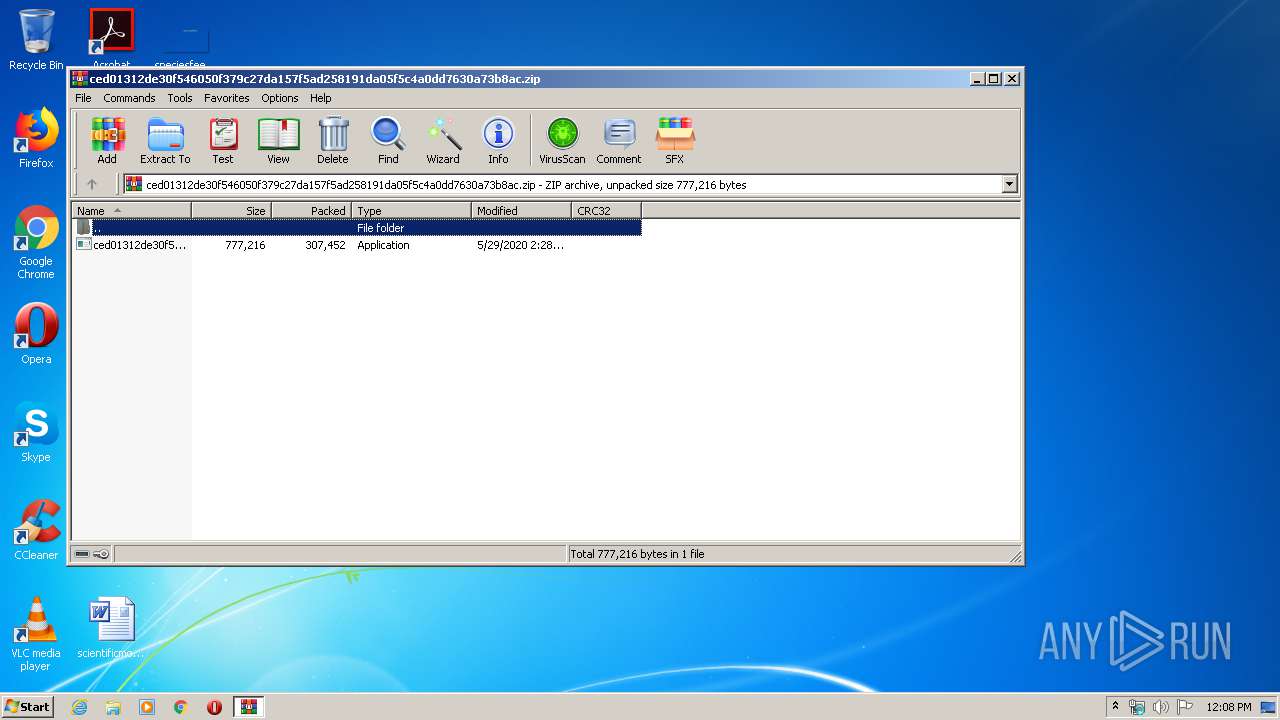
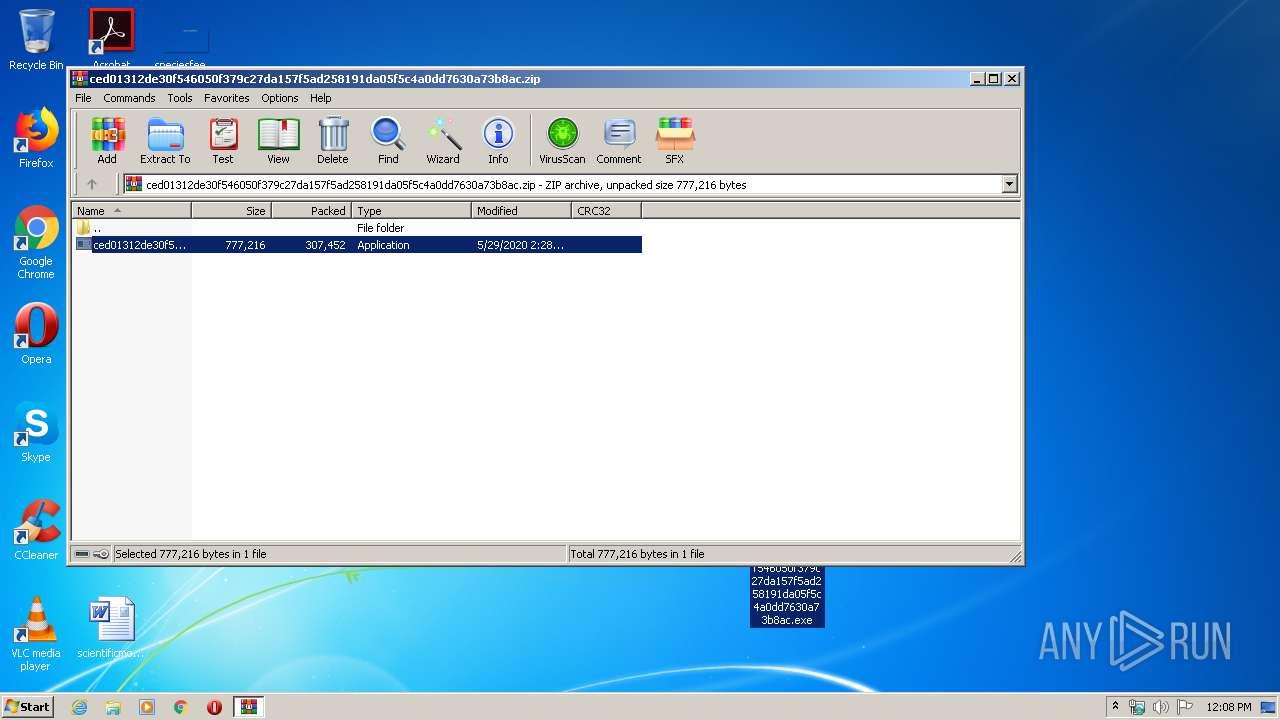
| File name: | ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.zip |
| Full analysis: | https://app.any.run/tasks/06518365-95d4-4fb3-a6c3-28e7e062b7e1 |
| Verdict: | Malicious activity |
| Analysis date: | May 30, 2020, 11:08:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 243D812B1881BFC4BCD50CDA01AC9053 |
| SHA1: | 35E4F84C1F4BC6D08DE4BEDC481DEB3C5BCD201C |
| SHA256: | 940015D5F3EF686053C70B1162E2A86ACD0BD9F4C42169E1B4E9E5769286611A |
| SSDEEP: | 6144:qudrzMkkUjQSvxm9n2UF+fY8+TK+hUgs2w9HFe8zuE0Xee9IAdKyP05GSmY8:quZwBSvAUUUfYRTKpNlh6E0XRjPsGNP |
MALICIOUS
Application was dropped or rewritten from another process
- ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe (PID: 2216)
- ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe (PID: 768)
- ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe (PID: 1524)
- ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe (PID: 2924)
- ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe (PID: 2296)
- ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe (PID: 3832)
- ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe (PID: 3016)
- ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe (PID: 3000)
- ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe (PID: 4084)
- ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe (PID: 2464)
- ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe (PID: 3036)
- ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe (PID: 2192)
- ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe (PID: 1516)
- ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe (PID: 2600)
- ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe (PID: 1356)
- InstallUtil.exe (PID: 2204)
- ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe (PID: 3632)
- InstallUtil.exe (PID: 1820)
- notepad_guide.exe (PID: 2116)
Writes to a start menu file
- ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe (PID: 2216)
Changes the autorun value in the registry
- InstallUtil.exe (PID: 2204)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2460)
- ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe (PID: 2216)
- InstallUtil.exe (PID: 2204)
Starts CMD.EXE for commands execution
- ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe (PID: 2216)
- ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe (PID: 3632)
- notepad_guide.exe (PID: 2116)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 2144)
- cmd.exe (PID: 2424)
- cmd.exe (PID: 2668)
Creates files in the user directory
- ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe (PID: 2216)
- InstallUtil.exe (PID: 2204)
Starts itself from another location
- ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe (PID: 2216)
INFO
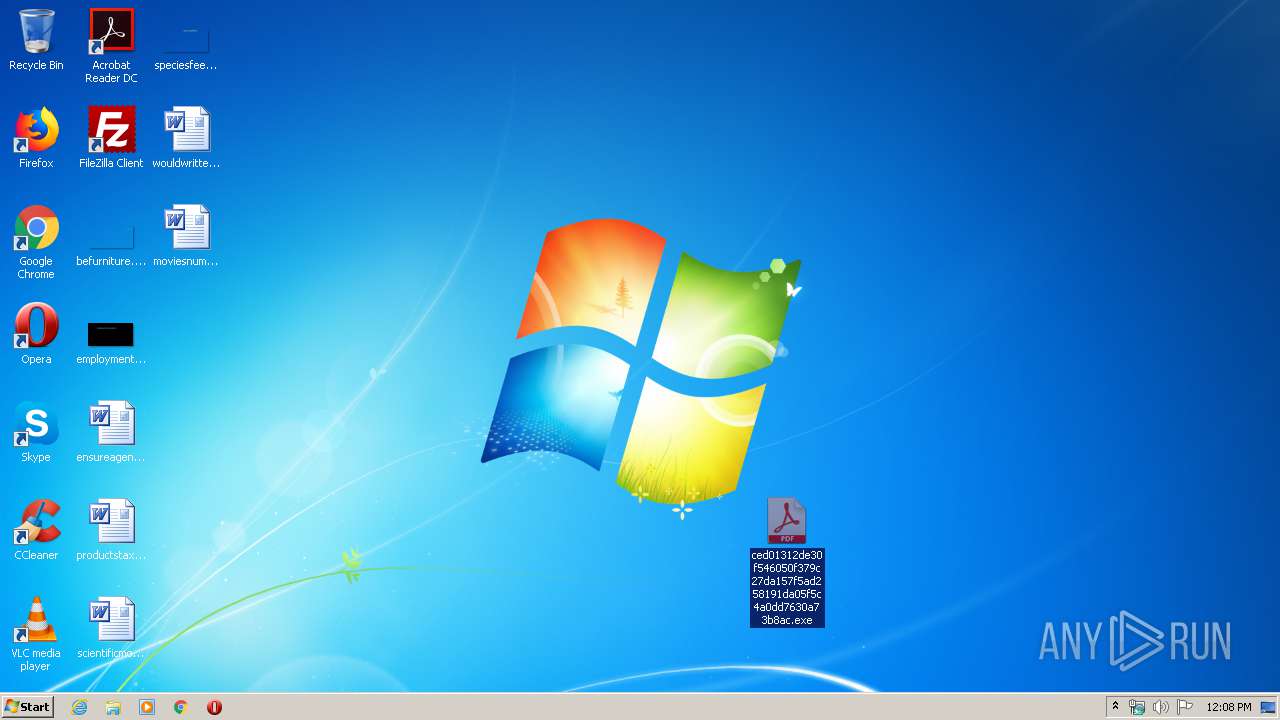
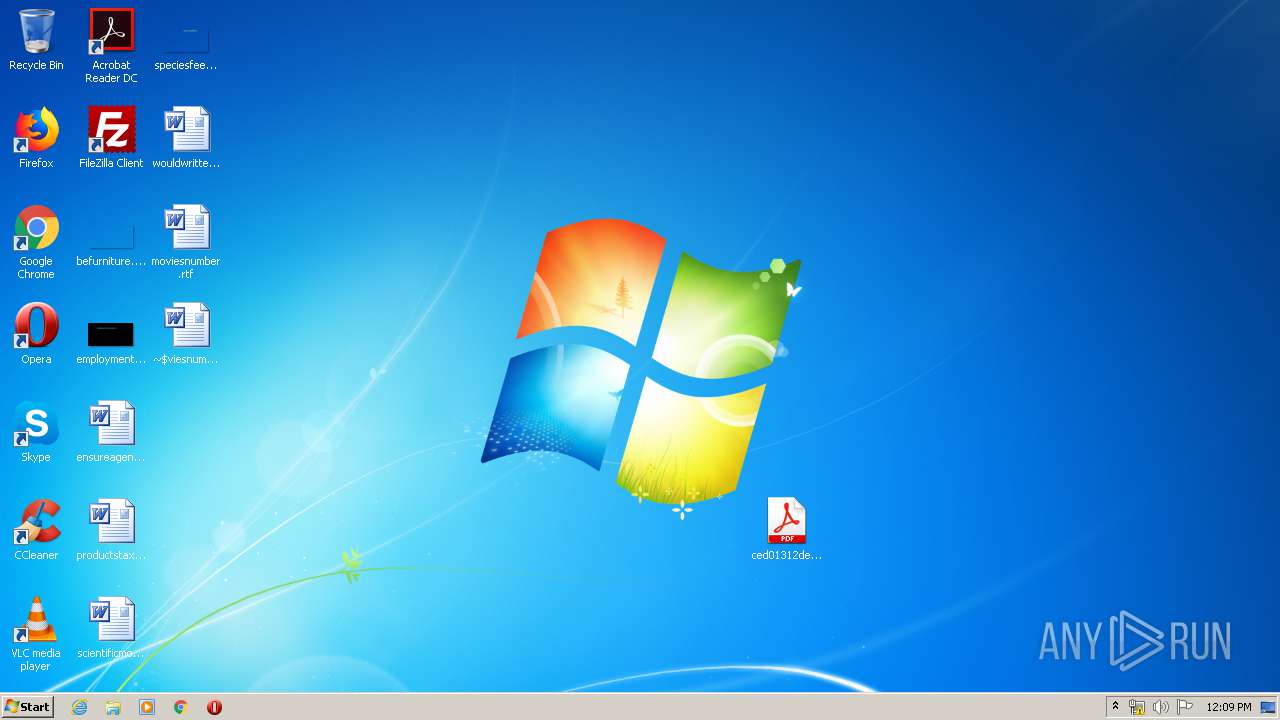
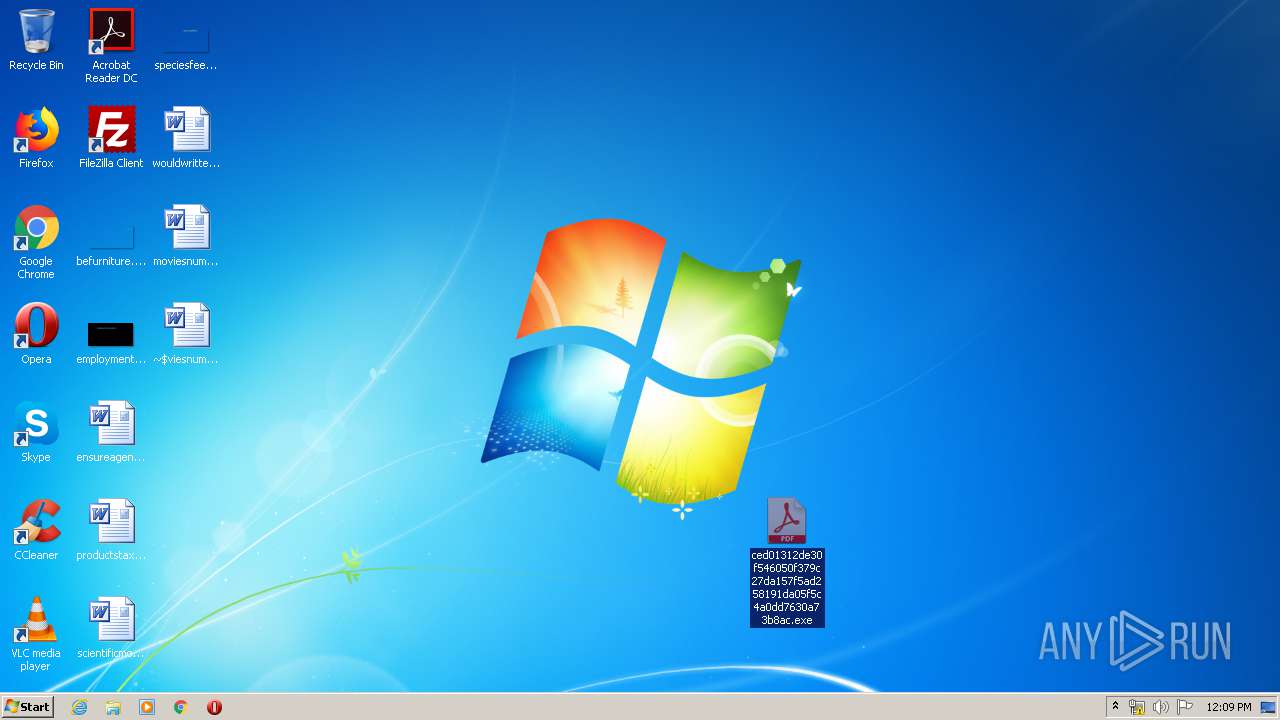
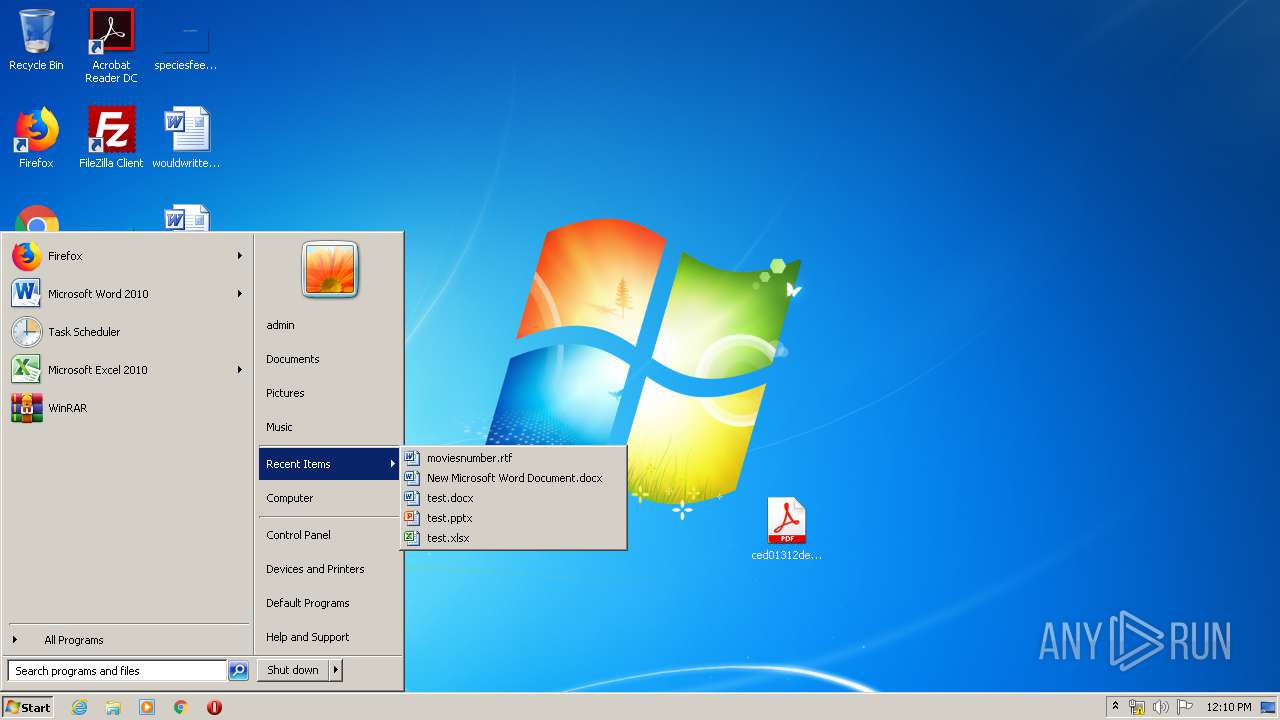
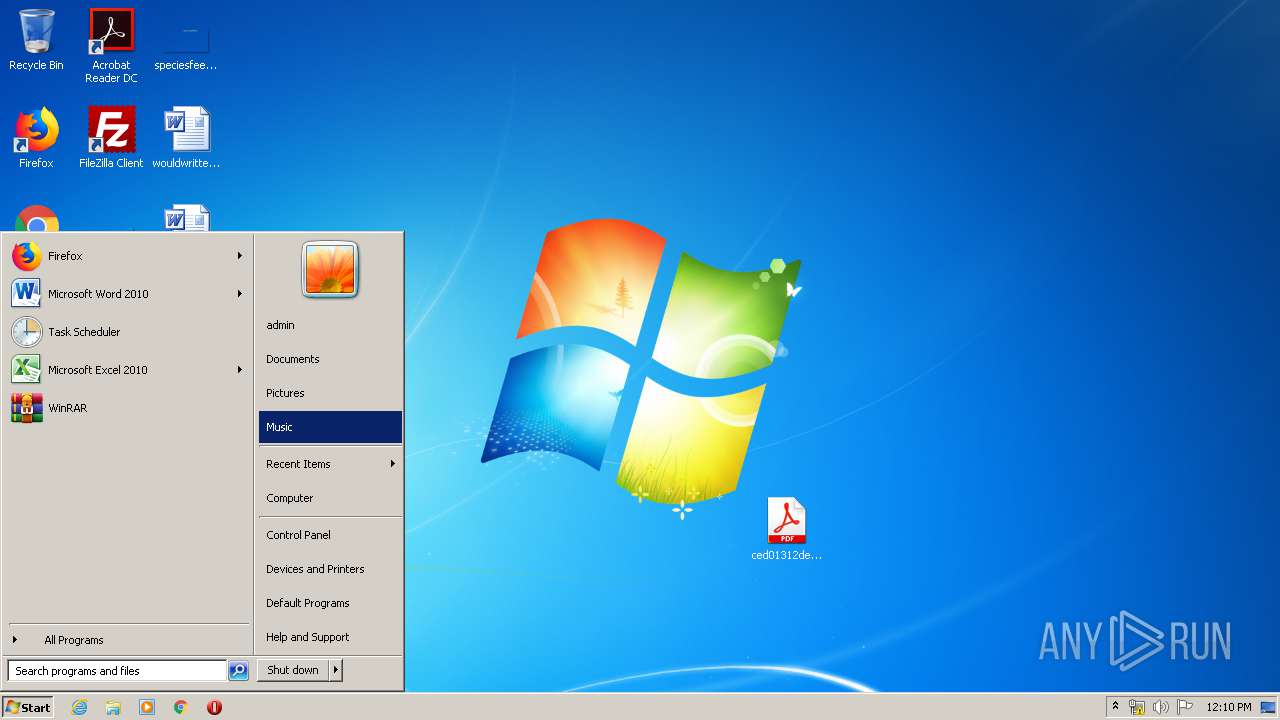
Manual execution by user
- ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe (PID: 2216)
- ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe (PID: 768)
- ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe (PID: 1524)
- ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe (PID: 2924)
- ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe (PID: 2296)
- ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe (PID: 3832)
- ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe (PID: 3016)
- ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe (PID: 3036)
- ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe (PID: 4084)
- ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe (PID: 2192)
- ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe (PID: 1516)
- ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe (PID: 3000)
- ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe (PID: 2600)
- ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe (PID: 1356)
- ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe (PID: 2464)
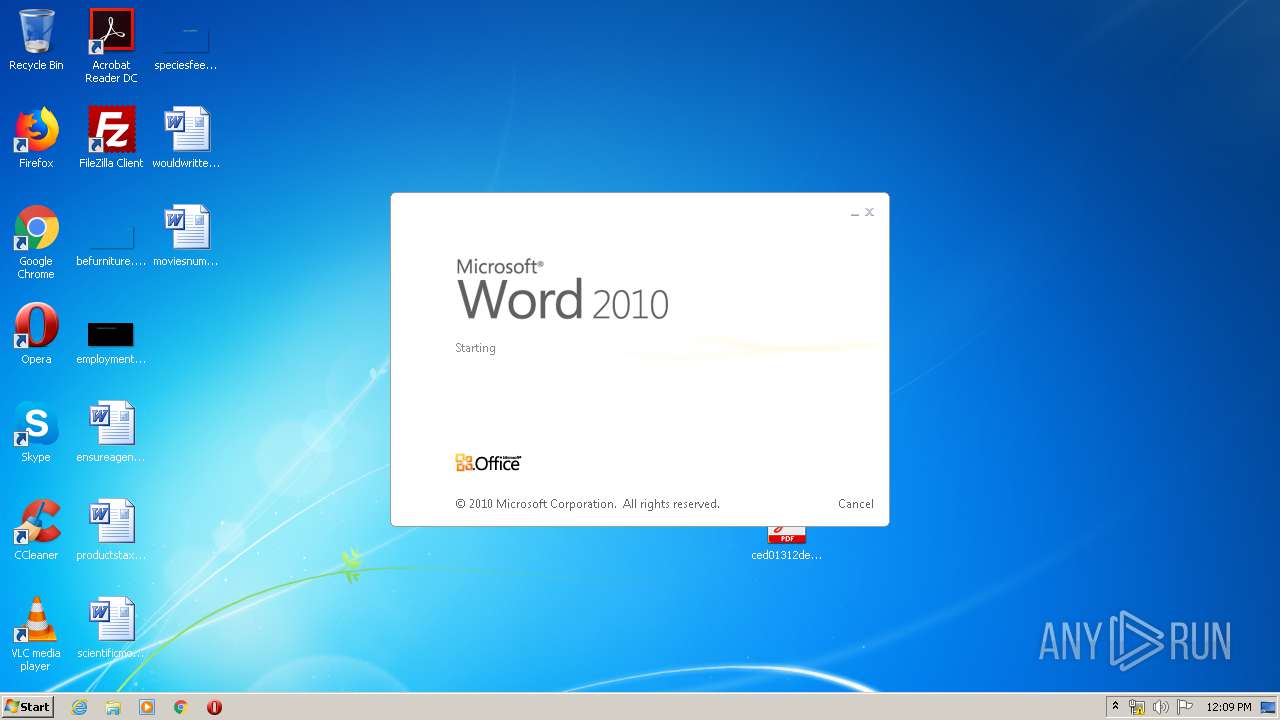
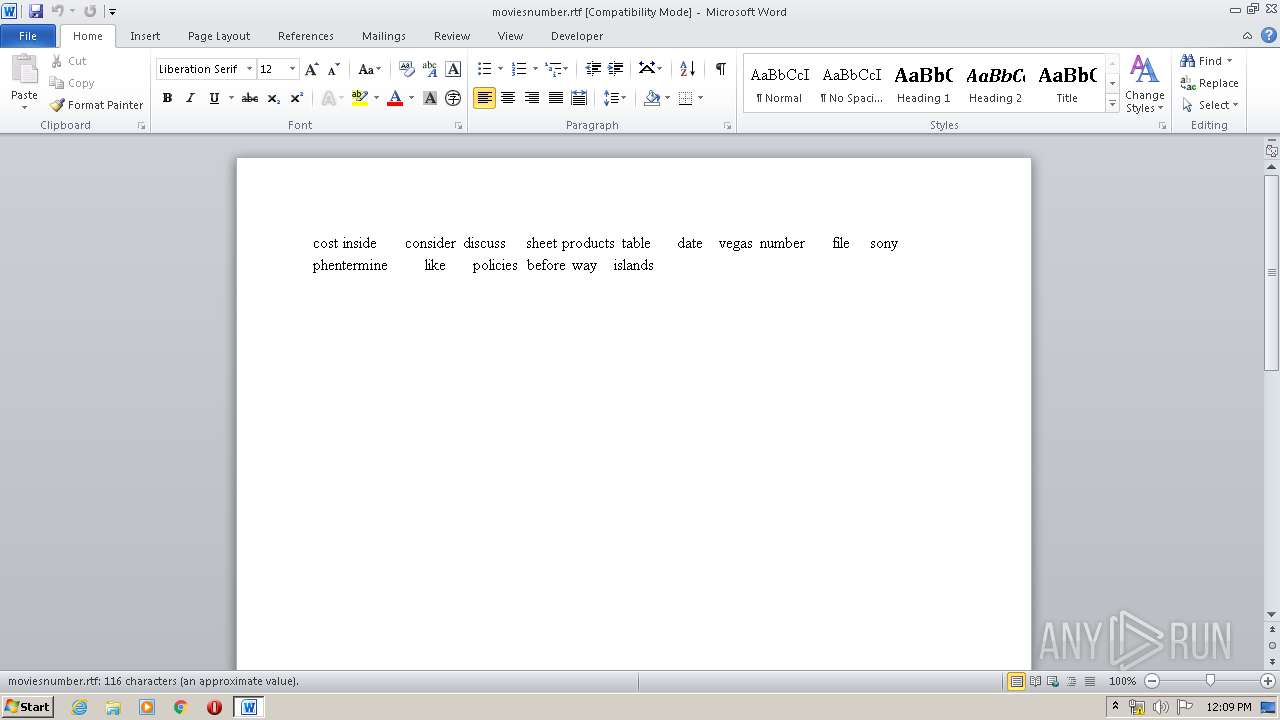
- WINWORD.EXE (PID: 4088)
- ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe (PID: 3632)
Creates files in the user directory
- WINWORD.EXE (PID: 4088)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 4088)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2020:05:29 14:28:28 |
| ZipCRC: | 0x6e90ceb1 |
| ZipCompressedSize: | 307452 |
| ZipUncompressedSize: | 777216 |
| ZipFileName: | ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe |
Total processes
69
Monitored processes
27
Malicious processes
10
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 612 | REG ADD HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run /f /v Notepad guide /t REG_SZ /d C:\Windows\system32\pcalua.exe" -a C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\notepad_guide.exe" | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 768 | "C:\Users\admin\Desktop\ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe" | C:\Users\admin\Desktop\ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe | — | explorer.exe | |||||||||||
User: admin Company: Oracle Notepad guide Integrity Level: MEDIUM Description: Notepad guide Exit code: 0 Version: 8.12.17.21 Modules
| |||||||||||||||
| 1356 | "C:\Users\admin\Desktop\ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe" | C:\Users\admin\Desktop\ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe | — | explorer.exe | |||||||||||
User: admin Company: Oracle Notepad guide Integrity Level: MEDIUM Description: Notepad guide Exit code: 0 Version: 8.12.17.21 Modules
| |||||||||||||||
| 1516 | "C:\Users\admin\Desktop\ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe" | C:\Users\admin\Desktop\ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe | — | explorer.exe | |||||||||||
User: admin Company: Oracle Notepad guide Integrity Level: MEDIUM Description: Notepad guide Exit code: 0 Version: 8.12.17.21 Modules
| |||||||||||||||
| 1524 | "C:\Users\admin\Desktop\ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe" | C:\Users\admin\Desktop\ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe | — | explorer.exe | |||||||||||
User: admin Company: Oracle Notepad guide Integrity Level: MEDIUM Description: Notepad guide Exit code: 0 Version: 8.12.17.21 Modules
| |||||||||||||||
| 1820 | "C:\Users\admin\AppData\Local\Temp\InstallUtil.exe" | C:\Users\admin\AppData\Local\Temp\InstallUtil.exe | — | ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: .NET Framework installation utility Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 2116 | "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\notepad_guide.exe" | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\notepad_guide.exe | — | ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe | |||||||||||
User: admin Company: Oracle Notepad guide Integrity Level: MEDIUM Description: Notepad guide Exit code: 0 Version: 8.12.17.21 Modules
| |||||||||||||||
| 2144 | "cmd.exe" /c REG ADD HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run /f /v Notepad guide /t REG_SZ /d C:\Windows\system32\pcalua.exe" -a C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\notepad_guide.exe" | C:\Windows\system32\cmd.exe | — | ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2192 | "C:\Users\admin\Desktop\ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe" | C:\Users\admin\Desktop\ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe | — | explorer.exe | |||||||||||
User: admin Company: Oracle Notepad guide Integrity Level: MEDIUM Description: Notepad guide Exit code: 0 Version: 8.12.17.21 Modules
| |||||||||||||||
| 2204 | "C:\Users\admin\AppData\Local\Temp\InstallUtil.exe" | C:\Users\admin\AppData\Local\Temp\InstallUtil.exe | notepad_guide.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: .NET Framework installation utility Exit code: 4294967295 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
Total events
1 935
Read events
1 594
Write events
194
Delete events
147
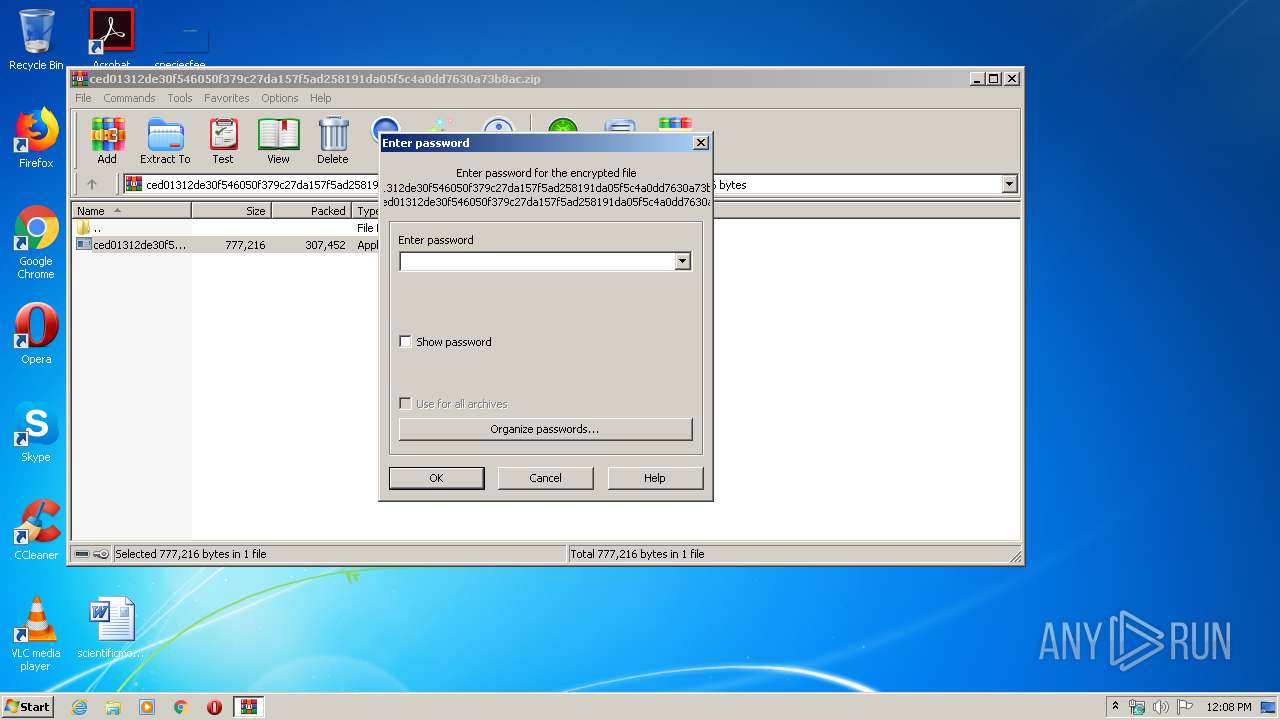
Modification events
| (PID) Process: | (2460) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2460) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2460) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2460) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (2460) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.zip | |||
| (PID) Process: | (2460) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2460) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2460) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2460) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2460) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
4
Suspicious files
0
Text files
2
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4088 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRABD5.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 4088 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{082E8A4B-D317-4140-894E-ED8AE61DE9B7}.tmp | — | |
MD5:— | SHA256:— | |||
| 4088 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{436BB445-AFA3-45D7-BBEF-654A04F09C42}.tmp | — | |
MD5:— | SHA256:— | |||
| 4088 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{D6656A34-183C-4AF6-B66B-A7EBB0478BE1}.tmp | — | |
MD5:— | SHA256:— | |||
| 4088 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\moviesnumber.rtf.LNK | lnk | |
MD5:— | SHA256:— | |||
| 2216 | ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\notepad_guide.exe | executable | |
MD5:— | SHA256:— | |||
| 2460 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2460.25708\ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe | executable | |
MD5:— | SHA256:— | |||
| 4088 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2216 | ced01312de30f546050f379c27da157f5ad258191da05f5c4a0dd7630a73b8ac.exe | C:\Users\admin\AppData\Local\Temp\InstallUtil.exe | executable | |
MD5:91C9AE9C9A17A9DB5E08B120E668C74C | SHA256:E56A7E5D3AB9675555E2897FC3FAA2DD9265008A4967A7D54030AB8184D2D38F | |||
| 4088 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report