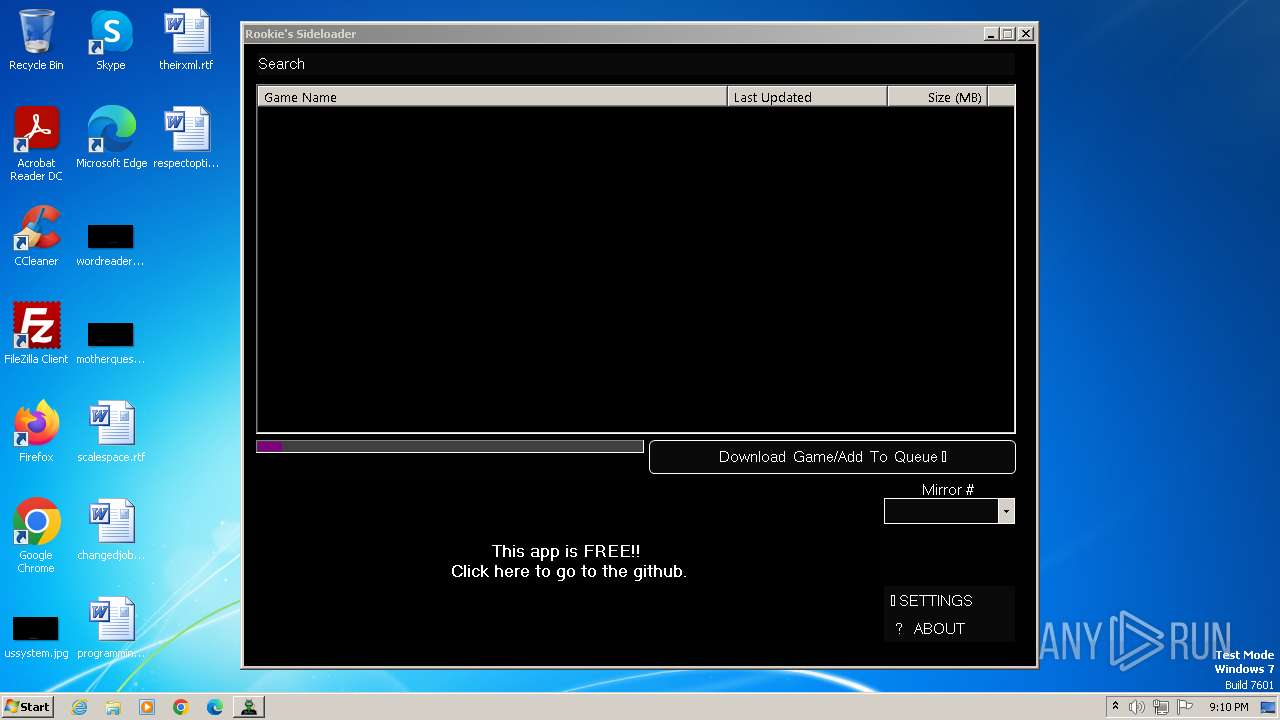
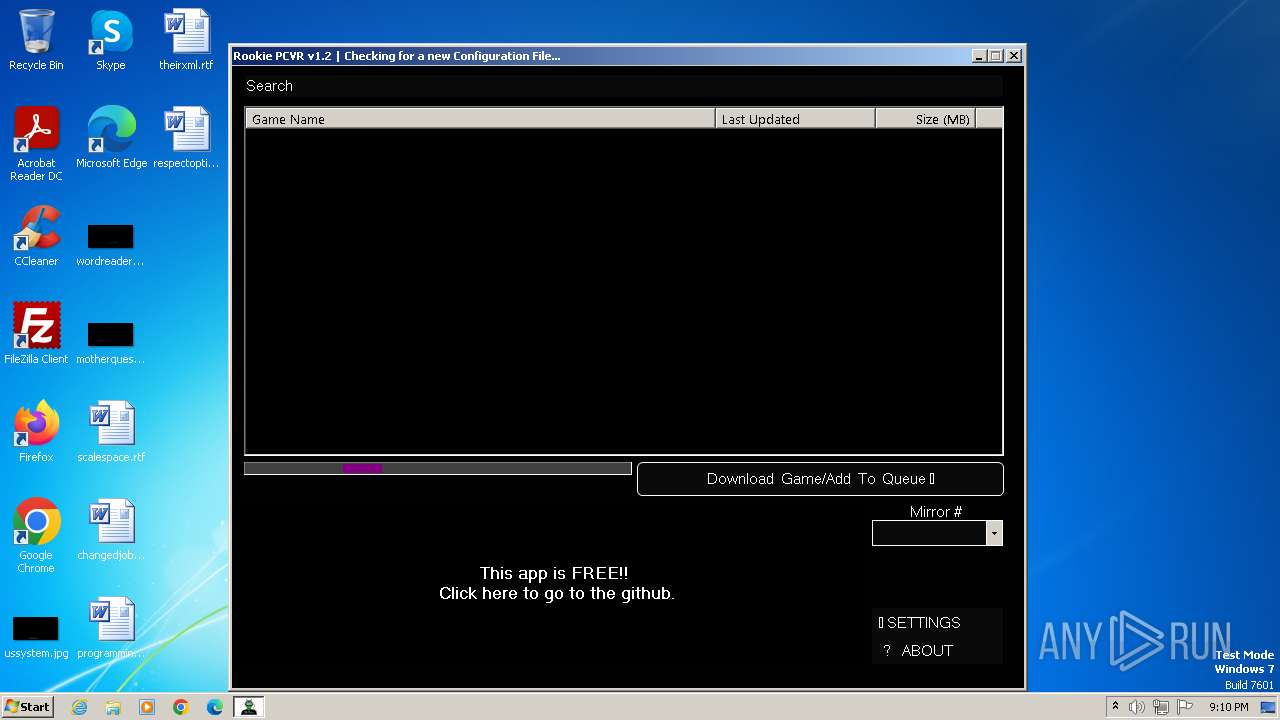
| File name: | Rookie-PCVR.exe |
| Full analysis: | https://app.any.run/tasks/6f111a30-625c-41ec-9a79-00c1c64573c5 |
| Verdict: | Malicious activity |
| Analysis date: | October 29, 2023, 21:09:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 6F7671B6F4C5583653891C8CCD85411B |
| SHA1: | 4A906FB871909A3AAB7D1DBD40ABECF8CE874B5D |
| SHA256: | 931CCA55BD22449CD1128FE9537157627DFBD63A3DBA9AB86C510CC9C52814D9 |
| SSDEEP: | 6144:uYZyaYekq+NuM3uBJgUpL8SNFDu/O63hGSb/DB5pr0+UTsWkef1XwxQ1GA/azzZh:PGuHp5bu9TlLfUTdwq1hrkE4yTO/ |
MALICIOUS
Drops the executable file immediately after the start
- Rookie-PCVR.exe (PID: 3828)
Application was dropped or rewritten from another process
- 7z.exe (PID: 3344)
SUSPICIOUS
Reads the Internet Settings
- Rookie-PCVR.exe (PID: 3828)
Reads settings of System Certificates
- Rookie-PCVR.exe (PID: 3828)
Drops 7-zip archiver for unpacking
- Rookie-PCVR.exe (PID: 3828)
INFO
Checks supported languages
- Rookie-PCVR.exe (PID: 3828)
- 7z.exe (PID: 3344)
- rclone.exe (PID: 2608)
- rclone.exe (PID: 2420)
- rclone.exe (PID: 1608)
Reads the machine GUID from the registry
- Rookie-PCVR.exe (PID: 3828)
Reads the computer name
- Rookie-PCVR.exe (PID: 3828)
- 7z.exe (PID: 3344)
- rclone.exe (PID: 2608)
- rclone.exe (PID: 2420)
- rclone.exe (PID: 1608)
Reads Environment values
- Rookie-PCVR.exe (PID: 3828)
Create files in a temporary directory
- Rookie-PCVR.exe (PID: 3828)
- 7z.exe (PID: 3344)
Creates files or folders in the user directory
- Rookie-PCVR.exe (PID: 3828)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2073:12:15 00:15:43+01:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 529920 |
| InitializedDataSize: | 413184 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x8359e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.0.0 |
| ProductVersionNumber: | 2.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | Rookie Sideloader |
| CompanyName: | Rookie.WTF |
| FileDescription: | AndroidSideloader |
| FileVersion: | 2.0.0.0 |
| InternalName: | Rookie-PCVR.exe |
| LegalCopyright: | Copyright © 2020 |
| LegalTrademarks: | - |
| OriginalFileName: | Rookie-PCVR.exe |
| ProductName: | AndroidSideloader |
| ProductVersion: | 2.0.0.0 |
| AssemblyVersion: | 2.0.0.0 |
Total processes
44
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1608 | "C:\Users\admin\AppData\Local\Temp\rclone\rclone.exe" cat ":PCVR Games/VRP-GameList.txt" --config vrp.download.config | C:\Users\admin\AppData\Local\Temp\rclone\rclone.exe | — | Rookie-PCVR.exe | |||||||||||
User: admin Company: https://rclone.org Integrity Level: MEDIUM Description: Rsync for cloud storage Exit code: 1 Version: 1.62.2 Modules
| |||||||||||||||
| 2420 | "C:\Users\admin\AppData\Local\Temp\rclone\rclone.exe" cat ":PCVR Games/VRP-GameList.txt" --config vrp.download.config | C:\Users\admin\AppData\Local\Temp\rclone\rclone.exe | — | Rookie-PCVR.exe | |||||||||||
User: admin Company: https://rclone.org Integrity Level: MEDIUM Description: Rsync for cloud storage Exit code: 1 Version: 1.62.2 Modules
| |||||||||||||||
| 2608 | "C:\Users\admin\AppData\Local\Temp\rclone\rclone.exe" listremotes --config vrp.download.config | C:\Users\admin\AppData\Local\Temp\rclone\rclone.exe | — | Rookie-PCVR.exe | |||||||||||
User: admin Company: https://rclone.org Integrity Level: MEDIUM Description: Rsync for cloud storage Exit code: 0 Version: 1.62.2 Modules
| |||||||||||||||
| 3344 | "7z.exe" x "C:\Users\admin\AppData\Local\Temp\rclone.zip" -y -o"C:\Users\admin\AppData\Local\Temp" | C:\Users\admin\AppData\Local\Temp\7z.exe | — | Rookie-PCVR.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Standalone Console Exit code: 0 Version: 23.01 Modules
| |||||||||||||||
| 3828 | "C:\Users\admin\AppData\Local\Temp\Rookie-PCVR.exe" | C:\Users\admin\AppData\Local\Temp\Rookie-PCVR.exe | explorer.exe | ||||||||||||
User: admin Company: Rookie.WTF Integrity Level: MEDIUM Description: AndroidSideloader Exit code: 0 Version: 2.0.0.0 Modules
| |||||||||||||||
Total events
5 661
Read events
5 641
Write events
20
Delete events
0
Modification events
| (PID) Process: | (3828) Rookie-PCVR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3828) Rookie-PCVR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3828) Rookie-PCVR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3828) Rookie-PCVR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3828) Rookie-PCVR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\178\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
2
Suspicious files
5
Text files
10
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3344 | 7z.exe | C:\Users\admin\AppData\Local\Temp\rclone-v1.62.2-windows-386\rclone.exe | — | |
MD5:— | SHA256:— | |||
| 3828 | Rookie-PCVR.exe | C:\Users\admin\AppData\Local\Temp\rclone\vrp.download.config | — | |
MD5:— | SHA256:— | |||
| 3828 | Rookie-PCVR.exe | C:\Users\admin\AppData\Local\Rookie.WTF\Rookie-PCVR.exe_Url_hsnaya4ojx5bnelk51fptp1m2y03dnhx\2.0.0.0\user.config | xml | |
MD5:410AFDA4BDE459246A3CA55E2EE36BC3 | SHA256:4C28889E076FC03D80185C5CC0C85F26B4078E84C279CC2943C0B3CCAD0F9B4E | |||
| 3828 | Rookie-PCVR.exe | C:\Users\admin\AppData\Local\Temp\CabB43A.tmp | compressed | |
MD5:F3441B8572AAE8801C04F3060B550443 | SHA256:6720349E7D82EE0A8E73920D3C2B7CB2912D9FCF2EDB6FD98F2F12820158B0BF | |||
| 3828 | Rookie-PCVR.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:864A50B65F1B3D0FAC505B86E678D2D6 | SHA256:A5D0BC8077FE8172EBA83E8855ED7BA384507B8EF5CF8F8055A7BABACB7E415F | |||
| 3828 | Rookie-PCVR.exe | C:\Users\admin\AppData\Local\Temp\TarB43B.tmp | binary | |
MD5:9441737383D21192400ECA82FDA910EC | SHA256:BC3A6E84E41FAEB57E7C21AA3B60C2A64777107009727C5B7C0ED8FE658909E5 | |||
| 3828 | Rookie-PCVR.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:F3441B8572AAE8801C04F3060B550443 | SHA256:6720349E7D82EE0A8E73920D3C2B7CB2912D9FCF2EDB6FD98F2F12820158B0BF | |||
| 3344 | 7z.exe | C:\Users\admin\AppData\Local\Temp\rclone-v1.62.2-windows-386\README.txt | text | |
MD5:9DF0B3D5F6D545A514318D0220FD643B | SHA256:544A5933C1FE2451B3FF4B8C0D4A9F6BE20F4C30CA04A3B3090AC28345A925D1 | |||
| 3828 | Rookie-PCVR.exe | C:\Users\admin\AppData\Local\Rookie.WTF\Rookie-PCVR.exe_Url_hsnaya4ojx5bnelk51fptp1m2y03dnhx\2.0.0.0\ycmgm3hv.newcfg | xml | |
MD5:80FB0F0A5948978437AC75F5C13B722E | SHA256:C58BFDDB714A283BAE69704D4BF76B7BA673739E08245862F7157AFE6F2A7BE7 | |||
| 3828 | Rookie-PCVR.exe | C:\Users\admin\AppData\Local\Temp\7z.dll | executable | |
MD5:AE7DE9A0278F37331D2E9F8D5C0281F0 | SHA256:A3FC74468477BA54517157EFA5021EAA6FF72F8F5C31E53D89F07D59071C0AE7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
10
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3828 | Rookie-PCVR.exe | GET | 200 | 8.248.95.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?2d3bf7d3efa6c8d3 | unknown | compressed | 61.6 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2656 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
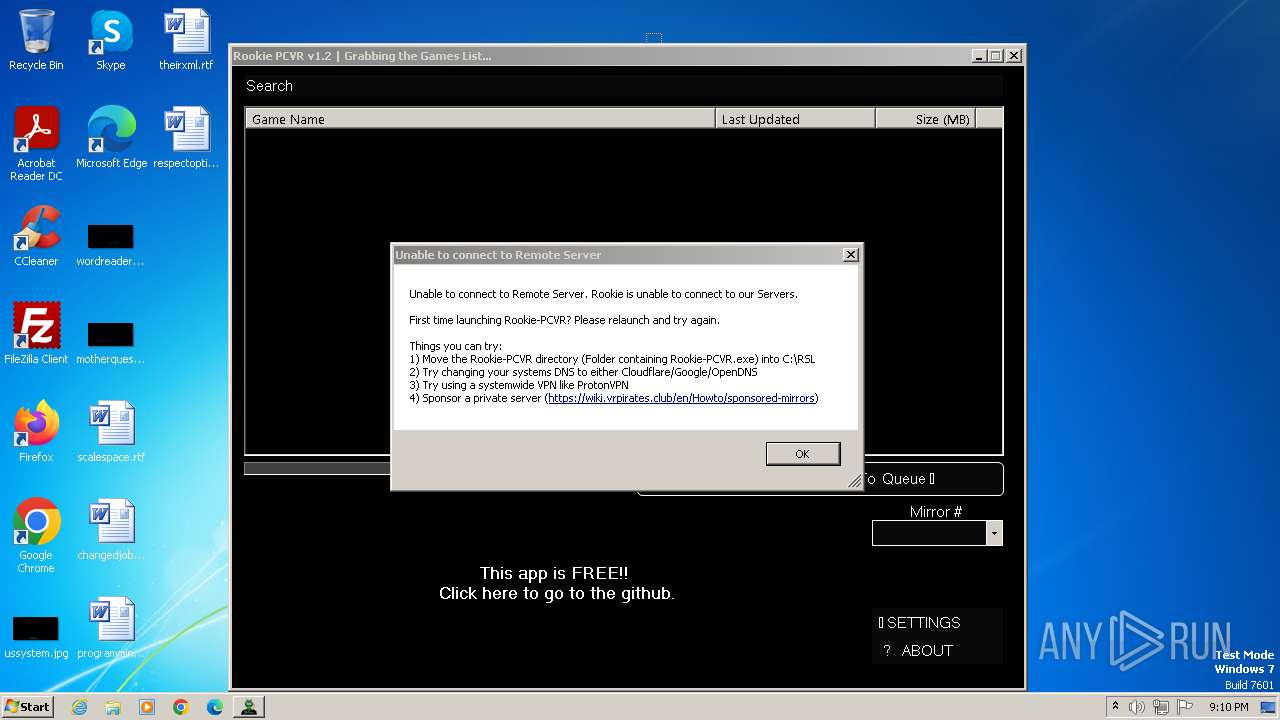
3828 | Rookie-PCVR.exe | 95.217.6.16:443 | downloads.rclone.org | Hetzner Online GmbH | FI | unknown |
3828 | Rookie-PCVR.exe | 8.248.95.254:80 | ctldl.windowsupdate.com | LEVEL3 | US | unknown |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3828 | Rookie-PCVR.exe | 140.82.121.4:443 | github.com | GITHUB | US | unknown |
3828 | Rookie-PCVR.exe | 185.199.110.133:443 | raw.githubusercontent.com | FASTLY | US | unknown |
3828 | Rookie-PCVR.exe | 185.165.171.105:443 | wiki.vrpirates.club | Flokinet Ltd | SC | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
downloads.rclone.org |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
github.com |
| shared |
raw.githubusercontent.com |
| shared |
wiki.vrpirates.club |
| malicious |