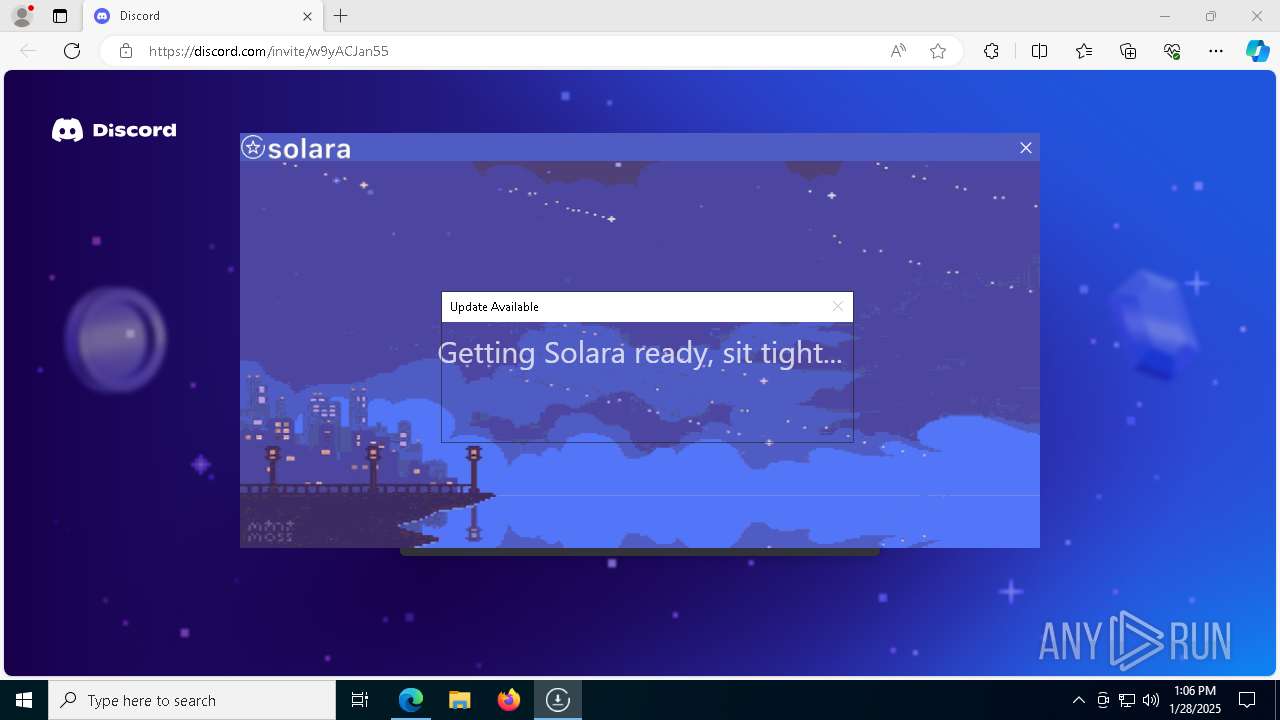
| File name: | BootstrapperNew (1).exe |
| Full analysis: | https://app.any.run/tasks/a734d5ef-6f85-4227-9f90-4dfd319312f7 |
| Verdict: | Malicious activity |
| Analysis date: | January 28, 2025, 13:06:13 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64 Mono/.Net assembly, for MS Windows, 2 sections |
| MD5: | A36750FE814C6CD0A94312EBAF85E07E |
| SHA1: | 9382378C4831247B2EFC387581DC909C6352571F |
| SHA256: | 933ACDB61D5D05BB55CD56957312B677719AC237A2DAAE0F1DAF9D70DC68F2DE |
| SSDEEP: | 98304:yYzoojJRba+nPSqNCrRasNk0LW4kr+zIIvt4Fi1VG86jieQEnYr2PCQekIflB2bQ:9+K |
MALICIOUS
GENERIC has been found (auto)
- BootstrapperNew (1).exe (PID: 6660)
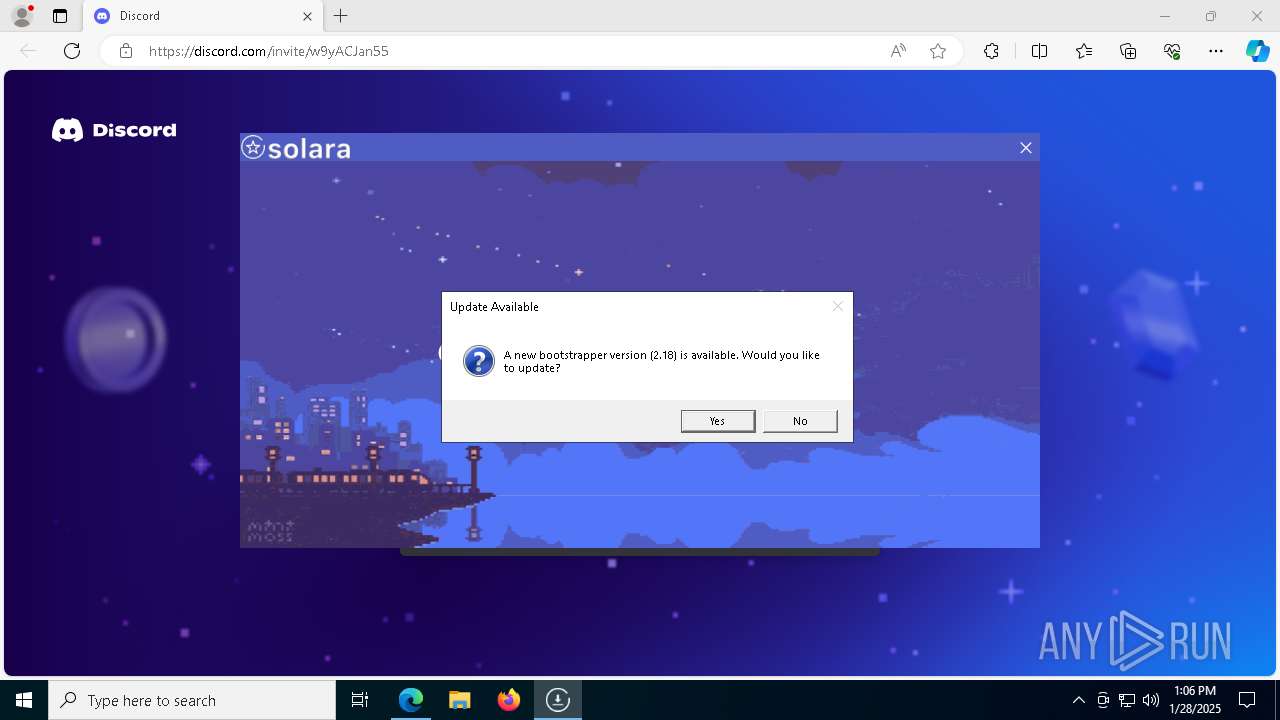
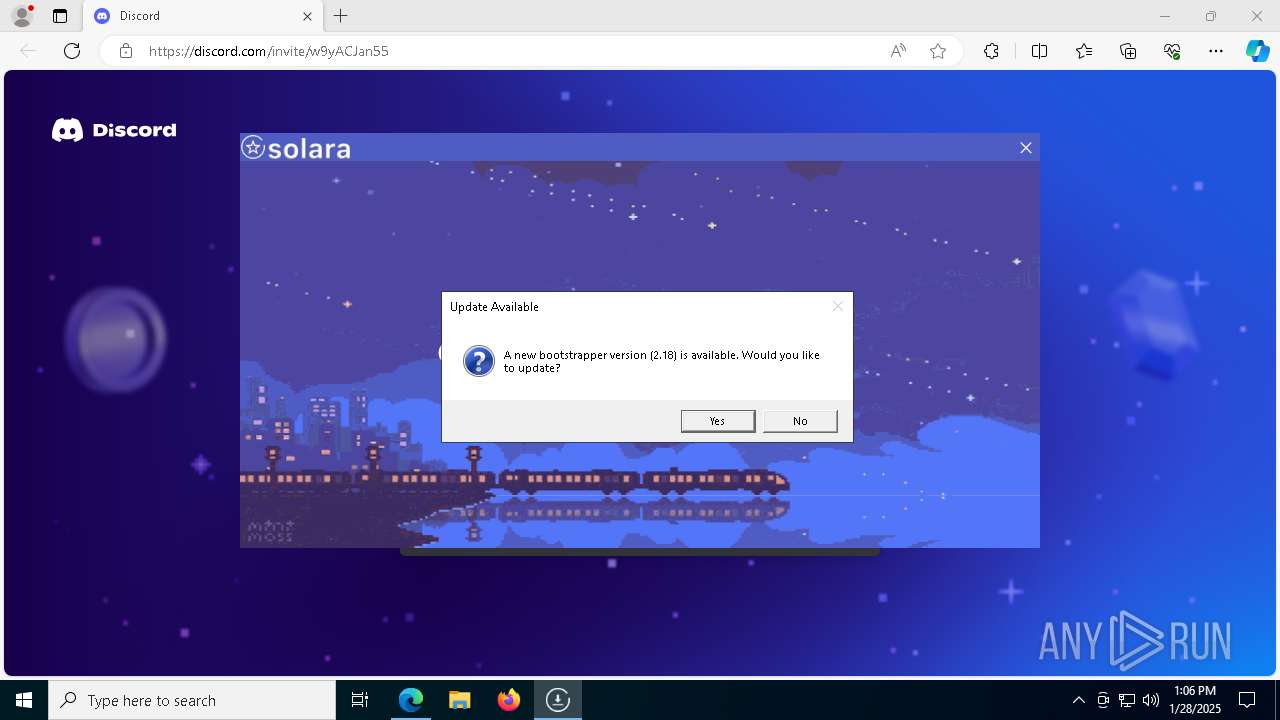
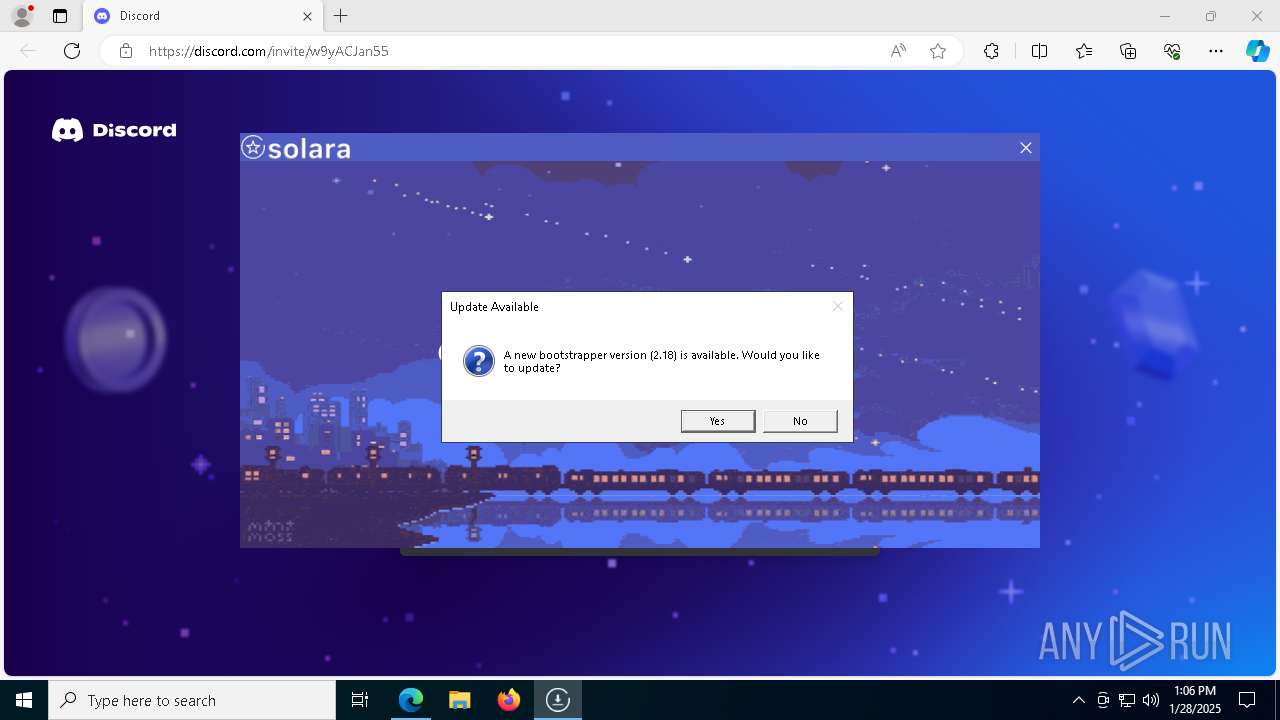
Adds path to the Windows Defender exclusion list
- Bootstrapper_v2.18.exe (PID: 7596)
SUSPICIOUS
Reads security settings of Internet Explorer
- Bootstrapper_v2.18.exe (PID: 7596)
- BootstrapperNew (1).exe (PID: 6660)
- MicrosoftEdgeUpdate.exe (PID: 624)
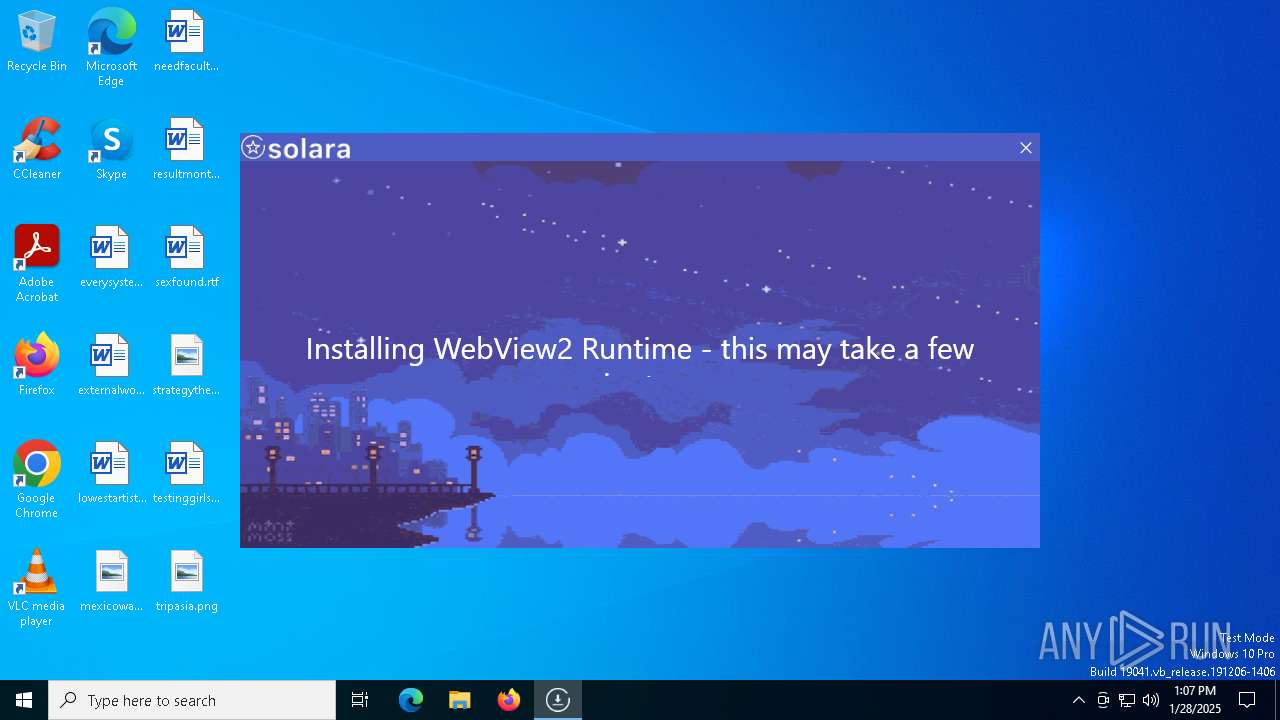
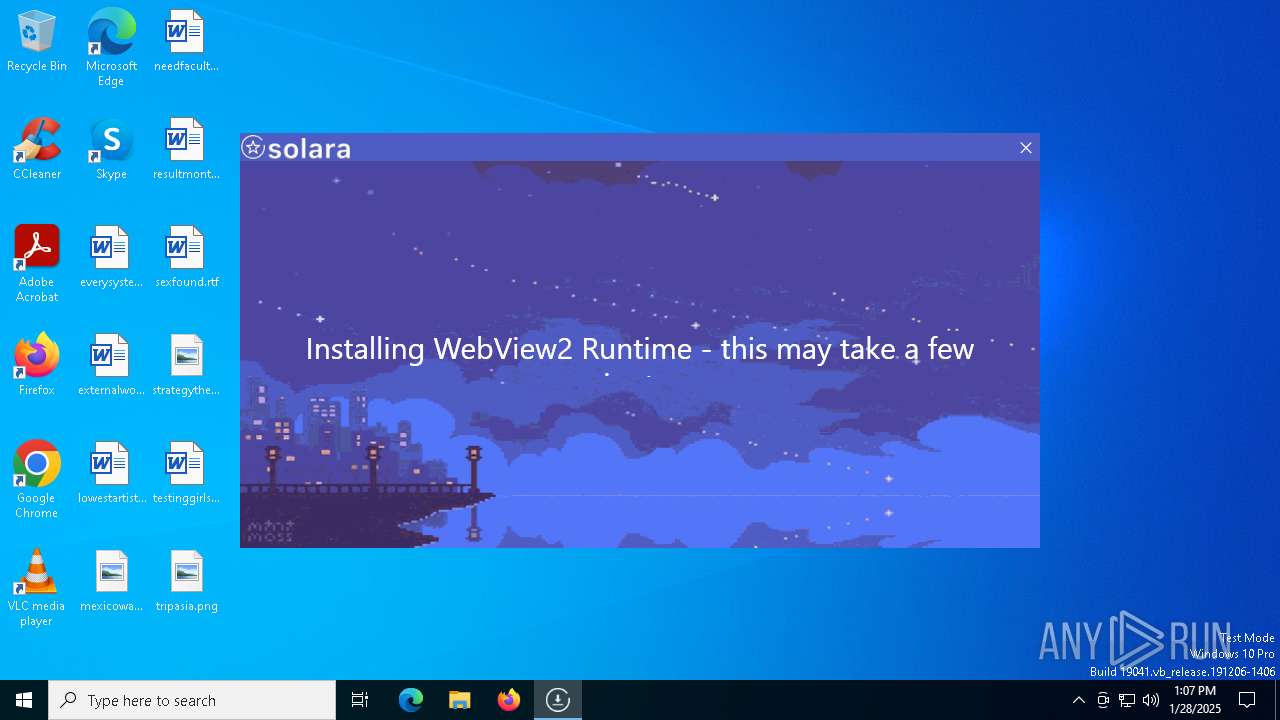
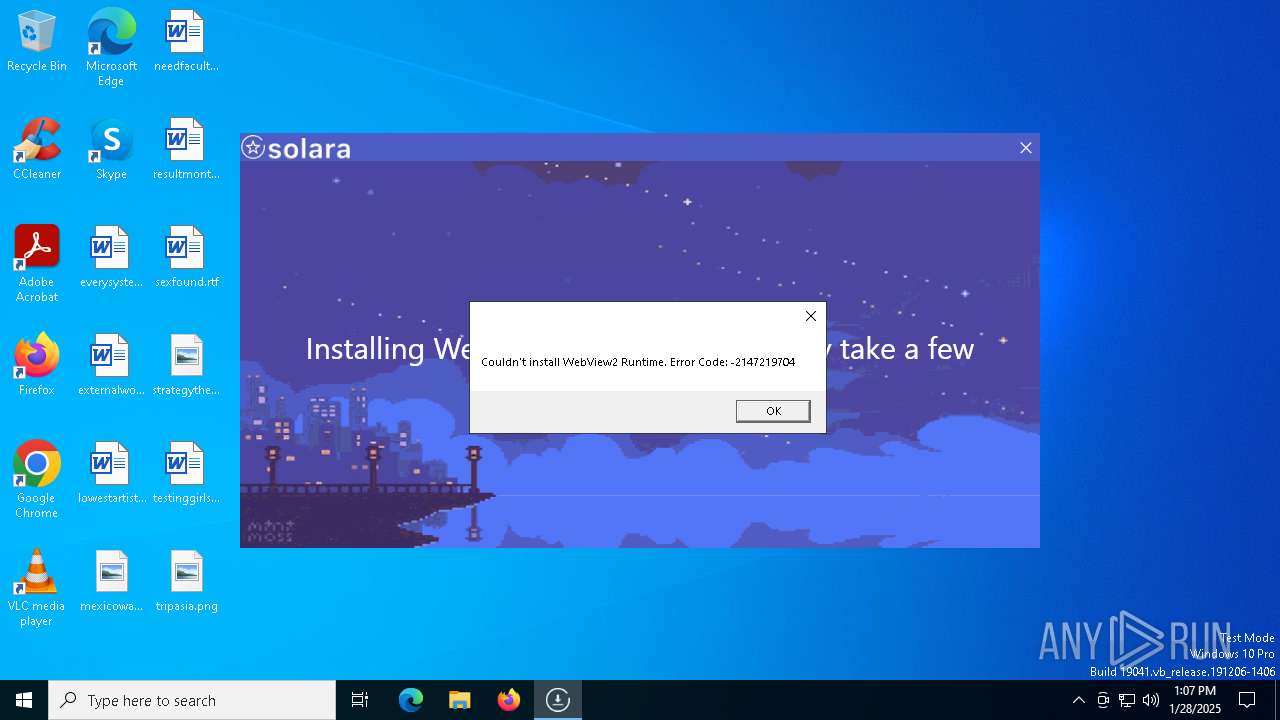
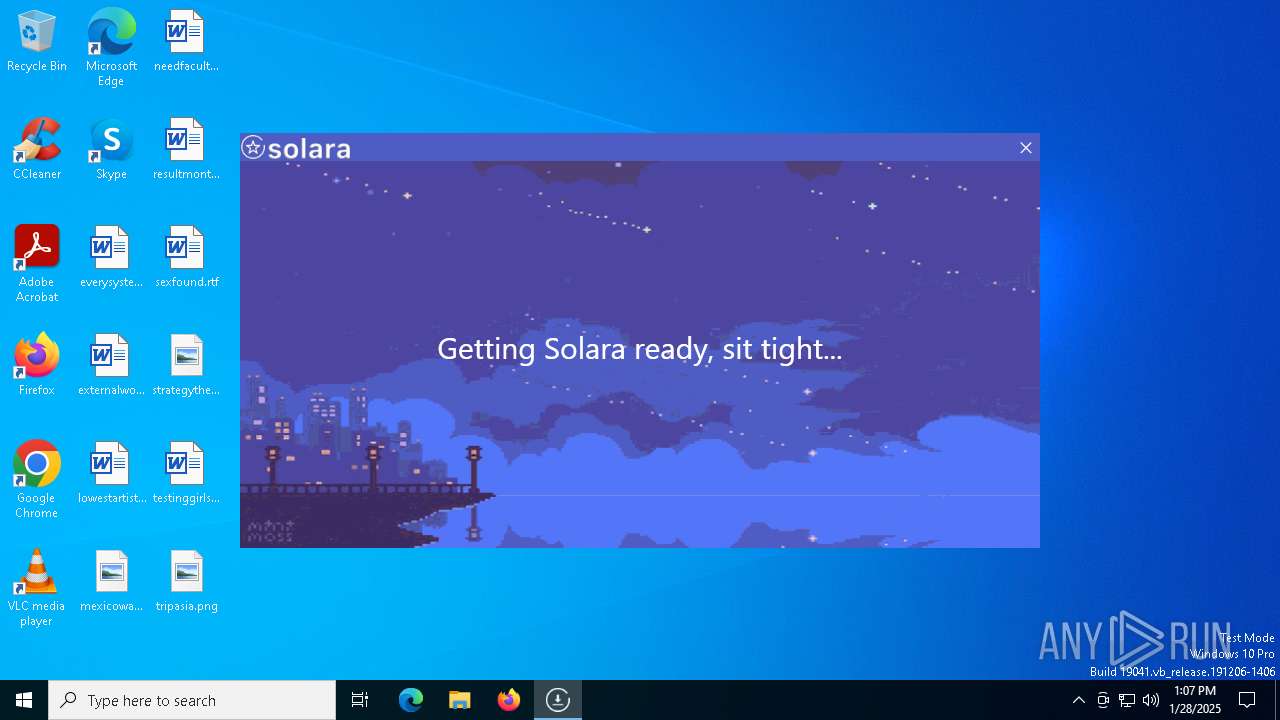
- Solara.exe (PID: 5464)
Executable content was dropped or overwritten
- BootstrapperNew (1).exe (PID: 6660)
- Bootstrapper_v2.18.exe (PID: 7596)
- MicrosoftEdgeWebview2Setup.exe (PID: 6208)
Reads the date of Windows installation
- BootstrapperNew (1).exe (PID: 6660)
- Bootstrapper_v2.18.exe (PID: 7596)
Starts POWERSHELL.EXE for commands execution
- Bootstrapper_v2.18.exe (PID: 7596)
Query Microsoft Defender preferences
- Bootstrapper_v2.18.exe (PID: 7596)
Script adds exclusion path to Windows Defender
- Bootstrapper_v2.18.exe (PID: 7596)
Process drops legitimate windows executable
- Bootstrapper_v2.18.exe (PID: 7596)
- MicrosoftEdgeWebview2Setup.exe (PID: 6208)
- MicrosoftEdgeUpdate.exe (PID: 624)
Starts a Microsoft application from unusual location
- MicrosoftEdgeWebview2Setup.exe (PID: 6208)
- MicrosoftEdgeUpdate.exe (PID: 624)
Disables SEHOP
- MicrosoftEdgeUpdate.exe (PID: 624)
The process drops C-runtime libraries
- Bootstrapper_v2.18.exe (PID: 7596)
Reads the BIOS version
- Solara.exe (PID: 5464)
INFO
Creates files in the program directory
- BootstrapperNew (1).exe (PID: 6660)
- MicrosoftEdgeWebview2Setup.exe (PID: 6208)
- Bootstrapper_v2.18.exe (PID: 7596)
Reads the computer name
- BootstrapperNew (1).exe (PID: 6660)
- Bootstrapper_v2.18.exe (PID: 7596)
- identity_helper.exe (PID: 7340)
- MicrosoftEdgeUpdate.exe (PID: 624)
- Solara.exe (PID: 5464)
- identity_helper.exe (PID: 6876)
Manual execution by a user
- msedge.exe (PID: 7096)
Reads the machine GUID from the registry
- BootstrapperNew (1).exe (PID: 6660)
- Bootstrapper_v2.18.exe (PID: 7596)
- Solara.exe (PID: 5464)
Application launched itself
- msedge.exe (PID: 6840)
- msedge.exe (PID: 7096)
- msedge.exe (PID: 7716)
Create files in a temporary directory
- BootstrapperNew (1).exe (PID: 6660)
- Bootstrapper_v2.18.exe (PID: 7596)
Checks supported languages
- Bootstrapper_v2.18.exe (PID: 7596)
- identity_helper.exe (PID: 7340)
- BootstrapperNew (1).exe (PID: 6660)
- MicrosoftEdgeWebview2Setup.exe (PID: 6208)
- MicrosoftEdgeUpdate.exe (PID: 624)
- Solara.exe (PID: 5464)
- identity_helper.exe (PID: 6876)
Reads Environment values
- identity_helper.exe (PID: 7340)
- Bootstrapper_v2.18.exe (PID: 7596)
- MicrosoftEdgeUpdate.exe (PID: 624)
- Solara.exe (PID: 5464)
- identity_helper.exe (PID: 6876)
- BootstrapperNew (1).exe (PID: 6660)
Process checks computer location settings
- BootstrapperNew (1).exe (PID: 6660)
- MicrosoftEdgeUpdate.exe (PID: 624)
- Bootstrapper_v2.18.exe (PID: 7596)
Reads the software policy settings
- BootstrapperNew (1).exe (PID: 6660)
- Bootstrapper_v2.18.exe (PID: 7596)
- MicrosoftEdgeUpdate.exe (PID: 624)
- wermgr.exe (PID: 5000)
- Solara.exe (PID: 5464)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6588)
- powershell.exe (PID: 2548)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6588)
Checks proxy server information
- Bootstrapper_v2.18.exe (PID: 7596)
- MicrosoftEdgeUpdate.exe (PID: 624)
- wermgr.exe (PID: 5000)
- Solara.exe (PID: 5464)
- BootstrapperNew (1).exe (PID: 6660)
Disables trace logs
- Bootstrapper_v2.18.exe (PID: 7596)
- Solara.exe (PID: 5464)
- BootstrapperNew (1).exe (PID: 6660)
The sample compiled with english language support
- MicrosoftEdgeWebview2Setup.exe (PID: 6208)
- MicrosoftEdgeUpdate.exe (PID: 624)
- Bootstrapper_v2.18.exe (PID: 7596)
- msedge.exe (PID: 7680)
Process checks whether UAC notifications are on
- Solara.exe (PID: 5464)
Executable content was dropped or overwritten
- msedge.exe (PID: 7680)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2043:03:03 18:53:39+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 48 |
| CodeSize: | 2989056 |
| InitializedDataSize: | 9216 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x0000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Bootstrapper |
| FileVersion: | 1.0.0.0 |
| InternalName: | Bootstrapper.exe |
| LegalCopyright: | Copyright © 2024 |
| LegalTrademarks: | - |
| OriginalFileName: | Bootstrapper.exe |
| ProductName: | Bootstrapper |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
204
Monitored processes
73
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 624 | "C:\Program Files (x86)\Microsoft\Temp\EU1C02.tmp\MicrosoftEdgeUpdate.exe" /silent /install "appguid={F3017226-FE2A-4295-8BDF-00C3A9A7E4C5}&appname=Microsoft%20Edge%20Webview2%20Runtime&needsadmin=prefers" | C:\Program Files (x86)\Microsoft\Temp\EU1C02.tmp\MicrosoftEdgeUpdate.exe | MicrosoftEdgeWebview2Setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Update Exit code: 2147747592 Version: 1.3.195.43 Modules
| |||||||||||||||
| 628 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1612 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=1668 --field-trial-handle=2872,i,10654423871682849523,16628198607472720512,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1732 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=4132 --field-trial-handle=2400,i,14914261383500173855,10057337325442164010,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2428 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4320 --field-trial-handle=2872,i,10654423871682849523,16628198607472720512,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2548 | "powershell" -Command "Get-MpPreference | Select-Object -ExpandProperty ExclusionPath" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Bootstrapper_v2.18.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2788 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2796 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=4672 --field-trial-handle=2872,i,10654423871682849523,16628198607472720512,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3564 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5844 --field-trial-handle=2400,i,14914261383500173855,10057337325442164010,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
29 042
Read events
28 928
Write events
112
Delete events
2
Modification events
| (PID) Process: | (6660) BootstrapperNew (1).exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (6660) BootstrapperNew (1).exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6660) BootstrapperNew (1).exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6660) BootstrapperNew (1).exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6840) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6840) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6840) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6840) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: A071F5245A8B2F00 | |||
| (PID) Process: | (7096) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7096) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
Executable files
226
Suspicious files
327
Text files
82
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7096 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF13886d.TMP | — | |
MD5:— | SHA256:— | |||
| 7096 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7096 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF13889c.TMP | — | |
MD5:— | SHA256:— | |||
| 7096 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7096 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1388cb.TMP | — | |
MD5:— | SHA256:— | |||
| 7096 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6660 | BootstrapperNew (1).exe | C:\Users\admin\AppData\Local\Temp\DISCORD | text | |
MD5:B86AEF3D31FDCC68C0138B25A632F939 | SHA256:9BED077BB37DD2F770ED6F960F9E1A22054174FB14BA1AA49CB13CF3008A8486 | |||
| 6840 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Local State | binary | |
MD5:F1A7466F7F39D0E8A5A91D187B3855EF | SHA256:3EC7580092DBEB33D807041785715579AB61AC53A78226A07807F4EE6E3D21BF | |||
| 6840 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Local State~RF13862b.TMP | binary | |
MD5:DFFC82B8D23613E62A20204028CEF32F | SHA256:114690F0417A9A6B079EA8D0534F095B04467809DCA929EB0983059E1C60FB6C | |||
| 7096 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF138928.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
38
TCP/UDP connections
83
DNS requests
74
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7452 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7452 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6952 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5000 | wermgr.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5000 | wermgr.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
760 | lsass.exe | GET | 200 | 142.250.181.227:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
7252 | svchost.exe | HEAD | 200 | 217.20.57.18:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5cbc98ff-b69b-4fda-ad94-17ec2f9cf48b?P1=1738091727&P2=404&P3=2&P4=bXjZ6%2frqejJj8Ztcvu3AxpXdbdG9D3G0weoPM7uR4PBVmXTR1%2bY%2bu6EB72iXwrHoDitIUSXPfF8iBDyGwARXjQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5064 | SearchApp.exe | 95.100.110.91:443 | — | Akamai International B.V. | NL | unknown |
6428 | msedge.exe | 162.159.133.234:443 | discord.gg | CLOUDFLARENET | — | whitelisted |
7096 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6428 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6428 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6428 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
discord.gg |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
discord.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6428 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
6428 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
6428 | msedge.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
6428 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
6428 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
6428 | msedge.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
6428 | msedge.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
6428 | msedge.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
6428 | msedge.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
6428 | msedge.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |