| File name: | 9302c0c054024f8d7f6f8e69aff9a16109d97a4d288732a894fdf00334929245 |
| Full analysis: | https://app.any.run/tasks/d68f4b83-ed4b-4d6b-839a-dc7dadfe0dac |
| Verdict: | Malicious activity |
| Analysis date: | August 15, 2019, 13:41:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 76B660A8095A4072D5A9BA23485CE7B3 |
| SHA1: | F2A38734AED92F06CE1B42FA255EB8DA67624290 |
| SHA256: | 9302C0C054024F8D7F6F8E69AFF9A16109D97A4D288732A894FDF00334929245 |
| SSDEEP: | 49152:/Sh98u+nxX45I4IABvIa4ZE5jv+mFiMUTGYOCGJWwT:6L7+nt4y4FvIjuhv+mYFrhGJWa |
MALICIOUS
Application was dropped or rewritten from another process
- 9302c0c054024f8d7f6f8e69aff9a16109d97a4d288732a894fdf0033492924532.exe (PID: 2712)
Loads the Task Scheduler COM API
- 9302c0c054024f8d7f6f8e69aff9a16109d97a4d288732a894fdf0033492924532.exe (PID: 2712)
Actions looks like stealing of personal data
- 9302c0c054024f8d7f6f8e69aff9a16109d97a4d288732a894fdf0033492924532.exe (PID: 2712)
SUSPICIOUS
Executable content was dropped or overwritten
- 9302c0c054024f8d7f6f8e69aff9a16109d97a4d288732a894fdf00334929245.exe (PID: 3708)
Reads CPU info
- 9302c0c054024f8d7f6f8e69aff9a16109d97a4d288732a894fdf00334929245.exe (PID: 3708)
- 9302c0c054024f8d7f6f8e69aff9a16109d97a4d288732a894fdf0033492924532.exe (PID: 2712)
Reads the date of Windows installation
- 9302c0c054024f8d7f6f8e69aff9a16109d97a4d288732a894fdf0033492924532.exe (PID: 2712)
Reads the machine GUID from the registry
- 9302c0c054024f8d7f6f8e69aff9a16109d97a4d288732a894fdf0033492924532.exe (PID: 2712)
Reads Windows Product ID
- 9302c0c054024f8d7f6f8e69aff9a16109d97a4d288732a894fdf0033492924532.exe (PID: 2712)
Reads Windows owner or organization settings
- 9302c0c054024f8d7f6f8e69aff9a16109d97a4d288732a894fdf0033492924532.exe (PID: 2712)
Reads Environment values
- 9302c0c054024f8d7f6f8e69aff9a16109d97a4d288732a894fdf0033492924532.exe (PID: 2712)
Reads the Windows organization settings
- 9302c0c054024f8d7f6f8e69aff9a16109d97a4d288732a894fdf0033492924532.exe (PID: 2712)
Creates files in the user directory
- notepad++.exe (PID: 3908)
Loads DLL from Mozilla Firefox
- 9302c0c054024f8d7f6f8e69aff9a16109d97a4d288732a894fdf0033492924532.exe (PID: 2712)
INFO
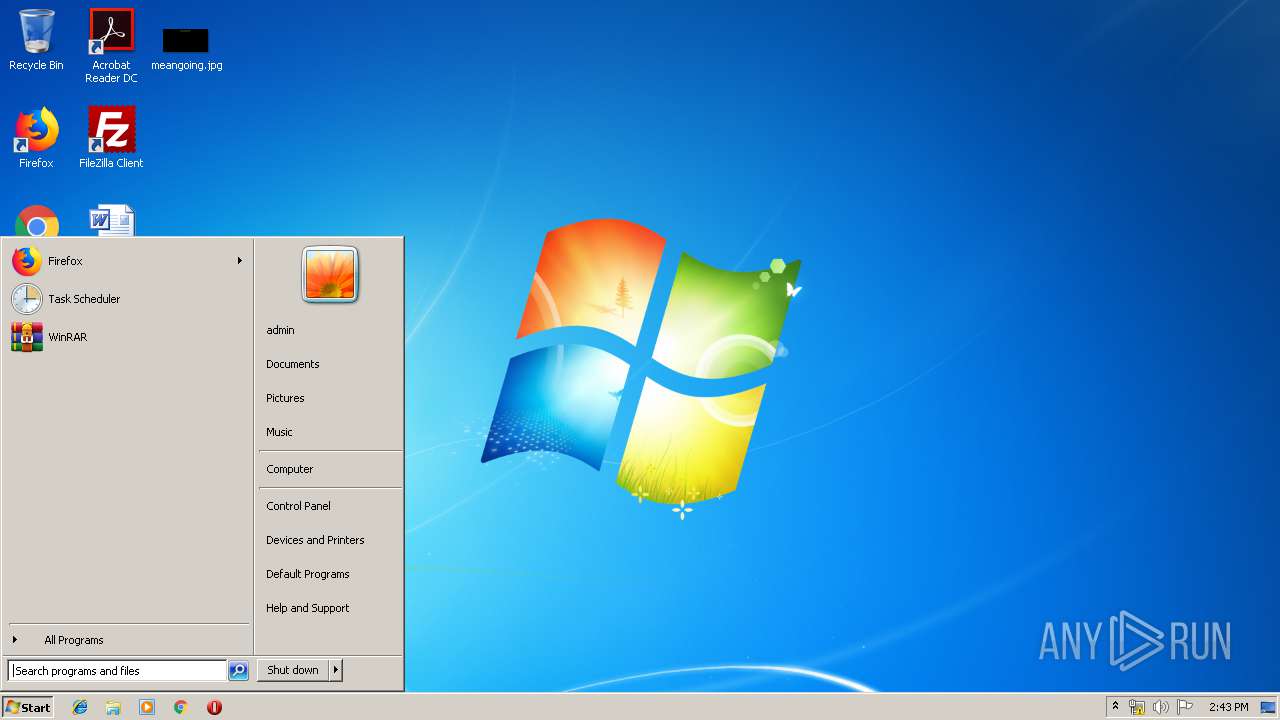
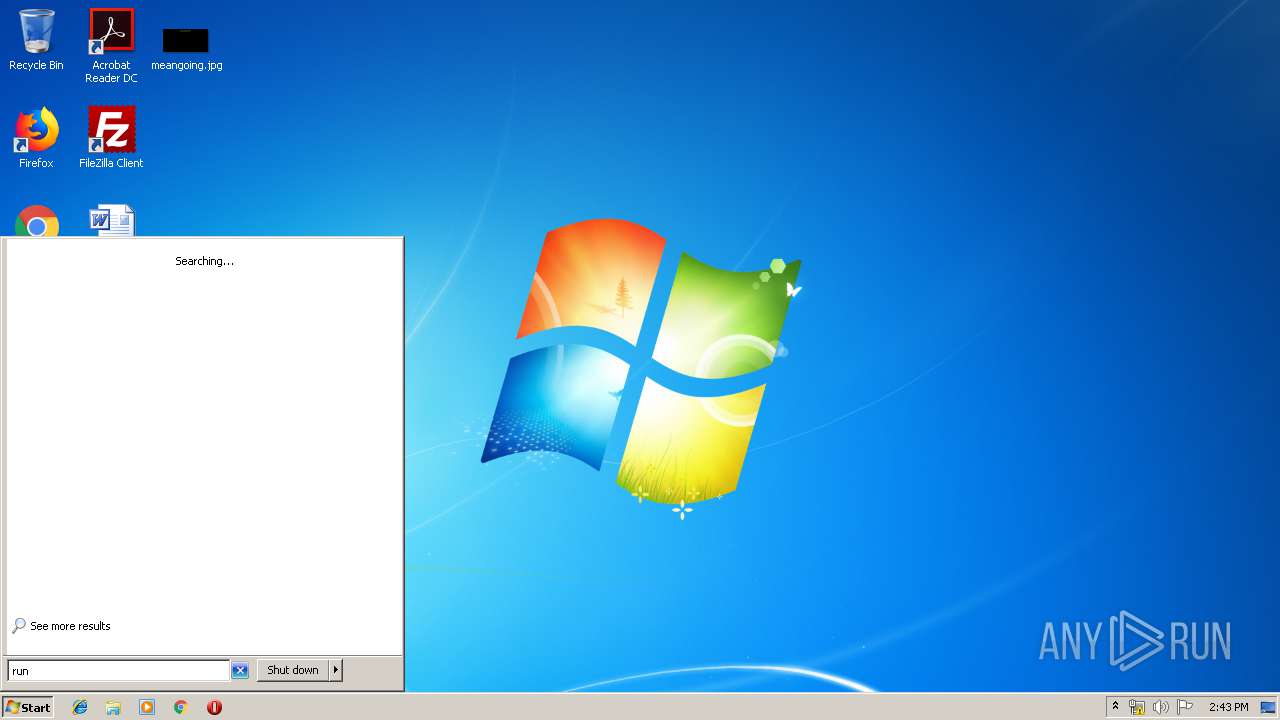
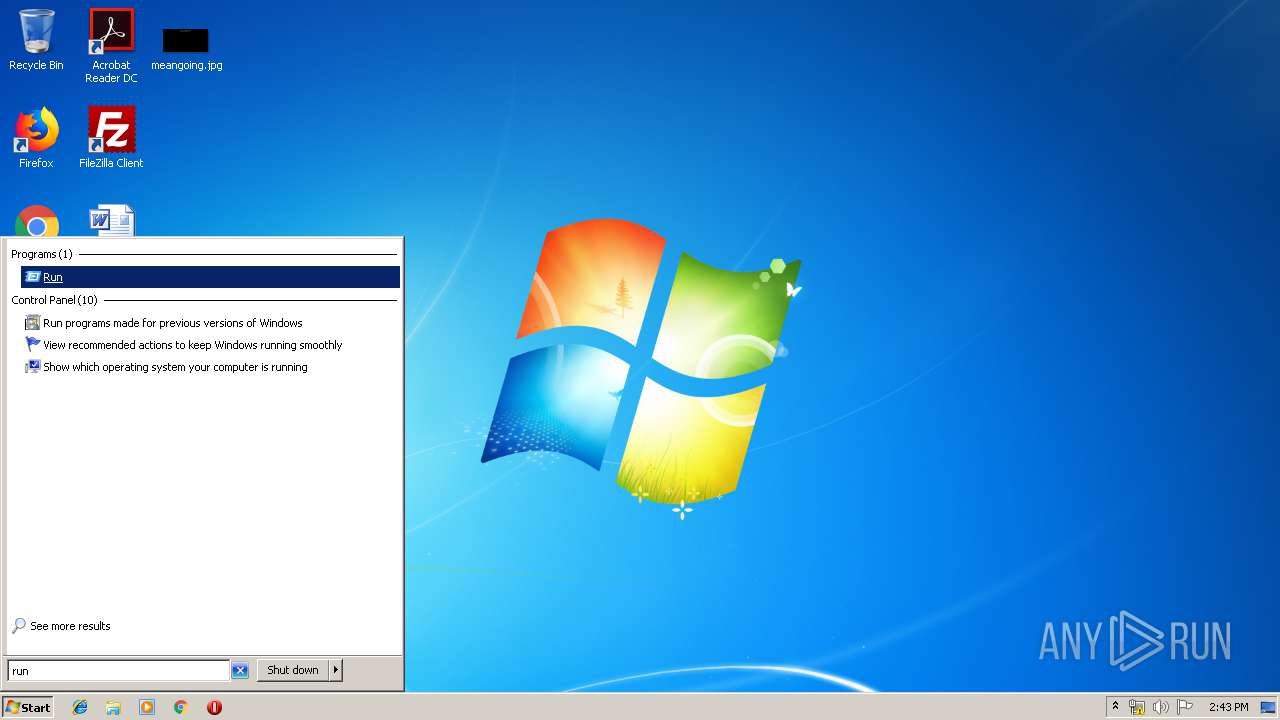
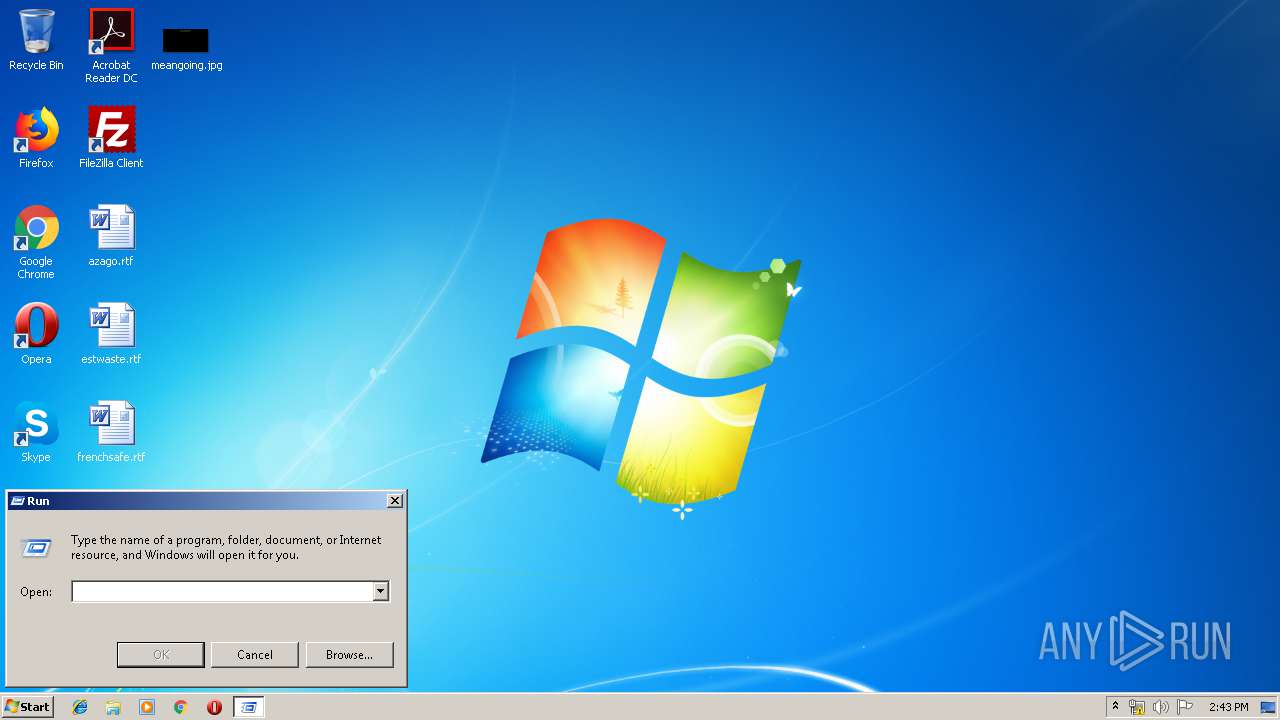
Manual execution by user
- notepad++.exe (PID: 3908)
- notepad++.exe (PID: 3940)
Reads settings of System Certificates
- 9302c0c054024f8d7f6f8e69aff9a16109d97a4d288732a894fdf0033492924532.exe (PID: 2712)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:02:19 17:44:52+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.15 |
| CodeSize: | 104448 |
| InitializedDataSize: | 2513408 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5399 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.0.224.0 |
| ProductVersionNumber: | 1.0.224.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | CrowdStrike, Inc. |
| FileDescription: | CrowdStrike Forensics Data Collection Tool |
| FileVersion: | 1.0.224.0 |
| InternalName: | FalconForensicsCollector.exe |
| LegalCopyright: | Copyright (C) CrowdStrike, Inc. 2019. All rights reserved. |
| OriginalFileName: | FalconForensicsCollector.exe |
| ProductName: | CrowdStrike Falcon Forensics - Collector |
| ProductVersion: | 1.0.224.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 19-Feb-2019 16:44:52 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | CrowdStrike, Inc. |
| FileDescription: | CrowdStrike Forensics Data Collection Tool |
| FileVersion: | 1.0.224.0 |
| InternalName: | FalconForensicsCollector.exe |
| LegalCopyright: | Copyright (C) CrowdStrike, Inc. 2019. All rights reserved. |
| OriginalFilename: | FalconForensicsCollector.exe |
| ProductName: | CrowdStrike Falcon Forensics - Collector |
| ProductVersion: | 1.0.224.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 19-Feb-2019 16:44:52 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001963E | 0x00019800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.67586 |
.rdata | 0x0001B000 | 0x00007AFE | 0x00007C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.17447 |
.data | 0x00023000 | 0x00005AF4 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.91852 |
.rsrc | 0x00029000 | 0x00256BD5 | 0x00256C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.98816 |
.reloc | 0x00280000 | 0x00001430 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.33537 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 2.95674 | 744 | UNKNOWN | English - United States | RT_ICON |
3 | 2.76907 | 296 | UNKNOWN | English - United States | RT_ICON |
4 | 4.87125 | 3752 | UNKNOWN | English - United States | RT_ICON |
5 | 4.97814 | 2216 | UNKNOWN | English - United States | RT_ICON |
6 | 4.80697 | 1384 | UNKNOWN | English - United States | RT_ICON |
7 | 3.88109 | 9640 | UNKNOWN | English - United States | RT_ICON |
8 | 3.95406 | 4264 | UNKNOWN | English - United States | RT_ICON |
9 | 4.29707 | 1128 | UNKNOWN | English - United States | RT_ICON |
101 | 7.99969 | 1029108 | UNKNOWN | English - United States | BIN |
Imports
ADVAPI32.dll |
Cabinet.dll |
KERNEL32.dll |
RPCRT4.dll |
USER32.dll |
Total processes
41
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
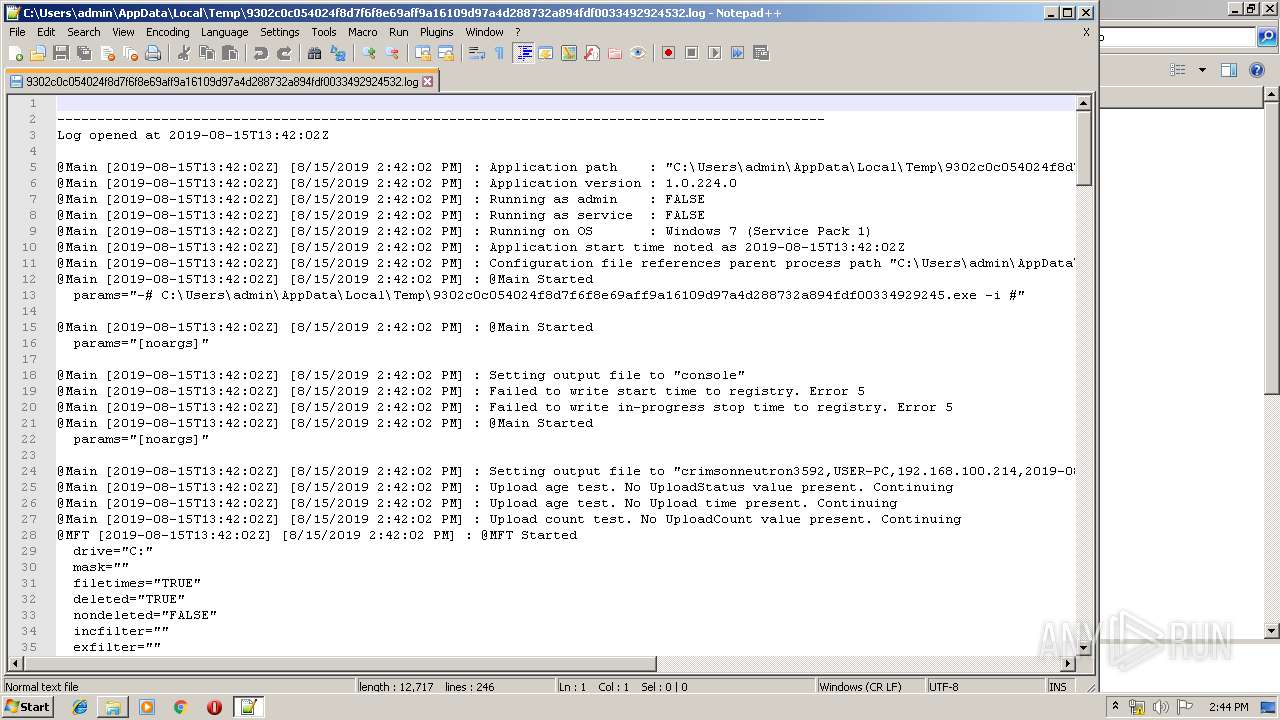
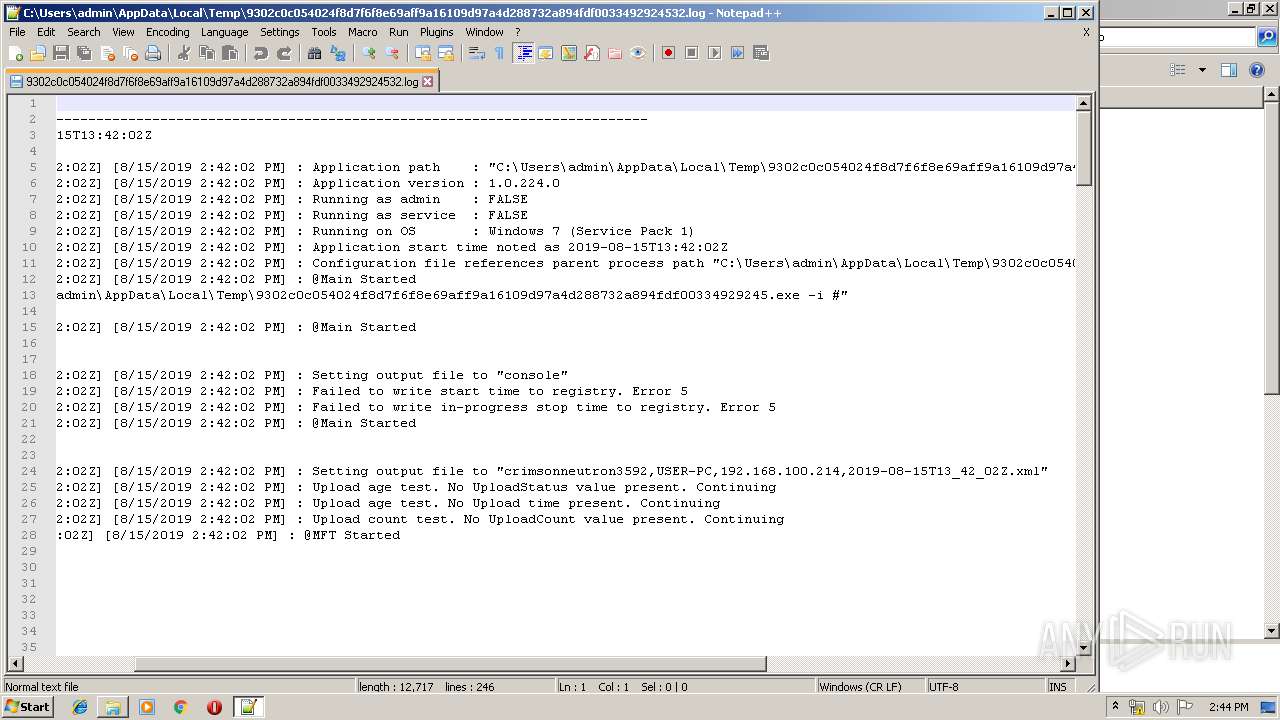
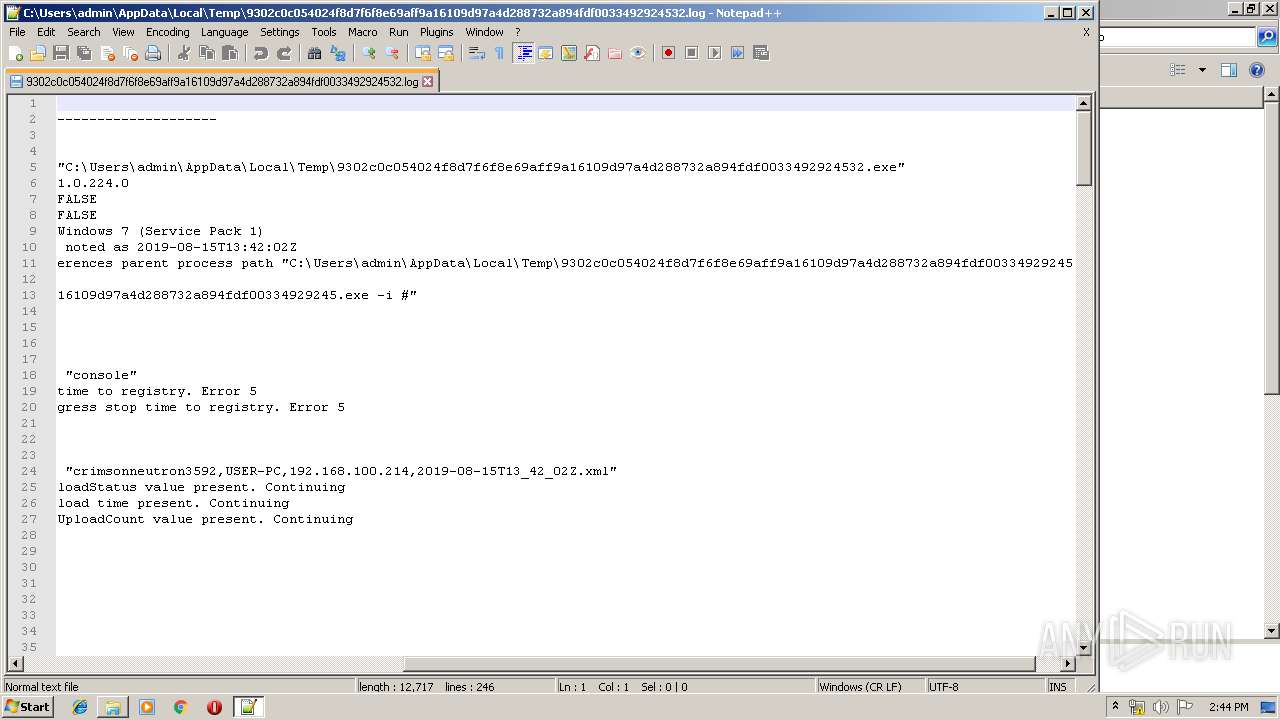
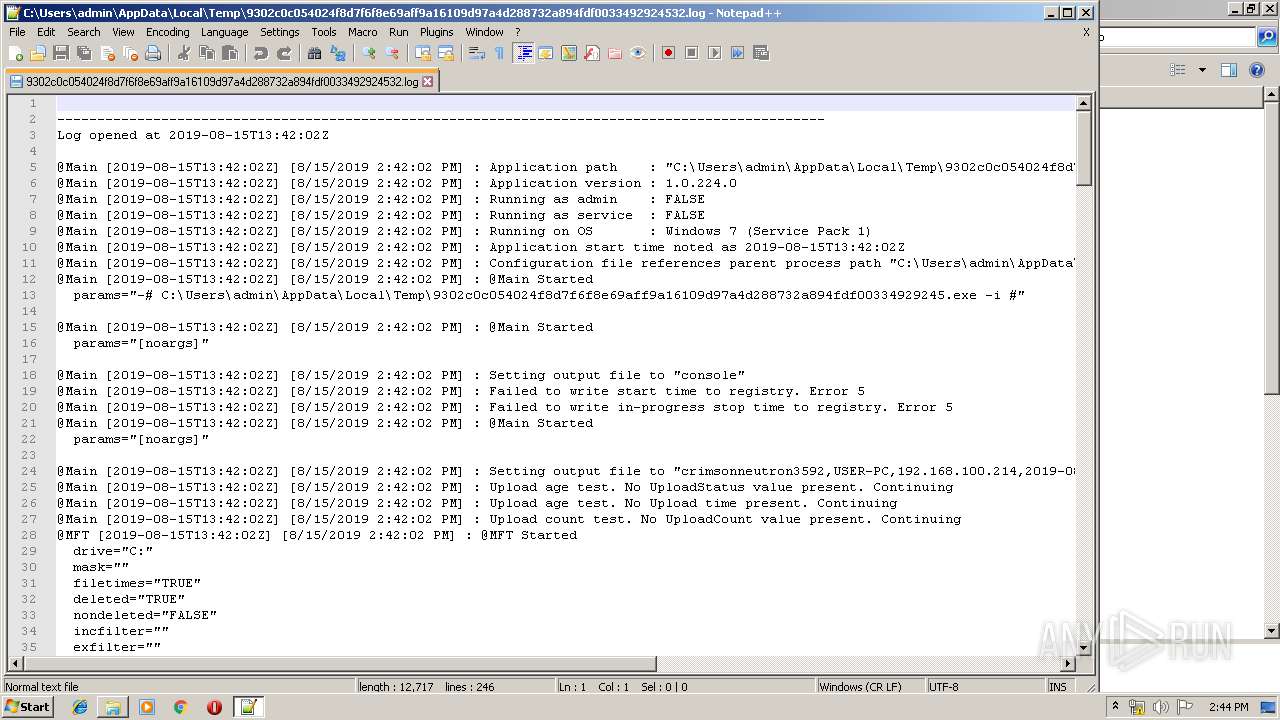
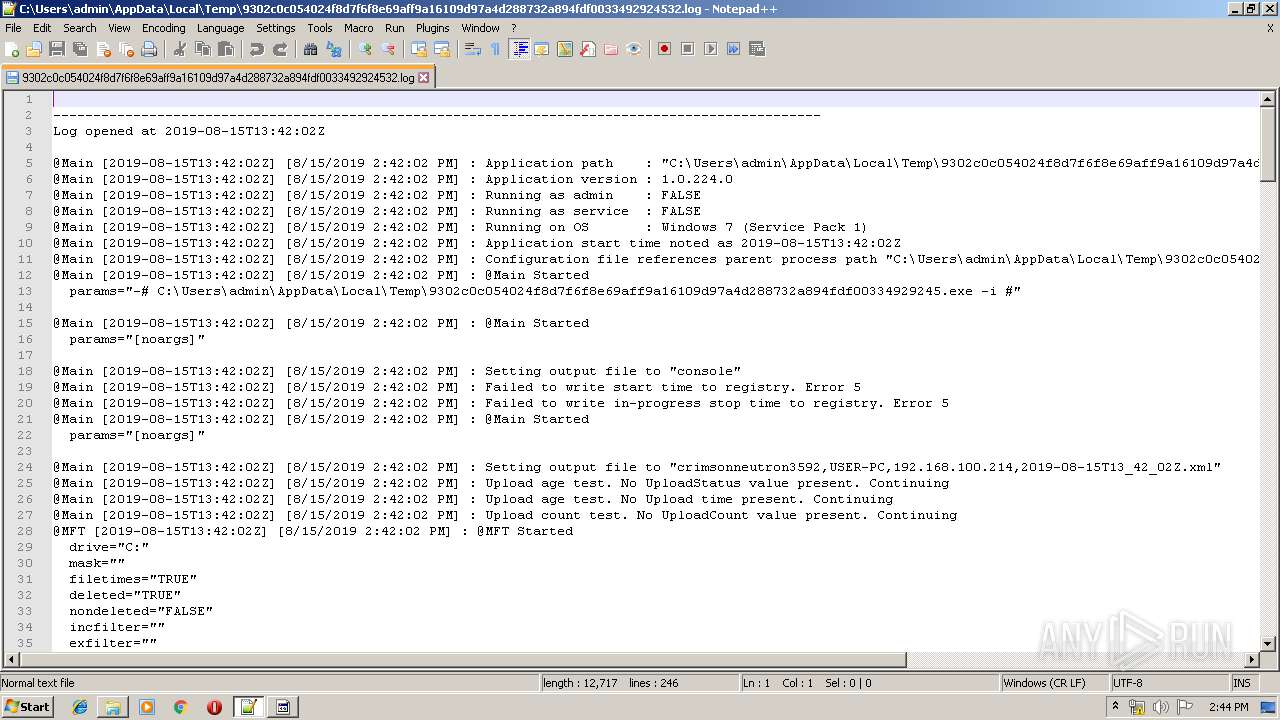
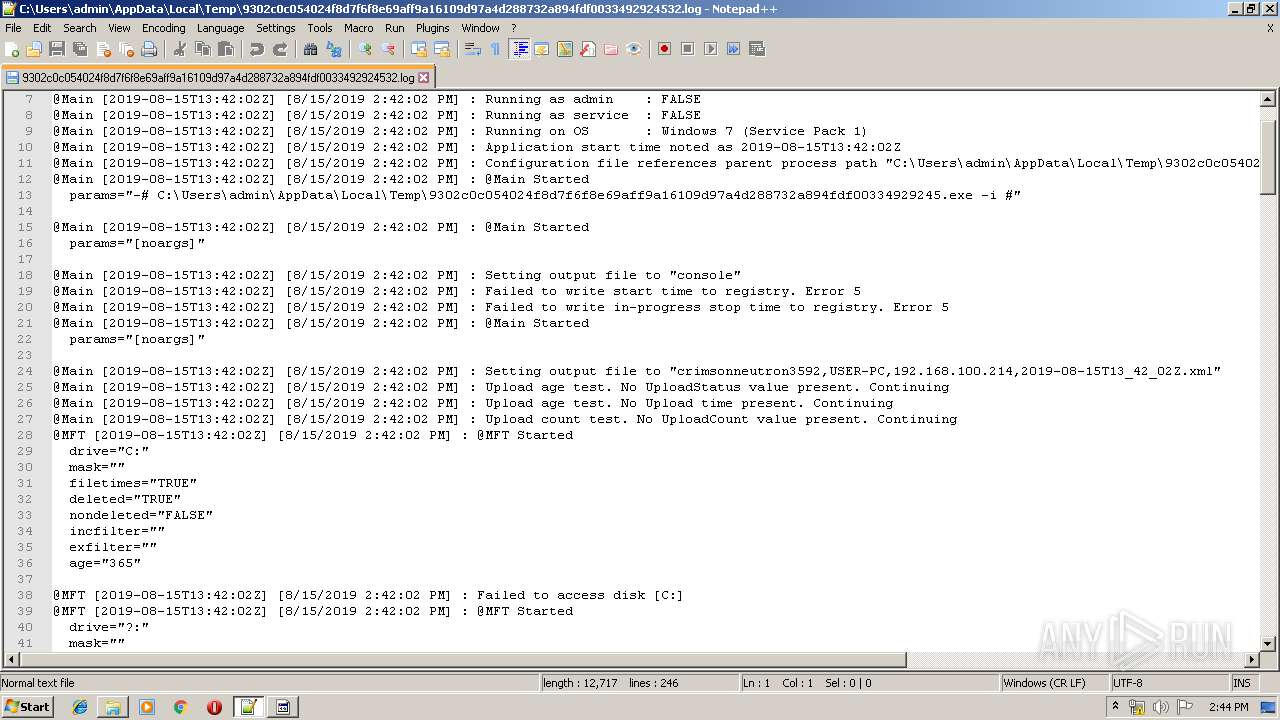
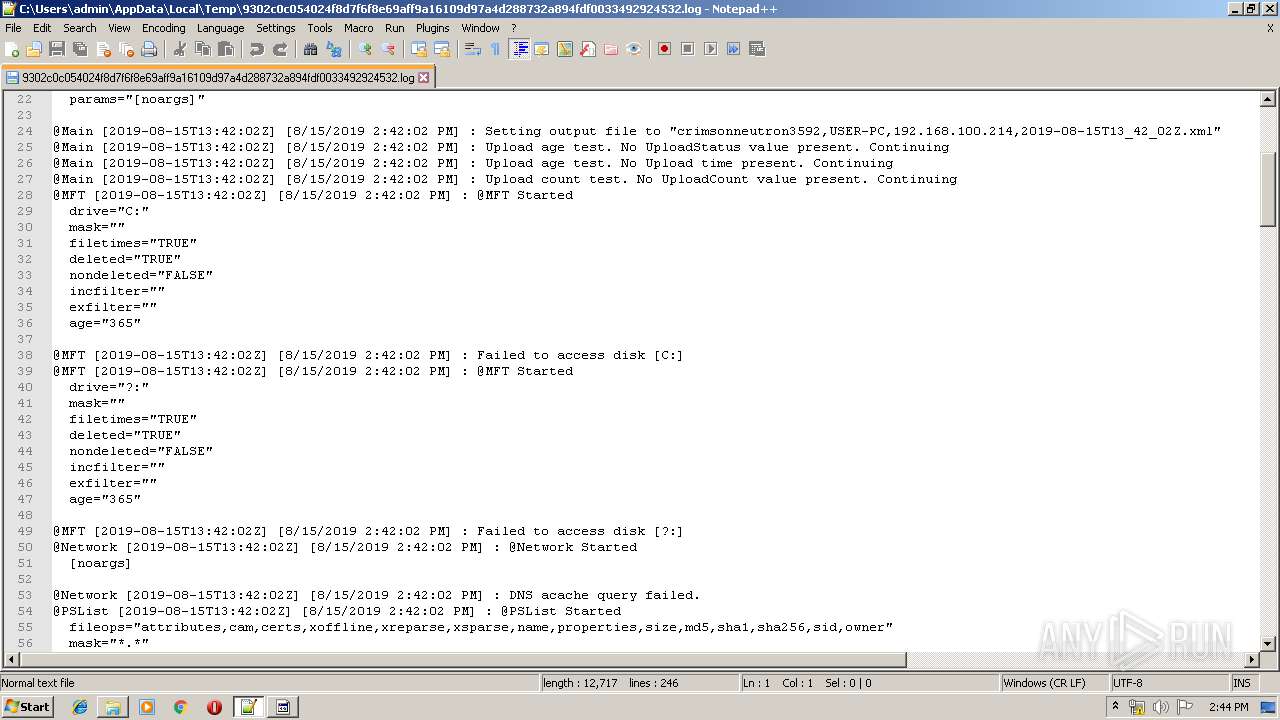
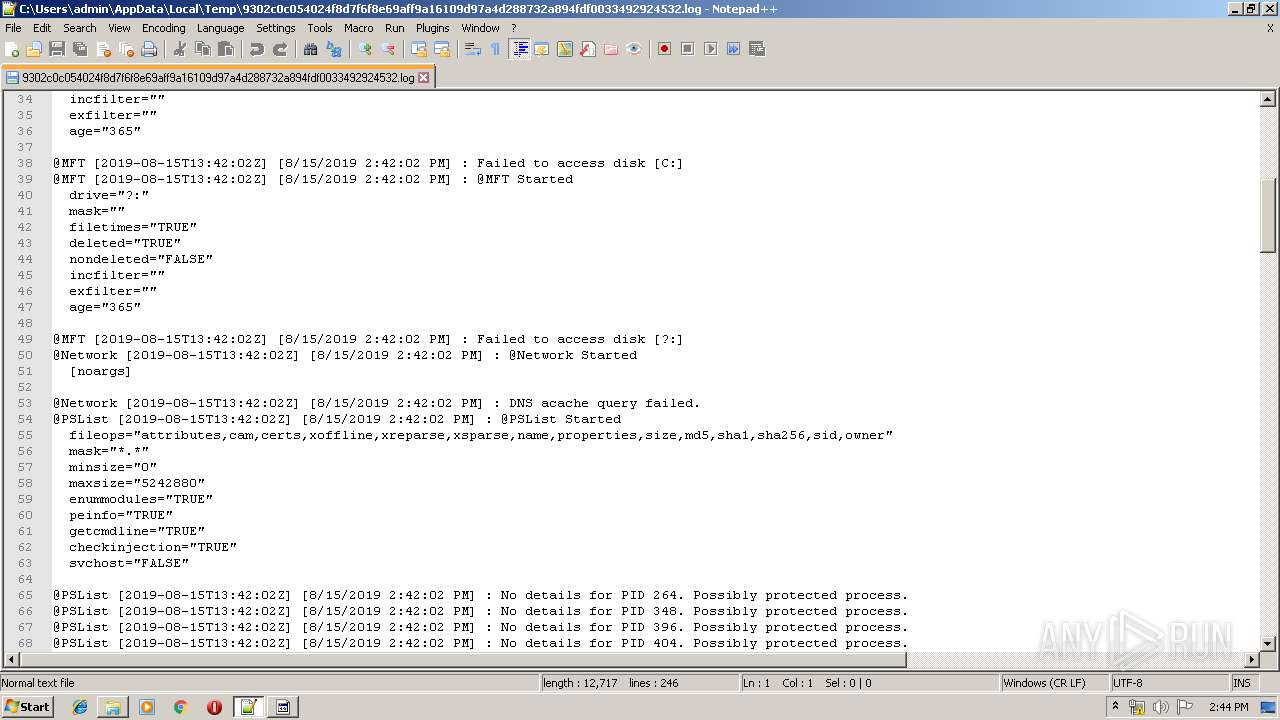
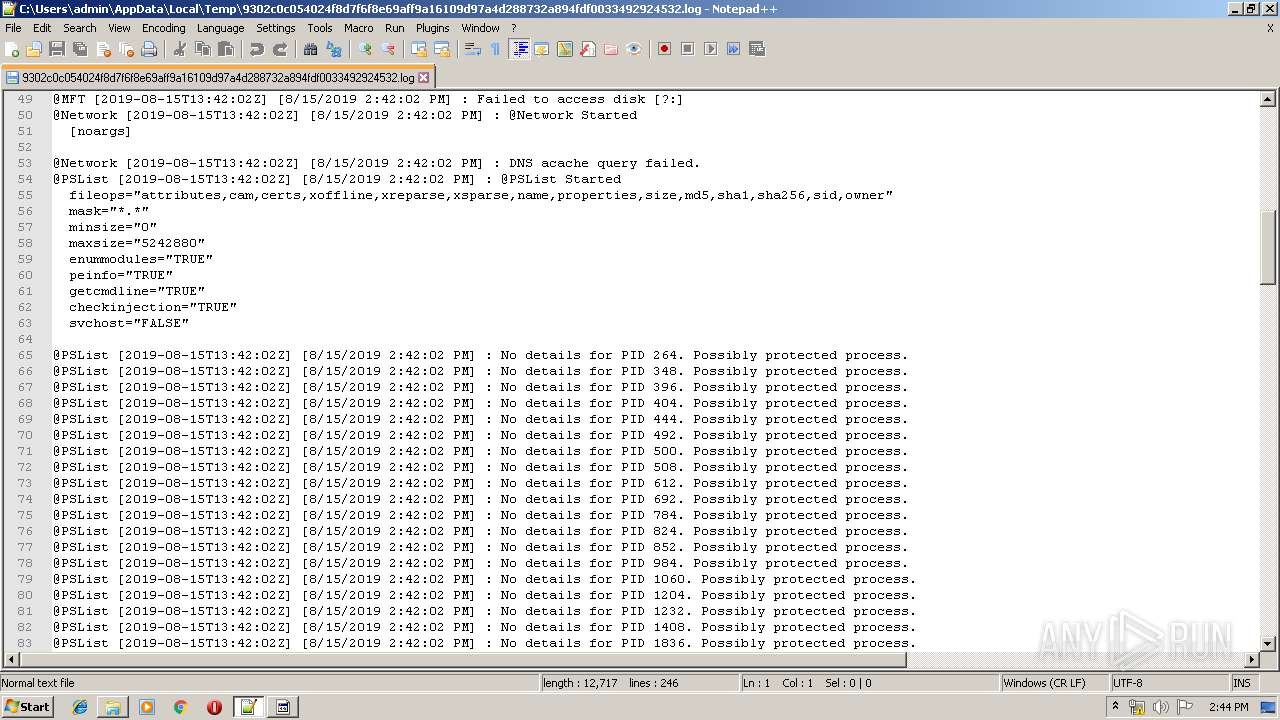
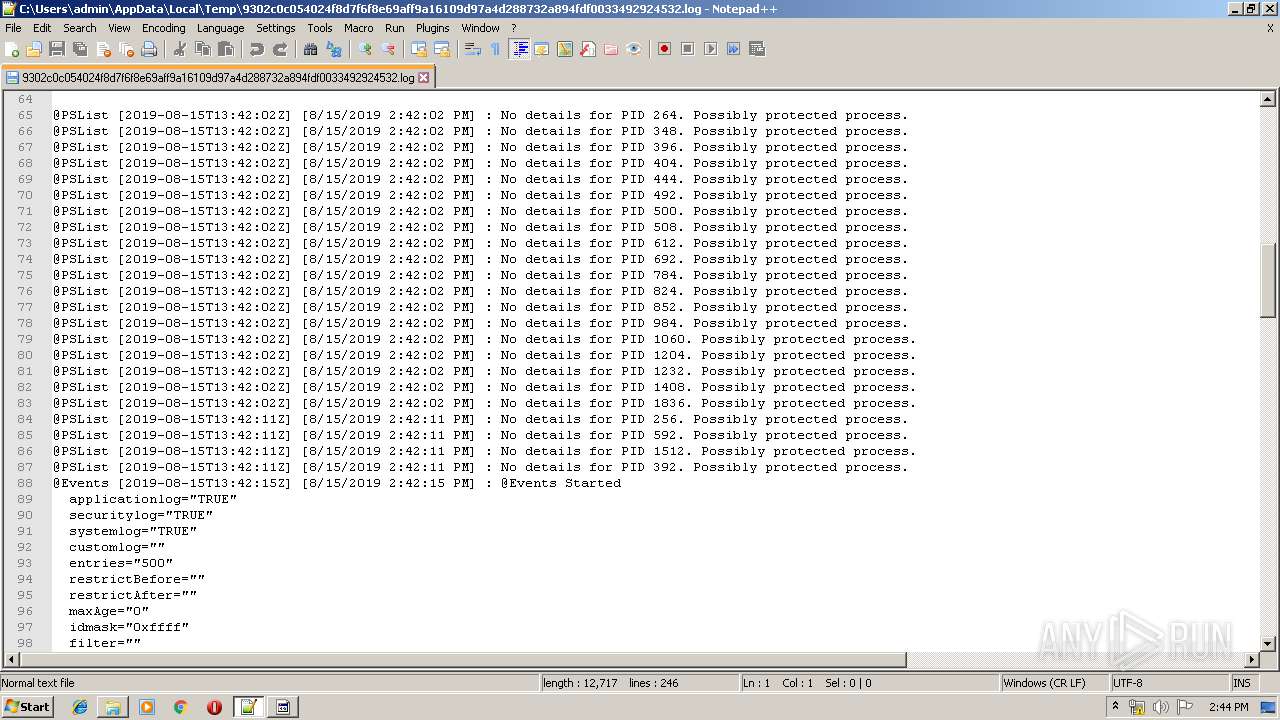
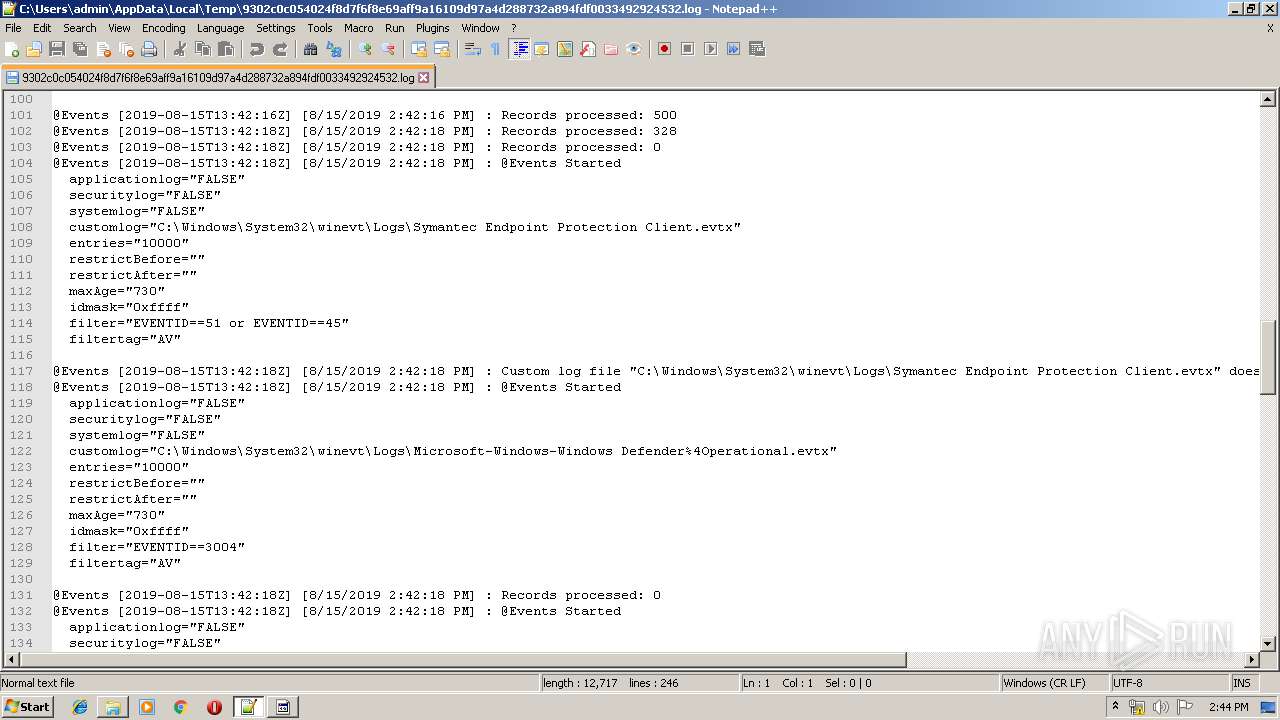
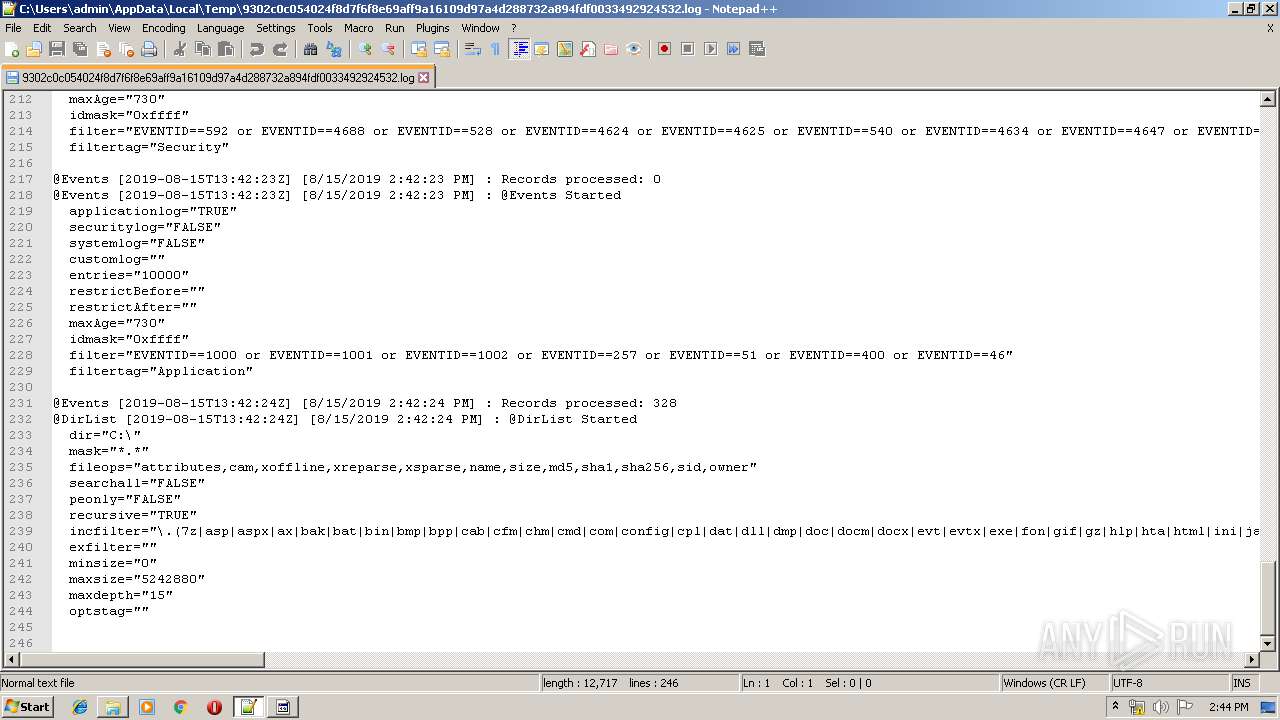
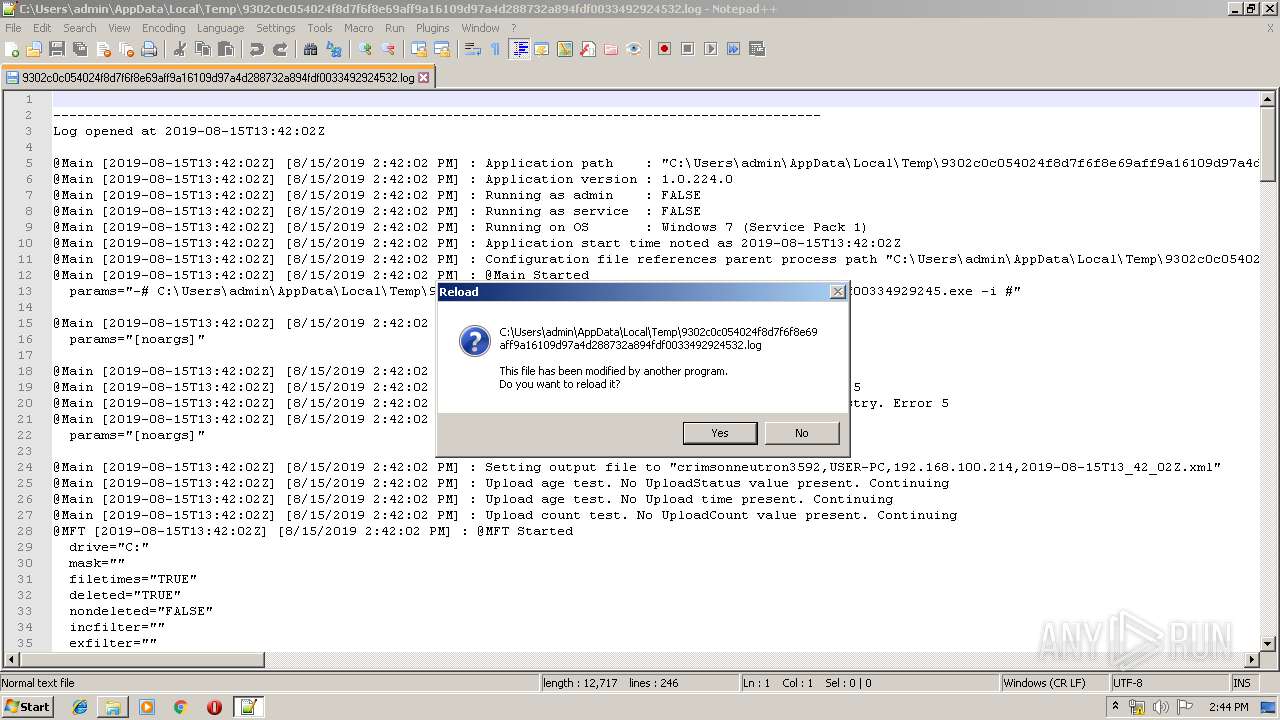
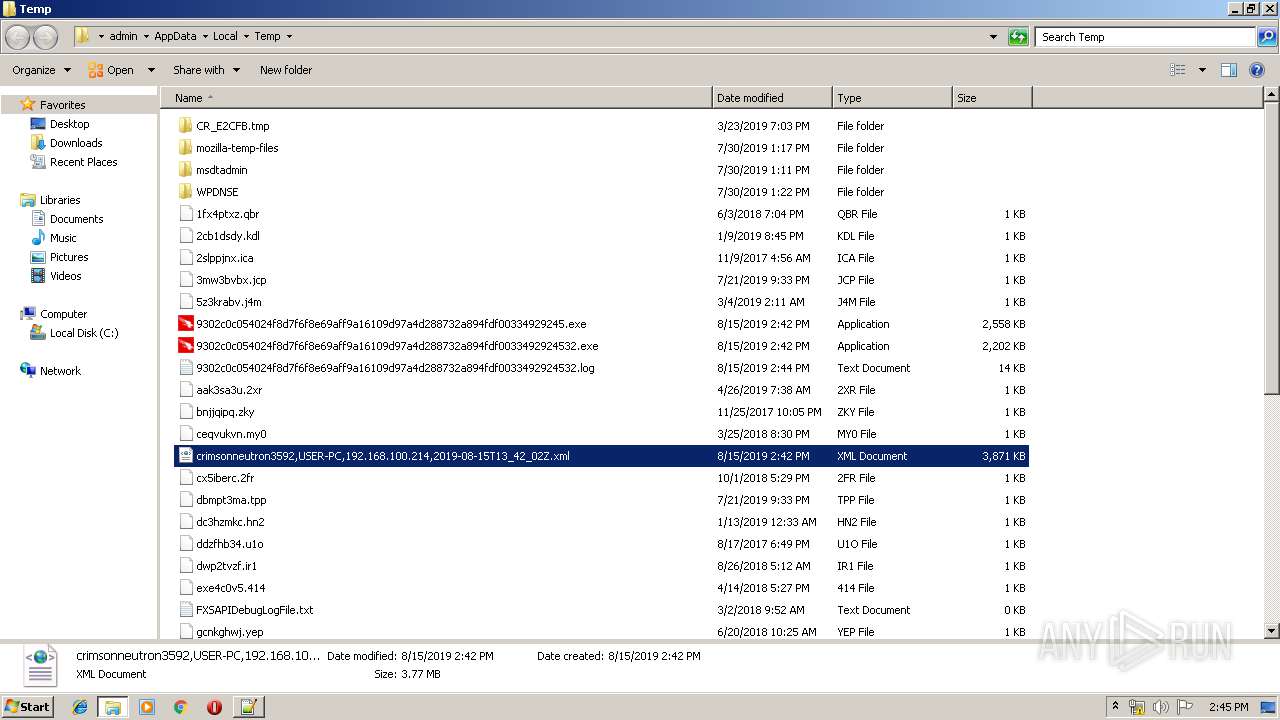
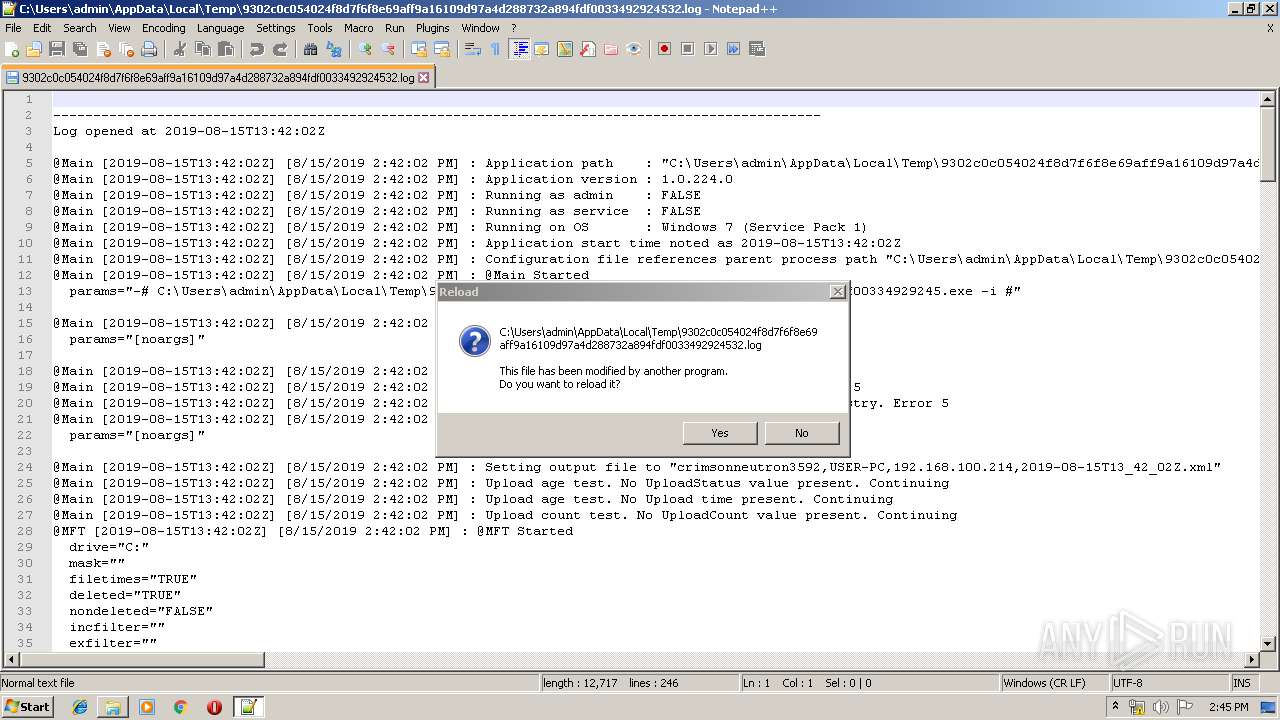
| 2712 | "C:\Users\admin\AppData\Local\Temp\9302c0c054024f8d7f6f8e69aff9a16109d97a4d288732a894fdf0033492924532.exe" -# "C:\Users\admin\AppData\Local\Temp\9302c0c054024f8d7f6f8e69aff9a16109d97a4d288732a894fdf00334929245.exe" -i "#" | C:\Users\admin\AppData\Local\Temp\9302c0c054024f8d7f6f8e69aff9a16109d97a4d288732a894fdf0033492924532.exe | 9302c0c054024f8d7f6f8e69aff9a16109d97a4d288732a894fdf00334929245.exe | ||||||||||||
User: admin Company: CrowdStrike, Inc. Integrity Level: MEDIUM Description: CrowdStrike Forensics Data Collection Tool Exit code: 0 Version: 1.0.224.0 Modules
| |||||||||||||||
| 3088 | "C:\Program Files\Notepad++\updater\gup.exe" -v7.51 | C:\Program Files\Notepad++\updater\gup.exe | notepad++.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: GUP : a free (LGPL) Generic Updater Exit code: 0 Version: 4.1 Modules
| |||||||||||||||
| 3708 | "C:\Users\admin\AppData\Local\Temp\9302c0c054024f8d7f6f8e69aff9a16109d97a4d288732a894fdf00334929245.exe" | C:\Users\admin\AppData\Local\Temp\9302c0c054024f8d7f6f8e69aff9a16109d97a4d288732a894fdf00334929245.exe | explorer.exe | ||||||||||||
User: admin Company: CrowdStrike, Inc. Integrity Level: MEDIUM Description: CrowdStrike Forensics Data Collection Tool Exit code: 0 Version: 1.0.224.0 Modules
| |||||||||||||||
| 3908 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\AppData\Local\Temp\9302c0c054024f8d7f6f8e69aff9a16109d97a4d288732a894fdf0033492924532.log" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.51 Modules
| |||||||||||||||
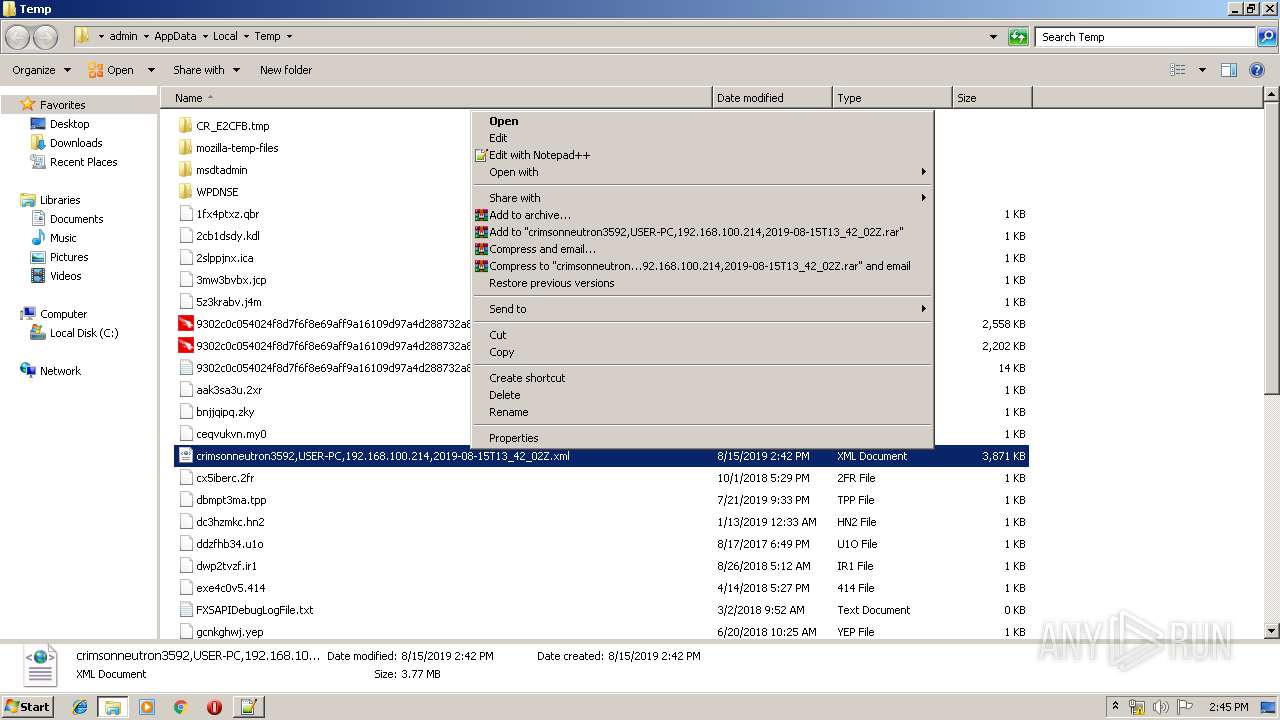
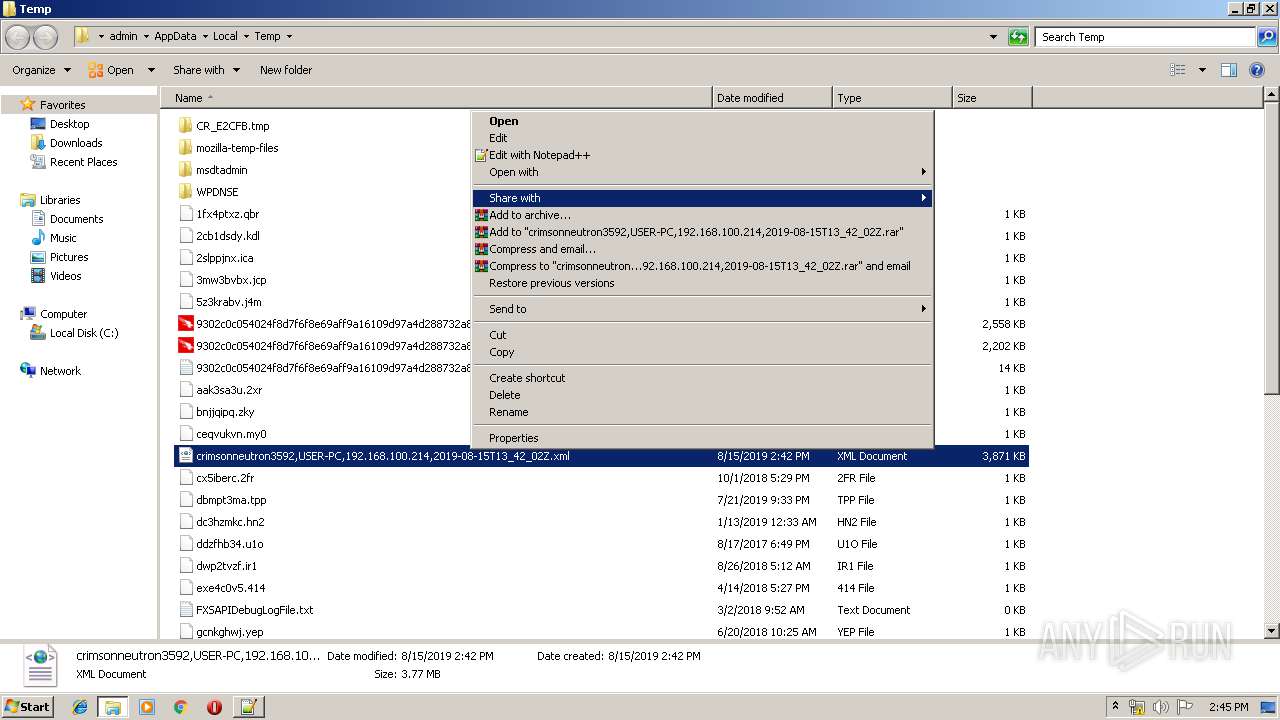
| 3940 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\AppData\Local\Temp\crimsonneutron3592,USER-PC,192.168.100.214,2019-08-15T13_42_02Z.xml" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.51 Modules
| |||||||||||||||
Total events
771
Read events
737
Write events
34
Delete events
0
Modification events
| (PID) Process: | (2712) 9302c0c054024f8d7f6f8e69aff9a16109d97a4d288732a894fdf0033492924532.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3908) notepad++.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3908) notepad++.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3908) notepad++.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3940) notepad++.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
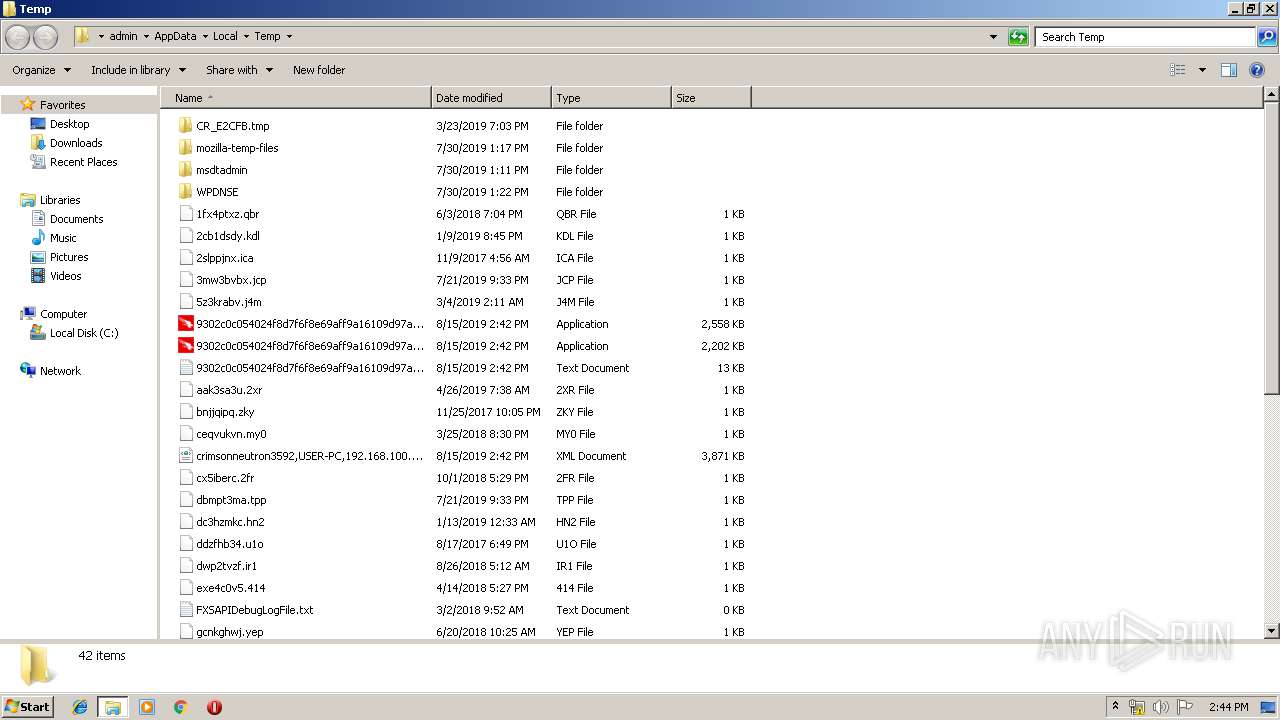
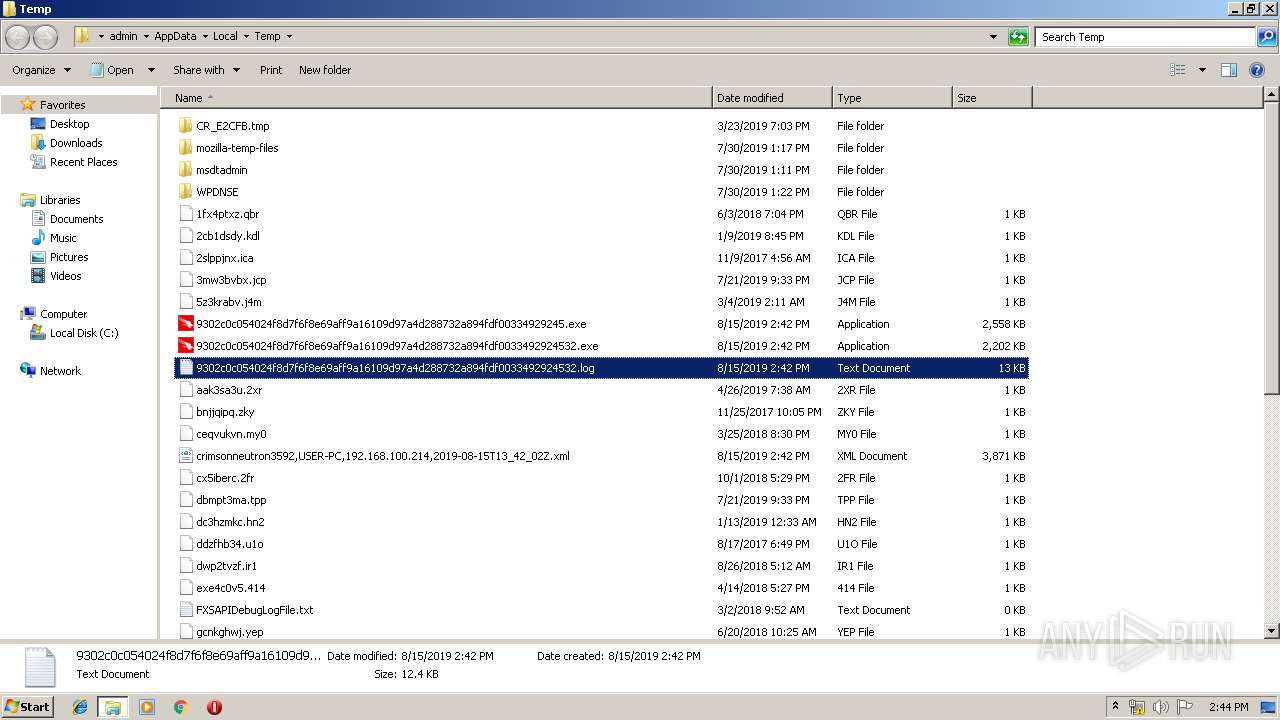
Executable files
1
Suspicious files
0
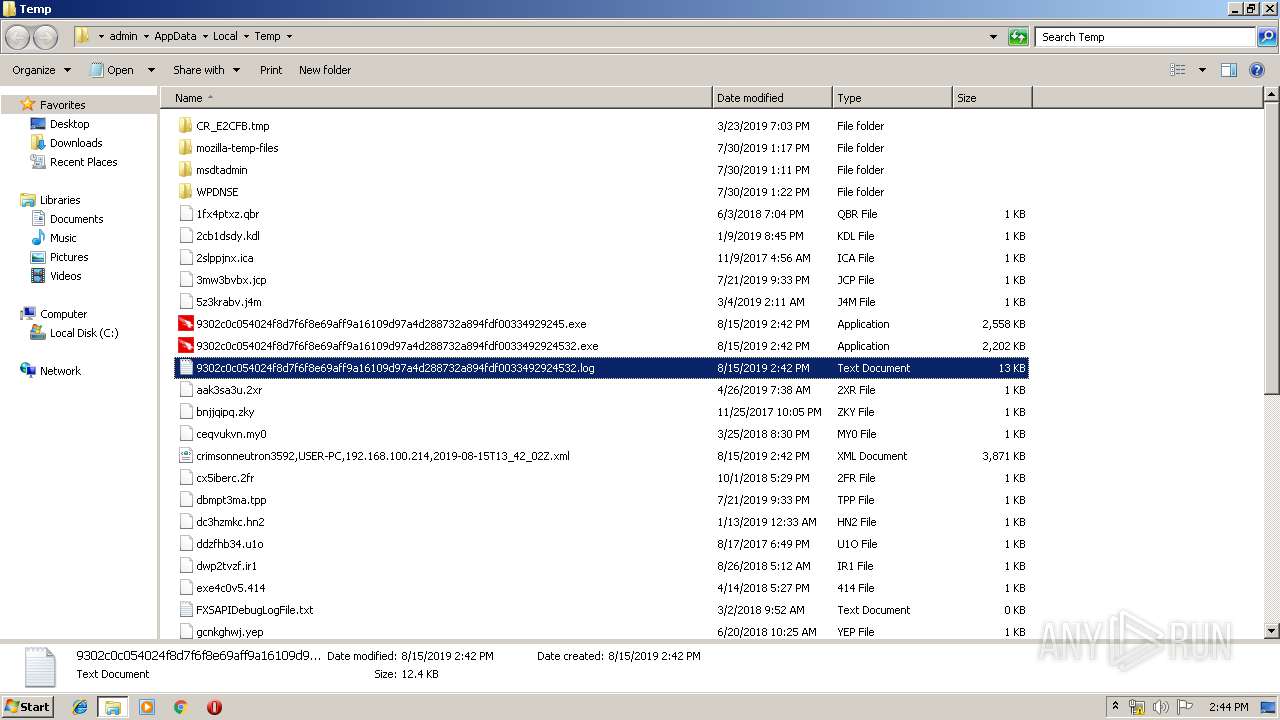
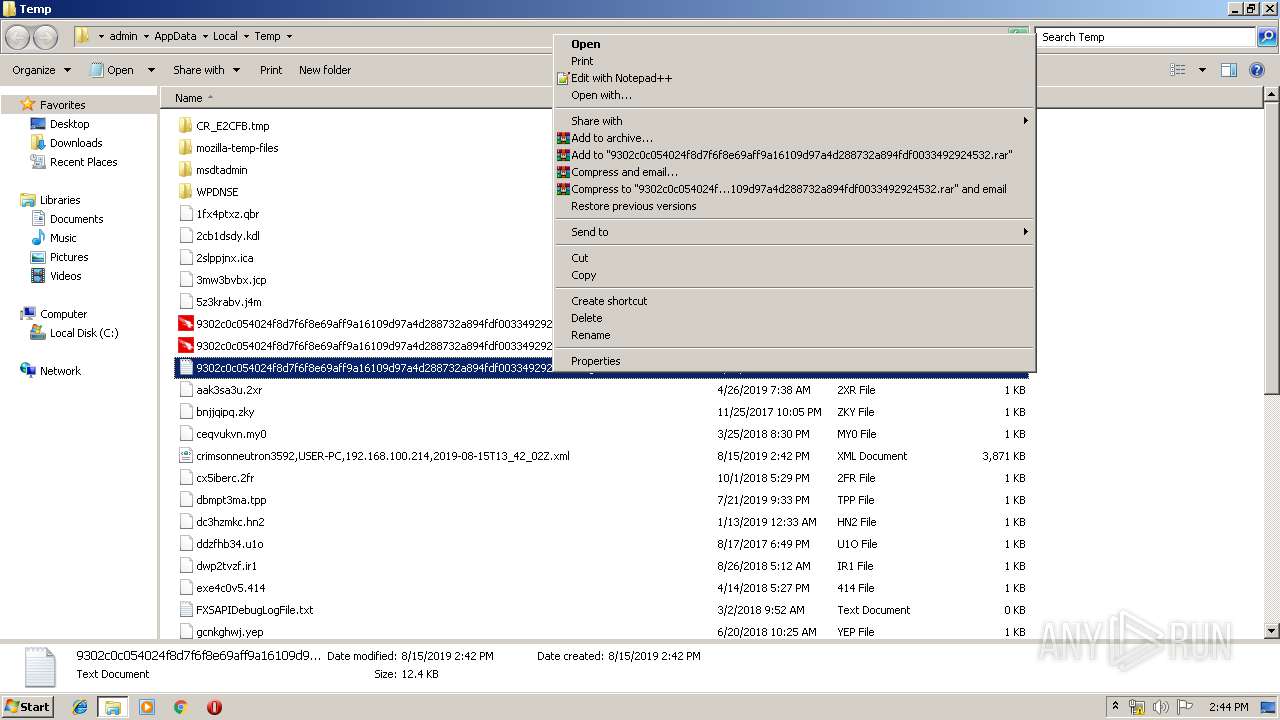
Text files
4
Unknown types
0
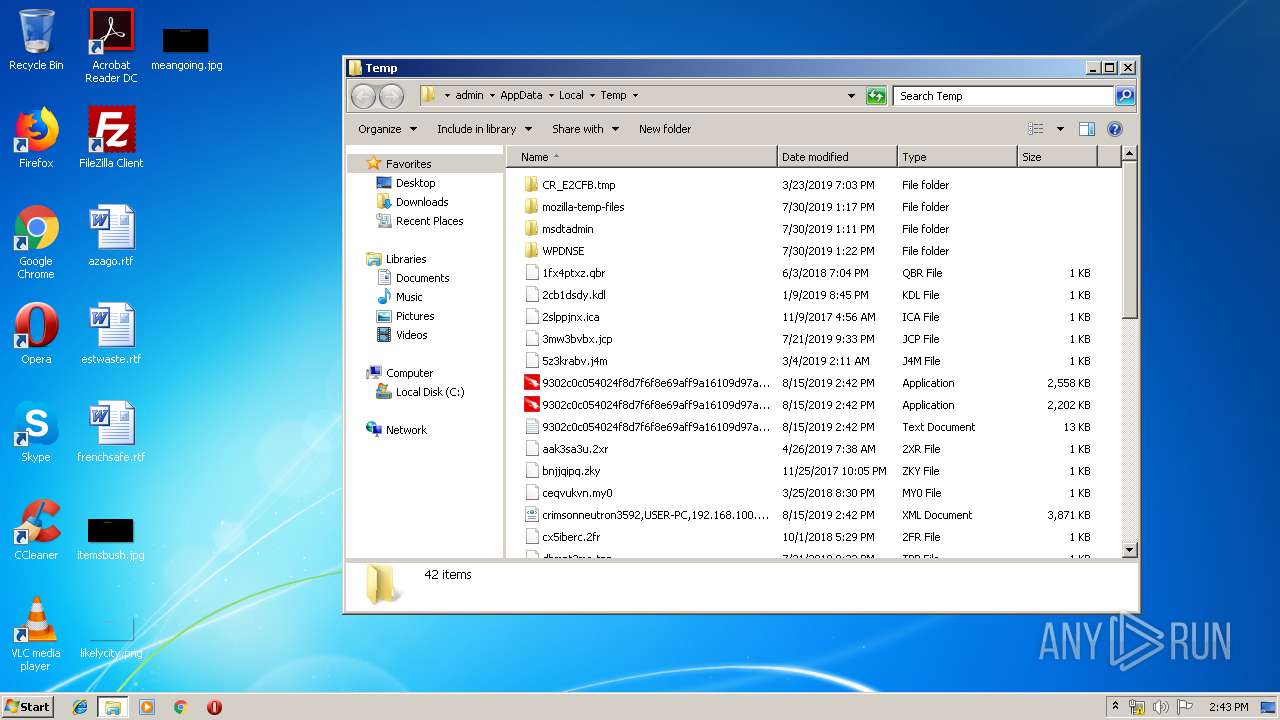
Dropped files
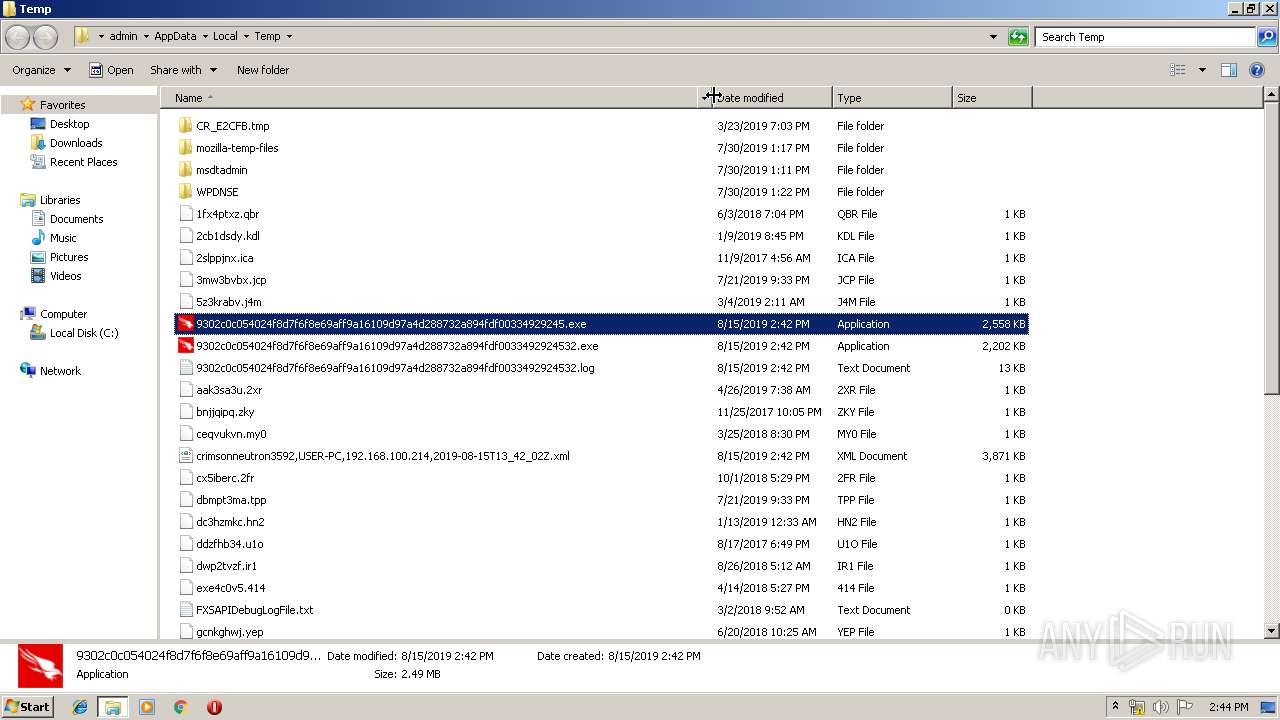
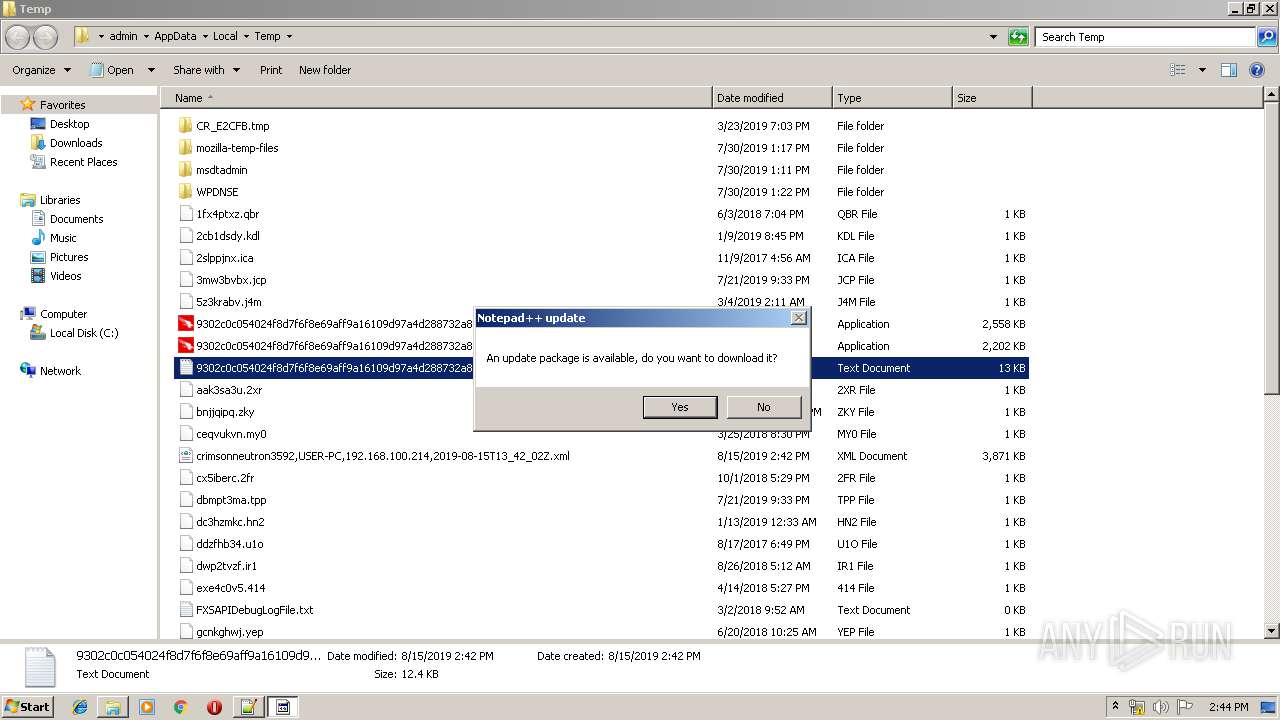
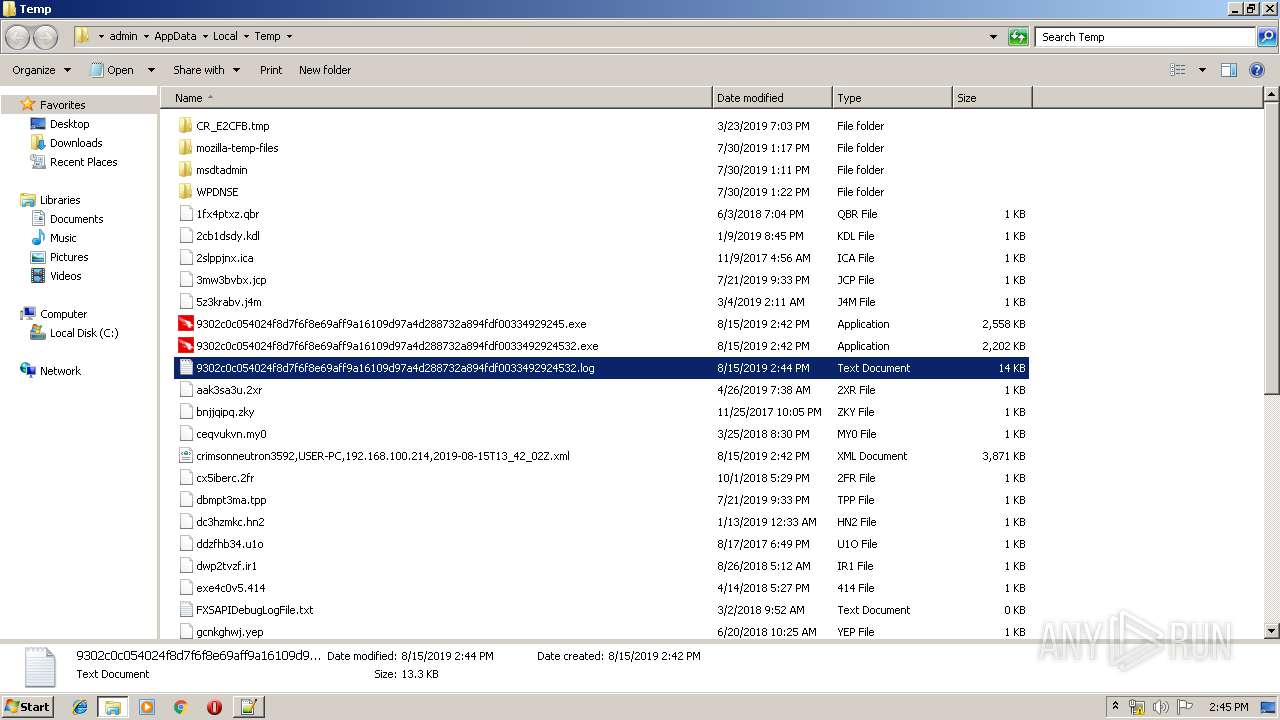
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3708 | 9302c0c054024f8d7f6f8e69aff9a16109d97a4d288732a894fdf00334929245.exe | C:\Users\admin\AppData\Local\Temp\cs0CA8FF234ADAD246AD285530BB2D789E.tmp | — | |
MD5:— | SHA256:— | |||
| 2712 | 9302c0c054024f8d7f6f8e69aff9a16109d97a4d288732a894fdf0033492924532.exe | C:\Users\admin\AppData\Local\Temp\crimsonneutron3592,USER-PC,192.168.100.214,2019-08-15T13_42_02Z.xml | — | |
MD5:— | SHA256:— | |||
| 2712 | 9302c0c054024f8d7f6f8e69aff9a16109d97a4d288732a894fdf0033492924532.exe | C:\Users\admin\AppData\Local\Temp\CabC558.tmp | — | |
MD5:— | SHA256:— | |||
| 2712 | 9302c0c054024f8d7f6f8e69aff9a16109d97a4d288732a894fdf0033492924532.exe | C:\Users\admin\AppData\Local\Temp\TarC559.tmp | — | |
MD5:— | SHA256:— | |||
| 3708 | 9302c0c054024f8d7f6f8e69aff9a16109d97a4d288732a894fdf00334929245.exe | C:\Users\admin\AppData\Local\Temp\9302c0c054024f8d7f6f8e69aff9a16109d97a4d288732a894fdf0033492924532.exe | executable | |
MD5:— | SHA256:— | |||
| 3908 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\shortcuts.xml | text | |
MD5:AD21A64014891793DD9B21D835278F36 | SHA256:C24699C9D00ABDD510140FE1B2ACE97BFC70D8B21BF3462DED85AFC4F73FE52F | |||
| 3908 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\plugins\Config\converter.ini | text | |
MD5:F70F579156C93B097E656CABA577A5C9 | SHA256:B926498A19CA95DC28964B7336E5847107DD3C0F52C85195C135D9DD6CA402D4 | |||
| 3908 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\langs.xml | xml | |
MD5:E792264BEC29005B9044A435FBA185AB | SHA256:5298FD2F119C43D04F6CF831F379EC25B4156192278E40E458EC356F9B49D624 | |||
| 3908 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\stylers.xml | xml | |
MD5:44982E1D48434C0AB3E8277E322DD1E4 | SHA256:3E661D3F1FF3977B022A0ACC26B840B5E57D600BC03DCFC6BEFDB408C665904C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.21.242.187:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | NL | der | 1.37 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 2.21.242.187:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | NL | whitelisted |
3088 | gup.exe | 37.59.28.236:443 | notepad-plus-plus.org | OVH SAS | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
notepad-plus-plus.org |
| whitelisted |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|