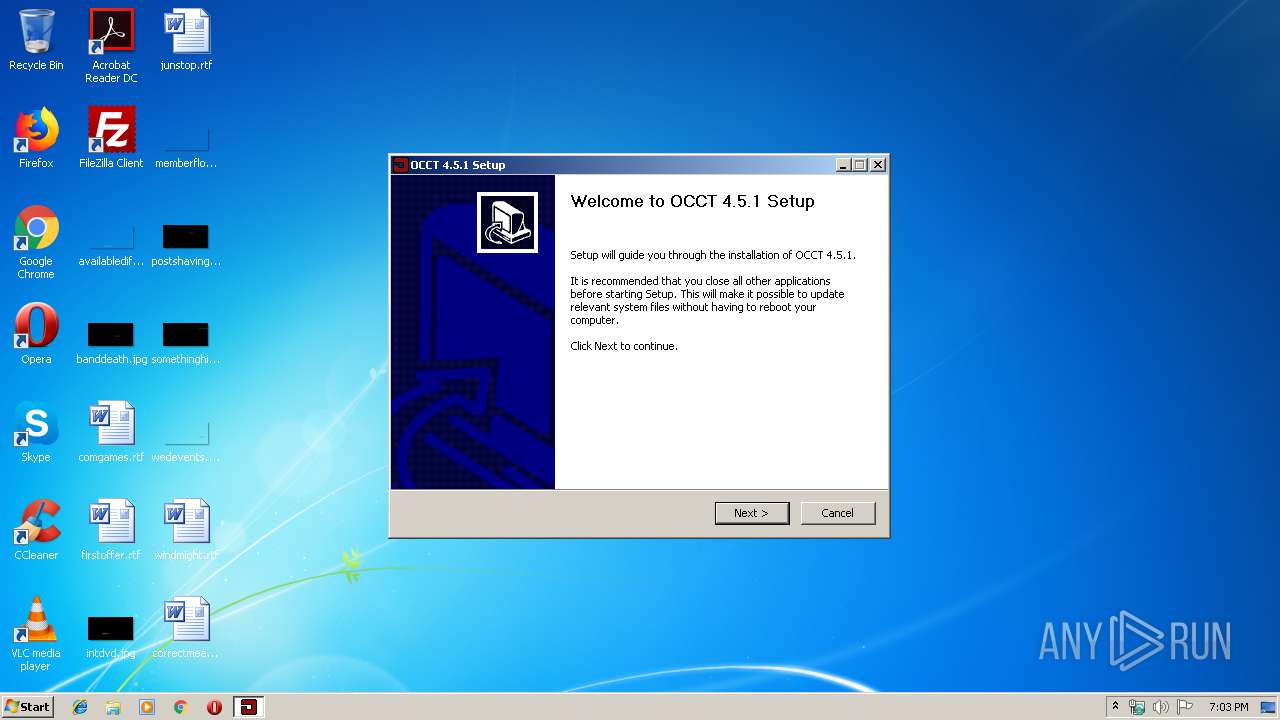
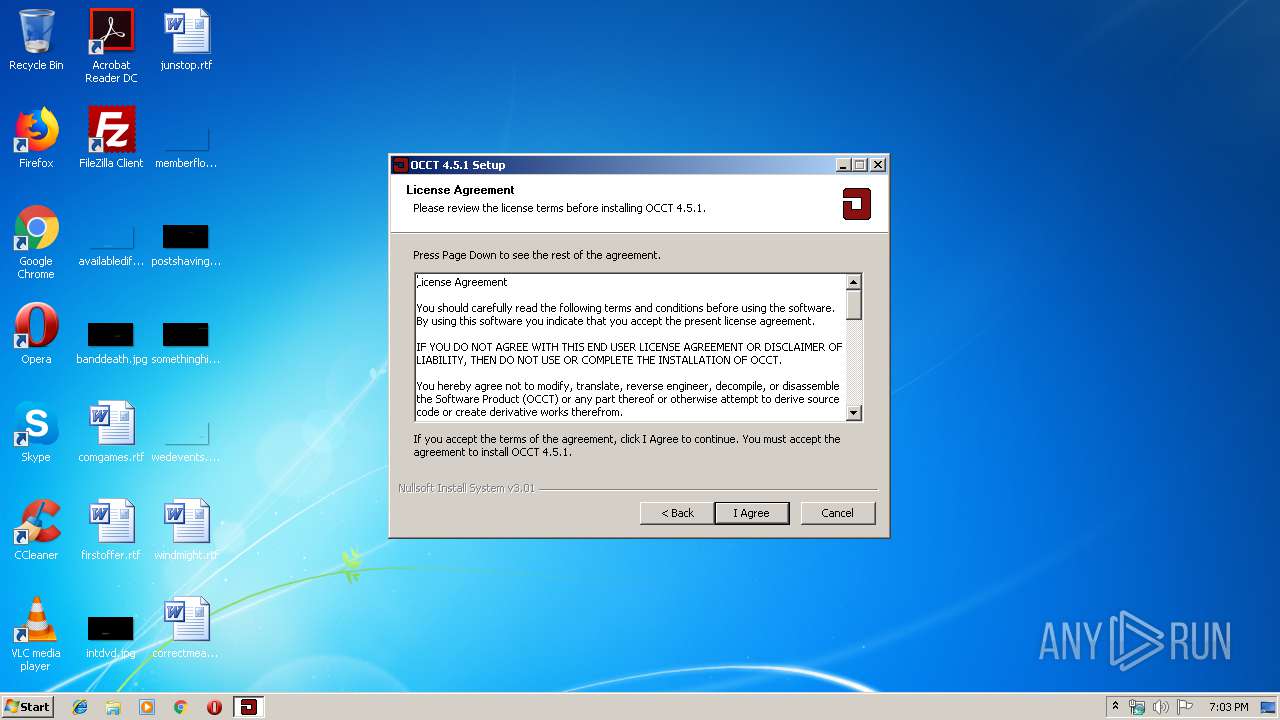
| File name: | OCCTPT4.5.1.exe |
| Full analysis: | https://app.any.run/tasks/49ea3d67-fe06-45f7-a010-819671b592a3 |
| Verdict: | Malicious activity |
| Analysis date: | November 10, 2019, 19:03:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 1375A2357431BCB928334068297B5266 |
| SHA1: | 6A84949103B885B9A0107E00EBEFB30EDBD587EA |
| SHA256: | 936457C564731C0FAB37E869C884F2D13F2115966C3FBD24C9167380BAF771BB |
| SSDEEP: | 196608:c7GSse8s/6af0ewwo+qYX3OclW+dBgma++jO1mNbec:c7GSsTafFkcXj7gma++qMbec |
MALICIOUS
Loads dropped or rewritten executable
- OCCTPT4.5.1.exe (PID: 4080)
- OCCT.exe (PID: 892)
Starts Visual C# compiler
- OCCT.exe (PID: 892)
Changes settings of System certificates
- OCCT.exe (PID: 892)
SUSPICIOUS
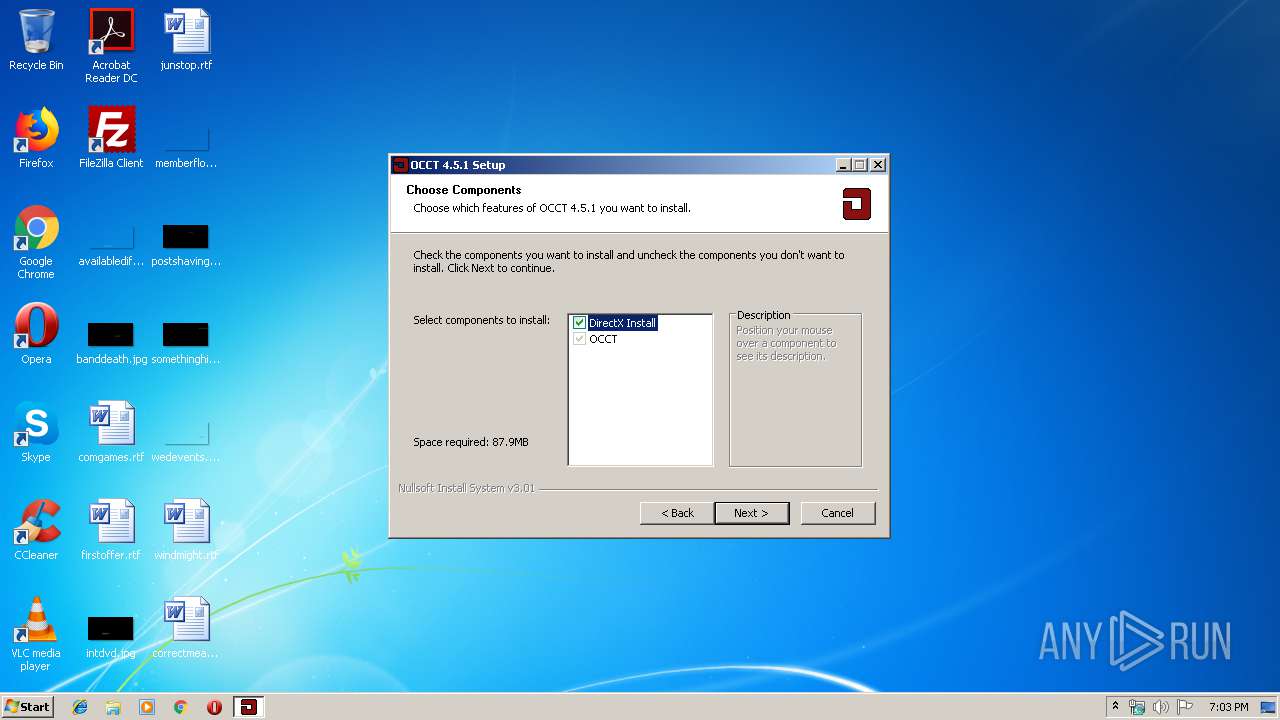
Executable content was dropped or overwritten
- OCCTPT4.5.1.exe (PID: 4080)
- OCCT.exe (PID: 892)
Creates a software uninstall entry
- OCCTPT4.5.1.exe (PID: 4080)
Creates files in the program directory
- OCCTPT4.5.1.exe (PID: 4080)
Creates files in the user directory
- OCCTPT4.5.1.exe (PID: 4080)
Adds / modifies Windows certificates
- OCCT.exe (PID: 892)
Creates files in the Windows directory
- OCCT.exe (PID: 892)
Low-level read access rights to disk partition
- OCCT.exe (PID: 892)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:12:11 22:50:45+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24576 |
| InitializedDataSize: | 118784 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x32bf |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-Dec-2016 21:50:45 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 11-Dec-2016 21:50:45 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005E59 | 0x00006000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.42419 |
.rdata | 0x00007000 | 0x00001246 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.0004 |
.data | 0x00009000 | 0x0001A818 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.21193 |
.ndata | 0x00024000 | 0x0000A000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0002E000 | 0x000083D0 | 0x00008400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.51226 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28813 | 1070 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 1.18752 | 3752 | UNKNOWN | English - United States | RT_ICON |
3 | 1.09189 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 0.646021 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 0 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 0 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 0 | 296 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.86546 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
104 | 2.70411 | 344 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
44
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 892 | "C:\Program Files\OCCTPT\OCCT.exe" | C:\Program Files\OCCTPT\OCCT.exe | OCCTPT4.5.1.exe | ||||||||||||
User: admin Company: OCCT - Ocbase - Adrien Mercier Integrity Level: HIGH Description: OCCT Exit code: 0 Version: 4.5.1.99 Modules
| |||||||||||||||
| 2868 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\vanjhtsq.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | — | OCCT.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 3032 | "C:\Users\admin\AppData\Local\Temp\OCCTPT4.5.1.exe" | C:\Users\admin\AppData\Local\Temp\OCCTPT4.5.1.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3364 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RESFB92.tmp" "c:\Users\admin\AppData\Local\Temp\CSCFB91.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 4080 | "C:\Users\admin\AppData\Local\Temp\OCCTPT4.5.1.exe" | C:\Users\admin\AppData\Local\Temp\OCCTPT4.5.1.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
420
Read events
389
Write events
31
Delete events
0
Modification events
| (PID) Process: | (4080) OCCTPT4.5.1.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\App Paths\OCCT.exe |
| Operation: | write | Name: | |
Value: C:\Program Files\OCCTPT\OCCT.exe | |||
| (PID) Process: | (4080) OCCTPT4.5.1.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\OCCT |
| Operation: | write | Name: | DisplayName |
Value: OCCT 4.5.1 | |||
| (PID) Process: | (4080) OCCTPT4.5.1.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\OCCT |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\OCCTPT\uninst.exe | |||
| (PID) Process: | (4080) OCCTPT4.5.1.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\OCCT |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\OCCTPT\OCCT.exe | |||
| (PID) Process: | (4080) OCCTPT4.5.1.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\OCCT |
| Operation: | write | Name: | DisplayVersion |
Value: 4.5.1 | |||
| (PID) Process: | (4080) OCCTPT4.5.1.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\OCCT |
| Operation: | write | Name: | URLInfoAbout |
Value: http://www.ocbase.com | |||
| (PID) Process: | (4080) OCCTPT4.5.1.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\OCCT |
| Operation: | write | Name: | Publisher |
Value: Ocbase.com | |||
| (PID) Process: | (4080) OCCTPT4.5.1.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\OCCT |
| Operation: | write | Name: | NSIS:Language |
Value: 1033 | |||
| (PID) Process: | (892) OCCT.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\OCCT_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (892) OCCT.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\OCCT_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
16
Suspicious files
0
Text files
53
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4080 | OCCTPT4.5.1.exe | C:\Program Files\OCCTPT\OCCT.exe | — | |
MD5:— | SHA256:— | |||
| 4080 | OCCTPT4.5.1.exe | C:\Users\admin\AppData\Local\Temp\nsuB8EC.tmp\ioSpecial.ini | text | |
MD5:— | SHA256:— | |||
| 4080 | OCCTPT4.5.1.exe | C:\Program Files\OCCTPT\GPU3DName.txt | text | |
MD5:— | SHA256:— | |||
| 4080 | OCCTPT4.5.1.exe | C:\Users\admin\AppData\Local\Temp\nsuB8EC.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 4080 | OCCTPT4.5.1.exe | C:\Users\admin\AppData\Local\Temp\nsuB8EC.tmp\LangDLL.dll | executable | |
MD5:B26B412D9F1050AD53F663C972FDCD9F | SHA256:70C842F318F691D92E5829616A283AA9BF9DC18CEA6F39BAD028E176056B591A | |||
| 4080 | OCCTPT4.5.1.exe | C:\Users\admin\AppData\Local\Temp\nsuB8EC.tmp\InstallOptions.dll | executable | |
MD5:3E277798B9D8F48806FBB5EBFD4990DB | SHA256:FE19353288A08A5D2640A9C022424A1D20E4909A351F2114423E087313A40D7C | |||
| 4080 | OCCTPT4.5.1.exe | C:\Program Files\OCCTPT\error.wav | wav | |
MD5:DCDA9D8947B0E8BB8EAAE9212EC4179B | SHA256:96FD21810715242C3441C7C06B966E06494ACF1D51198E1DDB35A135D9F24937 | |||
| 4080 | OCCTPT4.5.1.exe | C:\Users\admin\Desktop\OCCT.lnk | lnk | |
MD5:— | SHA256:— | |||
| 4080 | OCCTPT4.5.1.exe | C:\Program Files\OCCTPT\Plugins\AIDA64.dll | executable | |
MD5:— | SHA256:— | |||
| 4080 | OCCTPT4.5.1.exe | C:\Program Files\OCCTPT\occtaux.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 37.59.50.132:80 | www.ocbase.com | OVH SAS | FR | unknown |
892 | OCCT.exe | 37.59.50.132:443 | www.ocbase.com | OVH SAS | FR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.ocbase.com |
| unknown |