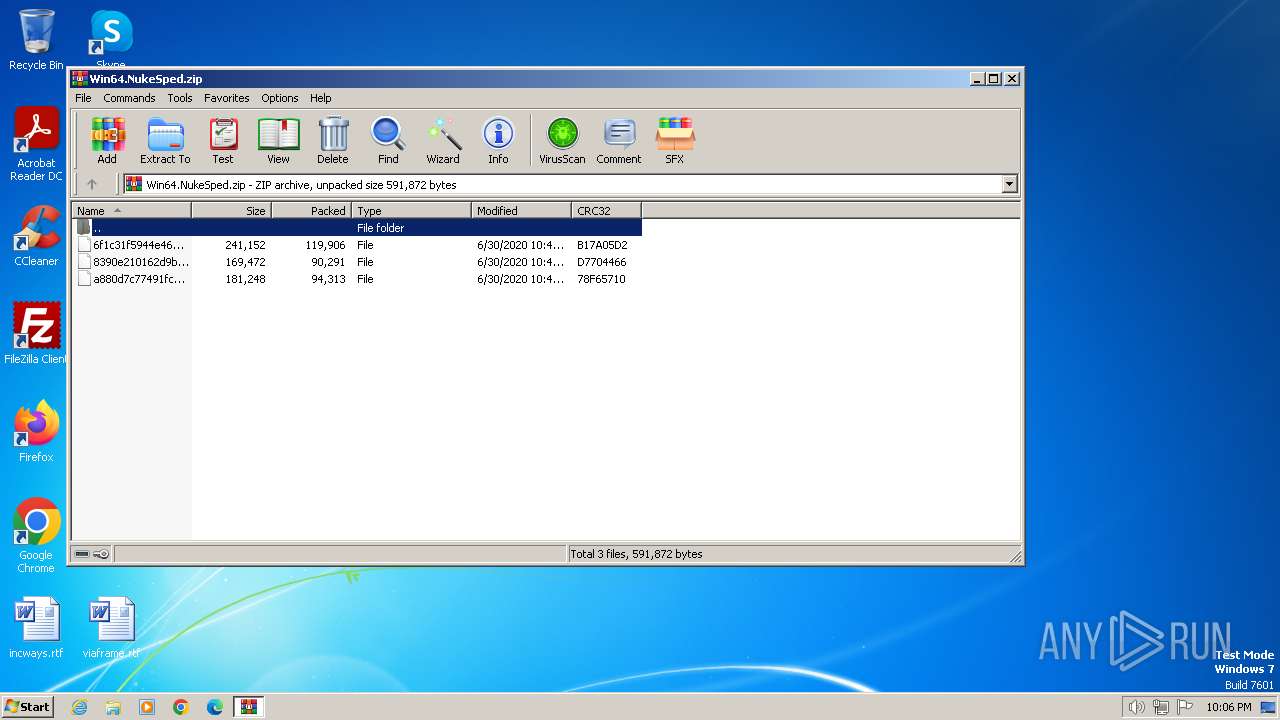
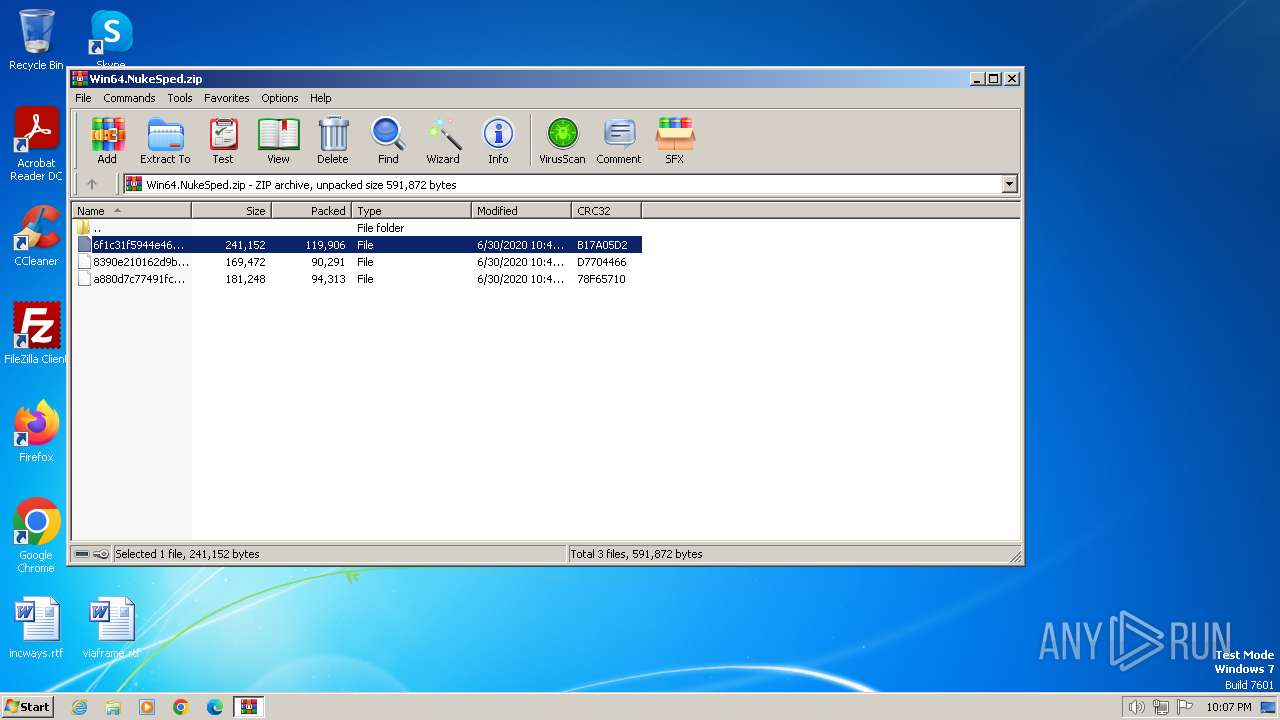
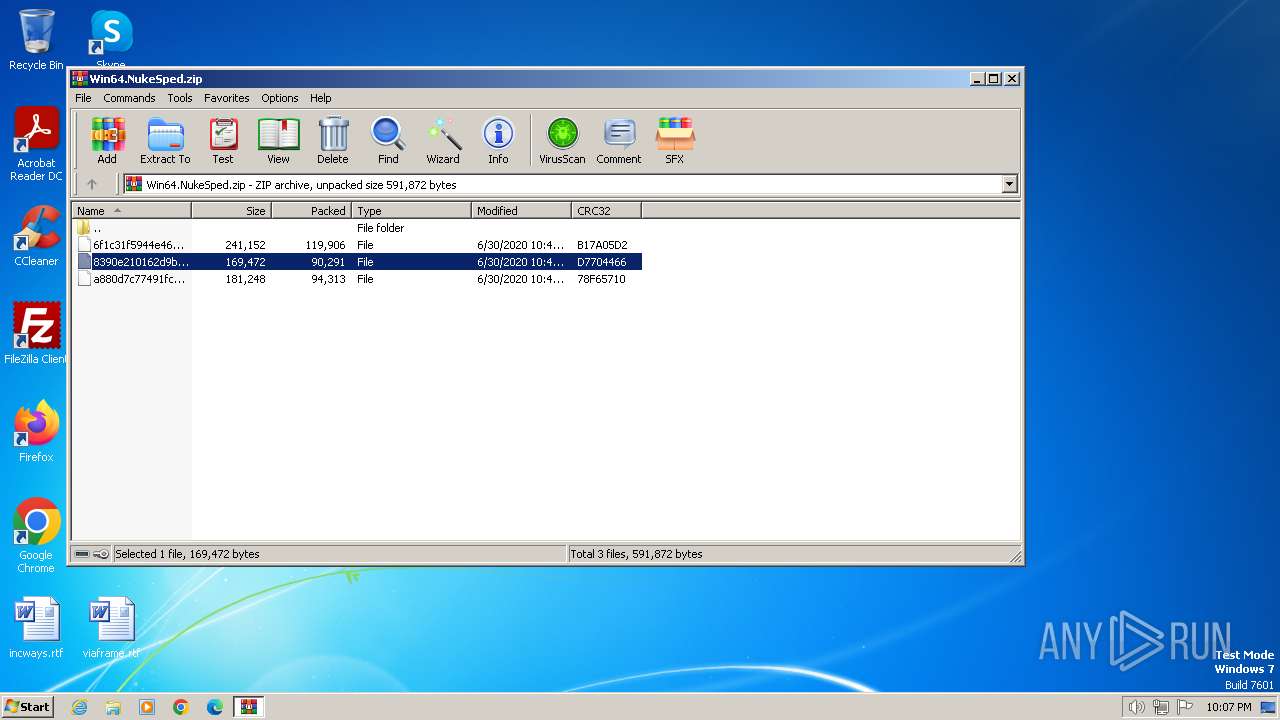
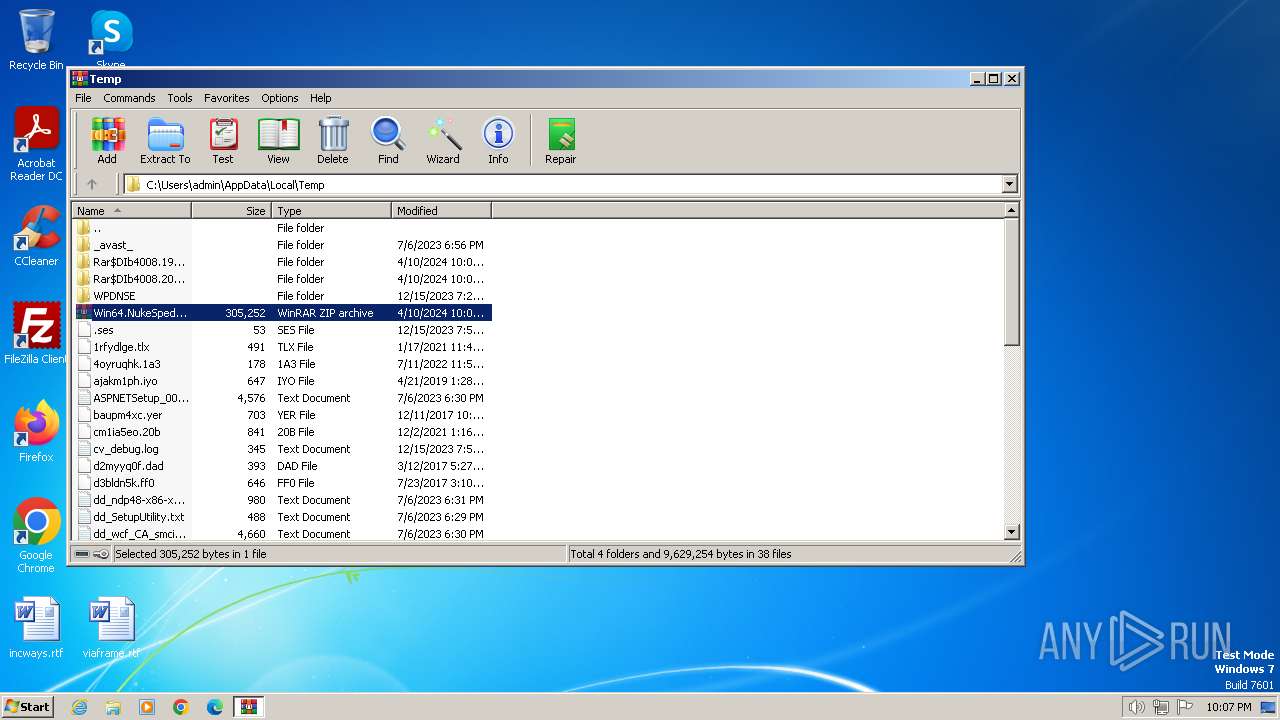
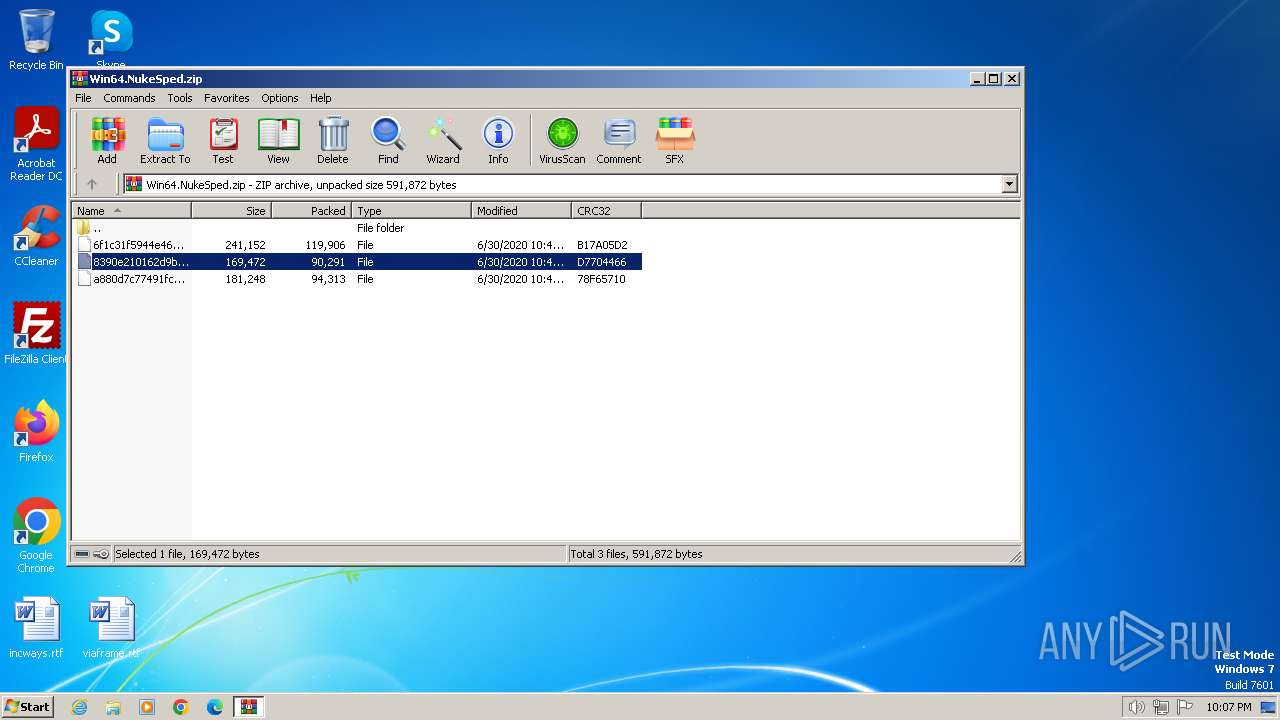
| File name: | Win64.NukeSped.zip |
| Full analysis: | https://app.any.run/tasks/5a7ef3cc-deac-44c5-9ea0-604aeb97880b |
| Verdict: | Malicious activity |
| Analysis date: | April 10, 2024, 21:06:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | C92AC2A5A2C6D2B1826A0BBC1A56B01A |
| SHA1: | 613D82ECD6E829C8A24ED7261097A746479F44BE |
| SHA256: | 931F062A629950AD6FB85B83262CC3F730A6E94D43A27B48F7FD857F7722C6BA |
| SSDEEP: | 12288:W23EAgKOY/E5GmUN71PG9pux9Txlo9Wl4uPozfd/+0mjrLMQpQpgc6e:W23EAgKOYM5GdvPG9pux9Txlo9Wl4uPQ |
MALICIOUS
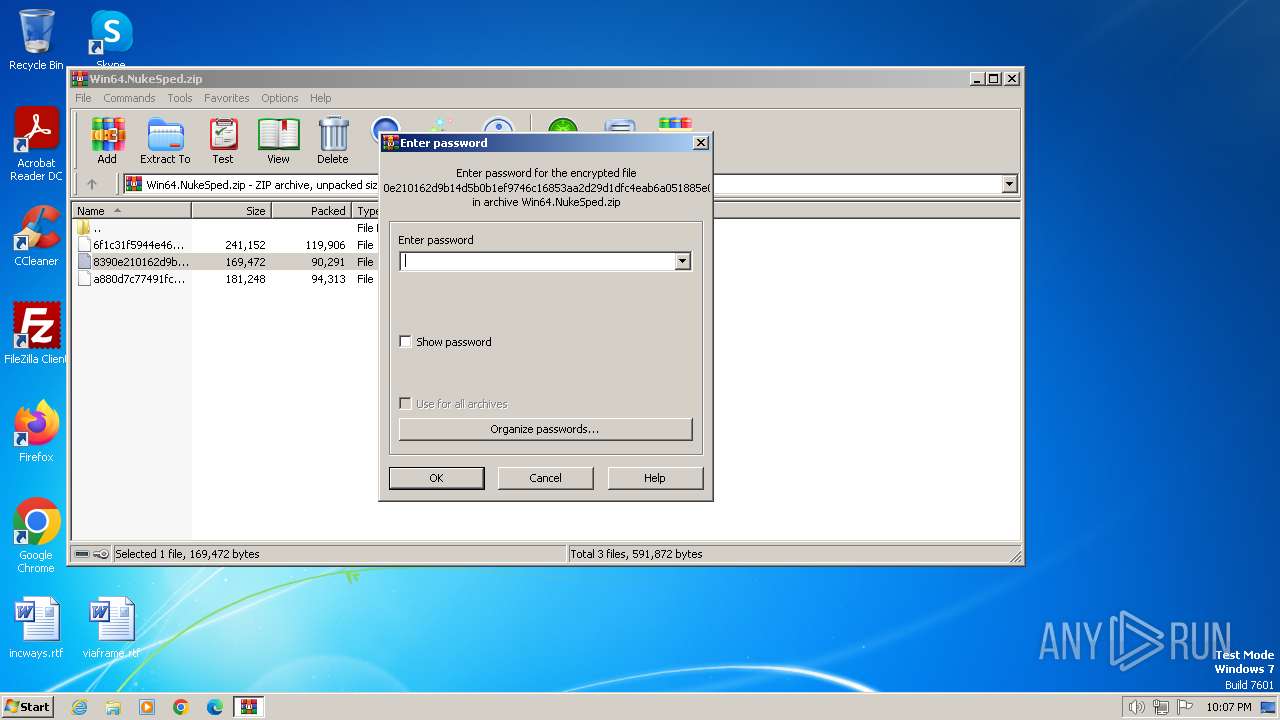
Drops the executable file immediately after the start
- WinRAR.exe (PID: 4008)
SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 4008)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 4008)
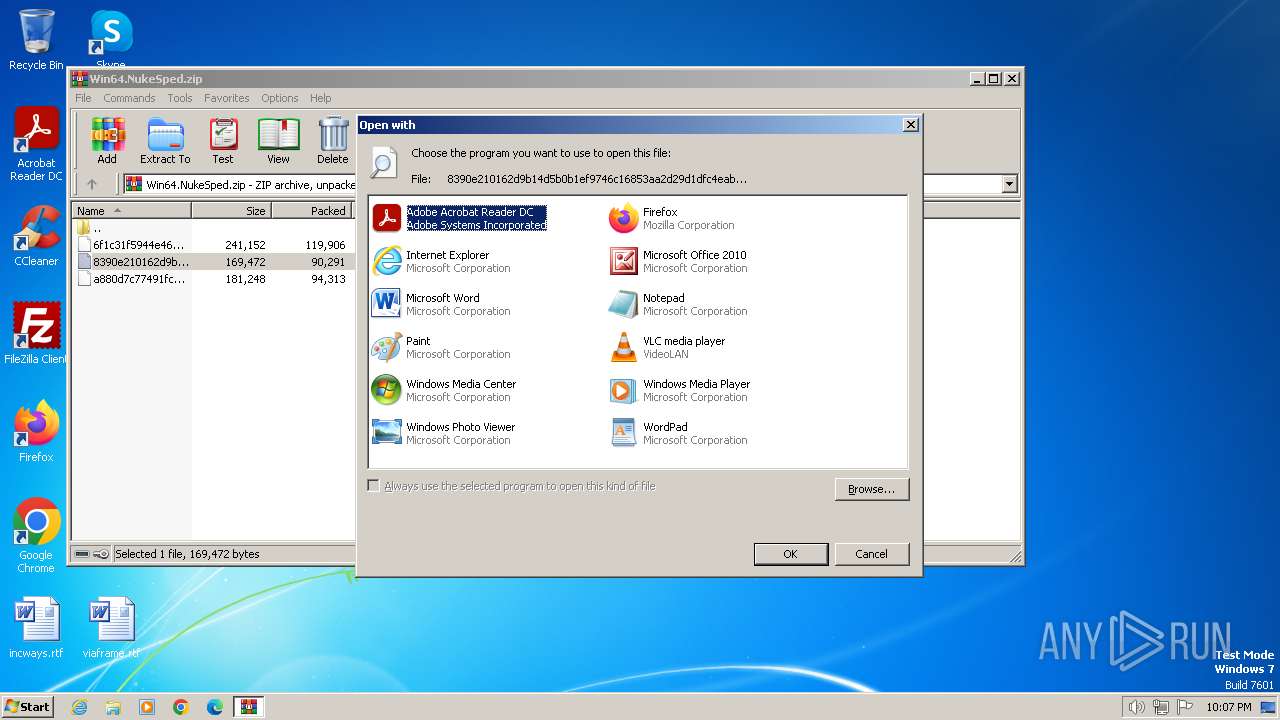
Uses RUNDLL32.EXE to load library
- WinRAR.exe (PID: 4008)
Reads the Internet Settings
- rundll32.exe (PID: 3180)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4008)
Reads security settings of Internet Explorer
- rundll32.exe (PID: 3180)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
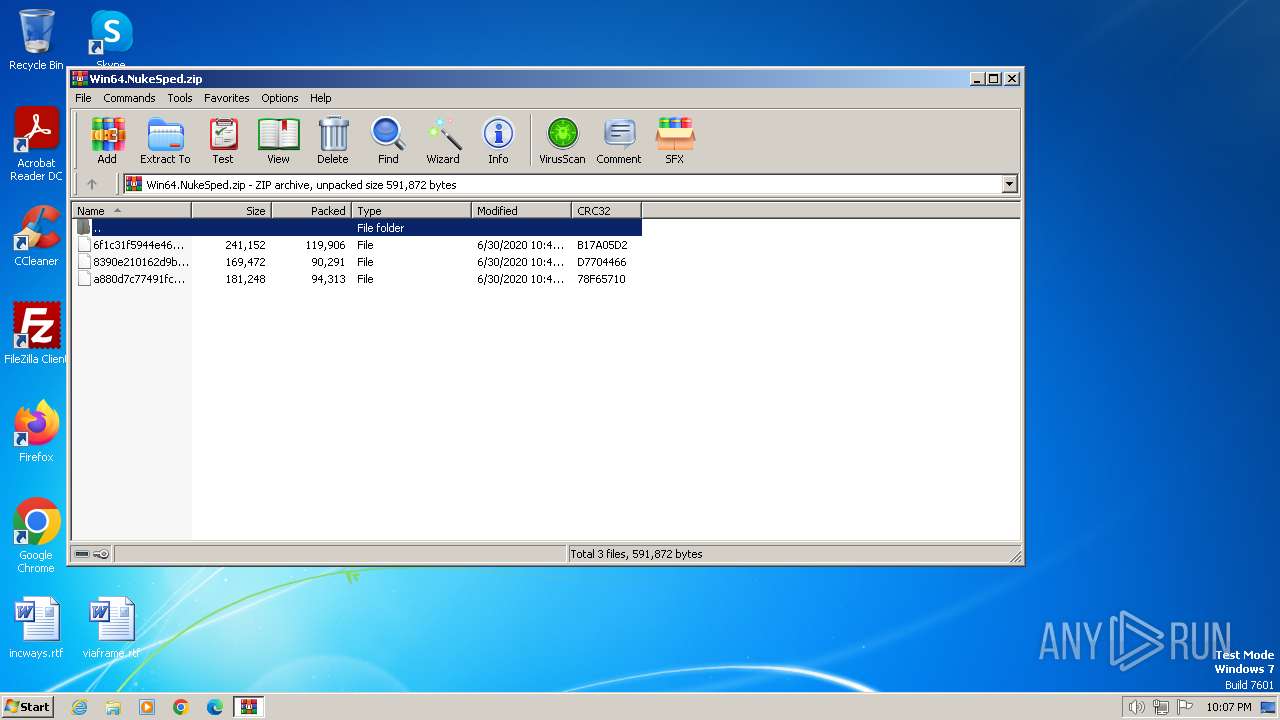
| ZipRequiredVersion: | 788 |
|---|---|
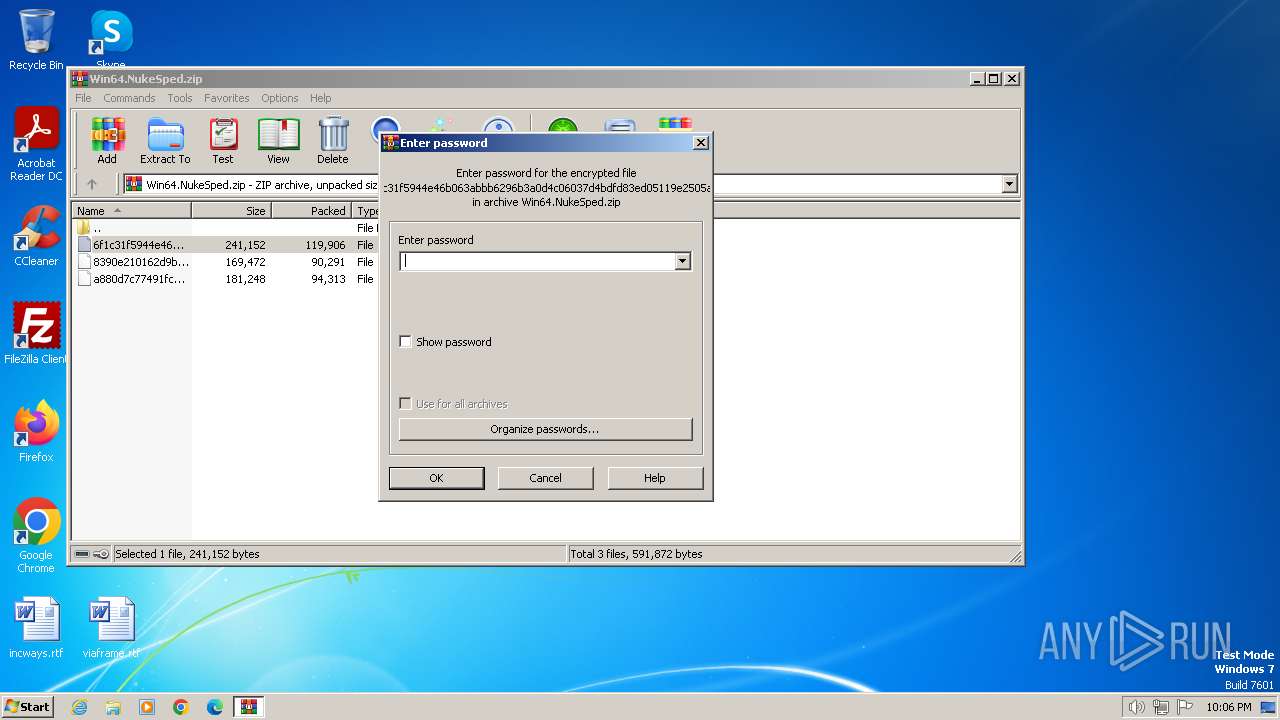
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:06:30 12:48:32 |
| ZipCRC: | 0xb17a05d2 |
| ZipCompressedSize: | 119906 |
| ZipUncompressedSize: | 241152 |
| ZipFileName: | 6f1c31f5944e46b063abbb6296b3a0d4c06037d4bdfd83ed05119e2505adabc5 |
Total processes
40
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
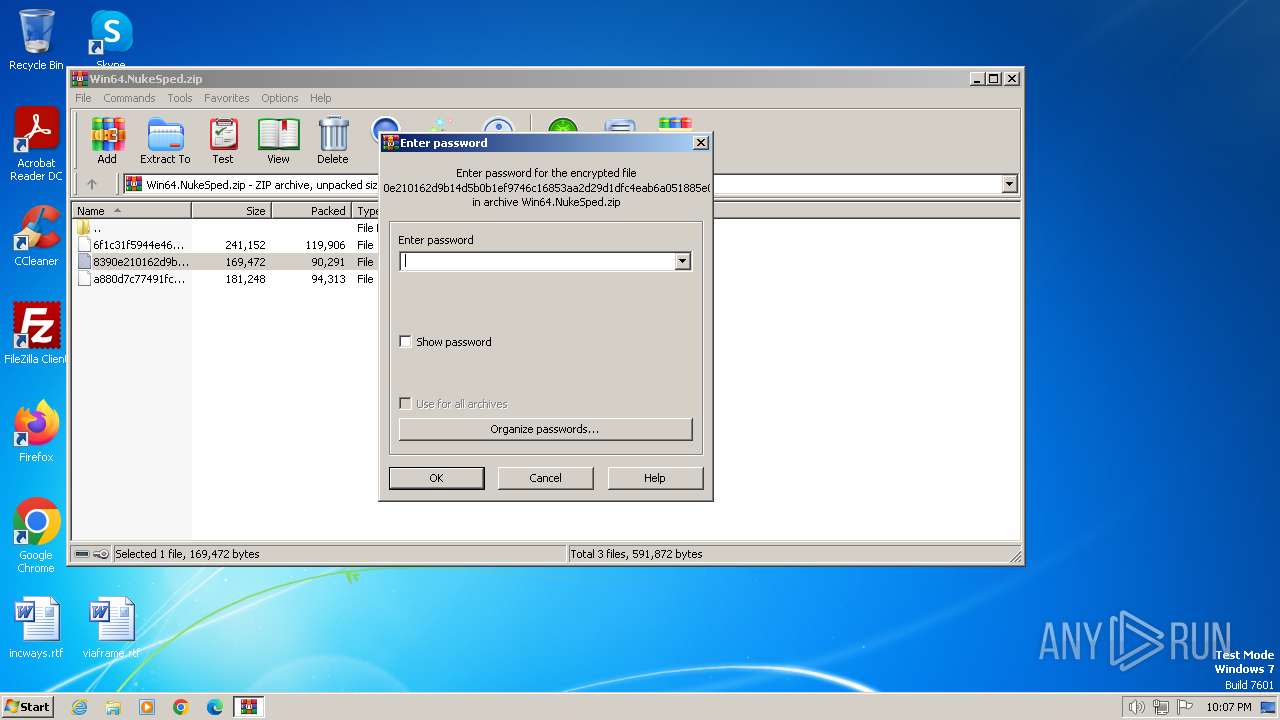
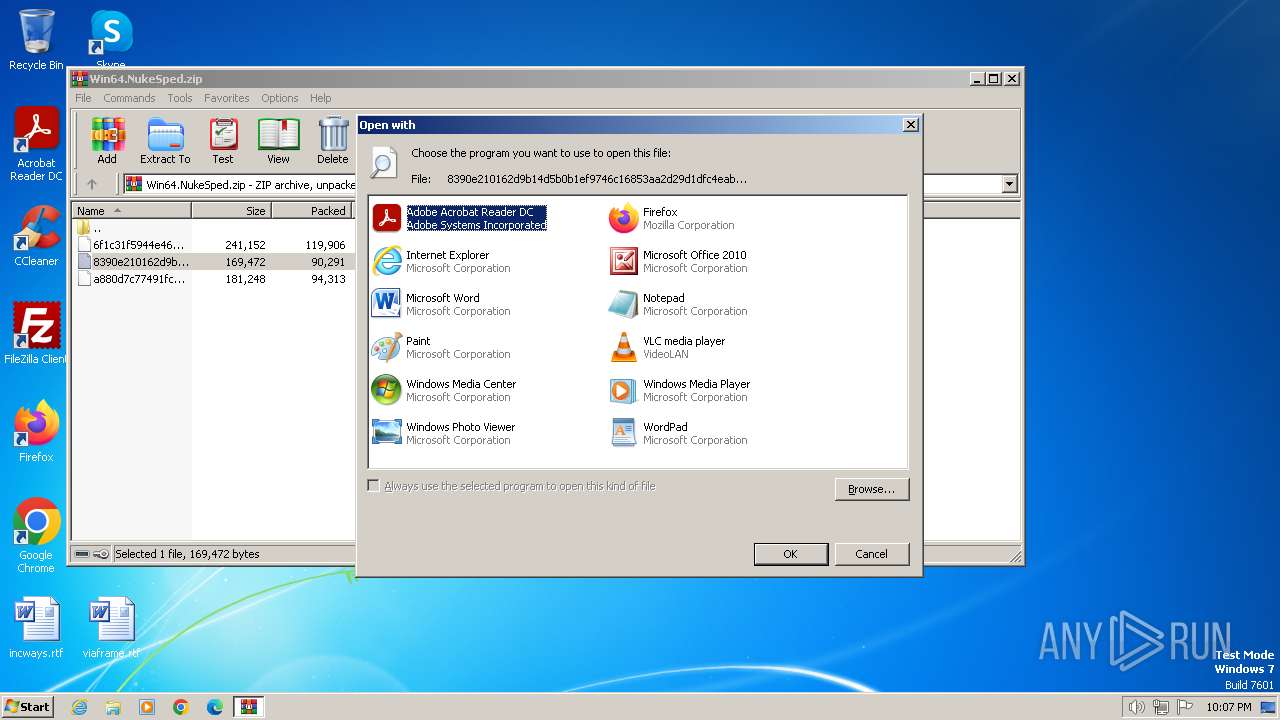
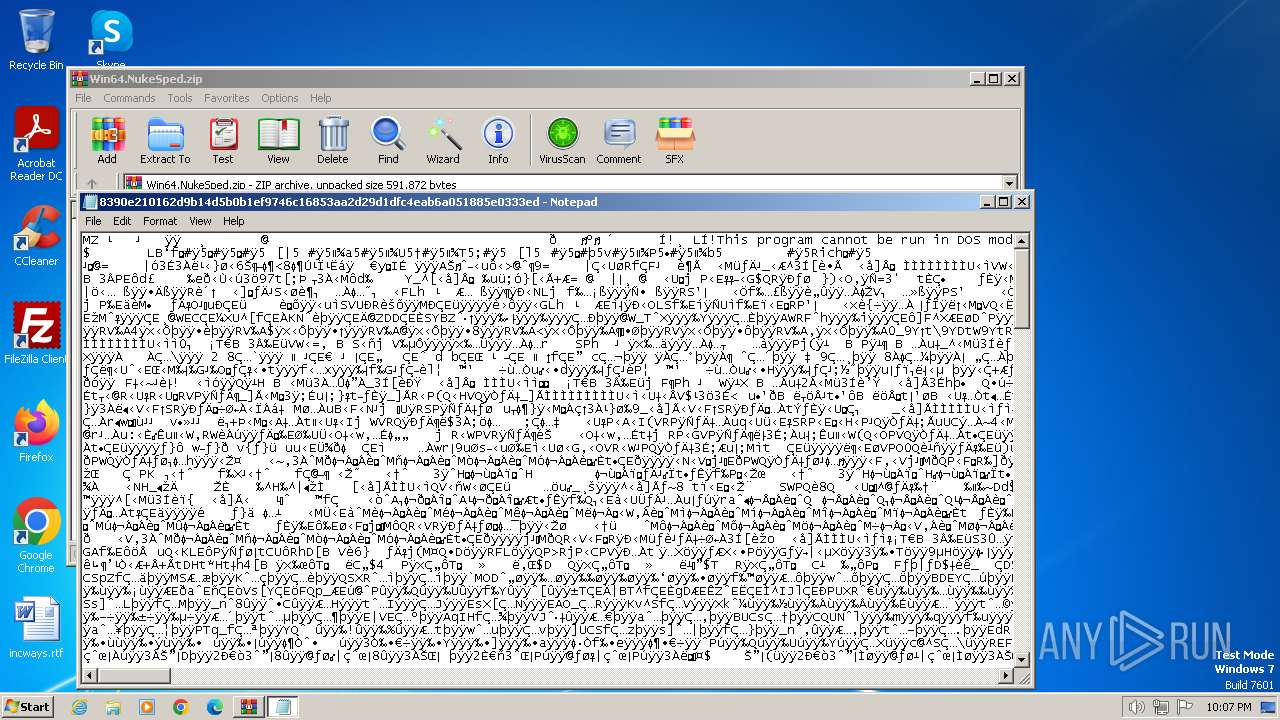
| 696 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\Rar$DIb4008.22234\8390e210162d9b14d5b0b1ef9746c16853aa2d29d1dfc4eab6a051885e0333ed | C:\Windows\System32\notepad.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
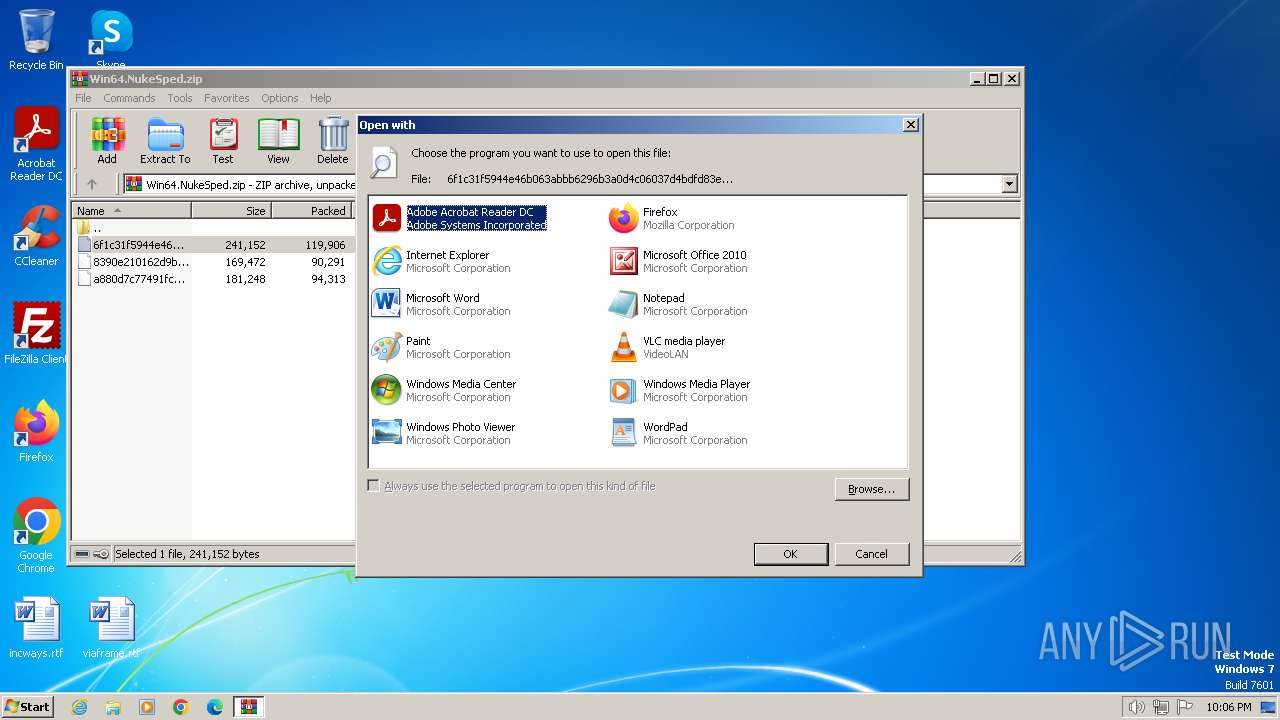
| 2856 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\Rar$DIb4008.19467\6f1c31f5944e46b063abbb6296b3a0d4c06037d4bdfd83ed05119e2505adabc5 | C:\Windows\System32\rundll32.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3180 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\Rar$DIb4008.22234\8390e210162d9b14d5b0b1ef9746c16853aa2d29d1dfc4eab6a051885e0333ed | C:\Windows\System32\rundll32.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4008 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Win64.NukeSped.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 4044 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\Rar$DIb4008.20422\8390e210162d9b14d5b0b1ef9746c16853aa2d29d1dfc4eab6a051885e0333ed | C:\Windows\System32\rundll32.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
9 066
Read events
8 944
Write events
122
Delete events
0
Modification events
| (PID) Process: | (4008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (4008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (4008) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (4008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (4008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (4008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (4008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Win64.NukeSped.zip | |||
| (PID) Process: | (4008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4008) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
3
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4008 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb4008.19467\6f1c31f5944e46b063abbb6296b3a0d4c06037d4bdfd83ed05119e2505adabc5 | executable | |
MD5:— | SHA256:— | |||
| 4008 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb4008.20422\8390e210162d9b14d5b0b1ef9746c16853aa2d29d1dfc4eab6a051885e0333ed | executable | |
MD5:— | SHA256:— | |||
| 4008 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb4008.22234\8390e210162d9b14d5b0b1ef9746c16853aa2d29d1dfc4eab6a051885e0333ed | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |