| File name: | ScannerInstallationAssistant.exe |
| Full analysis: | https://app.any.run/tasks/c410ac71-5f44-4094-b028-4dad48b129b9 |
| Verdict: | Malicious activity |
| Analysis date: | August 13, 2019, 14:49:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 0D4F5FF4C29619EE92DF0AEBC885871B |
| SHA1: | 44F8B4CE62BCE297CB82A028257D4D6DB2CAB8CC |
| SHA256: | 93C1DB9260A12FDB7D9A3F75DAB4682A9EAAC86037CE9B0567FB7A2E85DF3037 |
| SSDEEP: | 12288:4utPrtlDAs3WLOAjMJa+QaAnuID7hzwy6W9skHWobUCTDh/jhCQ:5tz3DAs3WLOAAs+Q3v7hvpskHWobFZ7Z |
MALICIOUS
Runs PING.EXE for delay simulation
- cmd.exe (PID: 3888)
- cmd.exe (PID: 2324)
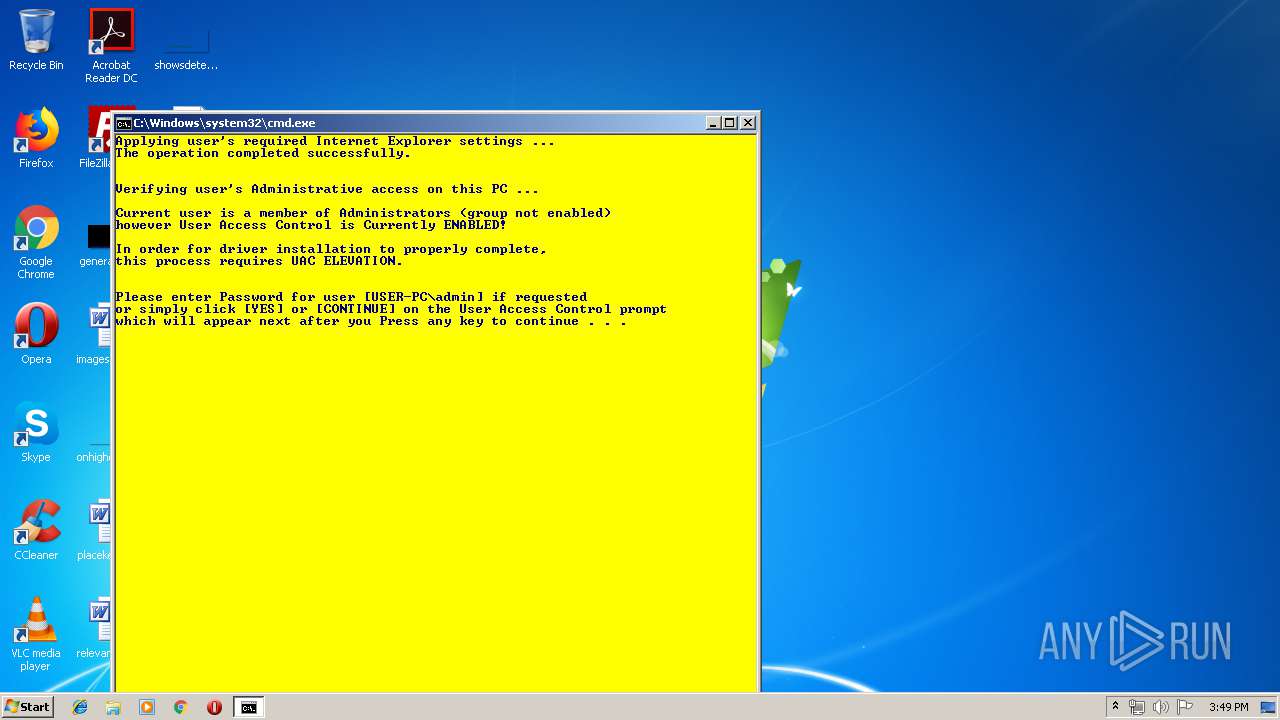
Changes internet zones settings
- reg.exe (PID: 284)
- reg.exe (PID: 3460)
Application was dropped or rewritten from another process
- IsAdmin.exe (PID: 3512)
- IsAdmin.exe (PID: 3144)
- Elevate32.exe (PID: 2392)
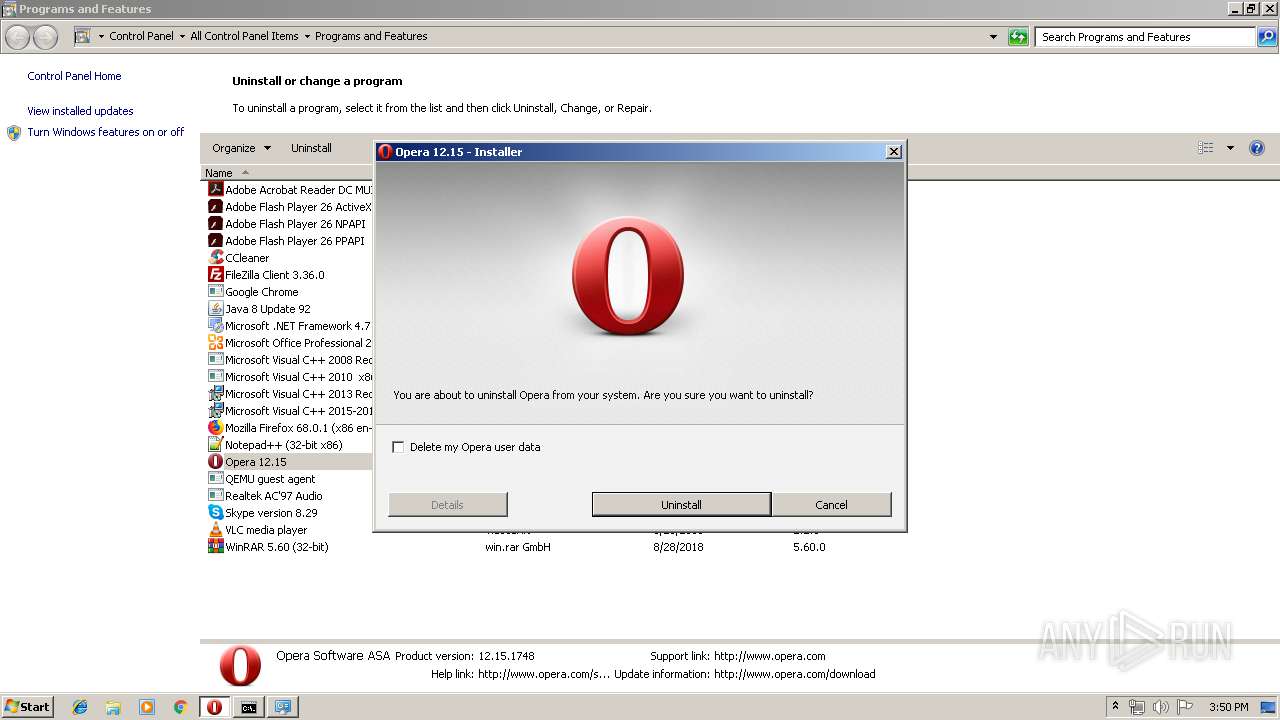
Renames files like Ransomware
- Opera.exe (PID: 356)
SUSPICIOUS
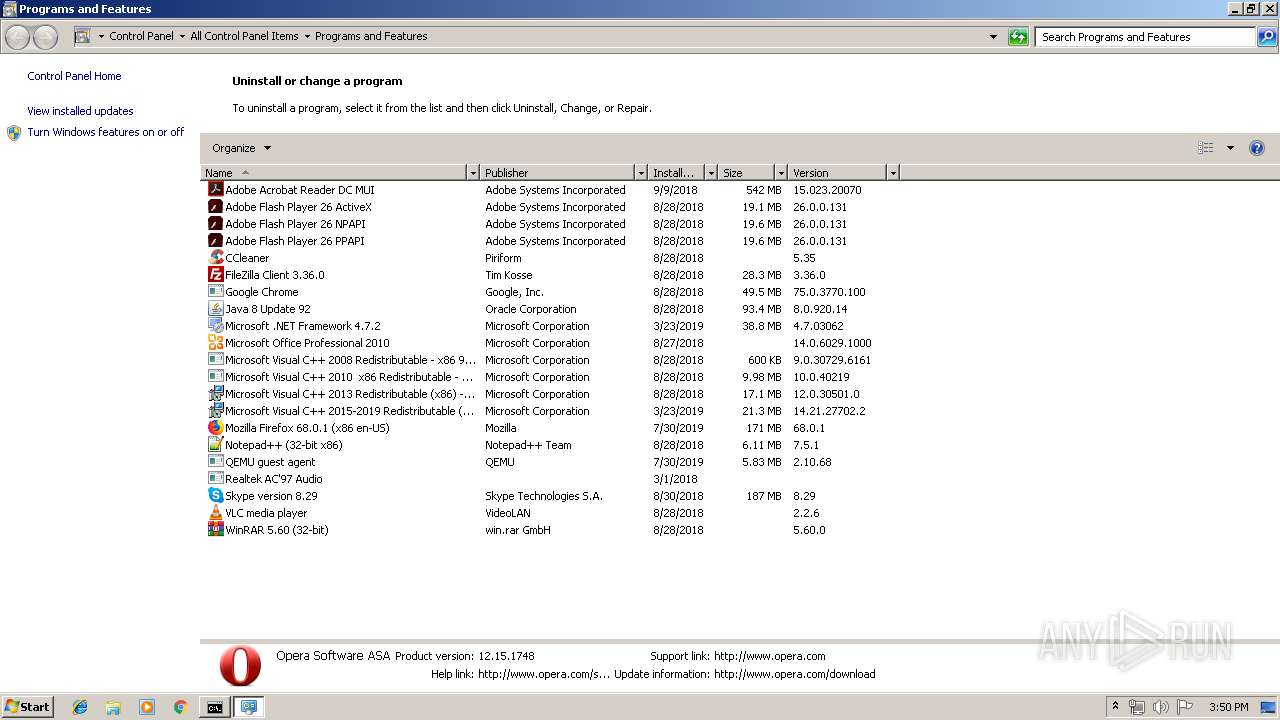
Executable content was dropped or overwritten
- ScannerInstallationAssistant.exe (PID: 2948)
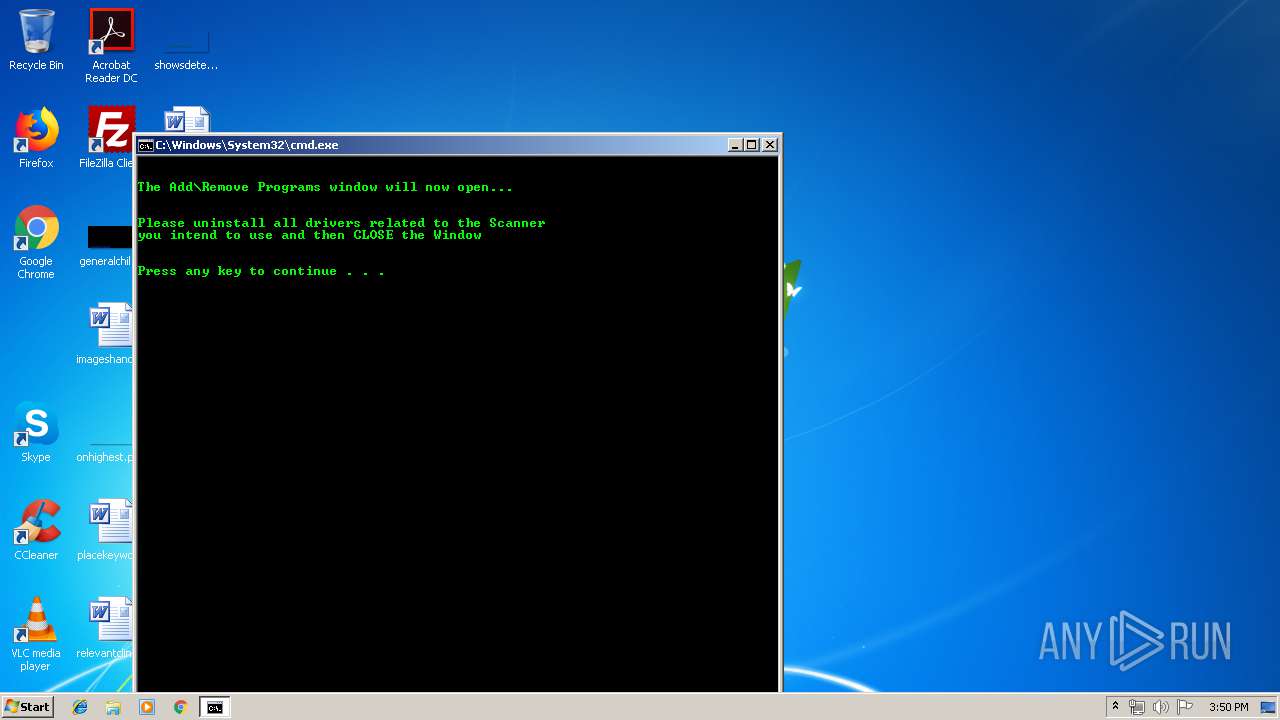
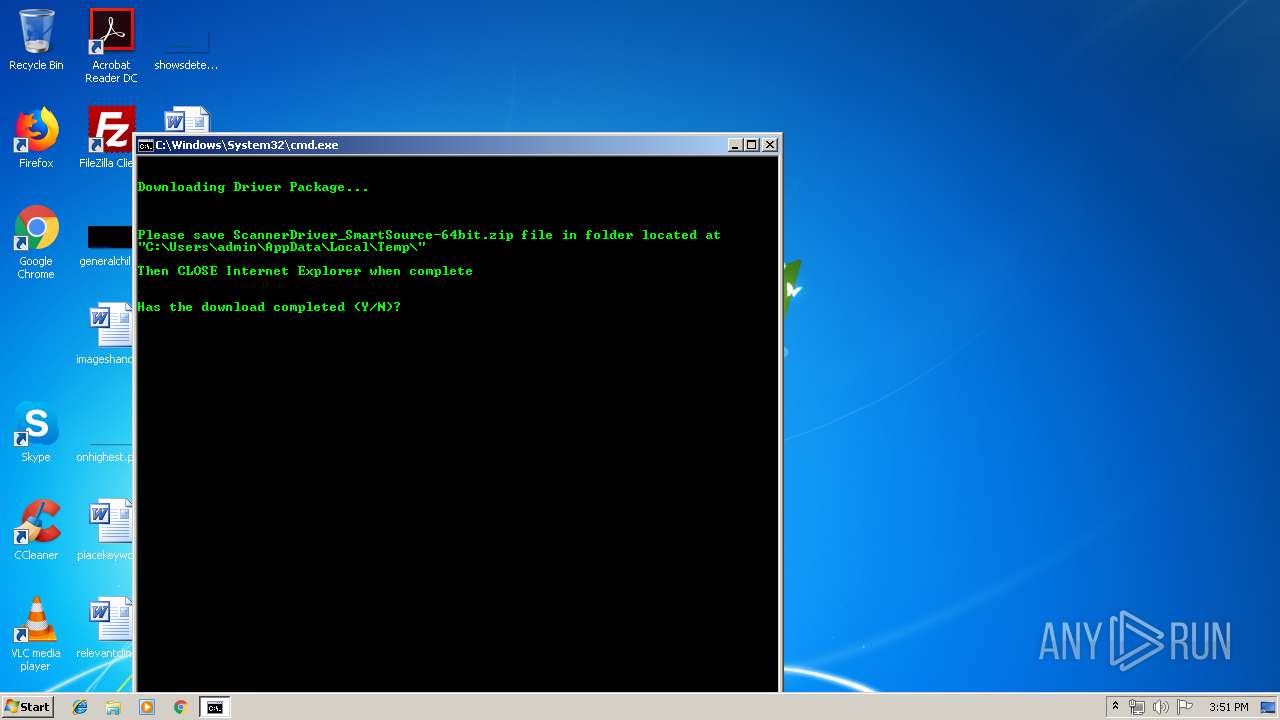
Starts CMD.EXE for commands execution
- ScannerInstallationAssistant.exe (PID: 2948)
- Opera.exe (PID: 356)
- Elevate32.exe (PID: 2392)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3888)
- cmd.exe (PID: 2324)
Creates files in the program directory
- Opera.exe (PID: 356)
Uses RUNDLL32.EXE to load library
- control.exe (PID: 284)
Executed via COM
- DllHost.exe (PID: 3464)
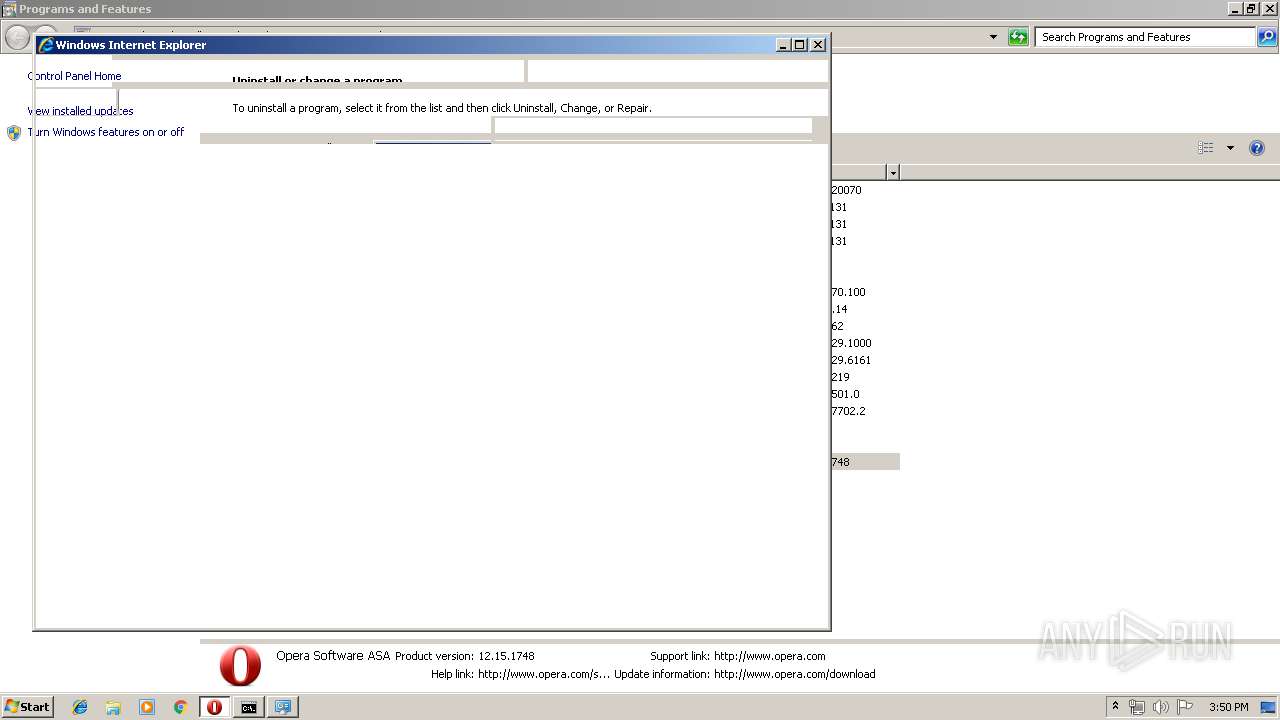
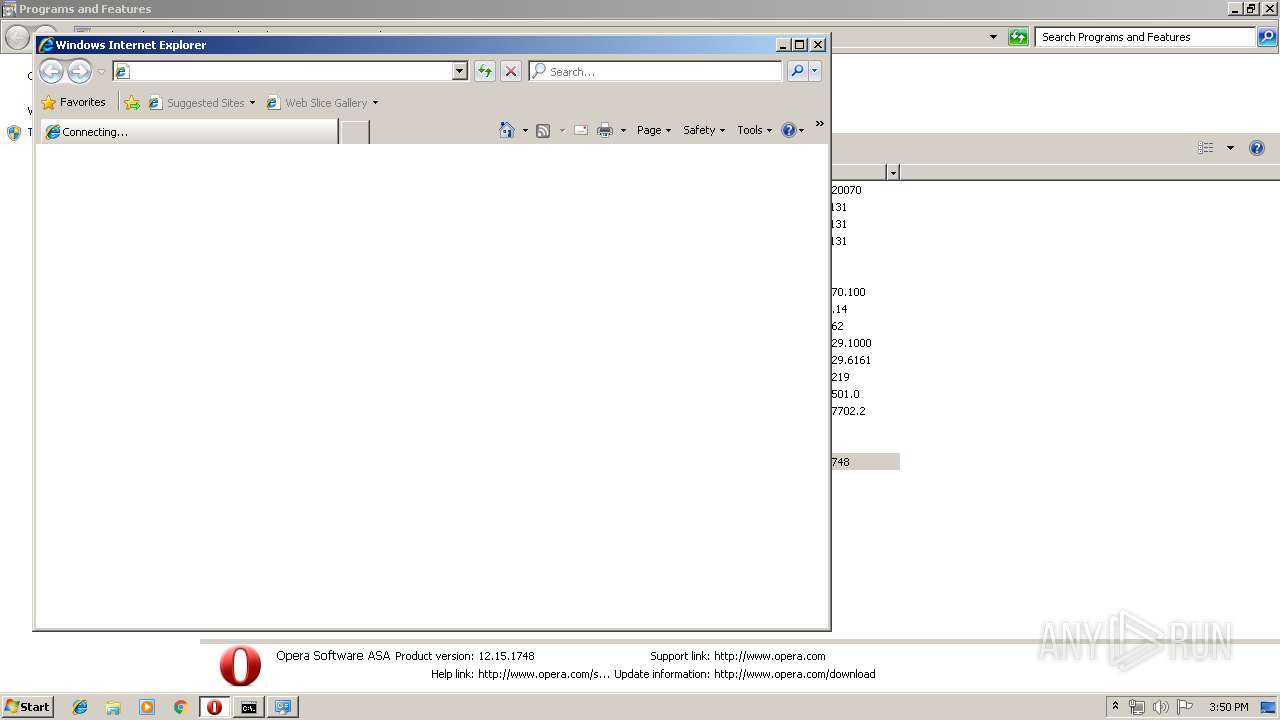
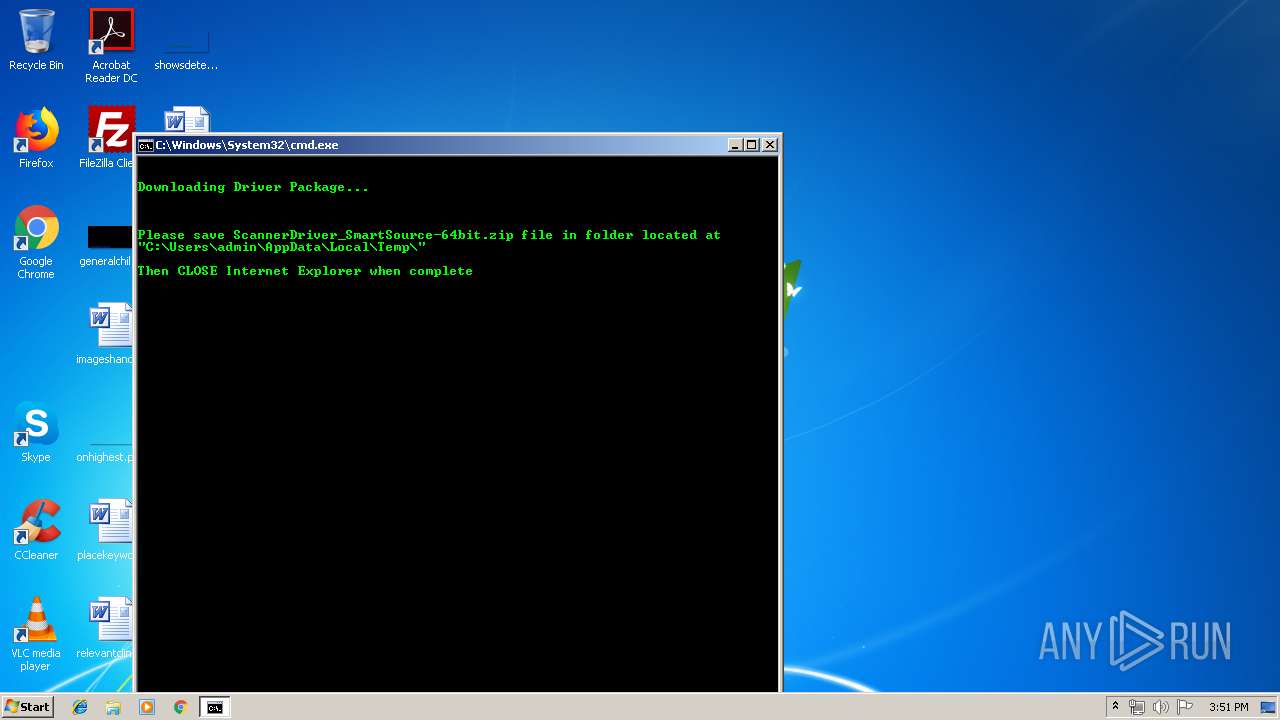
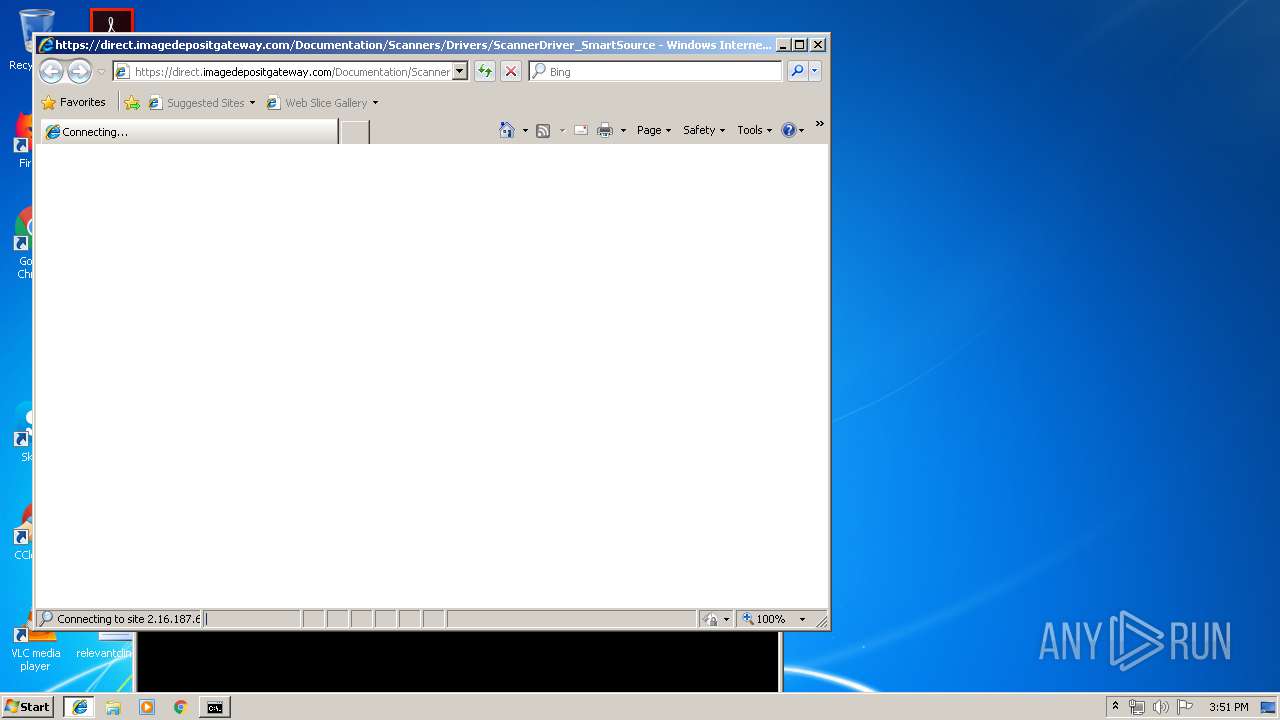
Starts Internet Explorer
- Opera.exe (PID: 356)
- cmd.exe (PID: 2324)
INFO
Application launched itself
- iexplore.exe (PID: 2916)
Changes internet zones settings
- iexplore.exe (PID: 2916)
- iexplore.exe (PID: 3652)
Creates files in the user directory
- Opera.exe (PID: 356)
- iexplore.exe (PID: 1996)
Reads Internet Cache Settings
- iexplore.exe (PID: 1996)
- iexplore.exe (PID: 3664)
Reads internet explorer settings
- iexplore.exe (PID: 1996)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:03:15 07:27:58+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 49152 |
| InitializedDataSize: | 144896 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x913f |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Mar-2010 06:27:58 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 15-Mar-2010 06:27:58 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000BE8F | 0x0000C000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.52204 |
.rdata | 0x0000D000 | 0x00001855 | 0x00001A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.17849 |
.data | 0x0000F000 | 0x00019CB8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.31023 |
.CRT | 0x00029000 | 0x00000010 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.213101 |
.rsrc | 0x0002A000 | 0x0002178C | 0x00021800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.54973 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.20816 | 1464 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.10942 | 1640 | Latin 1 / Western European | Process Default Language | RT_ICON |
3 | 3.85288 | 744 | Latin 1 / Western European | Process Default Language | RT_ICON |
4 | 3.76144 | 488 | Latin 1 / Western European | Process Default Language | RT_ICON |
5 | 3.09167 | 296 | Latin 1 / Western European | Process Default Language | RT_ICON |
6 | 7.982 | 35645 | Latin 1 / Western European | Process Default Language | RT_ICON |
7 | 3.24143 | 556 | Latin 1 / Western European | English - United States | RT_STRING |
8 | 3.28574 | 946 | Latin 1 / Western European | English - United States | RT_STRING |
9 | 3.04375 | 530 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 3.15563 | 638 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
68
Monitored processes
24
Malicious processes
6
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
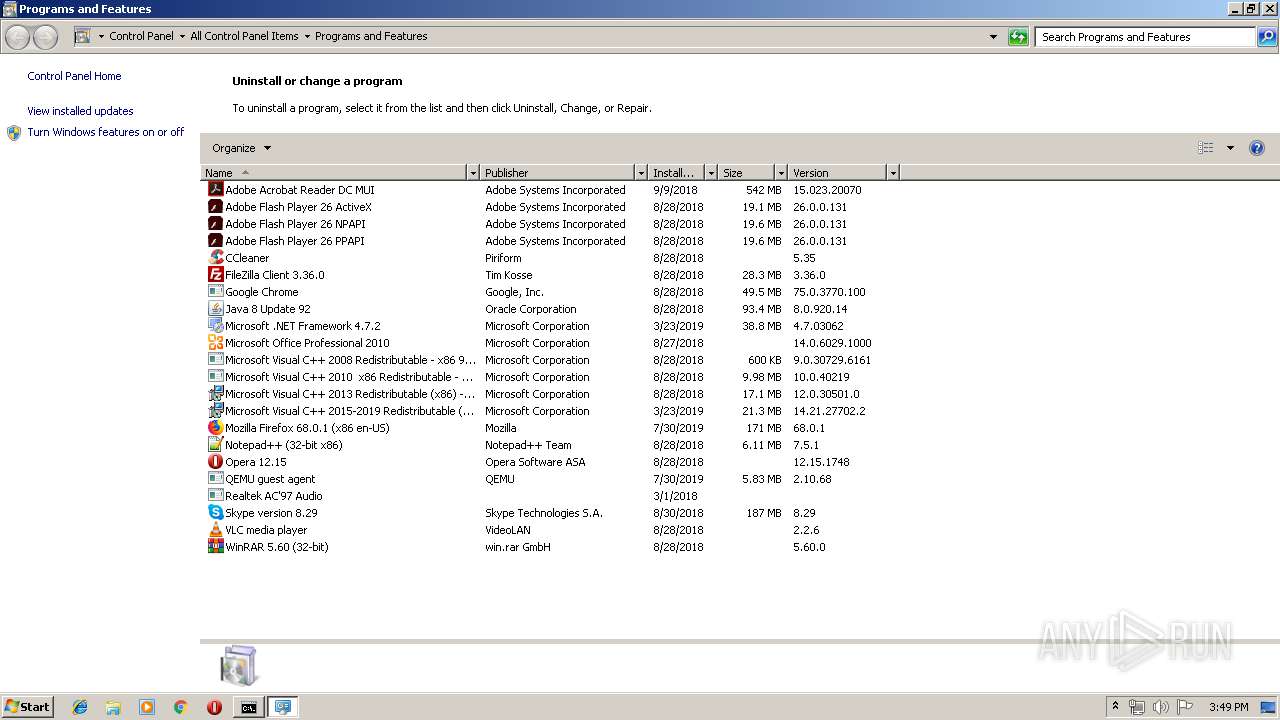
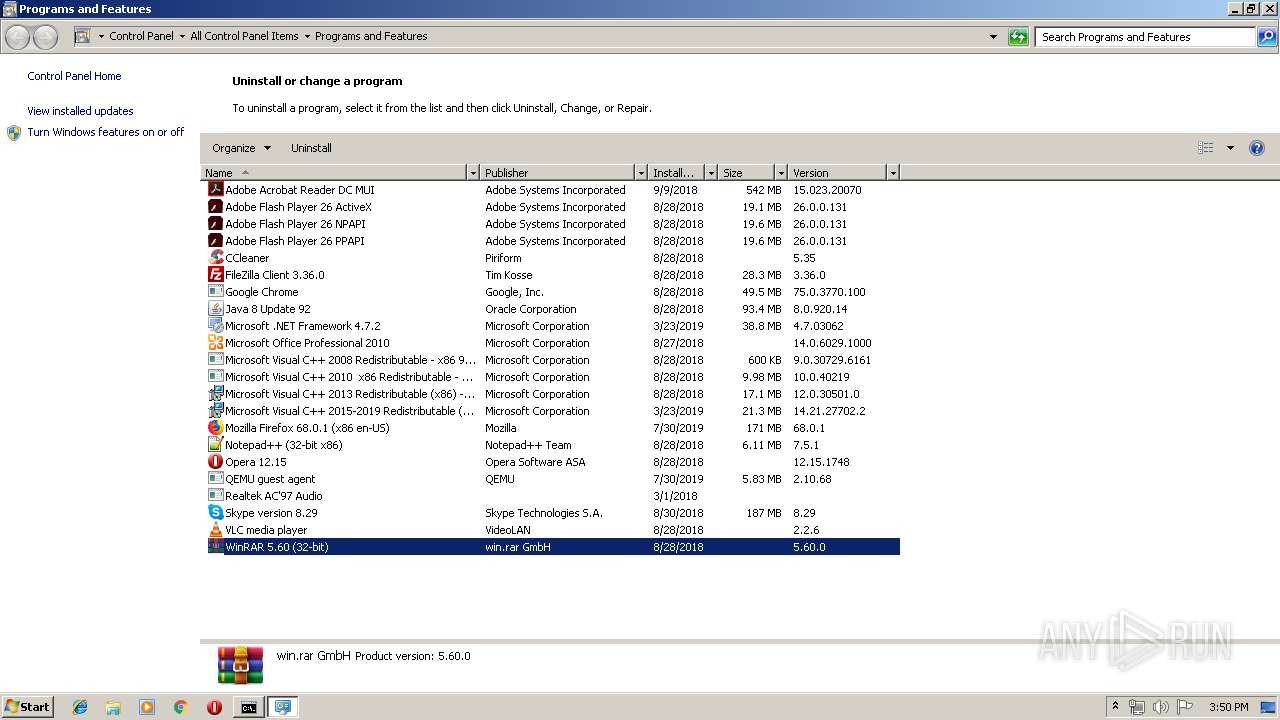
| 284 | "C:\Windows\System32\control.exe" "C:\Windows\system32\appwiz.cpl", | C:\Windows\System32\control.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Control Panel Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 284 | REG IMPORT "C:\Users\admin\AppData\Local\Temp\\IntConf.reg" | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 356 | "C:\Program Files\Opera\Opera.exe" /uninstall | C:\Program Files\Opera\Opera.exe | — | DllHost.exe | |||||||||||
User: admin Company: Opera Software Integrity Level: HIGH Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 1996 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2916 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2284 | ping 127.0.0.1 -n 3 -w 500 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
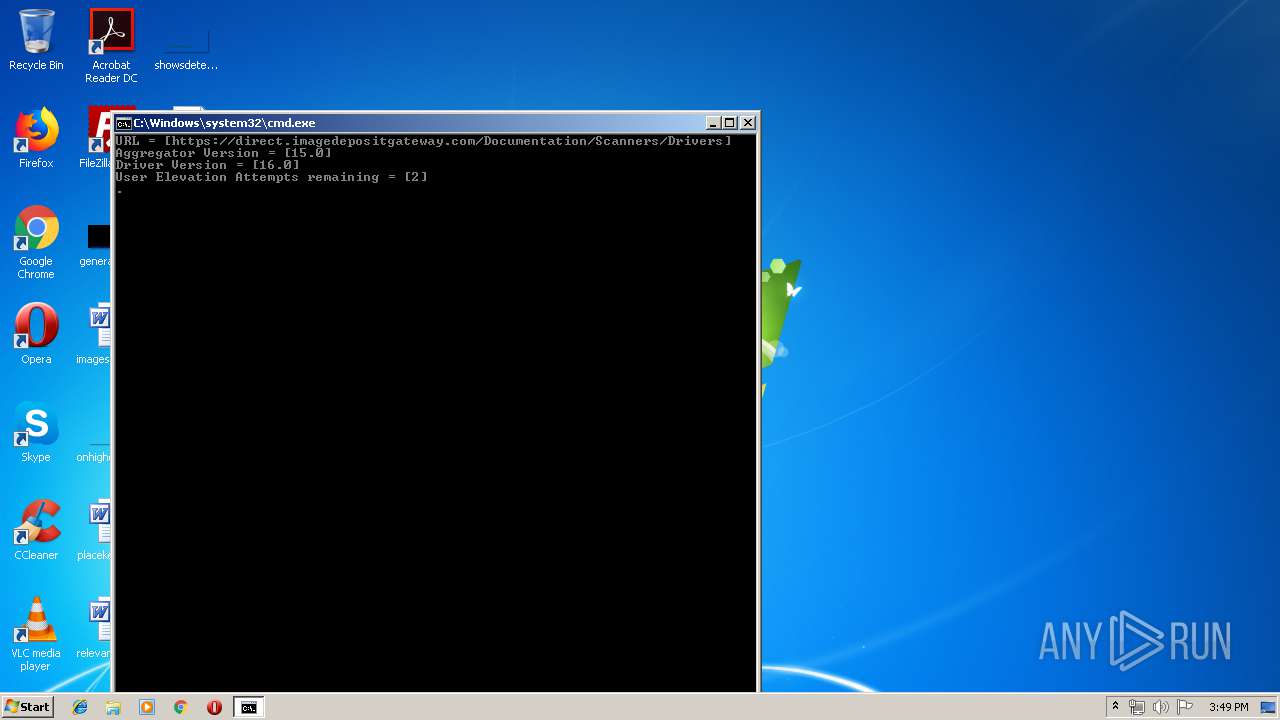
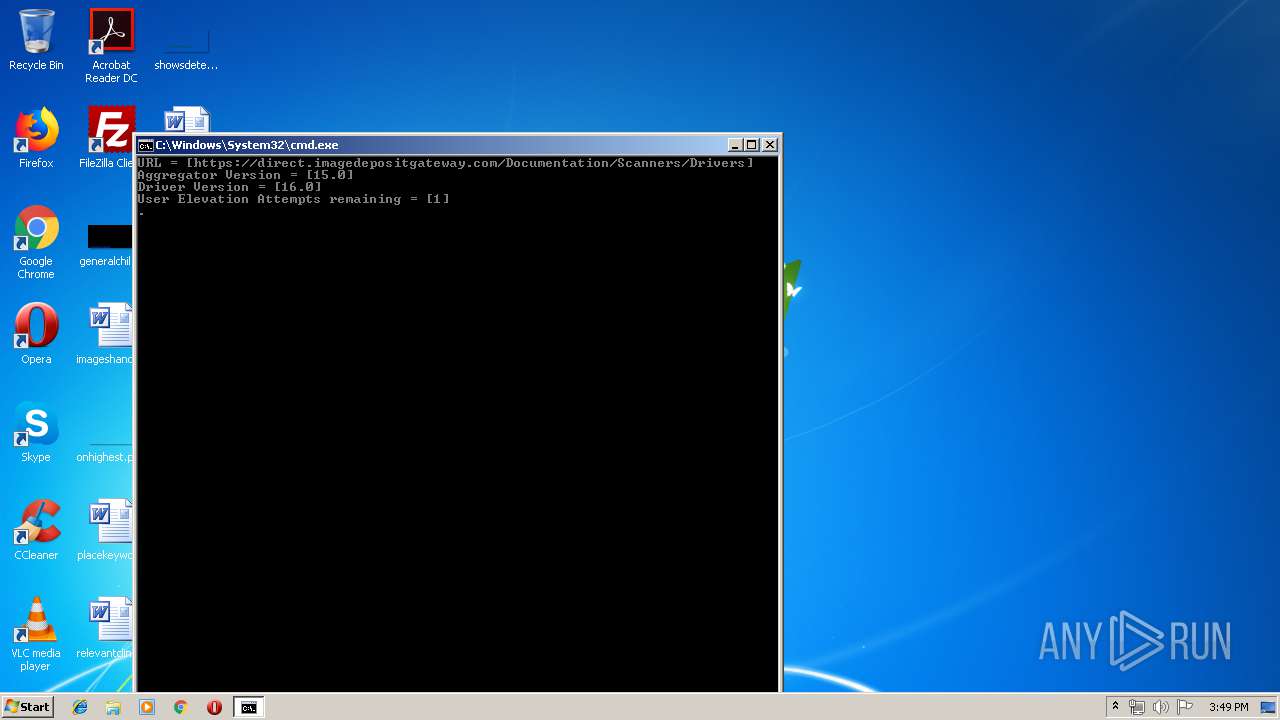
| 2324 | "C:\Windows\System32\cmd.exe" /C "C:\Users\admin\AppData\Local\Temp\InstallAssist.bat" https://direct.imagedepositgateway.com/Documentation/Scanners/Drivers 16.0 15.0 1 | C:\Windows\System32\cmd.exe | Elevate32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2392 | "C:\Users\admin\AppData\Local\Temp\\Elevate32.exe" -q -- "C:\Users\admin\AppData\Local\Temp\InstallAssist.bat" https://direct.imagedepositgateway.com/Documentation/Scanners/Drivers 16.0 15.0 1 | C:\Users\admin\AppData\Local\Temp\Elevate32.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Runs a program elevated Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2500 | cmd /c ""C:\Program Files\Opera\k.bat" " | C:\Windows\system32\cmd.exe | — | Opera.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2644 | mode con: cols=80 lines=50 | C:\Windows\system32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: DOS Device MODE Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2708 | REG.exe QUERY HKLM\Hardware\Description\System\CentralProcessor\0 /v Identifier | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 157
Read events
1 785
Write events
358
Delete events
14
Modification events
| (PID) Process: | (2948) ScannerInstallationAssistant.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2948) ScannerInstallationAssistant.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (284) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap\Domains\imagedepositgateway.com\* |
| Operation: | write | Name: | https |
Value: 2 | |||
| (PID) Process: | (284) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\2 |
| Operation: | write | Name: | CurrentLevel |
Value: 0 | |||
| (PID) Process: | (284) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\2 |
| Operation: | write | Name: | 1001 |
Value: 0 | |||
| (PID) Process: | (284) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\2 |
| Operation: | write | Name: | 1206 |
Value: 0 | |||
| (PID) Process: | (284) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\2 |
| Operation: | write | Name: | 1209 |
Value: 0 | |||
| (PID) Process: | (284) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\2 |
| Operation: | write | Name: | 1406 |
Value: 0 | |||
| (PID) Process: | (284) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\2 |
| Operation: | write | Name: | 1407 |
Value: 0 | |||
| (PID) Process: | (284) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\2 |
| Operation: | write | Name: | 1409 |
Value: 3 | |||
Executable files
3
Suspicious files
11
Text files
23
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 356 | Opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprC6A0.tmp | — | |
MD5:— | SHA256:— | |||
| 356 | Opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\operaprefs.ini | — | |
MD5:— | SHA256:— | |||
| 356 | Opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opssl6.dat | — | |
MD5:— | SHA256:— | |||
| 356 | Opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opcert6.dat | — | |
MD5:— | SHA256:— | |||
| 356 | Opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprC6C0.tmp | — | |
MD5:— | SHA256:— | |||
| 2948 | ScannerInstallationAssistant.exe | C:\Users\admin\AppData\Local\Temp\IntConf.reg | text | |
MD5:— | SHA256:— | |||
| 2948 | ScannerInstallationAssistant.exe | C:\Users\admin\AppData\Local\Temp\InstallAssist.bat | text | |
MD5:— | SHA256:— | |||
| 356 | Opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\revocation\oprC6D1.tmp | — | |
MD5:— | SHA256:— | |||
| 2948 | ScannerInstallationAssistant.exe | C:\Users\admin\AppData\Local\Temp\IsAdmin.exe | executable | |
MD5:7A3373F22EEC15834DEC404C6B2794BB | SHA256:102F1FB98A7AB61B63C7857E1273D225D422385E054F7F64241508A65C30C8F4 | |||
| 2948 | ScannerInstallationAssistant.exe | C:\Users\admin\AppData\Local\Temp\7za.exe | executable | |
MD5:42BADC1D2F03A8B1E4875740D3D49336 | SHA256:C136B1467D669A725478A6110EBAAAB3CB88A3D389DFA688E06173C066B76FCF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
12
DNS requests
11
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
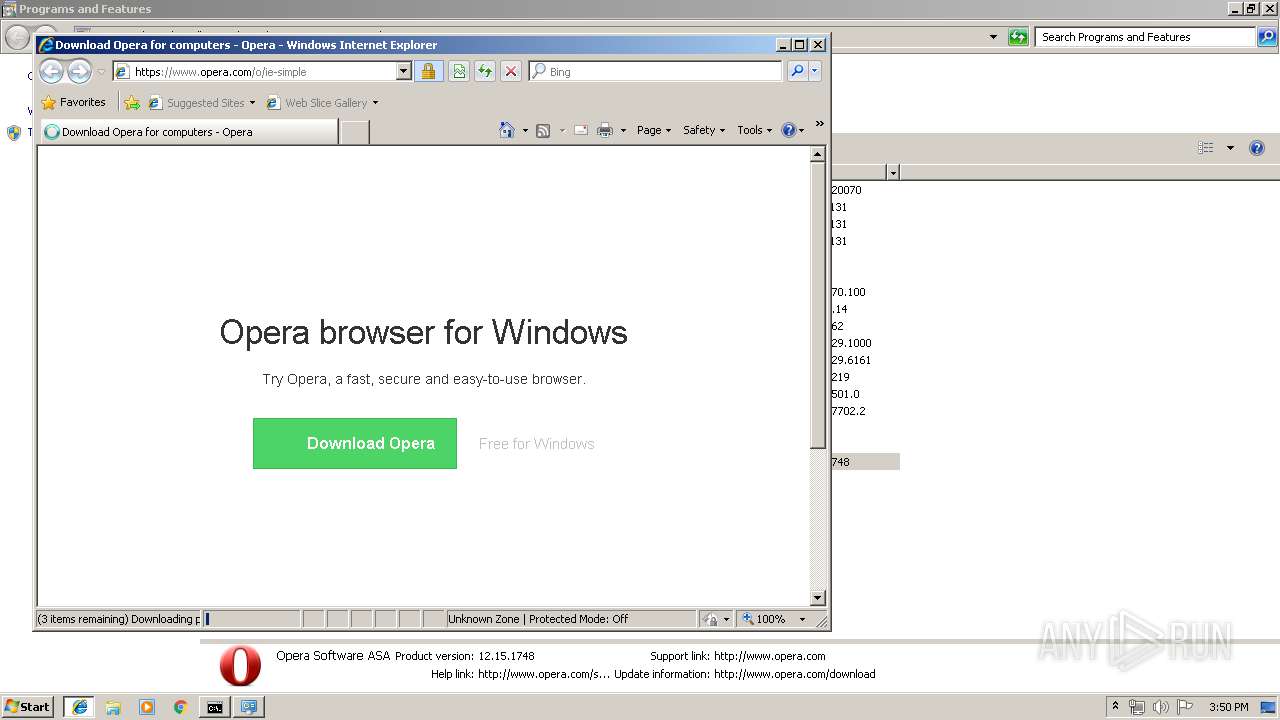
1996 | iexplore.exe | GET | 301 | 18.197.61.146:80 | http://www.opera.com/client/upgraded/ | DE | html | 334 b | whitelisted |
1996 | iexplore.exe | GET | 302 | 185.26.182.109:80 | http://redir.opera.com/uninstallsurvey/?version=12.15.1748&firstruntime=1535456794 | unknown | html | 283 b | whitelisted |
2916 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1996 | iexplore.exe | 185.26.182.109:80 | redir.opera.com | Opera Software AS | — | unknown |
2916 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1996 | iexplore.exe | 18.197.61.146:80 | www.opera.com | Amazon.com, Inc. | DE | unknown |
1996 | iexplore.exe | 18.197.61.146:443 | www.opera.com | Amazon.com, Inc. | DE | unknown |
1996 | iexplore.exe | 216.58.208.46:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
1996 | iexplore.exe | 185.60.216.19:443 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
1996 | iexplore.exe | 77.88.21.119:443 | mc.yandex.ru | YANDEX LLC | RU | whitelisted |
1996 | iexplore.exe | 147.75.32.75:443 | static.hotjar.com | Packet Host, Inc. | US | unknown |
3664 | iexplore.exe | 2.16.187.64:443 | direct.imagedepositgateway.com | Akamai International B.V. | — | whitelisted |
1996 | iexplore.exe | 172.217.22.40:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
redir.opera.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.opera.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
static.hotjar.com |
| whitelisted |
connect.facebook.net |
| whitelisted |
mc.yandex.ru |
| whitelisted |
direct.imagedepositgateway.com |
| suspicious |