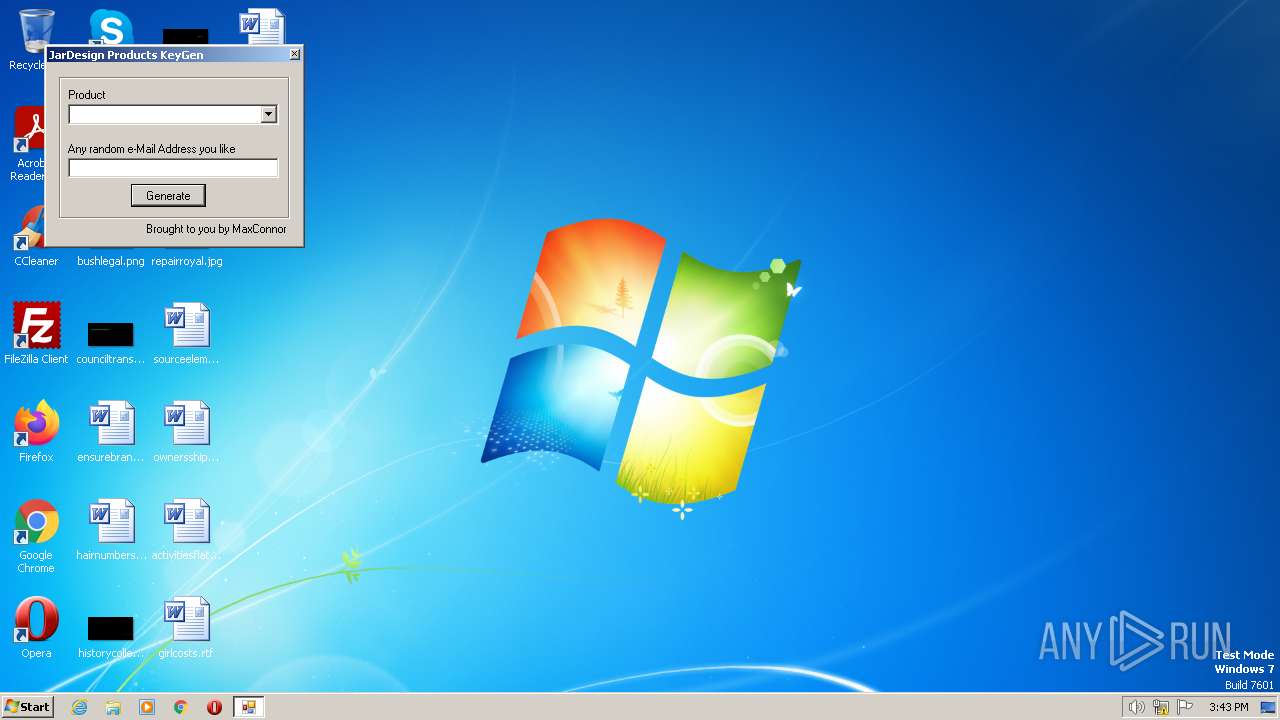
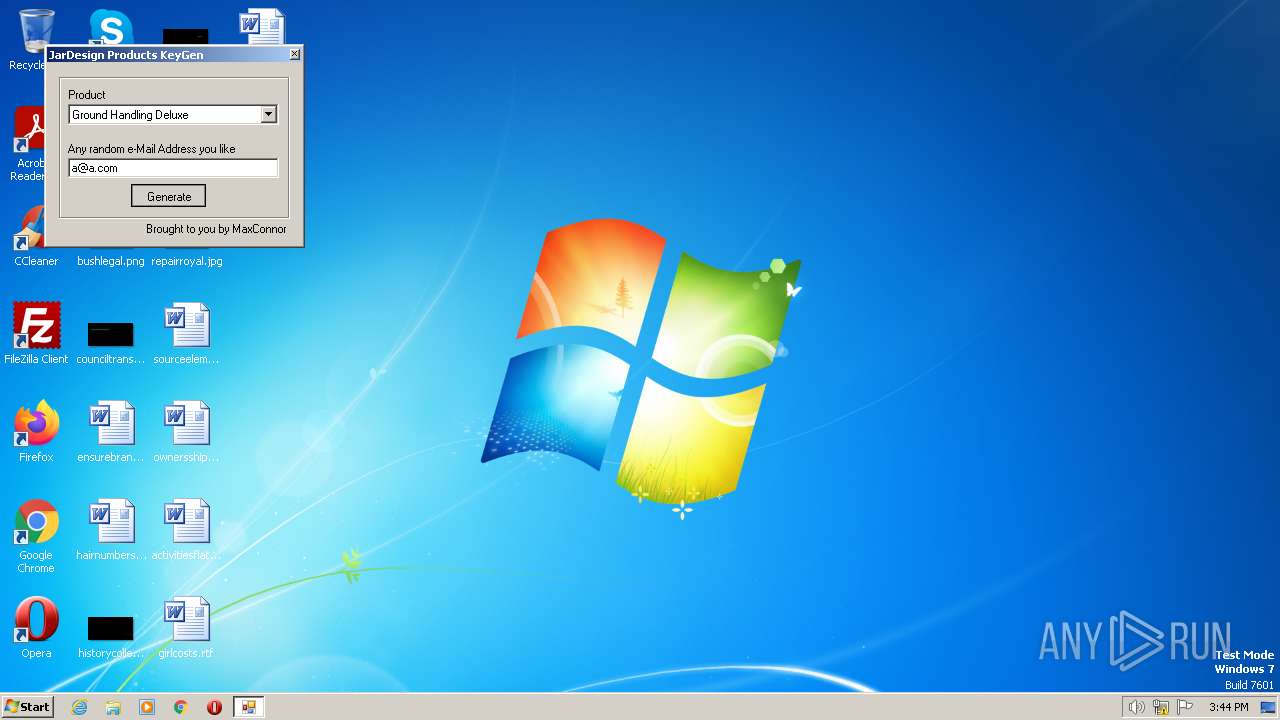
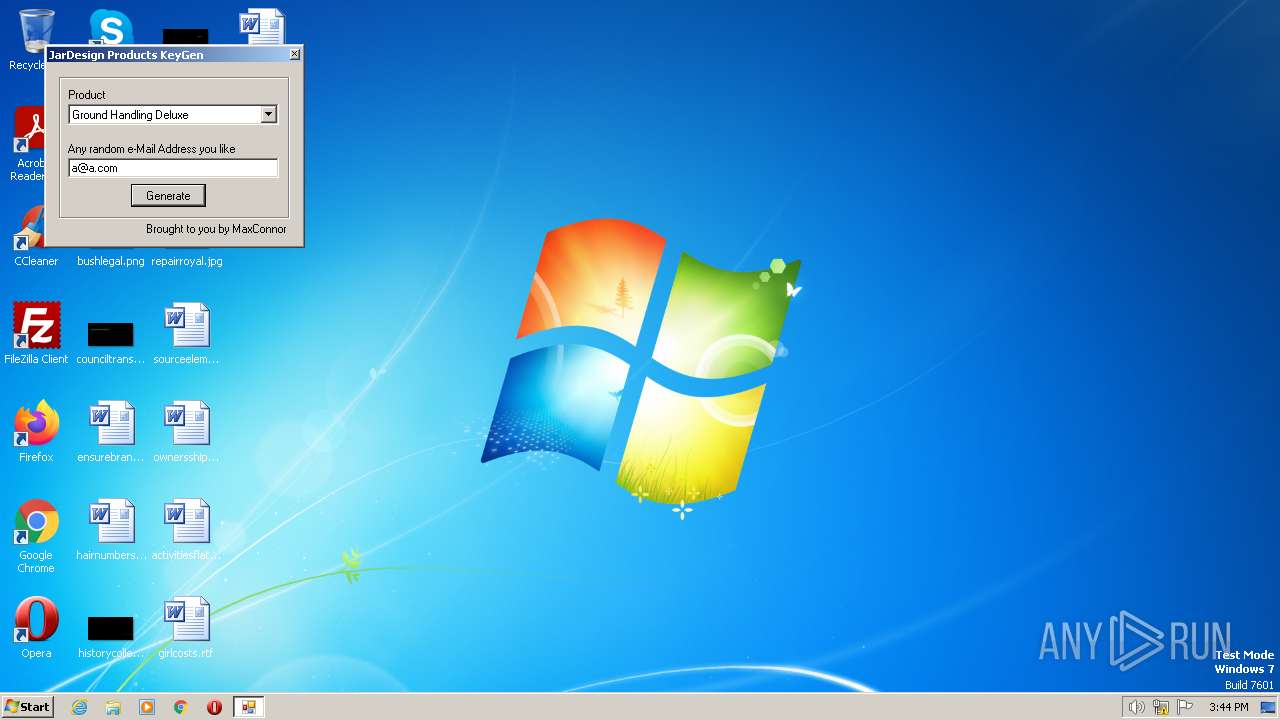
| File name: | JDKeygen.exe |
| Full analysis: | https://app.any.run/tasks/f95c6c60-fcd0-46c9-b5f4-966b89783f89 |
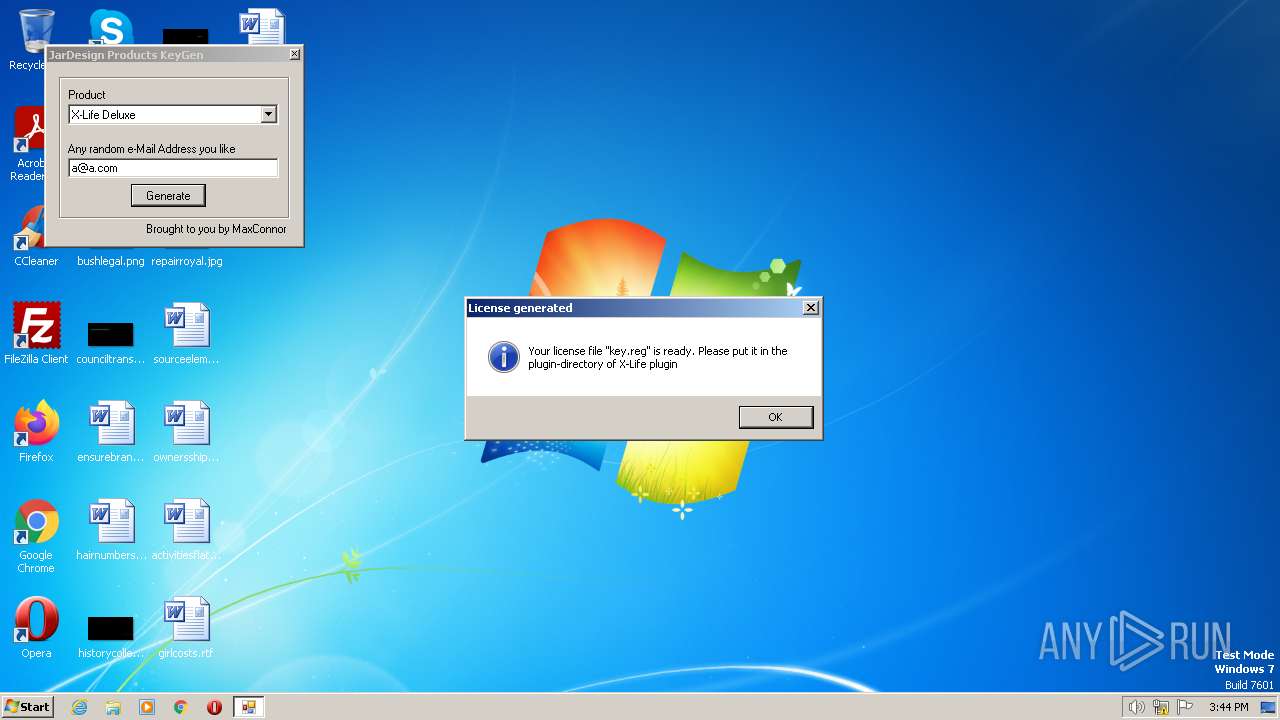
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2023, 14:43:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 6E3FD0DC16294E199E5727E1F8388F91 |
| SHA1: | D09F4912CEAE1A730FFBC9270EEF71F5CCEFA1B1 |
| SHA256: | 93296F3F6110E7217F42E18CD3FA8736069BF2478249427E67C4C078E75BBF1A |
| SSDEEP: | 6144:zvEN2U+T6i5LirrllHy4HUcMQY69z2pv4eroHGVLhn61:zENN+T5xYrllrU7QY69A4eroHGVLh8 |
MALICIOUS
Application was dropped or rewritten from another process
- jdkeygen.exe (PID: 2028)
SUSPICIOUS
Starts itself from another location
- JDKeygen.exe (PID: 3924)
Starts application with an unusual extension
- JDKeygen.exe (PID: 3924)
Executable content was dropped or overwritten
- JDKeygen.exe (PID: 3924)
INFO
Reads the machine GUID from the registry
- JDKeygen.exe (PID: 3924)
- icsys.icn.exe (PID: 656)
- jdkeygen.exe (PID: 2028)
The process checks LSA protection
- JDKeygen.exe (PID: 3924)
- icsys.icn.exe (PID: 656)
Checks supported languages
- JDKeygen.exe (PID: 3924)
- jdkeygen.exe (PID: 2028)
- icsys.icn.exe (PID: 656)
Reads the computer name
- JDKeygen.exe (PID: 3924)
- jdkeygen.exe (PID: 2028)
- icsys.icn.exe (PID: 656)
Create files in a temporary directory
- JDKeygen.exe (PID: 3924)
- icsys.icn.exe (PID: 656)
- jdkeygen.exe (PID: 2028)
Creates files or folders in the user directory
- JDKeygen.exe (PID: 3924)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Microsoft Visual Basic 6 (54.9) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (20.8) |
| .exe | | | Win64 Executable (generic) (18.4) |
| .exe | | | Win32 Executable (generic) (3) |
| .exe | | | Generic Win/DOS Executable (1.3) |
EXIF
EXE
| OriginalFileName: | Win.exe |
|---|---|
| InternalName: | Win |
| ProductVersion: | 1 |
| FileVersion: | 1 |
| ProductName: | Win |
| CompanyName: | Microsoft |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 1 |
| OSVersion: | 4 |
| EntryPoint: | 0x3670 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 12288 |
| CodeSize: | 176128 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| TimeStamp: | 2011:06:14 19:01:16+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Jun-2011 19:01:16 |
| Detected languages: |
|
| CompanyName: | Microsoft |
| ProductName: | Win |
| FileVersion: | 1.00 |
| ProductVersion: | 1.00 |
| InternalName: | Win |
| OriginalFilename: | Win.exe |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000B8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 14-Jun-2011 19:01:16 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002A728 | 0x0002B000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.9472 |
.data | 0x0002C000 | 0x00001B74 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0002E000 | 0x000005E0 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.55401 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.12197 | 500 | Unicode (UTF 16LE) | English - United States | RT_VERSION |
30001 | 3.49018 | 3280 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
Imports
MSVBVM60.DLL |
Total processes
38
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 656 | C:\Users\admin\AppData\Local\icsys.icn.exe | C:\Users\admin\AppData\Local\icsys.icn.exe | — | JDKeygen.exe | |||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2028 | c:\users\admin\appdata\local\temp\jdkeygen.exe | C:\Users\admin\AppData\Local\Temp\jdkeygen.exe | — | JDKeygen.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: JDKeygen Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3924 | "C:\Users\admin\AppData\Local\Temp\JDKeygen.exe" | C:\Users\admin\AppData\Local\Temp\JDKeygen.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
Total events
254
Read events
252
Write events
2
Delete events
0
Modification events
| (PID) Process: | (656) icsys.icn.exe | Key: | HKEY_CURRENT_USER\Software\VB and VBA Program Settings\Explorer\Process |
| Operation: | write | Name: | LO |
Value: 1 | |||
Executable files
2
Suspicious files
2
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3924 | JDKeygen.exe | C:\Users\admin\AppData\Local\icsys.icn.exe | executable | |
MD5:87B401E8CF8F6C23EDCCFF531EE50C20 | SHA256:43C6257184911746914E23169B6E50C3F7AE6D716A4A61ADACA785D96FCAD4D3 | |||
| 3924 | JDKeygen.exe | C:\users\admin\appdata\local\temp\jdkeygen.exe | executable | |
MD5:33E7502FE12D1F8B536FC0646BA5C82E | SHA256:50C9382AC1C200BC95C4A43BBBD138A756D55CED8E3E8AF8F8417E1BE3EDE0E8 | |||
| 3924 | JDKeygen.exe | C:\Users\admin\AppData\Local\Temp\~DF62E741D02CB6FDFC.TMP | binary | |
MD5:54A03545644972EC8100C47868F327A5 | SHA256:CCE429486C5E9B75ED24756497436E54FDB1A3FDEE9A0C4C008AB5BEA72AAD30 | |||
| 656 | icsys.icn.exe | C:\Users\admin\AppData\Local\Temp\~DF8BC44B22B050EDE6.TMP | binary | |
MD5:863B896333848B34EDAF0C312BF8E8F7 | SHA256:5B508D19E7C1975835023C484BA951489C2741D47ADB4C792099CCA44767B266 | |||
| 2028 | jdkeygen.exe | C:\Users\admin\AppData\Local\Temp\key.reg | text | |
MD5:6CD6706AB29A81F4BB96FA26F366B0DD | SHA256:81A361E98D0EC3D14E6CBD48719052BE468400D4CB09EFFCDE403174C1D289EA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3416 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |