| File name: | MatSploit_1.rar |
| Full analysis: | https://app.any.run/tasks/dac838cf-8ea0-4e42-b52e-638676ddd251 |
| Verdict: | Malicious activity |
| Analysis date: | June 03, 2020, 23:42:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | BA9C035A0DCBAD64DEAE45FB7A66C104 |
| SHA1: | 43D08BFA14BC93DE259C6579EEAEFDB9FF27EBA9 |
| SHA256: | 9343B716A9C4624606301671EBB3E8314D8138CAF474F97F975A073C9F1BDBF1 |
| SSDEEP: | 98304:L352xs5NtZYh28jUEVbi2ndvaQwsiw58gfdy+J:L1NtZczBbisaQwO+gfdBJ |
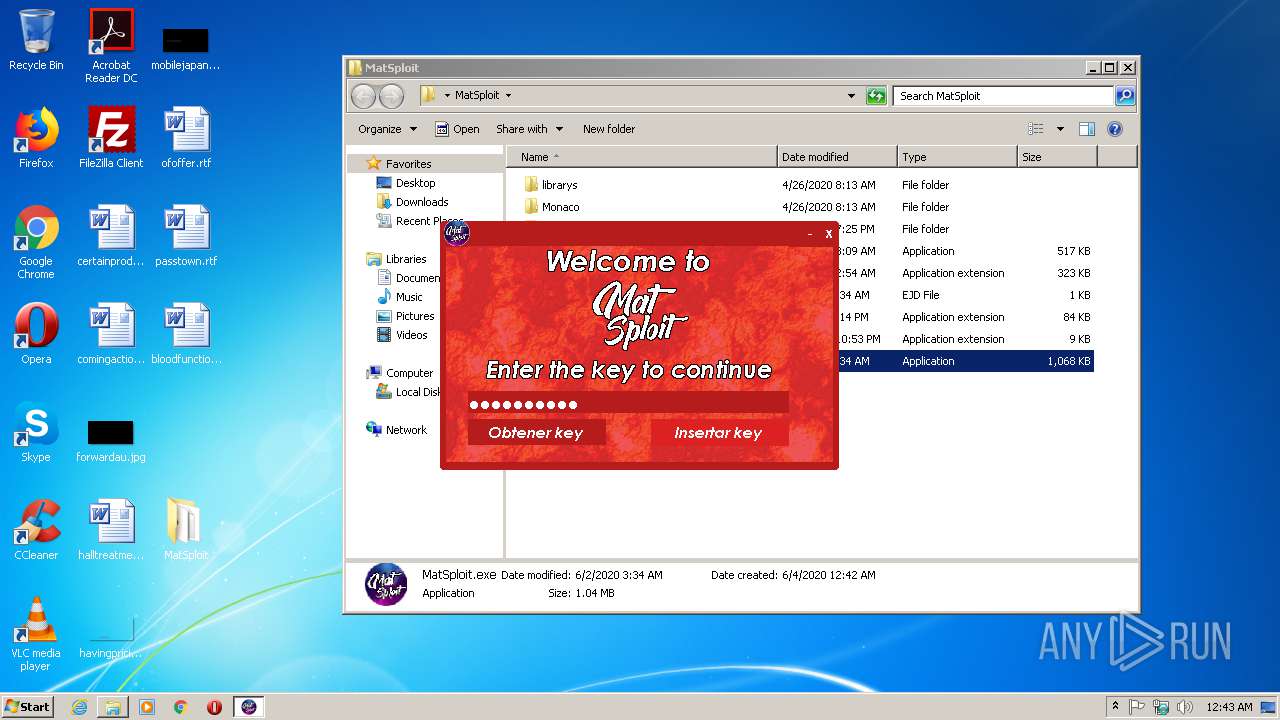
MALICIOUS
Application was dropped or rewritten from another process
- MatSploit.exe (PID: 332)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3376)
- MatSploit.exe (PID: 332)
SUSPICIOUS
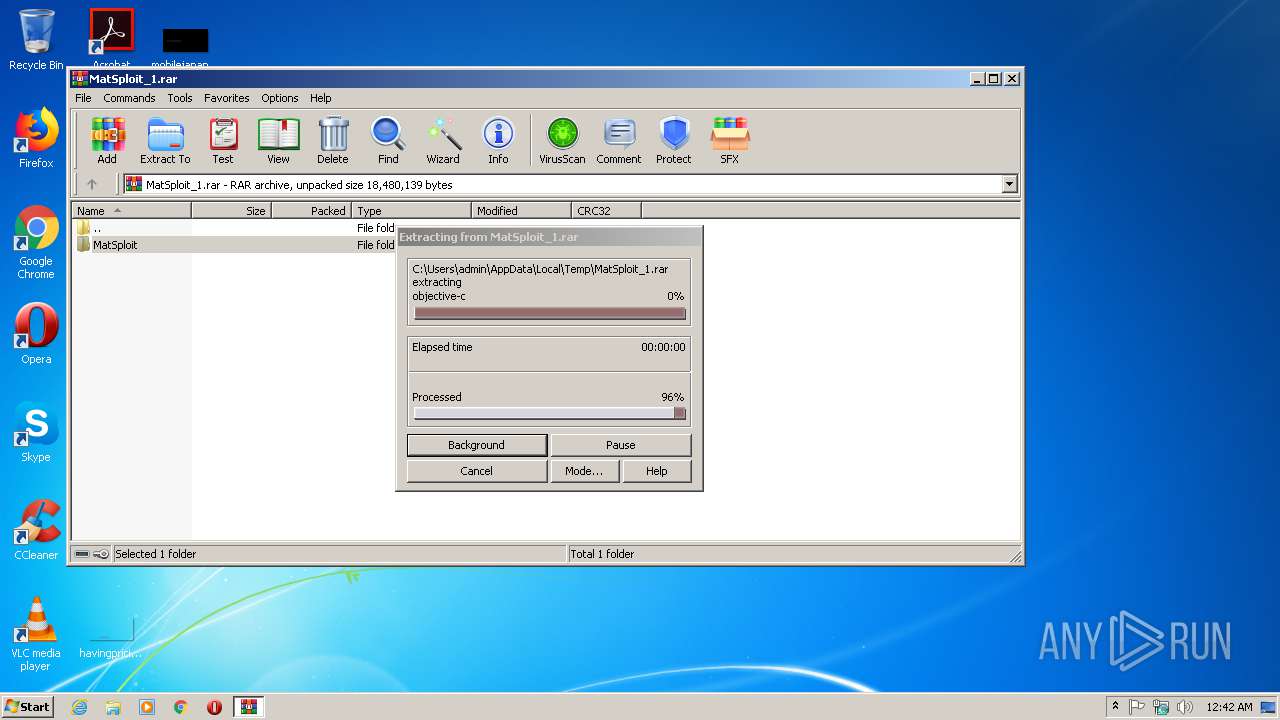
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1456)
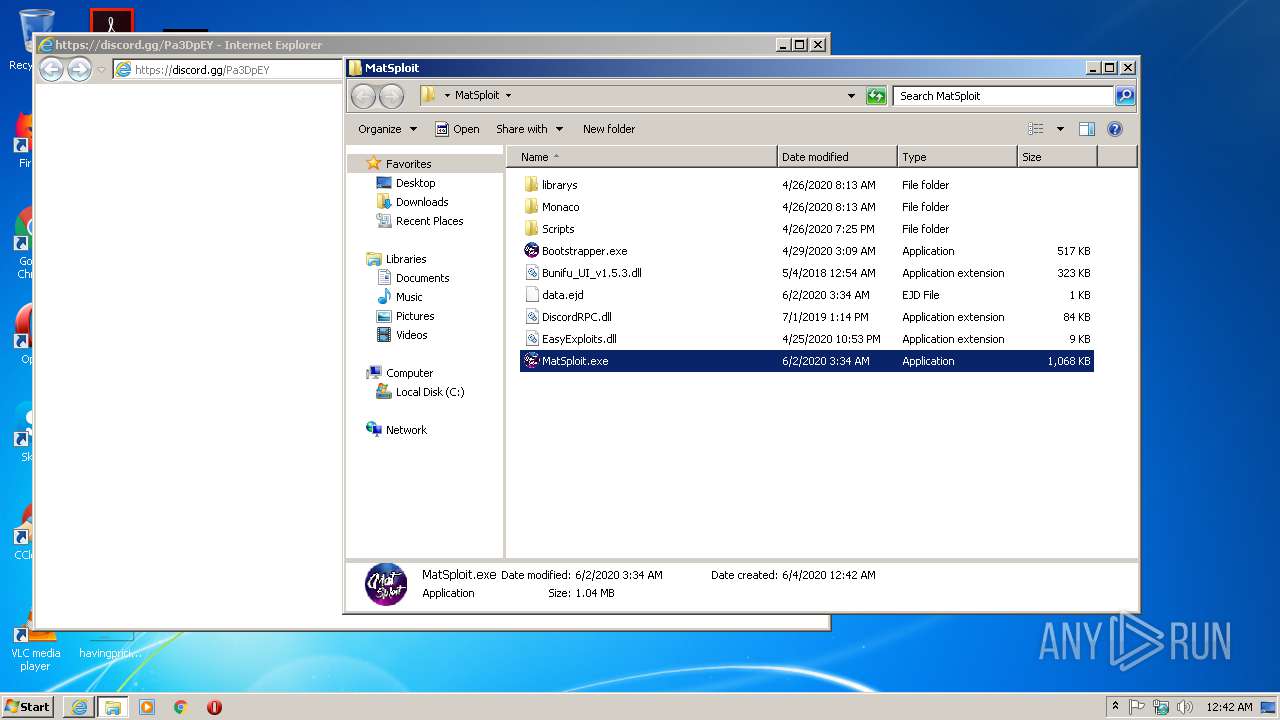
Starts Internet Explorer
- MatSploit.exe (PID: 332)
INFO
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 1456)
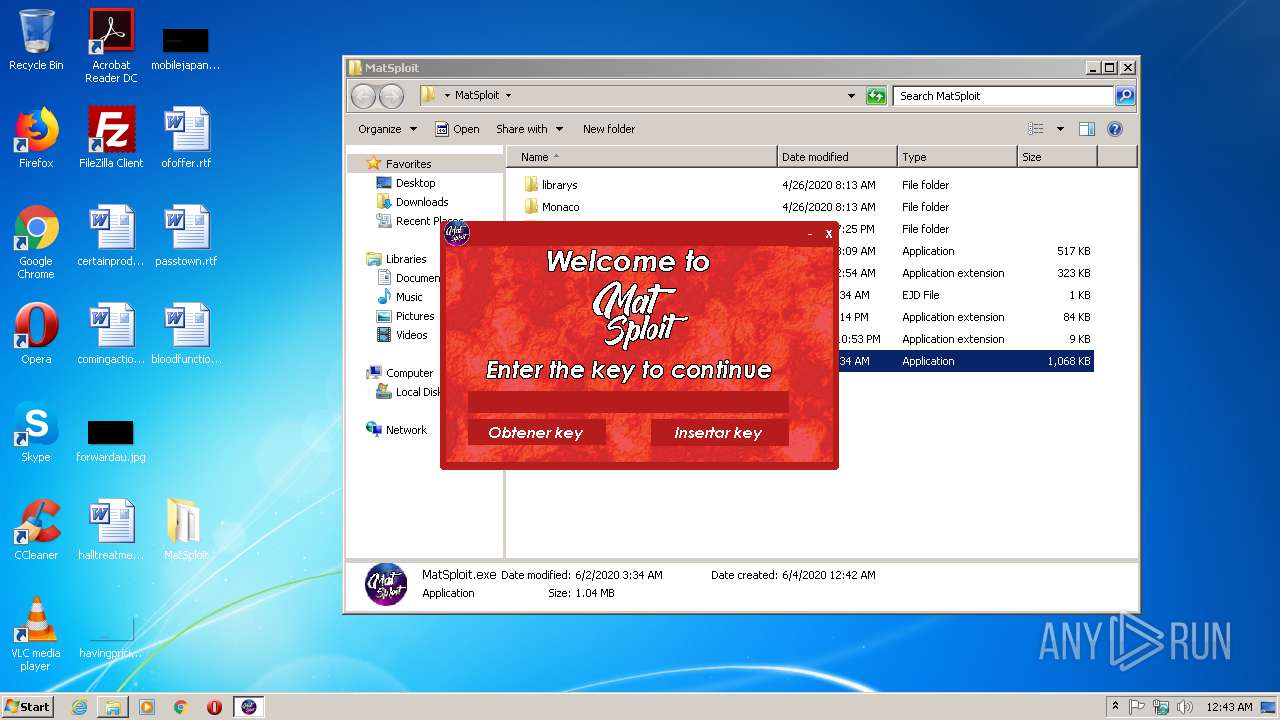
Manual execution by user
- MatSploit.exe (PID: 332)
Application launched itself
- iexplore.exe (PID: 2596)
Reads Internet Cache Settings
- iexplore.exe (PID: 2596)
- iexplore.exe (PID: 1928)
Changes internet zones settings
- iexplore.exe (PID: 2596)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
38
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
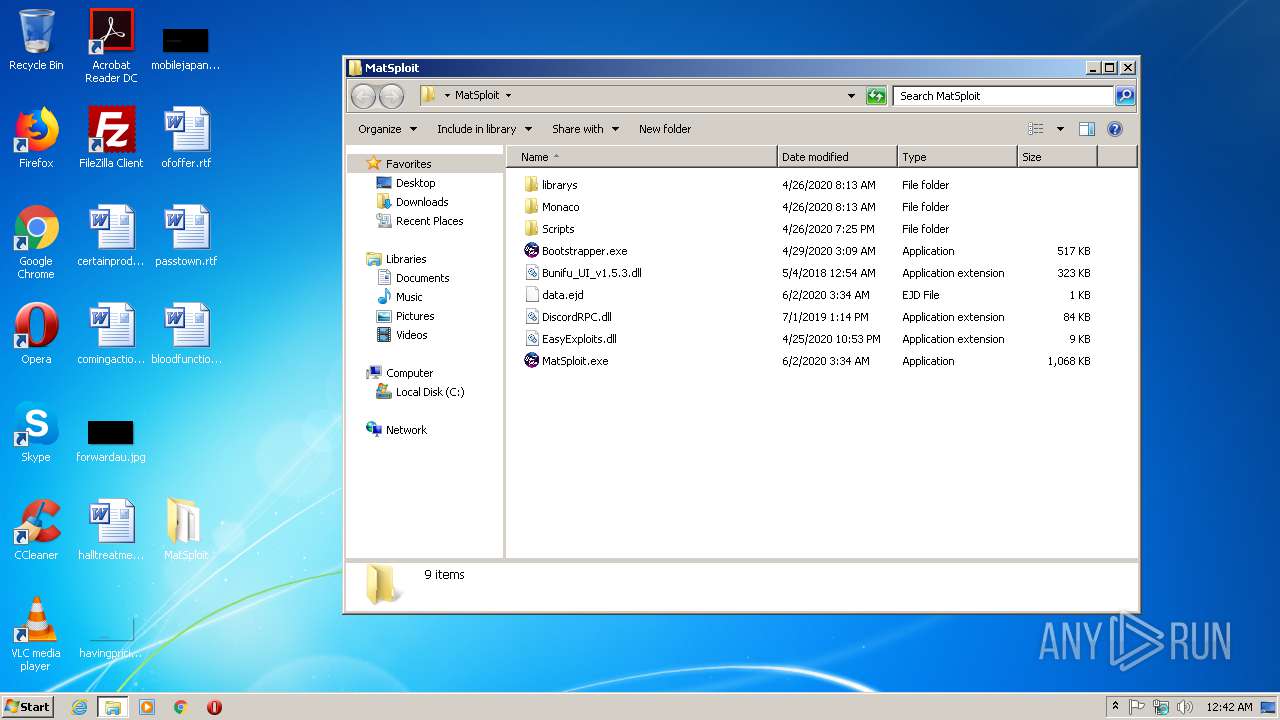
| 332 | "C:\Users\admin\Desktop\MatSploit\MatSploit.exe" | C:\Users\admin\Desktop\MatSploit\MatSploit.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: MatSploit Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
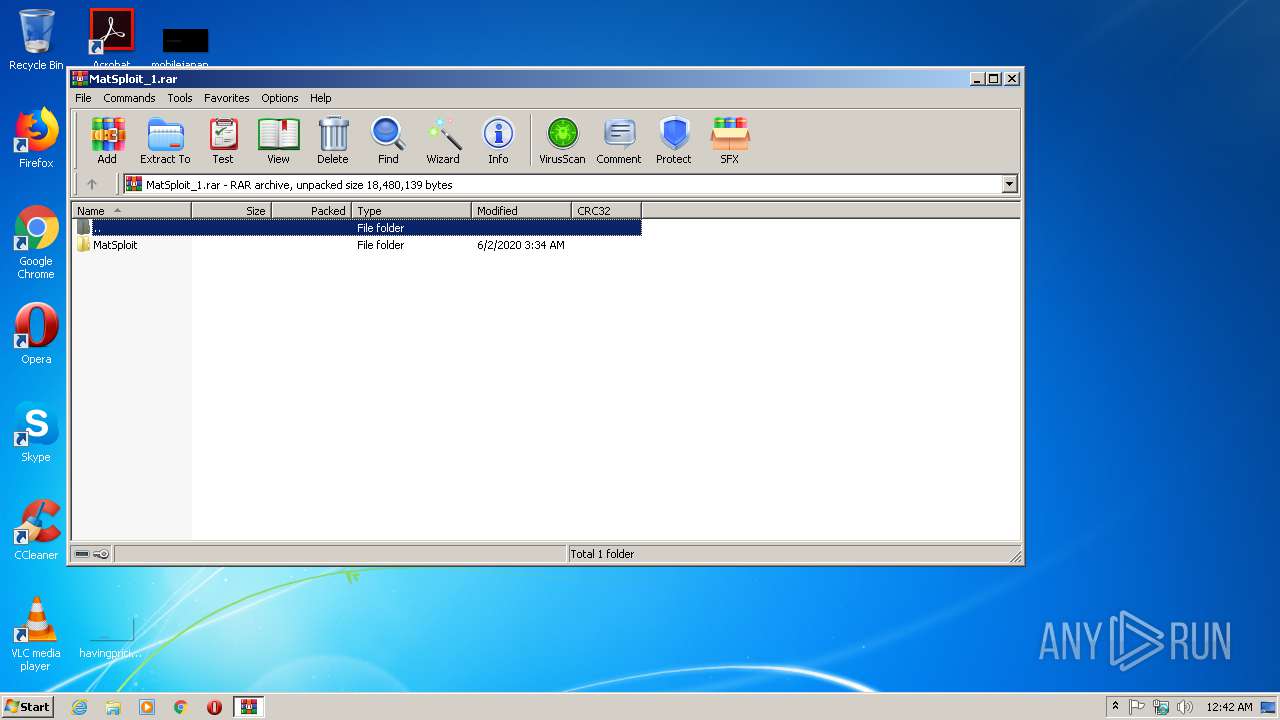
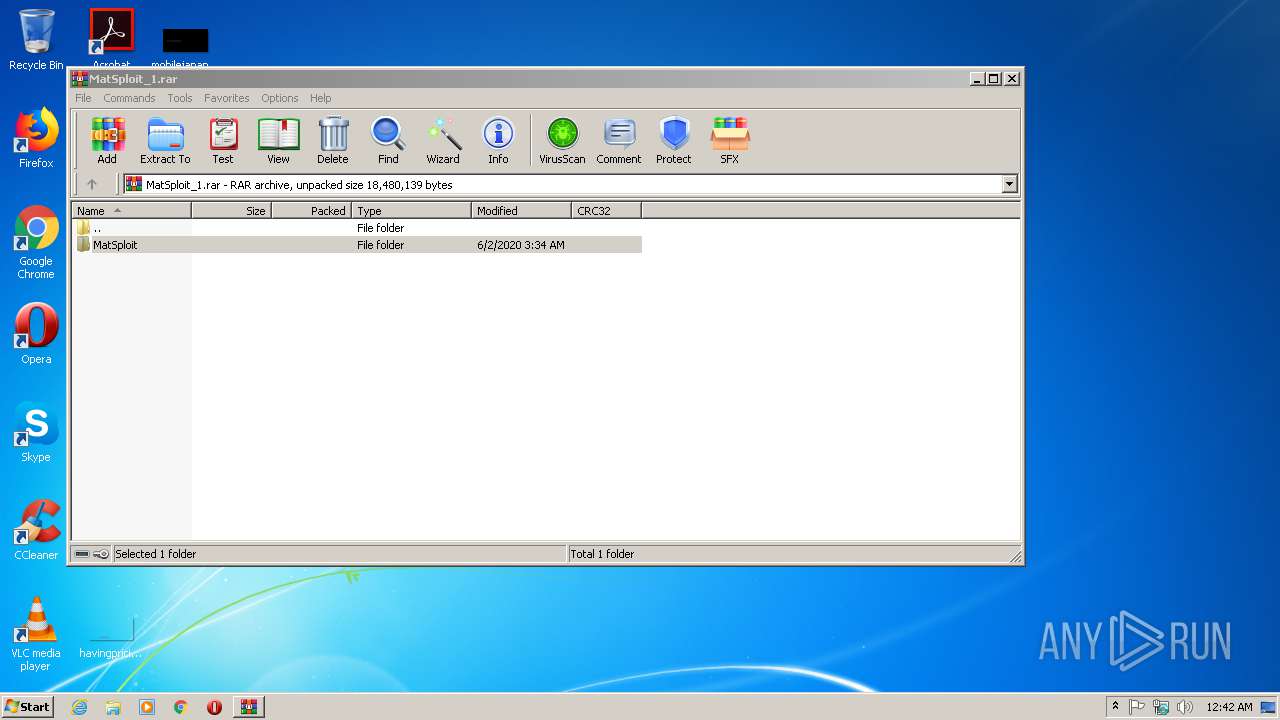
| 1456 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\MatSploit_1.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1928 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2596 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2596 | "C:\Program Files\Internet Explorer\iexplore.exe" https://discord.gg/Pa3DpEY | C:\Program Files\Internet Explorer\iexplore.exe | — | MatSploit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3376 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe4_ Global\UsGthrCtrlFltPipeMssGthrPipe4 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 046
Read events
959
Write events
83
Delete events
4
Modification events
| (PID) Process: | (1456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1456) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1456) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (1456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\MatSploit_1.rar | |||
| (PID) Process: | (1456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
6
Suspicious files
6
Text files
86
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1456.9420\MatSploit\DiscordRPC.dll | executable | |
MD5:— | SHA256:— | |||
| 1456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1456.9420\MatSploit\Bootstrapper.exe | executable | |
MD5:— | SHA256:— | |||
| 1456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1456.9420\MatSploit\Bunifu_UI_v1.5.3.dll | executable | |
MD5:E0EF2817EE5A7C8CD1EB837195768BD2 | SHA256:76E1D3EC95FDEF74ABAF90392DD6F4AA5E344922ABF11E572707287D467F2930 | |||
| 1456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1456.9420\MatSploit\librarys\discordrpc.dll | executable | |
MD5:A1C35901AD26A30C5B7836771B6BADFF | SHA256:517240600B04D454CC5AB7B03E43C4AF5A0B831FD2515F25C015A83652AD4CAC | |||
| 1456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1456.9420\MatSploit\data.ejd | text | |
MD5:— | SHA256:— | |||
| 1456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1456.9420\MatSploit\MatSploit.exe | executable | |
MD5:— | SHA256:— | |||
| 1456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1456.9420\MatSploit\Monaco\Monaco.html | html | |
MD5:— | SHA256:— | |||
| 1456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1456.9420\MatSploit\Monaco\vs\basic-languages\css\css.js | text | |
MD5:49AD30F1151CFD7A74677FDC6DD13DA9 | SHA256:BD331FD3BD2C37B0C3150035325F163AC9266BF6D942310764815E676D856D91 | |||
| 1456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1456.9420\MatSploit\Monaco\vs\basic-languages\coffee\coffee.js | text | |
MD5:9D0C4AC1691EED0A480C3E9246490D29 | SHA256:E706C9F8E5C5A0CB01B2F4E4879EC34A050D6EB2A8840284EB7BADD9D78099F9 | |||
| 1456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1456.9420\MatSploit\Monaco\vs\basic-languages\bat\bat.js | text | |
MD5:4CB475399C4490EEA41982DCD6D9653E | SHA256:9BCA42394FE8922FEC24B768EEB8CE04692DE6FAD82F9052D5B7E70F5C6B0F40 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
5
DNS requests
9
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1928 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca4.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTOpjOEf6LG1z52jqAxwDlTxoaOCgQUQAlhZ%2FC8g3FP3hIILG%2FU1Ct2PZYCEDsJGKKiFxWJllawuNqPxXw%3D | US | der | 278 b | whitelisted |
1928 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca4.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrJdiQ%2Ficg9B19asFe73bPYs%2BreAQUdXGnGUgZvJ2d6kFH35TESHeZ03kCEFslzmkHxCZVZtM5DJmpVK0%3D | US | der | 314 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
332 | MatSploit.exe | 3.22.48.245:443 | matshortener.xyz | — | US | suspicious |
1928 | iexplore.exe | 151.139.128.14:80 | ocsp.comodoca.com | Highwinds Network Group, Inc. | US | suspicious |
1928 | iexplore.exe | 162.159.130.234:443 | discord.gg | Cloudflare Inc | — | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
matshortener.xyz |
| malicious |
discord.gg |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.comodoca4.com |
| whitelisted |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
332 | MatSploit.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |