| File name: | 92f6380a349eb34a830d1d7e7b1b5ec2d7debc632fae980eb2746c14366a736f.exe |
| Full analysis: | https://app.any.run/tasks/d8c13ce0-fa4e-4487-ad2d-44a808c199f6 |
| Verdict: | Malicious activity |
| Analysis date: | August 02, 2025, 01:48:50 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | 64955BA699EA85BD8013D008A8F33B4B |
| SHA1: | 02E84BFD99D885A203C6EF3AC03500FB9CF9D2EA |
| SHA256: | 92F6380A349EB34A830D1D7E7B1B5EC2D7DEBC632FAE980EB2746C14366A736F |
| SSDEEP: | 98304:EuBftSXNj+NM2bm5JcxboHf2ZCDdLc3LVd4Z/c5GdgCB2hgvRzpg5fVBIqtsNBML:hWIyxq |
MALICIOUS
No malicious indicators.SUSPICIOUS
Drops 7-zip archiver for unpacking
- 92f6380a349eb34a830d1d7e7b1b5ec2d7debc632fae980eb2746c14366a736f.exe (PID: 1100)
Executable content was dropped or overwritten
- 92f6380a349eb34a830d1d7e7b1b5ec2d7debc632fae980eb2746c14366a736f.exe (PID: 1100)
Detected use of alternative data streams (AltDS)
- 92f6380a349eb34a830d1d7e7b1b5ec2d7debc632fae980eb2746c14366a736f.exe (PID: 1100)
There is functionality for taking screenshot (YARA)
- 92f6380a349eb34a830d1d7e7b1b5ec2d7debc632fae980eb2746c14366a736f.exe (PID: 1100)
INFO
Reads the computer name
- 92f6380a349eb34a830d1d7e7b1b5ec2d7debc632fae980eb2746c14366a736f.exe (PID: 1100)
Checks supported languages
- 92f6380a349eb34a830d1d7e7b1b5ec2d7debc632fae980eb2746c14366a736f.exe (PID: 1100)
- 7z.exe (PID: 2716)
The sample compiled with chinese language support
- 92f6380a349eb34a830d1d7e7b1b5ec2d7debc632fae980eb2746c14366a736f.exe (PID: 1100)
Reads mouse settings
- 92f6380a349eb34a830d1d7e7b1b5ec2d7debc632fae980eb2746c14366a736f.exe (PID: 1100)
The sample compiled with english language support
- 92f6380a349eb34a830d1d7e7b1b5ec2d7debc632fae980eb2746c14366a736f.exe (PID: 1100)
Create files in a temporary directory
- 92f6380a349eb34a830d1d7e7b1b5ec2d7debc632fae980eb2746c14366a736f.exe (PID: 1100)
Checks proxy server information
- slui.exe (PID: 7044)
The process uses AutoIt
- 92f6380a349eb34a830d1d7e7b1b5ec2d7debc632fae980eb2746c14366a736f.exe (PID: 1100)
Reads the software policy settings
- slui.exe (PID: 7044)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:10:26 02:29:38+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 570880 |
| InitializedDataSize: | 2369024 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x25f74 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 7.0.21.328 |
| ProductVersionNumber: | 7.0.21.315 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| FileVersion: | 7.0.21.0328 |
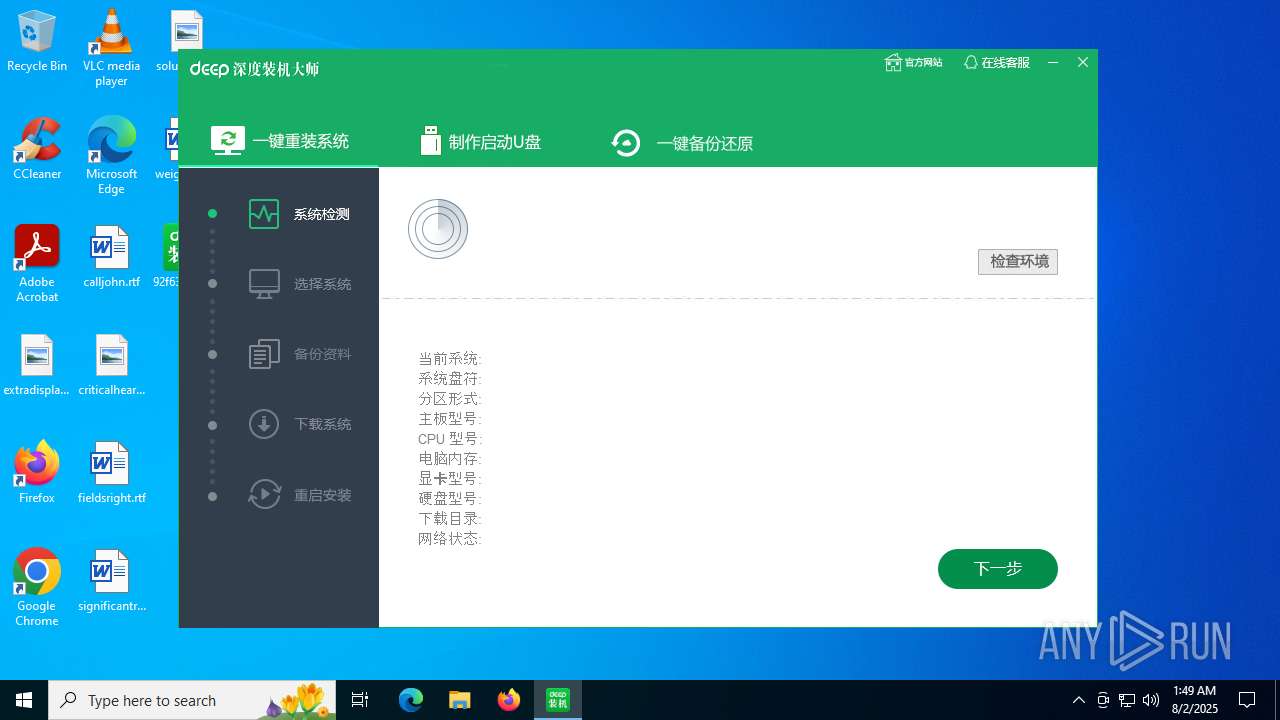
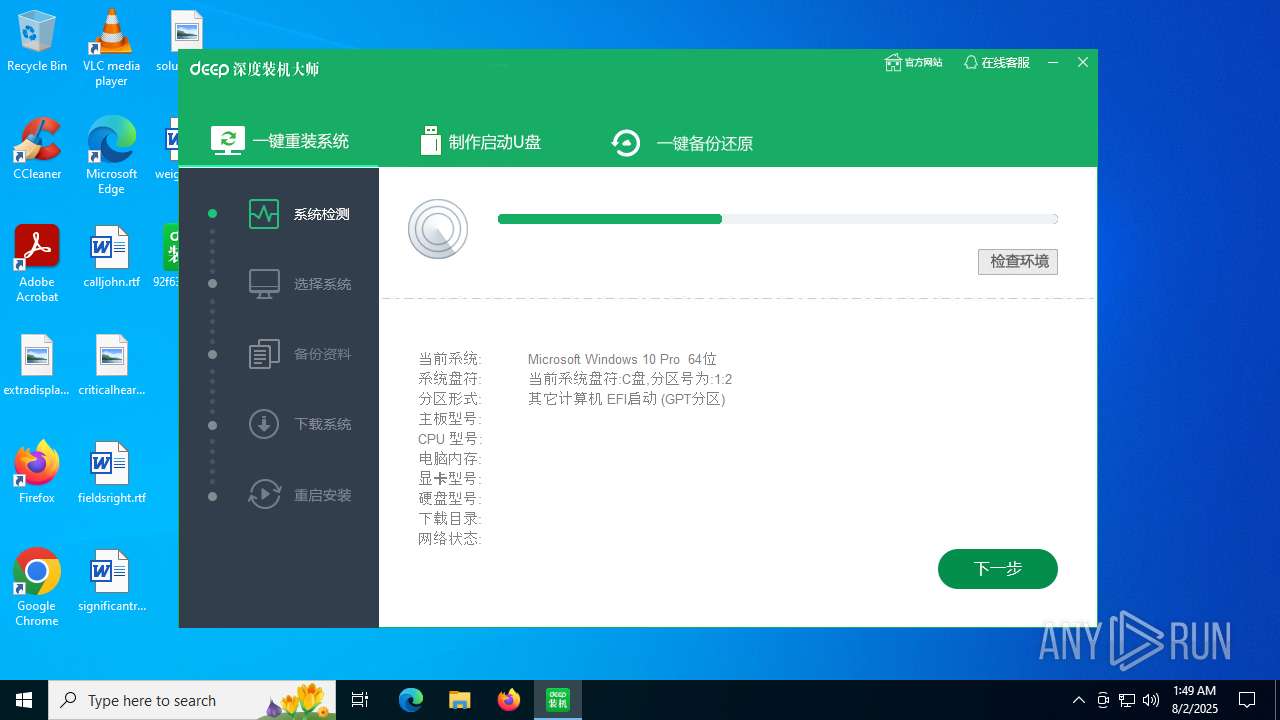
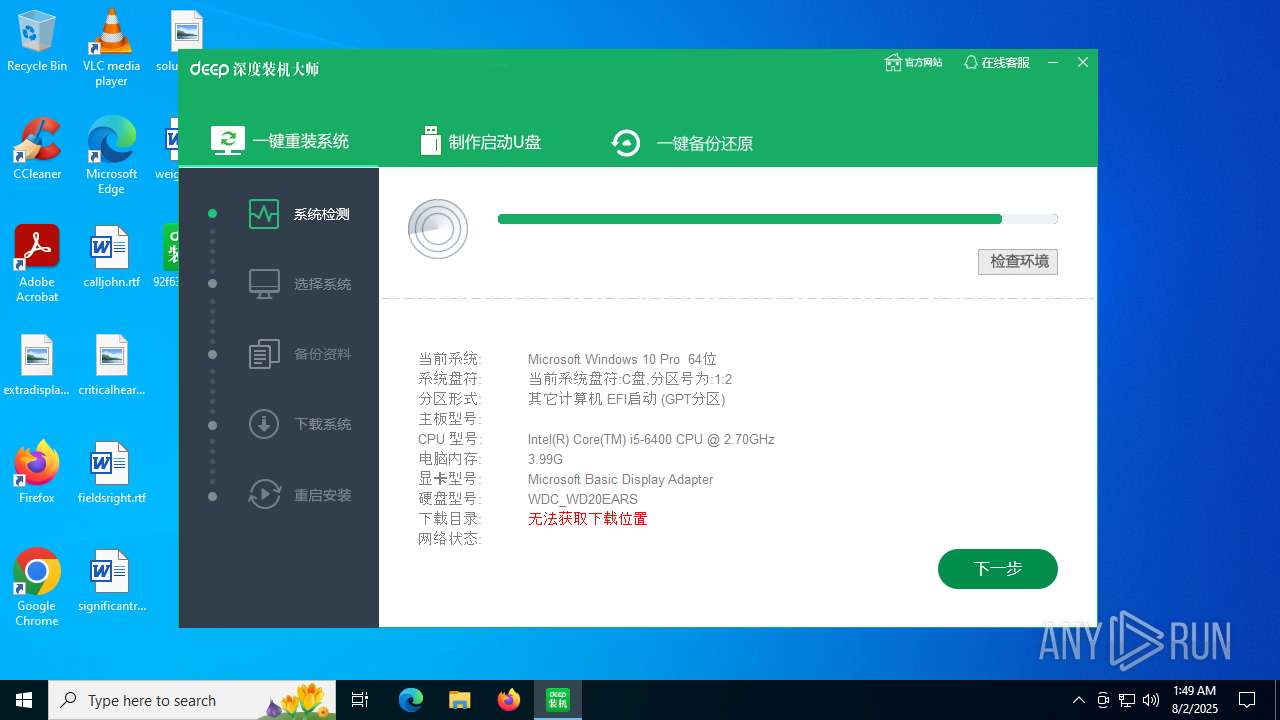
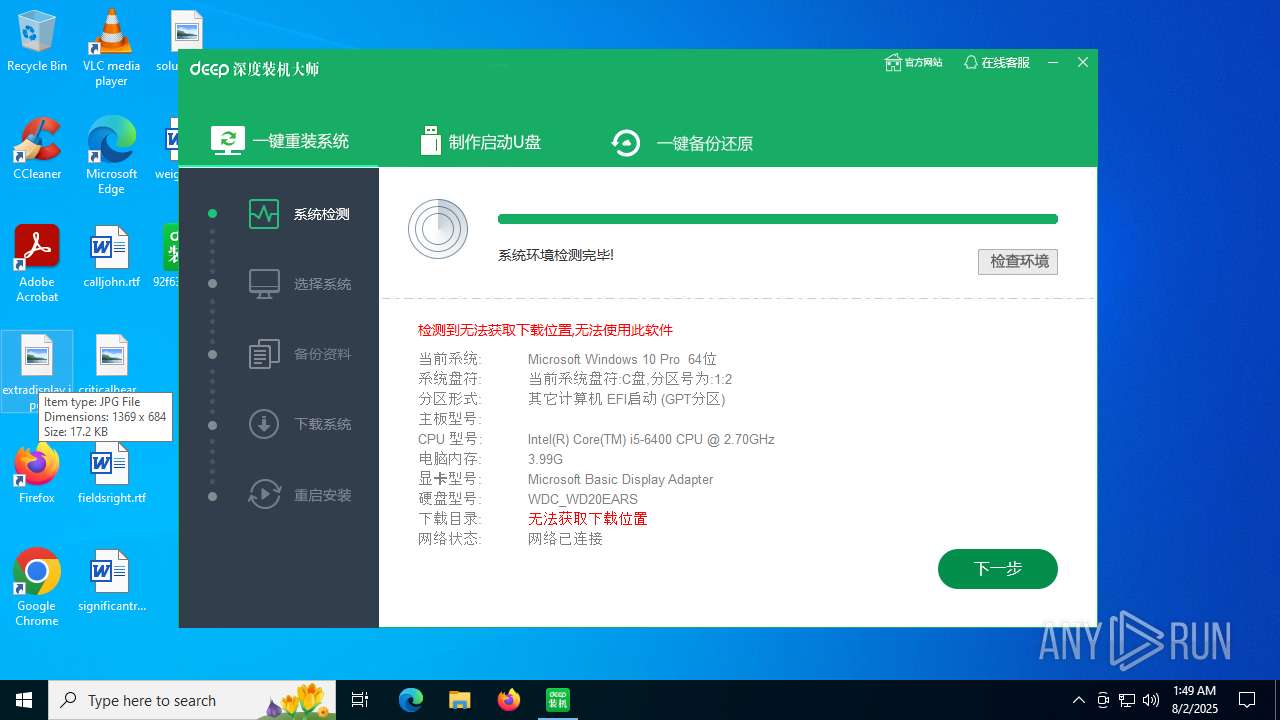
| Comments: | 深度技术-装机大师 |
| FileDescription: | 深度技术_网络维护系统,方便安全快捷高效! |
| ProductVersion: | 7.0.21.0315 |
| LegalCopyright: | Copyright 2018-2021 PEoss, All Rights Reserved. |
| ProductName: | 深度技术装机大师 |
| LegalTrademarks: | 深度技术装机大师 |
| OriginalFileName: | sdxitong.exe |
Total processes
139
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1100 | "C:\Users\admin\Desktop\92f6380a349eb34a830d1d7e7b1b5ec2d7debc632fae980eb2746c14366a736f.exe" | C:\Users\admin\Desktop\92f6380a349eb34a830d1d7e7b1b5ec2d7debc632fae980eb2746c14366a736f.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: 深度技术_网络维护系统,方便安全快捷高效! Version: 7.0.21.0328 Modules
| |||||||||||||||
| 2716 | C:\Users\admin\AppData\Local\Temp\xh_dtpjeiy.\7z.exe x "C:\Users\admin\Desktop\92f6380a349eb34a830d1d7e7b1b5ec2d7debc632fae980eb2746c14366a736f.exe" -y -o"C:\Users\admin\AppData\Local\Temp\xh_dtpjeiy." | C:\Users\admin\AppData\Local\Temp\xh_dtpjeiy\7z.exe | — | 92f6380a349eb34a830d1d7e7b1b5ec2d7debc632fae980eb2746c14366a736f.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7-Zip Console Exit code: 2 Version: 9.20 Modules
| |||||||||||||||
| 2980 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | 7z.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6508 | "C:\Users\admin\Desktop\92f6380a349eb34a830d1d7e7b1b5ec2d7debc632fae980eb2746c14366a736f.exe" | C:\Users\admin\Desktop\92f6380a349eb34a830d1d7e7b1b5ec2d7debc632fae980eb2746c14366a736f.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: 深度技术_网络维护系统,方便安全快捷高效! Exit code: 3221226540 Version: 7.0.21.0328 Modules
| |||||||||||||||
| 7044 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 876
Read events
3 876
Write events
0
Delete events
0
Modification events
Executable files
2
Suspicious files
36
Text files
63
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1100 | 92f6380a349eb34a830d1d7e7b1b5ec2d7debc632fae980eb2746c14366a736f.exe | C:\Users\admin\AppData\Local\Temp\xh_dtpjeiy\images\1_Mode2_1.jpg | image | |
MD5:4BB3958C16D8E5512D403FC76120B861 | SHA256:D4ABF5FA7E6EAD953C4B371CD88E3EA7F405843A7A4B3B95EEFEE382BBC6BC61 | |||
| 1100 | 92f6380a349eb34a830d1d7e7b1b5ec2d7debc632fae980eb2746c14366a736f.exe | C:\Users\admin\AppData\Local\Temp\autDB58.tmp | binary | |
MD5:3BB3F5324B757E8CAE7C06B7998D49AD | SHA256:2367FFD71171EE34C535E843BAC01CCE93AA788184C7DF51BE0B2391095136E6 | |||
| 1100 | 92f6380a349eb34a830d1d7e7b1b5ec2d7debc632fae980eb2746c14366a736f.exe | C:\Users\admin\AppData\Local\Temp\autDC5A.tmp | binary | |
MD5:43A794A353401A81F02CC9C0DAB9E597 | SHA256:8868D6A8F7A45607619F04BD3AAF1A43CF35A256EBA9EF7E6E0BE3844D41FAA8 | |||
| 1100 | 92f6380a349eb34a830d1d7e7b1b5ec2d7debc632fae980eb2746c14366a736f.exe | C:\Users\admin\AppData\Local\Temp\xh_dtpjeiy\7z.exe | executable | |
MD5:FF7A6F30A05959C05CA54D47BEBB28B8 | SHA256:29717709356C1C1C28339D80C97F202AB00D2D42B7E16296E5E7456056B7BB84 | |||
| 1100 | 92f6380a349eb34a830d1d7e7b1b5ec2d7debc632fae980eb2746c14366a736f.exe | C:\Users\admin\AppData\Local\Temp\autDC07.tmp | binary | |
MD5:C1DEA3D5E657BDB2FB31DD8AEC362FF6 | SHA256:90D27FE606D9CB74D6BEF68136EABAFD211D1FD13B639FEC9EFD130DC2AA25F3 | |||
| 1100 | 92f6380a349eb34a830d1d7e7b1b5ec2d7debc632fae980eb2746c14366a736f.exe | C:\Users\admin\AppData\Local\Temp\autDC06.tmp | binary | |
MD5:9E10B25B7F8D4B571176A79B67E05DAD | SHA256:A1AF7522E4B71F5EFF96B0199D1E2860A5FEE89F4D3108297D73C10F027E837F | |||
| 1100 | 92f6380a349eb34a830d1d7e7b1b5ec2d7debc632fae980eb2746c14366a736f.exe | C:\Users\admin\AppData\Local\Temp\autDBC7.tmp | binary | |
MD5:5C84E0523B807E578E9745C0111904A7 | SHA256:065C767CCAAFF68602F6D393DBA35FBB2194DF346E1822138FC0984898E1C260 | |||
| 1100 | 92f6380a349eb34a830d1d7e7b1b5ec2d7debc632fae980eb2746c14366a736f.exe | C:\Users\admin\AppData\Local\Temp\xh_dtpjeiy\images\1_Mode3_1.jpg | image | |
MD5:C004BB61B683D5AE80F28CDF45098B0C | SHA256:FA05A70CE373C2758A07EFE985DE5DE0F0BA5C797FEF88DF6E1976A9A61FED60 | |||
| 1100 | 92f6380a349eb34a830d1d7e7b1b5ec2d7debc632fae980eb2746c14366a736f.exe | C:\Users\admin\AppData\Local\Temp\autDC4A.tmp | binary | |
MD5:00F30E65E1EF59D249AFC5F309552625 | SHA256:D7C87EA9417D5E48D306379449F1F81619BC338AA14B79585029CF6F766B3892 | |||
| 1100 | 92f6380a349eb34a830d1d7e7b1b5ec2d7debc632fae980eb2746c14366a736f.exe | C:\Users\admin\AppData\Local\Temp\xh_dtpjeiy\images\bg.jpg | image | |
MD5:16264DE8792D0F674EA0E81574BD0C1E | SHA256:16F39D0E75DF77B08CE2A8D5BB104AC3E7D9EDD9FC8B88AC188D6C001A5C7C22 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
40
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.55.110.193:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.55.110.193:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3960 | RUXIMICS.exe | GET | 200 | 23.55.110.193:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3960 | RUXIMICS.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1100 | 92f6380a349eb34a830d1d7e7b1b5ec2d7debc632fae980eb2746c14366a736f.exe | GET | 200 | 185.106.177.142:80 | http://xiaohei.xiuchufang.com/config.txt | unknown | — | — | unknown |
— | — | POST | 400 | 20.190.160.2:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | POST | 400 | 20.190.159.73:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3960 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 23.55.110.193:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.55.110.193:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
3960 | RUXIMICS.exe | 23.55.110.193:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
xiaohei.xiuchufang.com |
| unknown |
self.events.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |