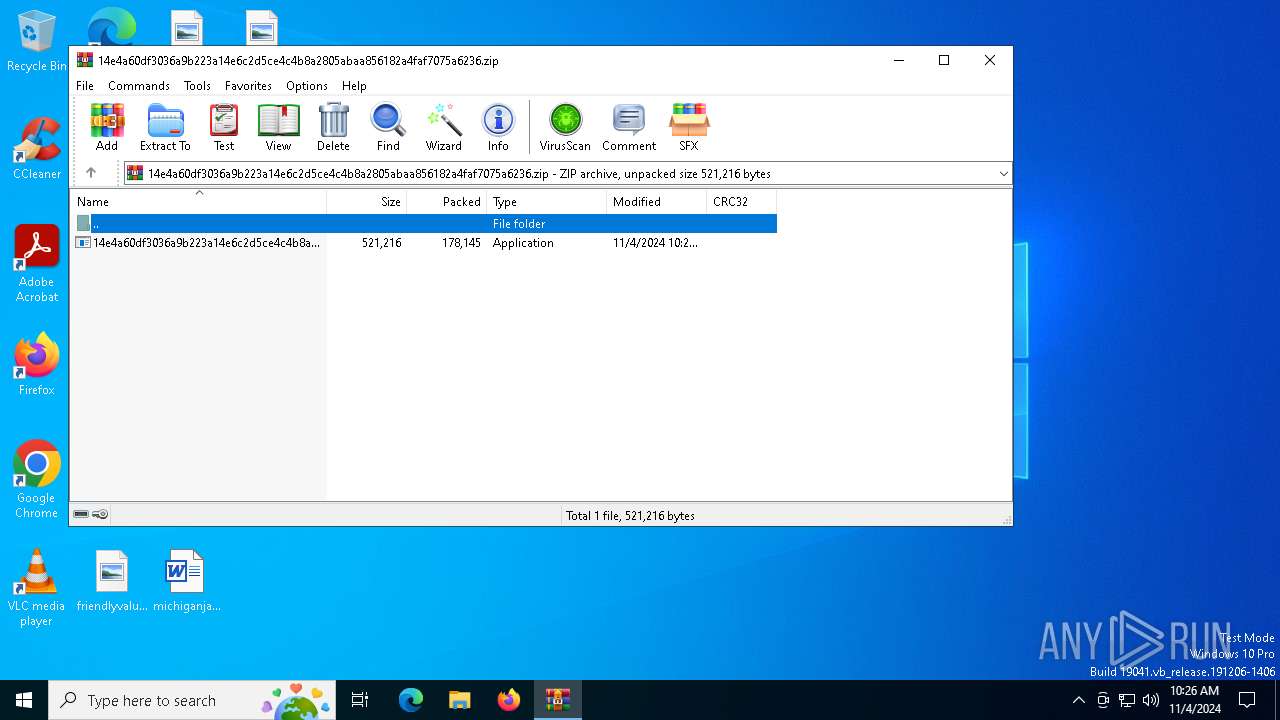
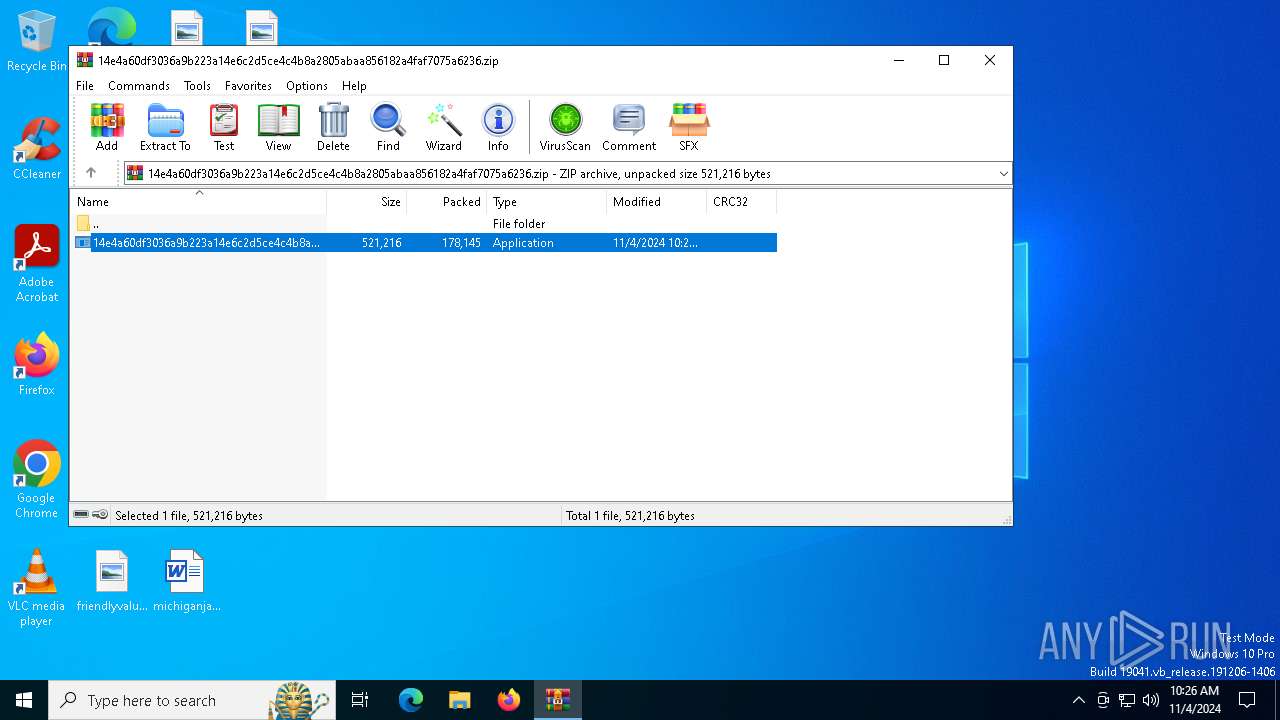
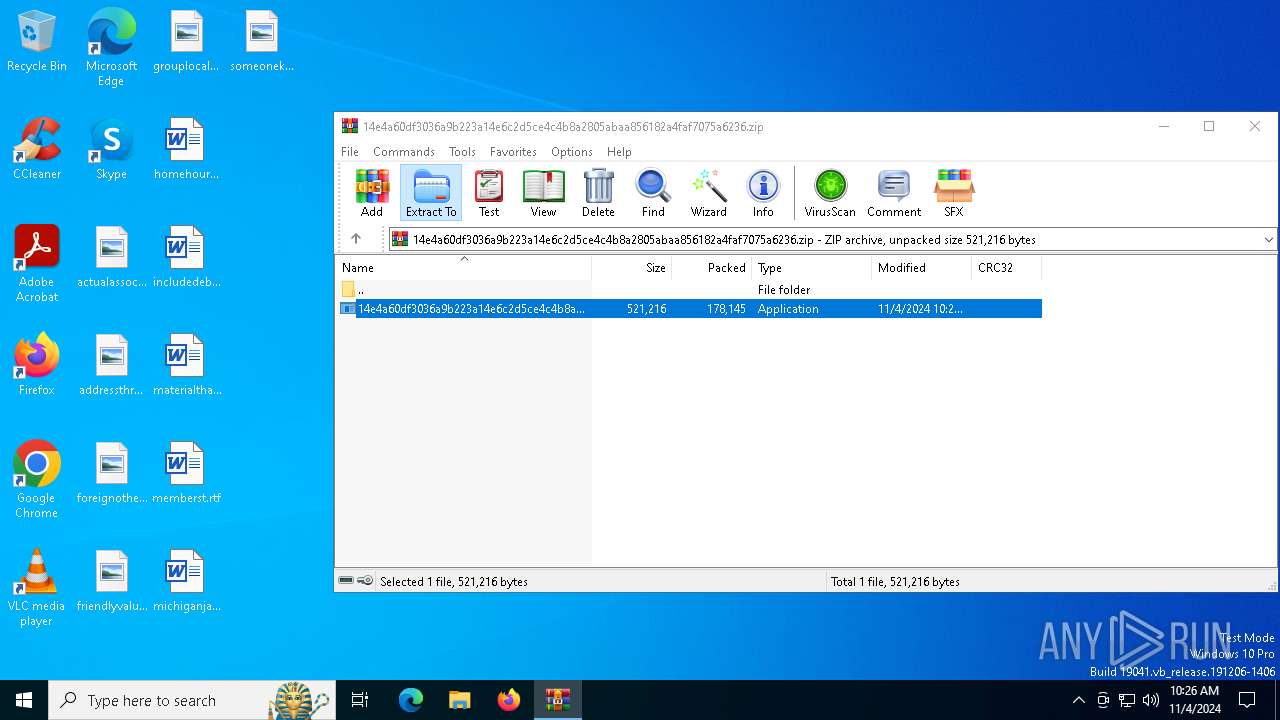
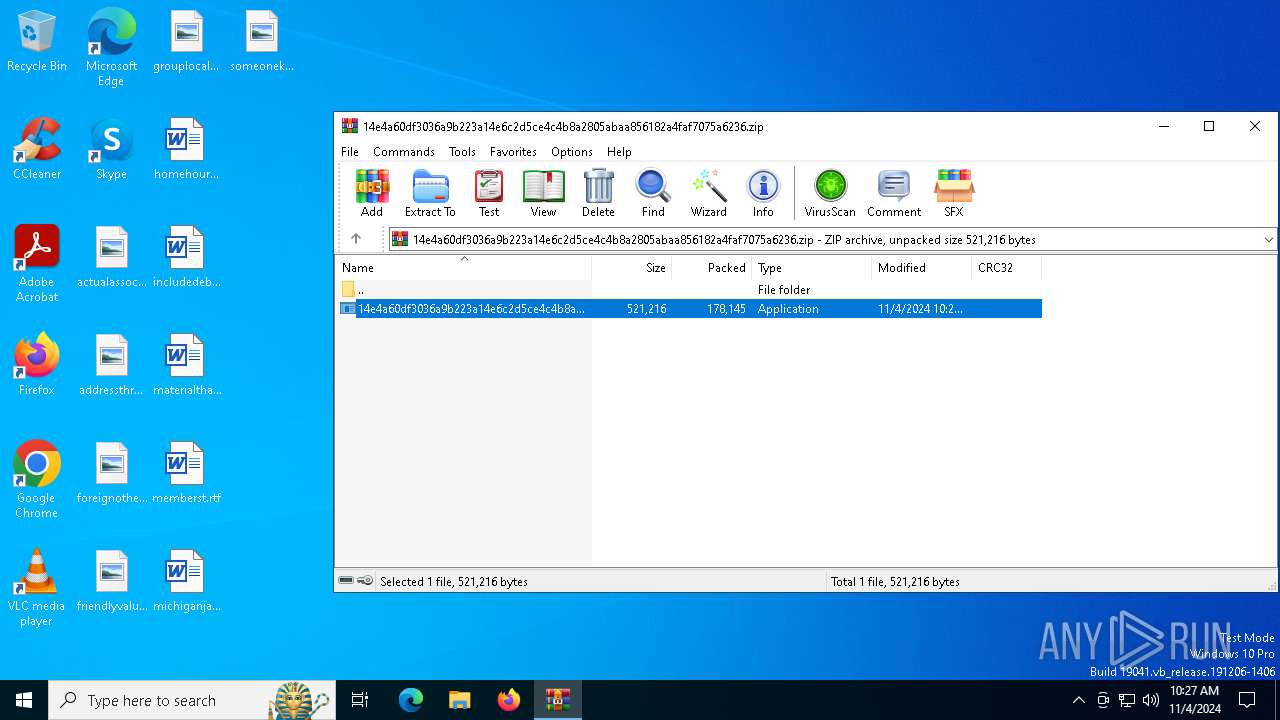
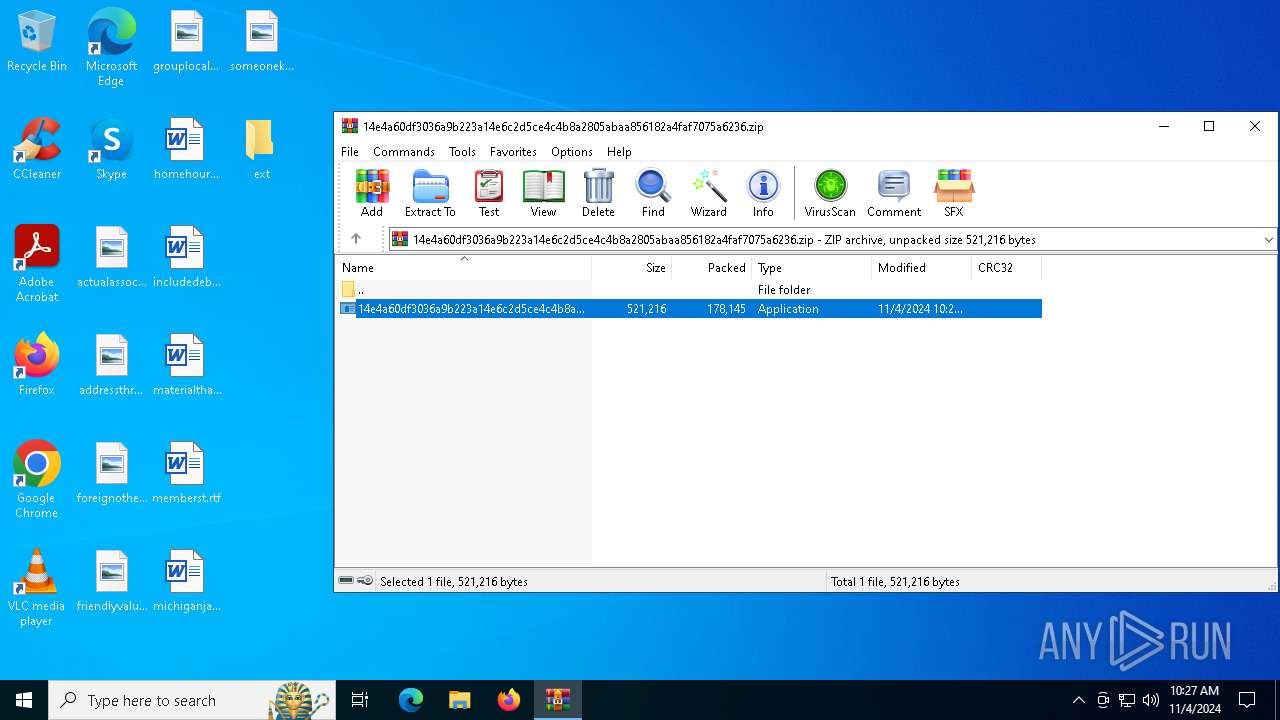
| File name: | 14e4a60df3036a9b223a14e6c2d5ce4c4b8a2805abaa856182a4faf7075a6236.zip |
| Full analysis: | https://app.any.run/tasks/8ff02895-5cb0-4175-a8bf-21dacf9d72ac |
| Verdict: | Malicious activity |
| Analysis date: | November 04, 2024, 10:26:14 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
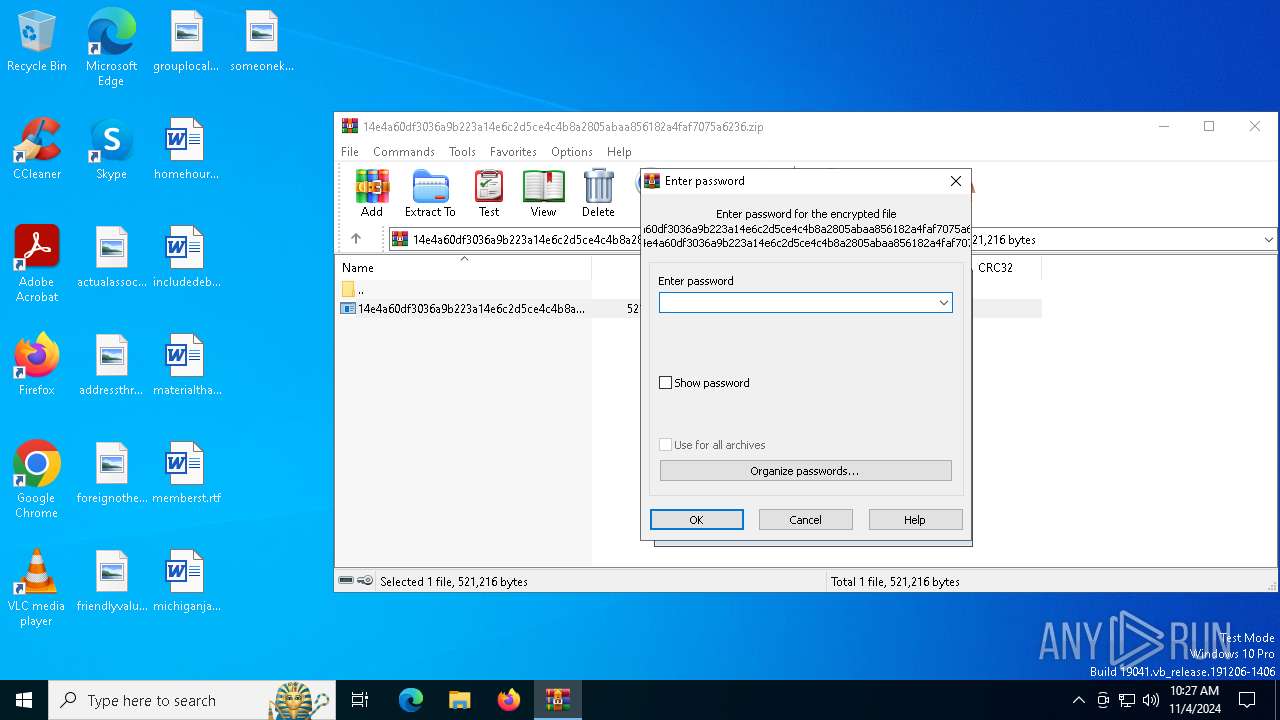
| MIME: | application/zip |
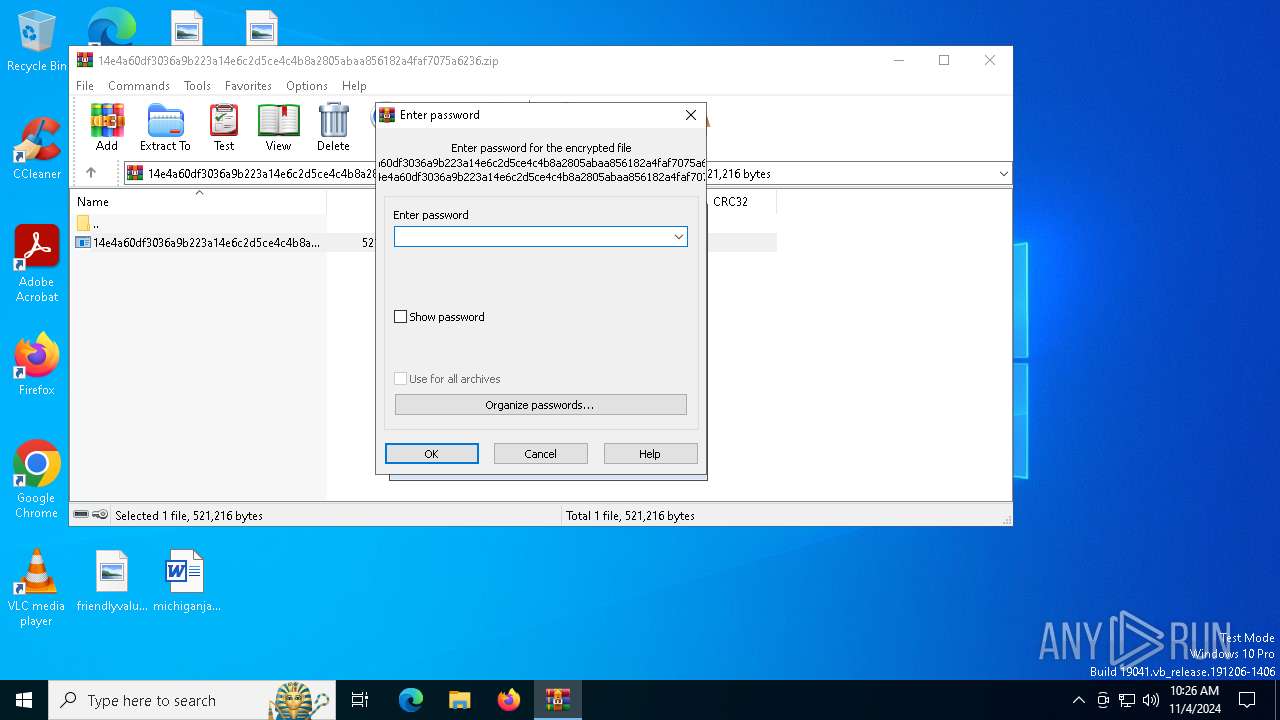
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | 87018BAC5B7E27C719246E2B452CC570 |
| SHA1: | 543600D3511EB94C6BFB267C900C62374347C61F |
| SHA256: | 933989FB09F1948627F0B4EC91340B3C17F76831459FA3655B061B1ECD4553DD |
| SSDEEP: | 6144:bTNClf0ivrWLu6kiX9Ey3qnT7sh+IAK/mxMQX:FClf0ivrTWbqnns/AyU7X |
MALICIOUS
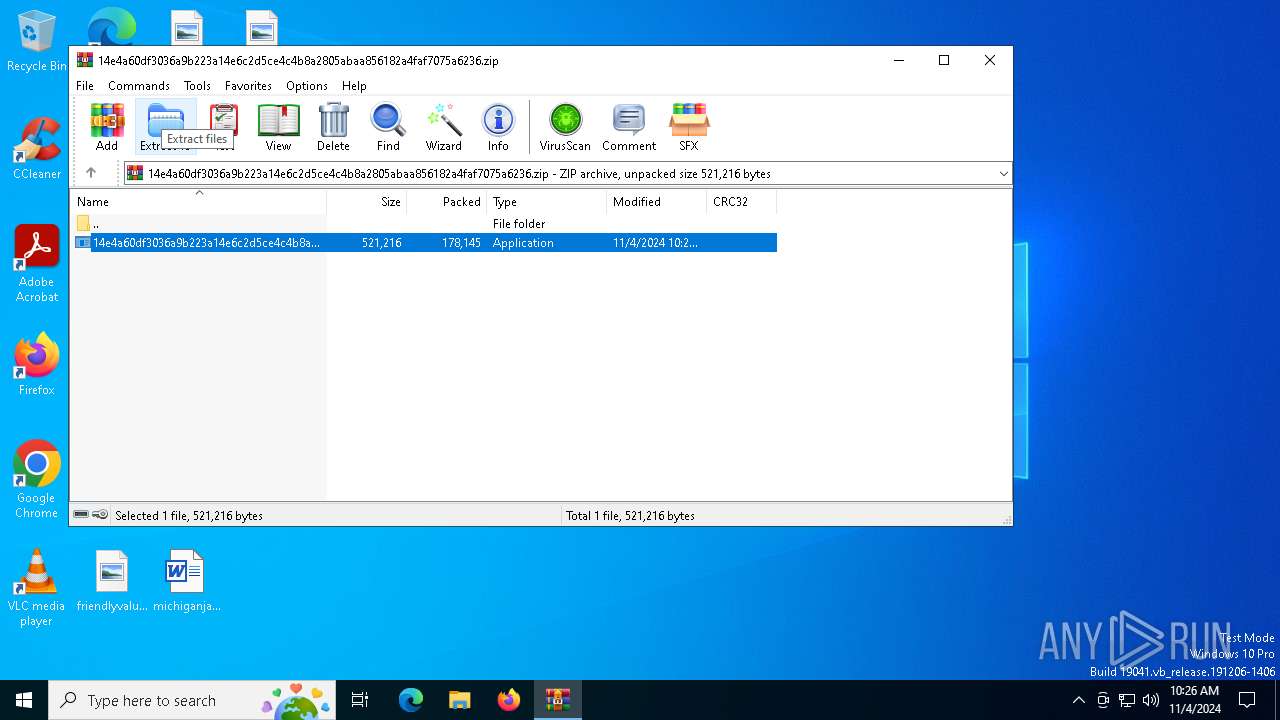
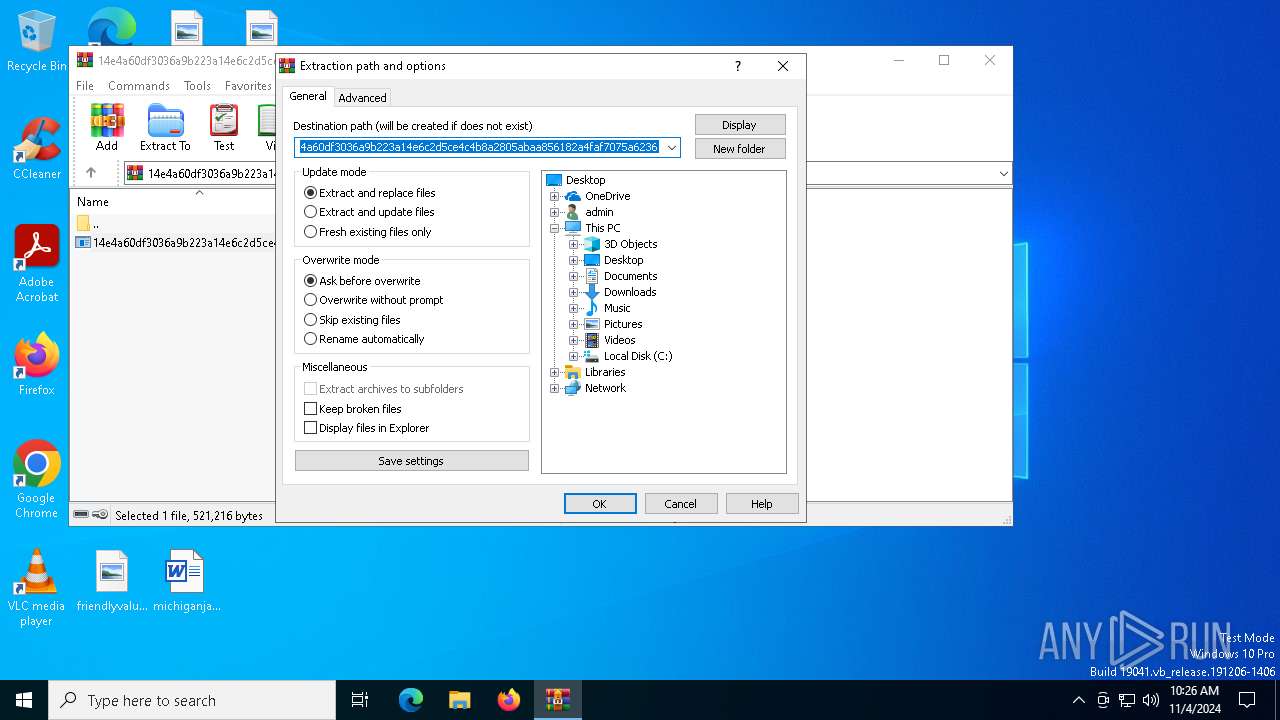
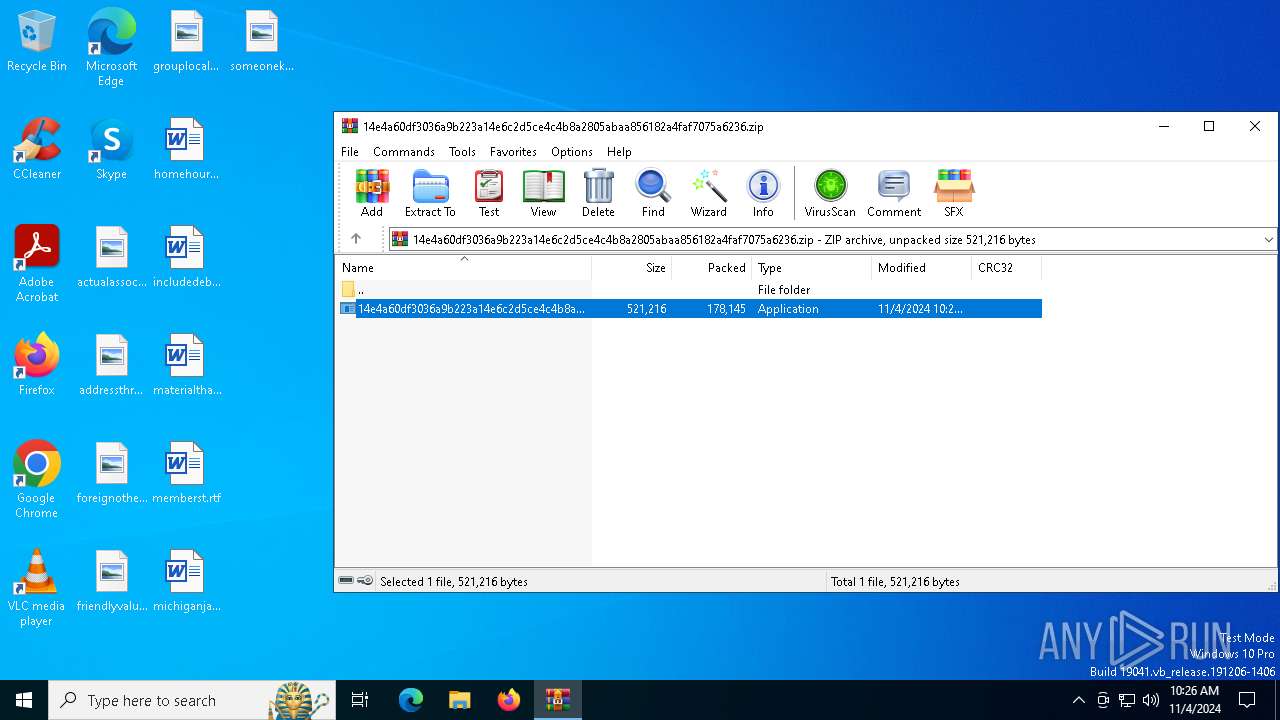
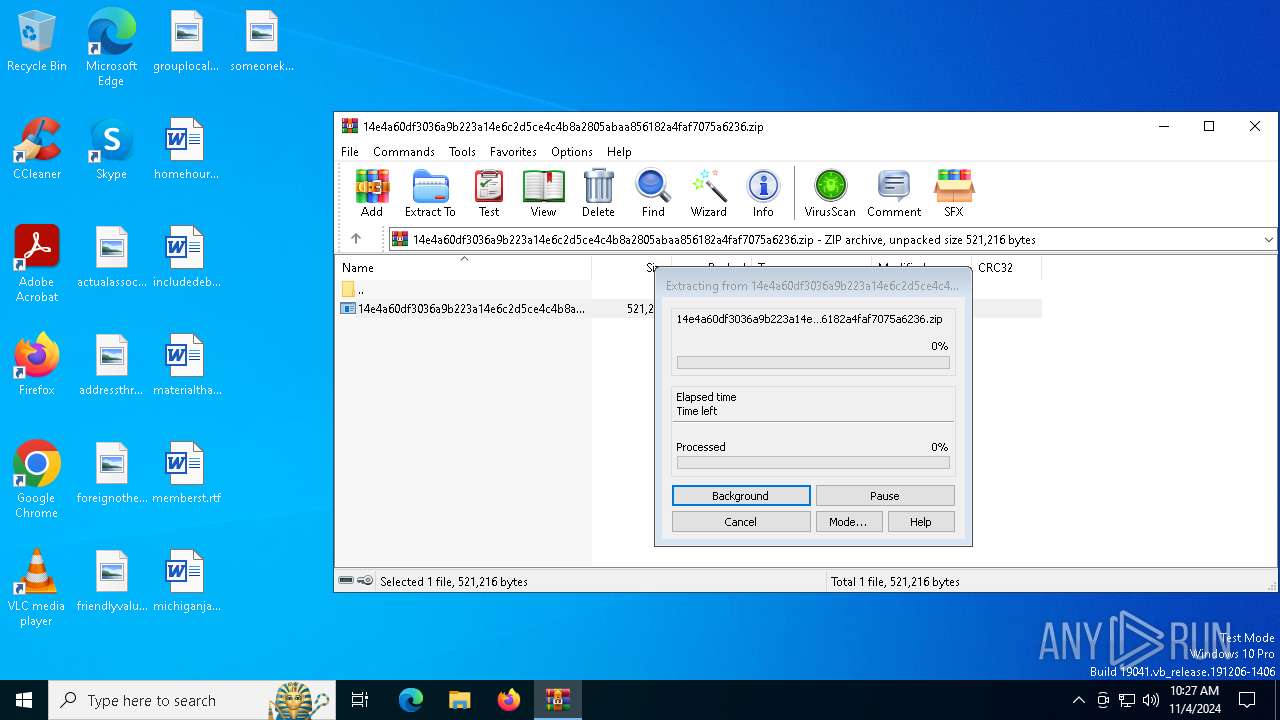
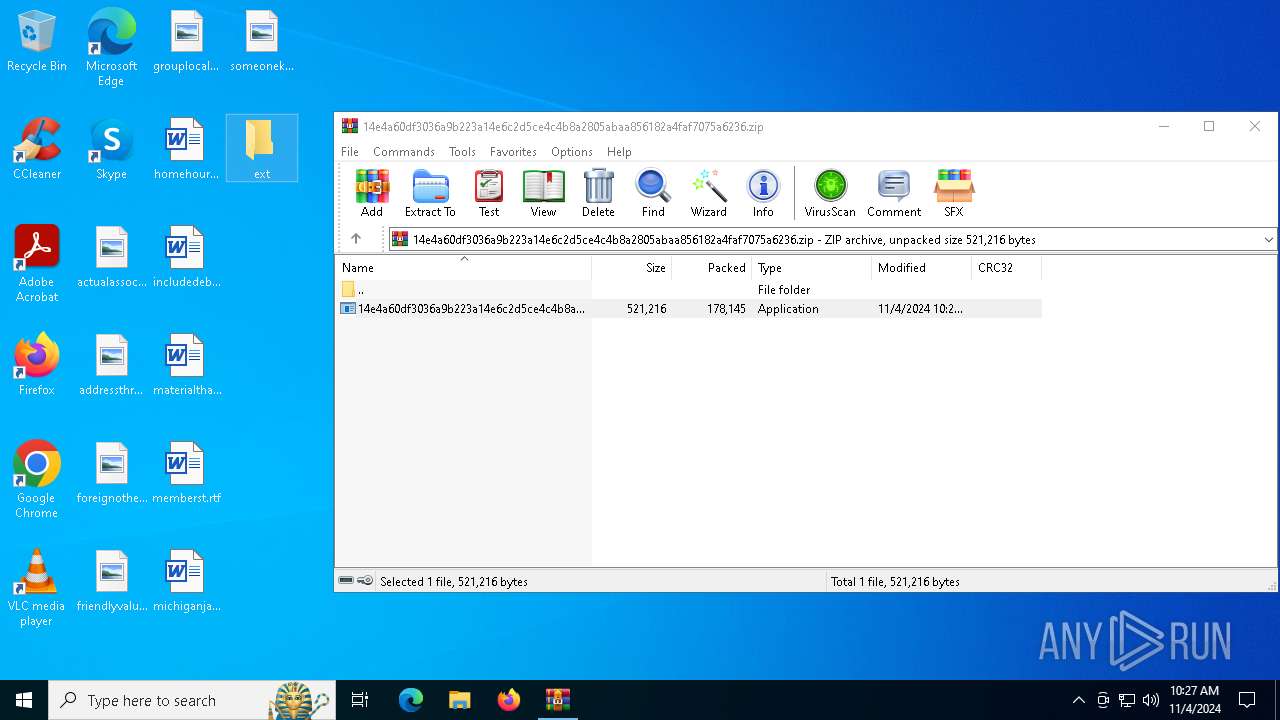
Generic archive extractor
- WinRAR.exe (PID: 6712)
WARZONE has been detected (YARA)
- images.exe (PID: 4812)
SUSPICIOUS
Executable content was dropped or overwritten
- 14e4a60df3036a9b223a14e6c2d5ce4c4b8a2805abaa856182a4faf7075a6236.exe (PID: 6408)
Connects to unusual port
- images.exe (PID: 4812)
Starts itself from another location
- 14e4a60df3036a9b223a14e6c2d5ce4c4b8a2805abaa856182a4faf7075a6236.exe (PID: 6408)
Starts CMD.EXE for commands execution
- images.exe (PID: 4812)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6712)
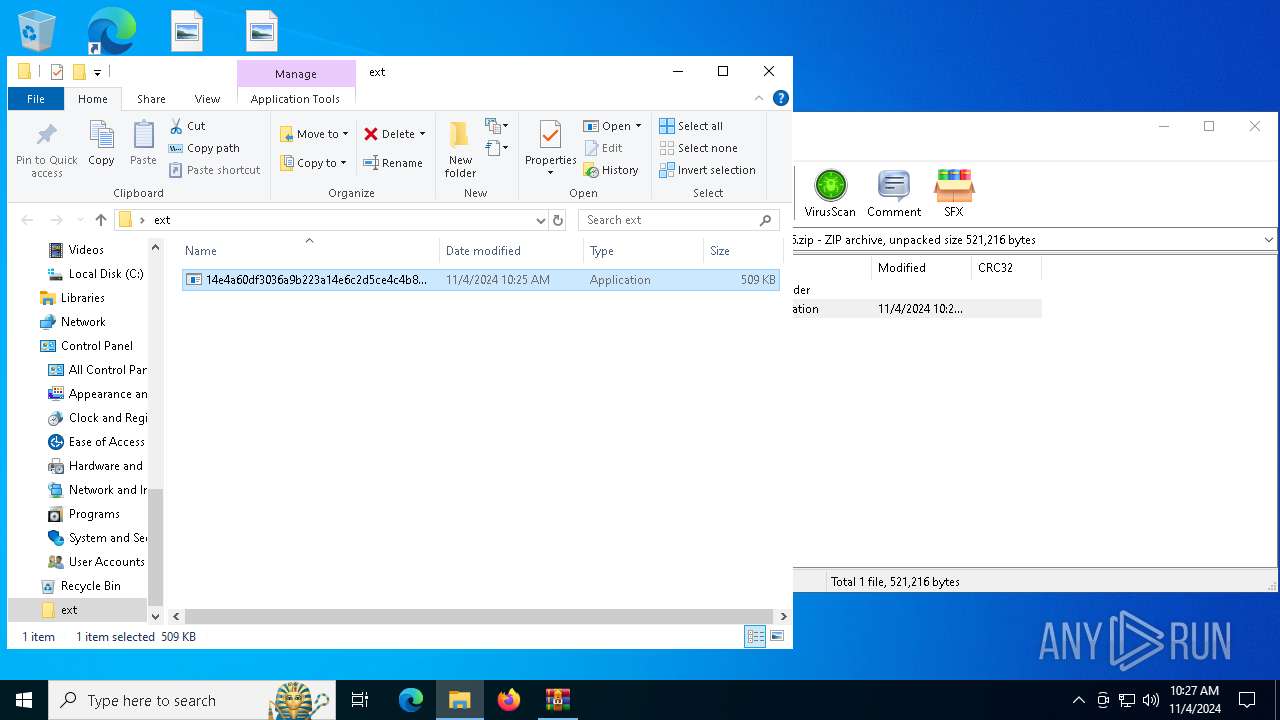
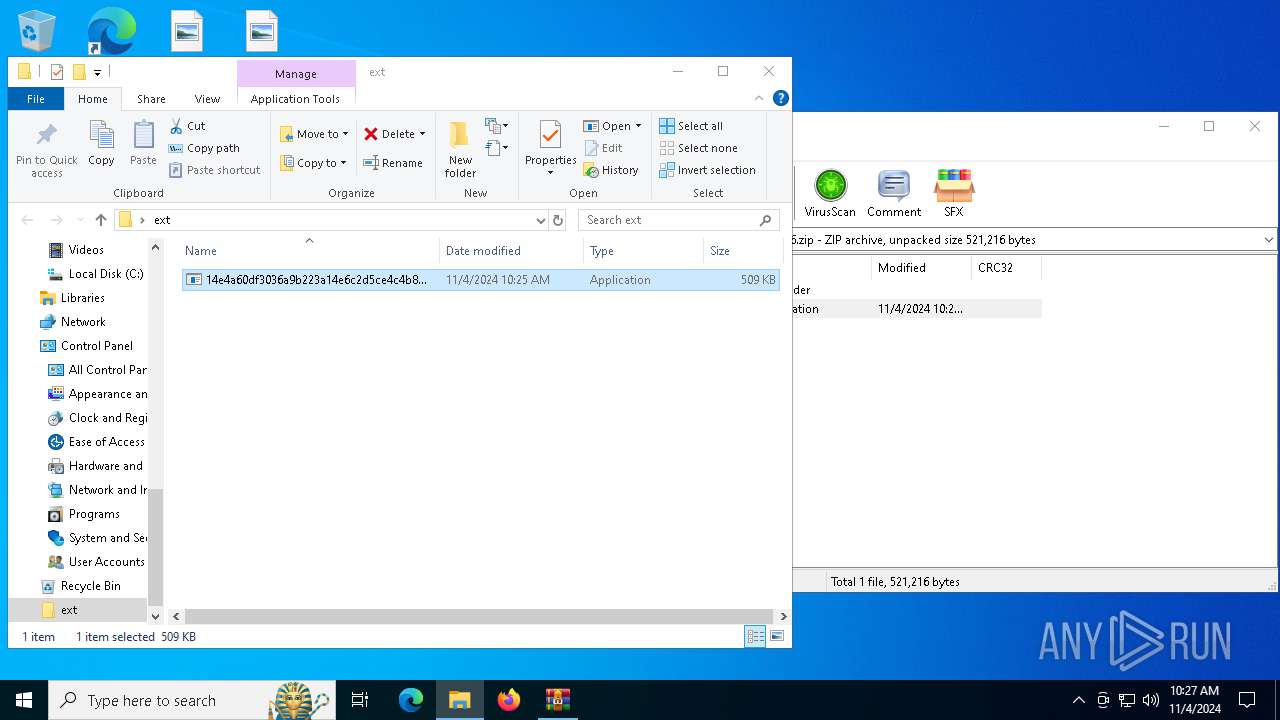
Manual execution by a user
- 14e4a60df3036a9b223a14e6c2d5ce4c4b8a2805abaa856182a4faf7075a6236.exe (PID: 6408)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
WarZone
(PID) Process(4812) images.exe
C2 (1)172.94.88.130:2030
Options
Install FlagTrue
Startup FlagFalse
Startup nameimages.exe
2Q4M42YN8W1
Reverse Proxy local portNone
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2024:11:04 10:25:14 |
| ZipCRC: | 0x4a3ffefb |
| ZipCompressedSize: | 178145 |
| ZipUncompressedSize: | 521216 |
| ZipFileName: | 14e4a60df3036a9b223a14e6c2d5ce4c4b8a2805abaa856182a4faf7075a6236.exe |
Total processes
138
Monitored processes
8
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 624 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | images.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4812 | "C:\Users\admin\Documents\images.exe" | C:\Users\admin\Documents\images.exe | 14e4a60df3036a9b223a14e6c2d5ce4c4b8a2805abaa856182a4faf7075a6236.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
WarZone(PID) Process(4812) images.exe C2 (1)172.94.88.130:2030 Options Install FlagTrue Startup FlagFalse Startup nameimages.exe
2Q4M42YN8W1 Reverse Proxy local portNone | |||||||||||||||
| 6408 | "C:\Users\admin\Desktop\ext\14e4a60df3036a9b223a14e6c2d5ce4c4b8a2805abaa856182a4faf7075a6236.exe" | C:\Users\admin\Desktop\ext\14e4a60df3036a9b223a14e6c2d5ce4c4b8a2805abaa856182a4faf7075a6236.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
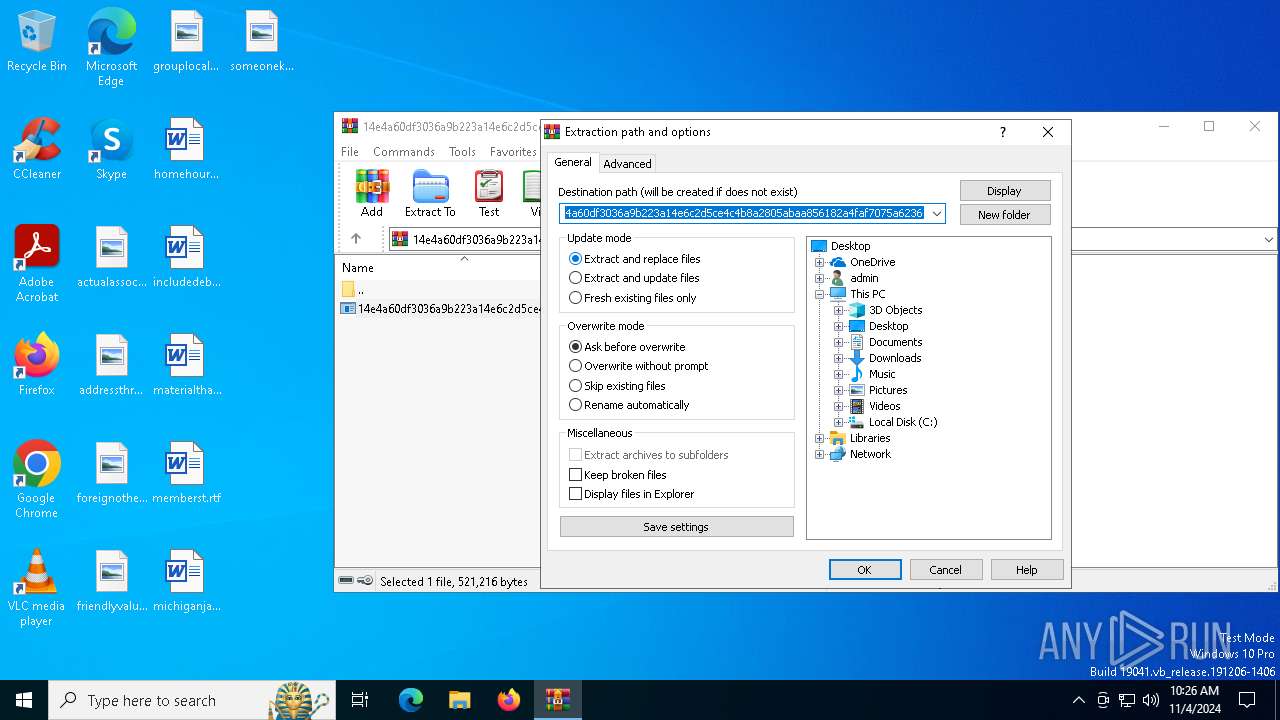
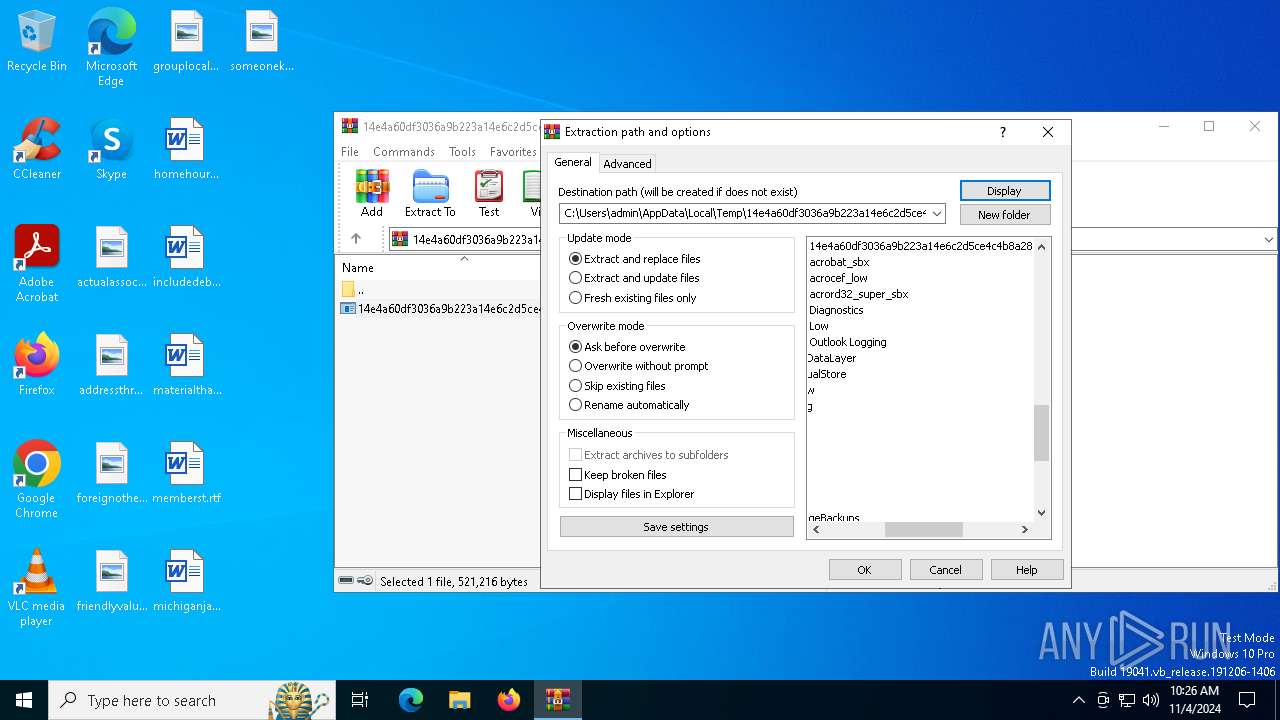
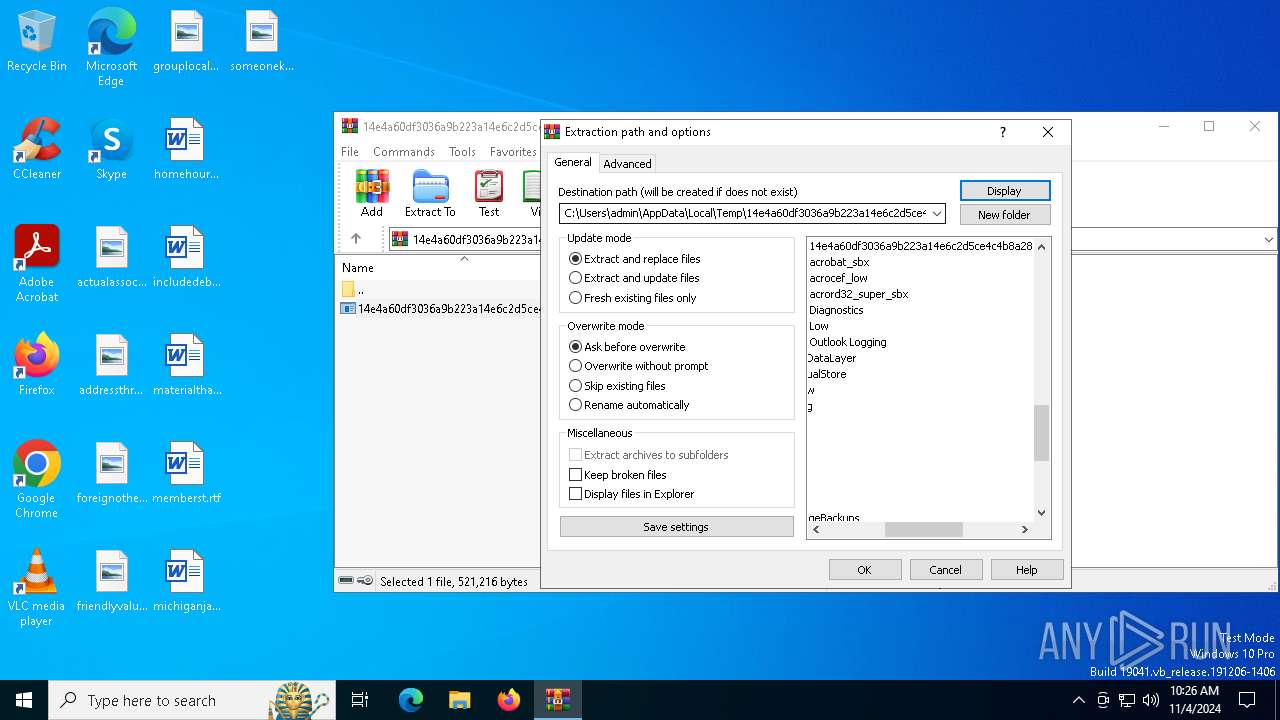
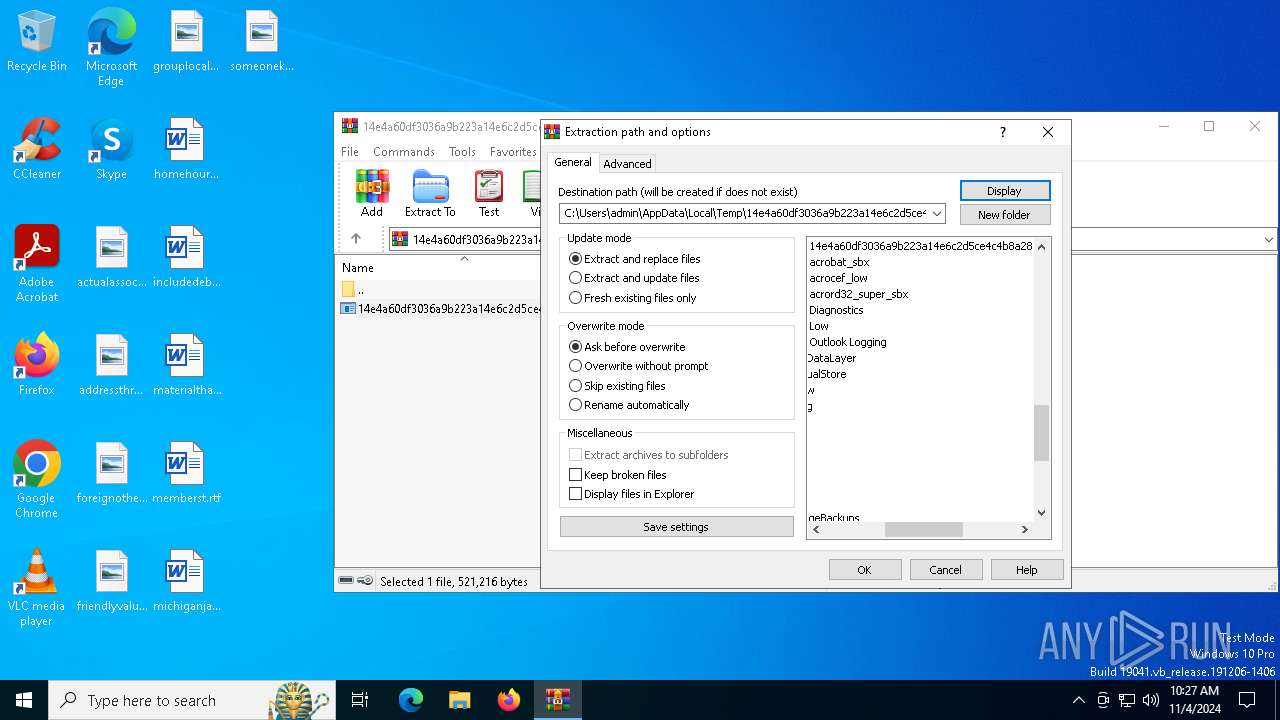
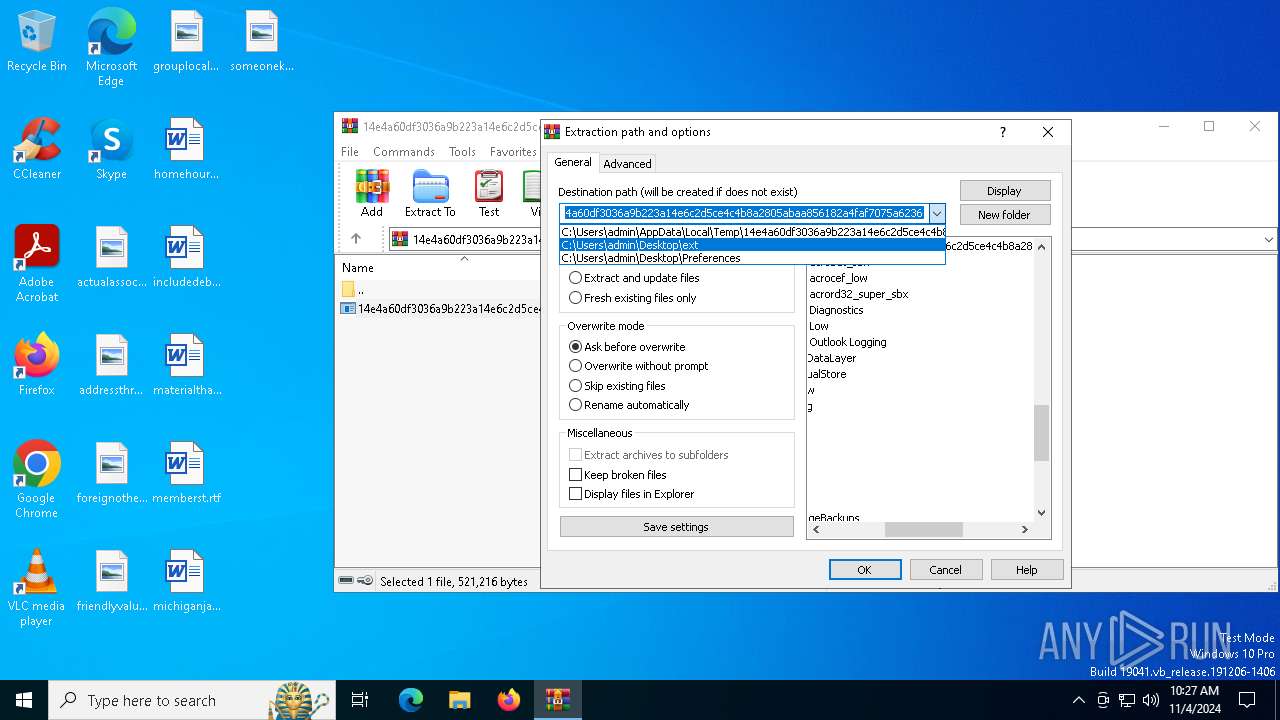
| 6712 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\14e4a60df3036a9b223a14e6c2d5ce4c4b8a2805abaa856182a4faf7075a6236.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 6764 | "C:\WINDOWS\System32\cmd.exe" | C:\Windows\SysWOW64\cmd.exe | — | images.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6880 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7084 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | 14e4a60df3036a9b223a14e6c2d5ce4c4b8a2805abaa856182a4faf7075a6236.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7144 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 287
Read events
3 245
Write events
29
Delete events
13
Modification events
| (PID) Process: | (6712) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6712) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\14e4a60df3036a9b223a14e6c2d5ce4c4b8a2805abaa856182a4faf7075a6236.zip | |||
| (PID) Process: | (6712) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6712) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6712) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6712) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6712) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (6712) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
| (PID) Process: | (6712) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 13 |
Value: | |||
| (PID) Process: | (6712) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 12 |
Value: | |||
Executable files
3
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6408 | 14e4a60df3036a9b223a14e6c2d5ce4c4b8a2805abaa856182a4faf7075a6236.exe | C:\Users\admin\Documents\images.exe | executable | |
MD5:72D23702D7E13E2101E8EB1BBA9FF6BB | SHA256:14E4A60DF3036A9B223A14E6C2D5CE4C4B8A2805ABAA856182A4FAF7075A6236 | |||
| 6712 | WinRAR.exe | C:\Users\admin\Desktop\ext\14e4a60df3036a9b223a14e6c2d5ce4c4b8a2805abaa856182a4faf7075a6236.exe | executable | |
MD5:72D23702D7E13E2101E8EB1BBA9FF6BB | SHA256:14E4A60DF3036A9B223A14E6C2D5CE4C4B8A2805ABAA856182A4FAF7075A6236 | |||
| 6712 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\14e4a60df3036a9b223a14e6c2d5ce4c4b8a2805abaa856182a4faf7075a6236\14e4a60df3036a9b223a14e6c2d5ce4c4b8a2805abaa856182a4faf7075a6236.exe | executable | |
MD5:72D23702D7E13E2101E8EB1BBA9FF6BB | SHA256:14E4A60DF3036A9B223A14E6C2D5CE4C4B8A2805ABAA856182A4FAF7075A6236 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
46
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5488 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.32.185.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6376 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6572 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6960 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6960 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4360 | SearchApp.exe | 2.23.209.133:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
5640 | RUXIMICS.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5488 | MoUsoCoreWorker.exe | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5488 | MoUsoCoreWorker.exe | 23.32.185.131:80 | www.microsoft.com | AKAMAI-AS | BR | whitelisted |
4020 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6944 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6376 | svchost.exe | 20.190.160.17:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |