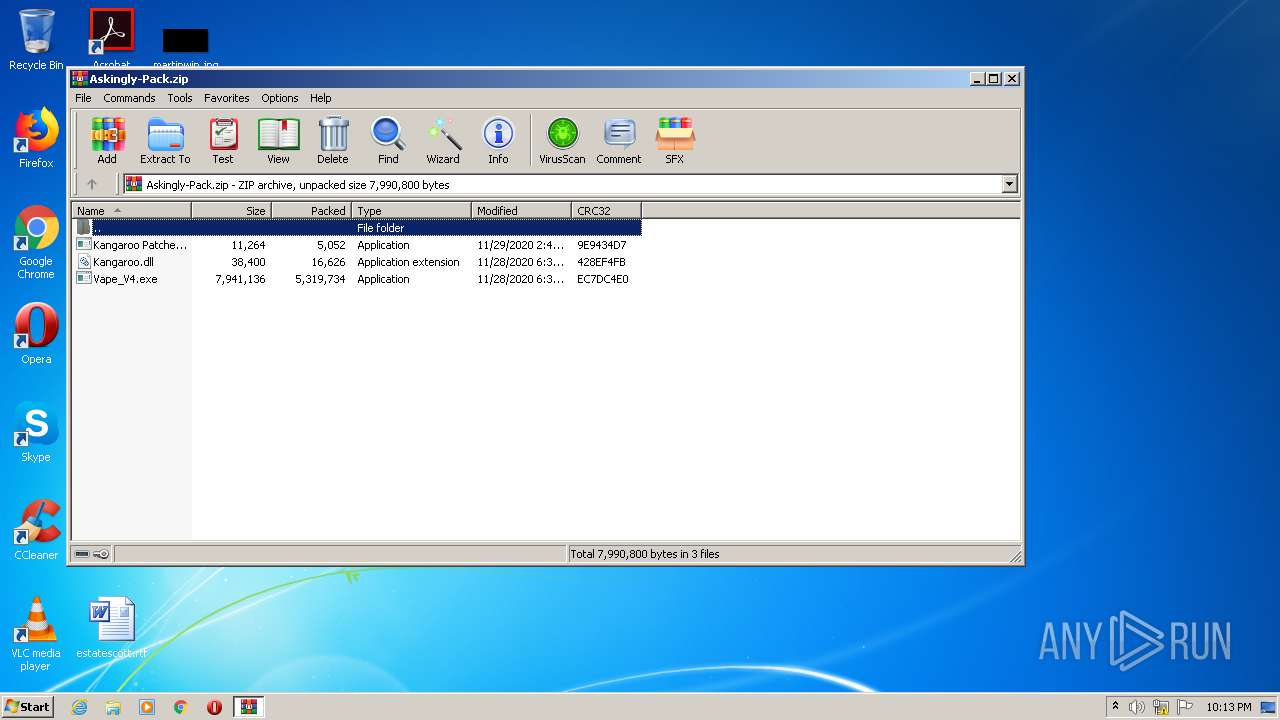
| File name: | Askingly-Pack.zip |
| Full analysis: | https://app.any.run/tasks/5055977c-a7cc-44e9-9f13-3ec9a5a46d61 |
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2020, 22:13:08 |
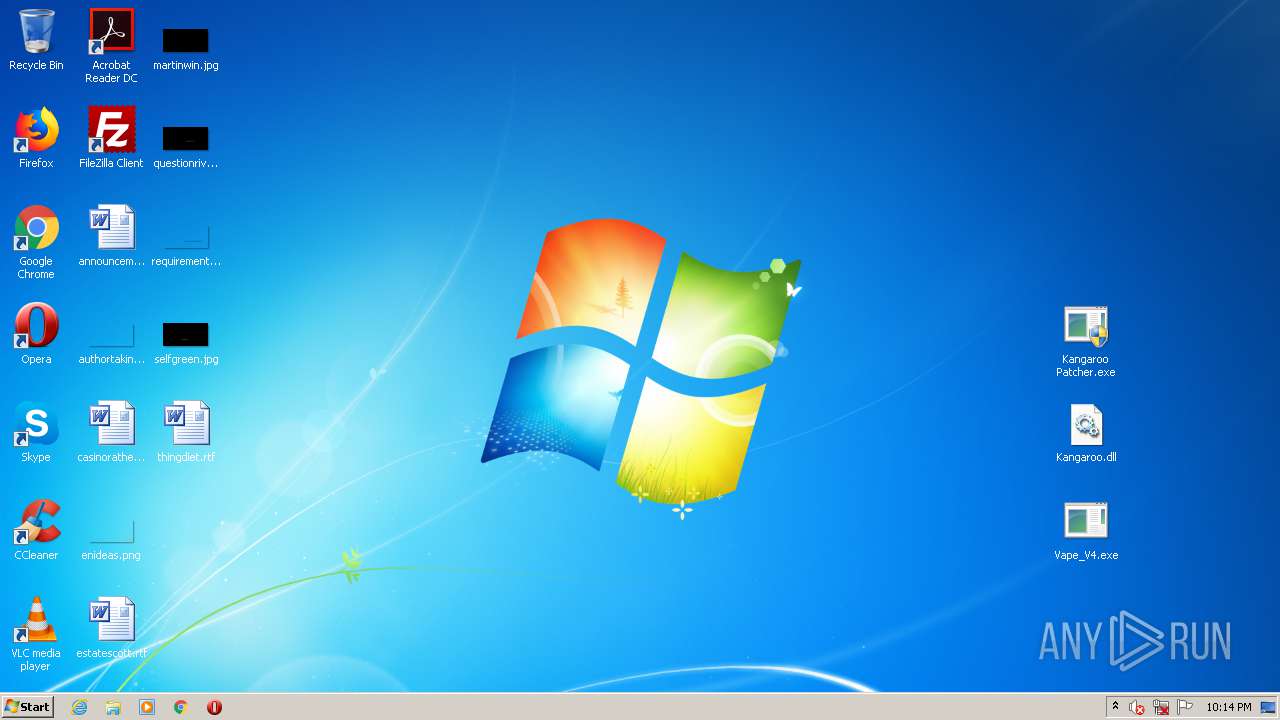
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 4EEAA368343FB8E53D5A2F37CF5CE94B |
| SHA1: | 23E3D154EE27D9BE2EFD20C7E626322720888761 |
| SHA256: | 93E55101DE59007A9017A7AE561C49348684663E79D3CF2C30D069EDF2C8AA61 |
| SSDEEP: | 98304:regG62QdYOn6drlcNvXeXugSKdU5CtDrLAI+a27/Hh27GaokI8mG/haJC68:h16dr6tuoKeC5Z+aoH07Hs4Ek |
MALICIOUS
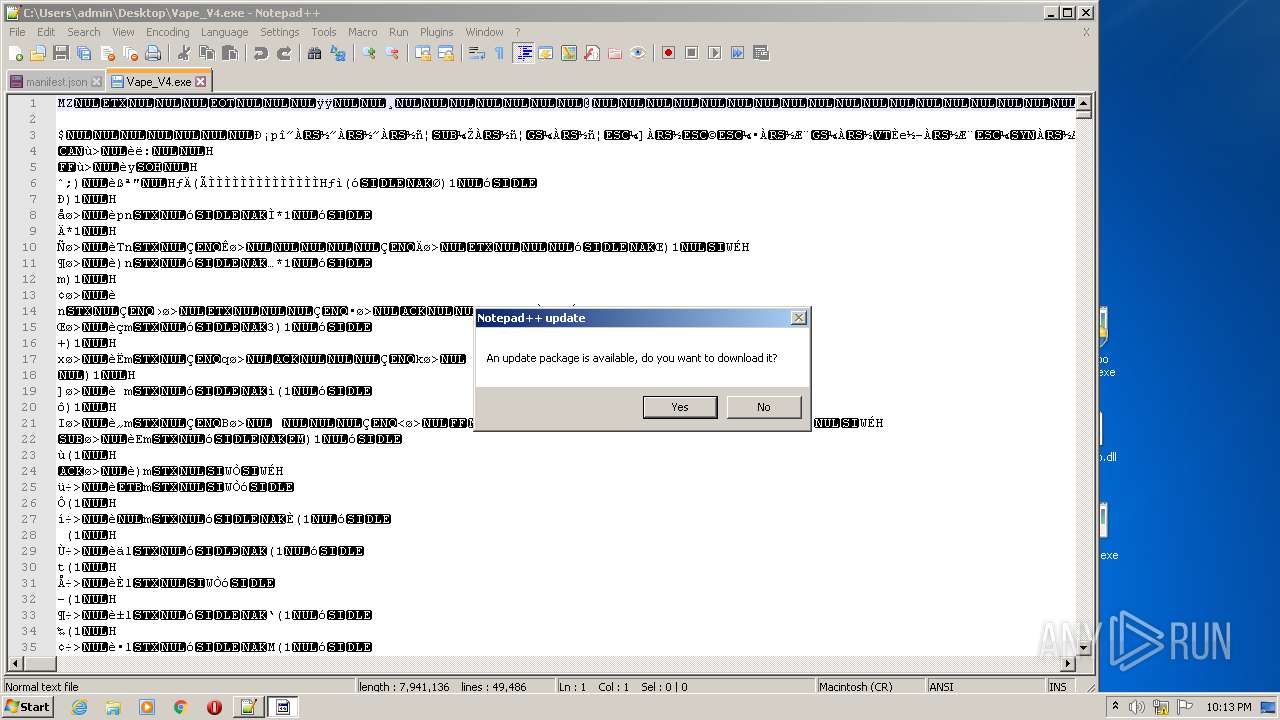
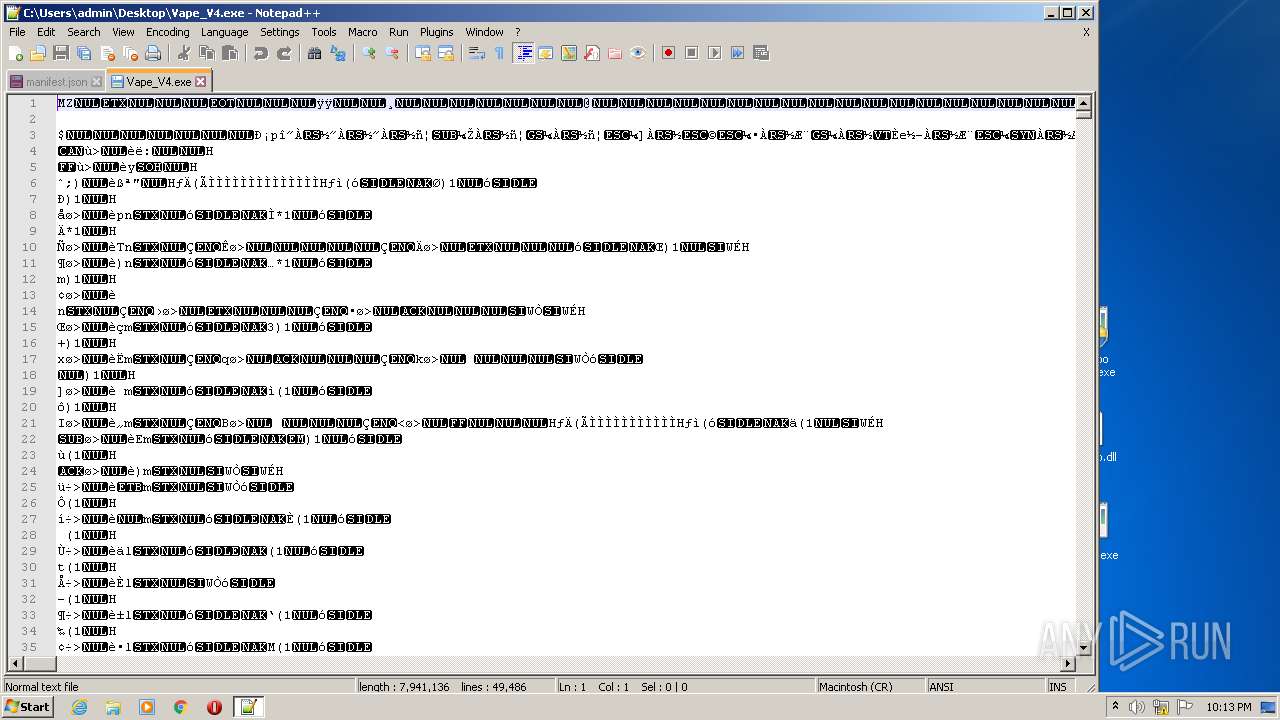
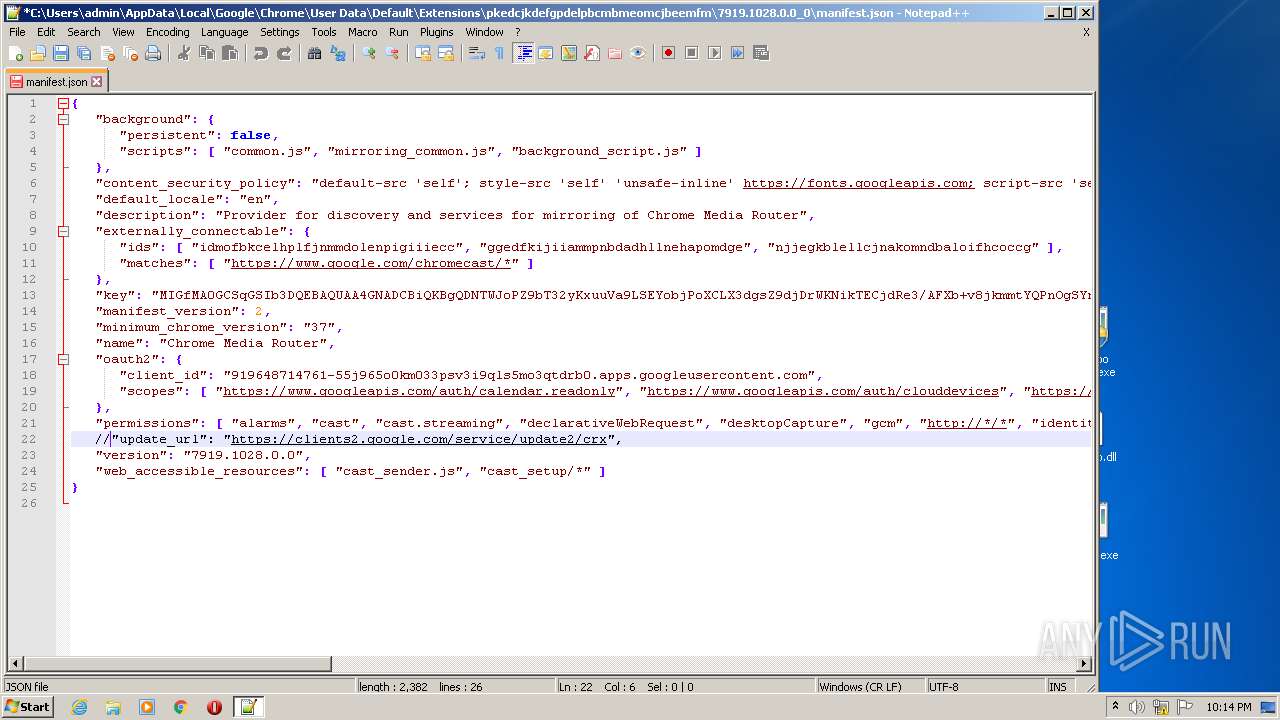
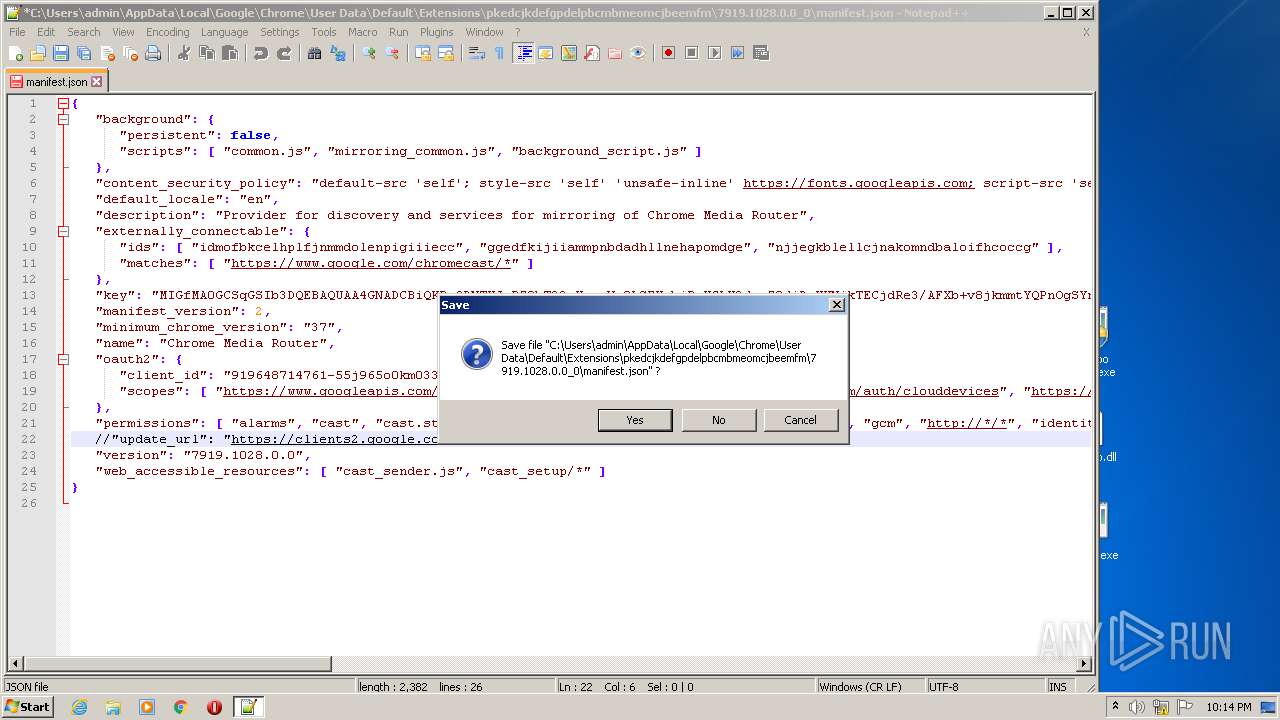
Modifies files in Chrome extension folder
- notepad++.exe (PID: 3024)
SUSPICIOUS
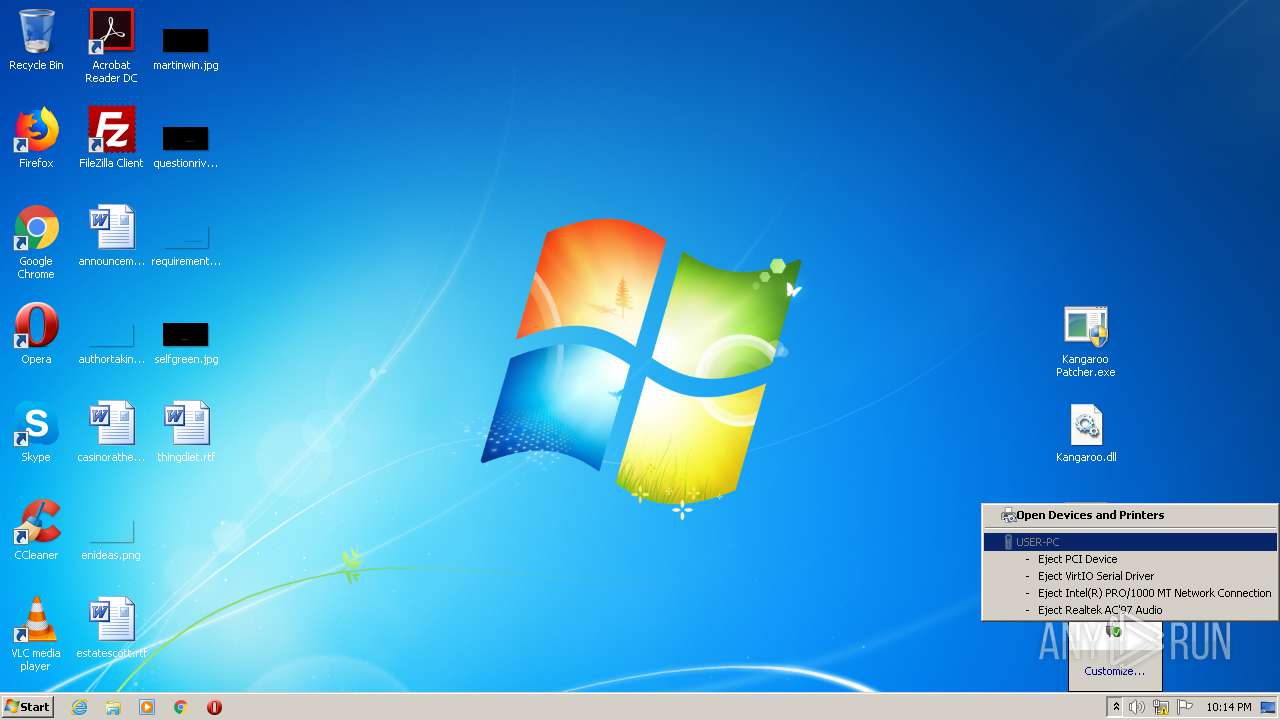
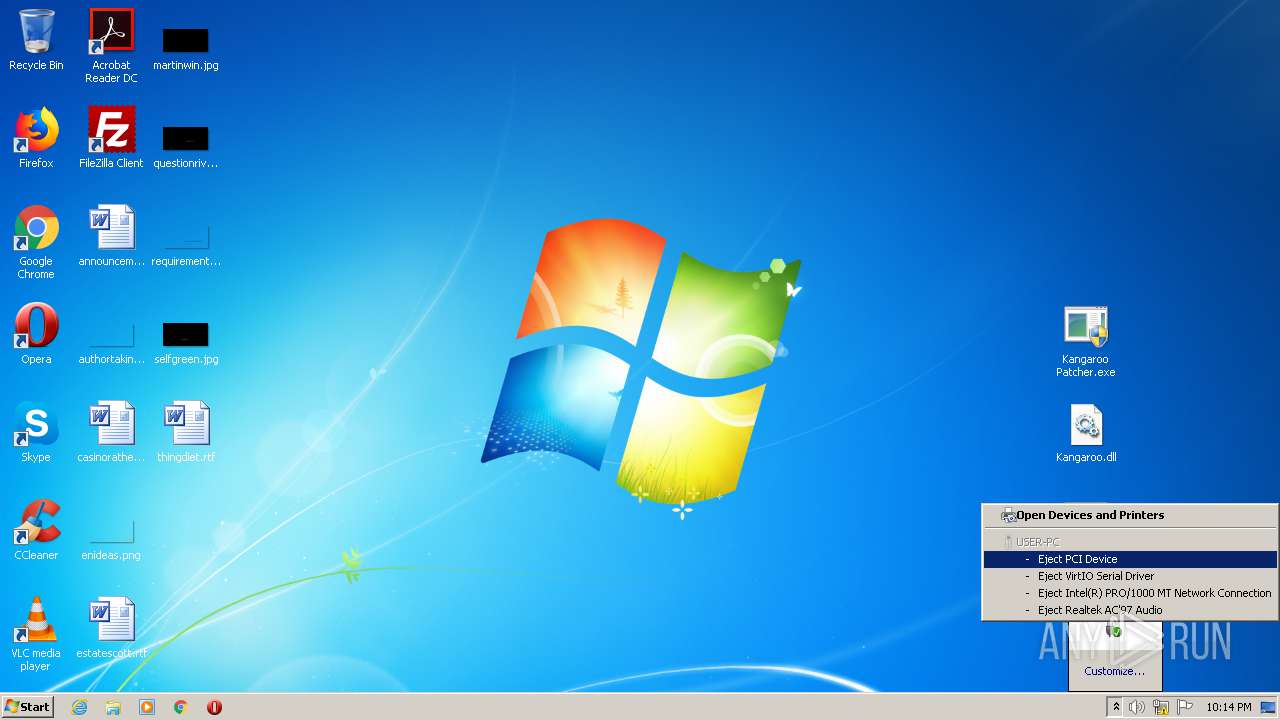
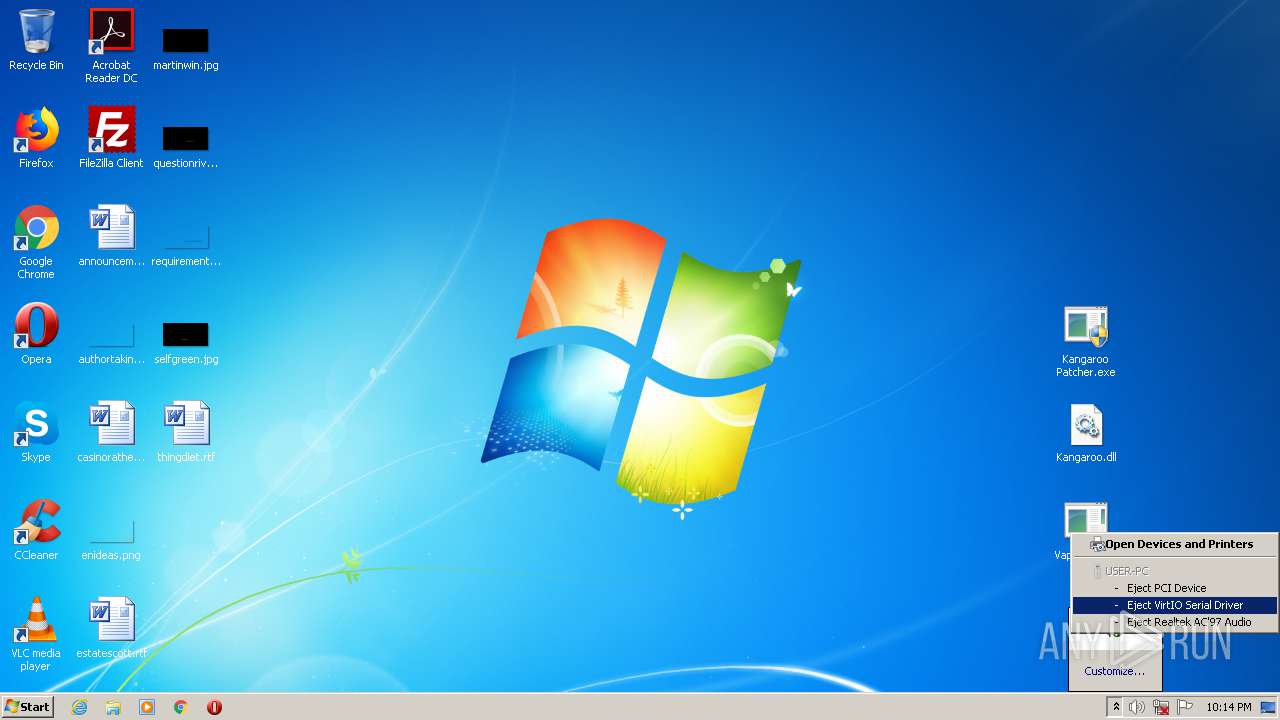
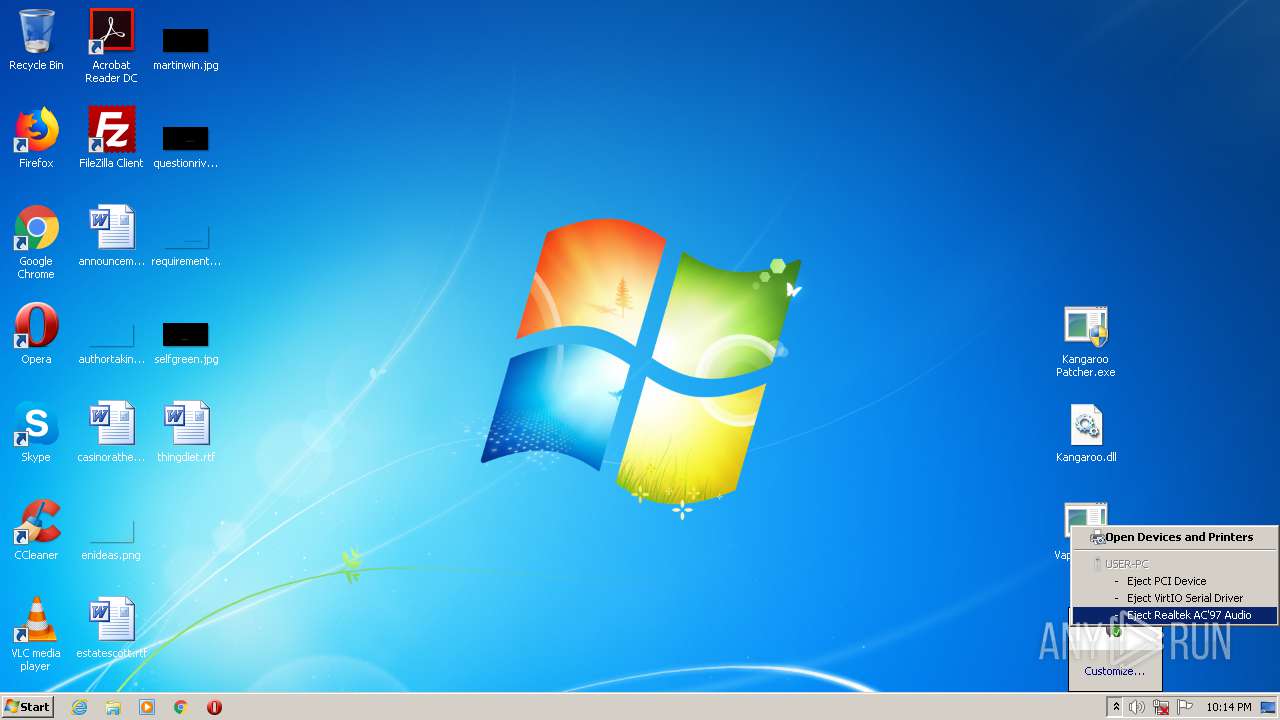
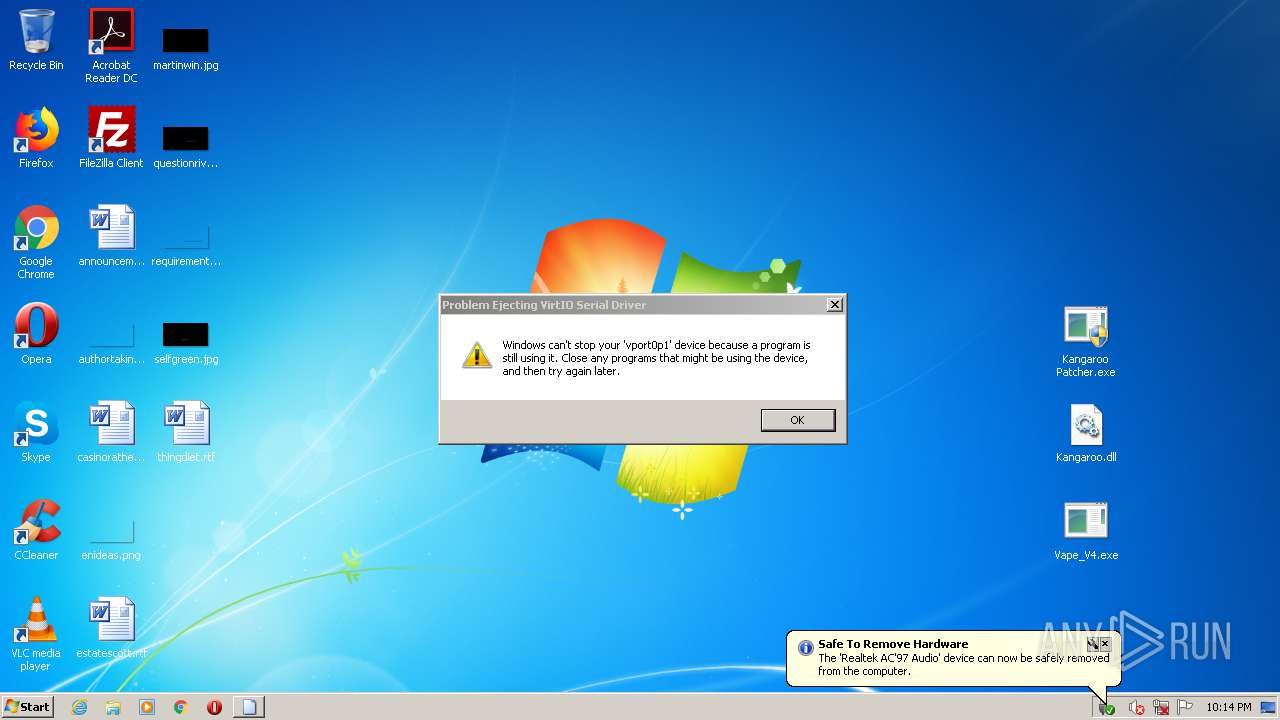
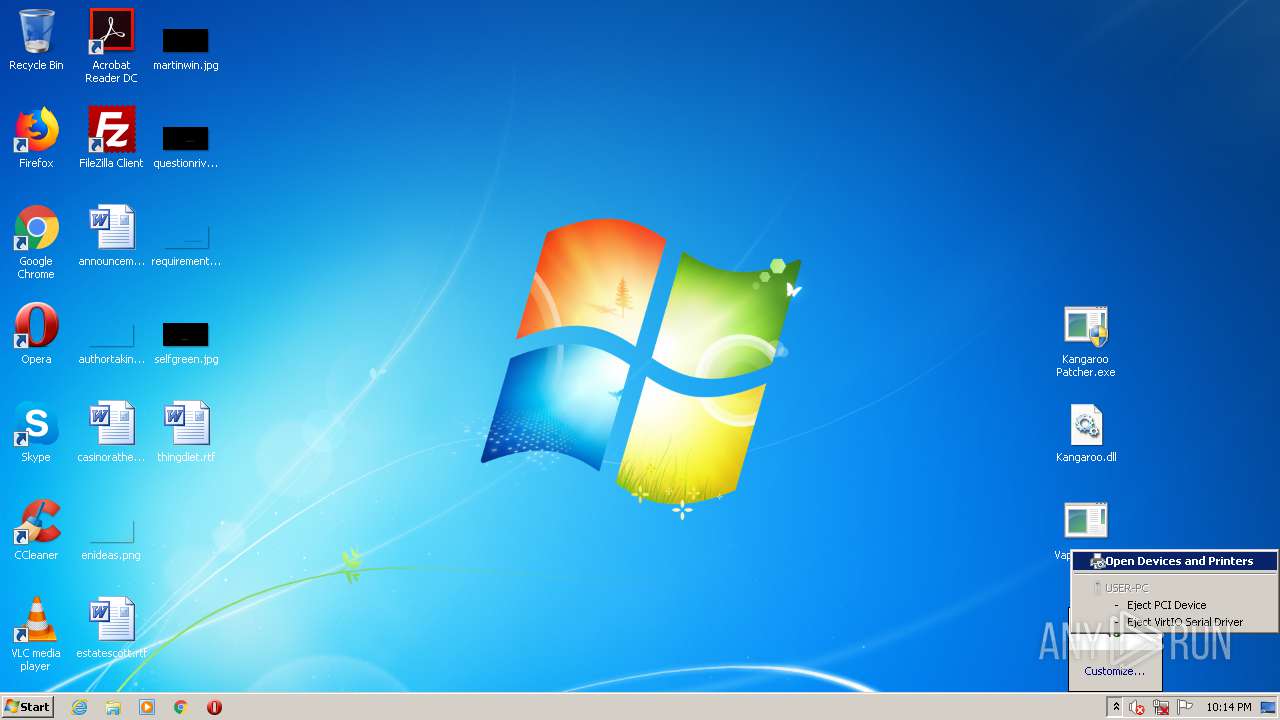
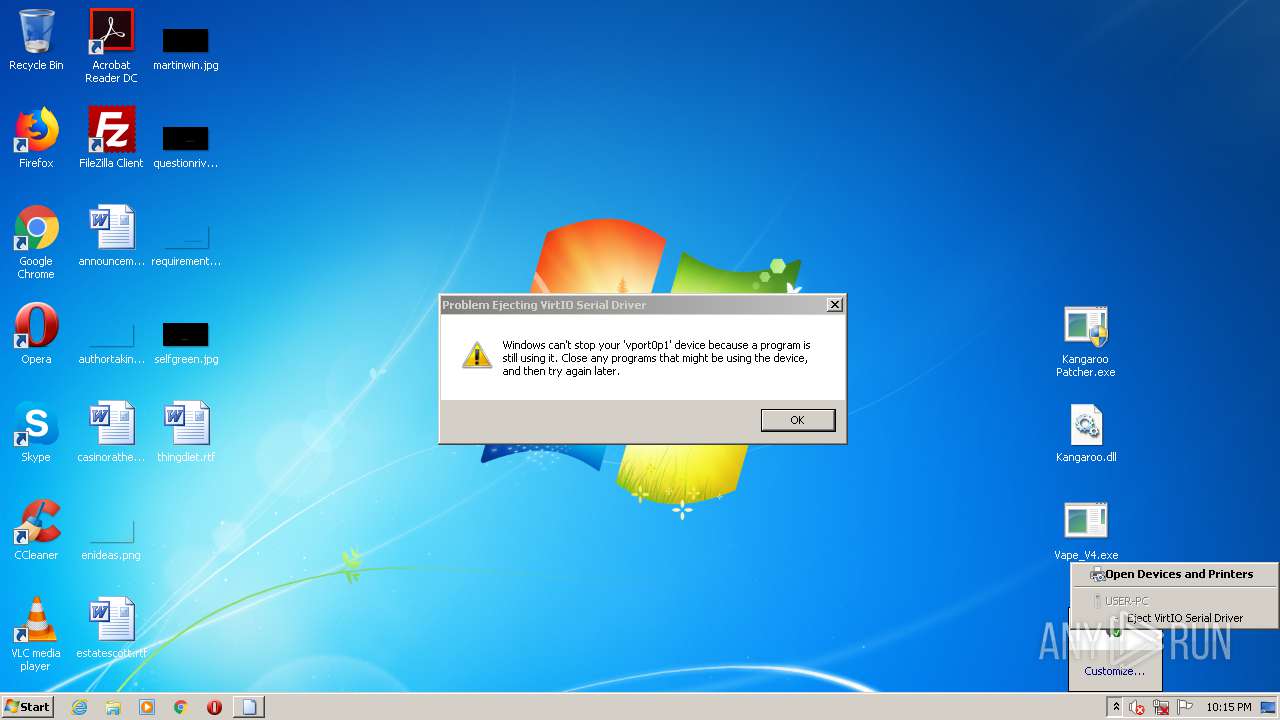
Executed via COM
- DeviceDisplayObjectProvider.exe (PID: 1312)
- rundll32.exe (PID: 2608)
- rundll32.exe (PID: 1796)
- DeviceDisplayObjectProvider.exe (PID: 2956)
- DeviceDisplayObjectProvider.exe (PID: 3464)
- rundll32.exe (PID: 2896)
- rundll32.exe (PID: 3772)
- DeviceDisplayObjectProvider.exe (PID: 4016)
- DeviceDisplayObjectProvider.exe (PID: 2180)
- rundll32.exe (PID: 3248)
- rundll32.exe (PID: 968)
- rundll32.exe (PID: 2948)
- DeviceDisplayObjectProvider.exe (PID: 1040)
INFO
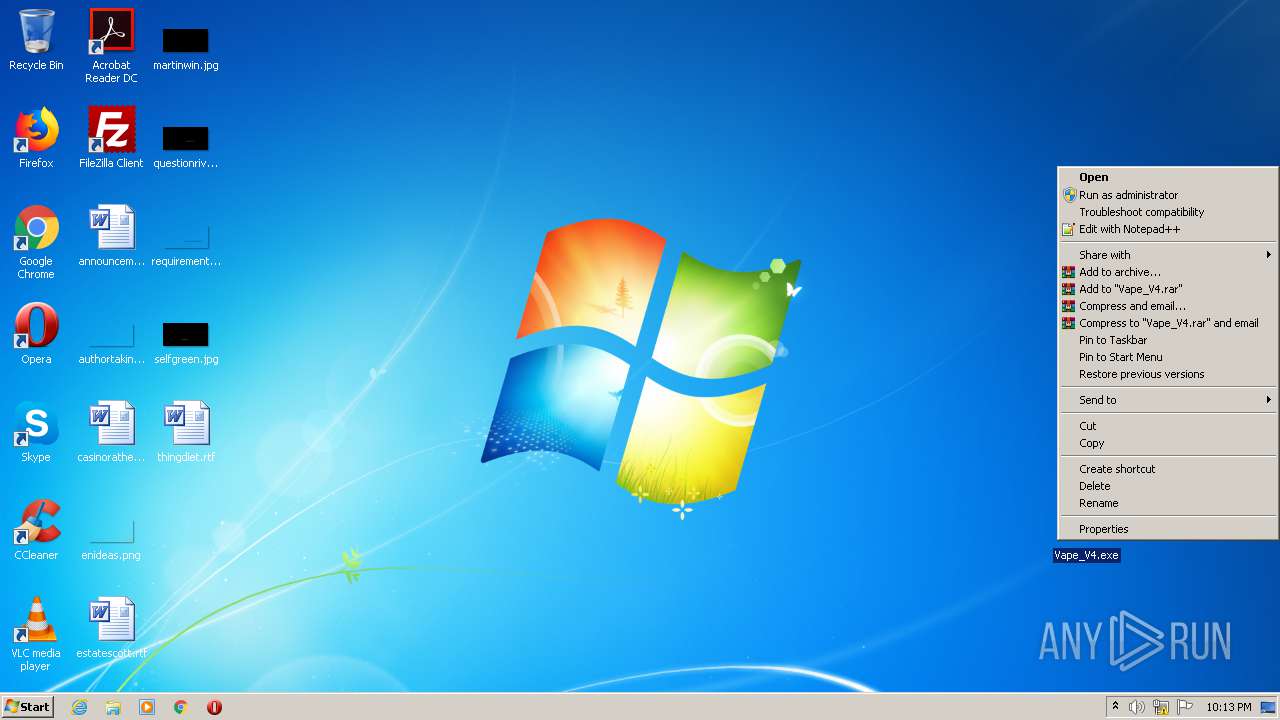
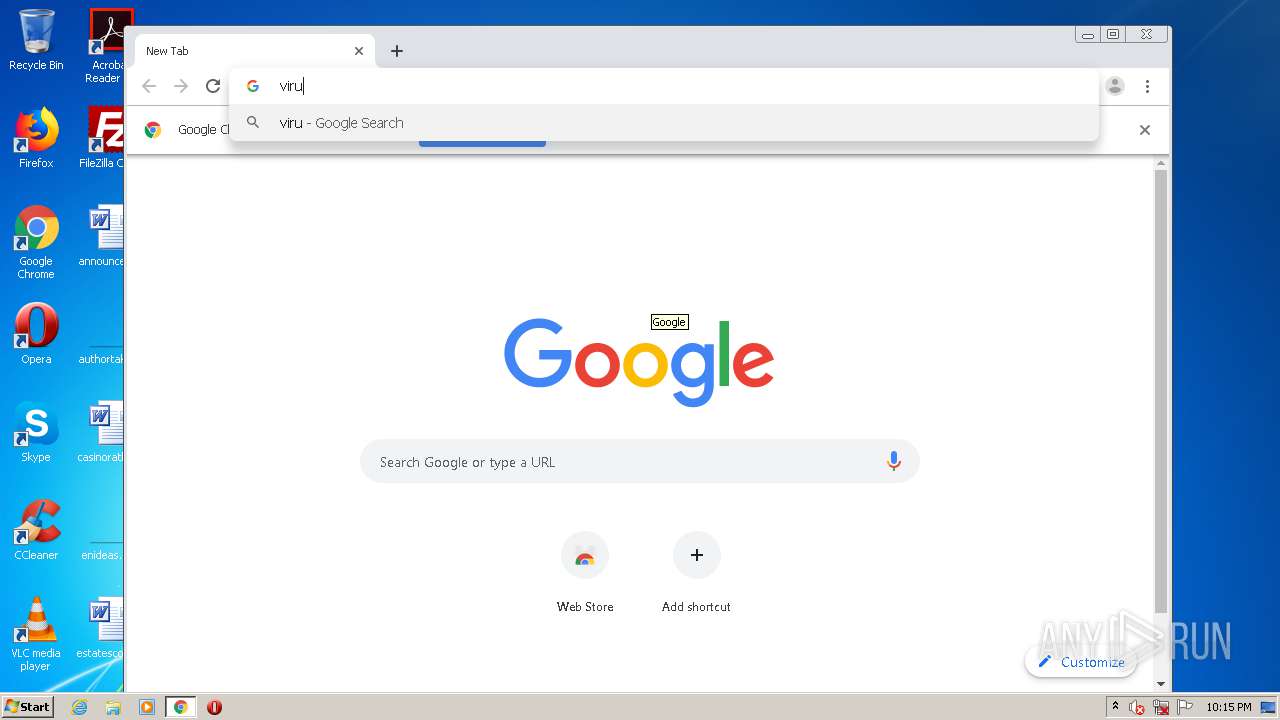
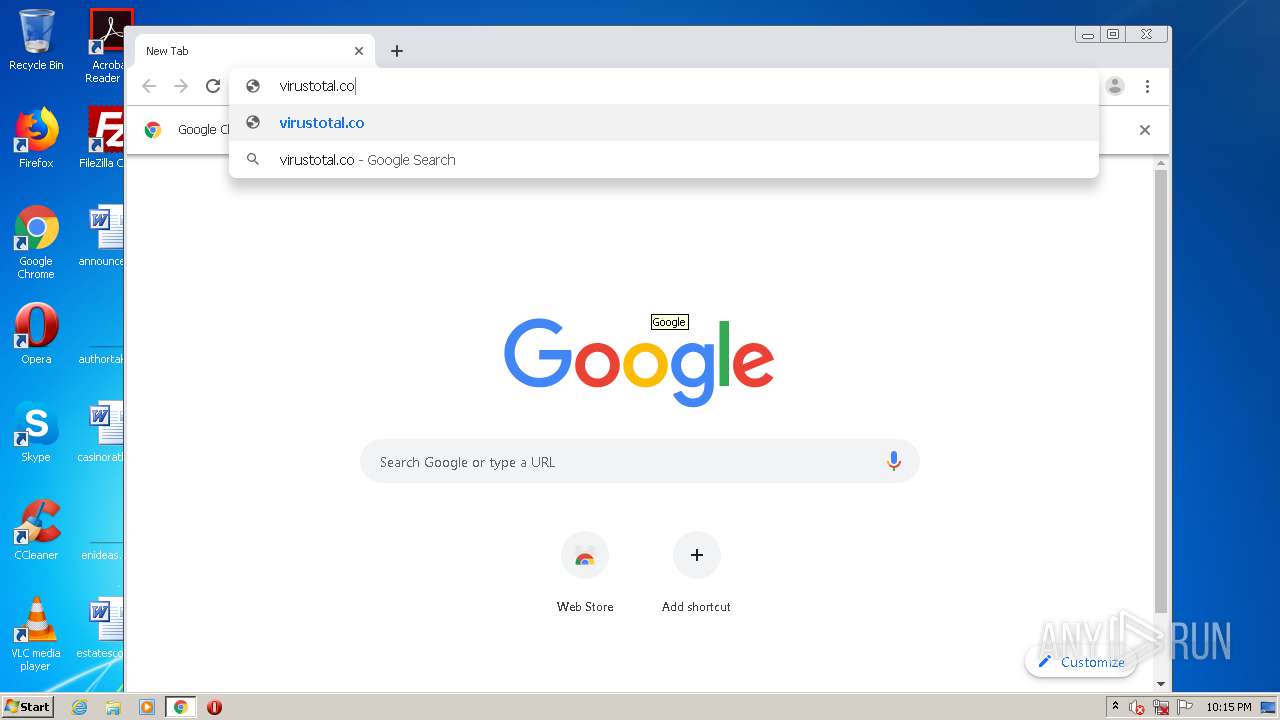
Manual execution by user
- notepad++.exe (PID: 3100)
- notepad++.exe (PID: 3024)
- chrome.exe (PID: 2932)
Reads the hosts file
- chrome.exe (PID: 2932)
- chrome.exe (PID: 1996)
Application launched itself
- chrome.exe (PID: 2932)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:11:28 19:34:28 |
| ZipCRC: | 0xec7dc4e0 |
| ZipCompressedSize: | 5319734 |
| ZipUncompressedSize: | 7941136 |
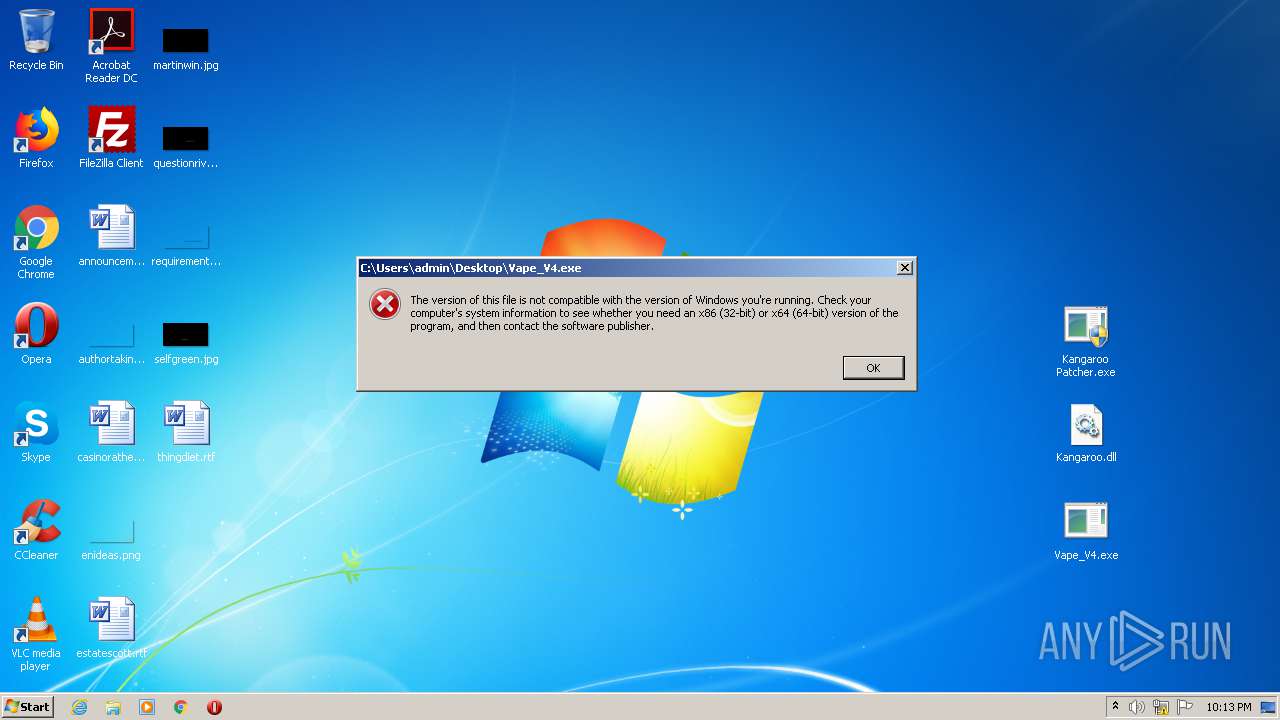
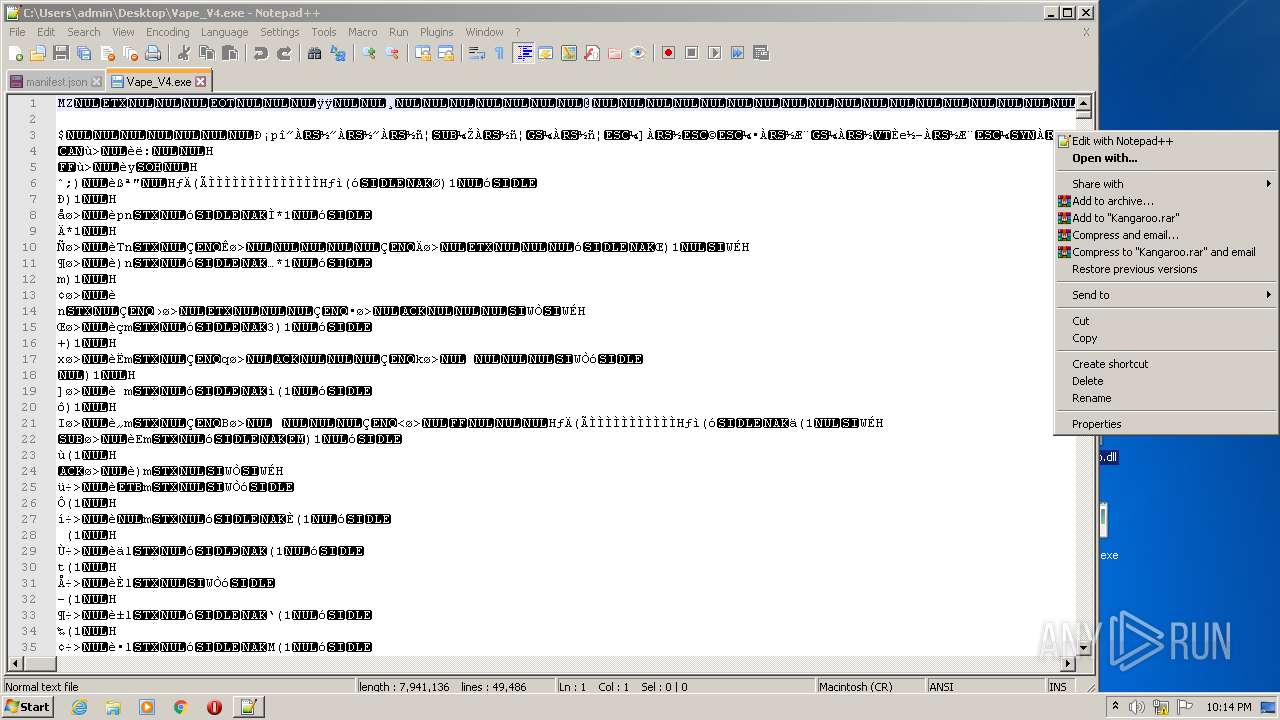
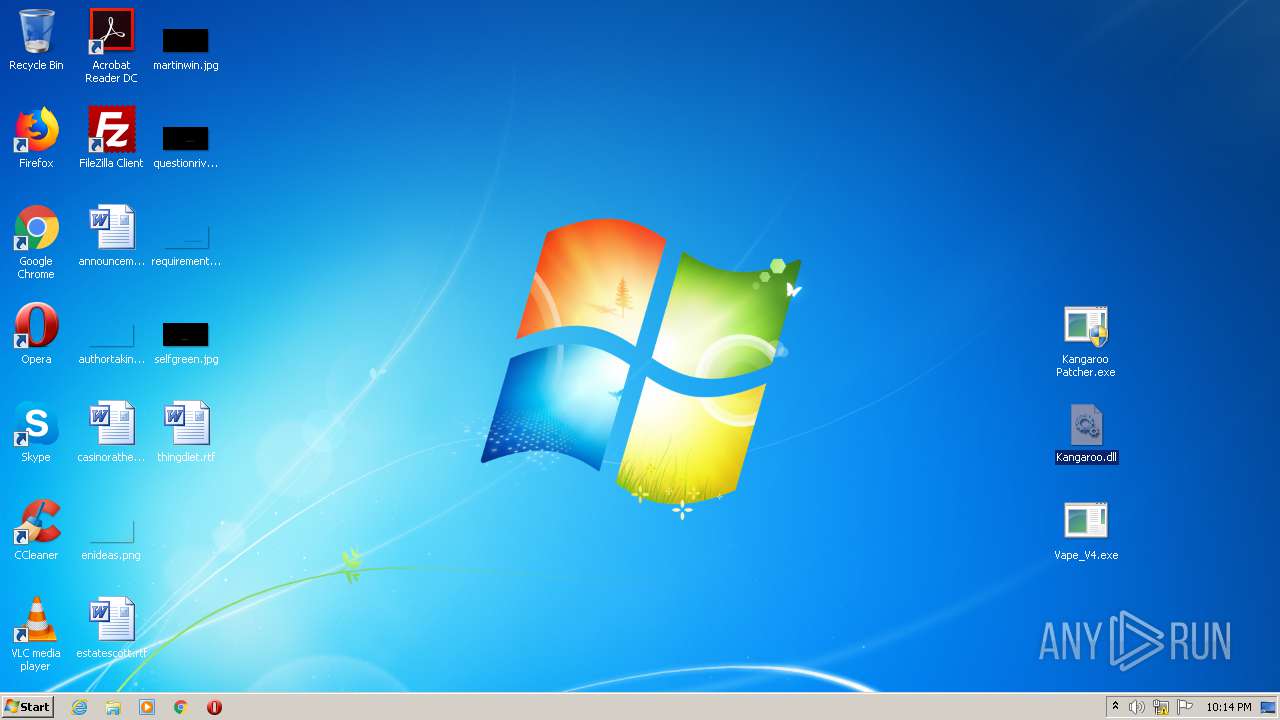
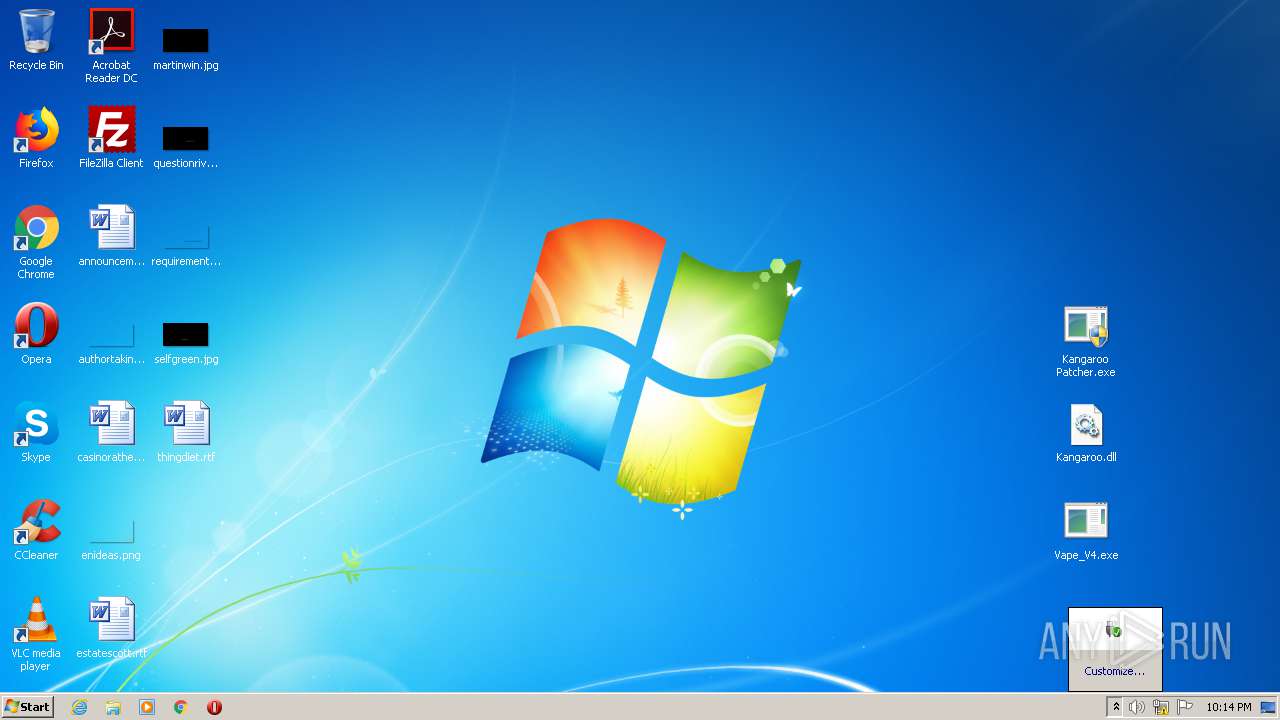
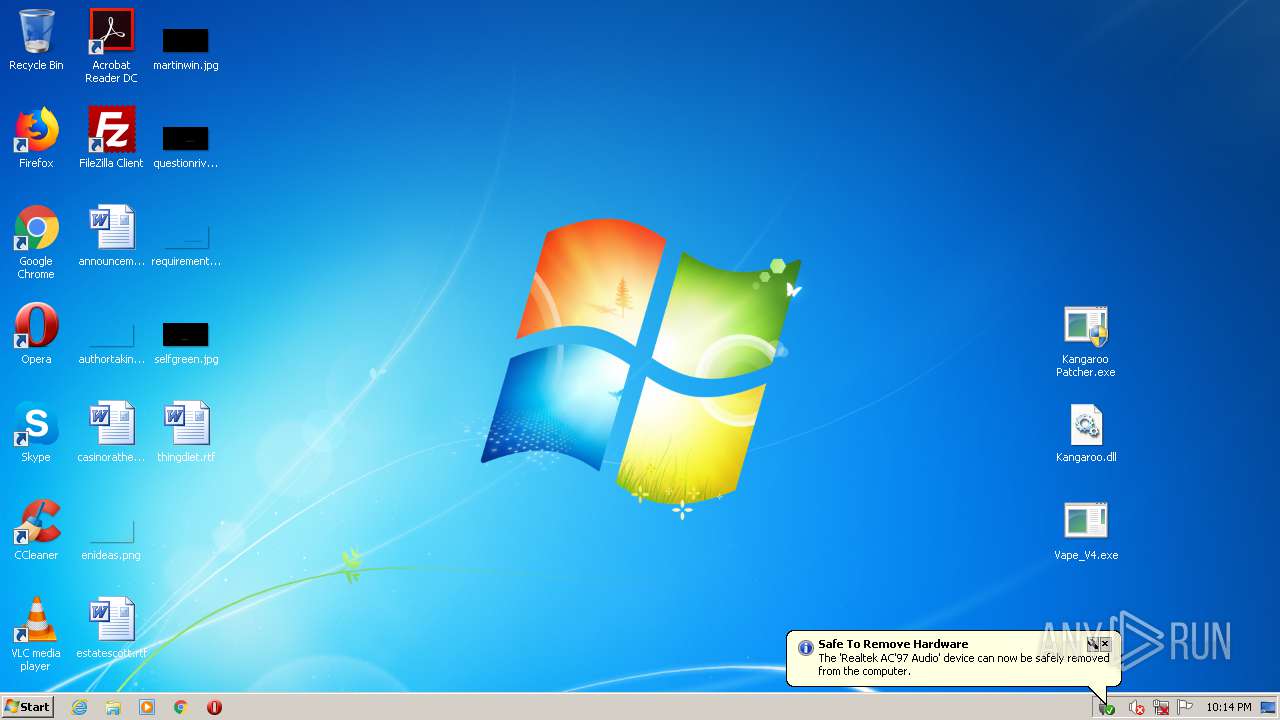
| ZipFileName: | Vape_V4.exe |
Total processes
65
Monitored processes
28
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,7823600251485745633,10528965267666358002,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16440397408567077452 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1012 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
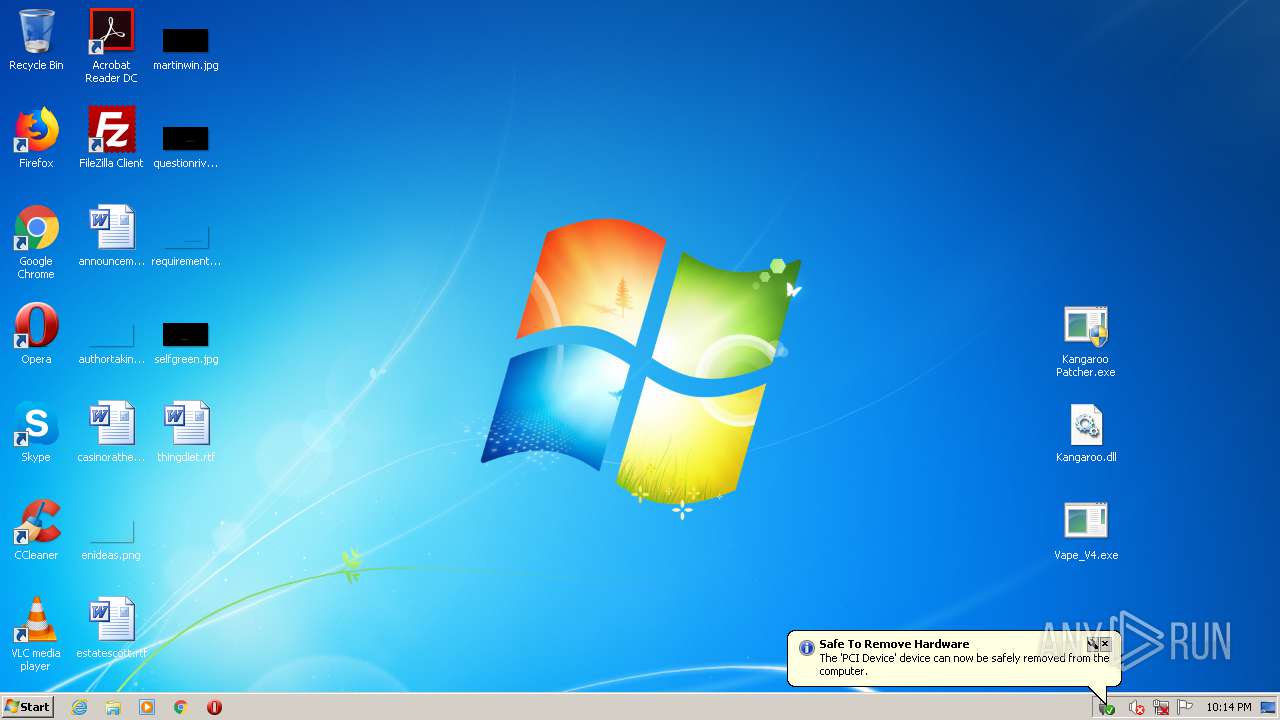
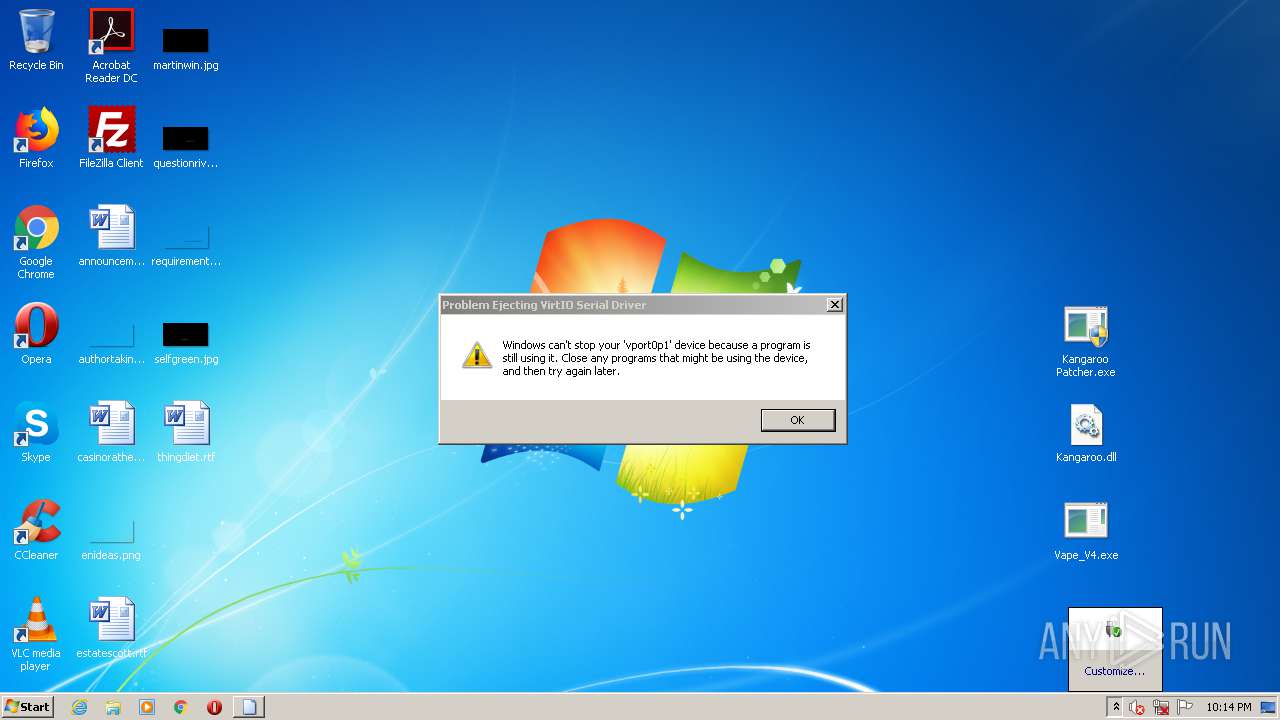
| 968 | rundll32.exe C:\Windows\system32\hotplug.dll,HotPlugEjectVetoed \\.\pipe\PNP_HotPlug_Pipe_1.{b981ff4b-3a4d-4690-ab7c-ed026600b15d} | C:\Windows\system32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1040 | C:\Windows\system32\DeviceDisplayObjectProvider.exe -Embedding | C:\Windows\system32\DeviceDisplayObjectProvider.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Device Display Object Function Discovery Provider Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1312 | C:\Windows\system32\DeviceDisplayObjectProvider.exe -Embedding | C:\Windows\system32\DeviceDisplayObjectProvider.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Device Display Object Function Discovery Provider Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,7823600251485745633,10528965267666358002,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9003294708981481199 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2464 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1796 | C:\Windows\System32\rundll32.exe shell32.dll,SHCreateLocalServerRunDll {995C996E-D918-4a8c-A302-45719A6F4EA7} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,7823600251485745633,10528965267666358002,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=11485131376846496994 --mojo-platform-channel-handle=1604 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2180 | C:\Windows\system32\DeviceDisplayObjectProvider.exe -Embedding | C:\Windows\system32\DeviceDisplayObjectProvider.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Device Display Object Function Discovery Provider Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1008,7823600251485745633,10528965267666358002,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=6796516925288565687 --mojo-platform-channel-handle=2604 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2588 | "C:\Program Files\Notepad++\updater\gup.exe" -v7.51 | C:\Program Files\Notepad++\updater\gup.exe | notepad++.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: GUP : a free (LGPL) Generic Updater Exit code: 0 Version: 4.1 Modules
| |||||||||||||||
Total events
914
Read events
837
Write events
74
Delete events
3
Modification events
| (PID) Process: | (2920) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2920) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2920) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2920) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Askingly-Pack.zip | |||
| (PID) Process: | (2920) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2920) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2920) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2920) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2920) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (2920) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\AppData\Local\Temp | |||
Executable files
0
Suspicious files
18
Text files
52
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
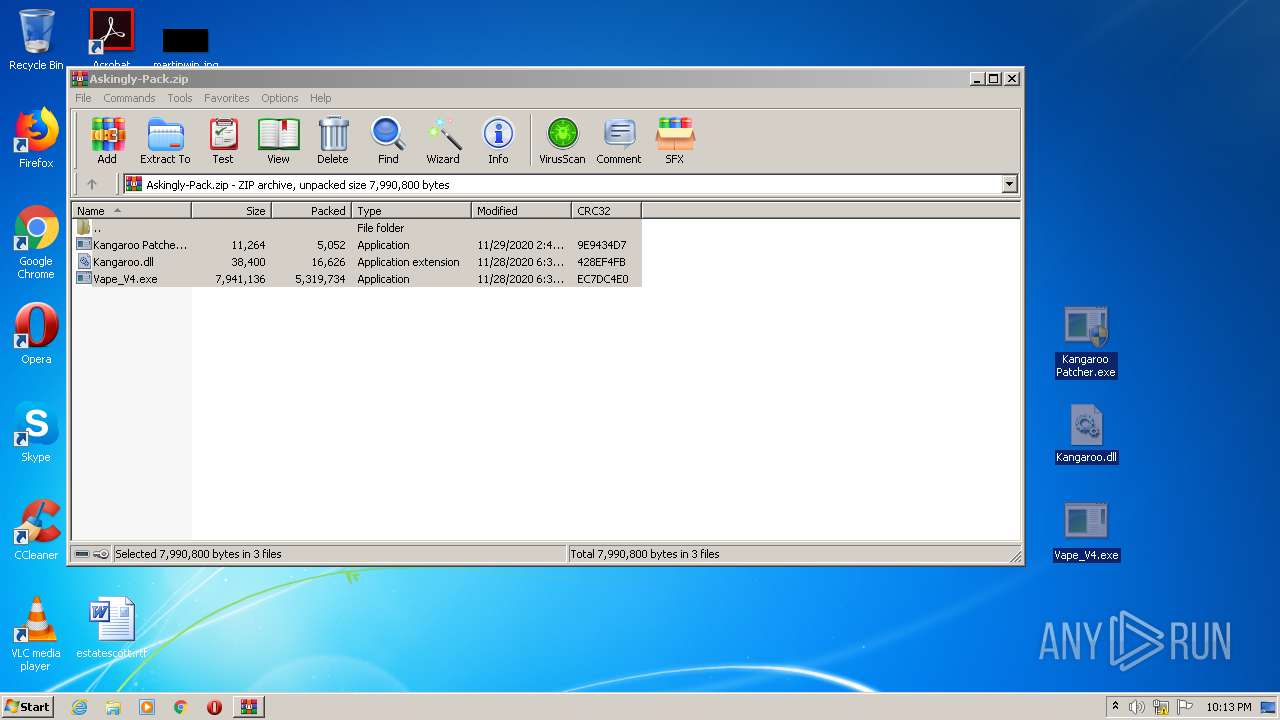
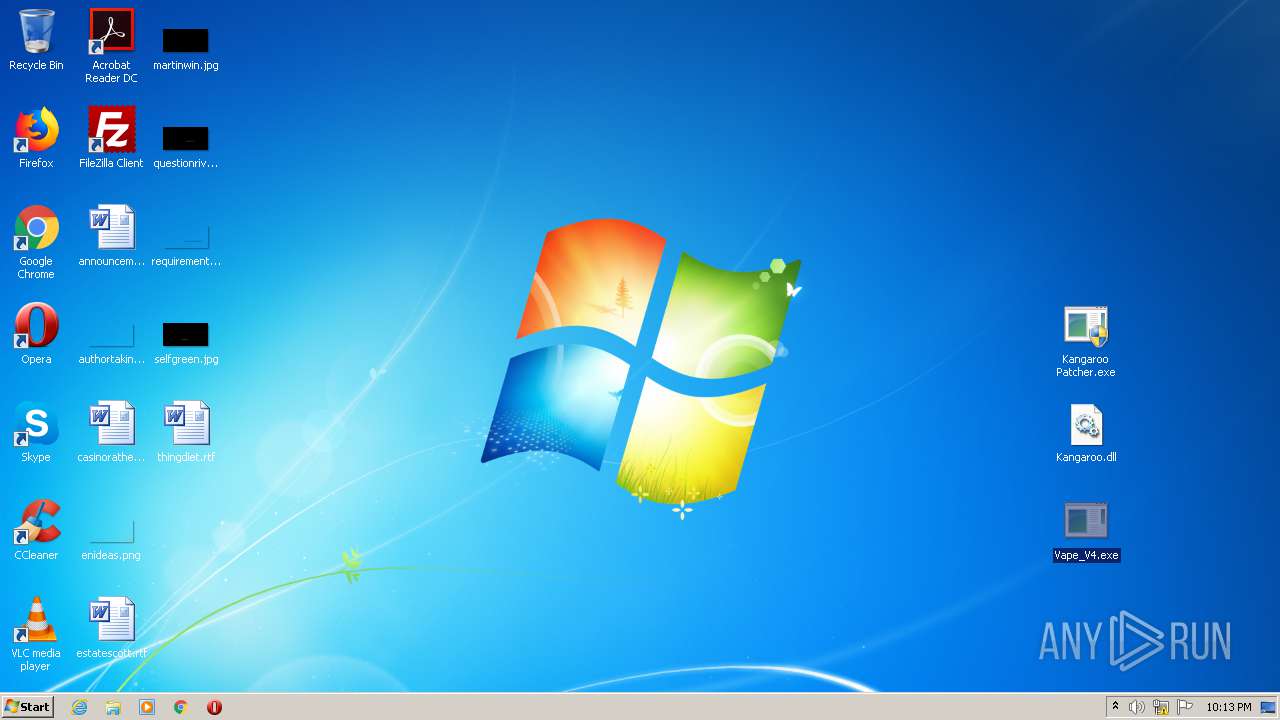
| 2920 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2920.34058\Vape_V4.exe | — | |
MD5:— | SHA256:— | |||
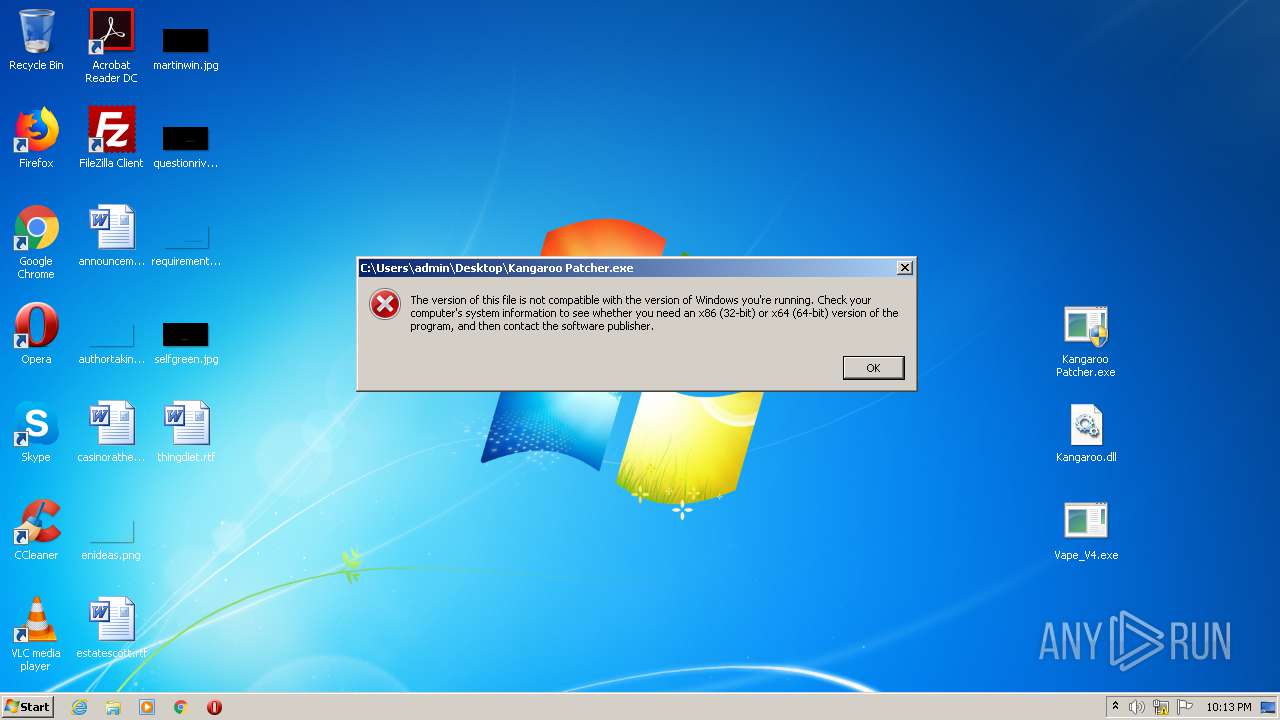
| 2920 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2920.34058\Kangaroo Patcher.exe | — | |
MD5:— | SHA256:— | |||
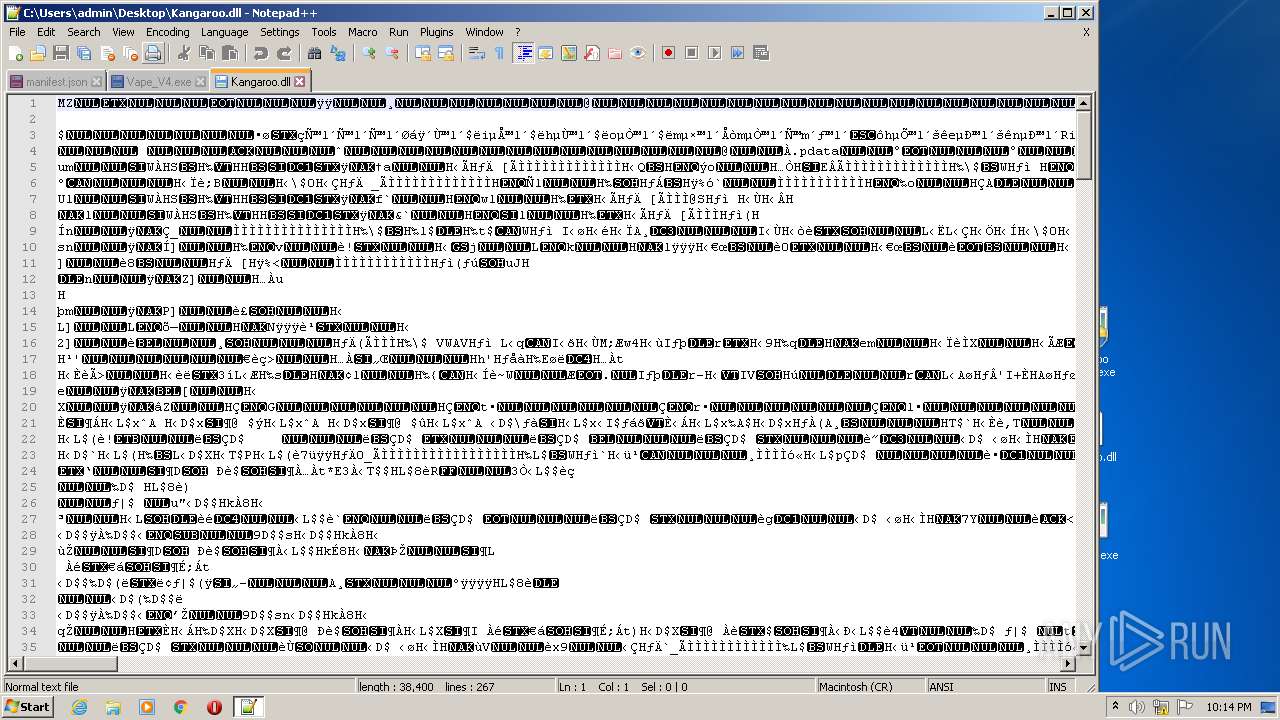
| 2920 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2920.34058\Kangaroo.dll | — | |
MD5:— | SHA256:— | |||
| 1312 | DeviceDisplayObjectProvider.exe | C:\Users\admin\AppData\Local\Microsoft\Device Metadata\dmrc.idx.0 | — | |
MD5:— | SHA256:— | |||
| 1312 | DeviceDisplayObjectProvider.exe | C:\Users\admin\AppData\Local\Microsoft\Device Metadata\OLDCACHE.000 | — | |
MD5:— | SHA256:— | |||
| 2956 | DeviceDisplayObjectProvider.exe | C:\Users\admin\AppData\Local\Microsoft\Device Metadata\dmrc.idx.0 | — | |
MD5:— | SHA256:— | |||
| 2956 | DeviceDisplayObjectProvider.exe | C:\Users\admin\AppData\Local\Microsoft\Device Metadata\OLDCACHE.000 | — | |
MD5:— | SHA256:— | |||
| 3464 | DeviceDisplayObjectProvider.exe | C:\Users\admin\AppData\Local\Microsoft\Device Metadata\dmrc.idx.0 | — | |
MD5:— | SHA256:— | |||
| 3464 | DeviceDisplayObjectProvider.exe | C:\Users\admin\AppData\Local\Microsoft\Device Metadata\OLDCACHE.000 | — | |
MD5:— | SHA256:— | |||
| 4016 | DeviceDisplayObjectProvider.exe | C:\Users\admin\AppData\Local\Microsoft\Device Metadata\dmrc.idx.0 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
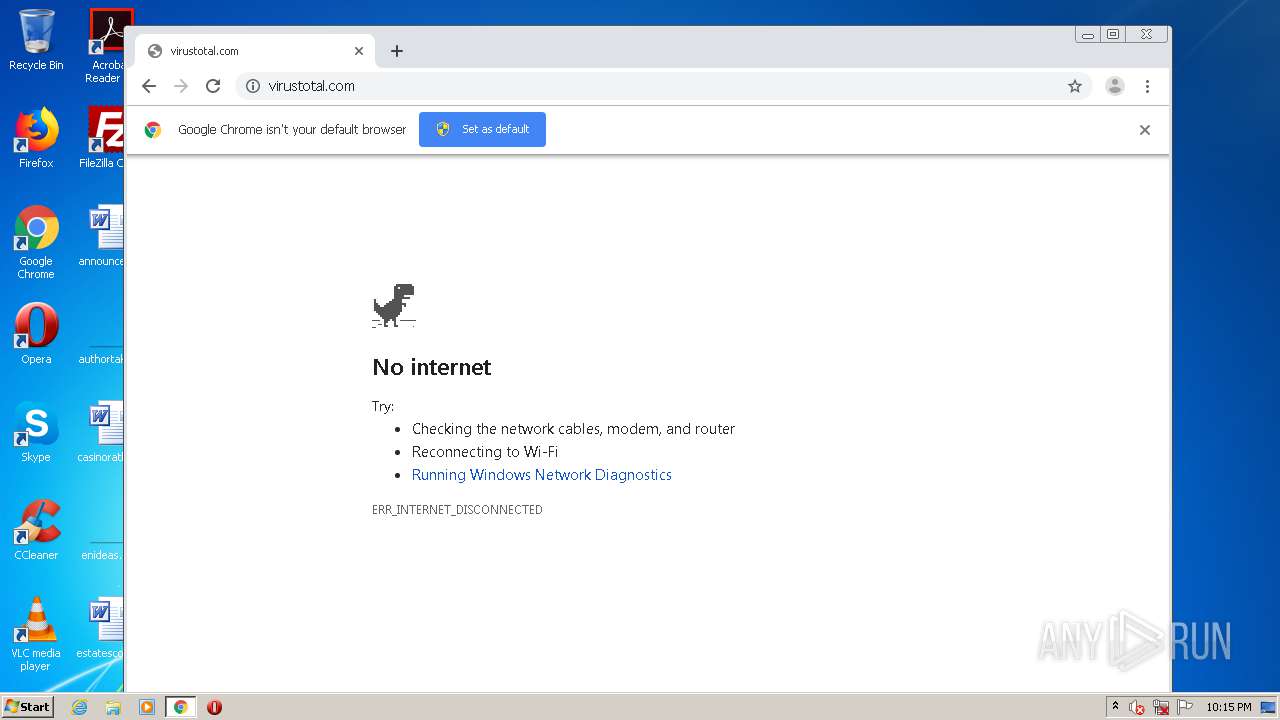
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2588 | gup.exe | 104.31.88.28:443 | notepad-plus-plus.org | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
notepad-plus-plus.org |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabl⋂ϵ魬욜ǖ≊ϵVerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|