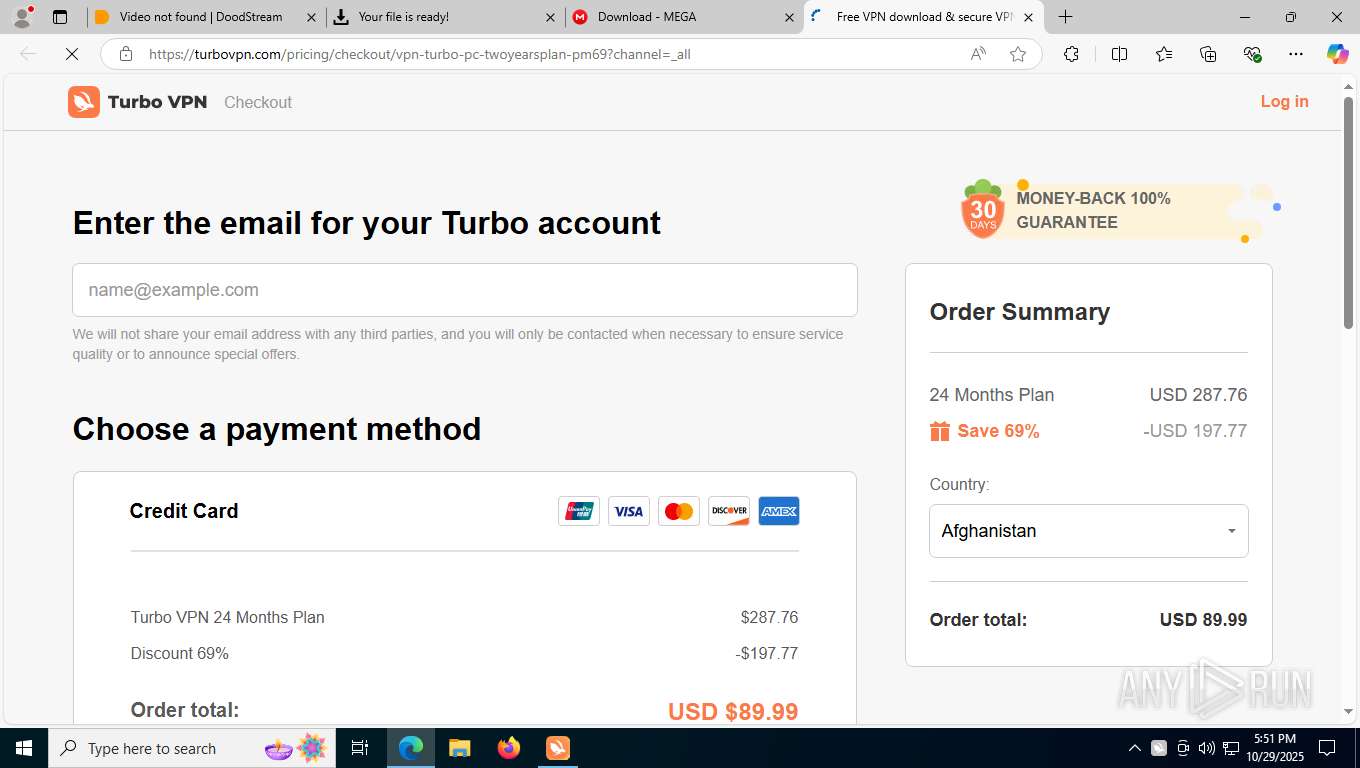
| URL: | https://dsvplay.com/e/ |
| Full analysis: | https://app.any.run/tasks/3af2613f-0626-4ef8-880c-8685bf4918b9 |
| Verdict: | Malicious activity |
| Analysis date: | October 29, 2025, 17:49:23 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | FCF1AE21194CC8037AABA7EBD26CA9E5 |
| SHA1: | 13E32FA02D8298A7044F6ECBCDAA2A7DD8324F8E |
| SHA256: | 93F1C3DA31090242904768FEAC793F9BF6A9422C3CC42300E420012333C498C1 |
| SSDEEP: | 3:N8OZKcLGK3v:2OZKcLd/ |
MALICIOUS
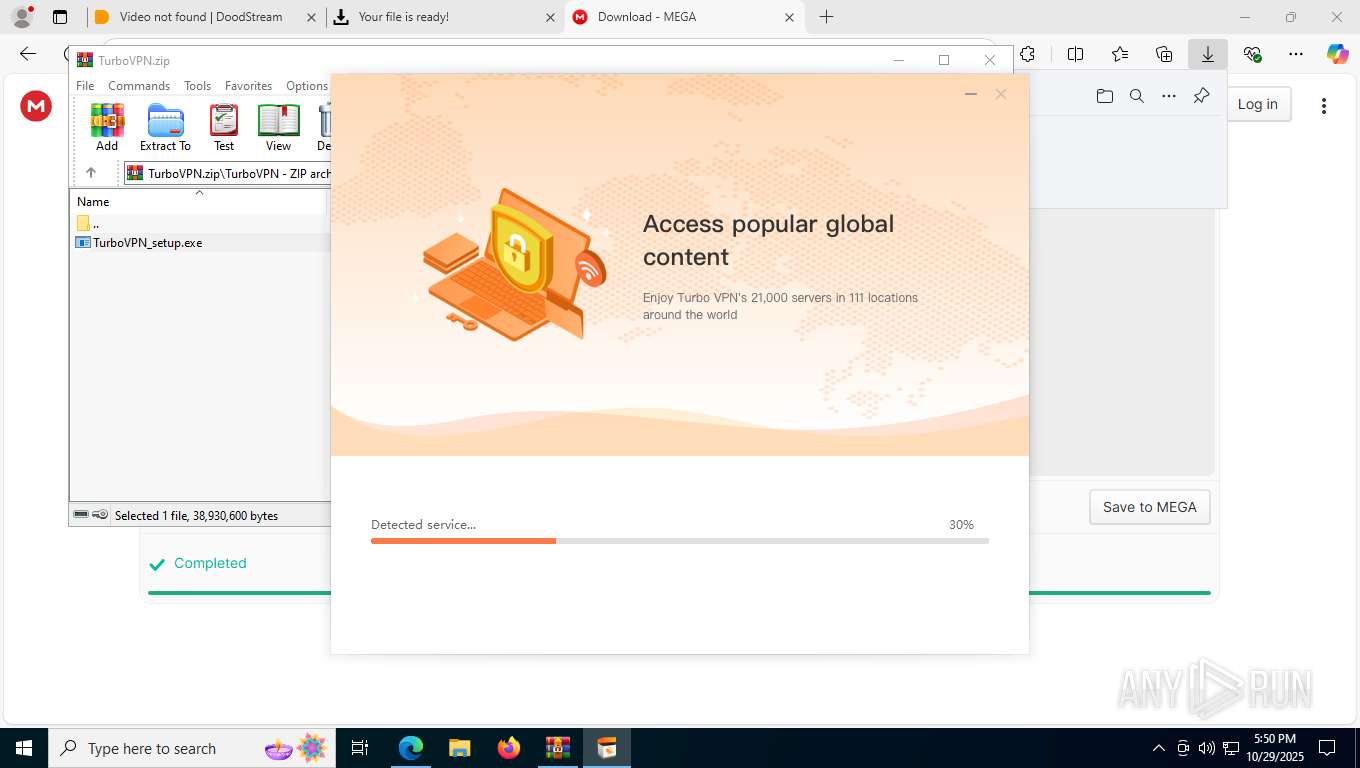
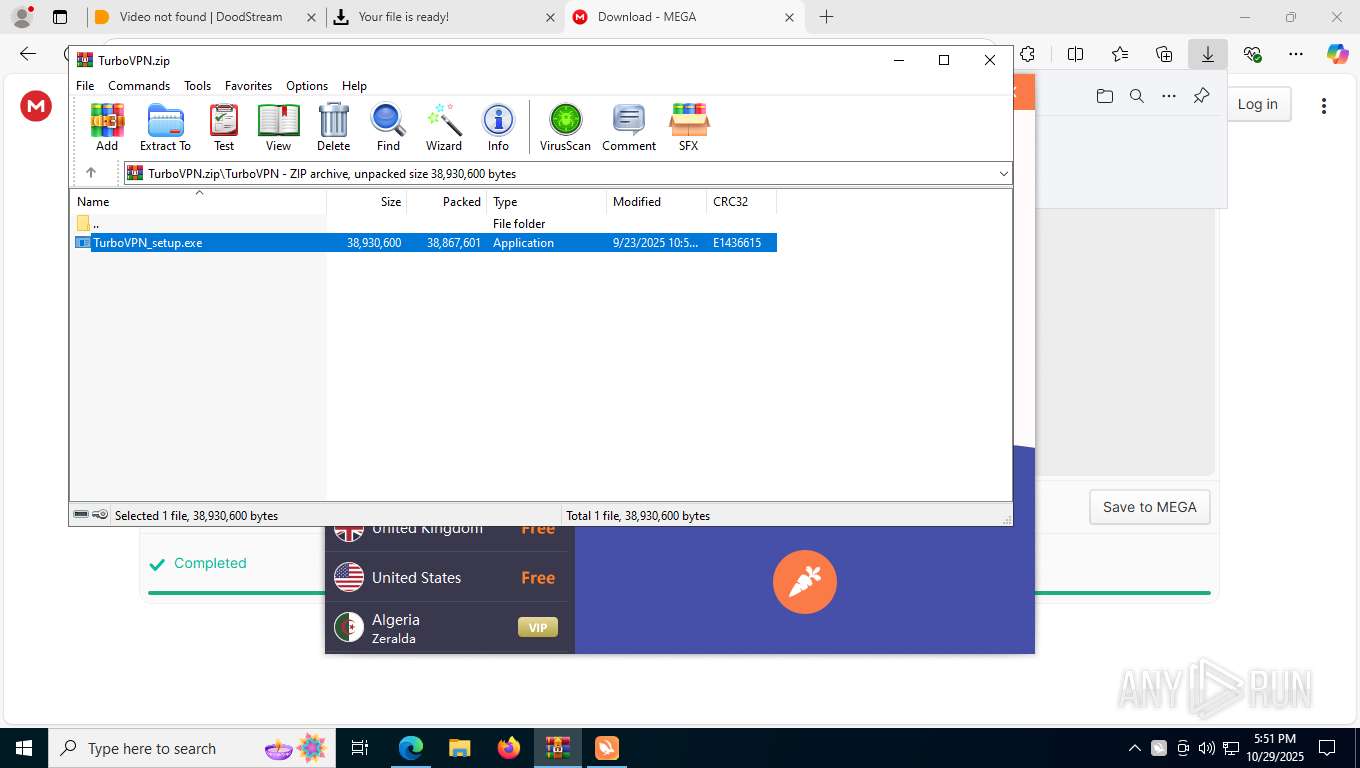
Executing a file with an untrusted certificate
- TurboVPN_setup.exe (PID: 2288)
- TurboVPN_setup.exe (PID: 8840)
PHISHING has been detected (SURICATA)
- msedge.exe (PID: 7840)
Changes the autorun value in the registry
- TurboVPN_setup.exe (PID: 8840)
Changes settings of System certificates
- TurboVPN.exe (PID: 4684)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 5256)
- installtapx64.exe (PID: 4916)
- TurboVPN.exe (PID: 4684)
Malware-specific behavior (creating "System.dll" in Temp)
- TurboVPN_setup.exe (PID: 8840)
Checks for external IP
- svchost.exe (PID: 2276)
Executable content was dropped or overwritten
- TurboVPN_setup.exe (PID: 8840)
- installtapx64.exe (PID: 4916)
- installtapx64.exe (PID: 7920)
The process creates files with name similar to system file names
- TurboVPN_setup.exe (PID: 8840)
The process drops C-runtime libraries
- TurboVPN_setup.exe (PID: 8840)
Process drops legitimate windows executable
- TurboVPN_setup.exe (PID: 8840)
Drops a system driver (possible attempt to evade defenses)
- TurboVPN_setup.exe (PID: 8840)
- drvinst.exe (PID: 6076)
- drvinst.exe (PID: 4712)
- installtapx64.exe (PID: 4916)
- installtapx64.exe (PID: 7920)
Creates files in the driver directory
- installtapx64.exe (PID: 7920)
Executes as Windows Service
- turbo_vpn-service.exe (PID: 8988)
Non windows owned service launched
- turbo_vpn-service.exe (PID: 8988)
Adds/modifies Windows certificates
- TurboVPN.exe (PID: 4684)
INFO
Application launched itself
- msedge.exe (PID: 7496)
- msedge.exe (PID: 6224)
Connects to unusual port
- msedge.exe (PID: 7840)
Reads Environment values
- identity_helper.exe (PID: 4784)
Checks supported languages
- identity_helper.exe (PID: 4784)
- TurboVPN_setup.exe (PID: 8840)
- installtapx64.exe (PID: 4916)
- drvinst.exe (PID: 4712)
- drvinst.exe (PID: 6076)
- installtapx64.exe (PID: 5812)
- installtapx64.exe (PID: 7920)
- turbo_vpn-service.exe (PID: 9208)
- turbo_vpn-service.exe (PID: 8988)
- TurboVPN.exe (PID: 4684)
- installtapx64.exe (PID: 7300)
- installtapx64.exe (PID: 8656)
Reads the computer name
- identity_helper.exe (PID: 4784)
- TurboVPN_setup.exe (PID: 8840)
- drvinst.exe (PID: 4712)
- drvinst.exe (PID: 6076)
- installtapx64.exe (PID: 5812)
- installtapx64.exe (PID: 4916)
- installtapx64.exe (PID: 7920)
- turbo_vpn-service.exe (PID: 9208)
- turbo_vpn-service.exe (PID: 8988)
- TurboVPN.exe (PID: 4684)
- installtapx64.exe (PID: 8656)
- installtapx64.exe (PID: 7300)
Reads the machine GUID from the registry
- installtapx64.exe (PID: 4916)
- drvinst.exe (PID: 4712)
- TurboVPN.exe (PID: 4684)
Create files in a temporary directory
- TurboVPN_setup.exe (PID: 8840)
- installtapx64.exe (PID: 4916)
The sample compiled with chinese language support
- TurboVPN_setup.exe (PID: 8840)
Creates files in the program directory
- TurboVPN_setup.exe (PID: 8840)
- turbo_vpn-service.exe (PID: 8988)
- TurboVPN.exe (PID: 4684)
The sample compiled with english language support
- TurboVPN_setup.exe (PID: 8840)
- installtapx64.exe (PID: 4916)
- drvinst.exe (PID: 4712)
- drvinst.exe (PID: 6076)
Reads the software policy settings
- installtapx64.exe (PID: 4916)
- drvinst.exe (PID: 4712)
- TurboVPN.exe (PID: 4684)
- slui.exe (PID: 8276)
Launching a file from a Registry key
- TurboVPN_setup.exe (PID: 8840)
Creates a software uninstall entry
- TurboVPN_setup.exe (PID: 8840)
Creates files or folders in the user directory
- TurboVPN_setup.exe (PID: 8840)
- TurboVPN.exe (PID: 4684)
Checks proxy server information
- TurboVPN.exe (PID: 4684)
- slui.exe (PID: 8276)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
224
Monitored processes
80
Malicious processes
4
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 644 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=47 --always-read-main-dll --field-trial-handle=8320,i,16924749562798937906,6509739452321288457,262144 --variations-seed-version --mojo-platform-channel-handle=8520 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 864 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=35 --always-read-main-dll --field-trial-handle=7668,i,16924749562798937906,6509739452321288457,262144 --variations-seed-version --mojo-platform-channel-handle=7656 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1300 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_xpay_wallet.mojom.EdgeXPayWalletService --lang=en-US --service-sandbox-type=utility --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5116,i,16924749562798937906,6509739452321288457,262144 --variations-seed-version --mojo-platform-channel-handle=4576 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2028 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=10 --always-read-main-dll --field-trial-handle=5380,i,16924749562798937906,6509739452321288457,262144 --variations-seed-version --mojo-platform-channel-handle=5388 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2276 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2288 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa5256.37559\TurboVPN\TurboVPN_setup.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa5256.37559\TurboVPN\TurboVPN_setup.exe | — | WinRAR.exe | |||||||||||
User: admin Company: INNOVATIVE CONNECTING PTE. LIMITED Integrity Level: MEDIUM Description: TurboVPN Exit code: 3221226540 Version: 3.2.0.0 Modules
| |||||||||||||||
| 2552 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=59 --always-read-main-dll --field-trial-handle=9364,i,16924749562798937906,6509739452321288457,262144 --variations-seed-version --mojo-platform-channel-handle=9284 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3064 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=5784,i,16924749562798937906,6509739452321288457,262144 --variations-seed-version --mojo-platform-channel-handle=7676 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3144 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=11 --always-read-main-dll --field-trial-handle=5712,i,16924749562798937906,6509739452321288457,262144 --variations-seed-version --mojo-platform-channel-handle=5788 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4280 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=54 --always-read-main-dll --field-trial-handle=6504,i,16924749562798937906,6509739452321288457,262144 --variations-seed-version --mojo-platform-channel-handle=8156 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
19 455
Read events
19 365
Write events
81
Delete events
9
Modification events
| (PID) Process: | (5256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
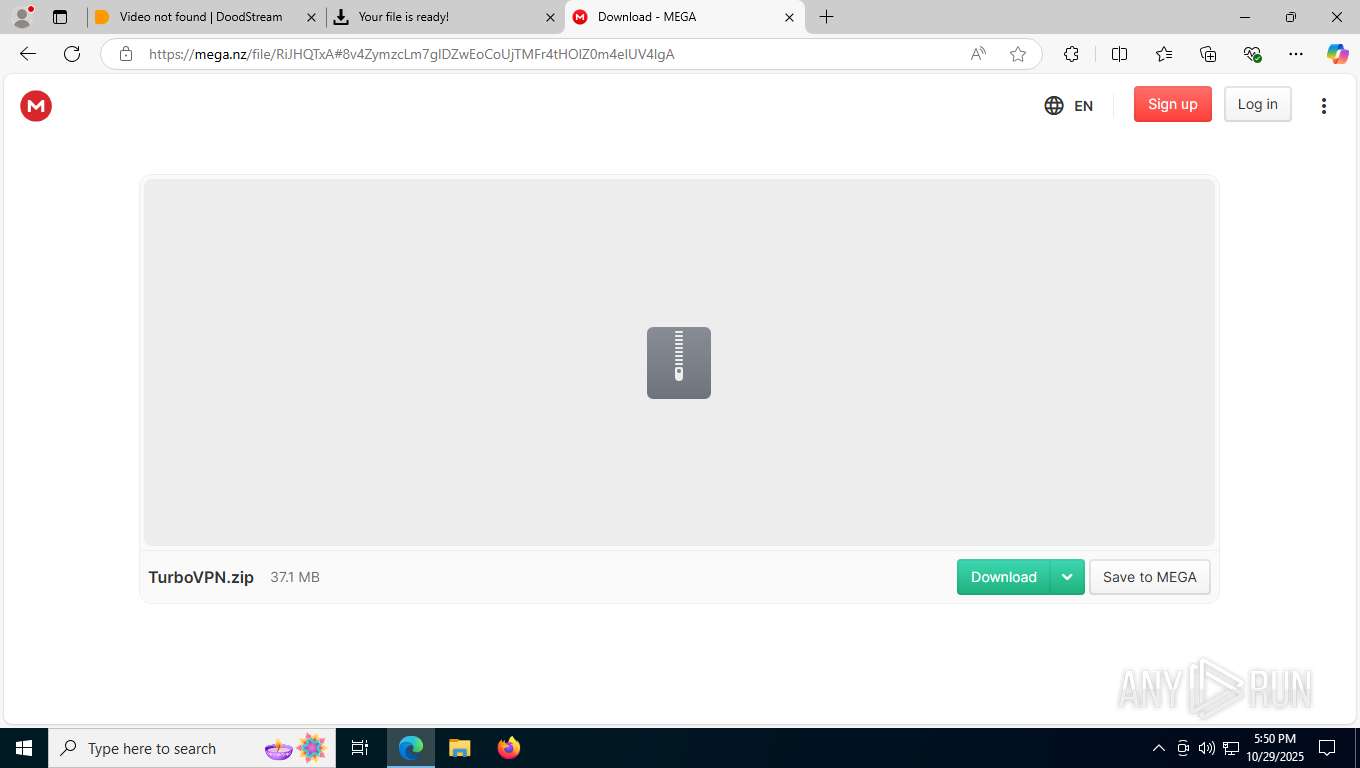
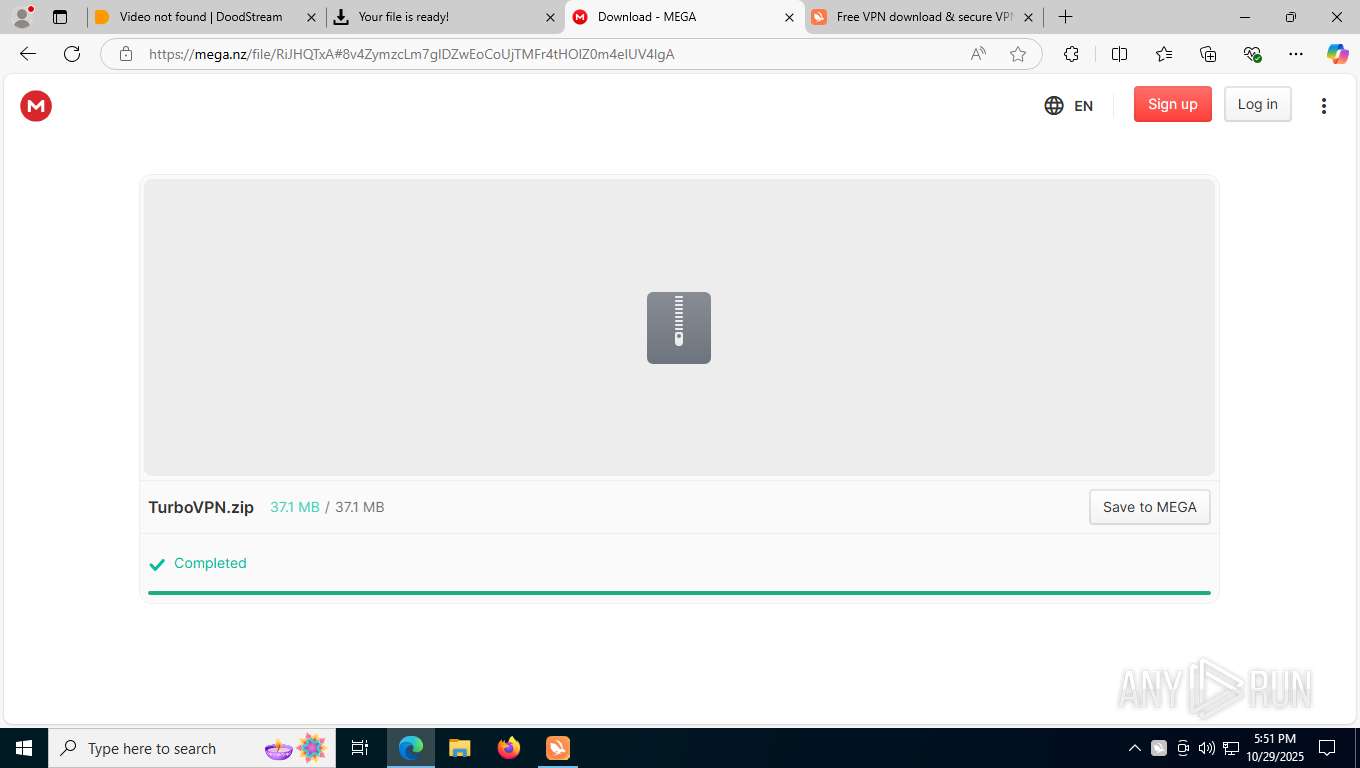
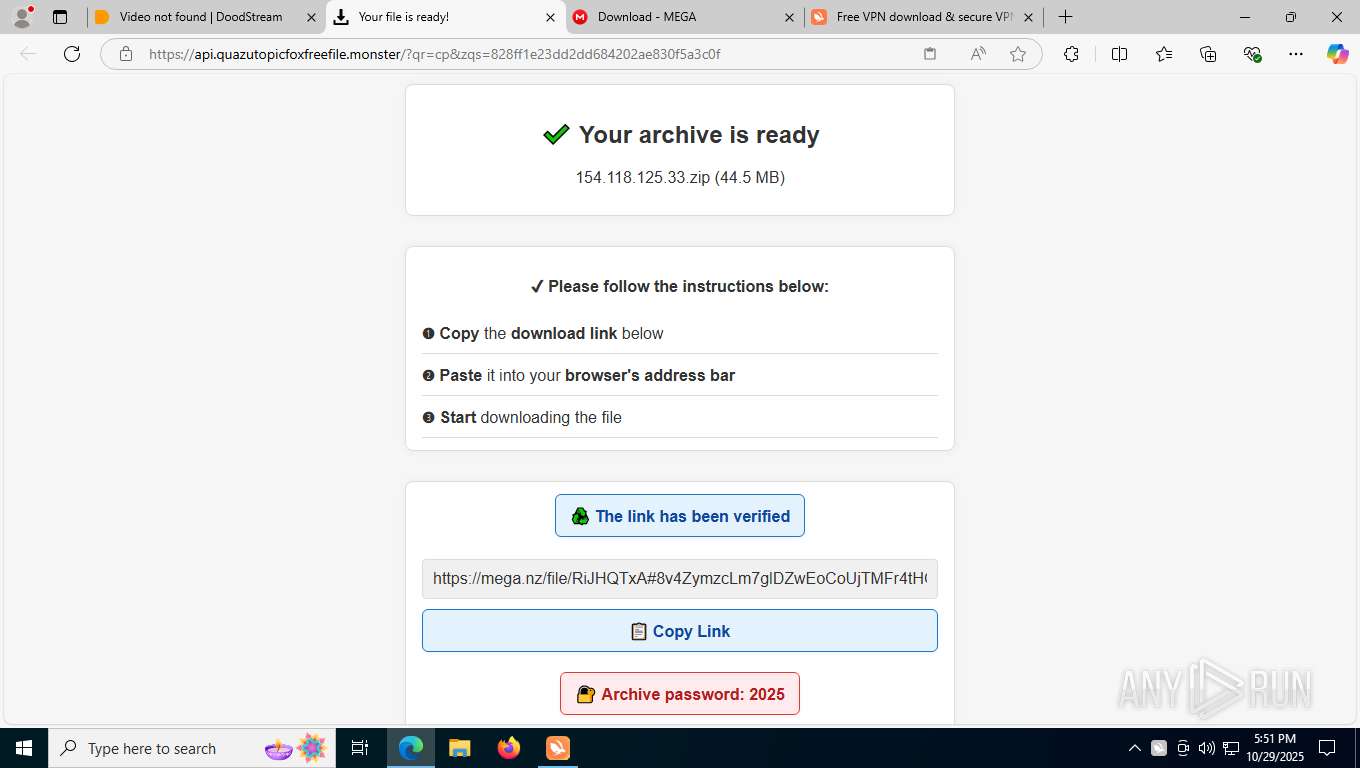
Value: C:\Users\admin\Downloads\TurboVPN.zip | |||
| (PID) Process: | (5256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6076) drvinst.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\tap0901 |
| Operation: | write | Name: | Owners |
Value: oem9.inf | |||
| (PID) Process: | (6076) drvinst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Setup\PnpLockdownFiles\%SystemRoot%/System32/drivers/tap0901.sys |
| Operation: | write | Name: | Owners |
Value: oem9.inf | |||
Executable files
95
Suspicious files
846
Text files
148
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7496 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RFfbaea.TMP | — | |
MD5:— | SHA256:— | |||
| 7496 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7496 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFfbaea.TMP | — | |
MD5:— | SHA256:— | |||
| 7496 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7496 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFfbafa.TMP | — | |
MD5:— | SHA256:— | |||
| 7496 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7496 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFfbafa.TMP | — | |
MD5:— | SHA256:— | |||
| 7496 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RFfbafa.TMP | — | |
MD5:— | SHA256:— | |||
| 7496 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7496 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
415
DNS requests
542
Threats
127
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5472 | svchost.exe | GET | 200 | 23.63.118.230:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
7840 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:IjLN7aFwn7mpbPcm_Z9N9O_2G5DrkcGH0bD1CZo_70c&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 95 b | whitelisted |
4684 | TurboVPN.exe | GET | 200 | 18.66.20.124:80 | http://ocsp.r2m01.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBShdVEFnSEQ0gG5CBtzM48cPMe9XwQUgbgOY4qJEhjl%2Bjs7UJWf5uWQE4UCEAMrS6dWw0aVZuR1TOcEmbM%3D | US | binary | 471 b | whitelisted |
816 | lsass.exe | GET | 200 | 142.250.186.163:80 | http://c.pki.goog/r/gsr1.crl | US | binary | 1.70 Kb | whitelisted |
1264 | svchost.exe | GET | 200 | 95.101.78.42:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
8752 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | DE | binary | 813 b | whitelisted |
8752 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | DE | binary | 814 b | whitelisted |
9020 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/ddbf4492-d475-4fe4-bcde-6cbac56f6034?P1=1762360253&P2=404&P3=2&P4=X3uORpOABL%2fNudWX22vq%2fqPBdyjIDdUvXdq7%2bdudg98LkbmC81Gx%2b1873QmTVIA6cQnDP766jsyybTosJCo4Iw%3d%3d | US | — | — | whitelisted |
8752 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.3.crl | DE | binary | 401 b | whitelisted |
9020 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/ddbf4492-d475-4fe4-bcde-6cbac56f6034?P1=1762360253&P2=404&P3=2&P4=X3uORpOABL%2fNudWX22vq%2fqPBdyjIDdUvXdq7%2bdudg98LkbmC81Gx%2b1873QmTVIA6cQnDP766jsyybTosJCo4Iw%3d%3d | US | binary | 1.09 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5472 | svchost.exe | 40.126.31.3:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1264 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5596 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7840 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7840 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7840 | msedge.exe | 172.67.68.48:443 | dsvplay.com | CLOUDFLARENET | US | unknown |
7840 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7840 | msedge.exe | 92.123.104.45:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
dsvplay.com |
| unknown |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
i.doodcdn.io |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7840 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7840 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7840 | msedge.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
7840 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing Domain (faqirsgoliard .top) |
7840 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing Domain (faqirsgoliard .top) |
7840 | msedge.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Possible Domain Associated with Malware Distribution (ghabovethec .info) |
7840 | msedge.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Possible Domain Associated with Malware Distribution (ukankingwithea .com) |
7840 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7840 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7840 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
Process | Message |
|---|---|
TurboVPN_setup.exe | Window, size, 698,580
|
TurboVPN_setup.exe | Window, shadowimage, bk_shadow.png
|
TurboVPN_setup.exe | Window, shadowsize, 14
|
TurboVPN_setup.exe | Window, sizebox, 0,0,0,0
|
TurboVPN_setup.exe | Window, showshadow, true
|
TurboVPN_setup.exe | Window, shadowcorner, 14,14,14,14
|
TurboVPN_setup.exe | Window, caption, 0,0,0,442
|
TurboVPN_setup.exe | VerticalLayoutUI, width, 698
|
TurboVPN_setup.exe | ButtonUI, font, 10
|
TurboVPN_setup.exe | VerticalLayoutUI, name, HomeBKLogo1
|