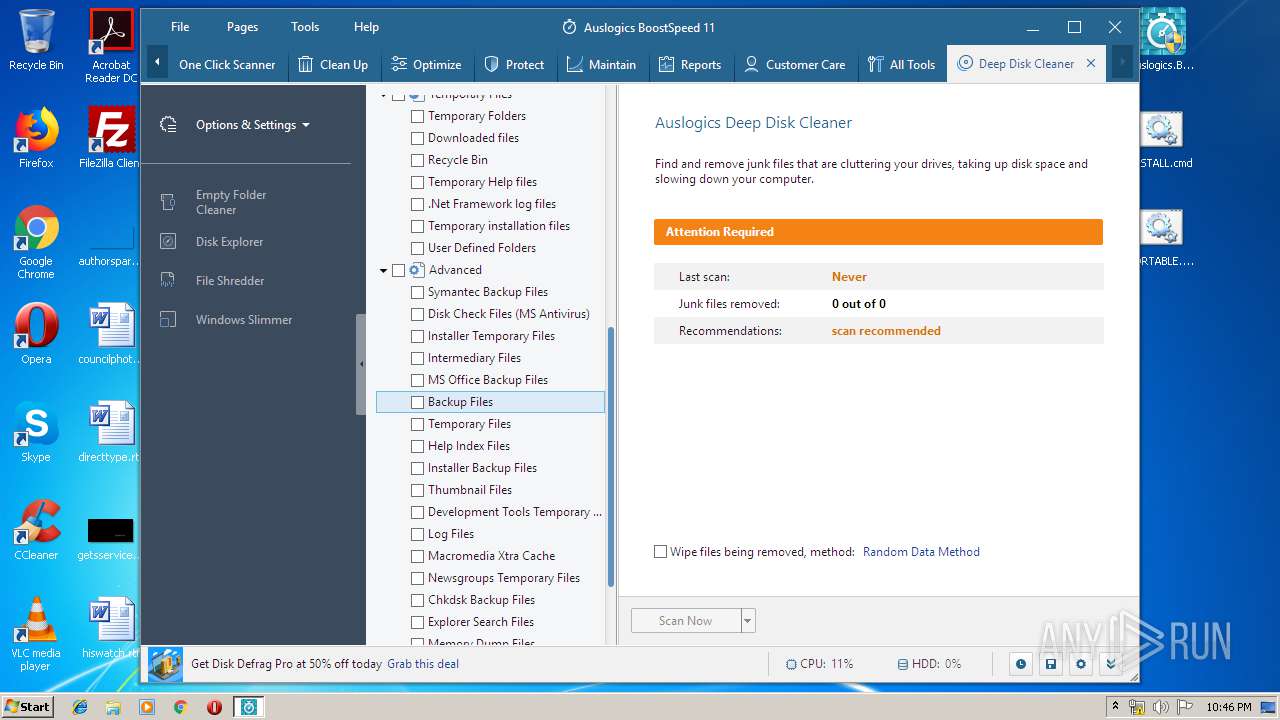
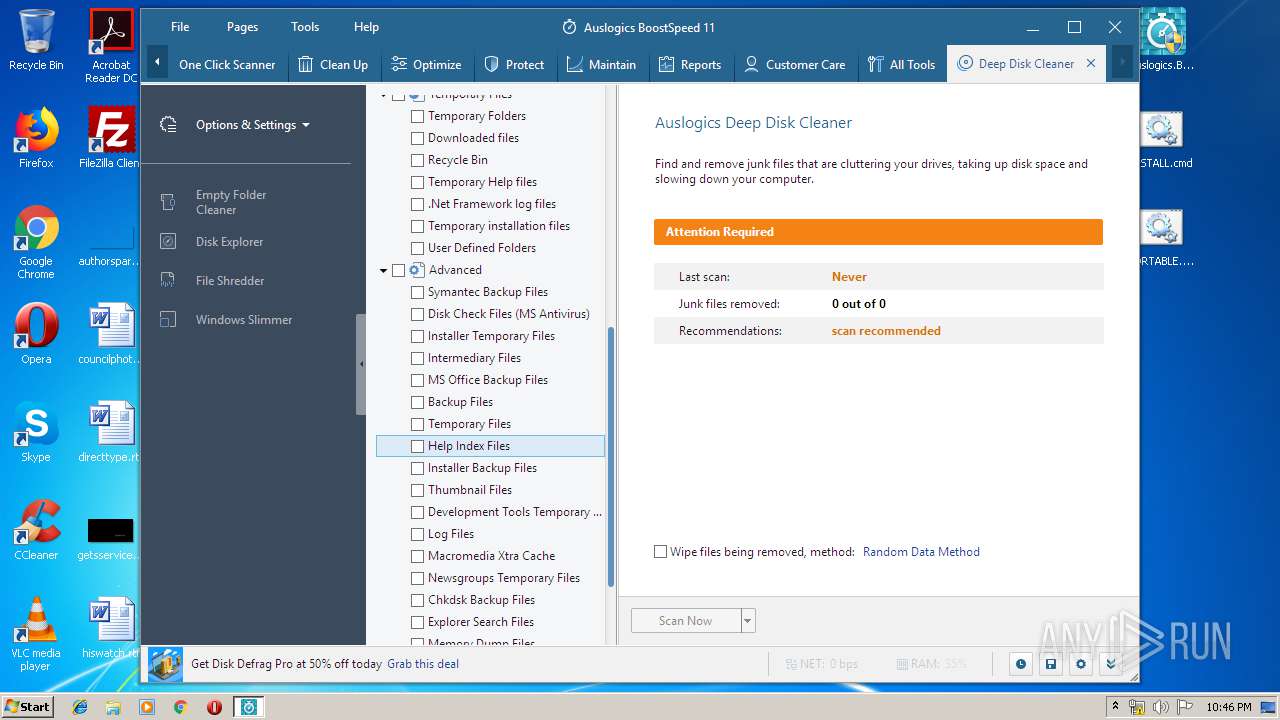
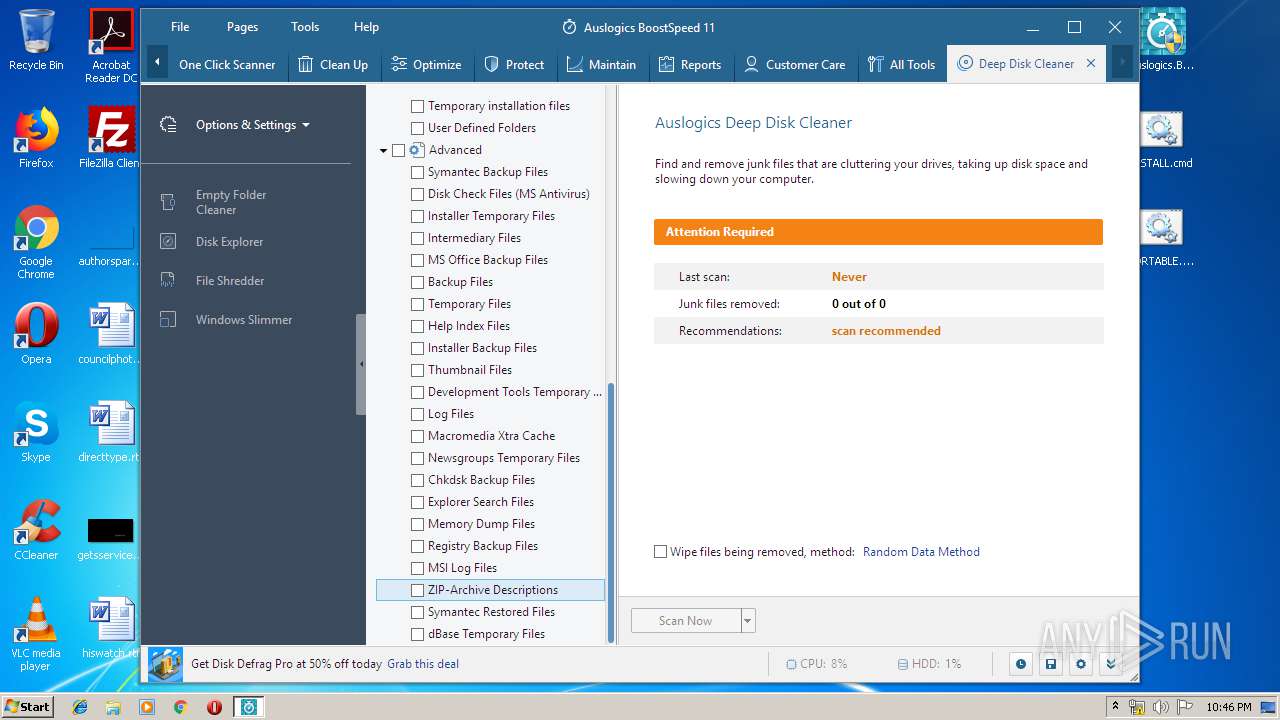
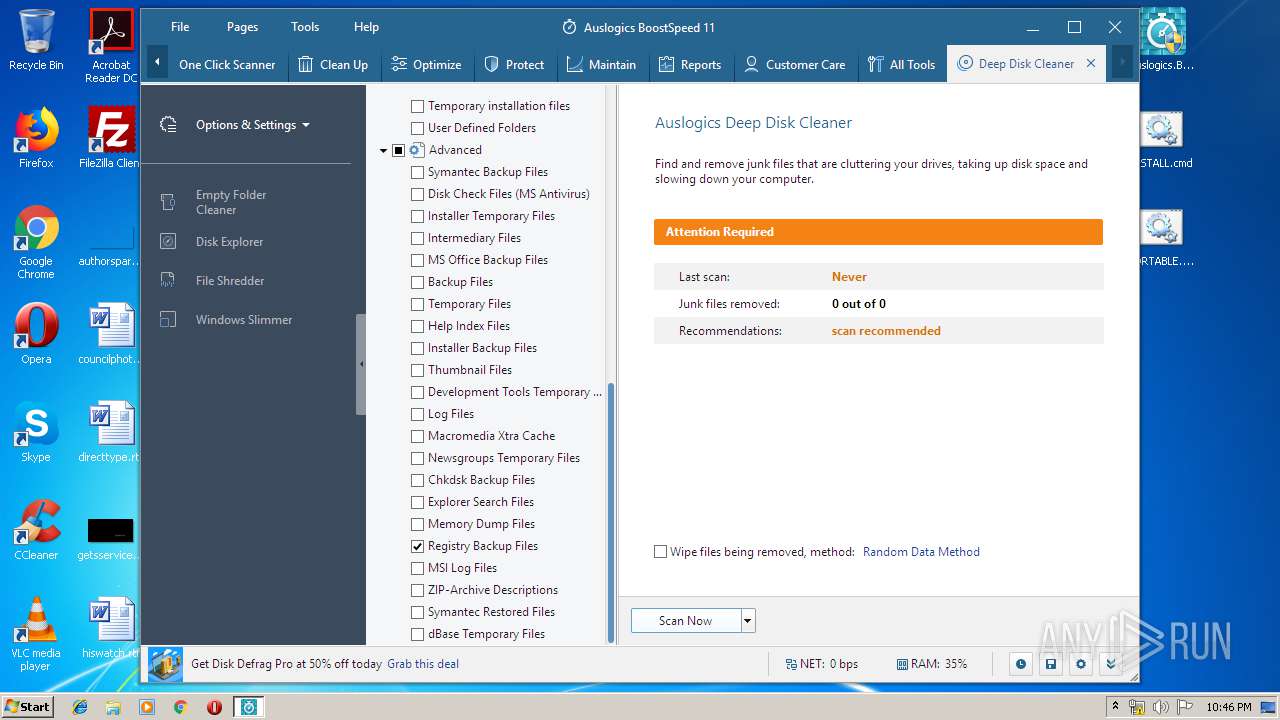
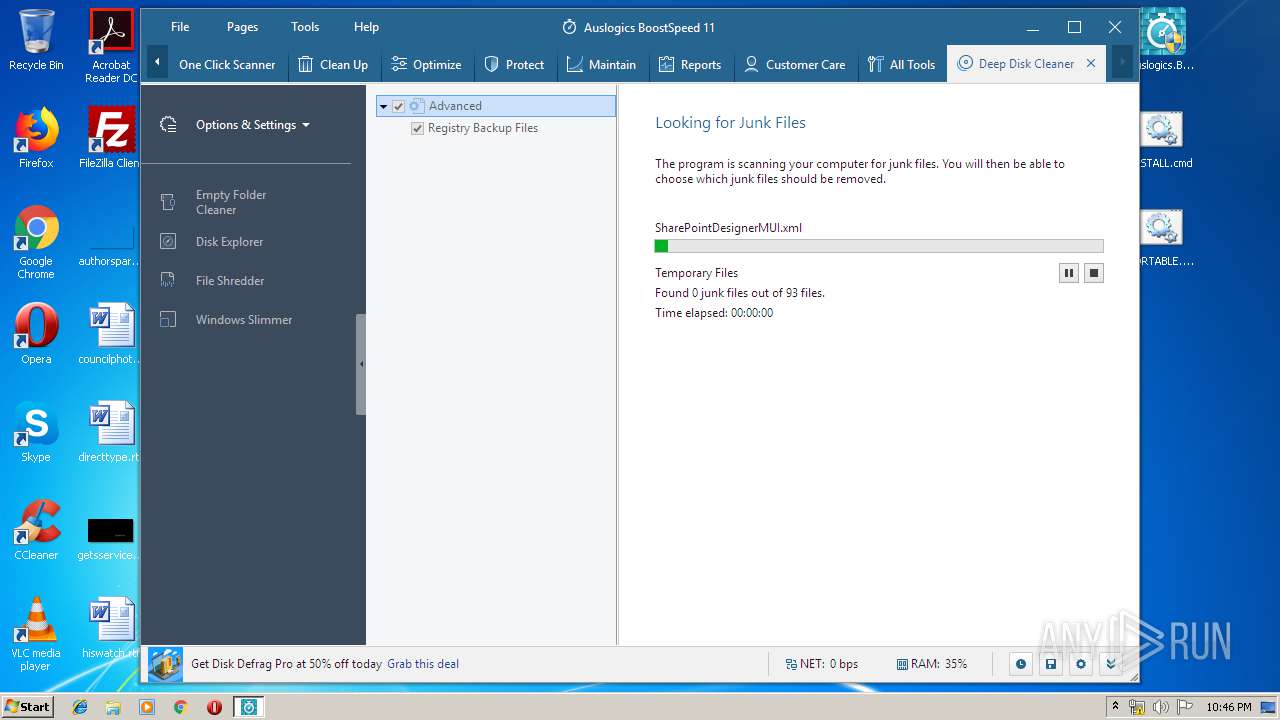
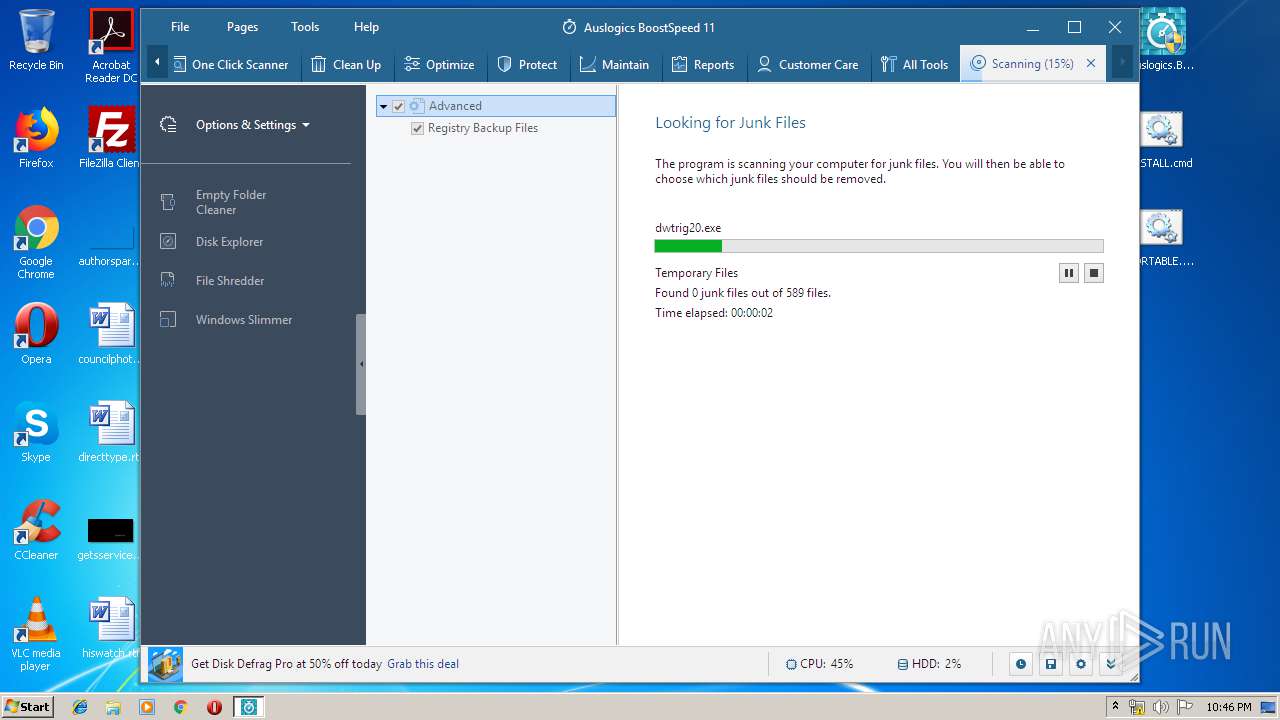
- DeepDiskCleaner.exe (PID: 2120)
Loads dropped or rewritten executable
- Auslogics.BoostSpeed.v11.2.0.3.exe (PID: 1532)
- SearchProtocolHost.exe (PID: 3088)
- AusLogicsBoostSpeed11Portable.exe (PID: 3712)
- Integrator.exe (PID: 436)
- tabcleanup.exe (PID: 1596)
- taboptimize.exe (PID: 2484)
- tabdashboard.exe (PID: 2308)
- tabprotect.exe (PID: 3676)
- tabcarecenter.exe (PID: 2900)
- tabmaintain.exe (PID: 3856)
- taballtools.exe (PID: 4032)
- taboneclickscanner.exe (PID: 3076)
- tabreports.exe (PID: 2280)
- DllHost.exe (PID: 2756)
- DeepDiskCleaner.exe (PID: 2120)
Loads the Task Scheduler COM API
- Integrator.exe (PID: 436)
- taboptimize.exe (PID: 2484)
- tabdashboard.exe (PID: 2308)
Actions looks like stealing of personal data
- tabprotect.exe (PID: 3676)
SUSPICIOUS
Starts application with an unusual extension
- Auslogics.BoostSpeed.v11.2.0.3.exe (PID: 1532)
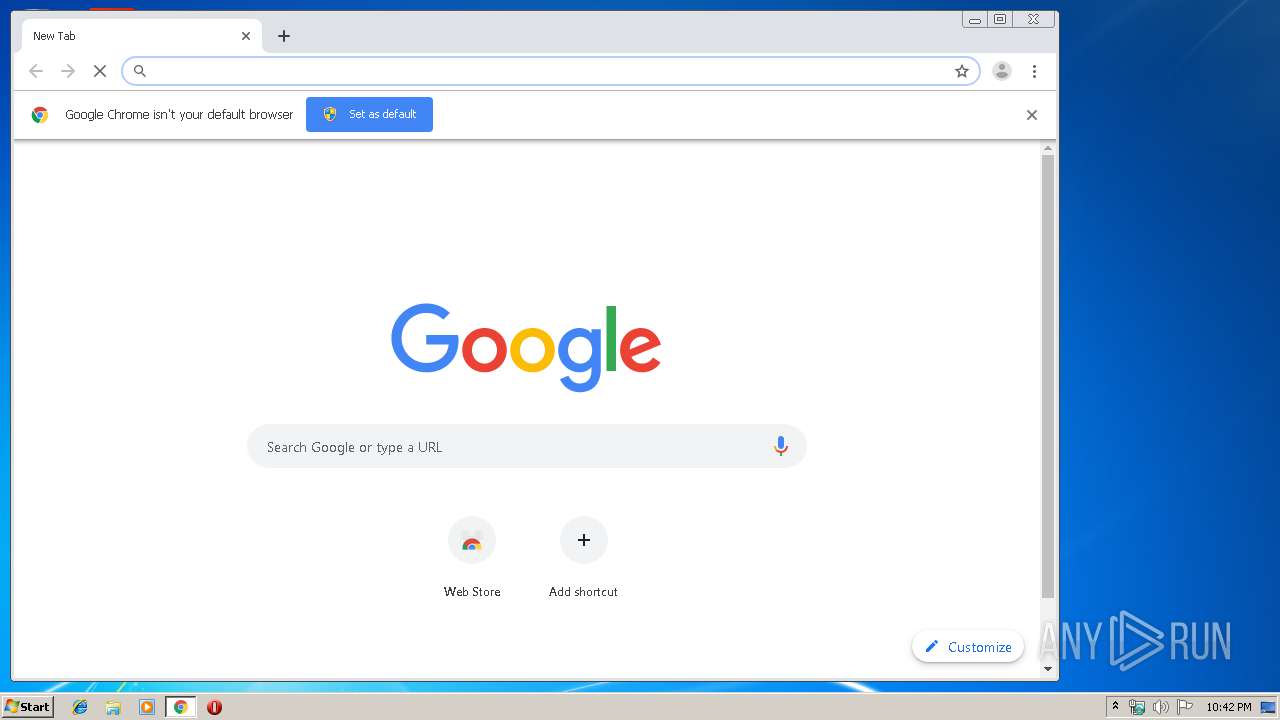
Modifies files in Chrome extension folder
- chrome.exe (PID: 3932)
Uses NETSH.EXE for network configuration
- nsF84.tmp (PID: 444)
Creates COM task schedule object
- AusLogicsBoostSpeed11Portable.exe (PID: 3712)
Reads Windows Product ID
- Integrator.exe (PID: 436)
- tabcleanup.exe (PID: 1596)
- taboneclickscanner.exe (PID: 3076)
- tabdashboard.exe (PID: 2308)
- tabreports.exe (PID: 2280)
- taballtools.exe (PID: 4032)
- tabprotect.exe (PID: 3676)
- taboptimize.exe (PID: 2484)
- tabmaintain.exe (PID: 3856)
- tabcarecenter.exe (PID: 2900)
- DeepDiskCleaner.exe (PID: 2120)
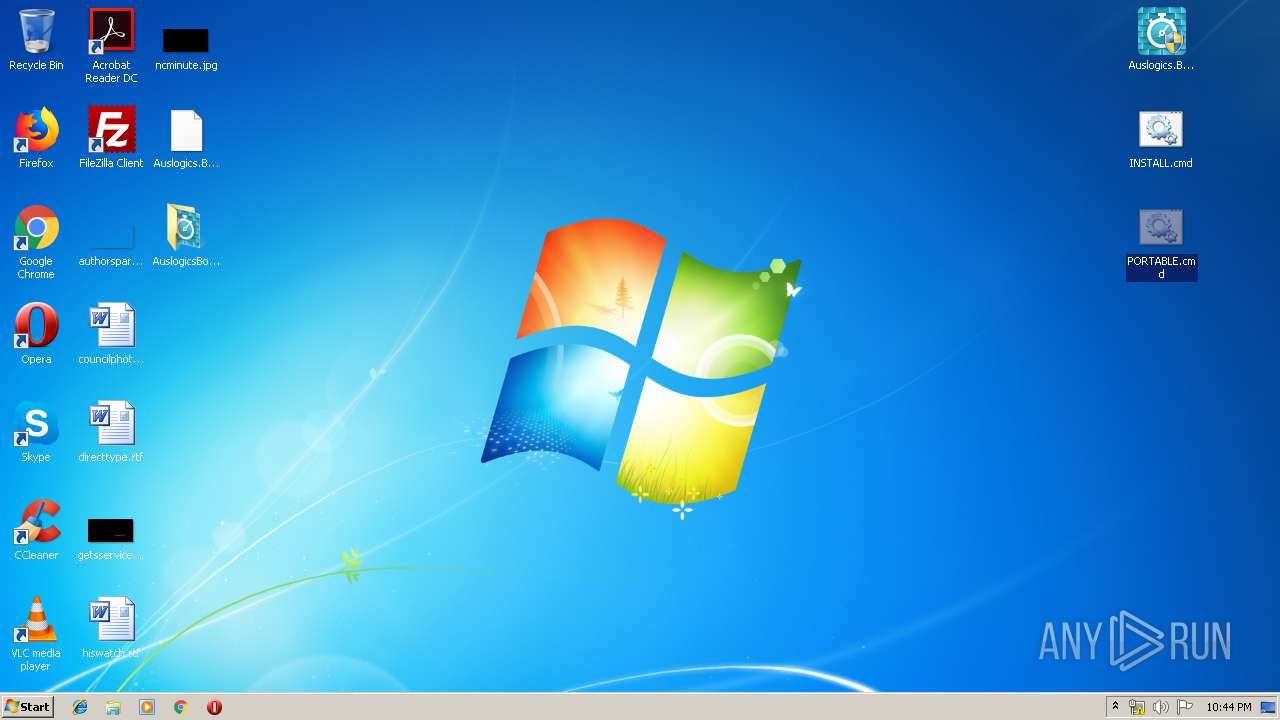
Executable content was dropped or overwritten
- AusLogicsBoostSpeed11Portable.exe (PID: 3712)
- Auslogics.BoostSpeed.v11.2.0.3.exe (PID: 1532)
Reads the machine GUID from the registry
- Integrator.exe (PID: 436)
- tabcleanup.exe (PID: 1596)
- tabdashboard.exe (PID: 2308)
- taboneclickscanner.exe (PID: 3076)
- tabreports.exe (PID: 2280)
- taballtools.exe (PID: 4032)
- taboptimize.exe (PID: 2484)
- tabprotect.exe (PID: 3676)
- tabmaintain.exe (PID: 3856)
- tabcarecenter.exe (PID: 2900)
- DeepDiskCleaner.exe (PID: 2120)
Low-level read access rights to disk partition
- Integrator.exe (PID: 436)
- tabcleanup.exe (PID: 1596)
- tabmaintain.exe (PID: 3856)
- taboptimize.exe (PID: 2484)
- tabdashboard.exe (PID: 2308)
- DeepDiskCleaner.exe (PID: 2120)
Reads the BIOS version
- tabprotect.exe (PID: 3676)
- tabcarecenter.exe (PID: 2900)
- Integrator.exe (PID: 436)
- taboptimize.exe (PID: 2484)
- tabdashboard.exe (PID: 2308)
Executed via COM
- DllHost.exe (PID: 2756)
Creates files in the program directory
- Integrator.exe (PID: 436)
- taboptimize.exe (PID: 2484)
- tabprotect.exe (PID: 3676)
- tabcarecenter.exe (PID: 2900)
Reads Internet Cache Settings
- Integrator.exe (PID: 436)
Searches for installed software
- tabmaintain.exe (PID: 3856)
- taboneclickscanner.exe (PID: 3076)
- taboptimize.exe (PID: 2484)
- Integrator.exe (PID: 436)
- DeepDiskCleaner.exe (PID: 2120)
INFO
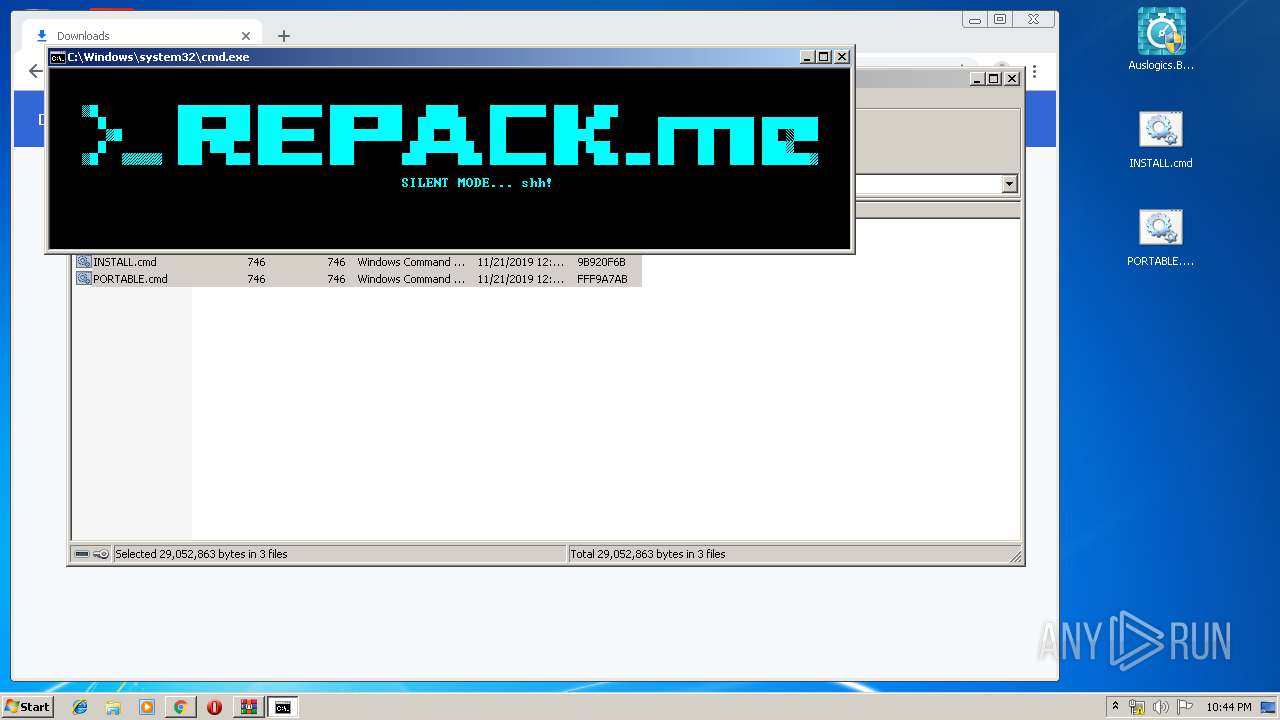
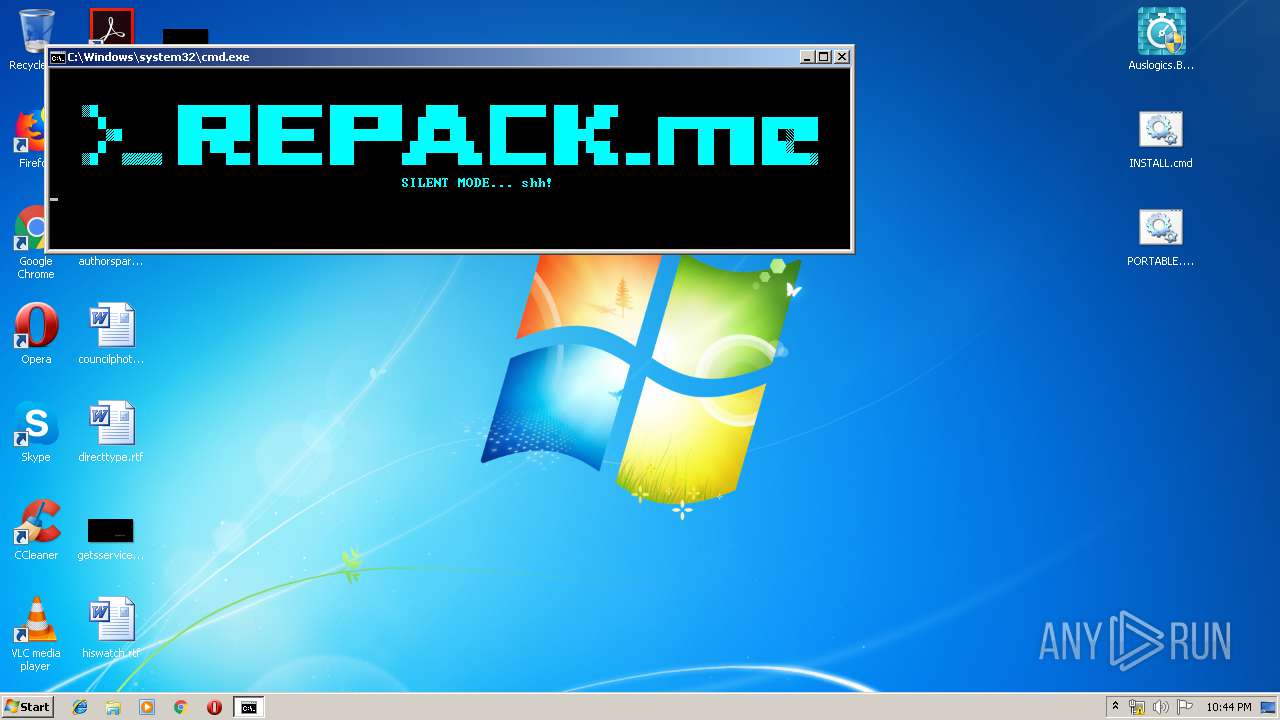
Manual execution by user
- chrome.exe (PID: 3932)
- cmd.exe (PID: 3260)
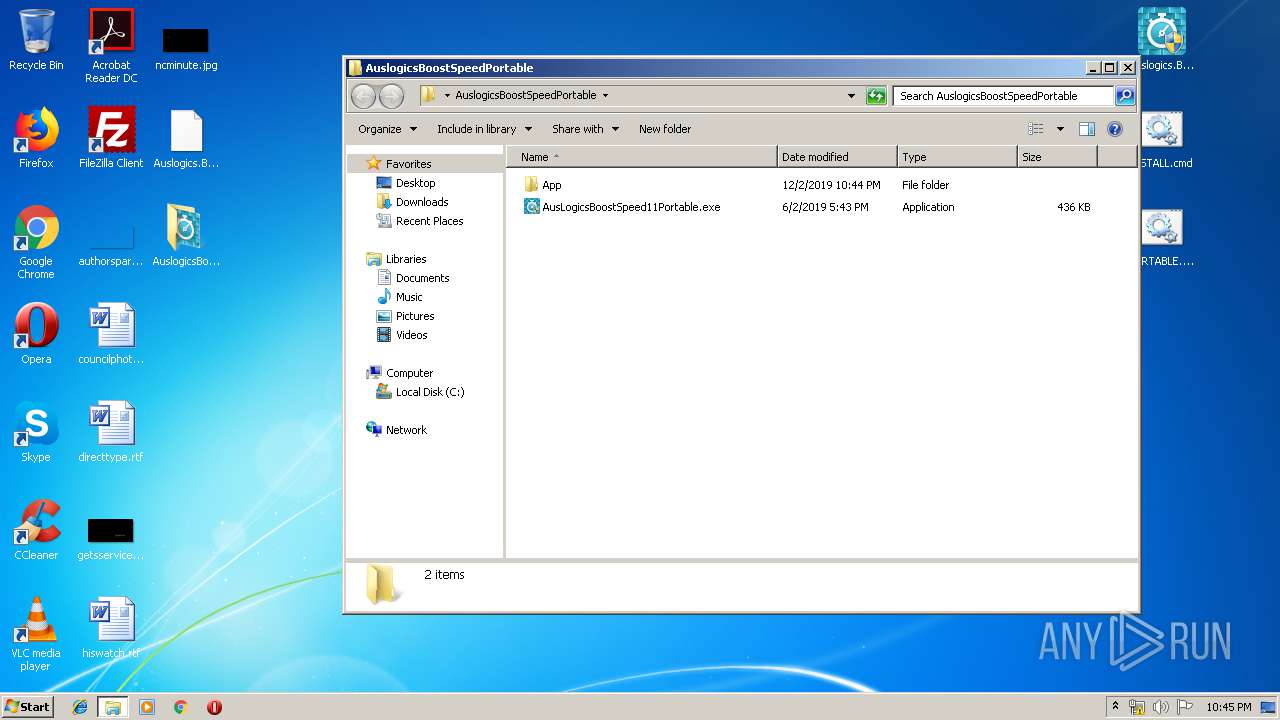
- AusLogicsBoostSpeed11Portable.exe (PID: 2264)
- AusLogicsBoostSpeed11Portable.exe (PID: 3712)
Reads the hosts file
- chrome.exe (PID: 3932)
- chrome.exe (PID: 2444)
- Auslogics.BoostSpeed.v11.2.0.3.exe (PID: 1532)
Reads Internet Cache Settings
- chrome.exe (PID: 3932)
Dropped object may contain Bitcoin addresses
- Auslogics.BoostSpeed.v11.2.0.3.exe (PID: 1532)
Application launched itself
- chrome.exe (PID: 3932)
Reads Microsoft Office registry keys
- taboneclickscanner.exe (PID: 3076)
- taboptimize.exe (PID: 2484)
- tabmaintain.exe (PID: 3856)
Reads settings of System Certificates
- Integrator.exe (PID: 436)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
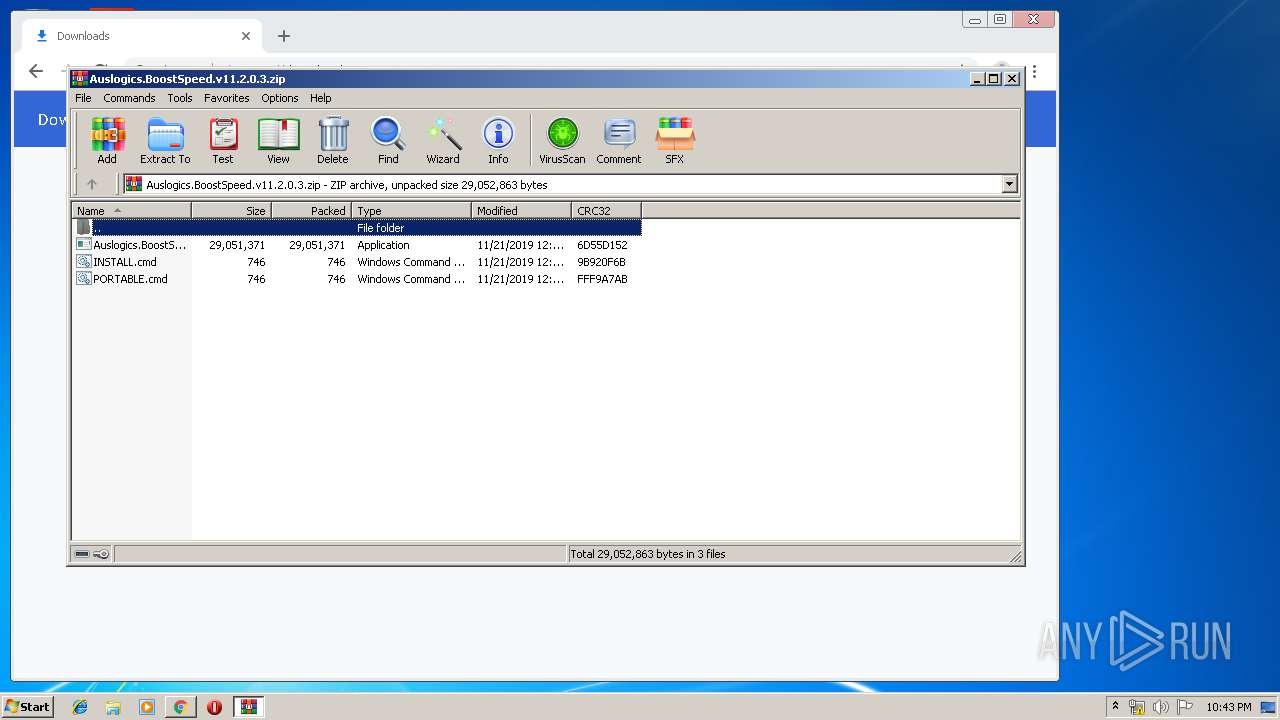
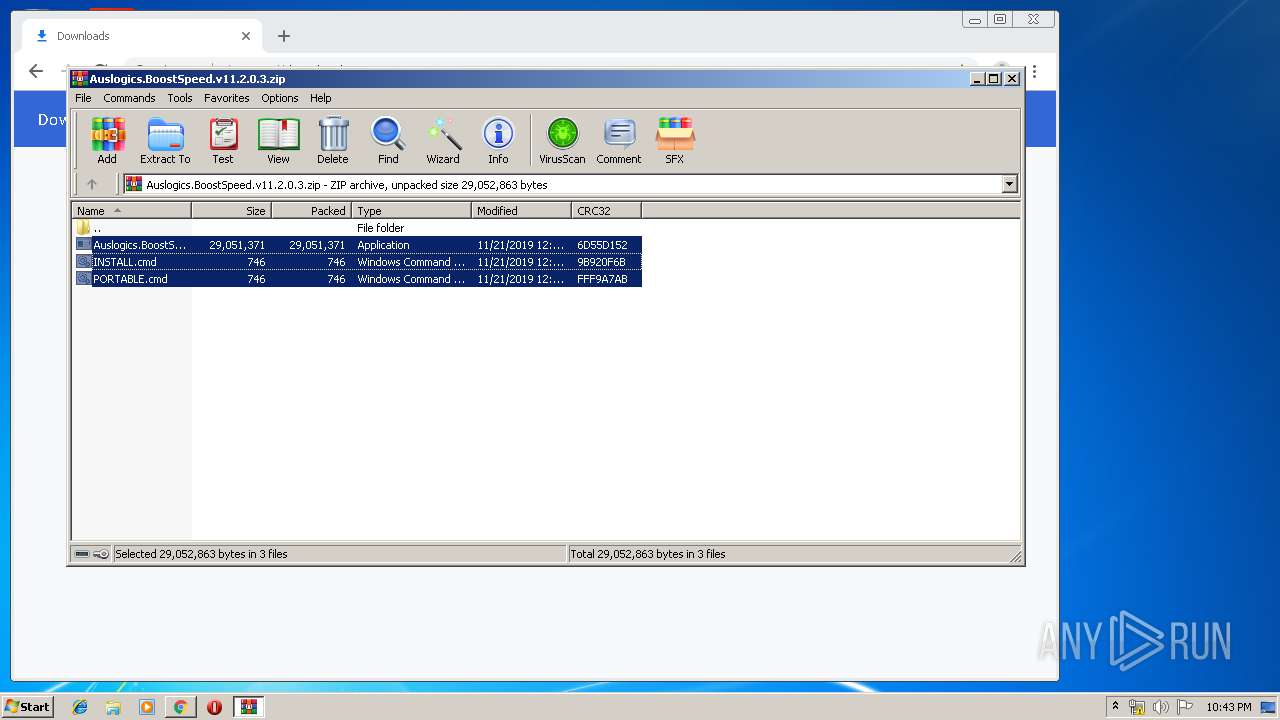
TRiD
| .xpi | | | Mozilla Firefox browser extension (66.6) |
|---|---|---|
| .zip | | | ZIP compressed archive (33.3) |
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2019:11:21 15:19:21 |
| ZipCRC: | 0x6d55d152 |
| ZipCompressedSize: | 29051371 |
| ZipUncompressedSize: | 29051371 |
| ZipFileName: | Auslogics.BoostSpeed.v11.2.0.3.exe |
Total processes
111
Monitored processes
59
Malicious processes
14
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,6257888759196021999,14135989984620507422,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2626912688140284569 --mojo-platform-channel-handle=3948 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 436 | C:\Users\admin\Desktop\AuslogicsBoostSpeedPortable\App\BoostSpeed\Integrator.exe | C:\Users\admin\Desktop\AuslogicsBoostSpeedPortable\App\BoostSpeed\Integrator.exe | AusLogicsBoostSpeed11Portable.exe | ||||||||||||
User: admin Company: Auslogics Integrity Level: HIGH Description: BoostSpeed Exit code: 0 Version: 11.2.0.3 Modules
| |||||||||||||||
| 444 | "C:\Users\admin\AppData\Local\Temp\nskF74.tmp\nsF84.tmp" netsh.exe advfirewall firewall delete rule name="all" remoteip=95.141.193.133 | C:\Users\admin\AppData\Local\Temp\nskF74.tmp\nsF84.tmp | — | Auslogics.BoostSpeed.v11.2.0.3.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,6257888759196021999,14135989984620507422,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15484833072955790595 --mojo-platform-channel-handle=3672 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=960,6257888759196021999,14135989984620507422,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=1279665896131150078 --mojo-platform-channel-handle=4424 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,6257888759196021999,14135989984620507422,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4538661755835593619 --mojo-platform-channel-handle=3820 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1048 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,6257888759196021999,14135989984620507422,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7228255290540667775 --mojo-platform-channel-handle=4072 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,6257888759196021999,14135989984620507422,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1510537234933610683 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2480 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1248 | netsh.exe advfirewall firewall delete rule name="all" remoteip=95.141.193.133 | C:\Windows\system32\netsh.exe | — | nsF84.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1328 | "C:\Users\admin\Desktop\Auslogics.BoostSpeed.v11.2.0.3.exe" /S /P | C:\Users\admin\Desktop\Auslogics.BoostSpeed.v11.2.0.3.exe | — | cmd.exe | |||||||||||
User: admin Company: Auslogics Software Pty Ltd. Integrity Level: MEDIUM Description: Auslogics BoostSpeed v11.2.0.3 Exit code: 3221226540 Version: 11.2.0.3 Modules
| |||||||||||||||
Total events
15 930
Read events
15 368
Write events
524
Delete events
38
Modification events
| (PID) Process: | (3568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3932-13219800123363250 |
Value: 259 | |||
| (PID) Process: | (3932) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3932) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3932) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3932) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3932) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3932) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3932) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3932) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3932) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
108
Suspicious files
44
Text files
275
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\17bd1ddb-9007-4c70-ada3-d62cd3eee546.tmp | — | |
MD5:— | SHA256:— | |||
| 3932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF3933fb.TMP | text | |
MD5:— | SHA256:— | |||
| 3932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF393449.TMP | text | |
MD5:— | SHA256:— | |||
| 3932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
49
DNS requests
31
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
436 | Integrator.exe | HEAD | 200 | 45.33.8.241:80 | http://ads.auslogics.com/uploads/50af3d5413855c55b7843c2659c42f65.png | US | — | — | whitelisted |
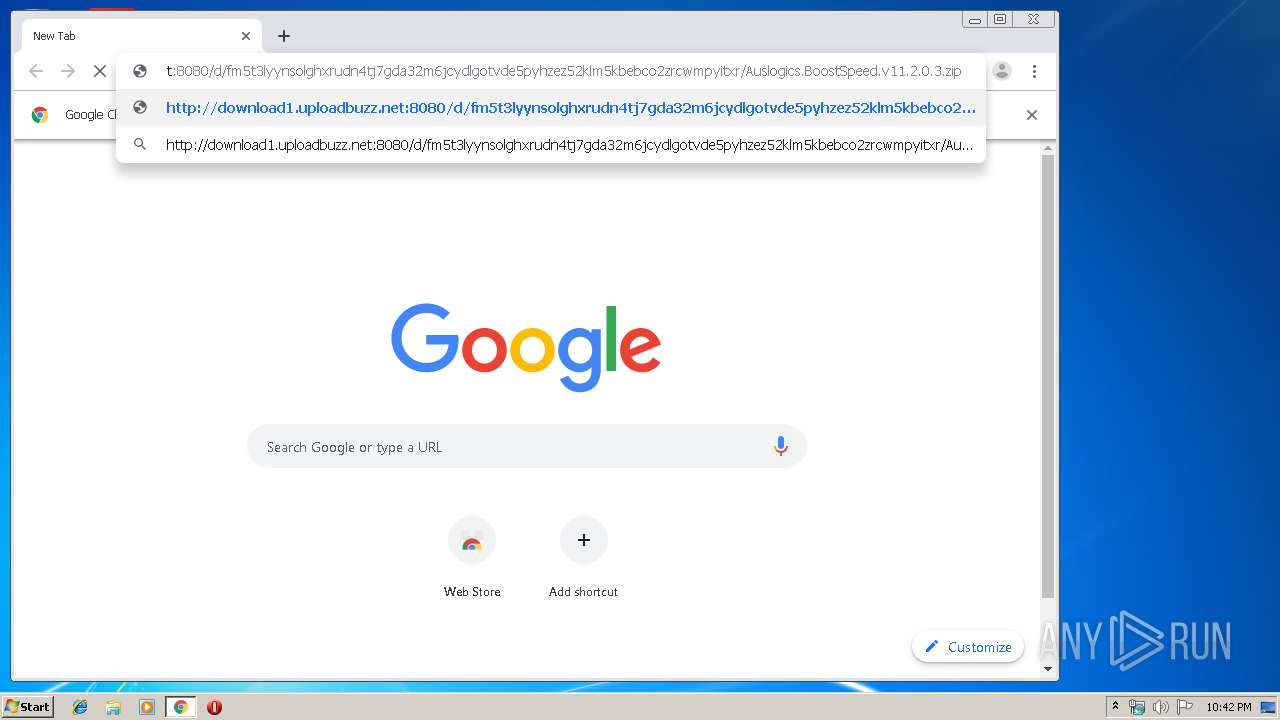
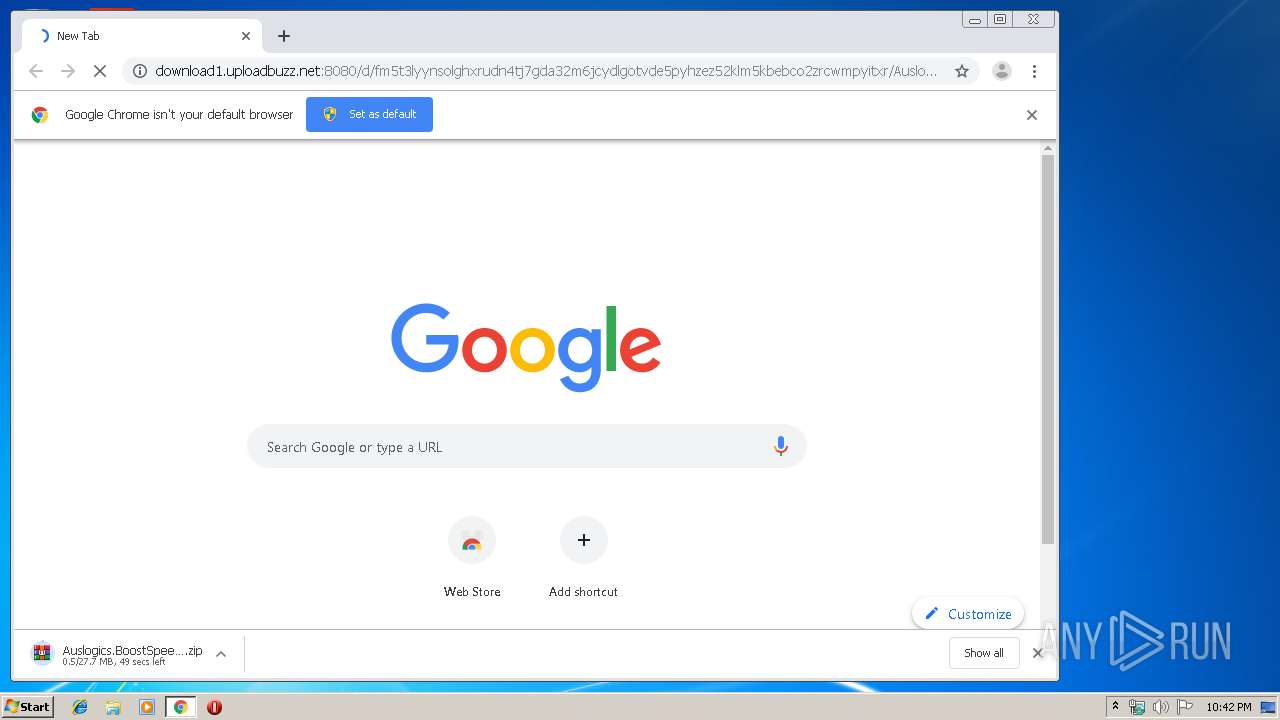
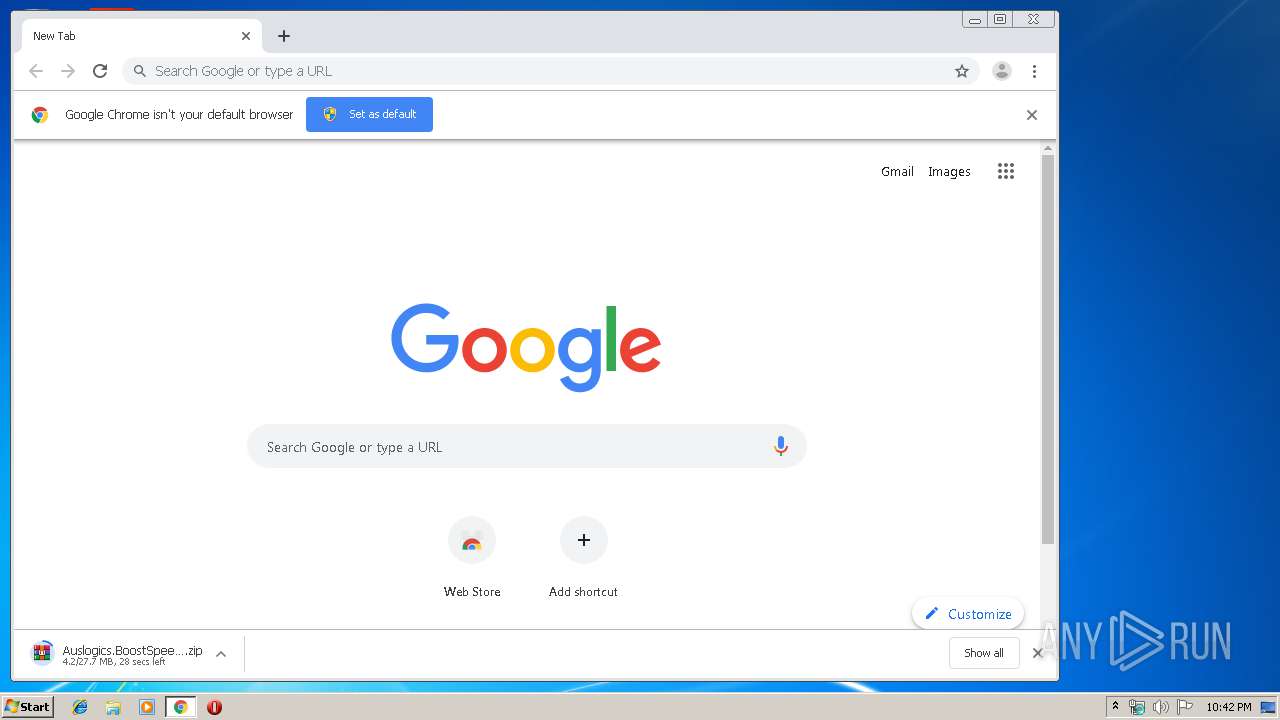
2444 | chrome.exe | GET | — | 5.79.69.194:8080 | http://download1.uploadbuzz.net:8080/d/fm5t3lyynsolghxrudn4tj7gda32m6jcydlgotvde5pyhzez52klm5kbebco2zrcwmpyitxr/Auslogics.BoostSpeed.v11.2.0.3.zip | NL | — | — | unknown |
2444 | chrome.exe | GET | 200 | 159.148.69.143:80 | http://r4---sn-a5uoxu-gpme.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=159.148.186.246&mm=28&mn=sn-a5uoxu-gpme&ms=nvh&mt=1575325999&mv=u&mvi=3&pcm2cms=yes&pl=24&shardbypass=yes | LV | crx | 293 Kb | whitelisted |
2444 | chrome.exe | GET | 302 | 172.217.23.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 522 b | whitelisted |
2444 | chrome.exe | GET | 302 | 172.217.23.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 533 b | whitelisted |
2444 | chrome.exe | GET | 200 | 5.79.69.194:8080 | http://download1.uploadbuzz.net:8080/d/fm5t3lyynsolghxrudn4tj7gda32m6jcydlgotvde5pyhzez52klm5kbebco2zrcwmpyitxr/Auslogics.BoostSpeed.v11.2.0.3.zip | NL | compressed | 27.7 Mb | unknown |
2444 | chrome.exe | GET | 200 | 159.148.69.142:80 | http://r3---sn-a5uoxu-gpme.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=159.148.186.246&mm=28&mn=sn-a5uoxu-gpme&ms=nvh&mt=1575325999&mv=u&mvi=2&pl=24&shardbypass=yes | LV | crx | 862 Kb | whitelisted |
— | — | GET | 200 | 143.204.208.79:80 | http://ocsp.sca1b.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQz9arGHWbnBV0DFzpNHz4YcTiFDQQUWaRmBlKge5WSPKOUByeWdFv5PdACEA4vBMJJxPg6SKCVbxEbKkA%3D | US | der | 471 b | whitelisted |
— | — | GET | 200 | 13.35.254.176:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
— | — | GET | 200 | 13.35.254.52:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2444 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2444 | chrome.exe | 172.217.18.3:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2444 | chrome.exe | 5.79.69.194:8080 | download1.uploadbuzz.net | LeaseWeb Netherlands B.V. | NL | unknown |
2444 | chrome.exe | 172.217.22.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2444 | chrome.exe | 172.217.16.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2444 | chrome.exe | 216.58.210.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
2444 | chrome.exe | 172.217.16.164:443 | www.google.com | Google Inc. | US | whitelisted |
2444 | chrome.exe | 172.217.22.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
2444 | chrome.exe | 172.217.18.14:443 | apis.google.com | Google Inc. | US | whitelisted |
2444 | chrome.exe | 172.217.22.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
download1.uploadbuzz.net |
| unknown |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
Threats
5 ETPRO signatures available at the full report