| File name: | 93aed254d2ed40b308e1236a0686fa02229e124b86efe1e7eddcac8f0bcaed07.exe |
| Full analysis: | https://app.any.run/tasks/7244601d-9049-47f2-ab7f-026f627dda72 |
| Verdict: | Malicious activity |
| Analysis date: | June 27, 2022, 12:51:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 7A330F121E03976F0B022CCCED19297B |
| SHA1: | B3935CC3E1A51AA7715A30F581EC735A369397EB |
| SHA256: | 93AED254D2ED40B308E1236A0686FA02229E124B86EFE1E7EDDCAC8F0BCAED07 |
| SSDEEP: | 6144:Z3VIjKDDMtZZZZZZZZZZZZZZZZZZZZZZ0hiwm:FVIjKDgqsT |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- 93aed254d2ed40b308e1236a0686fa02229e124b86efe1e7eddcac8f0bcaed07.exe (PID: 3700)
Reads the computer name
- 93aed254d2ed40b308e1236a0686fa02229e124b86efe1e7eddcac8f0bcaed07.exe (PID: 3700)
Executes application which crashes
- 93aed254d2ed40b308e1236a0686fa02229e124b86efe1e7eddcac8f0bcaed07.exe (PID: 3700)
INFO
Checks supported languages
- ntvdm.exe (PID: 2564)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| ProductVersion: | 38.45.27.68 |
|---|---|
| ProductName: | Full Version |
| OriginalFileName: | Full Version |
| LegalTrademarks: | Full Version |
| LegalCopyright: | Full Version |
| InternalName: | Full Version |
| FileVersion: | 41.34.22.68 |
| FileDescription: | Full Version |
| CompanyName: | Full Version |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT 32-bit |
| FileFlags: | Private build |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 38.45.27.68 |
| FileVersionNumber: | 41.34.22.68 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x6f7d |
| UninitializedDataSize: | - |
| InitializedDataSize: | 101888 |
| CodeSize: | 78336 |
| LinkerVersion: | 12 |
| PEType: | PE32 |
| TimeStamp: | 2017:06:10 12:10:06+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 10-Jun-2017 10:10:06 |
| Detected languages: |
|
| CompanyName: | Full Version |
| FileDescription: | Full Version |
| FileVersion: | 41.34.22.68 |
| InternalName: | Full Version |
| LegalCopyright: | Full Version |
| LegalTrademarks: | Full Version |
| OriginalFilename: | Full Version |
| ProductName: | Full Version |
| ProductVersion: | 38.45.27.68 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 10-Jun-2017 10:10:06 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001309F | 0x00013200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.58714 |
.rdata | 0x00015000 | 0x00006AEA | 0x00006C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.70468 |
.data | 0x0001C000 | 0x00003380 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.41497 |
.rsrc | 0x00020000 | 0x0000D718 | 0x0000D800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.63661 |
.reloc | 0x0002E000 | 0x00001470 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.365 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.39188 | 1144 | UNKNOWN | UNKNOWN | RT_MANIFEST |
111 | 5.06141 | 925 | UNKNOWN | UNKNOWN | RT_RIBBON_XML |
112 | 0.4689 | 1256 | UNKNOWN | UNKNOWN | RT_BITMAP |
121 | 2.83097 | 176 | UNKNOWN | UNKNOWN | RT_MENU |
125 | 2.30316 | 224 | UNKNOWN | Russian - Russia | RT_BITMAP |
127 | 5.41188 | 49197 | UNKNOWN | Russian - Russia | RT_HTML |
128 | 3.0495 | 156 | UNKNOWN | Russian - Russia | RT_DIALOG |
129 | 1.83876 | 20 | UNKNOWN | Russian - Russia | RT_GROUP_CURSOR |
Imports
KERNEL32.dll |
USER32.dll |
ole32.dll |
Total processes
41
Monitored processes
3
Malicious processes
0
Suspicious processes
0
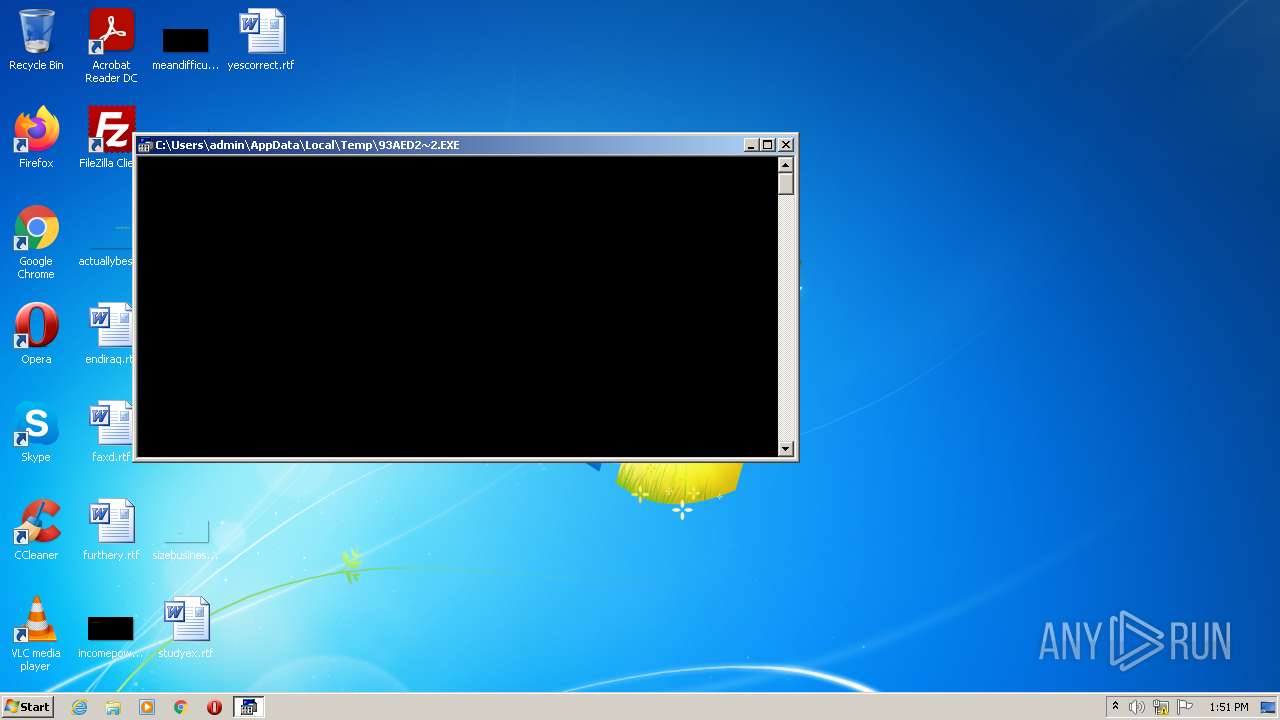
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1780 | "C:\Users\admin\AppData\Local\Temp\93aed254d2ed40b308e1236a0686fa02229e124b86efe1e7eddcac8f0bcaed07.exe" | C:\Users\admin\AppData\Local\Temp\93aed254d2ed40b308e1236a0686fa02229e124b86efe1e7eddcac8f0bcaed07.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Full Version Integrity Level: MEDIUM Description: Full Version Exit code: 3221226540 Version: 41.34.22.68 Modules
| |||||||||||||||
| 2564 | "C:\Windows\system32\ntvdm.exe" -i1 | C:\Windows\system32\ntvdm.exe | — | 93aed254d2ed40b308e1236a0686fa02229e124b86efe1e7eddcac8f0bcaed07.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: NTVDM.EXE Exit code: 3221225477 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3700 | "C:\Users\admin\AppData\Local\Temp\93aed254d2ed40b308e1236a0686fa02229e124b86efe1e7eddcac8f0bcaed07.exe" | C:\Users\admin\AppData\Local\Temp\93aed254d2ed40b308e1236a0686fa02229e124b86efe1e7eddcac8f0bcaed07.exe | Explorer.EXE | ||||||||||||
User: admin Company: Full Version Integrity Level: HIGH Description: Full Version Exit code: 0 Version: 41.34.22.68 Modules
| |||||||||||||||
Total events
985
Read events
955
Write events
30
Delete events
0
Modification events
| (PID) Process: | (3700) 93aed254d2ed40b308e1236a0686fa02229e124b86efe1e7eddcac8f0bcaed07.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3700) 93aed254d2ed40b308e1236a0686fa02229e124b86efe1e7eddcac8f0bcaed07.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3700) 93aed254d2ed40b308e1236a0686fa02229e124b86efe1e7eddcac8f0bcaed07.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3700) 93aed254d2ed40b308e1236a0686fa02229e124b86efe1e7eddcac8f0bcaed07.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3700) 93aed254d2ed40b308e1236a0686fa02229e124b86efe1e7eddcac8f0bcaed07.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3700) 93aed254d2ed40b308e1236a0686fa02229e124b86efe1e7eddcac8f0bcaed07.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3700) 93aed254d2ed40b308e1236a0686fa02229e124b86efe1e7eddcac8f0bcaed07.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3700) 93aed254d2ed40b308e1236a0686fa02229e124b86efe1e7eddcac8f0bcaed07.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3700) 93aed254d2ed40b308e1236a0686fa02229e124b86efe1e7eddcac8f0bcaed07.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3700) 93aed254d2ed40b308e1236a0686fa02229e124b86efe1e7eddcac8f0bcaed07.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\{362E934C-743B-4588-8259-D2482DB771A8} |
| Operation: | write | Name: | WpadDecisionReason |
Value: 1 | |||
Executable files
0
Suspicious files
0
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3700 | 93aed254d2ed40b308e1236a0686fa02229e124b86efe1e7eddcac8f0bcaed07.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\3EIXY1MR.htm | html | |
MD5:— | SHA256:— | |||
| 3700 | 93aed254d2ed40b308e1236a0686fa02229e124b86efe1e7eddcac8f0bcaed07.exe | C:\Users\admin\AppData\Local\Temp\93aed254d2ed40b308e1236a0686fa02229e124b86efe1e7eddcac8f0bcaed07(H).exe | html | |
MD5:— | SHA256:— | |||
| 2564 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs570B.tmp | text | |
MD5:8CF6DDB5AA59B49F34B967CD46F013B6 | SHA256:EE06792197C3E025B84860A72460EAF628C66637685F8C52C5A08A9CC35D376C | |||
| 2564 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scs571C.tmp | text | |
MD5:4C361DEA398F7AEEF49953BDC0AB4A9B | SHA256:06D61C23E6CA59B9DDAD1796ECCC42C032CD8F6F424AF6CFEE5D085D36FF7DFD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3700 | 93aed254d2ed40b308e1236a0686fa02229e124b86efe1e7eddcac8f0bcaed07.exe | GET | 200 | 185.53.178.7:80 | http://discriminate.blockey.ru/gGF5FCOwVRPsERIZAXXFxEeJUFaJRWBFQBNk0EQNFUahADWFlWa4RDe0zKUNkQHJlTOxBFf0hJbMAO5wUQZ5USfoBEP4wAGIAMTIBArMzWIRUBUMwDJdVMdcQHERSTLBFWSR0FLEUTVRUQaEwUIQVQCY1VDhlCWMVVC5kVIoVEEh1WoEBBDVSCJowVFIwEIsgDFAhEKExDNEwBQgFDQkFAdMUJLpzUJMwEPQEVP1QEfgQALYBCWoxHwMhEAsyMbhERFQxAPk0Vx0BEAQEJNtEUYJFRXsQQNVFRBpRAThAVBJgVXNEWKYxUVJkTWhgWRQEWbhSEEMUJJkgCXVgATgwCOUAESoQEP0QAHABWMARWA0xQlskOTlwAT8ARU9EHbIxEagBDZ0zEQwwKrEEWOtlXEVwCCgzDFwBDMcANfIhG7IDQYRlBEUBToEgFHgkGOYRCIwxDAggWOwQAJkgABo1RCBwBGMQQMEASRtkRKZlXfBkWBlVVApUSfFQEZNzWokFBY0ADEN1WechB5oACfYgDLExC7oABXkCMWhVQdwBGLpDHLklHC0QDCUgFF1BAYoABP0BBMcQHHsFMWhDXZ0wAPUEXMRQGVQDFVsQADcwEpggEXwzKOV1UQ5lTG1VRfsgB28BCZYRFIwABrkSTYxUUMplSUJFXNZUXFJwCIoxKAsRFbgQADIRKwYFWBx0XOxVUctUQeVEXMlAArAwGVsBCBMgEpAjVYZQAe0gXEJwFeswEDkgMaoRSUZlSBwlWFFEDHFxUQ8lTVNACbYhXeB1XLoQQYlxRAVAXbZFTNpxEKcwMcQxHdYSGOYwCBkwSYtlQWxBFUYxKYYQFZwAEOVlRVxASPZFUF0FCZBBWPVEHF8wAN9UWFJBAB9FGX9FCI5URdREAKAwB00BBAAhMM0xFCsBE8MRBLsARFlUTFJgFXkhNaIQGZYBAyUQHEAgVYJlTOJhCPUgJQkgDCEgDHEBNPExF74xCrw0AVEwFGUwDGpkWDVVCI8QHfwgA08hGQAgABoxEw8hGKgxMDhwBc0QBOEBRCx1UWBgFdUxOJcAAa4wBr8QFZ0xOVAgJNtgBToxHAIQSUZVTCgQAWA0VC1UVGhQSBEFWIFBBFUQXVxVQOoRQAd1XbZFTNlxGHoRDLYkSLhUVdVEFLsxSYtlQWtEAE0jFDwhVYFERONkRCAgJVIBFEJECaghCe40WUQAGGNBDGsRBWBUSUZVUL5UXFNAFEohVHpFBMABCRYFTNFBBaAgTVZ0RMsgEvckEdgQHVcCWQgxCBwwAZsCVfAQFeoDRGlEASwyRR9VXbRFGd0RDNEwCAMyTEEiBakRLGx1ScohBJQkQPxADOYlFNpEXMRkDKAgGGYgHWARS10hFIsACZIQDbdTDGcFHIYhGT0hBbchWd1RBJUwFAgwAJJjQ140GMAQEGdFQYQgGWhlUNpVQeRUDQQQRcojZu1Wa0tGe0lHZtJGd29Gd0NGdslHZmlWe3d2Z | DE | html | 2.49 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3700 | 93aed254d2ed40b308e1236a0686fa02229e124b86efe1e7eddcac8f0bcaed07.exe | 185.53.178.7:80 | discriminate.blockey.ru | Team Internet AG | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
discriminate.blockey.ru |
| malicious |