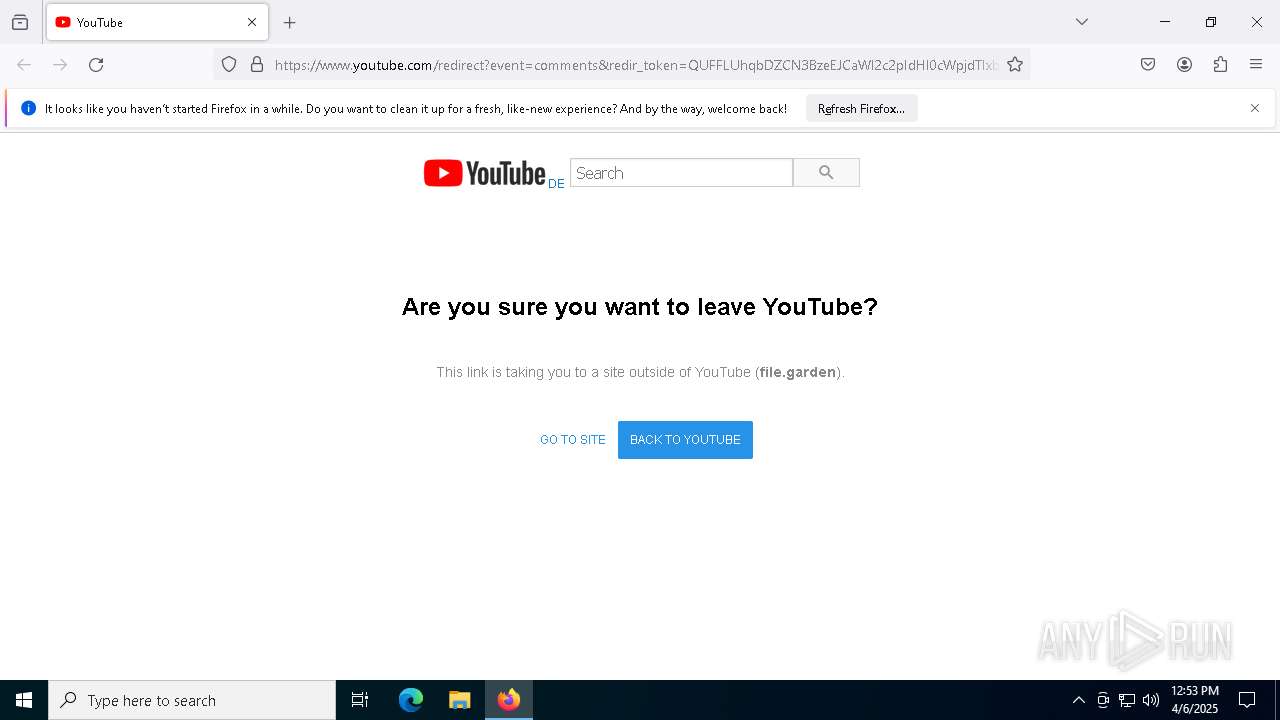
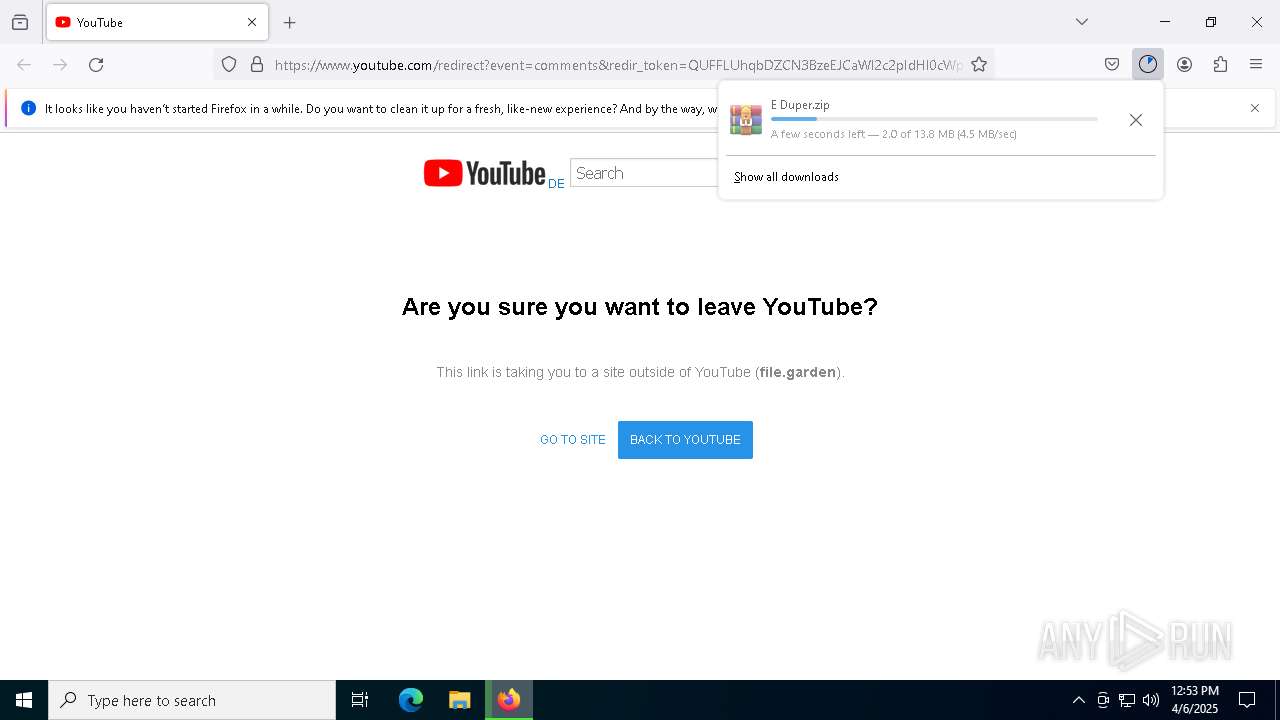
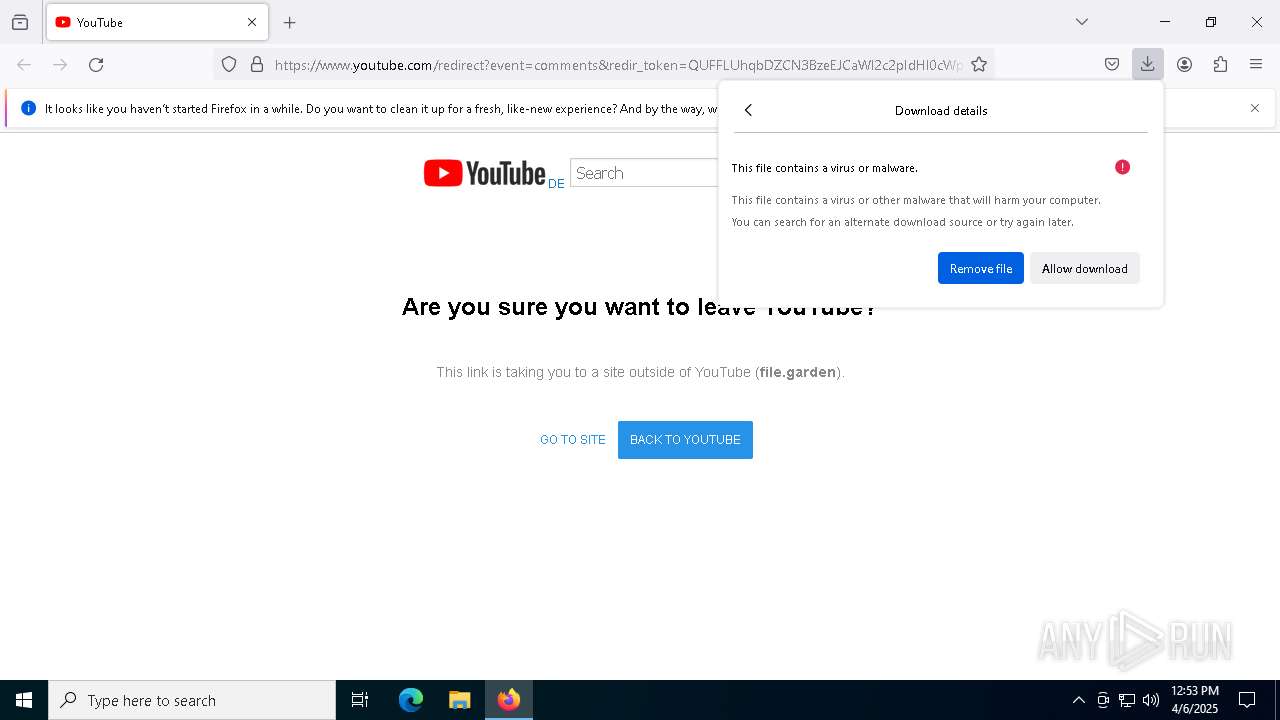
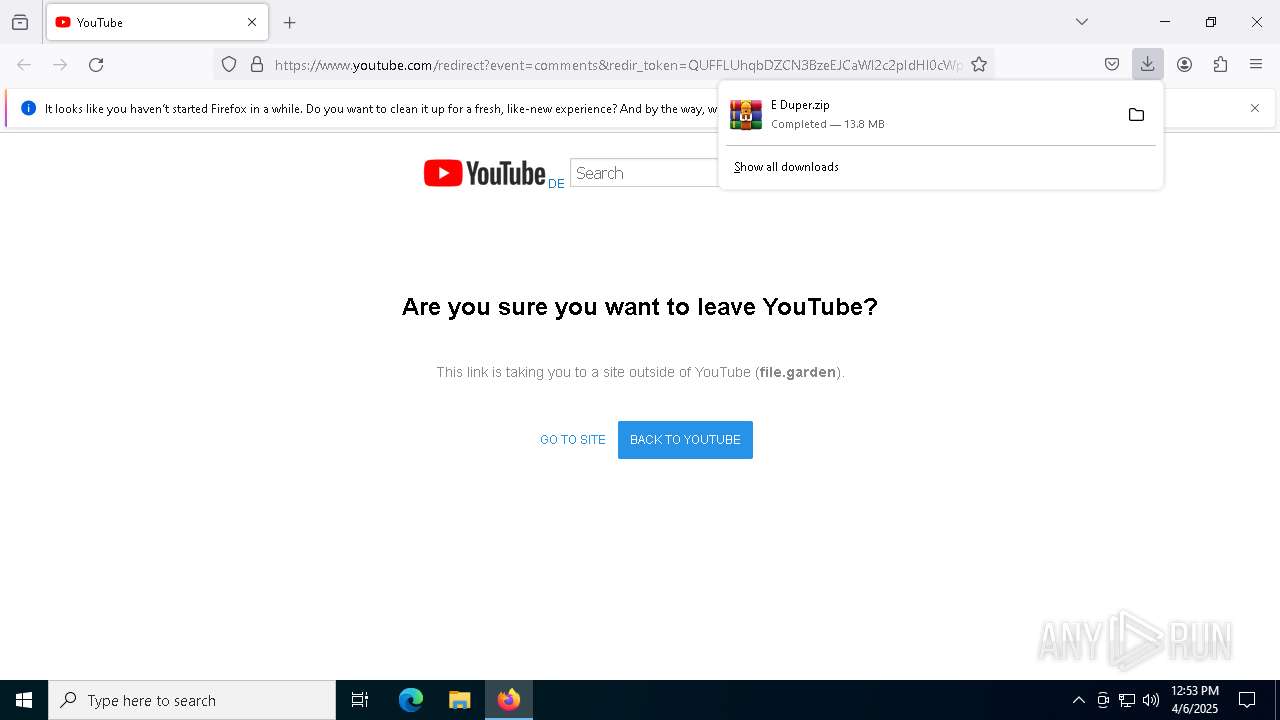
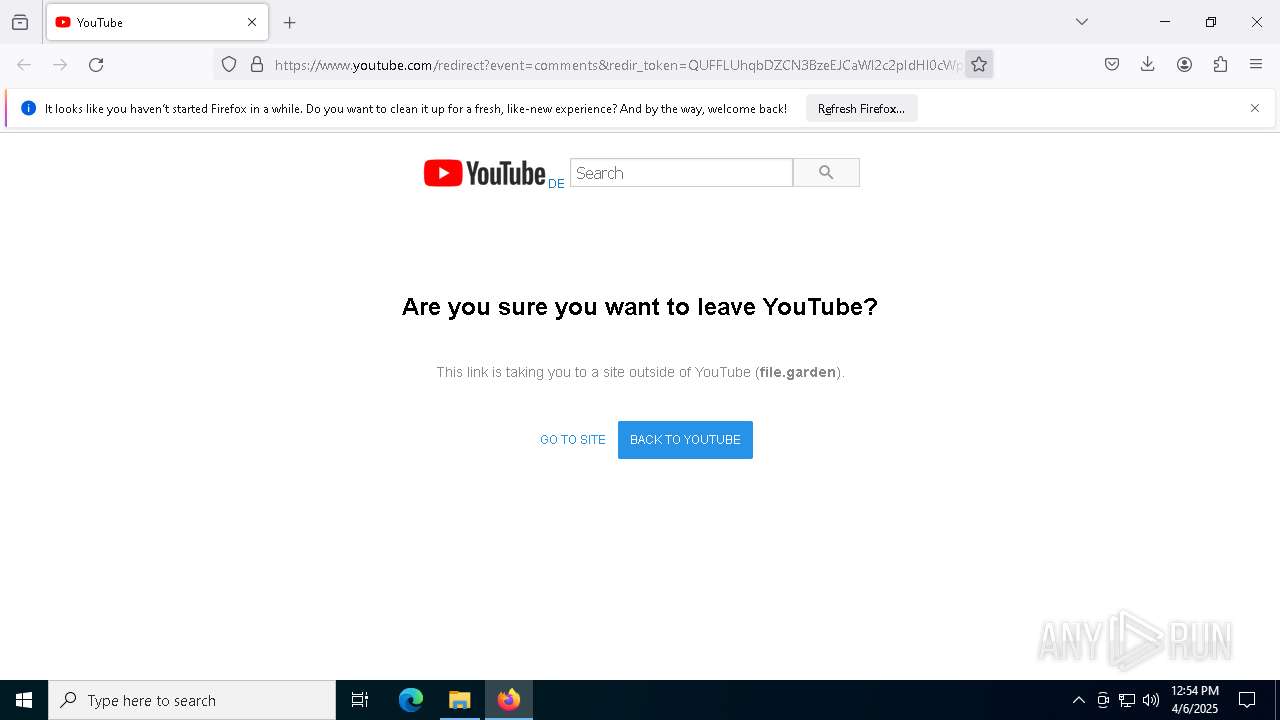
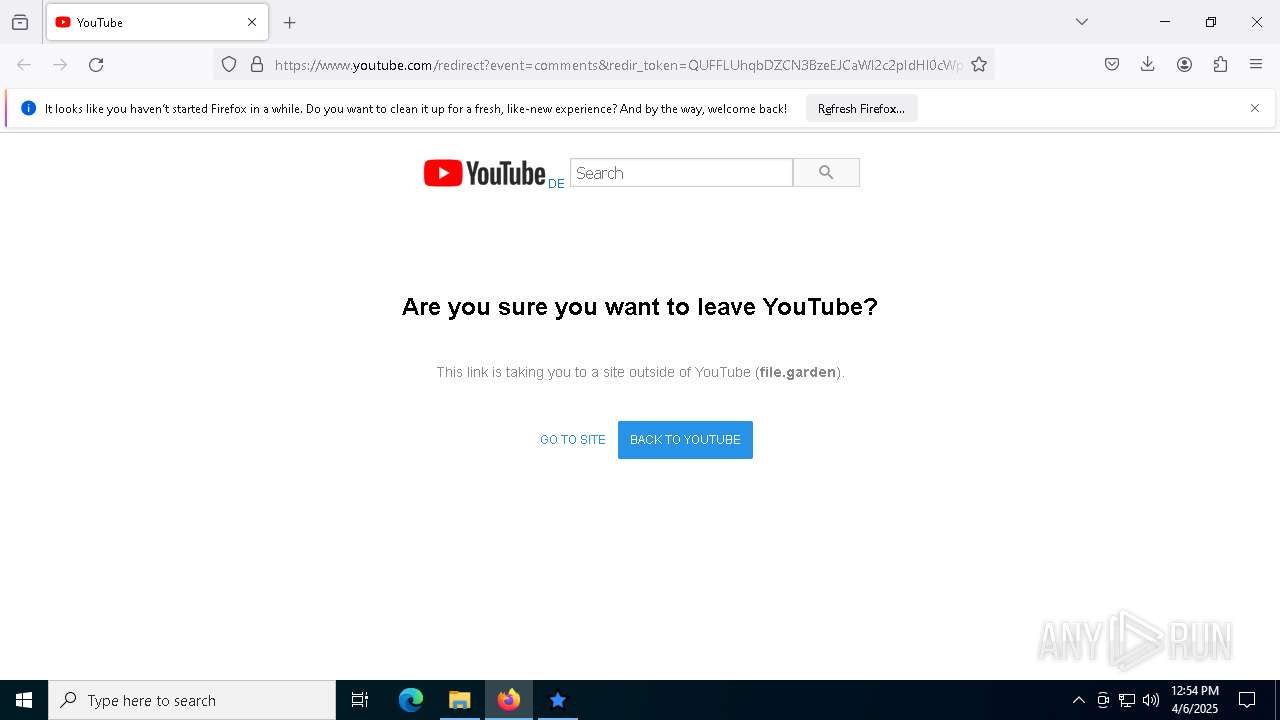
| URL: | https://www.youtube.com/redirect?event=comments&redir_token=QUFFLUhqbDZCN3BzeEJCaWl2c2pIdHl0cWpjdTIxbi1mUXxBQ3Jtc0trVHlJb21nVzNQRE14clNTZTdUWDdILXlBb1ZpRG5lWDdPOGZWbzdMR1RMOGlpS2ZYdTl4LW41RUhzTWNnXzdJN1FwUHlzR25hX3lKZ3V4RmR1QnNZWHB6Y0o3NkRHbXlLaEg0ZmREOGx3ZW5aWnplRQ&q=https%3A%2F%2Ffile.garden%2FZ0YSOE83ozp28Cum%2FE%2520Duper.zip |
| Full analysis: | https://app.any.run/tasks/adc048b3-8d5a-4453-a115-1f4c7e691d8b |
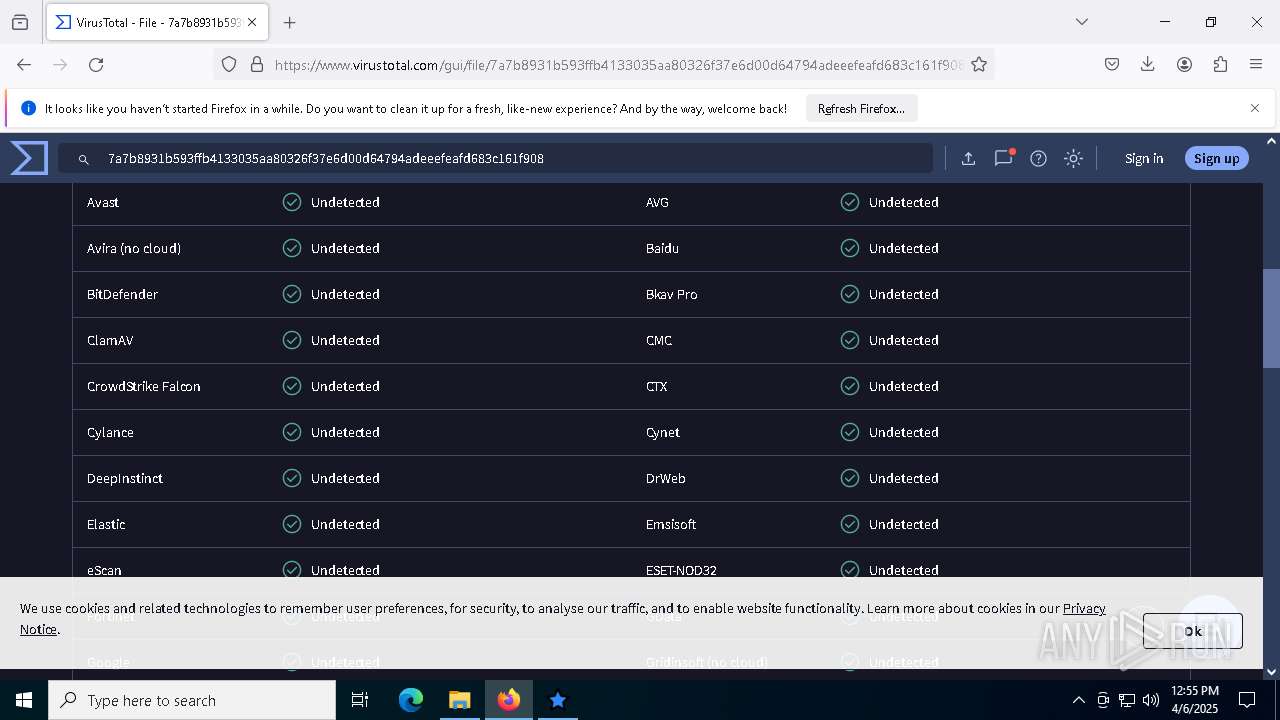
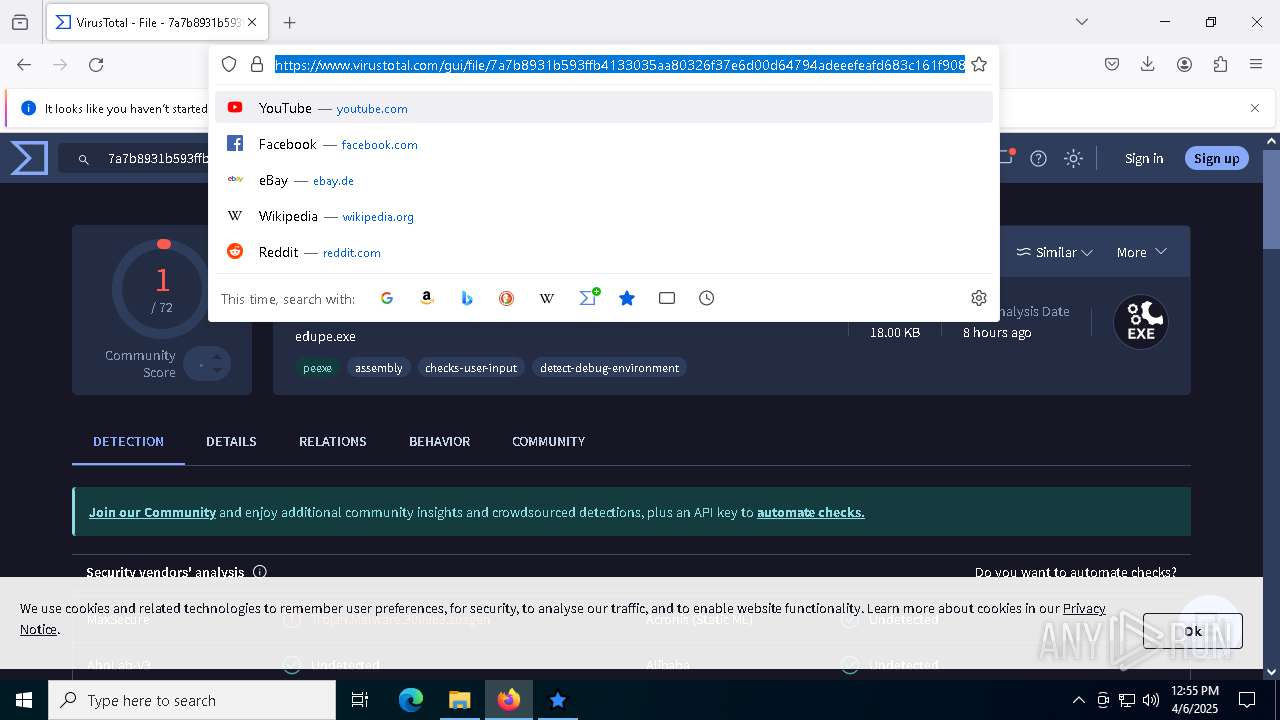
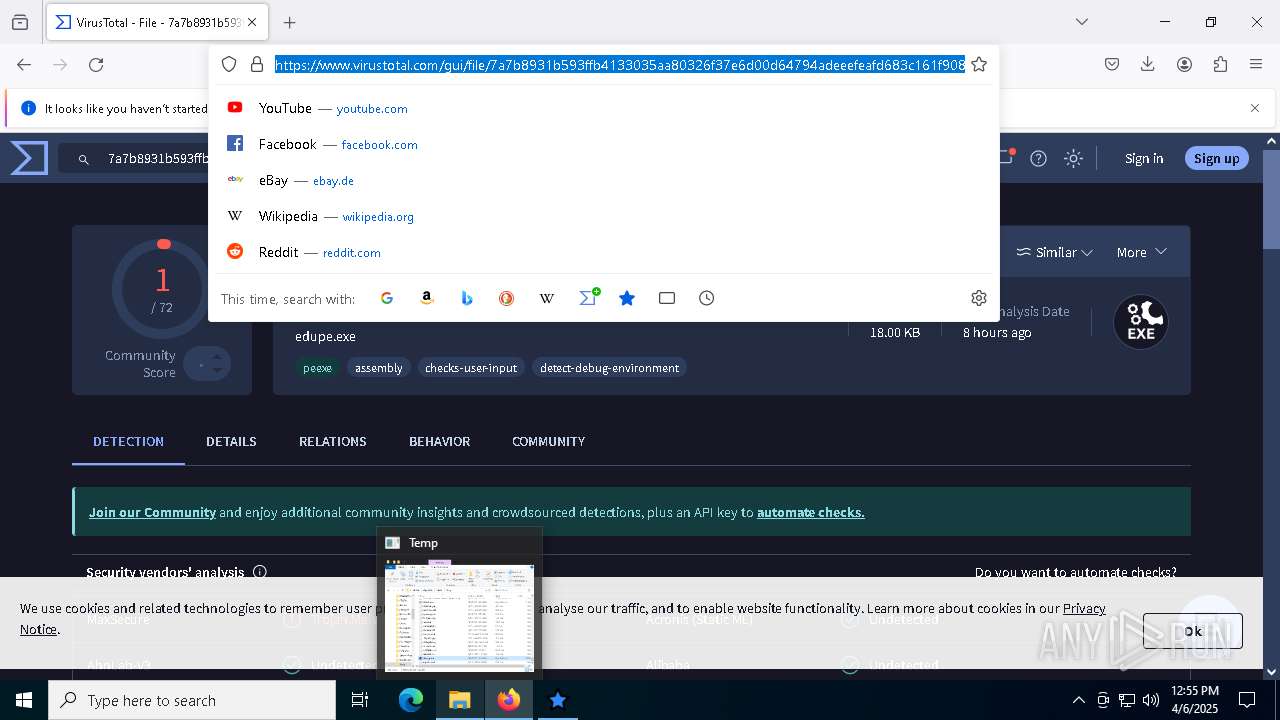
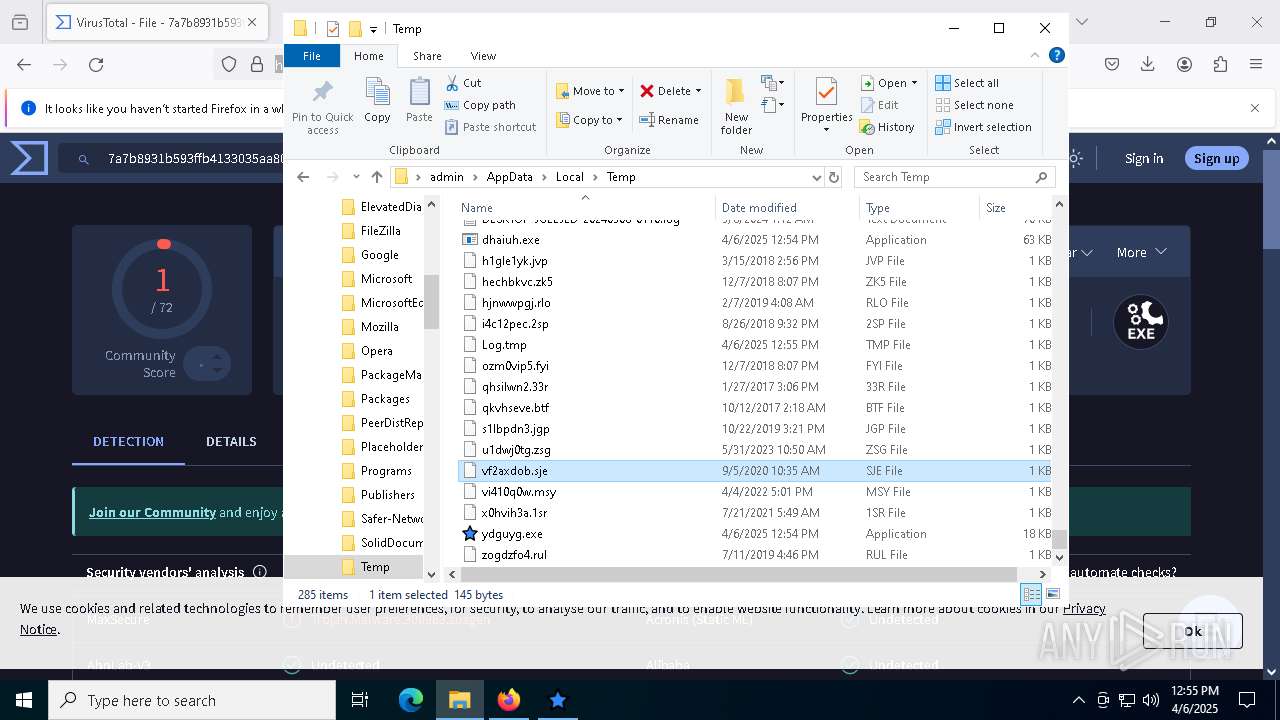
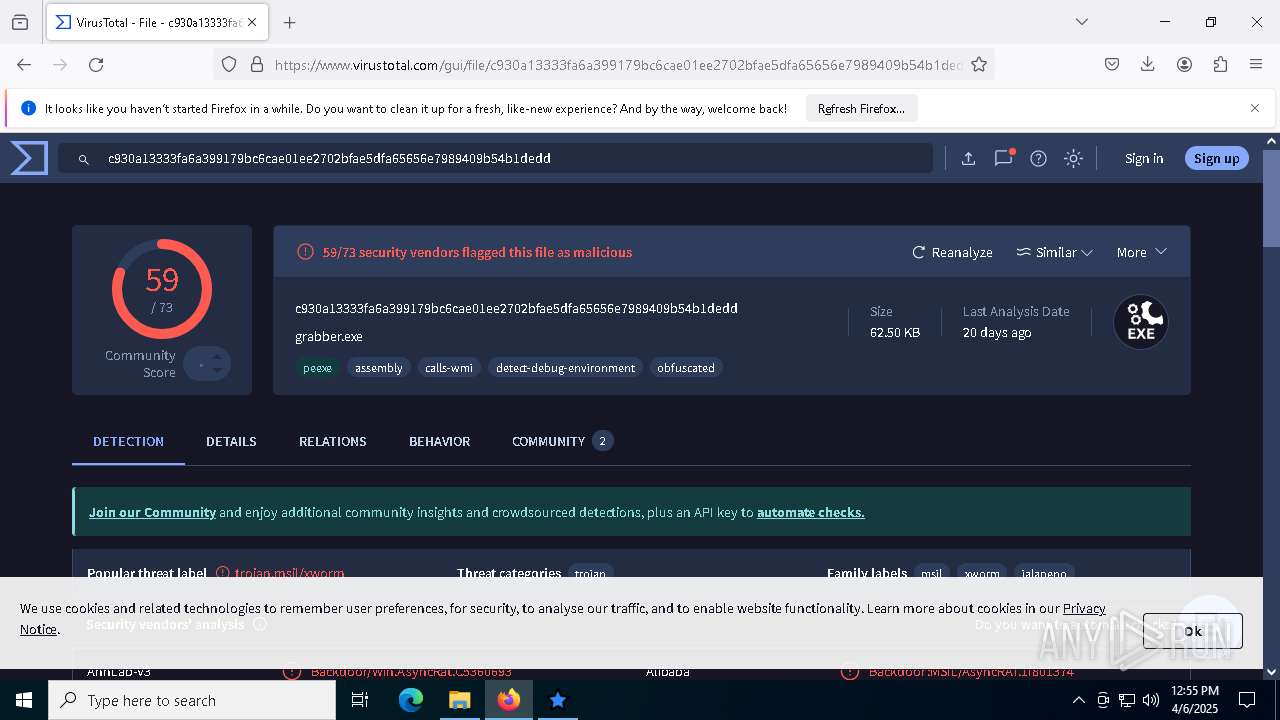
| Verdict: | Malicious activity |
| Threats: | XWorm is a remote access trojan (RAT) sold as a malware-as-a-service. It possesses an extensive hacking toolset and is capable of gathering private information and files from the infected computer, hijacking MetaMask and Telegram accounts, and tracking user activity. XWorm is typically delivered to victims' computers through multi-stage attacks that start with phishing emails. |
| Analysis date: | April 06, 2025, 12:53:22 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 30F7AA3FB375DE3619577594DBAEACB5 |
| SHA1: | 1A5BDF9B12DBC62BD6032E1F7ADDB04307EC7BF1 |
| SHA256: | 93A02DC9F38411F14D623D23F2B8960244665182A93CDEEB484F49DEA04594E8 |
| SSDEEP: | 6:2OLUxGKmquxZOGVwi3vszRRD9UvcvkYlBPIk6oyik0LrDTicGYN3zQY9Bf:2jGRPPOyUzR3vvXUNy7YaU2Bf |
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 7220)
- powershell.exe (PID: 7680)
- powershell.exe (PID: 9000)
- powershell.exe (PID: 9052)
Bypass execution policy to execute commands
- powershell.exe (PID: 7220)
- powershell.exe (PID: 7680)
- powershell.exe (PID: 9000)
- powershell.exe (PID: 9052)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 6036)
- cmd.exe (PID: 5400)
- cmd.exe (PID: 3332)
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 3332)
Changes Windows Defender settings
- cmd.exe (PID: 3332)
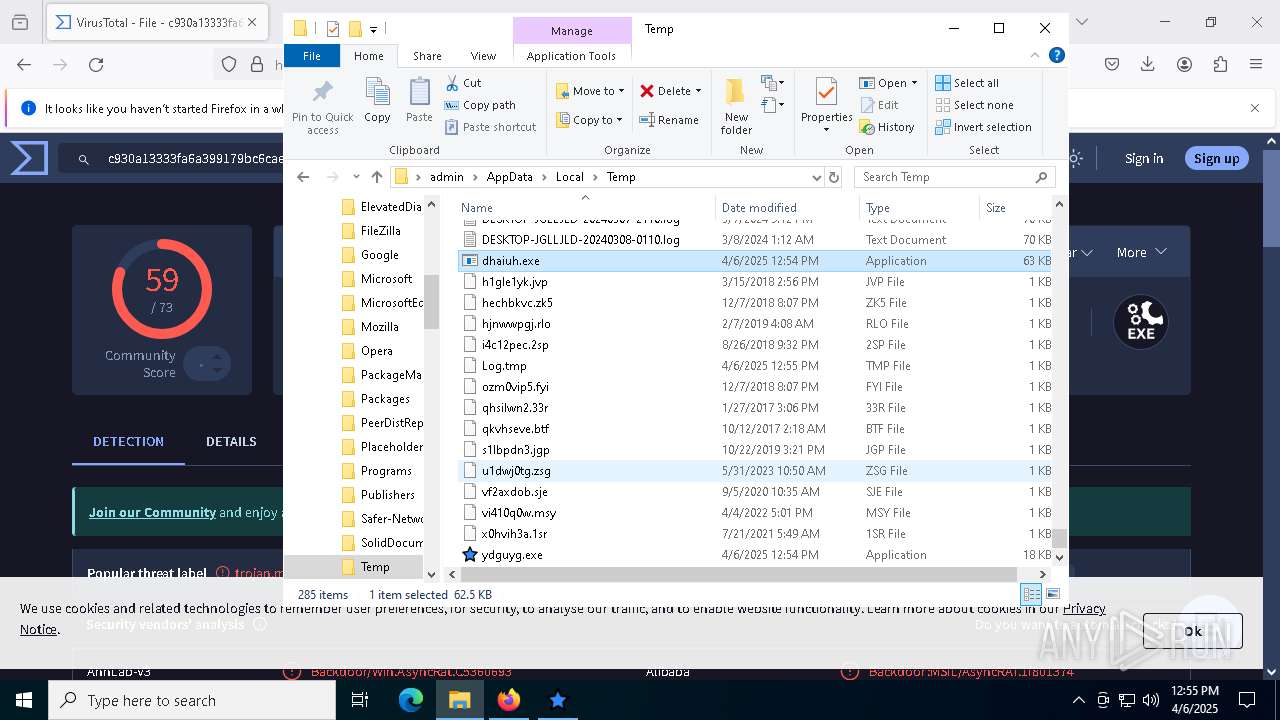
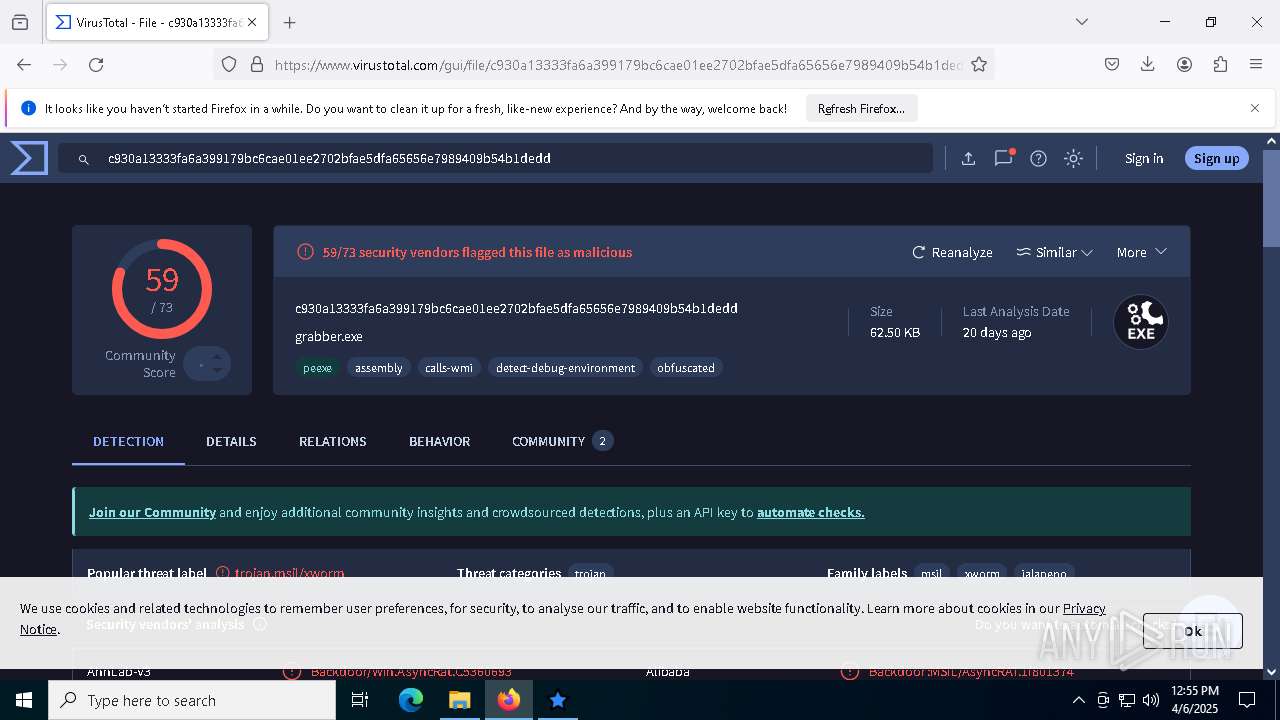
XWORM has been detected (SURICATA)
- dhaiuh.exe (PID: 6516)
XWORM has been detected (YARA)
- dhaiuh.exe (PID: 6516)
SUSPICIOUS
Node.exe was dropped
- firefox.exe (PID: 7476)
Executing commands from a ".bat" file
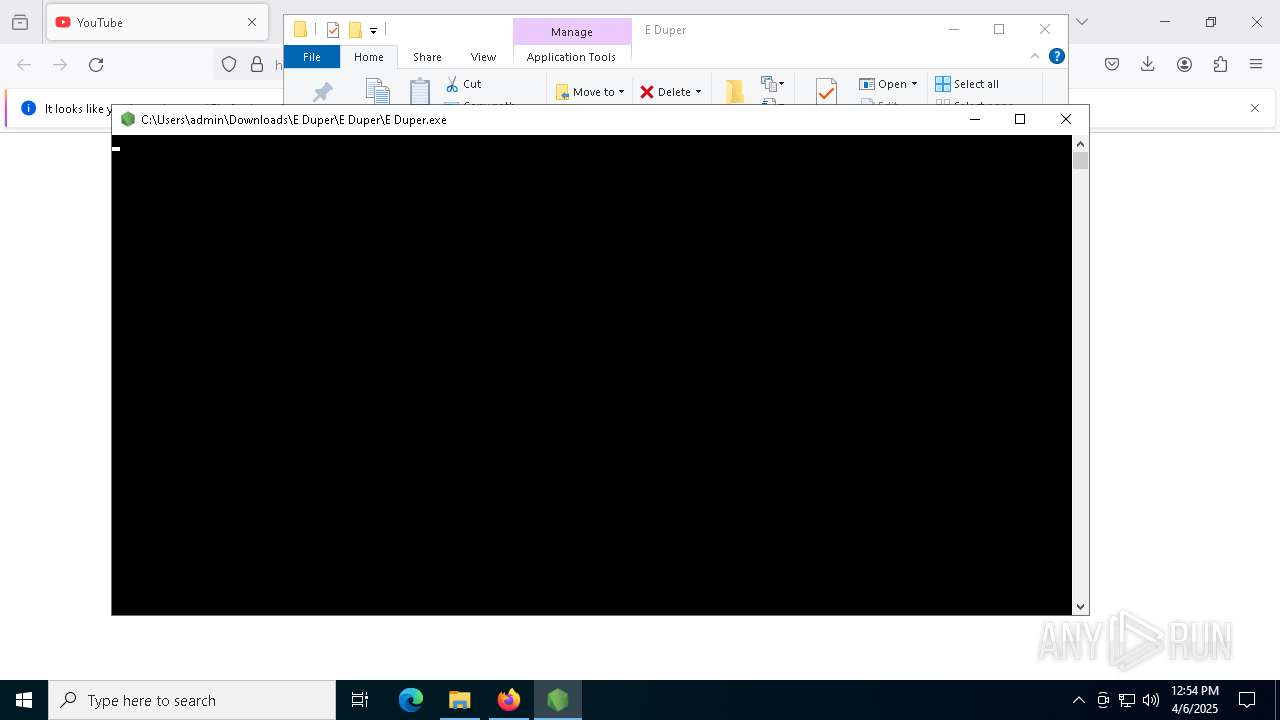
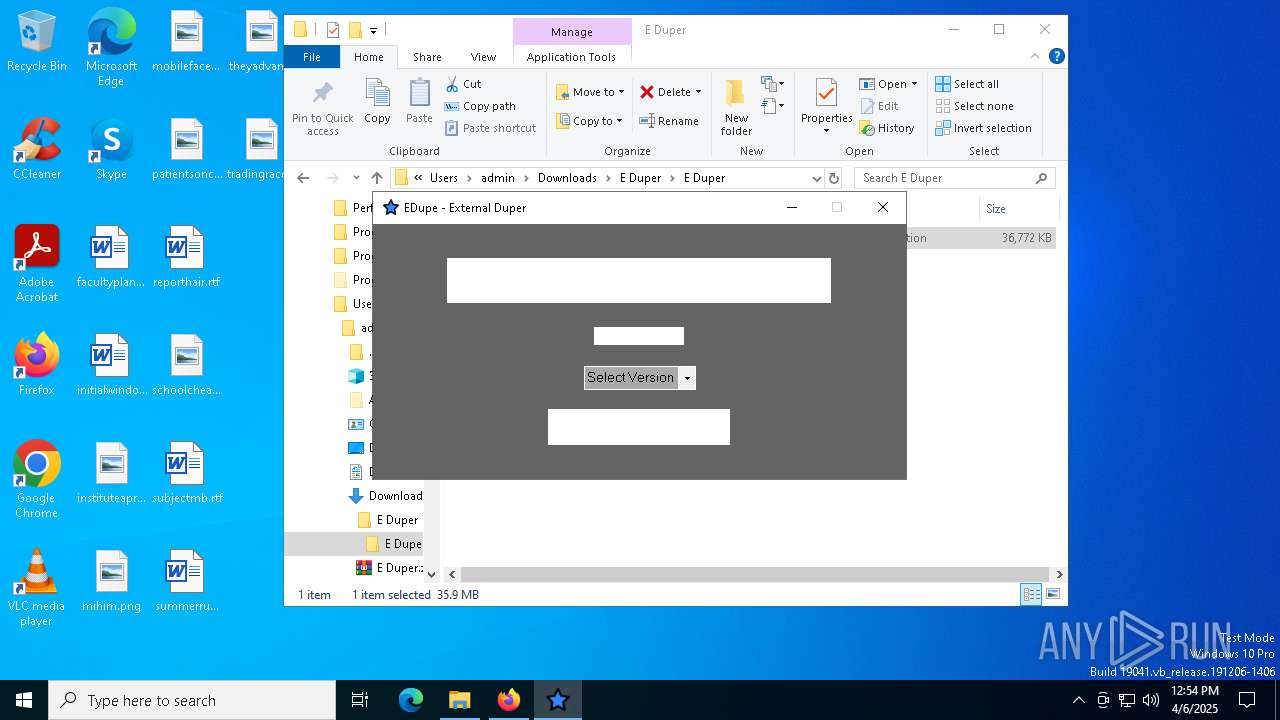
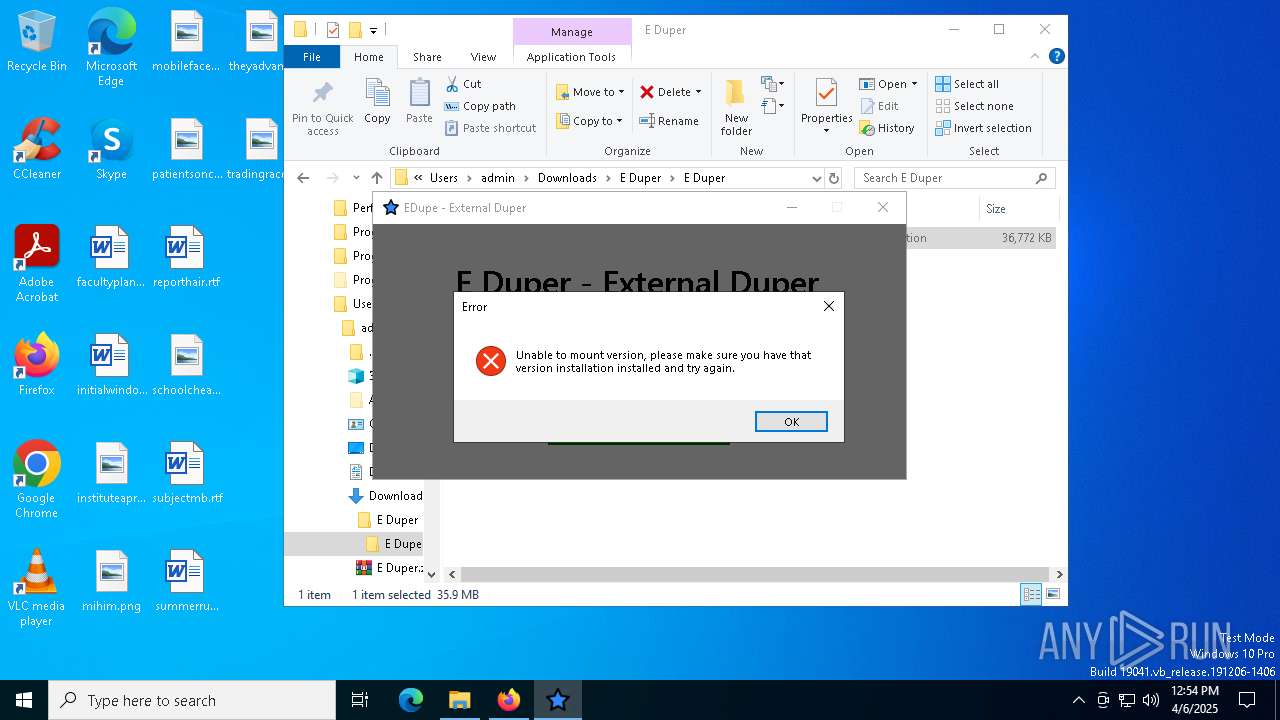
- E Duper.exe (PID: 5552)
- powershell.exe (PID: 7220)
- powershell.exe (PID: 7680)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 4620)
- cmd.exe (PID: 6036)
- cmd.exe (PID: 5400)
- cmd.exe (PID: 3332)
BASE64 encoded PowerShell command has been detected
- cmd.exe (PID: 4620)
Base64-obfuscated command line is found
- cmd.exe (PID: 4620)
Starts CMD.EXE for commands execution
- E Duper.exe (PID: 5552)
- powershell.exe (PID: 7220)
- powershell.exe (PID: 7680)
Starts NET.EXE to display or manage information about active sessions
- cmd.exe (PID: 6036)
- net.exe (PID: 7188)
- cmd.exe (PID: 5400)
- net.exe (PID: 7912)
- cmd.exe (PID: 3332)
- net.exe (PID: 6712)
Executes script without checking the security policy
- powershell.exe (PID: 7220)
- powershell.exe (PID: 7680)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 6036)
- cmd.exe (PID: 3332)
- cmd.exe (PID: 5400)
Starts process via Powershell
- powershell.exe (PID: 7220)
- powershell.exe (PID: 7680)
- powershell.exe (PID: 9000)
- powershell.exe (PID: 9052)
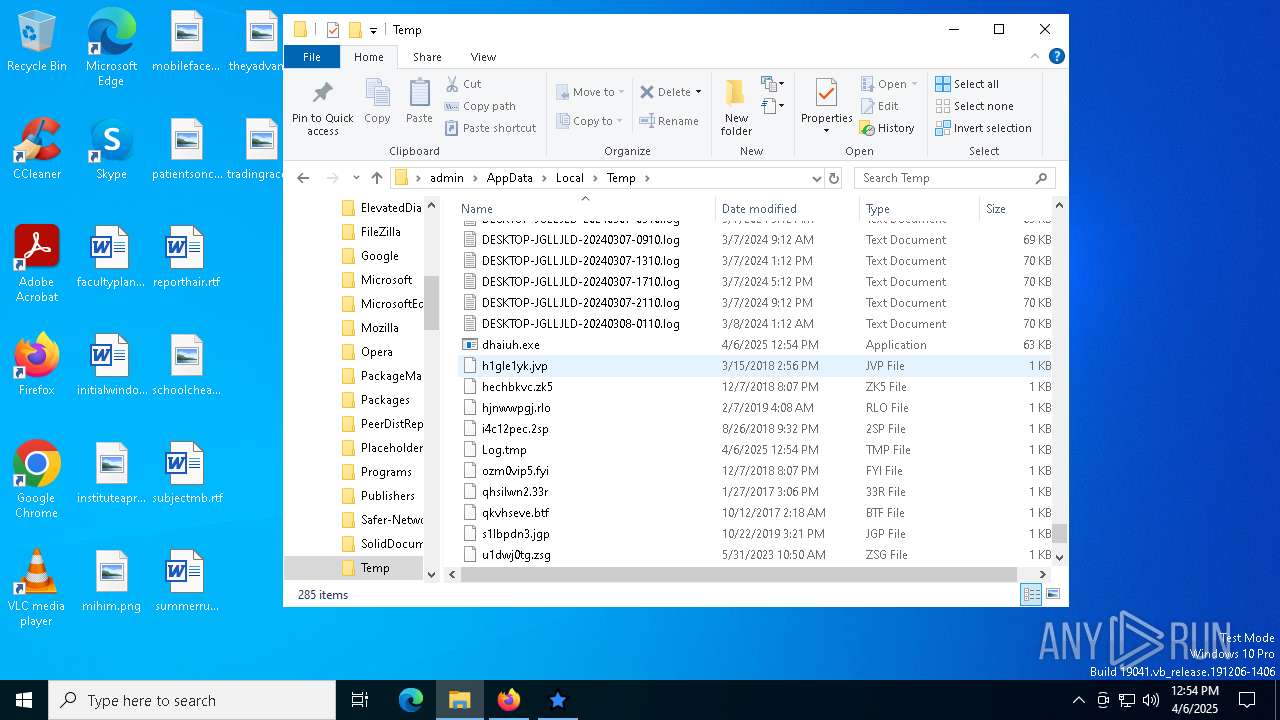
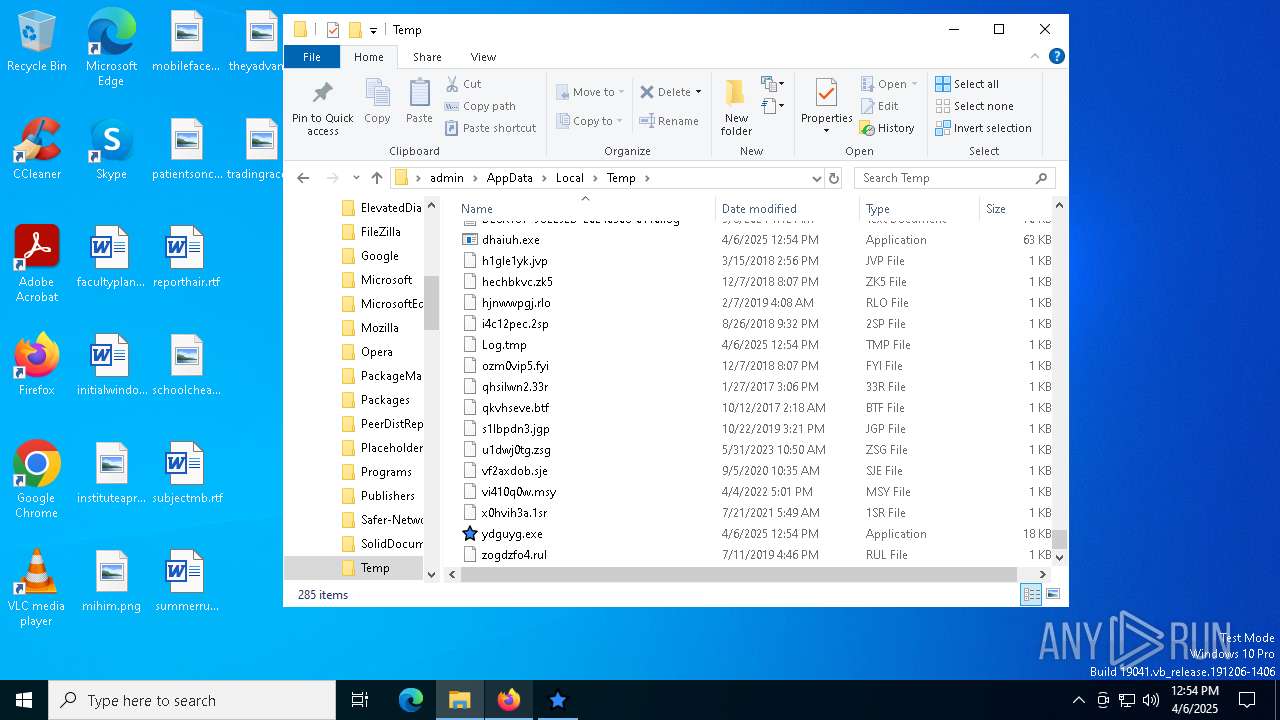
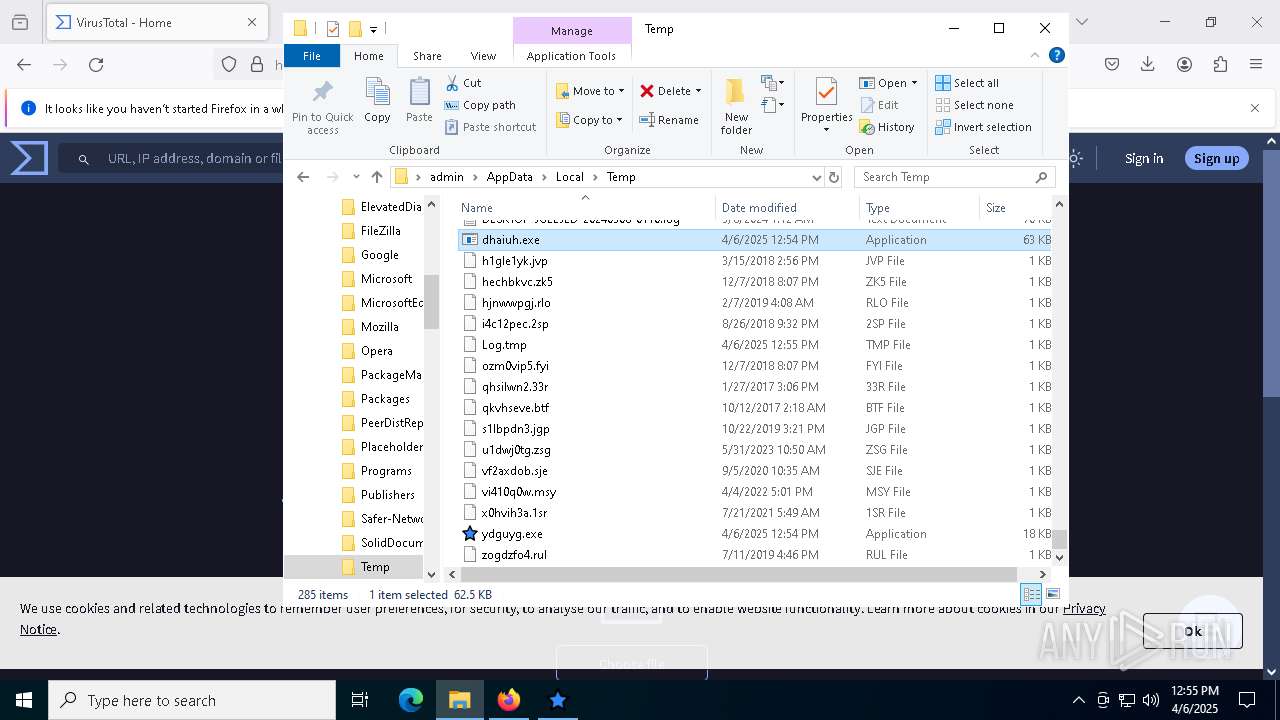
Executable content was dropped or overwritten
- csc.exe (PID: 8636)
- powershell.exe (PID: 9052)
- powershell.exe (PID: 9000)
CSC.EXE is used to compile C# code
- csc.exe (PID: 8636)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 3332)
Removes files via Powershell
- powershell.exe (PID: 8924)
Checks for external IP
- svchost.exe (PID: 2196)
- dhaiuh.exe (PID: 6516)
Connects to unusual port
- dhaiuh.exe (PID: 6516)
Contacting a server suspected of hosting an CnC
- dhaiuh.exe (PID: 6516)
PowerShell delay command usage (probably sleep evasion)
- powershell.exe (PID: 8924)
INFO
Application launched itself
- firefox.exe (PID: 7456)
- firefox.exe (PID: 7476)
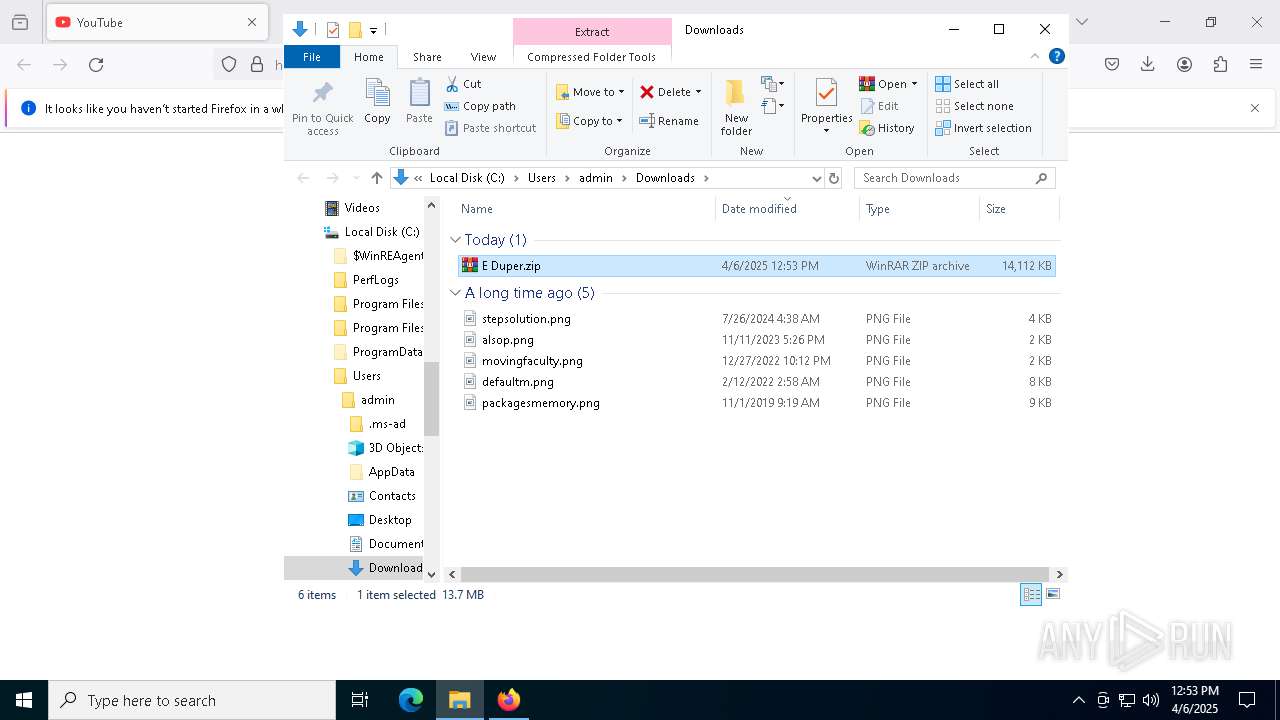
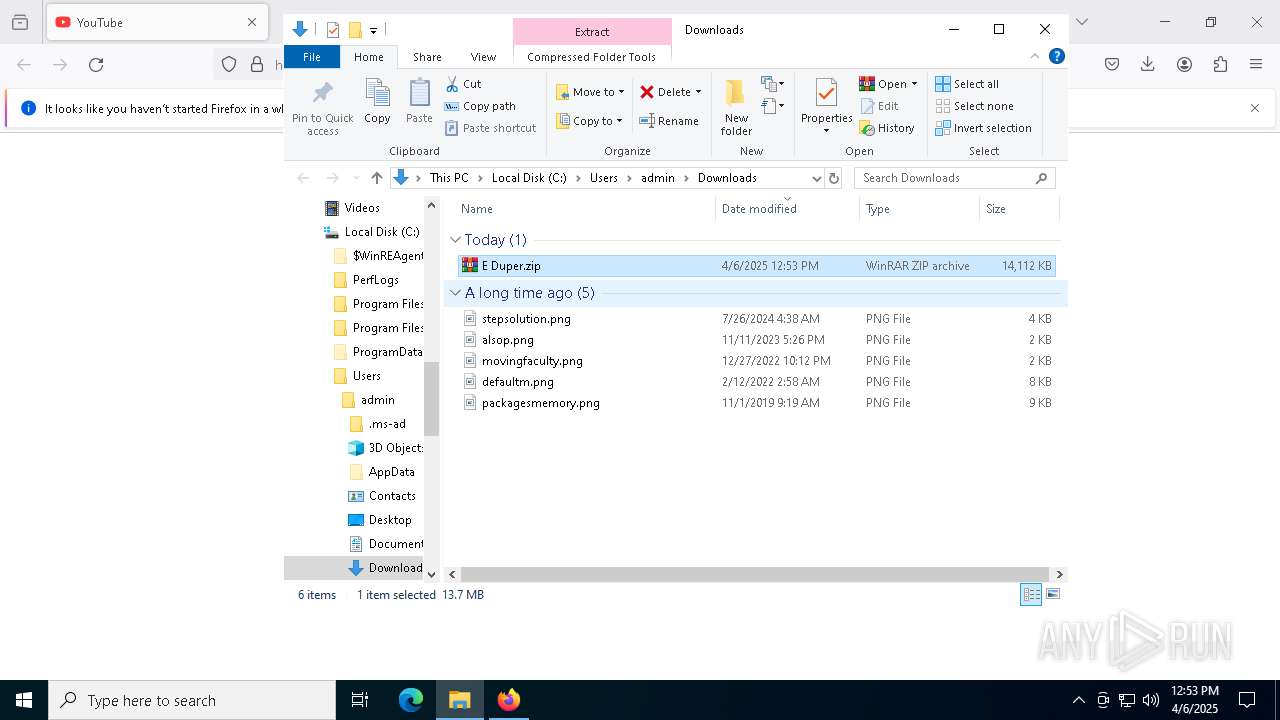
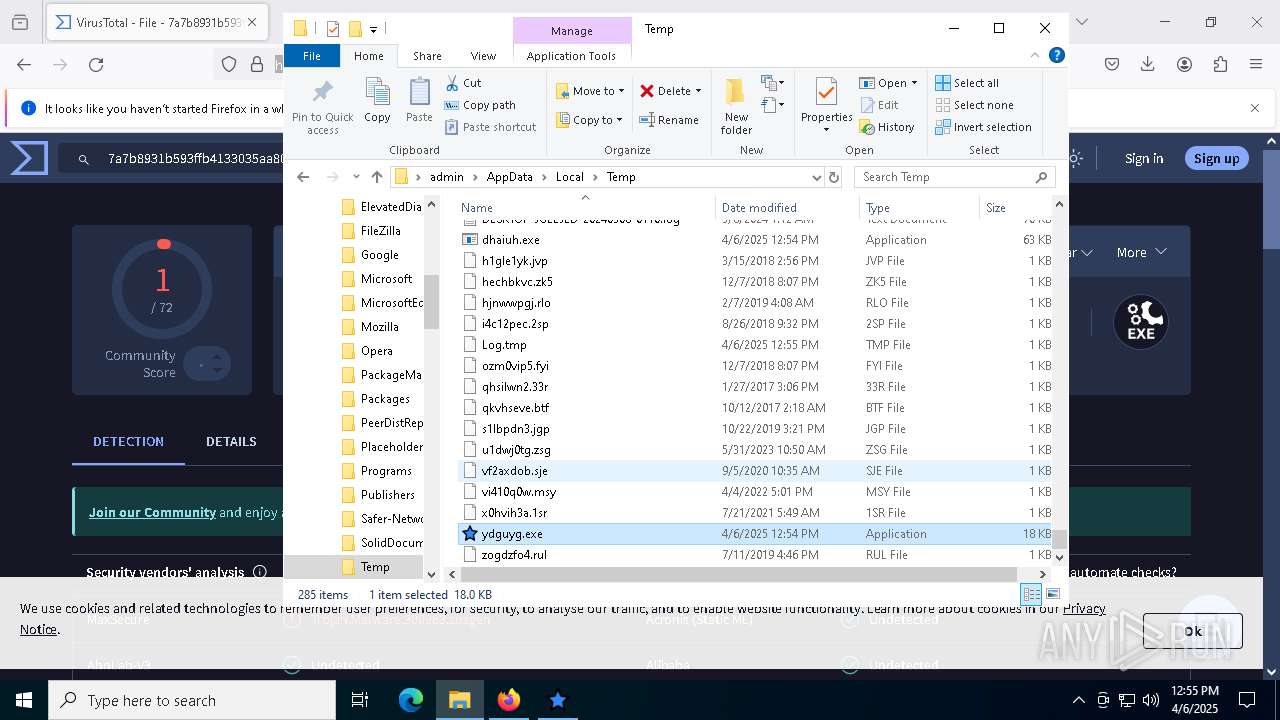
Autorun file from Downloads
- firefox.exe (PID: 7476)
The sample compiled with english language support
- firefox.exe (PID: 7476)
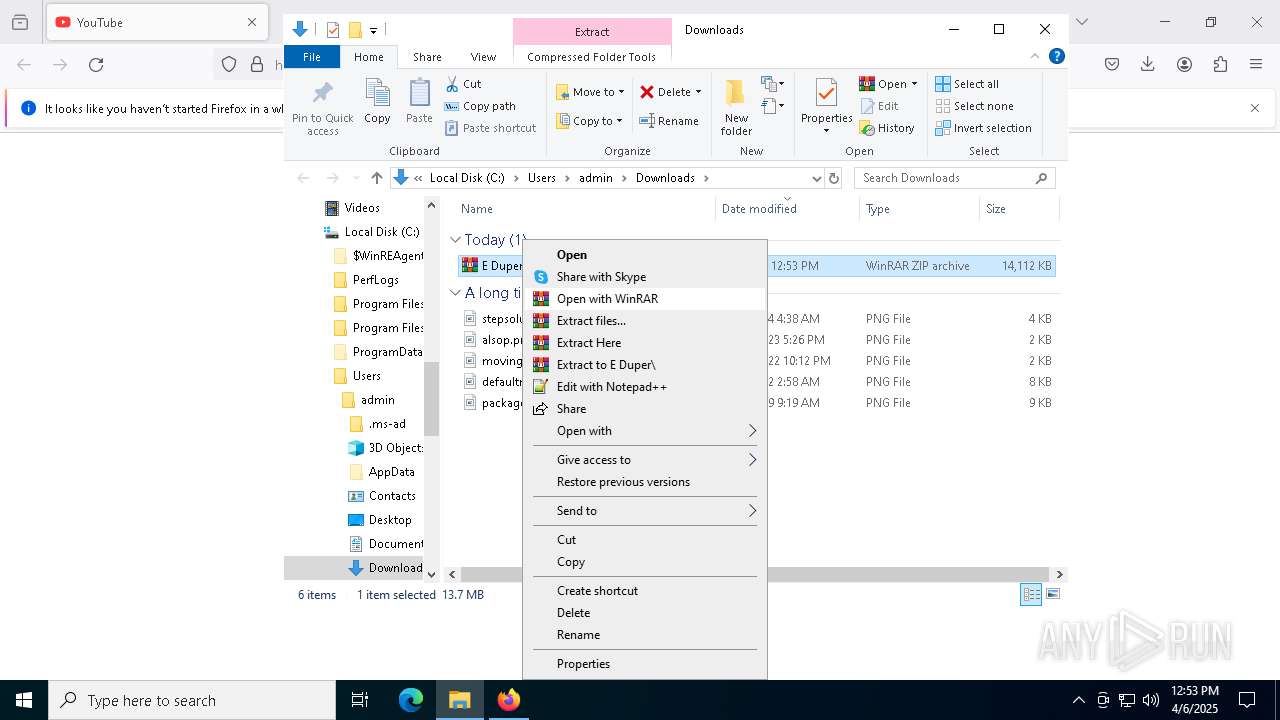
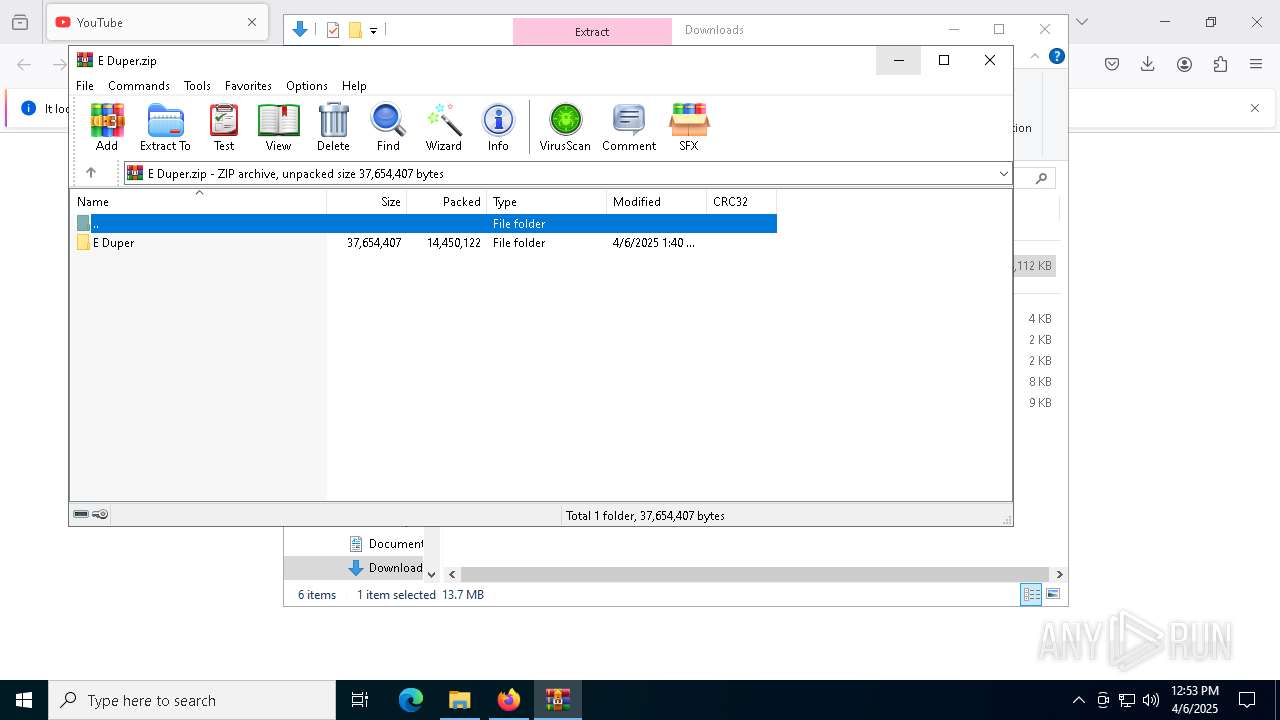
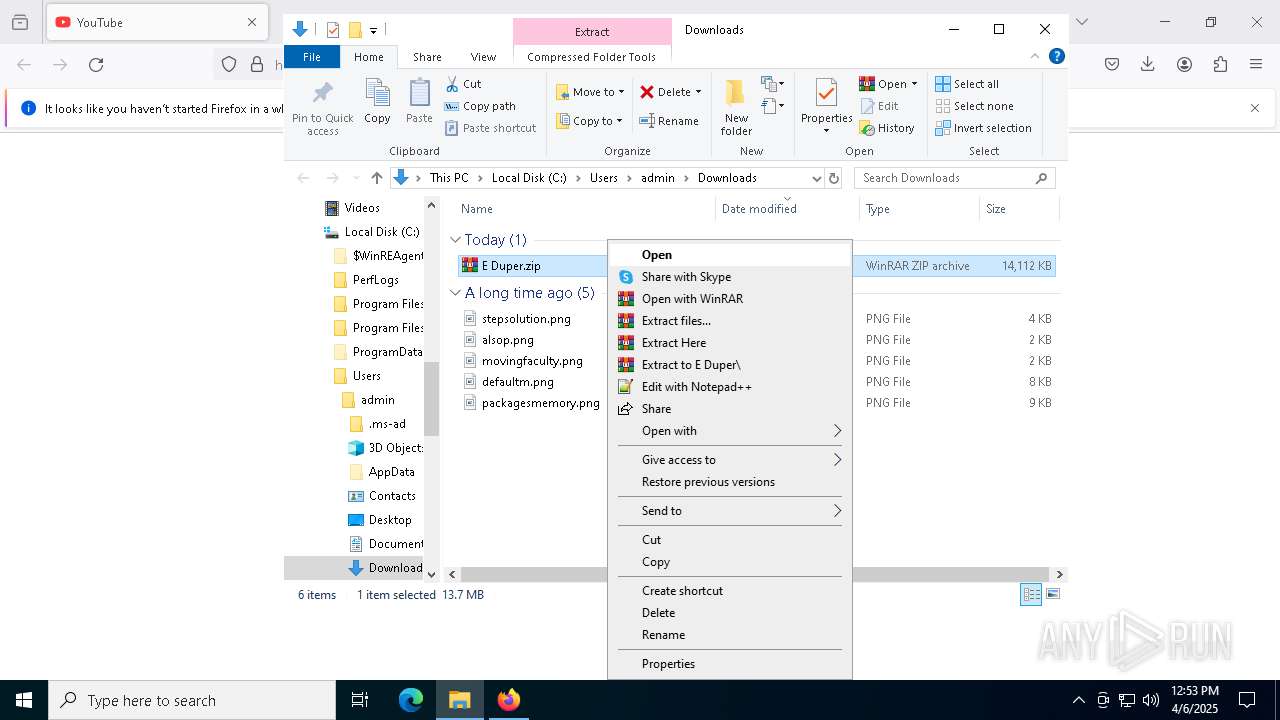
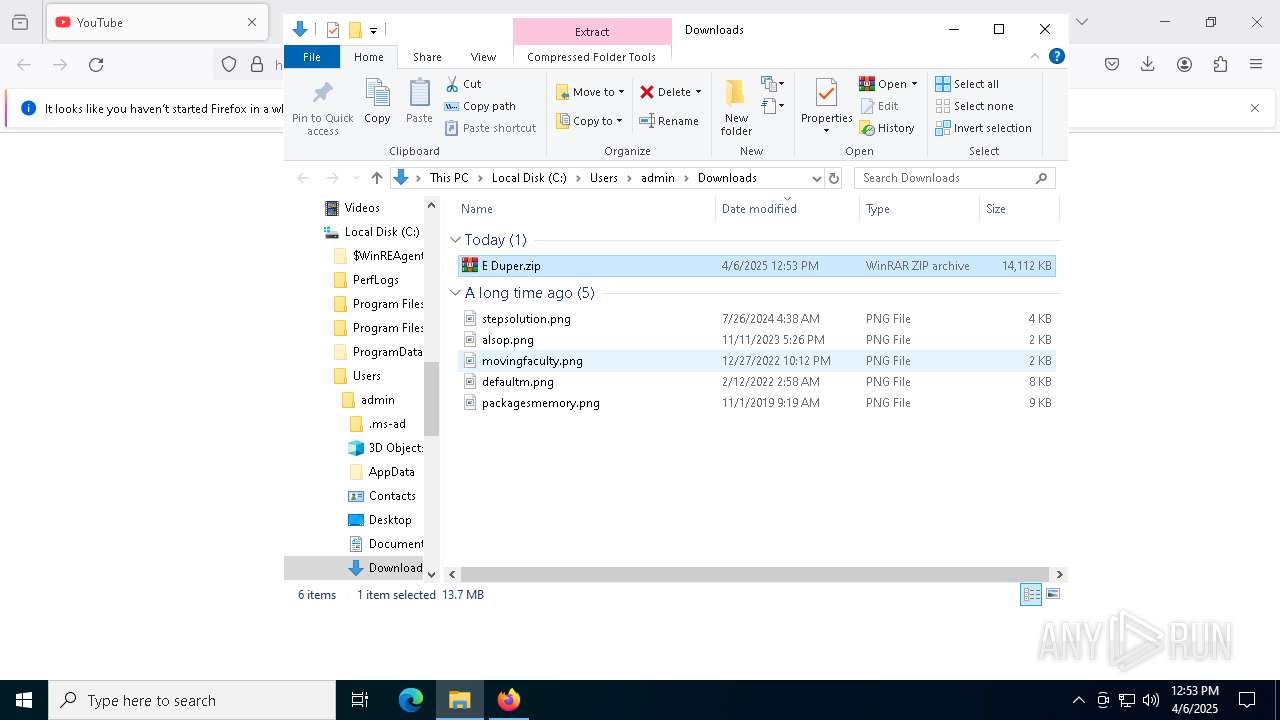
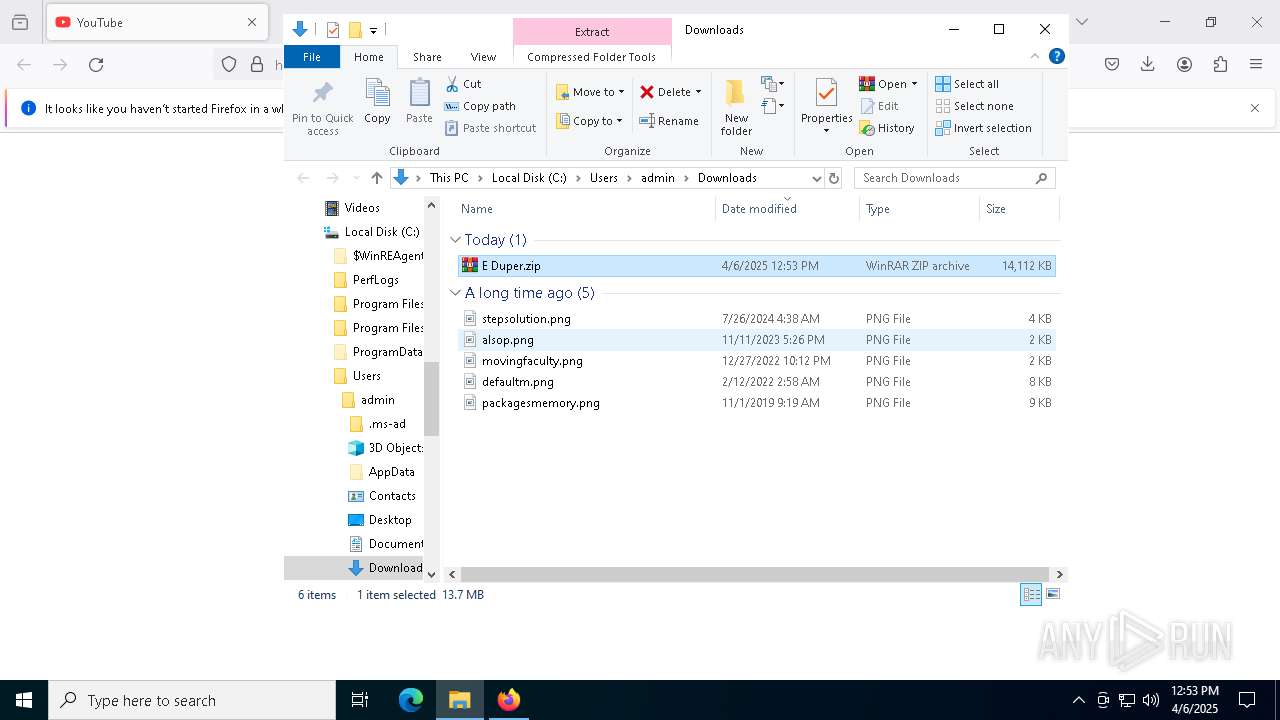
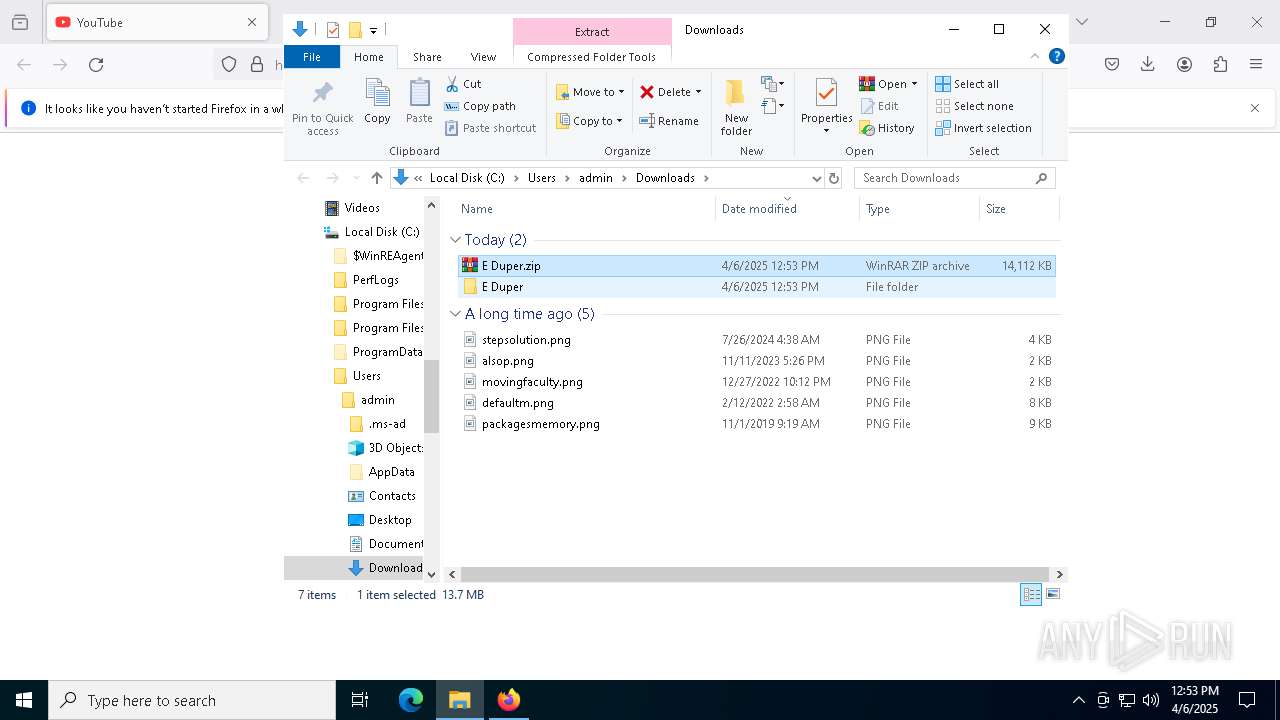
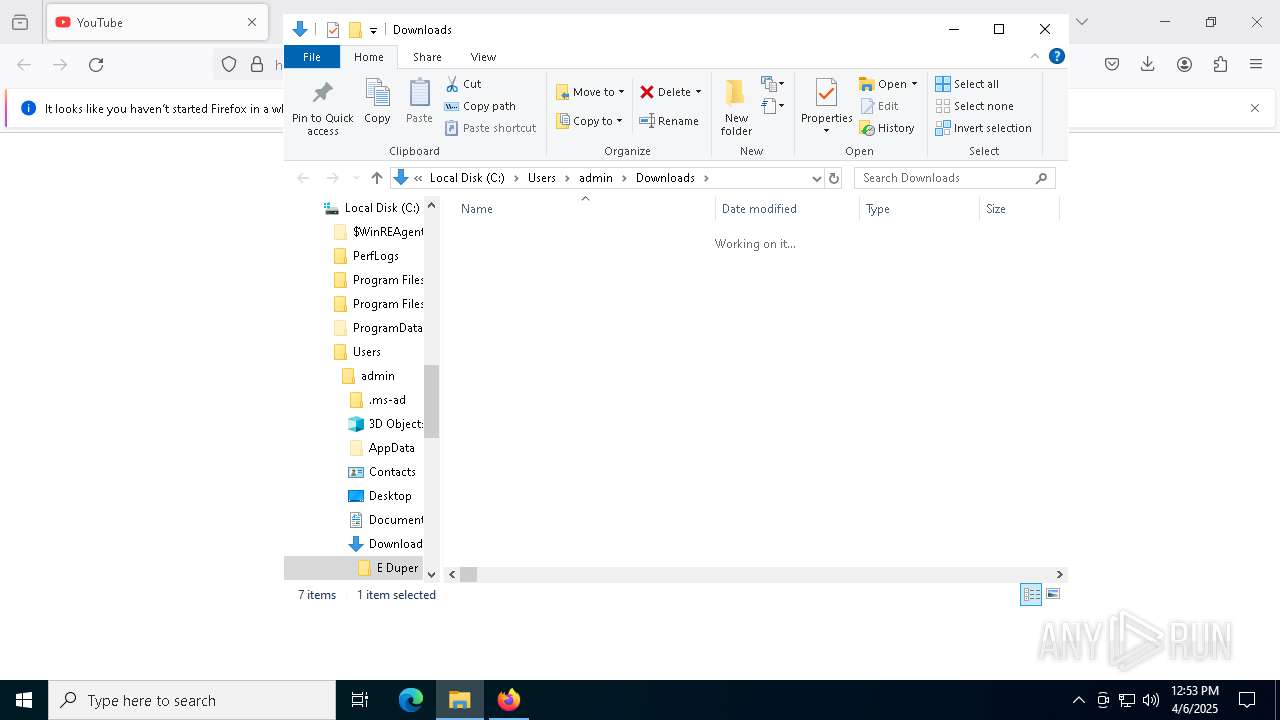
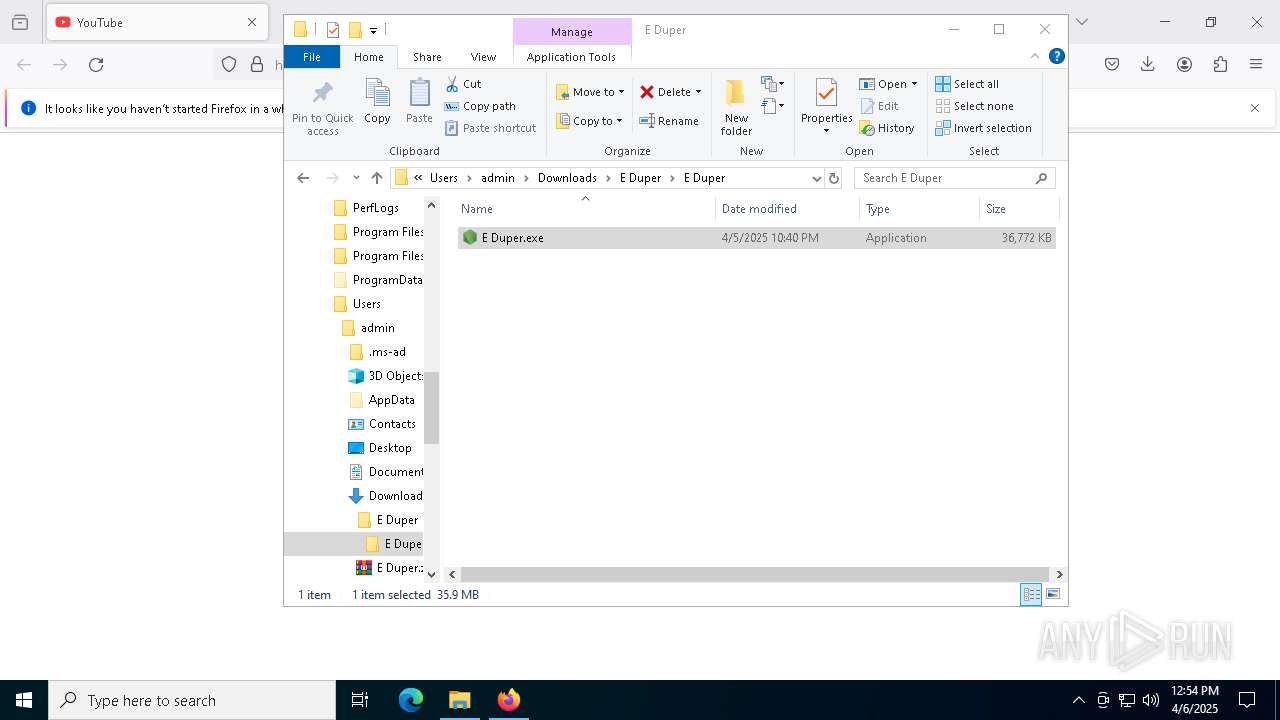
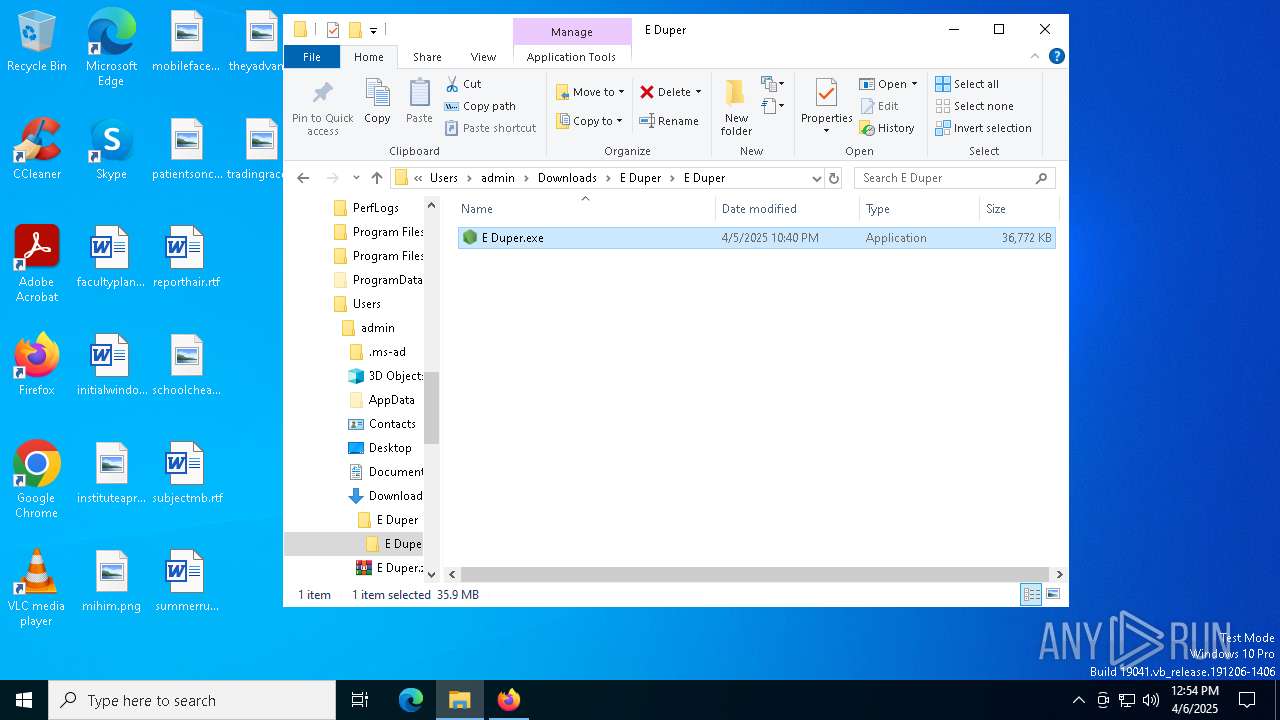
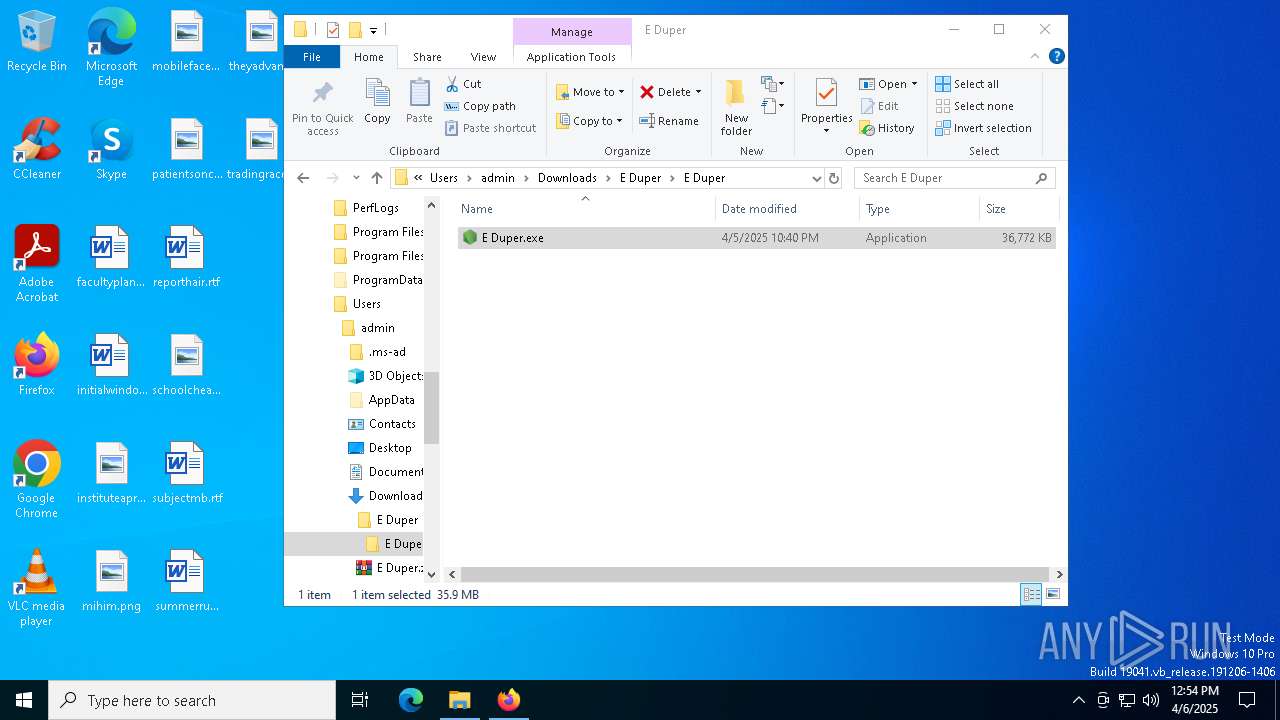
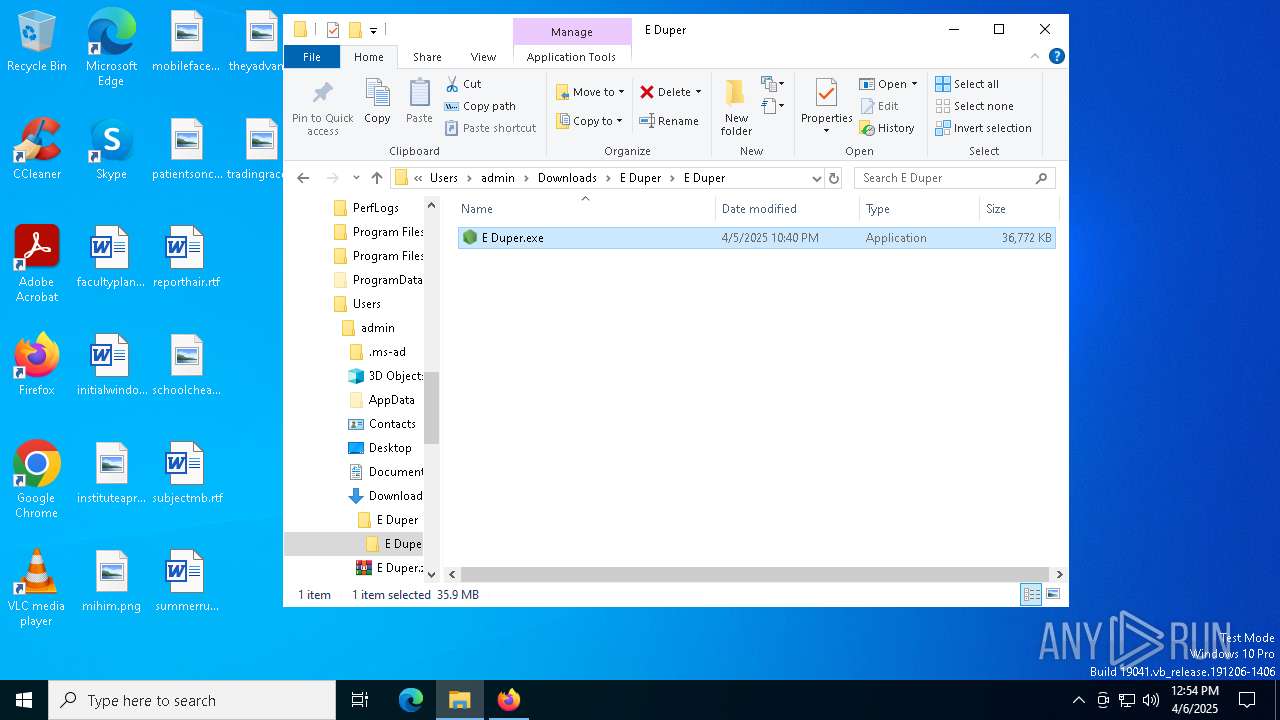
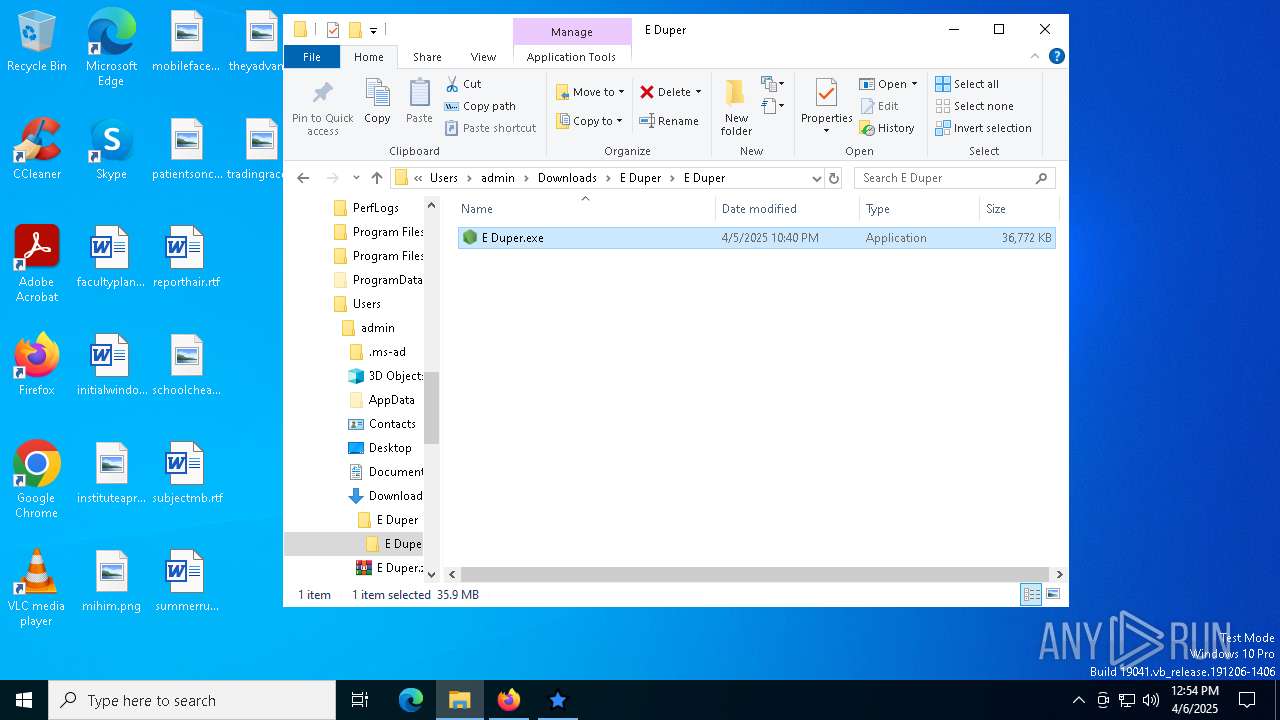
Manual execution by a user
- WinRAR.exe (PID: 3300)
- E Duper.exe (PID: 5552)
- WinRAR.exe (PID: 8976)
Checks supported languages
- E Duper.exe (PID: 5552)
- csc.exe (PID: 8636)
- cvtres.exe (PID: 2240)
- dhaiuh.exe (PID: 6516)
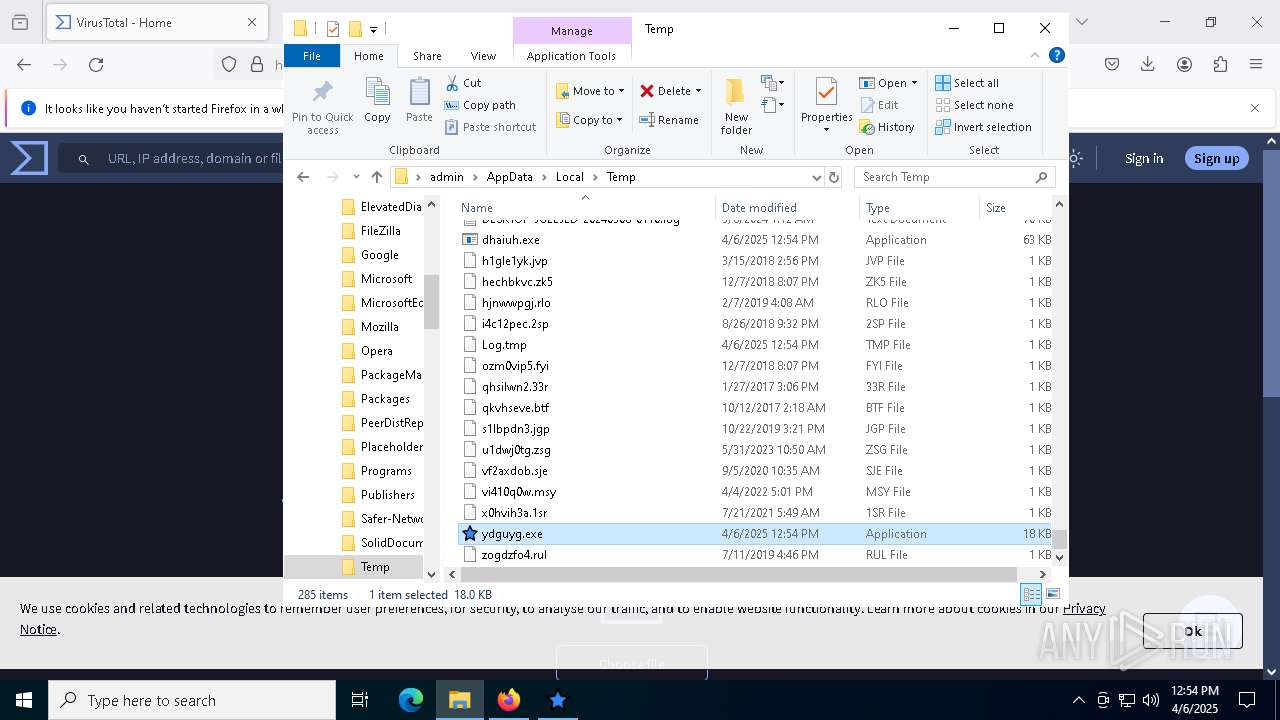
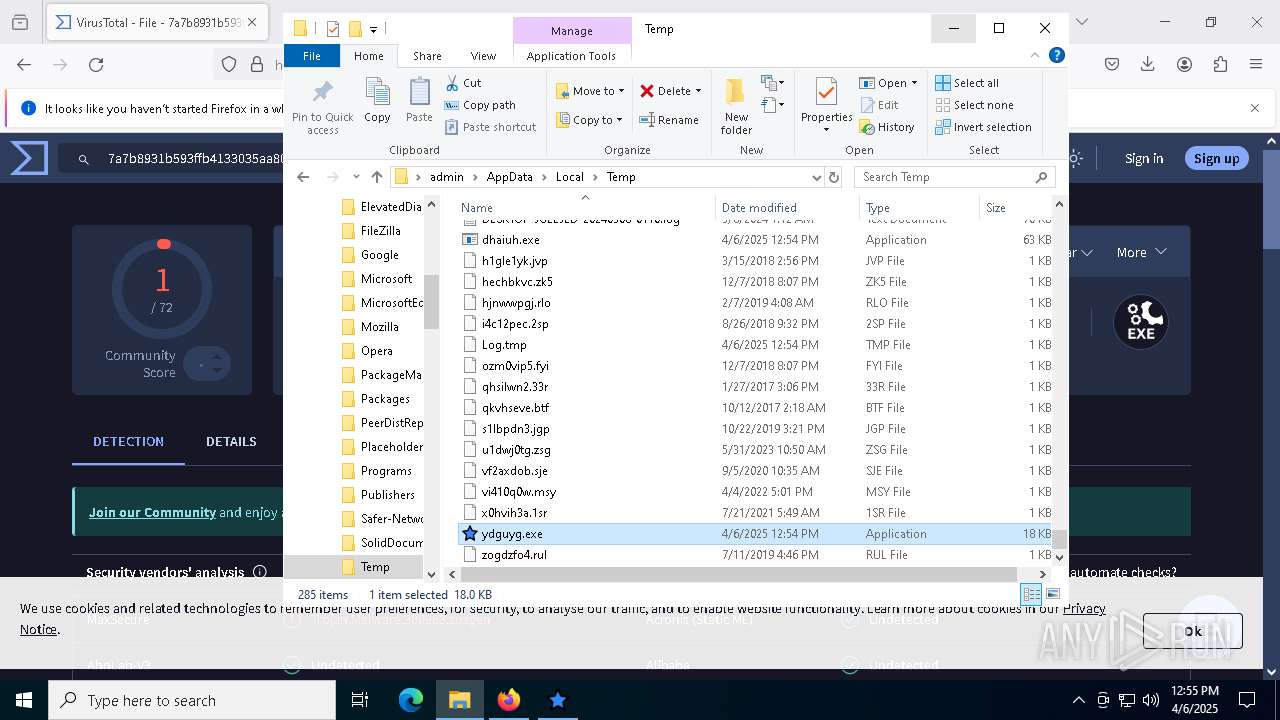
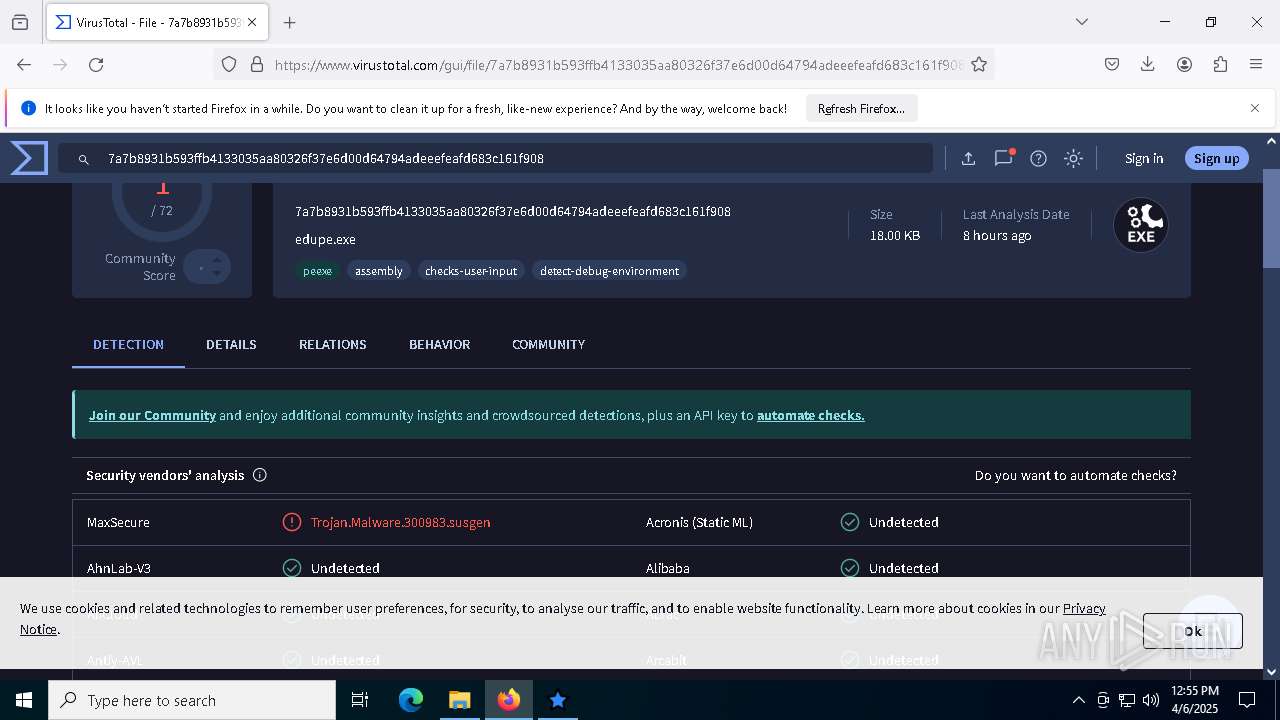
- ydguyg.exe (PID: 8412)
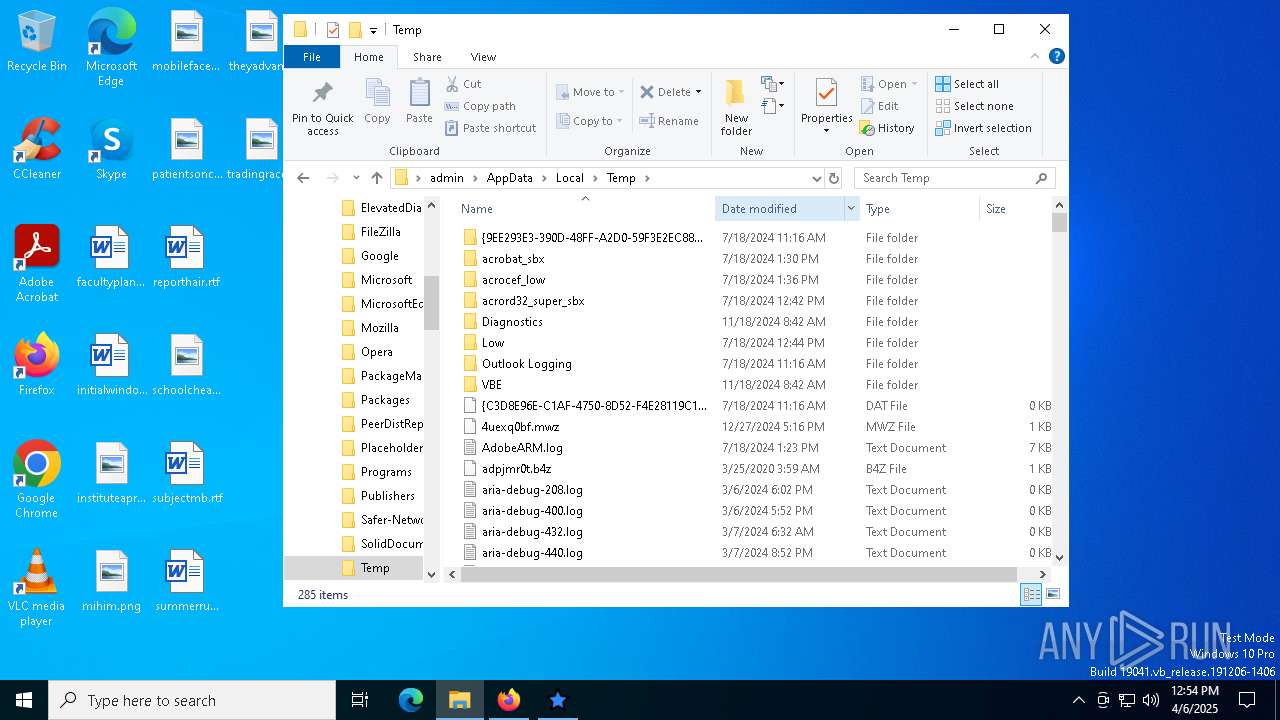
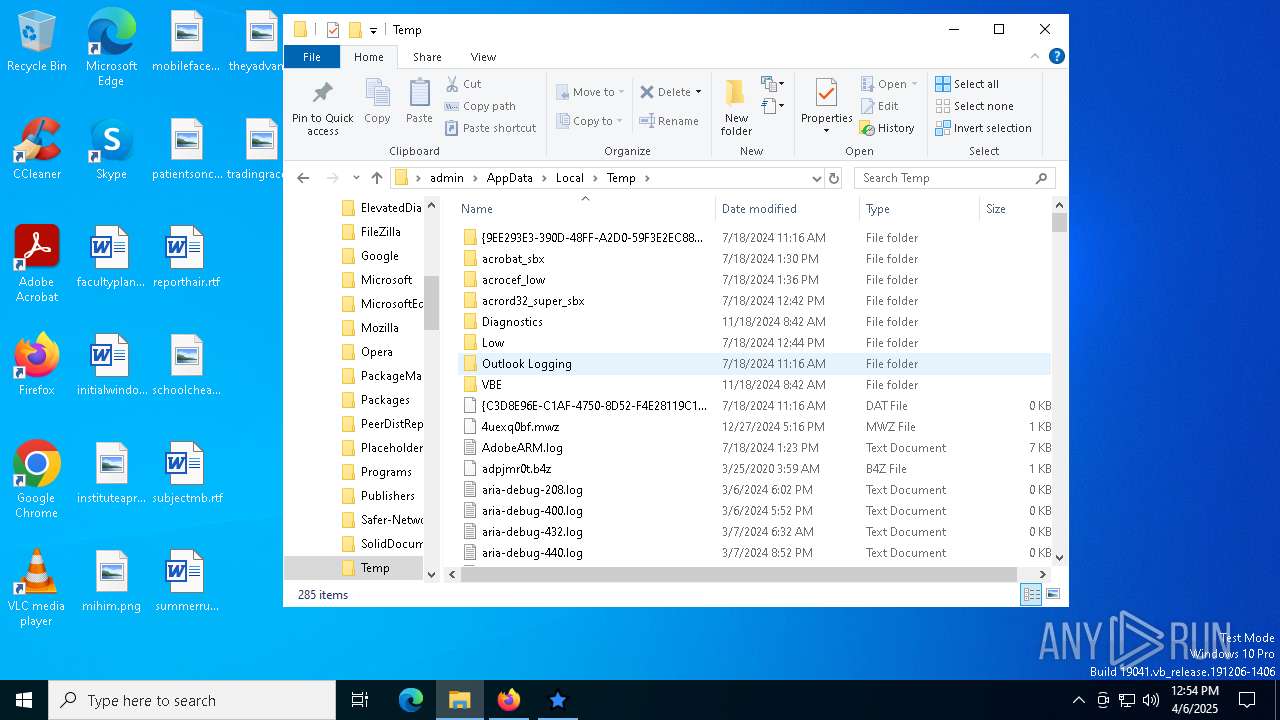
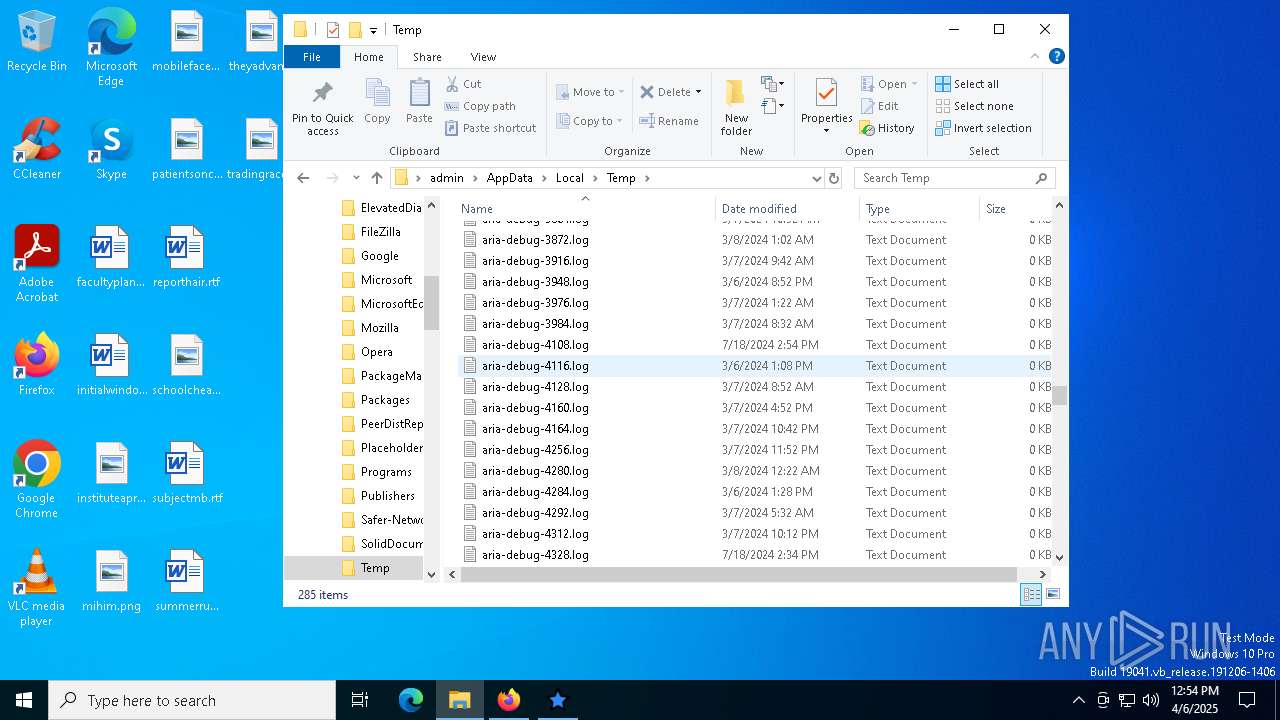
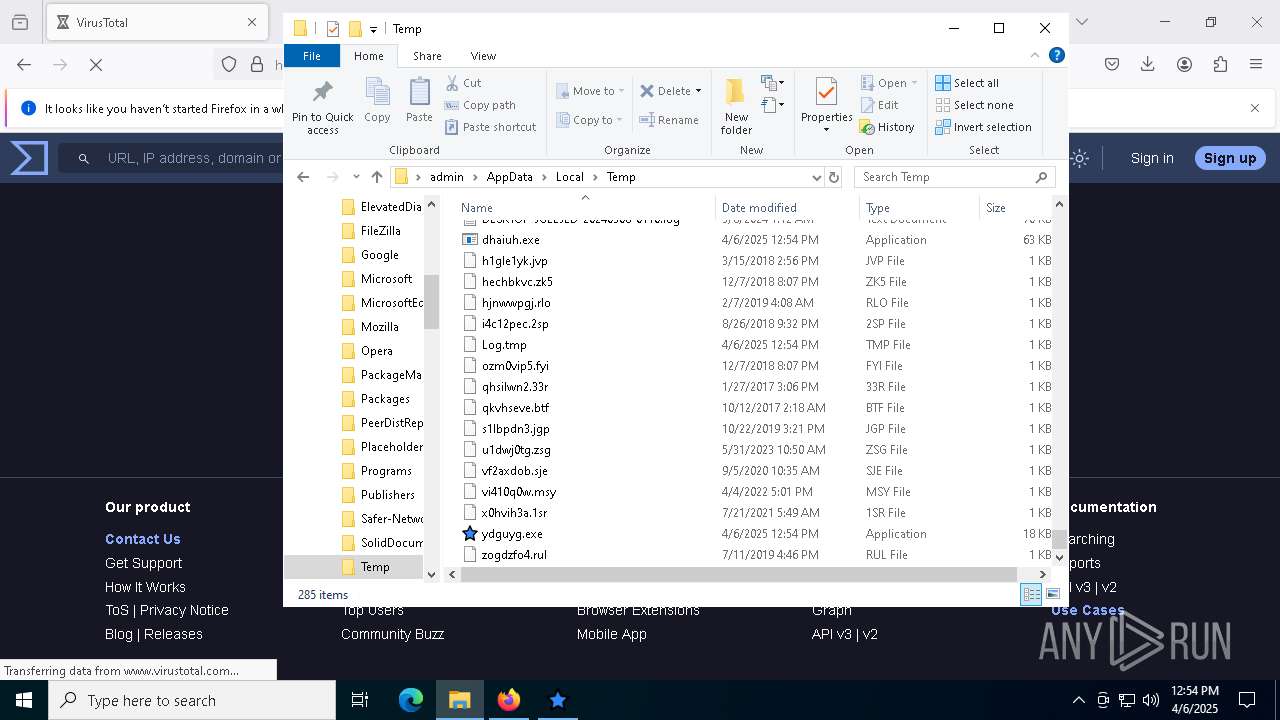
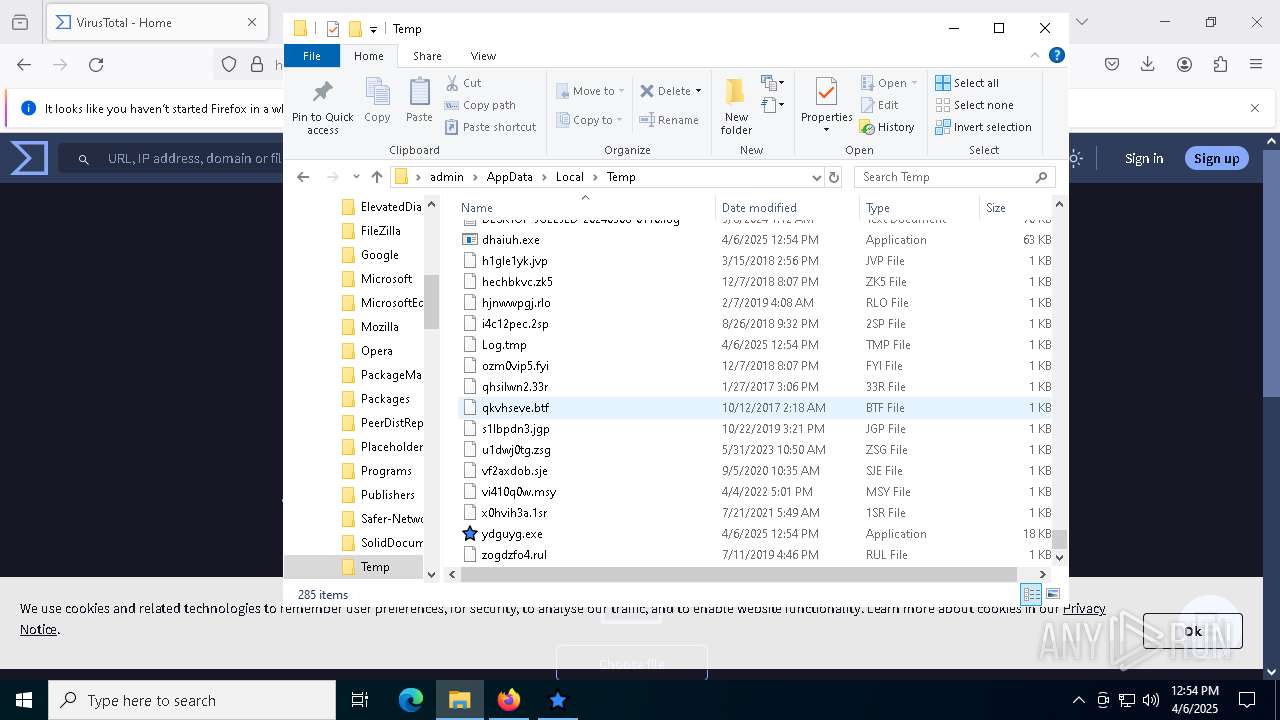
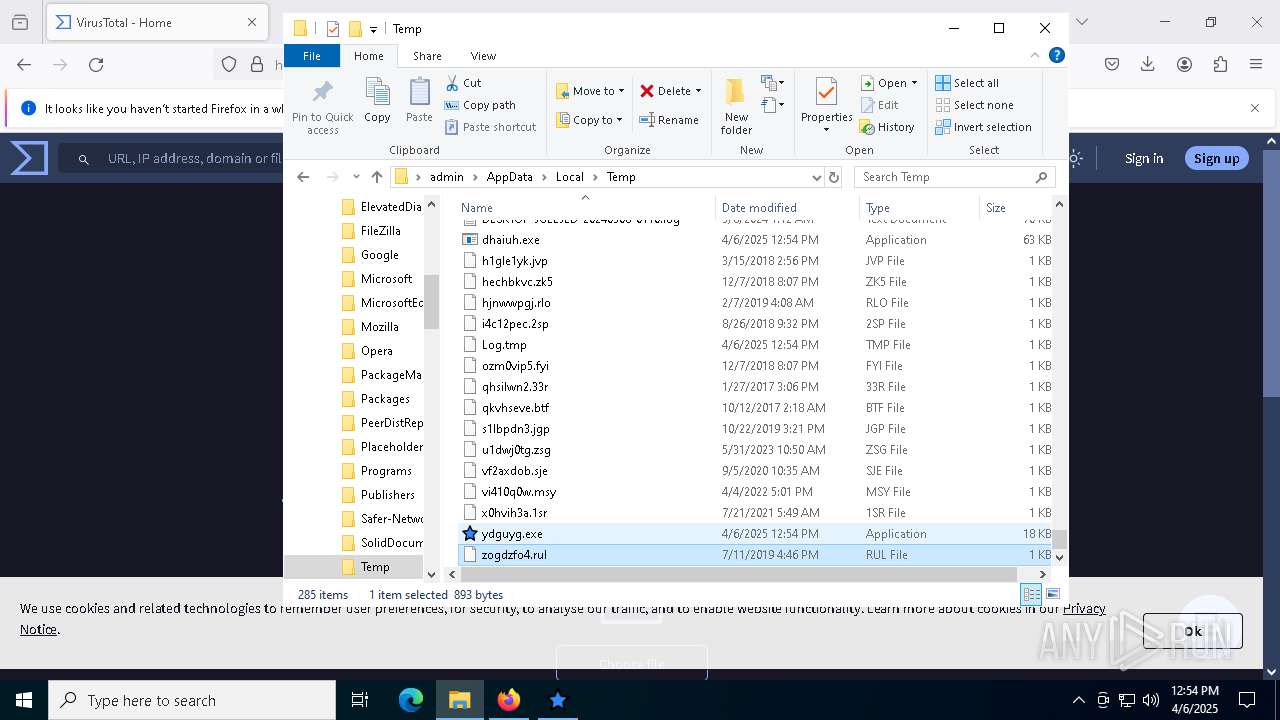
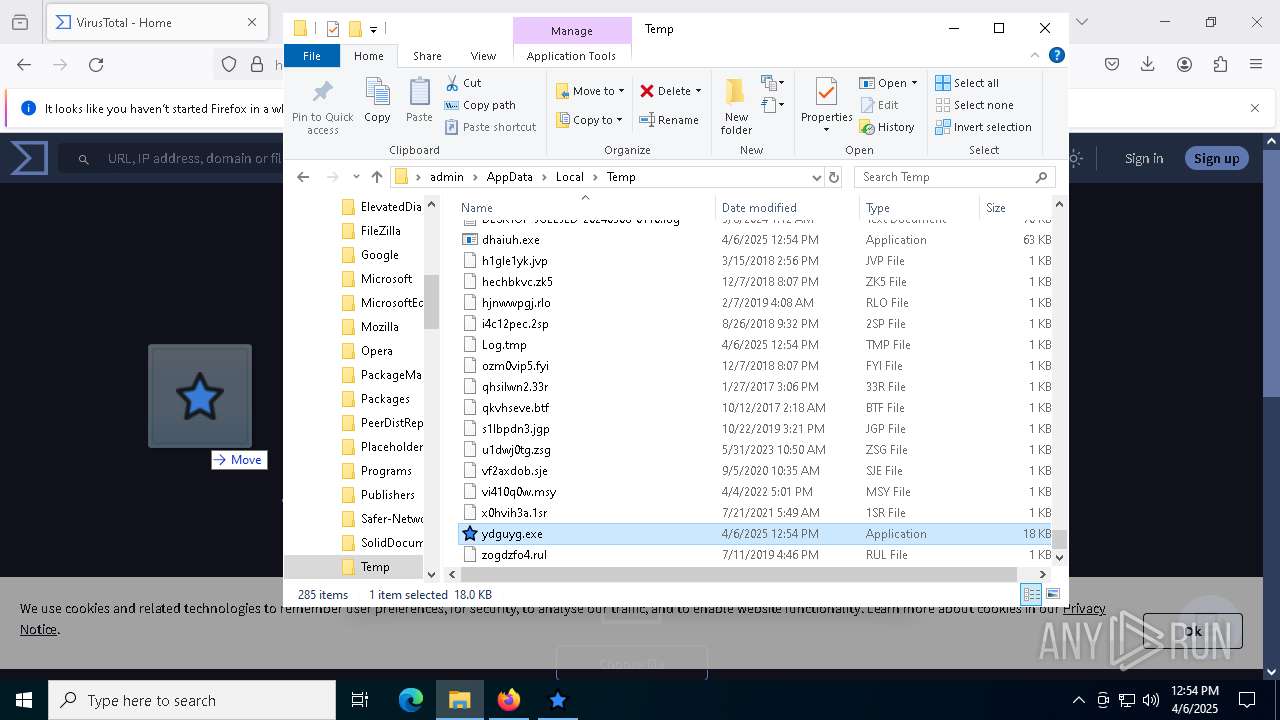
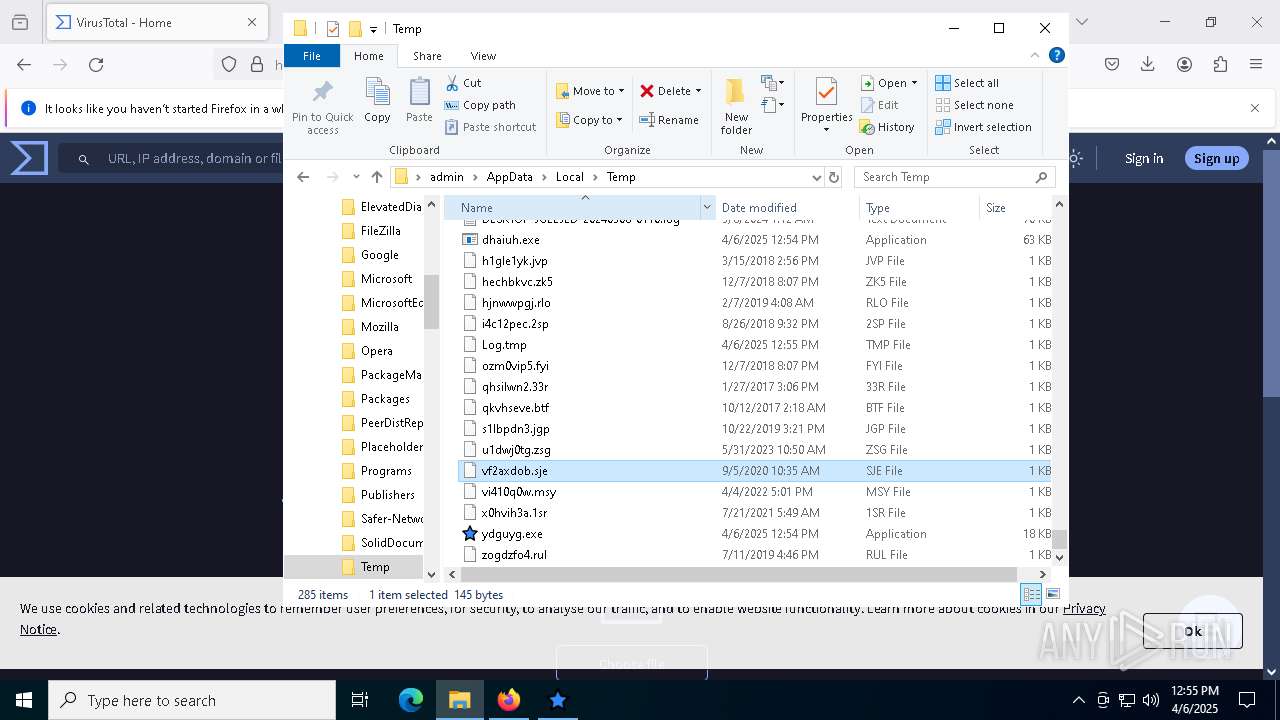
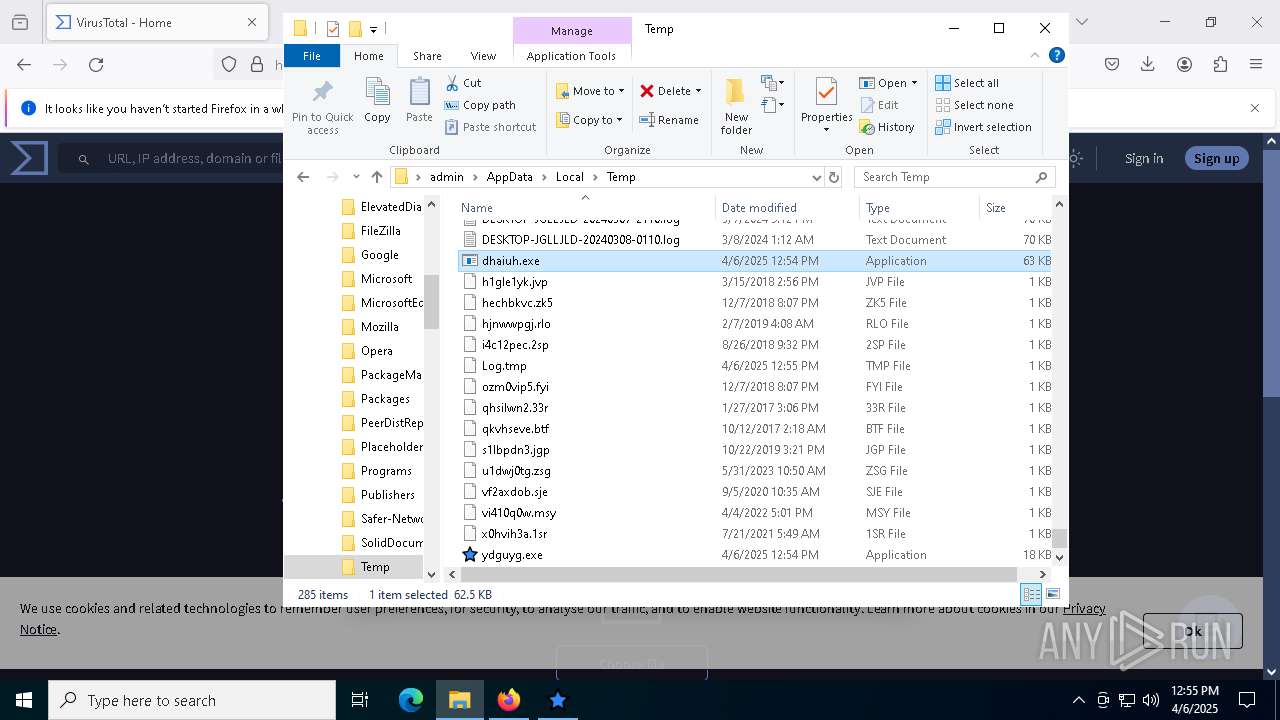
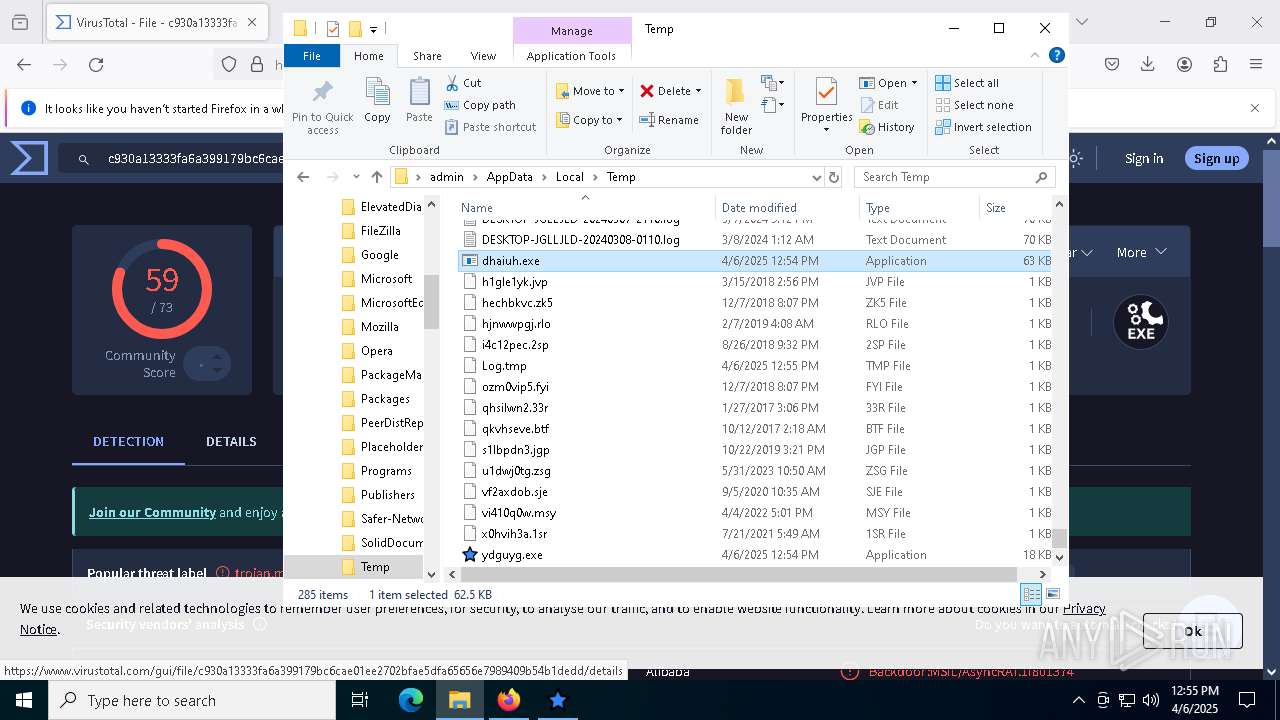
Create files in a temporary directory
- E Duper.exe (PID: 5552)
- csc.exe (PID: 8636)
- cvtres.exe (PID: 2240)
- dhaiuh.exe (PID: 6516)
Reads Environment values
- E Duper.exe (PID: 5552)
- dhaiuh.exe (PID: 6516)
Reads product name
- E Duper.exe (PID: 5552)
Reads the machine GUID from the registry
- csc.exe (PID: 8636)
- ydguyg.exe (PID: 8412)
- dhaiuh.exe (PID: 6516)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7036)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7036)
Disables trace logs
- powershell.exe (PID: 9052)
- powershell.exe (PID: 9000)
- dhaiuh.exe (PID: 6516)
Reads the computer name
- ydguyg.exe (PID: 8412)
- dhaiuh.exe (PID: 6516)
Checks proxy server information
- powershell.exe (PID: 9052)
- powershell.exe (PID: 9000)
- dhaiuh.exe (PID: 6516)
- slui.exe (PID: 7216)
The executable file from the user directory is run by the Powershell process
- dhaiuh.exe (PID: 6516)
- ydguyg.exe (PID: 8412)
Reads the software policy settings
- dhaiuh.exe (PID: 6516)
- slui.exe (PID: 8496)
- slui.exe (PID: 7216)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
XWorm
(PID) Process(6516) dhaiuh.exe
C2https://pastebin.com/raw/ZpWEzbQr:caprisun
Keys
AES<Xwormmm>
Options
Splitter3
Sleep timeXWorm V5.2
USB drop nameSystem Volume Information Prefetch.exe
Mutex4VdyZg72SquKXsEK
Total processes
176
Monitored processes
46
Malicious processes
8
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1512 | powershell -E QQBkAGQALQBUAHkAcABlACAAQAAiAAoAIAAgACAAIAB1AHMAaQBuAGcAIABTAHkAcwB0AGUAbQA7AAoAIAAgACAAIAB1AHMAaQBuAGcAIABTAHkAcwB0AGUAbQAuAFIAdQBuAHQAaQBtAGUALgBJAG4AdABlAHIAbwBwAFMAZQByAHYAaQBjAGUAcwA7AAoAIAAgACAAIABwAHUAYgBsAGkAYwAgAGMAbABhAHMAcwAgAEMAbwBuAHMAbwBsAGUAVwBpAG4AZABvAHcAVQB0AGkAbABzACAAewAKACAAIAAgACAAIAAgACAAIABbAEQAbABsAEkAbQBwAG8AcgB0ACgAIgBrAGUAcgBuAGUAbAAzADIALgBkAGwAbAAiACkAXQAKACAAIAAgACAAIAAgACAAIABwAHUAYgBsAGkAYwAgAHMAdABhAHQAaQBjACAAZQB4AHQAZQByAG4AIABJAG4AdABQAHQAcgAgAEcAZQB0AEMAbwBuAHMAbwBsAGUAVwBpAG4AZABvAHcAKAApADsACgAgACAAIAAgACAAIAAgACAACgAgACAAIAAgACAAIAAgACAAWwBEAGwAbABJAG0AcABvAHIAdAAoACIAdQBzAGUAcgAzADIALgBkAGwAbAAiACkAXQAKACAAIAAgACAAIAAgACAAIABwAHUAYgBsAGkAYwAgAHMAdABhAHQAaQBjACAAZQB4AHQAZQByAG4AIABJAG4AdABQAHQAcgAgAEcAZQB0AFAAYQByAGUAbgB0ACgASQBuAHQAUAB0AHIAIABoAFcAbgBkACkAOwAKAAoAIAAgACAAIAAgACAAIAAgAFsARABsAGwASQBtAHAAbwByAHQAKAAiAHUAcwBlAHIAMwAyAC4AZABsAGwAIgApAF0ACgAgACAAIAAgACAAIAAgACAAcAB1AGIAbABpAGMAIABzAHQAYQB0AGkAYwAgAGUAeAB0AGUAcgBuACAAYgBvAG8AbAAgAFMAaABvAHcAVwBpAG4AZABvAHcAKABJAG4AdABQAHQAcgAgAGgAVwBuAGQALAAgAGkAbgB0ACAAbgBDAG0AZABTAGgAbwB3ACkAOwAKACAAIAAgACAAIAAgACAAIAAKACAAIAAgACAAIAAgACAAIABwAHUAYgBsAGkAYwAgAHMAdABhAHQAaQBjACAASQBuAHQAUAB0AHIAIABHAGUAdABUAGEAcgBnAGUAdABXAGkAbgBkAG8AdwAoACkAIAB7AAoAIAAgACAAIAAgACAAIAAgACAAIAAgACAASQBuAHQAUAB0AHIAIABjAG8AbgBzAG8AbABlAFcAaQBuAGQAbwB3ACAAPQAgAEcAZQB0AEMAbwBuAHMAbwBsAGUAVwBpAG4AZABvAHcAKAApADsACgAgACAAIAAgACAAIAAgACAAIAAgACAAIABJAG4AdABQAHQAcgAgAHAAYQByAGUAbgB0AFcAaQBuAGQAbwB3ACAAPQAgAEcAZQB0AFAAYQByAGUAbgB0ACgAYwBvAG4AcwBvAGwAZQBXAGkAbgBkAG8AdwApADsACgAgACAAIAAgACAAIAAgACAAIAAgACAAIAAKACAAIAAgACAAIAAgACAAIAAgACAAIAAgAGkAZgAgACgAcABhAHIAZQBuAHQAVwBpAG4AZABvAHcAIAA9AD0AIABJAG4AdABQAHQAcgAuAFoAZQByAG8AKQAgAHsACgAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgAHIAZQB0AHUAcgBuACAAYwBvAG4AcwBvAGwAZQBXAGkAbgBkAG8AdwA7AAoAIAAgACAAIAAgACAAIAAgACAAIAAgACAAfQAKACAAIAAgACAAIAAgACAAIAAgACAAIAAgAHIAZQB0AHUAcgBuACAAcABhAHIAZQBuAHQAVwBpAG4AZABvAHcAOwAKACAAIAAgACAAIAAgACAAIAB9AAoAIAAgACAAIAB9AAoAIgBAAAoACgBbAEMAbwBuAHMAbwBsAGUAVwBpAG4AZABvAHcAVQB0AGkAbABzAF0AOgA6AFMAaABvAHcAVwBpAG4AZABvAHcAKABbAEMAbwBuAHMAbwBsAGUAVwBpAG4AZABvAHcAVQB0AGkAbABzAF0AOgA6AEcAZQB0AFQAYQByAGcAZQB0AFcAaQBuAGQAbwB3ACgAKQAsACAAMAApACAAfAAgAE8AdQB0AC0ATgB1AGwAbAA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2096 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5336 -childID 6 -isForBrowser -prefsHandle 5256 -prefMapHandle 5264 -prefsLen 31243 -prefMapSize 244583 -jsInitHandle 1352 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {c1a011dc-bcde-4b6b-9863-3f47147618a2} 7476 "\\.\pipe\gecko-crash-server-pipe.7476" 1cc05633690 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2240 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES59C5.tmp" "c:\Users\admin\AppData\Local\Temp\CSCD090C76A704446B2B4AB1F163C7AF4B9.TMP" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.32.31326.0 Modules
| |||||||||||||||
| 2268 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4360 -childID 7 -isForBrowser -prefsHandle 5168 -prefMapHandle 5912 -prefsLen 31555 -prefMapSize 244583 -jsInitHandle 1352 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {96da2b53-cc0f-4dde-af35-a2e5eb3038e9} 7476 "\\.\pipe\gecko-crash-server-pipe.7476" 1cbff5d2f50 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 3300 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\E Duper.zip" "C:\Users\admin\Downloads\E Duper\" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3332 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\76e4ff66729463153ddcdf09b1a4ad3e.bat" hidden " | C:\Windows\System32\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4212 | C:\WINDOWS\system32\net1 session | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4620 | cmd.exe /C call powershell -E QQBkAGQALQBUAHkAcABlACAAQAAiAAoAIAAgACAAIAB1AHMAaQBuAGcAIABTAHkAcwB0AGUAbQA7AAoAIAAgACAAIAB1AHMAaQBuAGcAIABTAHkAcwB0AGUAbQAuAFIAdQBuAHQAaQBtAGUALgBJAG4AdABlAHIAbwBwAFMAZQByAHYAaQBjAGUAcwA7AAoAIAAgACAAIABwAHUAYgBsAGkAYwAgAGMAbABhAHMAcwAgAEMAbwBuAHMAbwBsAGUAVwBpAG4AZABvAHcAVQB0AGkAbABzACAAewAKACAAIAAgACAAIAAgACAAIABbAEQAbABsAEkAbQBwAG8AcgB0ACgAIgBrAGUAcgBuAGUAbAAzADIALgBkAGwAbAAiACkAXQAKACAAIAAgACAAIAAgACAAIABwAHUAYgBsAGkAYwAgAHMAdABhAHQAaQBjACAAZQB4AHQAZQByAG4AIABJAG4AdABQAHQAcgAgAEcAZQB0AEMAbwBuAHMAbwBsAGUAVwBpAG4AZABvAHcAKAApADsACgAgACAAIAAgACAAIAAgACAACgAgACAAIAAgACAAIAAgACAAWwBEAGwAbABJAG0AcABvAHIAdAAoACIAdQBzAGUAcgAzADIALgBkAGwAbAAiACkAXQAKACAAIAAgACAAIAAgACAAIABwAHUAYgBsAGkAYwAgAHMAdABhAHQAaQBjACAAZQB4AHQAZQByAG4AIABJAG4AdABQAHQAcgAgAEcAZQB0AFAAYQByAGUAbgB0ACgASQBuAHQAUAB0AHIAIABoAFcAbgBkACkAOwAKAAoAIAAgACAAIAAgACAAIAAgAFsARABsAGwASQBtAHAAbwByAHQAKAAiAHUAcwBlAHIAMwAyAC4AZABsAGwAIgApAF0ACgAgACAAIAAgACAAIAAgACAAcAB1AGIAbABpAGMAIABzAHQAYQB0AGkAYwAgAGUAeAB0AGUAcgBuACAAYgBvAG8AbAAgAFMAaABvAHcAVwBpAG4AZABvAHcAKABJAG4AdABQAHQAcgAgAGgAVwBuAGQALAAgAGkAbgB0ACAAbgBDAG0AZABTAGgAbwB3ACkAOwAKACAAIAAgACAAIAAgACAAIAAKACAAIAAgACAAIAAgACAAIABwAHUAYgBsAGkAYwAgAHMAdABhAHQAaQBjACAASQBuAHQAUAB0AHIAIABHAGUAdABUAGEAcgBnAGUAdABXAGkAbgBkAG8AdwAoACkAIAB7AAoAIAAgACAAIAAgACAAIAAgACAAIAAgACAASQBuAHQAUAB0AHIAIABjAG8AbgBzAG8AbABlAFcAaQBuAGQAbwB3ACAAPQAgAEcAZQB0AEMAbwBuAHMAbwBsAGUAVwBpAG4AZABvAHcAKAApADsACgAgACAAIAAgACAAIAAgACAAIAAgACAAIABJAG4AdABQAHQAcgAgAHAAYQByAGUAbgB0AFcAaQBuAGQAbwB3ACAAPQAgAEcAZQB0AFAAYQByAGUAbgB0ACgAYwBvAG4AcwBvAGwAZQBXAGkAbgBkAG8AdwApADsACgAgACAAIAAgACAAIAAgACAAIAAgACAAIAAKACAAIAAgACAAIAAgACAAIAAgACAAIAAgAGkAZgAgACgAcABhAHIAZQBuAHQAVwBpAG4AZABvAHcAIAA9AD0AIABJAG4AdABQAHQAcgAuAFoAZQByAG8AKQAgAHsACgAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgAHIAZQB0AHUAcgBuACAAYwBvAG4AcwBvAGwAZQBXAGkAbgBkAG8AdwA7AAoAIAAgACAAIAAgACAAIAAgACAAIAAgACAAfQAKACAAIAAgACAAIAAgACAAIAAgACAAIAAgAHIAZQB0AHUAcgBuACAAcABhAHIAZQBuAHQAVwBpAG4AZABvAHcAOwAKACAAIAAgACAAIAAgACAAIAB9AAoAIAAgACAAIAB9AAoAIgBAAAoACgBbAEMAbwBuAHMAbwBsAGUAVwBpAG4AZABvAHcAVQB0AGkAbABzAF0AOgA6AFMAaABvAHcAVwBpAG4AZABvAHcAKABbAEMAbwBuAHMAbwBsAGUAVwBpAG4AZABvAHcAVQB0AGkAbABzAF0AOgA6AEcAZQB0AFQAYQByAGcAZQB0AFcAaQBuAGQAbwB3ACgAKQAsACAAMAApACAAfAAgAE8AdQB0AC0ATgB1AGwAbAA= | C:\Windows\System32\cmd.exe | — | E Duper.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4736 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4692 -parentBuildID 20240213221259 -sandboxingKind 0 -prefsHandle 4800 -prefMapHandle 4812 -prefsLen 36588 -prefMapSize 244583 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {cec9eb61-b137-401a-9782-f4e8c5239617} 7476 "\\.\pipe\gecko-crash-server-pipe.7476" 1cc040a4b10 utility | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
Total events
55 962
Read events
55 923
Write events
39
Delete events
0
Modification events
| (PID) Process: | (7476) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (8976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (8976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (8976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (8976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\E Duper.zip | |||
| (PID) Process: | (8976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (8976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (8976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (8976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (8976) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
Executable files
3
Suspicious files
198
Text files
50
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7476 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 7476 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 7476 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 7476 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 7476 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7476 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\datareporting\glean\db\data.safe.tmp | binary | |
MD5:EF90022DF0735160DD056C0E6670E915 | SHA256:2B663C0B462A437C8DE3D9B95EE157AE181249B78BDD6F7BD73F7EB6D9E03F87 | |||
| 7476 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 7476 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7476 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7476 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
46
TCP/UDP connections
130
DNS requests
155
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7476 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
7476 | firefox.exe | POST | 200 | 2.16.206.148:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
7476 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
7476 | firefox.exe | POST | 200 | 2.16.206.148:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
7476 | firefox.exe | POST | 200 | 142.250.186.35:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
7476 | firefox.exe | POST | 200 | 142.250.186.35:80 | http://o.pki.goog/s/wr3/cgo | unknown | — | — | whitelisted |
7476 | firefox.exe | POST | 200 | 2.16.206.143:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
7476 | firefox.exe | POST | — | 142.250.186.35:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
7476 | firefox.exe | POST | 200 | 142.250.186.35:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.216.77.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.172.255.218:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7476 | firefox.exe | 34.117.188.166:443 | contile.services.mozilla.com | — | — | whitelisted |
7476 | firefox.exe | 216.58.212.138:443 | safebrowsing.googleapis.com | — | — | whitelisted |
7476 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
7476 | firefox.exe | 142.250.186.174:443 | www.youtube.com | GOOGLE | US | whitelisted |
7476 | firefox.exe | 34.107.243.93:443 | push.services.mozilla.com | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
www.youtube.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
youtube-ui.l.google.com |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
example.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |
6516 | dhaiuh.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
6516 | dhaiuh.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
6516 | dhaiuh.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] Xworm TCP Packet |