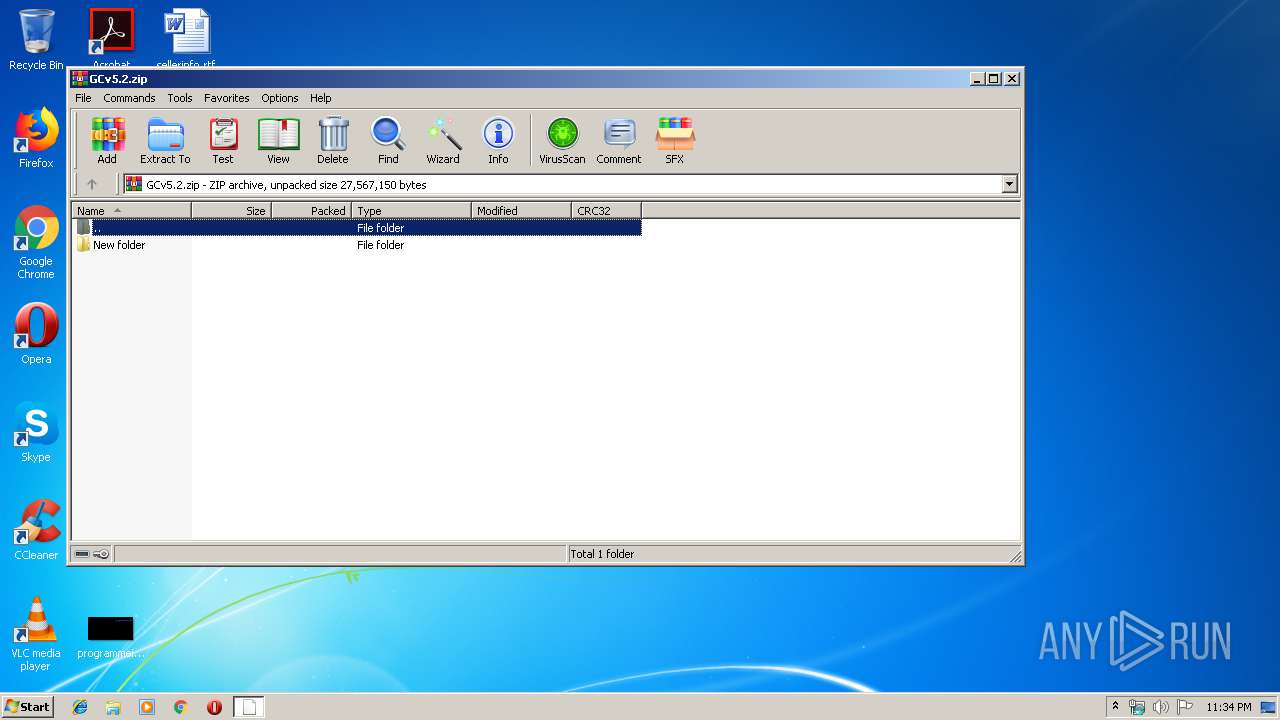
| File name: | GCv5.2.zip |
| Full analysis: | https://app.any.run/tasks/8679a172-db58-43e4-b4f1-77757c1603a8 |
| Verdict: | Malicious activity |
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
| Analysis date: | July 16, 2019, 22:33:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | C61E0472DEAE85F11D904187064B3AF1 |
| SHA1: | A52A841D0748A461B1F081C84DAD1F2B3D6857D6 |
| SHA256: | 9321C8C7A08B90E9DD0FB7991BCDFE95B088EFF60E2FB0268411373DC5AB6243 |
| SSDEEP: | 12288:PyNjzZYSdQjaAYBmmkFBOfTM9ooAbAxn3Cd:P2jzZtdAYreOL0ZRQ |
MALICIOUS
Application was dropped or rewritten from another process
- c2.exe (PID: 1864)
Loads dropped or rewritten executable
- c2.exe (PID: 1864)
- explorer.exe (PID: 124)
- WinRAR.exe (PID: 3044)
- SearchProtocolHost.exe (PID: 2136)
- DllHost.exe (PID: 1868)
- taskeng.exe (PID: 1948)
- WinRAR.exe (PID: 2848)
- dwm.exe (PID: 1988)
- ctfmon.exe (PID: 304)
Actions looks like stealing of personal data
- c2.exe (PID: 1864)
Writes file to Word startup folder
- c2.exe (PID: 1864)
Renames files like Ransomware
- c2.exe (PID: 1864)
Dropped file may contain instructions of ransomware
- c2.exe (PID: 1864)
Deletes shadow copies
- c2.exe (PID: 1864)
GANDCRAB detected
- c2.exe (PID: 1864)
SUSPICIOUS
Executable content was dropped or overwritten
- c2.exe (PID: 1864)
- WinRAR.exe (PID: 3044)
Application launched itself
- WinRAR.exe (PID: 2848)
Creates files in the program directory
- c2.exe (PID: 1864)
Reads the cookies of Mozilla Firefox
- c2.exe (PID: 1864)
Executed as Windows Service
- vssvc.exe (PID: 3552)
Creates files in the user directory
- c2.exe (PID: 1864)
INFO
Dropped object may contain Bitcoin addresses
- c2.exe (PID: 1864)
Reads Microsoft Office registry keys
- SearchProtocolHost.exe (PID: 2136)
Dropped object may contain TOR URL's
- c2.exe (PID: 1864)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:02:28 04:42:15 |
| ZipCRC: | 0x9c2a6d3d |
| ZipCompressedSize: | 66064 |
| ZipUncompressedSize: | 27216000 |
| ZipFileName: | New folder/33.bat |
Total processes
41
Monitored processes
11
Malicious processes
4
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 304 | C:\Windows\System32\ctfmon.exe | C:\Windows\System32\ctfmon.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CTF Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1864 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3044.46849\c2.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3044.46849\c2.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1868 | C:\Windows\system32\DllHost.exe /Processid:{AB8902B4-09CA-4BB6-B78D-A8F59079A8D5} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1948 | taskeng.exe {5D27F6D9-1489-4C63-9AA3-61A9E7172AB6} | C:\Windows\System32\taskeng.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Engine Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1988 | "C:\Windows\system32\Dwm.exe" | C:\Windows\System32\dwm.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Desktop Window Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2096 | "C:\Windows\system32\wbem\wmic.exe" shadowcopy delete | C:\Windows\system32\wbem\wmic.exe | c2.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2136 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe_S-1-5-21-1302019708-1500728564-335382590-10009_ Global\UsGthrCtrlFltPipeMssGthrPipe_S-1-5-21-1302019708-1500728564-335382590-10009 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" "1" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
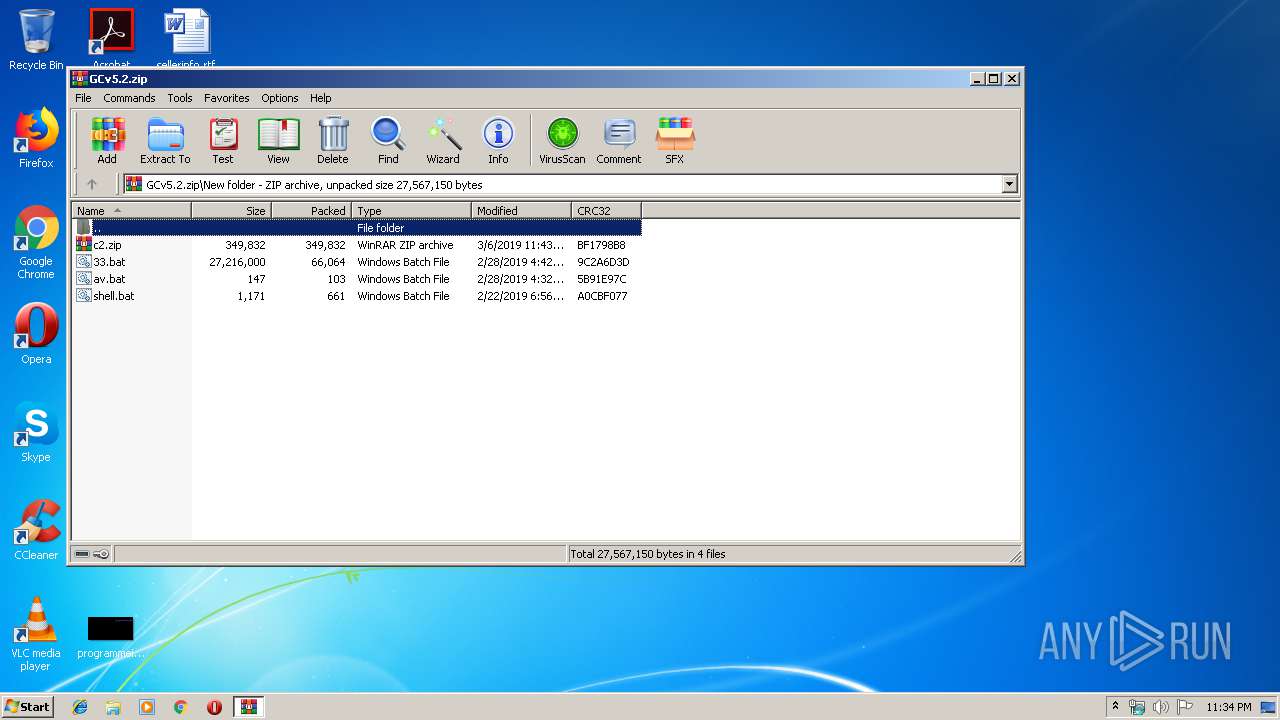
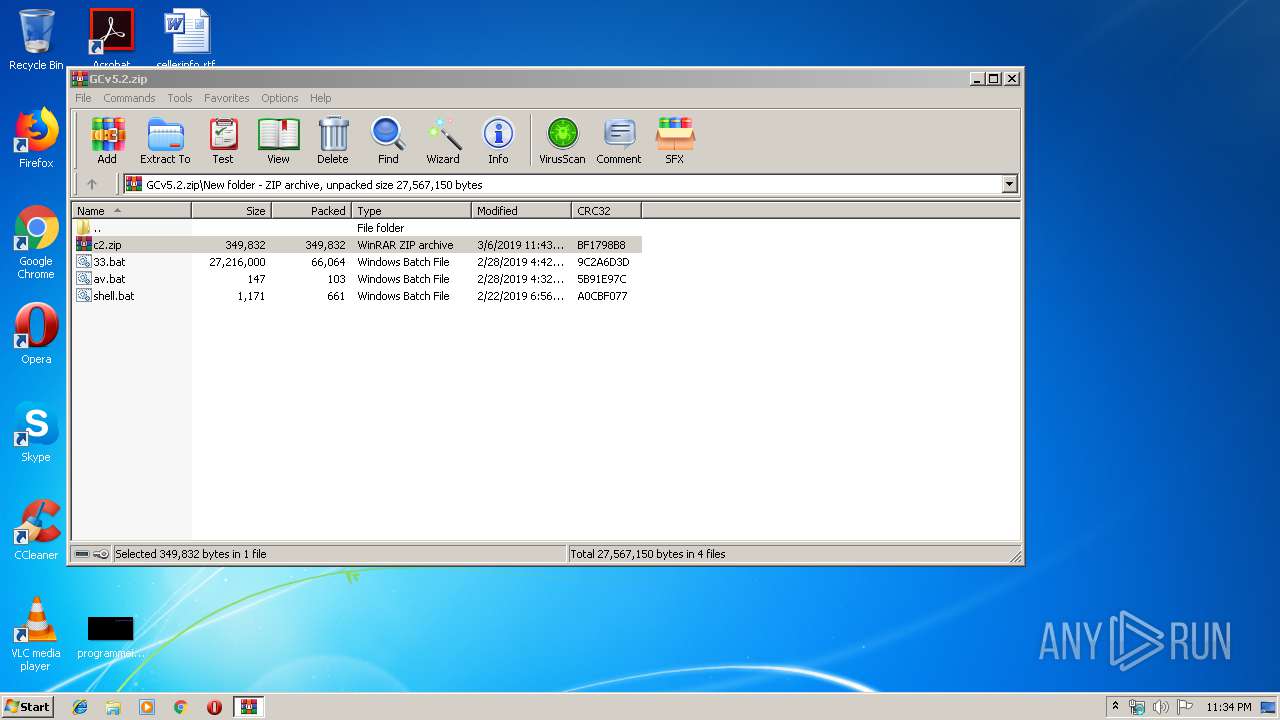
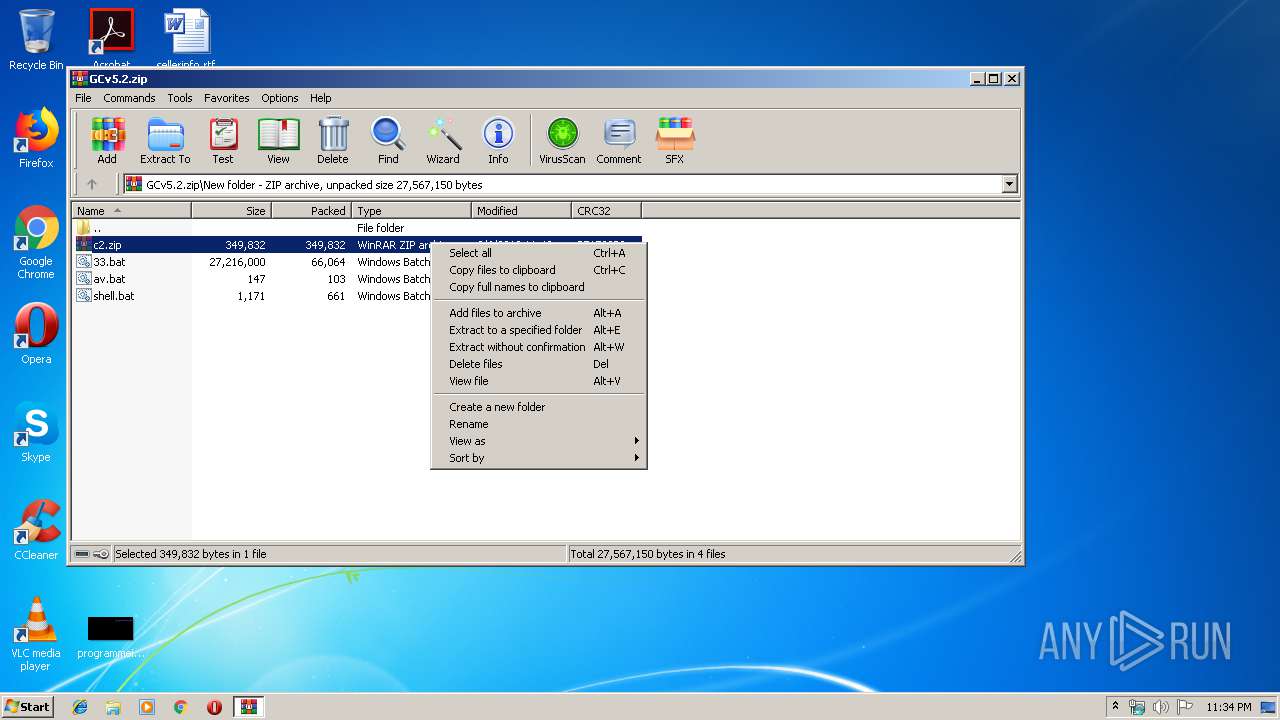
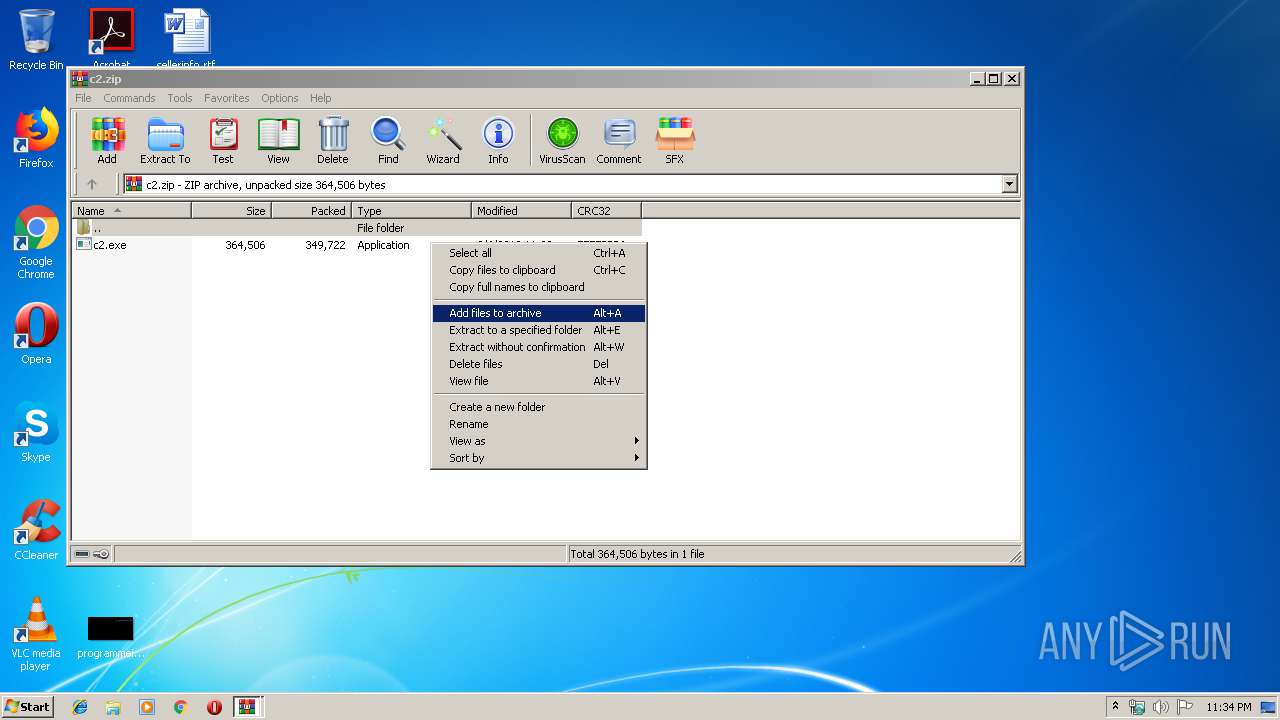
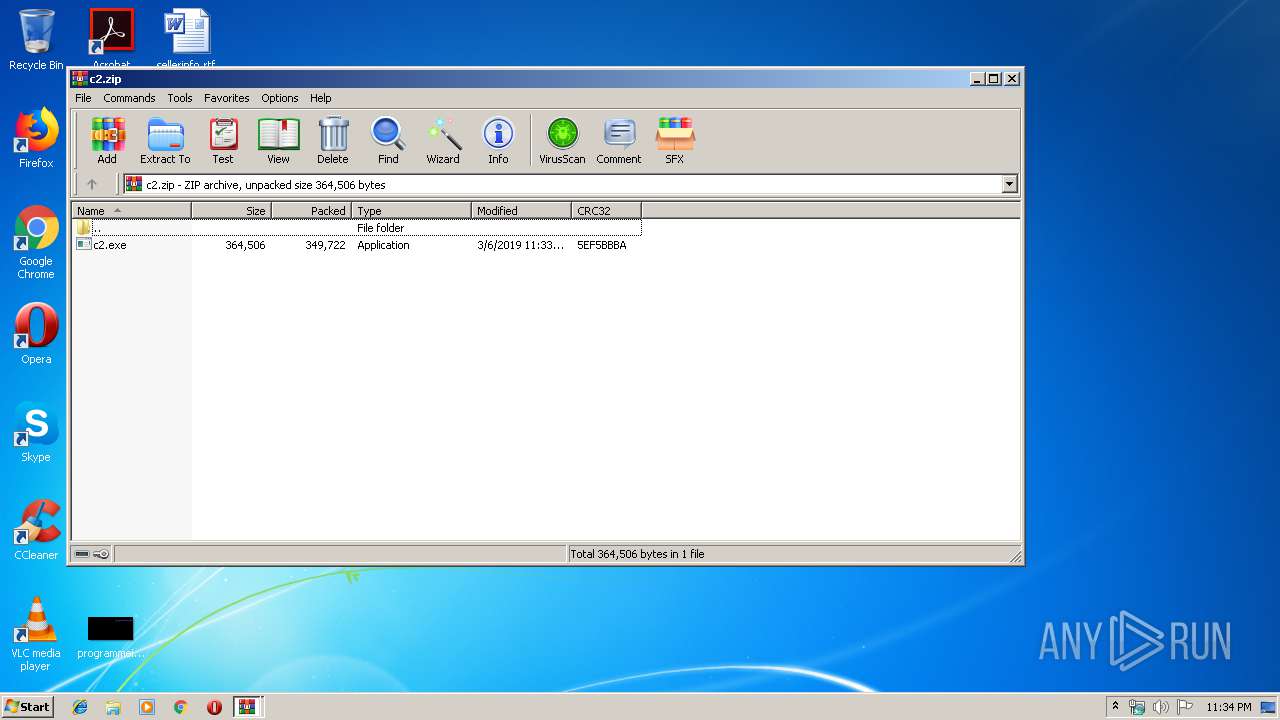
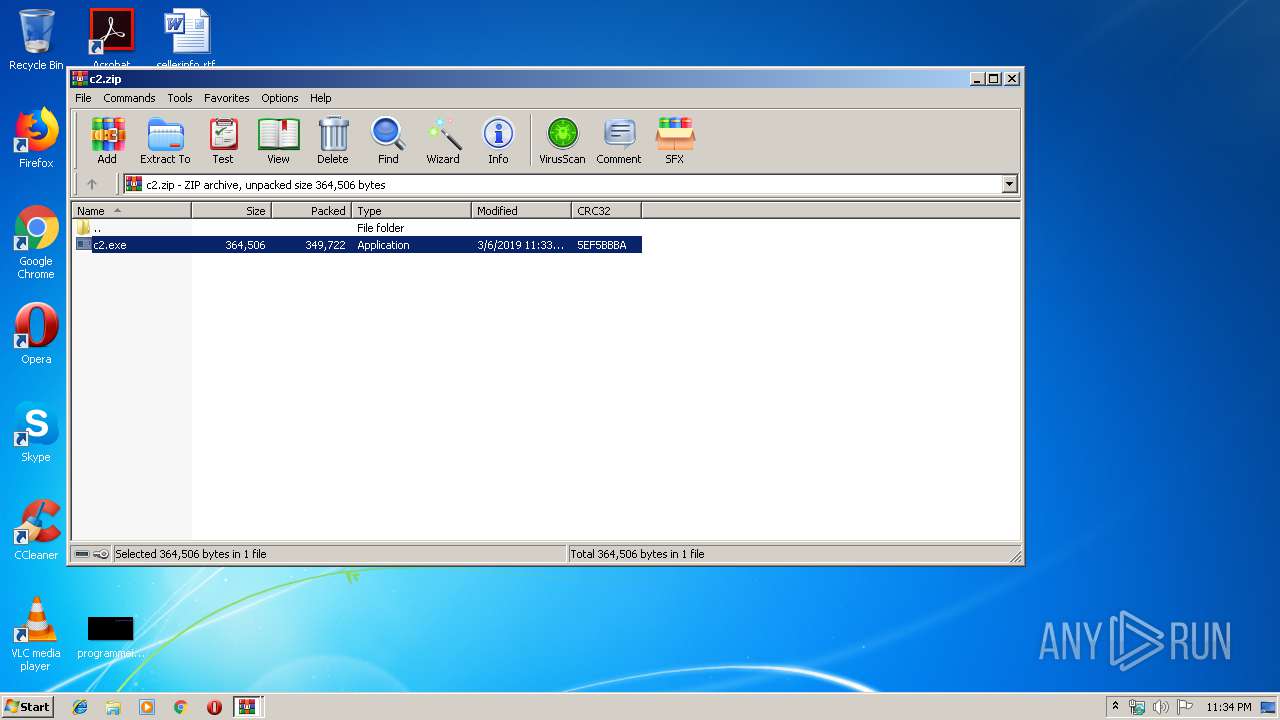
| 2848 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\GCv5.2.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3044 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIa2848.46073\c2.zip | C:\Program Files\WinRAR\WinRAR.exe | WinRAR.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
5 308
Read events
5 241
Write events
67
Delete events
0
Modification events
| (PID) Process: | (2848) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2848) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2848) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2848) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\GCv5.2.zip | |||
| (PID) Process: | (2848) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2848) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2848) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2848) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (124) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | a |
Value: WinRAR.exe | |||
| (PID) Process: | (124) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | MRUList |
Value: a | |||
Executable files
2
Suspicious files
439
Text files
322
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1864 | c2.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\boot.sdi | — | |
MD5:— | SHA256:— | |||
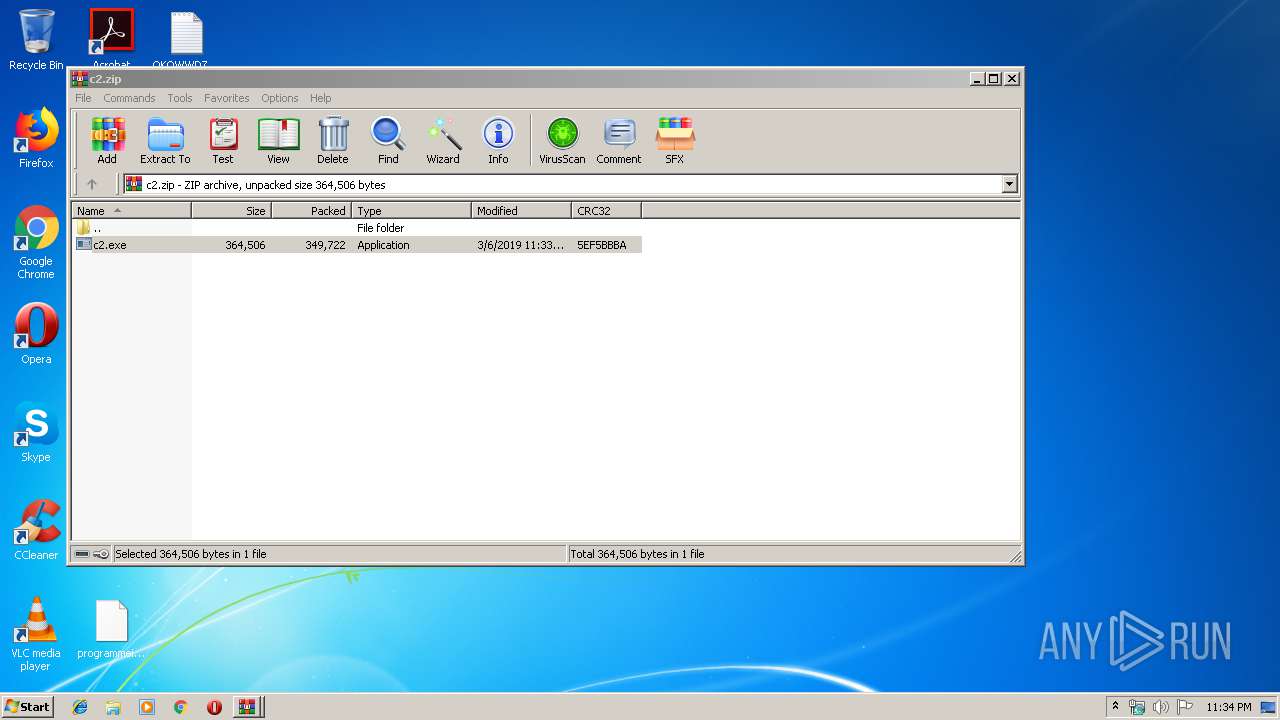
| 1864 | c2.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim.qkowwdz | — | |
MD5:— | SHA256:— | |||
| 1864 | c2.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{05ed3515-06b3-48f6-8cf2-bf24b1bf0727}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 1864 | c2.exe | C:\QKOWWDZ-MANUAL.txt | text | |
MD5:— | SHA256:— | |||
| 1864 | c2.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim | — | |
MD5:— | SHA256:— | |||
| 1864 | c2.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{14e6e058-39ee-43ce-ac15-7acb7d834dae}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 2848 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2848.46073\c2.zip | compressed | |
MD5:— | SHA256:— | |||
| 1864 | c2.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{16d74681-6bc3-4c44-97f0-8b8dfefe2355}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 3044 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3044.46849\c2.exe | executable | |
MD5:— | SHA256:— | |||
| 1864 | c2.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{31c64f4e-4eef-4f67-acde-eb3f4d02f051}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
1
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.kakaocorp.link |
| malicious |
Threats
1 ETPRO signatures available at the full report