| File name: | map.jnlp |
| Full analysis: | https://app.any.run/tasks/9a9cdfc5-bd13-4bb1-8fa0-cb31022c492f |
| Verdict: | Malicious activity |
| Analysis date: | April 22, 2020, 09:58:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/xml |
| File info: | XML 1.0 document, ASCII text |
| MD5: | E48255C212774748199D6BE7F31B58B4 |
| SHA1: | C16D4AC1C81B41BB1D3F0A075217101CA7171C87 |
| SHA256: | 9321AEB82EB04D2ADAD7C0D36002C6CC7589943EFEB26FB330B5320AA3FA0DA7 |
| SSDEEP: | 12:TMHdIoHd1DM2U+hllPv9y/AoOsodSh8B/umd9oB:2dl02UiDPveArszW/um7oB |
MALICIOUS
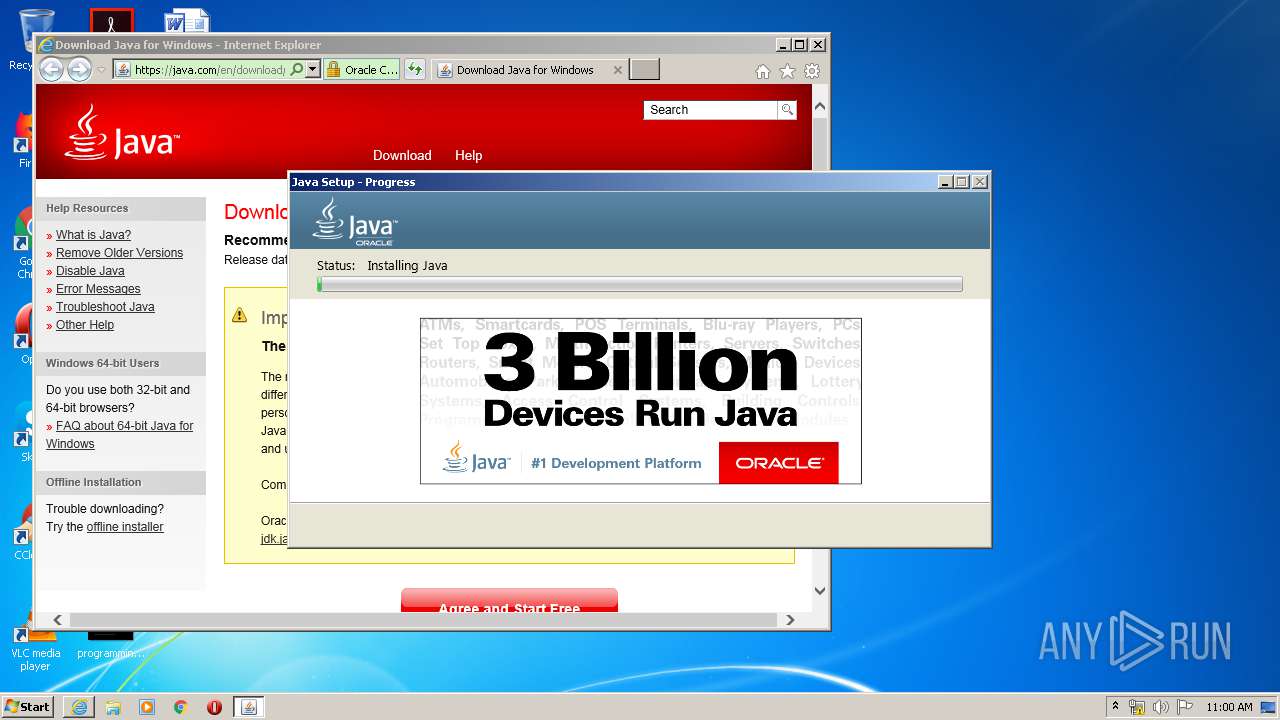
Application was dropped or rewritten from another process
- JavaSetup8u251.exe (PID: 1444)
- JavaSetup8u251.exe (PID: 3220)
- JavaSetup8u251.exe (PID: 2540)
- LZMA_EXE (PID: 3384)
- LZMA_EXE (PID: 1708)
- bspatch.exe (PID: 2056)
- javaw.exe (PID: 3780)
- unpack200.exe (PID: 3596)
- unpack200.exe (PID: 1876)
- unpack200.exe (PID: 4084)
- unpack200.exe (PID: 3784)
- unpack200.exe (PID: 3792)
- unpack200.exe (PID: 956)
- javaws.exe (PID: 1544)
- jp2launcher.exe (PID: 2136)
- javaws.exe (PID: 2552)
- unpack200.exe (PID: 3460)
- ssvagent.exe (PID: 2960)
- jp2launcher.exe (PID: 4088)
Loads dropped or rewritten executable
- installer.exe (PID: 1720)
- unpack200.exe (PID: 4084)
- unpack200.exe (PID: 3596)
- unpack200.exe (PID: 3784)
- unpack200.exe (PID: 1876)
- unpack200.exe (PID: 3460)
- unpack200.exe (PID: 956)
- unpack200.exe (PID: 3792)
- ssvagent.exe (PID: 2960)
- javaws.exe (PID: 1544)
- jp2launcher.exe (PID: 2136)
- javaws.exe (PID: 2552)
- svchost.exe (PID: 860)
- jp2launcher.exe (PID: 4088)
- javaw.exe (PID: 3780)
Changes settings of System certificates
- JavaSetup8u251.exe (PID: 3220)
Loads the Task Scheduler COM API
- MsiExec.exe (PID: 1792)
SUSPICIOUS
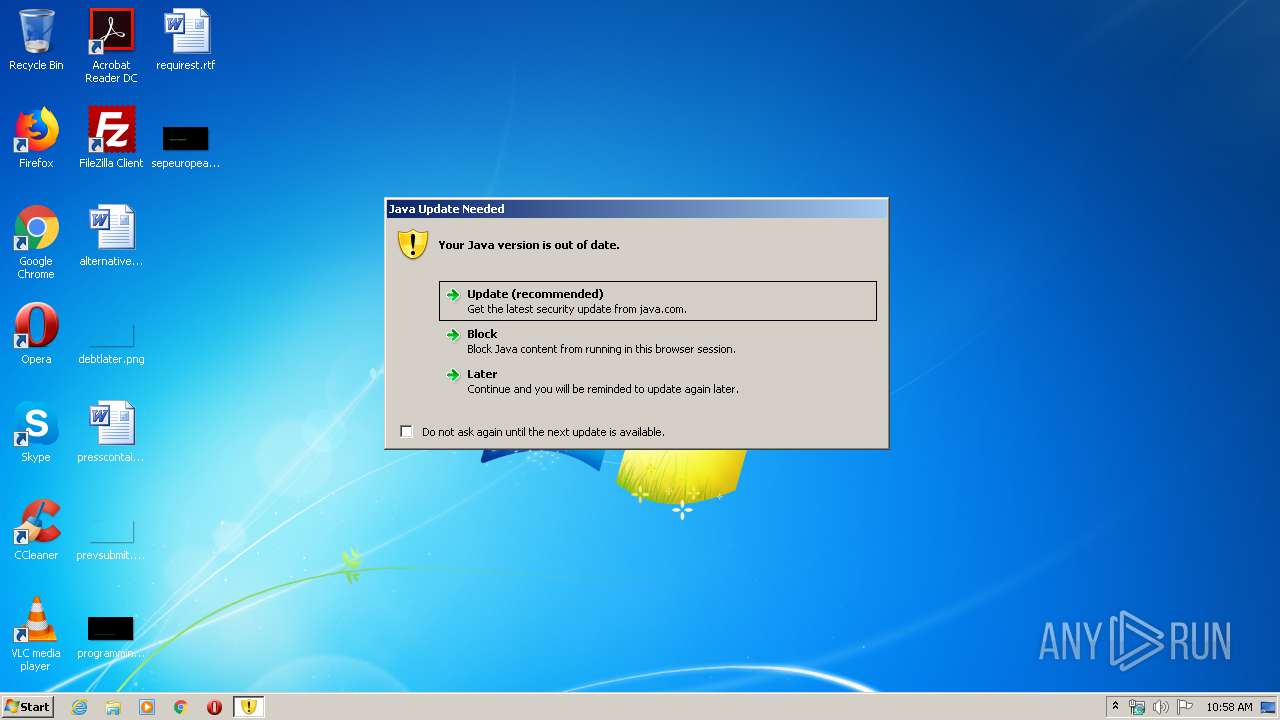
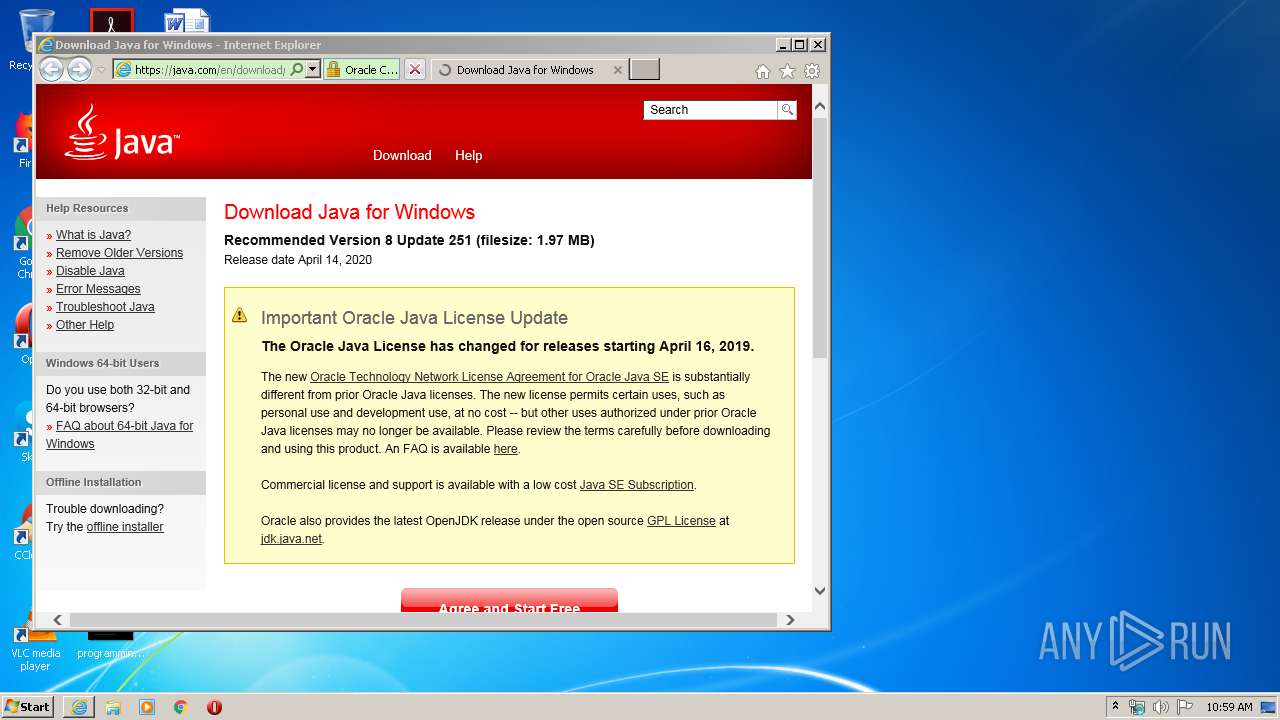
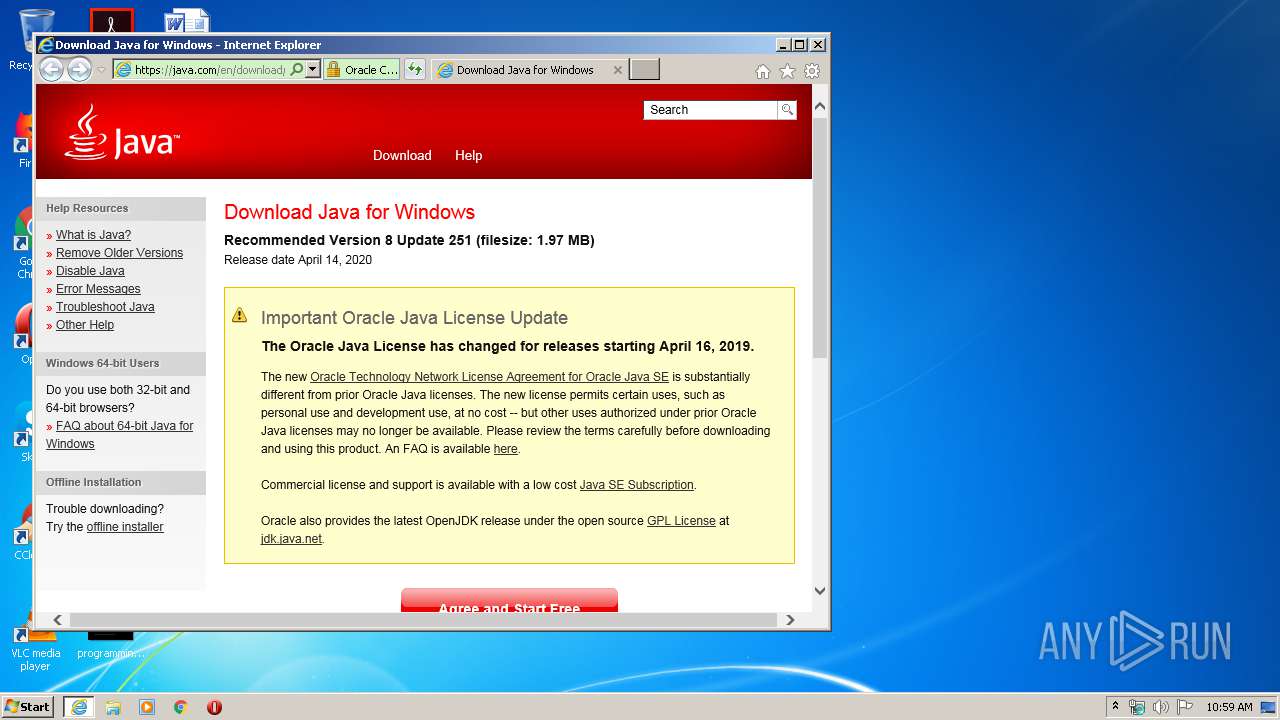
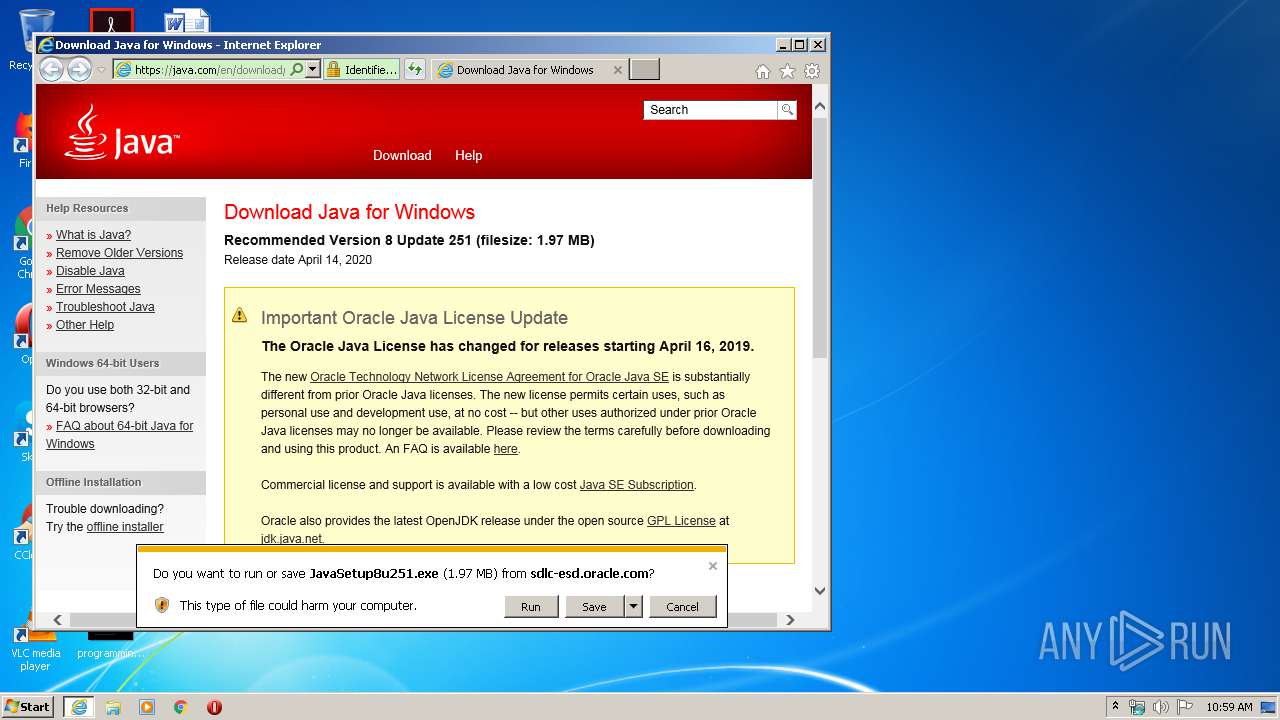
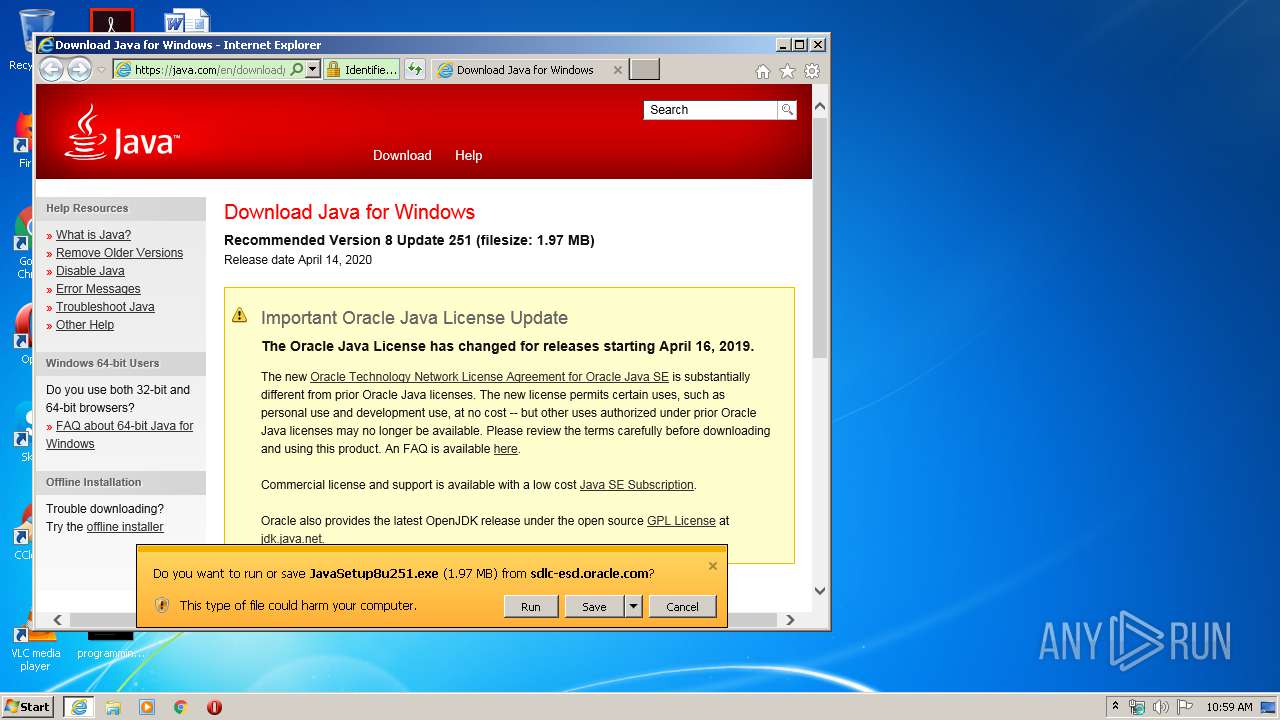
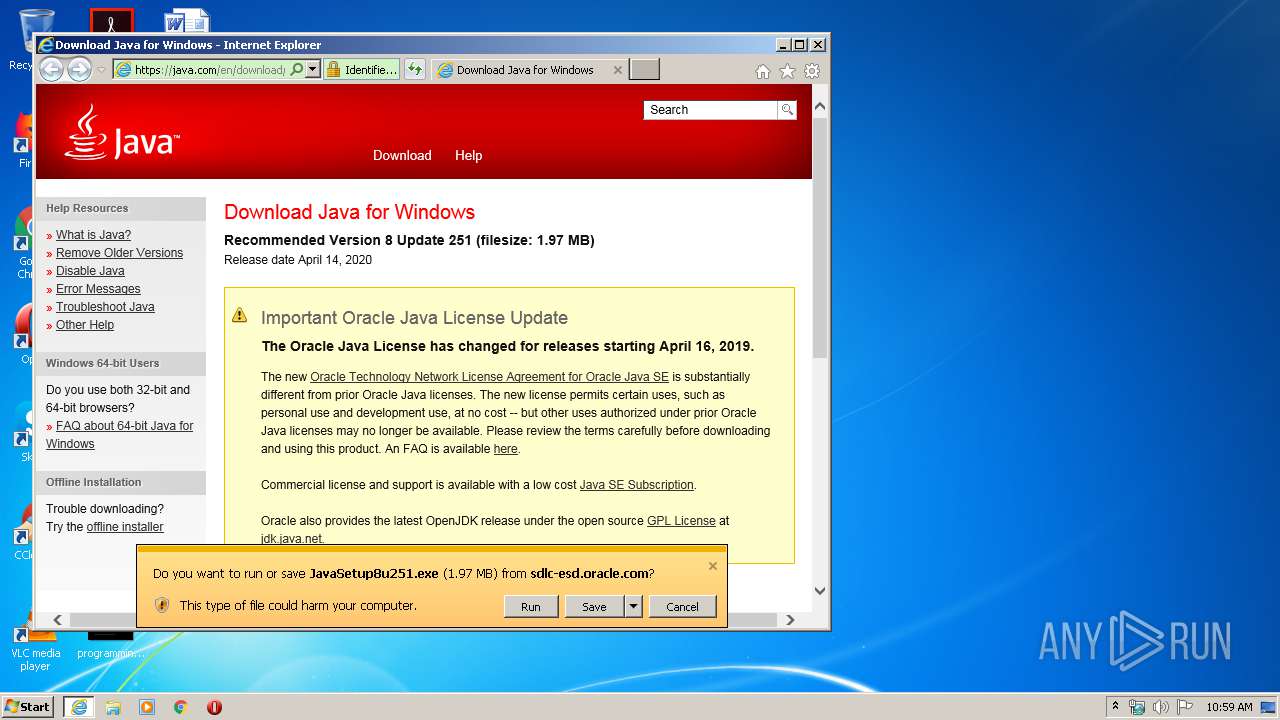
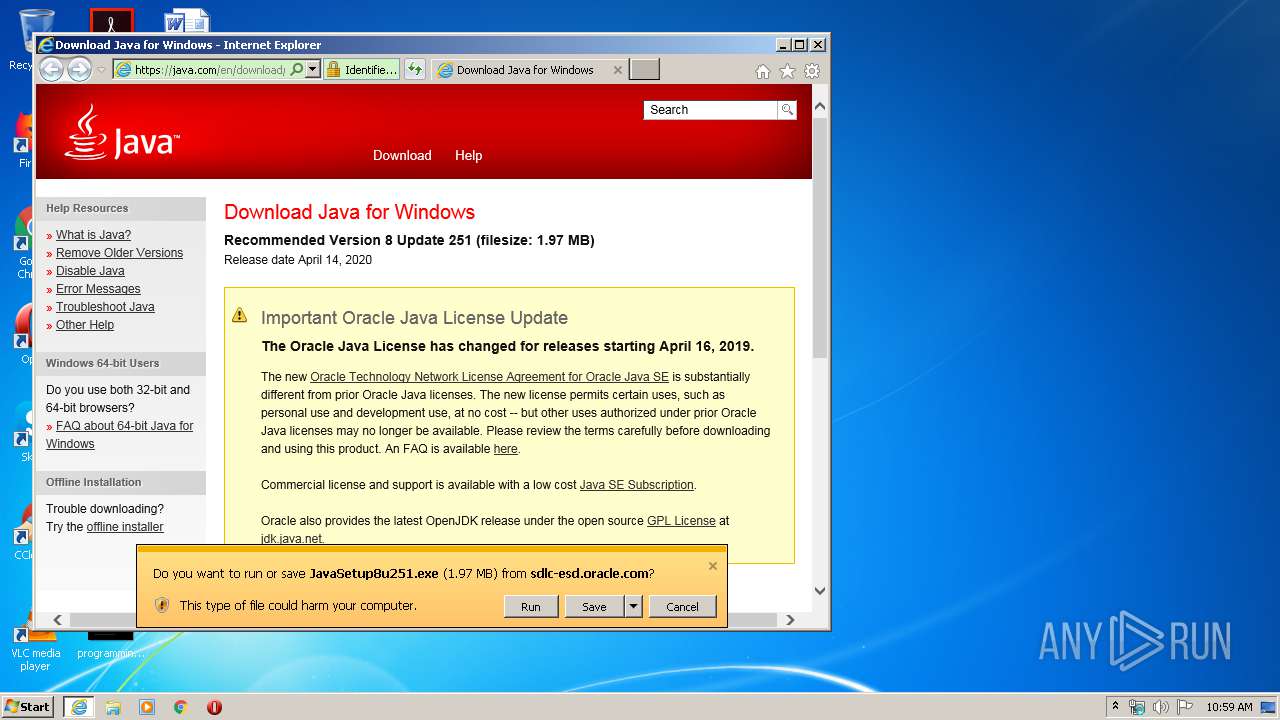
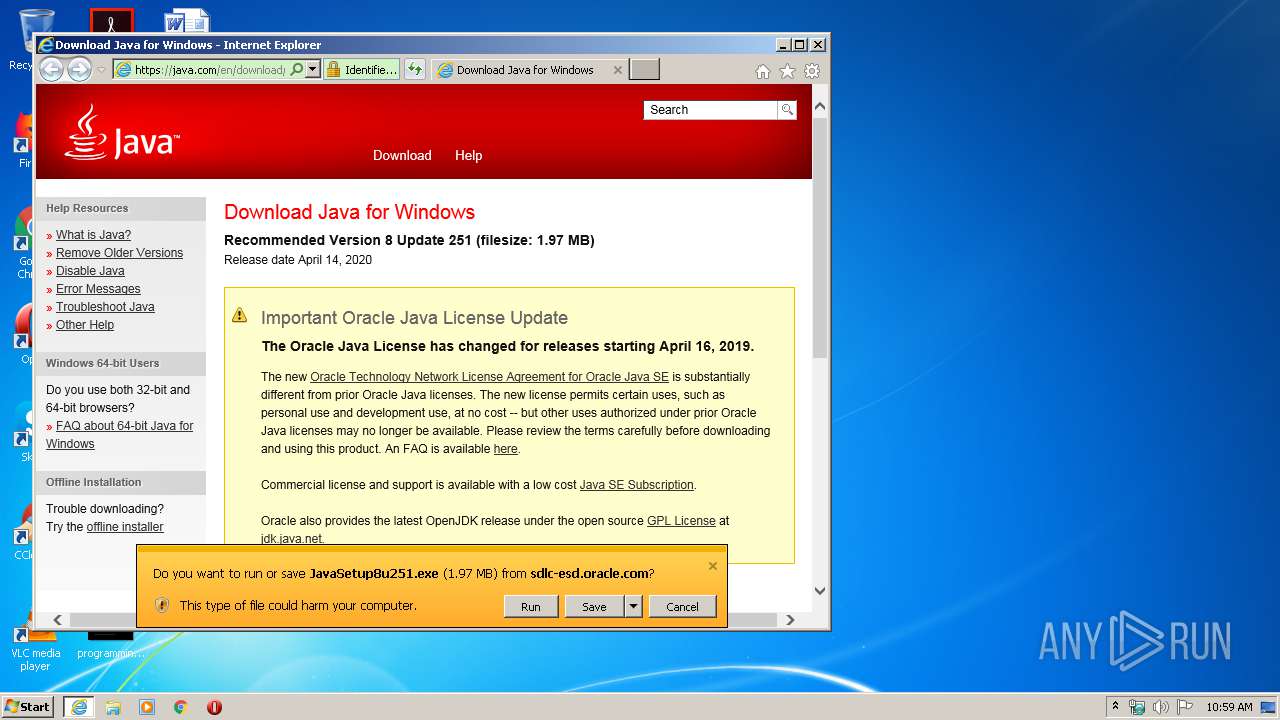
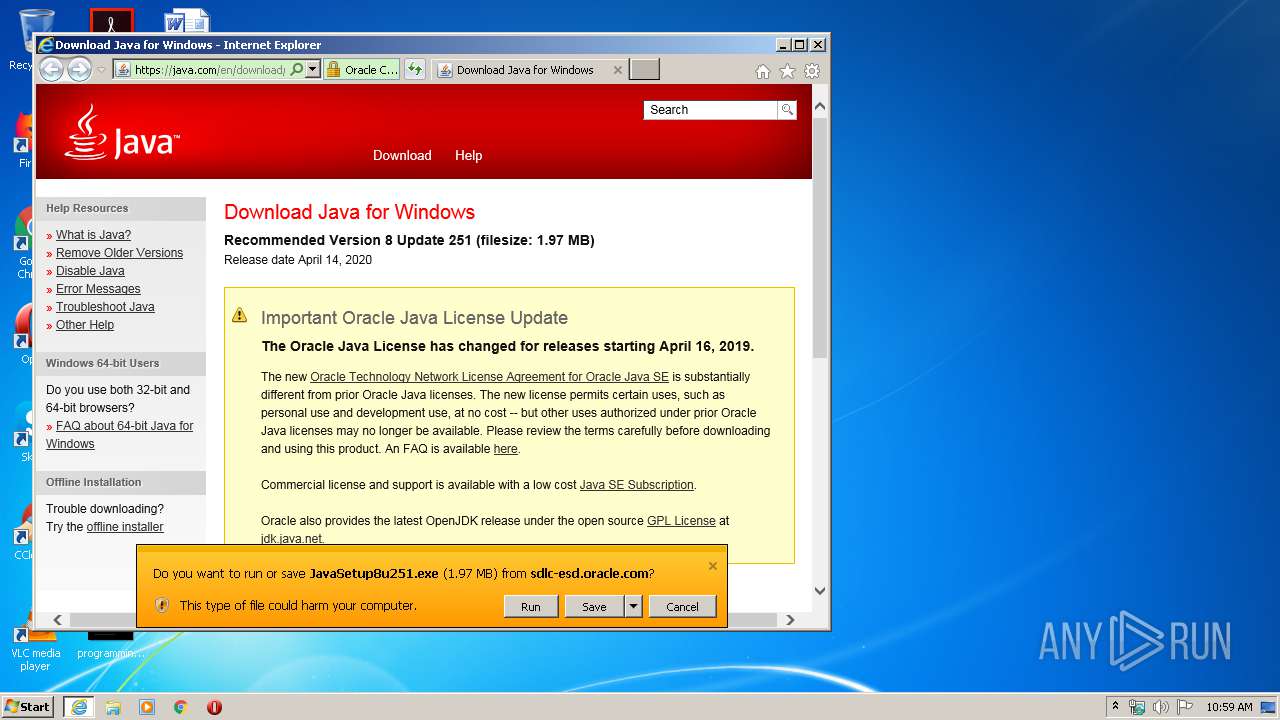
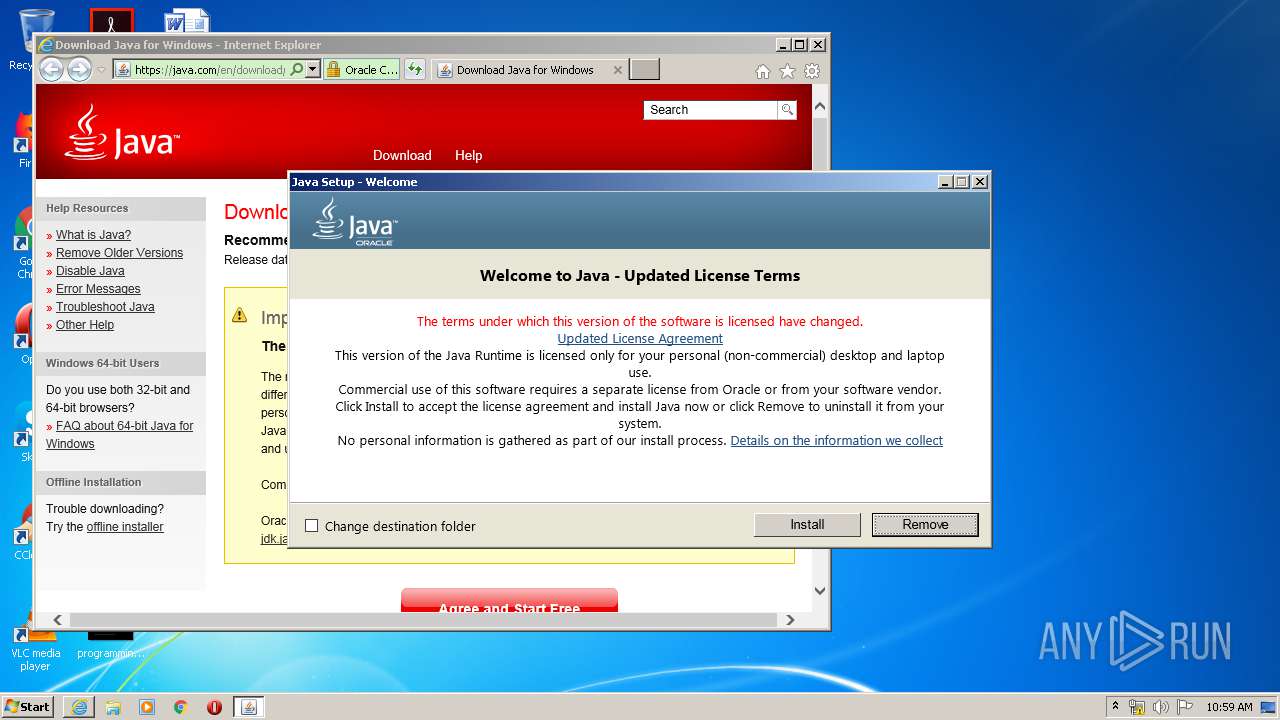
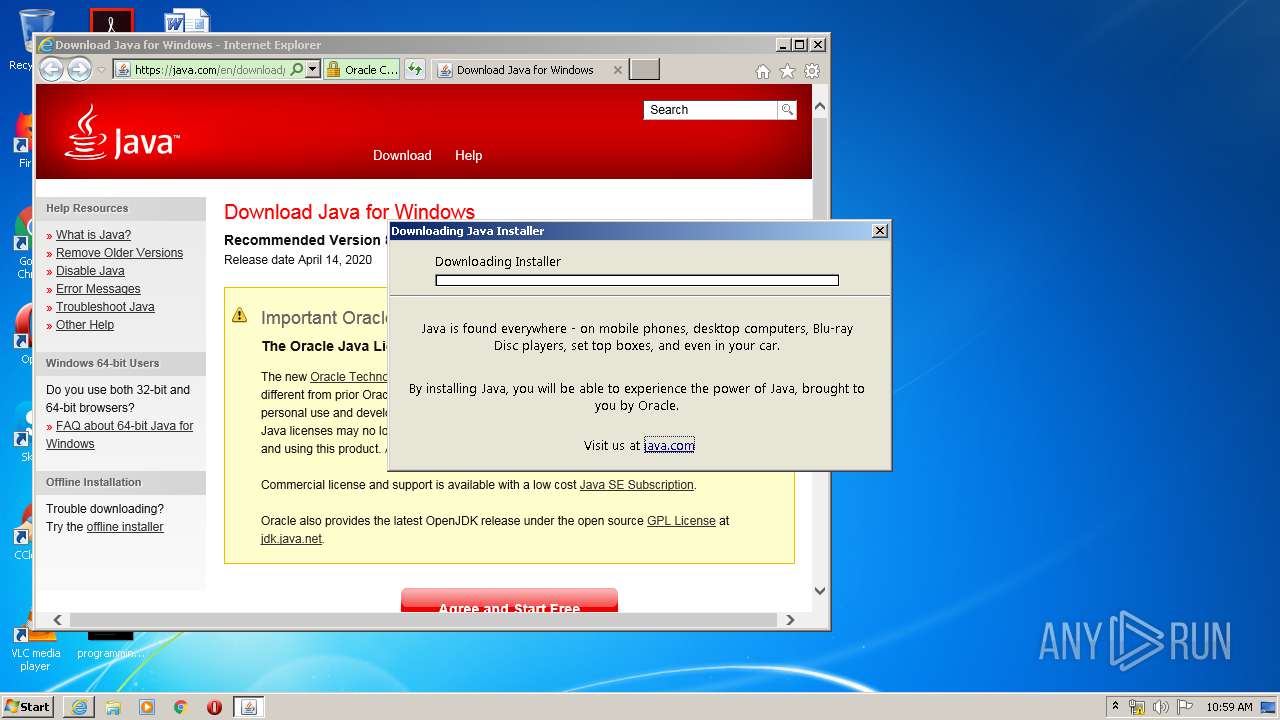
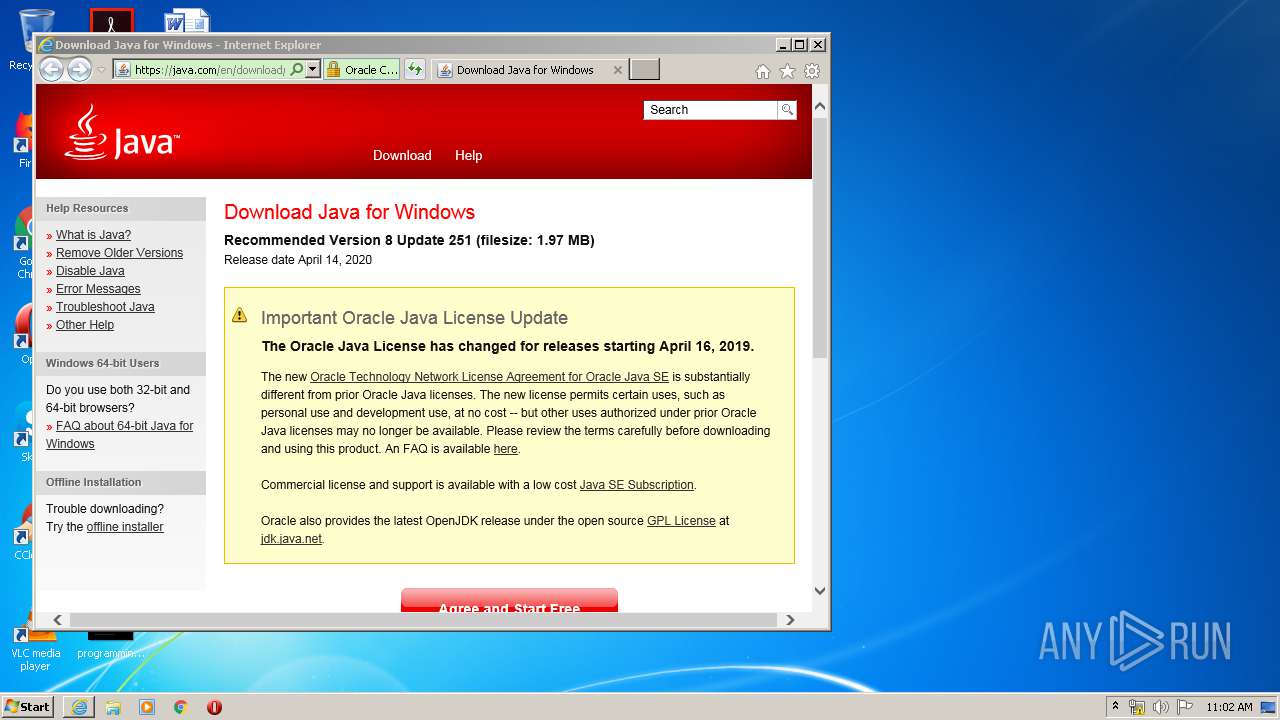
Starts Internet Explorer
- javaws.exe (PID: 3664)
Check for Java to be installed
- javaws.exe (PID: 3664)
- installer.exe (PID: 1720)
- JavaSetup8u251.exe (PID: 3220)
Executes JAVA applets
- javaws.exe (PID: 3664)
- installer.exe (PID: 1720)
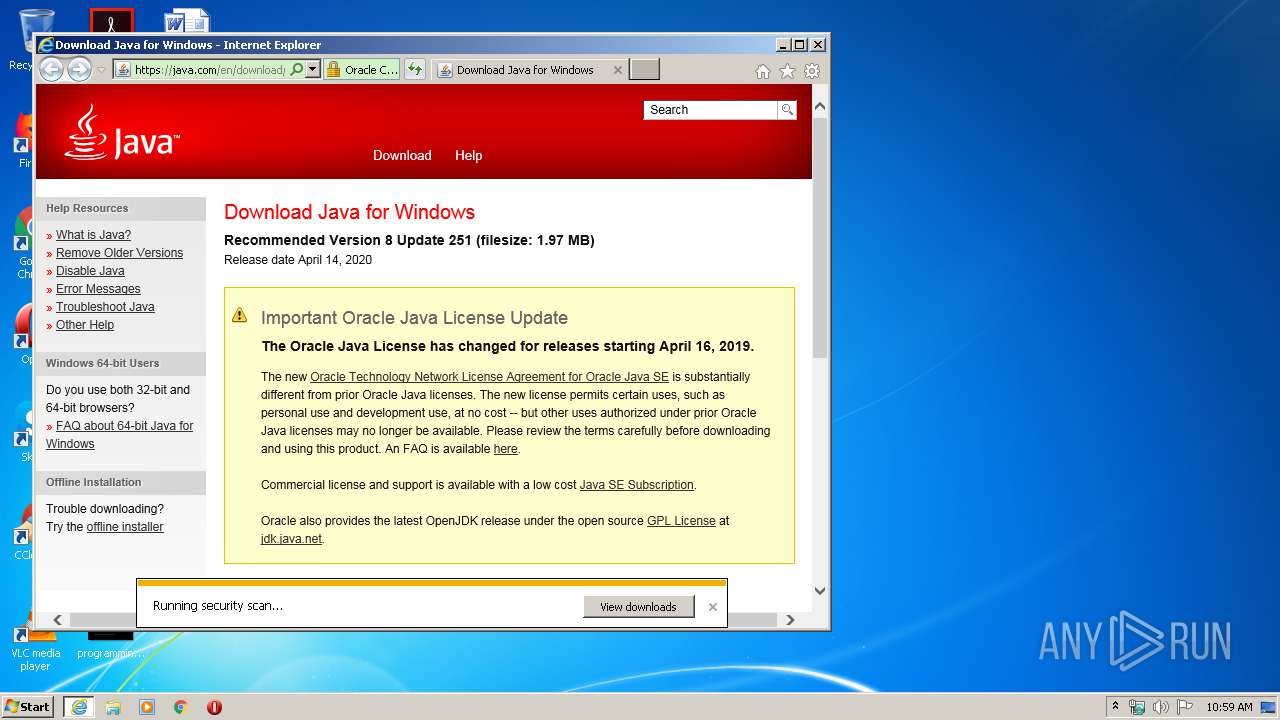
Executable content was dropped or overwritten
- iexplore.exe (PID: 3912)
- JavaSetup8u251.exe (PID: 1444)
- iexplore.exe (PID: 2228)
- msiexec.exe (PID: 1912)
- JavaSetup8u251.exe (PID: 3220)
- installer.exe (PID: 1720)
Reads Internet Cache Settings
- JavaSetup8u251.exe (PID: 3220)
Reads internet explorer settings
- JavaSetup8u251.exe (PID: 3220)
Starts application with an unusual extension
- JavaSetup8u251.exe (PID: 3220)
Creates files in the program directory
- bspatch.exe (PID: 2056)
- unpack200.exe (PID: 1876)
- unpack200.exe (PID: 3784)
- unpack200.exe (PID: 3792)
- unpack200.exe (PID: 4084)
- unpack200.exe (PID: 3596)
- unpack200.exe (PID: 3460)
- unpack200.exe (PID: 956)
- javaw.exe (PID: 3780)
- installer.exe (PID: 1720)
Modifies the open verb of a shell class
- installer.exe (PID: 1720)
Removes files from Windows directory
- installer.exe (PID: 1720)
Creates files in the Windows directory
- installer.exe (PID: 1720)
Changes the autorun value in the registry
- msiexec.exe (PID: 1912)
Adds / modifies Windows certificates
- JavaSetup8u251.exe (PID: 3220)
Creates COM task schedule object
- ssvagent.exe (PID: 2960)
- installer.exe (PID: 1720)
INFO
Application launched itself
- iexplore.exe (PID: 2228)
- msiexec.exe (PID: 1912)
Reads Internet Cache Settings
- iexplore.exe (PID: 2228)
- iexplore.exe (PID: 3912)
Changes internet zones settings
- iexplore.exe (PID: 2228)
Creates files in the user directory
- iexplore.exe (PID: 3912)
- iexplore.exe (PID: 2228)
Reads internet explorer settings
- iexplore.exe (PID: 3912)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2228)
Reads settings of System Certificates
- iexplore.exe (PID: 2228)
- JavaSetup8u251.exe (PID: 3220)
- iexplore.exe (PID: 3912)
- msiexec.exe (PID: 1912)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 940)
- MsiExec.exe (PID: 2564)
- MsiExec.exe (PID: 2920)
- MsiExec.exe (PID: 3244)
Creates a software uninstall entry
- msiexec.exe (PID: 1912)
Creates files in the program directory
- msiexec.exe (PID: 1912)
Dropped object may contain Bitcoin addresses
- JavaSetup8u251.exe (PID: 3220)
- MsiExec.exe (PID: 940)
- installer.exe (PID: 1720)
- MsiExec.exe (PID: 2564)
- MsiExec.exe (PID: 1792)
- MsiExec.exe (PID: 3244)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2228)
Changes settings of System certificates
- iexplore.exe (PID: 2228)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .jnlp | | | Java Web Start application descriptor (88.3) |
|---|---|---|
| .xml | | | Generic XML (ASCII) (11.6) |
EXIF
XMP
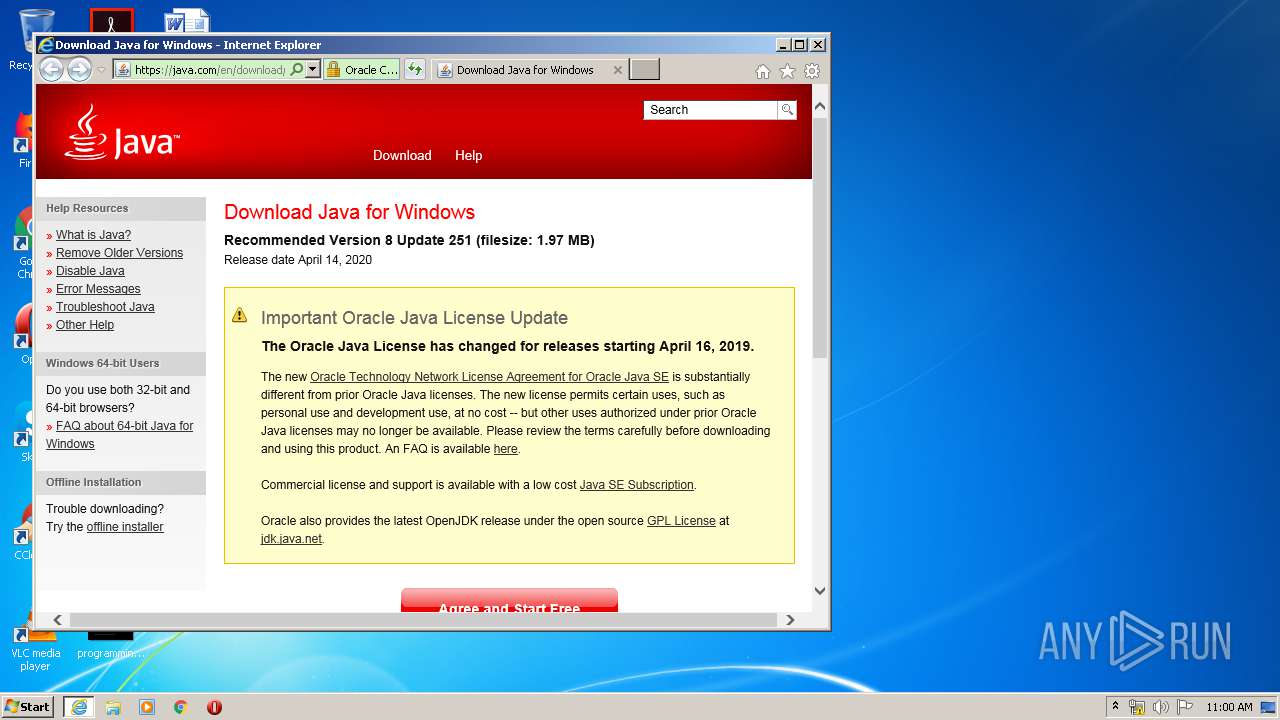
| JnlpSpec: | 1.0+ |
|---|---|
| JnlpCodebase: | https://coronavirusmaps.pro/ |
| JnlpHref: | map.jnlp |
| JnlpInformationTitle: | COVID-19 Map |
| JnlpInformationVendor: | Corona Virus Information Center |
| JnlpInformationHomepageHref: | https://coronavirusmaps.pro |
| JnlpInformationDescription: | This is interative COVID-19 World Map based on data from World Health Organization and National epidemic control centers. |
| JnlpSecurityAll-permissions: | - |
| JnlpResourcesJ2seVersion: | 1.6+ |
| JnlpResourcesJarHref: | map.jar |
| JnlpApplication-descMain-class: | Map |
| JnlpApplication-desc: |
Total processes
83
Monitored processes
34
Malicious processes
14
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 860 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 940 | C:\Windows\system32\MsiExec.exe -Embedding 05D786C7CFCE86ADC0812733719F27A3 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 956 | "C:\Program Files\Java\jre1.8.0_251\bin\unpack200.exe" -r "C:\Program Files\Java\jre1.8.0_251\lib/ext/localedata.pack" "C:\Program Files\Java\jre1.8.0_251\lib/ext/localedata.jar" | C:\Program Files\Java\jre1.8.0_251\bin\unpack200.exe | installer.exe | ||||||||||||
User: SYSTEM Company: Oracle Corporation Integrity Level: SYSTEM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2510.8 Modules
| |||||||||||||||
| 1444 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\JavaSetup8u251.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\JavaSetup8u251.exe | iexplore.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java Platform SE binary Exit code: 0 Version: 8.0.2510.8 Modules
| |||||||||||||||
| 1544 | "C:\Program Files\Java\jre1.8.0_251\bin\javaws.exe" -wait -fix -permissions -silent | C:\Program Files\Java\jre1.8.0_251\bin\javaws.exe | installer.exe | ||||||||||||
User: SYSTEM Company: Oracle Corporation Integrity Level: SYSTEM Description: Java(TM) Web Start Launcher Exit code: 0 Version: 11.251.2.08 Modules
| |||||||||||||||
| 1708 | "C:\Users\admin\AppData\LocalLow\Oracle\Java\jre1.8.0_251\LZMA_EXE" d "C:\Users\admin\AppData\LocalLow\Oracle\Java\jre1.8.0_251\jre1.8.0_251patch.msi" "C:\Users\admin\AppData\LocalLow\Oracle\Java\jre1.8.0_251\msi.tmp" | C:\Users\admin\AppData\LocalLow\Oracle\Java\jre1.8.0_251\LZMA_EXE | — | JavaSetup8u251.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1720 | "C:\Program Files\Java\jre1.8.0_251\installer.exe" /s INSTALLDIR="C:\Program Files\Java\jre1.8.0_251\\" INSTALL_SILENT=1 REPAIRMODE=0 ProductCode={26A24AE4-039D-4CA4-87B4-2F32180251F0} | C:\Program Files\Java\jre1.8.0_251\installer.exe | msiexec.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java Platform SE binary Exit code: 0 Version: 8.0.2510.8 Modules
| |||||||||||||||
| 1792 | C:\Windows\system32\MsiExec.exe -Embedding 4749223FB7A42E5EDB71BB9903DEAB54 M Global\MSI0000 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1876 | "C:\Program Files\Java\jre1.8.0_251\bin\unpack200.exe" -r "C:\Program Files\Java\jre1.8.0_251\lib/plugin.pack" "C:\Program Files\Java\jre1.8.0_251\lib/plugin.jar" | C:\Program Files\Java\jre1.8.0_251\bin\unpack200.exe | installer.exe | ||||||||||||
User: SYSTEM Company: Oracle Corporation Integrity Level: SYSTEM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2510.8 Modules
| |||||||||||||||
| 1912 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
46 907
Read events
1 797
Write events
31 225
Delete events
13 885
Modification events
| (PID) Process: | (3612) javaw.exe | Key: | HKEY_CURRENT_USER\Software\AppDataLow\Software\JavaSoft\DeploymentProperties |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3612) javaw.exe | Key: | HKEY_CURRENT_USER\Software\AppDataLow\Software\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.modified.timestamp |
Value: 1535457890299 | |||
| (PID) Process: | (3612) javaw.exe | Key: | HKEY_CURRENT_USER\Software\AppDataLow\Software\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.roaming.profile |
Value: false | |||
| (PID) Process: | (3612) javaw.exe | Key: | HKEY_CURRENT_USER\Software\AppDataLow\Software\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.version |
Value: 8 | |||
| (PID) Process: | (3612) javaw.exe | Key: | HKEY_CURRENT_USER\Software\AppDataLow\Software\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.expired.version |
Value: 11.92.2 | |||
| (PID) Process: | (3612) javaw.exe | Key: | HKEY_CURRENT_USER\Software\AppDataLow\Software\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.browser.path |
Value: C:\Program Files\Internet Explorer\iexplore.exe | |||
| (PID) Process: | (3612) javaw.exe | Key: | HKEY_CURRENT_USER\Software\AppDataLow\Software\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.expiration.decision.11.92.2 |
Value: update | |||
| (PID) Process: | (2316) javaw.exe | Key: | HKEY_CURRENT_USER\Software\AppDataLow\Software\JavaSoft\DeploymentProperties |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2316) javaw.exe | Key: | HKEY_CURRENT_USER\Software\AppDataLow\Software\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.modified.timestamp |
Value: 1587549543901 | |||
| (PID) Process: | (2316) javaw.exe | Key: | HKEY_CURRENT_USER\Software\AppDataLow\Software\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.roaming.profile |
Value: false | |||
Executable files
168
Suspicious files
62
Text files
488
Unknown types
41
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3912 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab104F.tmp | — | |
MD5:— | SHA256:— | |||
| 3912 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar1050.tmp | — | |
MD5:— | SHA256:— | |||
| 2228 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3612 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 2316 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 3180 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 3912 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\jv0_search_btn[1].gif | image | |
MD5:— | SHA256:— | |||
| 3912 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EDC238BFF48A31D55A97E1E93892934B_C31B2498754E340573F1336DE607D619 | der | |
MD5:— | SHA256:— | |||
| 3612 | javaw.exe | C:\Users\admin\AppData\Local\Temp\JavaDeployReg.log | text | |
MD5:— | SHA256:— | |||
| 3912 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\TPSPELFD.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
71
DNS requests
32
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
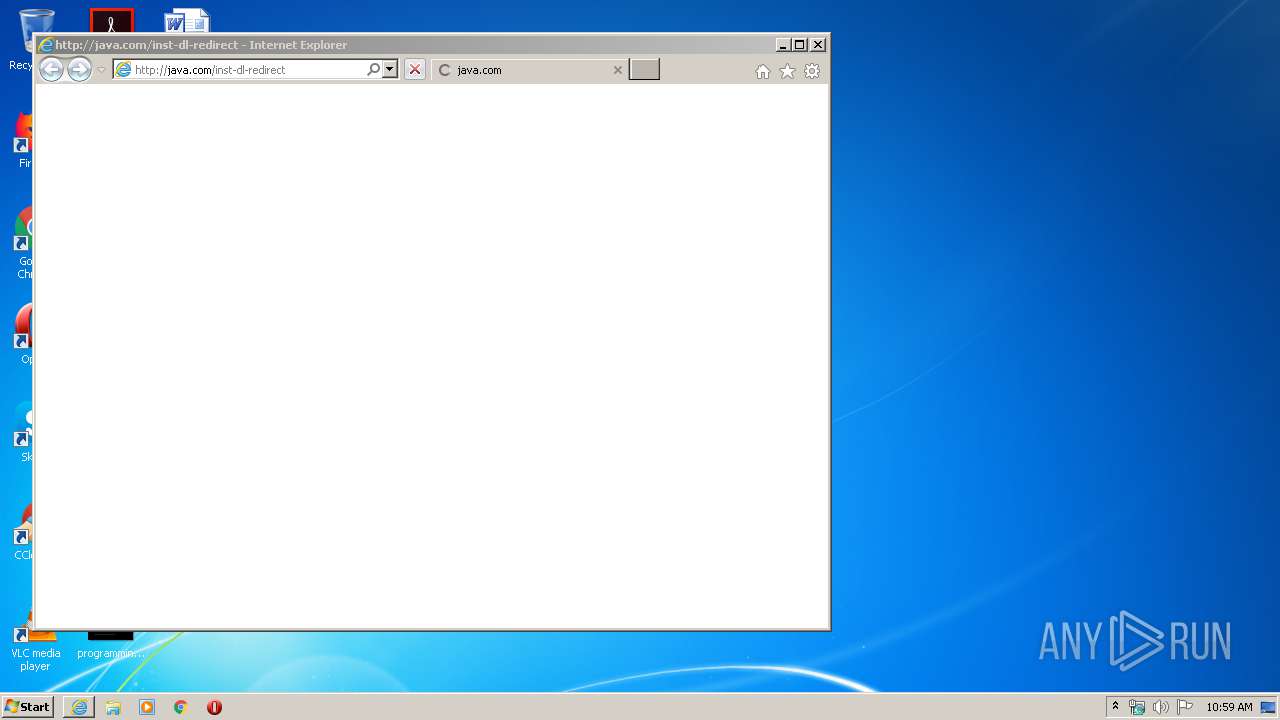
3912 | iexplore.exe | GET | 301 | 23.67.139.162:80 | http://java.com/inst-dl-redirect | NL | — | — | whitelisted |
3912 | iexplore.exe | GET | 301 | 23.67.139.162:80 | http://java.com/inst-dl-redirect/ | NL | — | — | whitelisted |
3912 | iexplore.exe | GET | 200 | 192.124.249.22:80 | http://ocsp.godaddy.com//MEkwRzBFMEMwQTAJBgUrDgMCGgUABBS2CA1fbGt26xPkOKX4ZguoUjM0TgQUQMK9J47MNIMwojPX%2B2yz8LQsgM4CCEJfUEAx8qrg | US | der | 1.73 Kb | whitelisted |
3912 | iexplore.exe | GET | 200 | 192.124.249.22:80 | http://ocsp.godaddy.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBTkIInKBAzXkF0Qh0pel3lfHJ9GPAQU0sSw0pHUTBFxs2HLPaH%2B3ahq1OMCAxvnFQ%3D%3D | US | der | 1.66 Kb | whitelisted |
3912 | iexplore.exe | GET | 200 | 72.21.91.29:80 | http://crl3.digicert.com/DigiCertGlobalRootCA.crl | US | der | 581 b | whitelisted |
3912 | iexplore.exe | GET | 200 | 192.124.249.23:80 | http://ocsp.godaddy.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBTkIInKBAzXkF0Qh0pel3lfHJ9GPAQU0sSw0pHUTBFxs2HLPaH%2B3ahq1OMCAxvnFQ%3D%3D | US | der | 1.66 Kb | whitelisted |
3912 | iexplore.exe | GET | 200 | 192.124.249.22:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | US | der | 1.69 Kb | whitelisted |
3912 | iexplore.exe | GET | 200 | 192.124.249.22:80 | http://ocsp.godaddy.com//MEkwRzBFMEMwQTAJBgUrDgMCGgUABBS2CA1fbGt26xPkOKX4ZguoUjM0TgQUQMK9J47MNIMwojPX%2B2yz8LQsgM4CCEJfUEAx8qrg | US | der | 1.73 Kb | whitelisted |
2228 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3912 | iexplore.exe | GET | 200 | 192.124.249.41:80 | http://crl.godaddy.com/gdroot.crl | US | der | 429 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2228 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3912 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3912 | iexplore.exe | 23.67.139.162:80 | java.com | Akamai International B.V. | NL | suspicious |
3912 | iexplore.exe | 23.67.139.162:443 | java.com | Akamai International B.V. | NL | suspicious |
3912 | iexplore.exe | 143.204.202.19:443 | consent.trustarc.com | — | US | malicious |
3912 | iexplore.exe | 104.96.148.17:443 | c.oracleinfinity.io | Akamai Technologies, Inc. | NL | unknown |
3912 | iexplore.exe | 23.67.141.135:443 | static.oracle.com | Akamai International B.V. | NL | suspicious |
3912 | iexplore.exe | 192.124.249.22:80 | ocsp.godaddy.com | Sucuri | US | suspicious |
3912 | iexplore.exe | 143.204.202.76:443 | consent-pref.trustarc.com | — | US | malicious |
3912 | iexplore.exe | 104.111.214.229:443 | s.go-mpulse.net | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
java.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
static.oracle.com |
| whitelisted |
consent.trustarc.com |
| shared |
c.oracleinfinity.io |
| whitelisted |
ocsp.godaddy.com |
| whitelisted |
s.go-mpulse.net |
| whitelisted |
consent-st.trustarc.com |
| whitelisted |