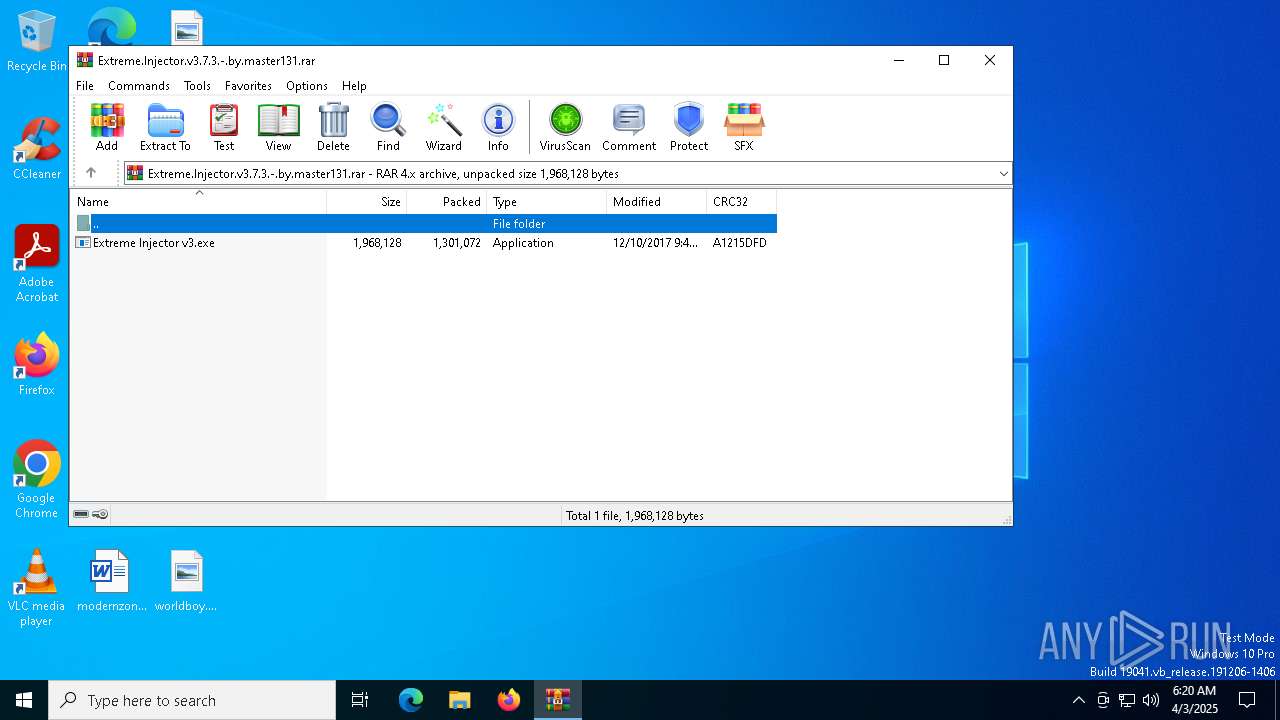
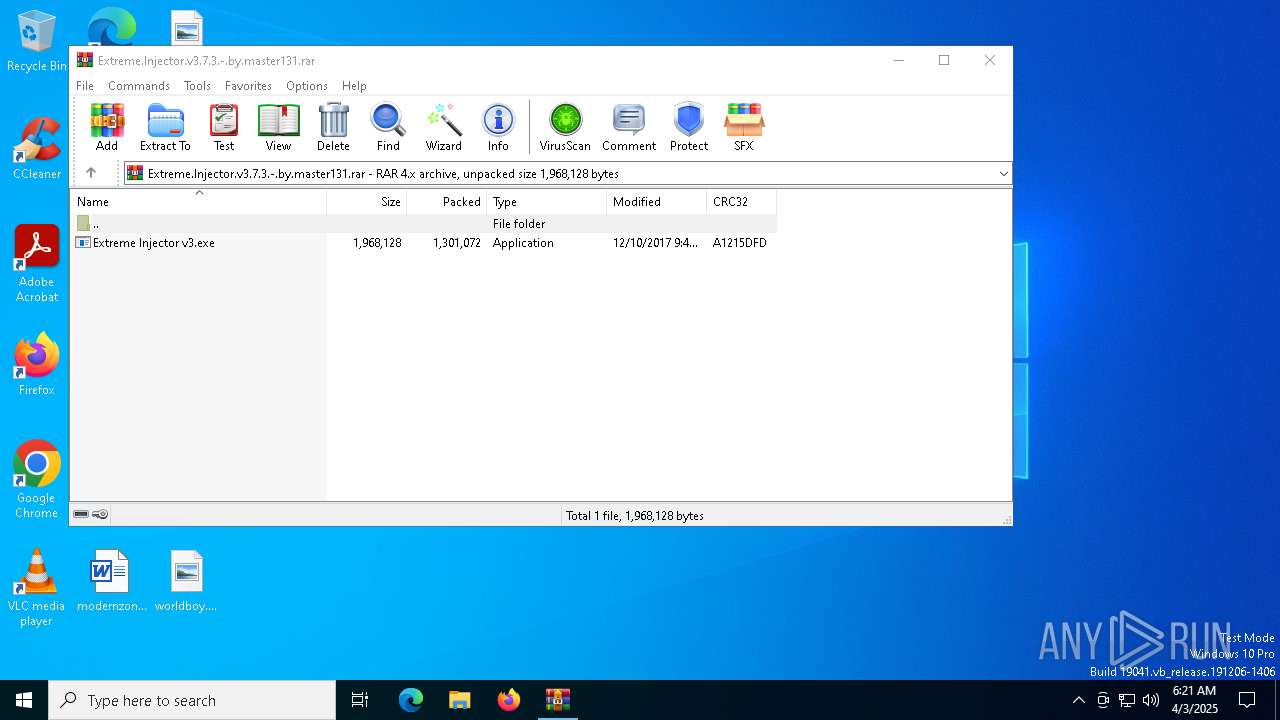
| download: | /master131/ExtremeInjector/releases/download/v3.7.3/Extreme.Injector.v3.7.3.-.by.master131.rar |
| Full analysis: | https://app.any.run/tasks/aeb7ef18-cf21-4089-9d3c-e41d92c6af5c |
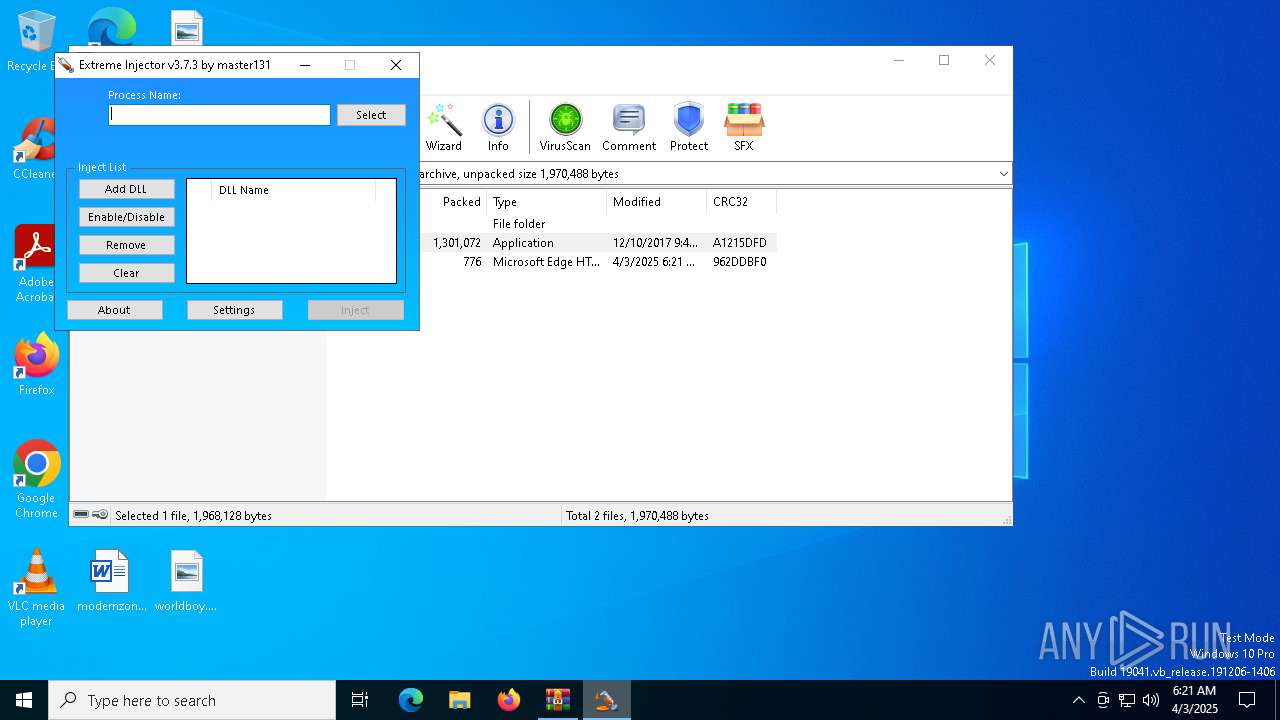
| Verdict: | Malicious activity |
| Analysis date: | April 03, 2025, 06:20:51 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | 90064F3C81022F4BEB1B660EA21F16C7 |
| SHA1: | 3FD13AC9BEF5DCA67F98750E002712DE219494F0 |
| SHA256: | 93DDA8B91586ACF53C70DFD3F512FCFF5793A9AF69E174D7E3AD67190361BCE8 |
| SSDEEP: | 24576:pp4nq3hGhlcEdjYeqBRmWsGWo53eM3dIqcyL76MQ22nkchgQCebXckQuM3n+2:ppJ3KaEg9sGWowM3qqcy76F2PmVn7jMv |
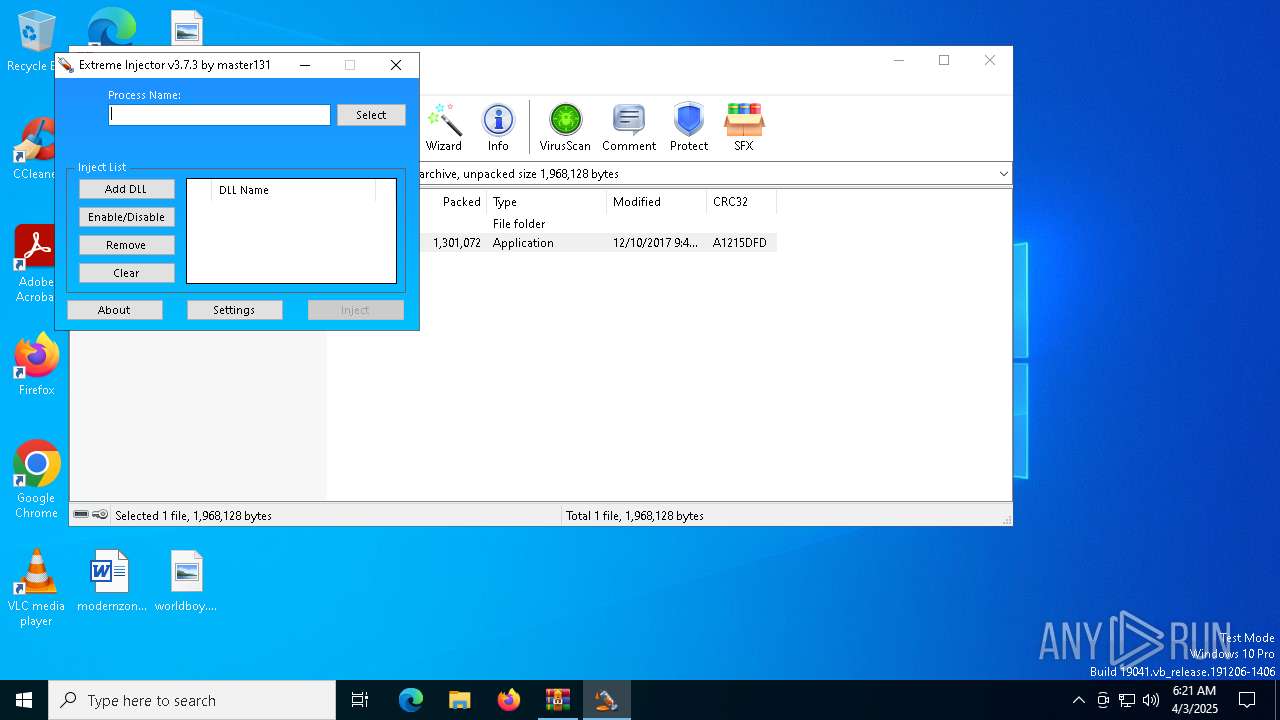
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 6040)
SUSPICIOUS
Reads the date of Windows installation
- Extreme Injector v3.exe (PID: 7664)
Reads security settings of Internet Explorer
- Extreme Injector v3.exe (PID: 7664)
- WinRAR.exe (PID: 6040)
Application launched itself
- Extreme Injector v3.exe (PID: 7664)
INFO
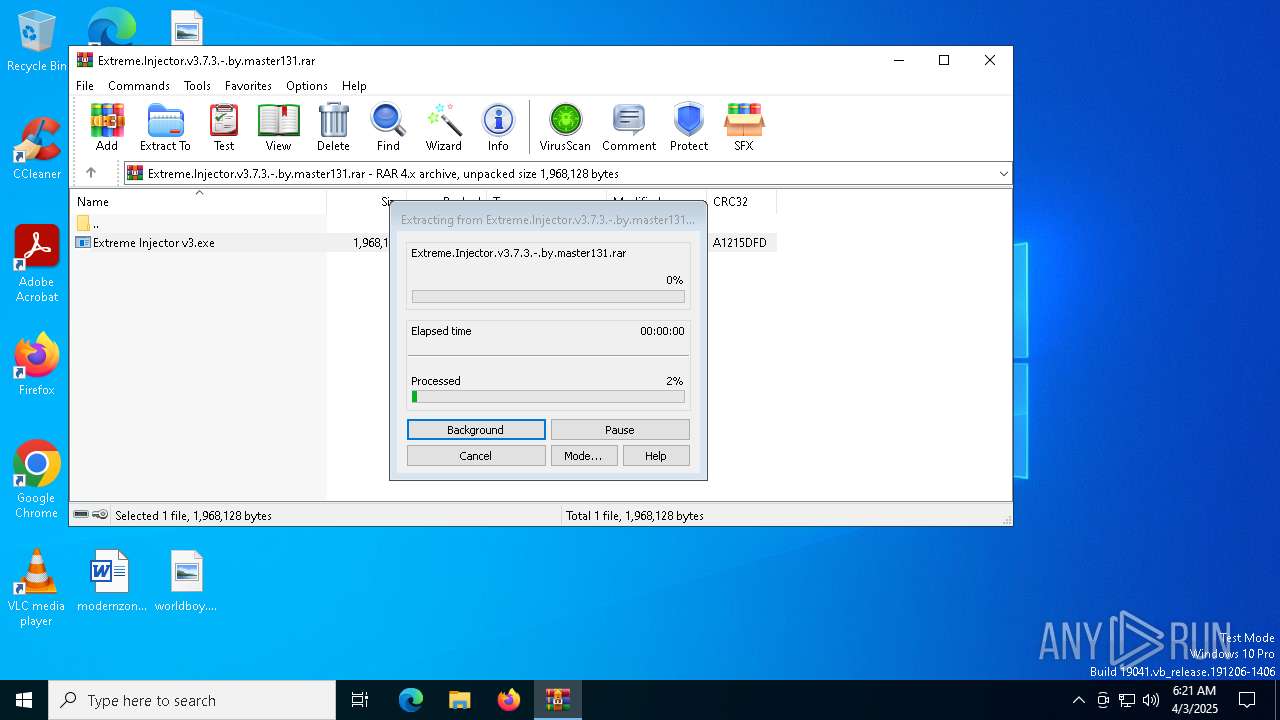
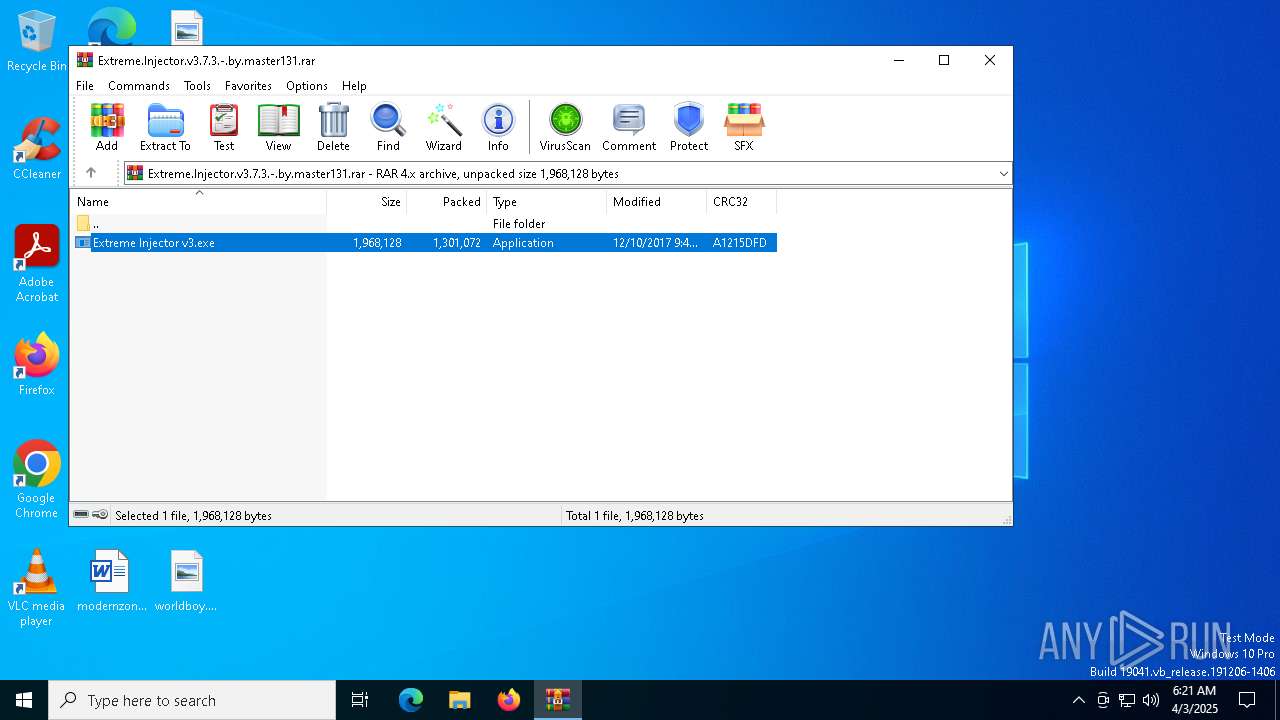
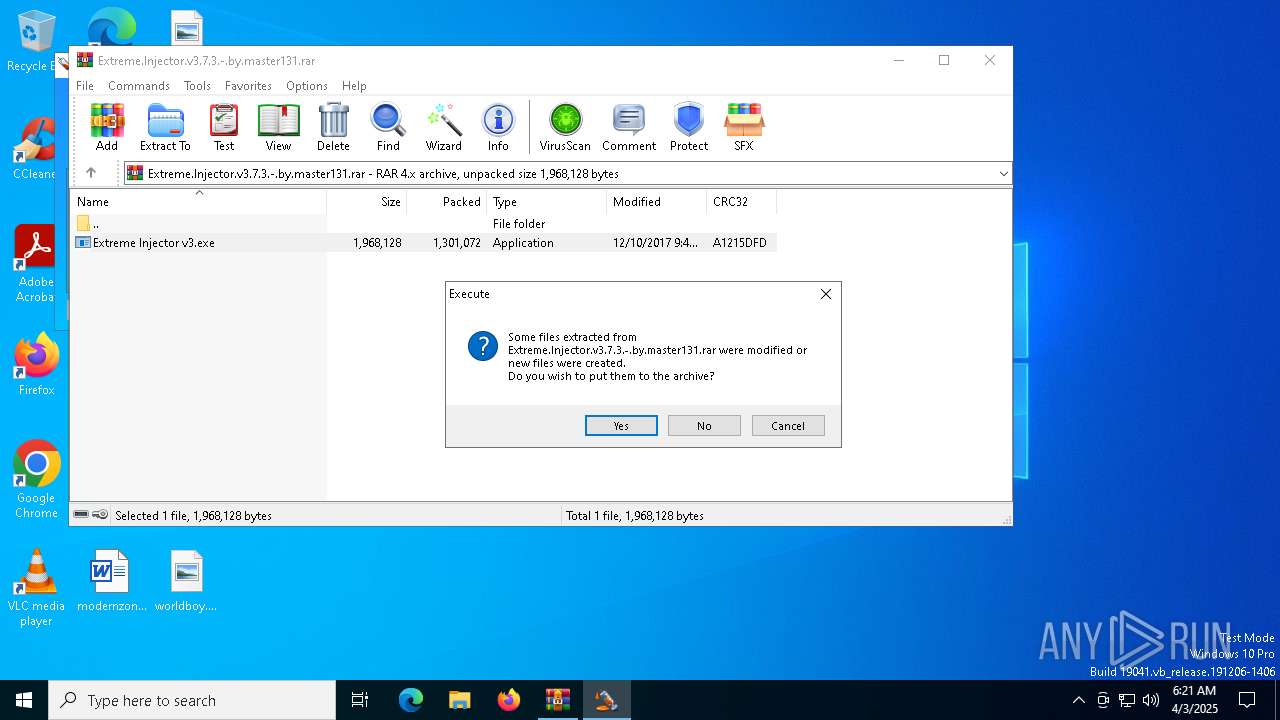
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6040)
Reads the computer name
- Extreme Injector v3.exe (PID: 7748)
- Extreme Injector v3.exe (PID: 7664)
Checks supported languages
- Extreme Injector v3.exe (PID: 7748)
- Extreme Injector v3.exe (PID: 7664)
Process checks computer location settings
- Extreme Injector v3.exe (PID: 7664)
Reads the machine GUID from the registry
- Extreme Injector v3.exe (PID: 7664)
- Extreme Injector v3.exe (PID: 7748)
Checks proxy server information
- Extreme Injector v3.exe (PID: 7748)
Disables trace logs
- Extreme Injector v3.exe (PID: 7748)
Reads Environment values
- Extreme Injector v3.exe (PID: 7748)
Create files in a temporary directory
- Extreme Injector v3.exe (PID: 7748)
Reads the software policy settings
- Extreme Injector v3.exe (PID: 7748)
Potential library load (Base64 Encoded 'LoadLibrary')
- Extreme Injector v3.exe (PID: 7748)
Potential access to remote process (Base64 Encoded 'OpenProcess')
- Extreme Injector v3.exe (PID: 7748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
| FileVersion: | RAR v4 |
|---|---|
| CompressedSize: | 1301121 |
| UncompressedSize: | 1968128 |
| OperatingSystem: | Win32 |
| ModifyDate: | 2017:12:10 09:48:48 |
| PackingMethod: | Normal |
| ArchivedFileName: | Extreme Injector v3.exe |
Total processes
133
Monitored processes
5
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6040 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Extreme.Injector.v3.7.3.-.by.master131.rar | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 7208 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7240 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7664 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa6040.8031\Extreme Injector v3.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa6040.8031\Extreme Injector v3.exe | — | WinRAR.exe | |||||||||||
User: admin Company: master131 Integrity Level: MEDIUM Description: Extreme Injector Exit code: 0 Version: 3.7.3.0 Modules
| |||||||||||||||
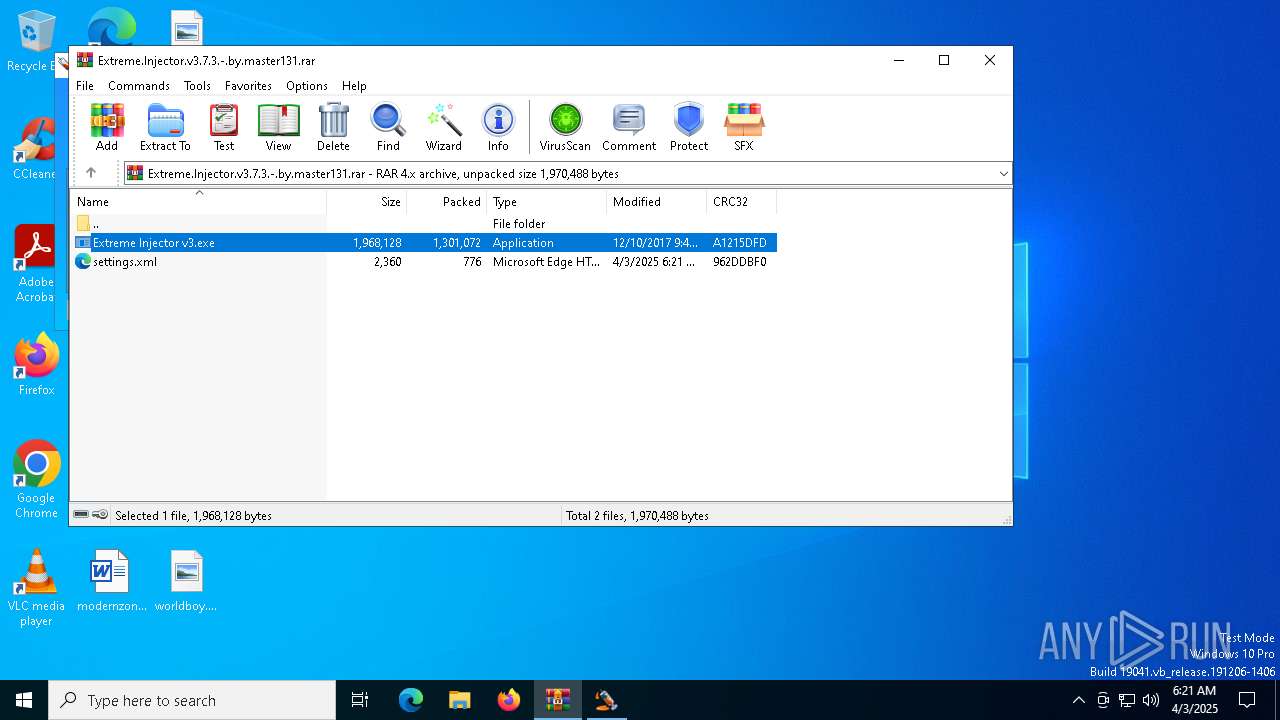
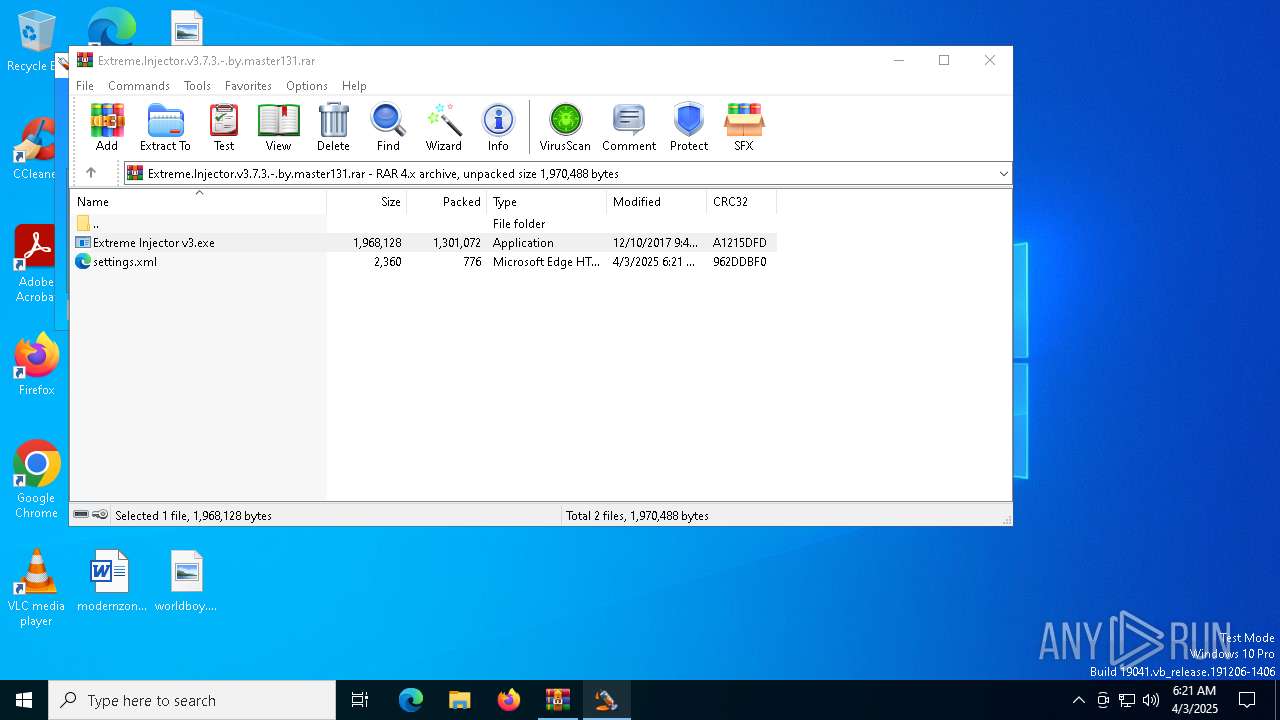
| 7748 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa6040.8031\Extreme Injector v3.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa6040.8031\Extreme Injector v3.exe | Extreme Injector v3.exe | ||||||||||||
User: admin Company: master131 Integrity Level: HIGH Description: Extreme Injector Version: 3.7.3.0 Modules
| |||||||||||||||
Total events
5 207
Read events
5 178
Write events
29
Delete events
0
Modification events
| (PID) Process: | (6040) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6040) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6040) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6040) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Extreme.Injector.v3.7.3.-.by.master131.rar | |||
| (PID) Process: | (6040) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6040) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6040) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6040) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7748) Extreme Injector v3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Extreme Injector v3_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (7748) Extreme Injector v3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Extreme Injector v3_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
Executable files
1
Suspicious files
3
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6040 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Extreme.Injector.v3.7.3.-.by.master131.rar | compressed | |
MD5:61A1A6ECE84DECA49E7FFFF70027CBA7 | SHA256:E44CBA0CF21C07A44C479B041E6DA7FD85023F1075AB1138C2A85C933EAF75B6 | |||
| 6040 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6040.8031\Extreme Injector v3.exe | executable | |
MD5:EC801A7D4B72A288EC6C207BB9FF0131 | SHA256:B65F40618F584303CA0BCF9B5F88C233CC4237699C0C4BF40BA8FACBE8195A46 | |||
| 6040 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Extreme.Injector.v3.7.3.-.by.master131.bak6040.9303 | compressed | |
MD5:90064F3C81022F4BEB1B660EA21F16C7 | SHA256:93DDA8B91586ACF53C70DFD3F512FCFF5793A9AF69E174D7E3AD67190361BCE8 | |||
| 6040 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\__rar_6040.9284 | compressed | |
MD5:61A1A6ECE84DECA49E7FFFF70027CBA7 | SHA256:E44CBA0CF21C07A44C479B041E6DA7FD85023F1075AB1138C2A85C933EAF75B6 | |||
| 7748 | Extreme Injector v3.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6040.8031\settings.xml | xml | |
MD5:B61590C0DEC6FE49D81BFD170E3D43CD | SHA256:CBCE641937EF6CB0664FD6E46A005BA3036D6A7168A7C28CF8912BBBBE39A850 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
20
DNS requests
13
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7964 | SIHClient.exe | GET | 200 | 23.218.209.163:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 407 b | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
7964 | SIHClient.exe | GET | 200 | 23.218.209.163:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
— | — | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 20.7.2.167:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6544 | svchost.exe | 20.190.160.132:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
raw.githubusercontent.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |