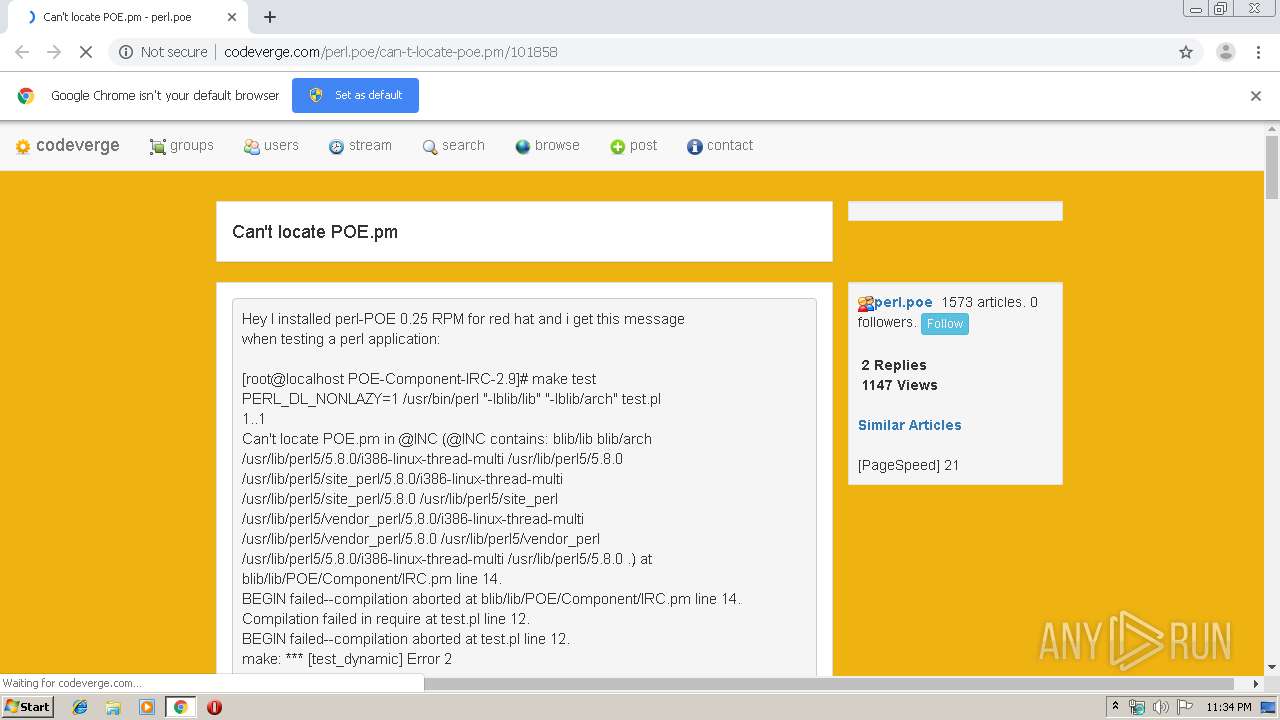
| URL: | http://codeverge.com/perl.poe/can-t-locate-poe.pm/101858 |
| Full analysis: | https://app.any.run/tasks/c7c4417d-0599-44c7-8352-b880c022a3a1 |
| Verdict: | Malicious activity |
| Analysis date: | January 17, 2020, 23:34:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 5DA35ECCC60F6C393920175427494F8C |
| SHA1: | 4CAF7C61DE48755187E14787625F614CF4E0F750 |
| SHA256: | 92DA344034B2D17B1FCADC1CACA76E2C3DCAF953183BF0F512B076FD20926D56 |
| SSDEEP: | 3:N1KdKBAWBVAXmGELs0d4vVImu:CI2W8XxELs0Ga |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2416)
INFO
Application launched itself
- chrome.exe (PID: 2416)
Reads settings of System Certificates
- chrome.exe (PID: 2092)
Reads the hosts file
- chrome.exe (PID: 2416)
- chrome.exe (PID: 2092)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
70
Monitored processes
35
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,6147491286848509495,8471258549834483080,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9766786835226917726 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4396 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,6147491286848509495,8471258549834483080,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17045640387054702277 --mojo-platform-channel-handle=4840 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,6147491286848509495,8471258549834483080,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7036553825241355293 --renderer-client-id=30 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5340 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,6147491286848509495,8471258549834483080,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1229510790967139323 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2256 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,6147491286848509495,8471258549834483080,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=367667657679070036 --mojo-platform-channel-handle=4180 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,6147491286848509495,8471258549834483080,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13487103939617319533 --mojo-platform-channel-handle=4568 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1788 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,6147491286848509495,8471258549834483080,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1015665861743094379 --mojo-platform-channel-handle=5380 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1892 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,6147491286848509495,8471258549834483080,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18421098103298668503 --mojo-platform-channel-handle=4872 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,6147491286848509495,8471258549834483080,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7391151260546491311 --mojo-platform-channel-handle=5060 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,6147491286848509495,8471258549834483080,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11599305402947193147 --mojo-platform-channel-handle=4976 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
619
Read events
519
Write events
95
Delete events
5
Modification events
| (PID) Process: | (2416) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2416) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2416) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2416) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2416) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2452) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2416-13223777655958125 |
Value: 259 | |||
| (PID) Process: | (2416) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2416) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2416) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2416) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
31
Text files
305
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\3ad11ff6-2e54-4736-b033-a899f647e9e6.tmp | — | |
MD5:— | SHA256:— | |||
| 2416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF39a8cd.TMP | text | |
MD5:— | SHA256:— | |||
| 2416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF39a87f.TMP | text | |
MD5:— | SHA256:— | |||
| 2416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
46
TCP/UDP connections
32
DNS requests
25
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2092 | chrome.exe | GET | 200 | 108.170.15.252:80 | http://codeverge.com/img/group16.png | US | image | 381 b | whitelisted |
2092 | chrome.exe | GET | 200 | 108.170.15.252:80 | http://codeverge.com/perl.poe/can-t-locate-poe.pm/101858 | US | html | 10.6 Kb | whitelisted |
2092 | chrome.exe | GET | 200 | 108.170.15.252:80 | http://codeverge.com/img/clock16.png | US | image | 841 b | whitelisted |
2092 | chrome.exe | GET | 200 | 108.170.15.252:80 | http://codeverge.com/_config/main.css | US | text | 293 b | whitelisted |
2092 | chrome.exe | GET | 200 | 108.170.15.252:80 | http://codeverge.com/img/add16.png | US | image | 838 b | whitelisted |
2092 | chrome.exe | GET | 200 | 108.170.15.252:80 | http://codeverge.com/js/main.js | US | html | 1.33 Kb | whitelisted |
2092 | chrome.exe | GET | 200 | 108.170.15.252:80 | http://codeverge.com/img/info16.png | US | image | 672 b | whitelisted |
2092 | chrome.exe | GET | 200 | 108.170.15.252:80 | http://codeverge.com/scripts/colorbox/colorbox.css | US | text | 950 b | whitelisted |
2092 | chrome.exe | GET | 200 | 108.170.15.252:80 | http://codeverge.com/img/icon_search.gif | US | image | 1009 b | whitelisted |
2092 | chrome.exe | GET | 200 | 108.170.15.252:80 | http://codeverge.com/bundles/menujs?v=sYkte-rP937TJGqV8dUKxWWx-neRhlNRKGng-En9k0s1 | US | text | 203 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2092 | chrome.exe | 108.170.15.252:80 | codeverge.com | SECURED SERVERS LLC | US | unknown |
2092 | chrome.exe | 172.217.21.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2092 | chrome.exe | 104.17.65.4:80 | cdnjs.cloudflare.com | Cloudflare Inc | US | unknown |
2092 | chrome.exe | 216.58.207.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
2092 | chrome.exe | 143.204.101.38:443 | ws.sharethis.com | — | US | malicious |
2092 | chrome.exe | 143.204.101.96:80 | static.adzerk.net | — | US | unknown |
2092 | chrome.exe | 172.217.23.142:443 | clients1.google.com | Google Inc. | US | whitelisted |
2092 | chrome.exe | 54.243.177.29:80 | e-2072.adzerk.net | Amazon.com, Inc. | US | unknown |
2092 | chrome.exe | 143.204.101.74:443 | c.sharethis.mgr.consensu.org | — | US | whitelisted |
2092 | chrome.exe | 104.111.218.17:443 | t.sharethis.com | Akamai International B.V. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
codeverge.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
cdnjs.cloudflare.com |
| whitelisted |
w.topage.net |
| unknown |
ajax.googleapis.com |
| whitelisted |
w.sharethis.com |
| shared |
king.sslproviders.net |
| whitelisted |
ws.sharethis.com |
| shared |
static.getclicky.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | A Network Trojan was detected | ET WEB_CLIENT Observed DNS Query to Malicious Cookie Monster Roulette JS Cookie Stealer Exfil Domain |