| File name: | 1U1BU_Donotrunme.bat |
| Full analysis: | https://app.any.run/tasks/6c940876-a34a-47c7-b44a-8ba336aa90d7 |
| Verdict: | Malicious activity |
| Analysis date: | December 13, 2024, 21:55:31 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with CRLF line terminators |
| MD5: | A4E4B7B3C75C041658836CE71010E43C |
| SHA1: | 3B71D1E219BDE2F97D131592FE6CB3364850FB0A |
| SHA256: | 92B6A564FDF9E056D3EA53E7FFAB933A3E2610CC4B0F5F5BD72A345908C0C3DF |
| SSDEEP: | 48:2Im3l9/LDwU/JIDnmfj8OJY+37B2TlC3RrqjZFFUxdi0bYDXMwuv7wrPxxAmGS:aLEUJIDK8OYG74Ikj1qTw1uS |
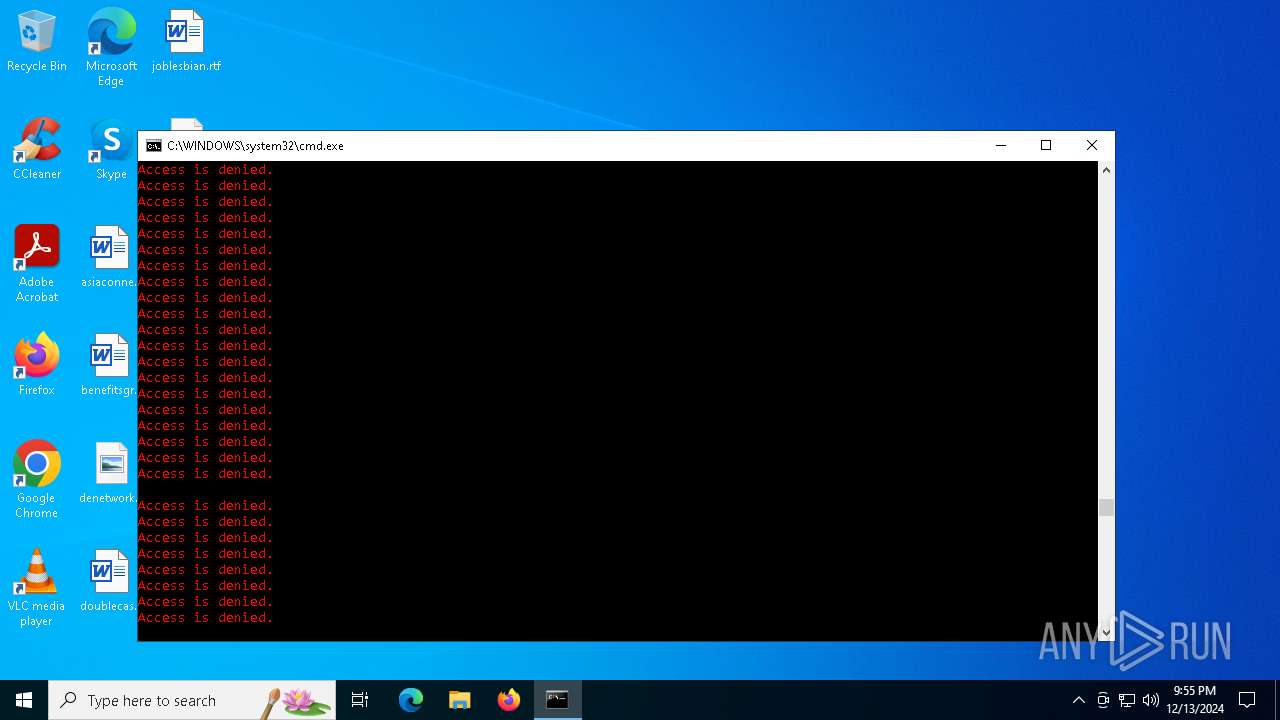
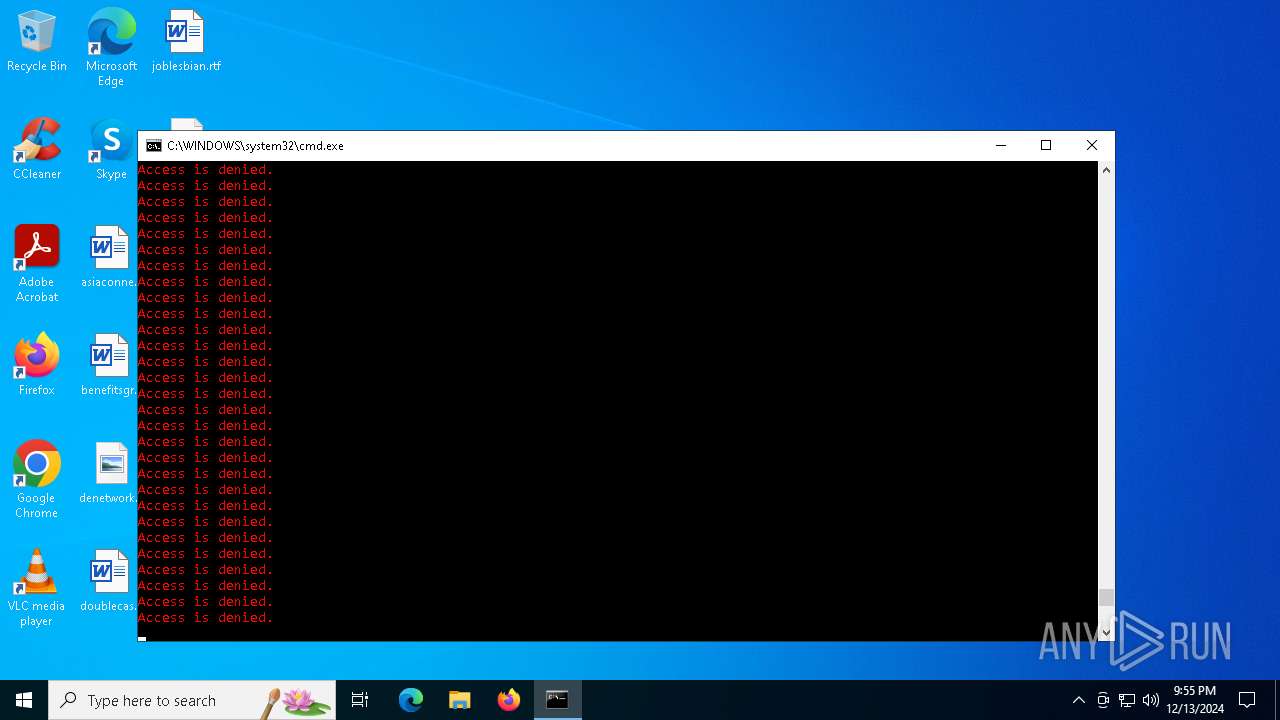
MALICIOUS
Deletes shadow copies
- cmd.exe (PID: 3612)
Create files in the Startup directory
- cmd.exe (PID: 3612)
SUSPICIOUS
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 3612)
Application launched itself
- cmd.exe (PID: 3612)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 3612)
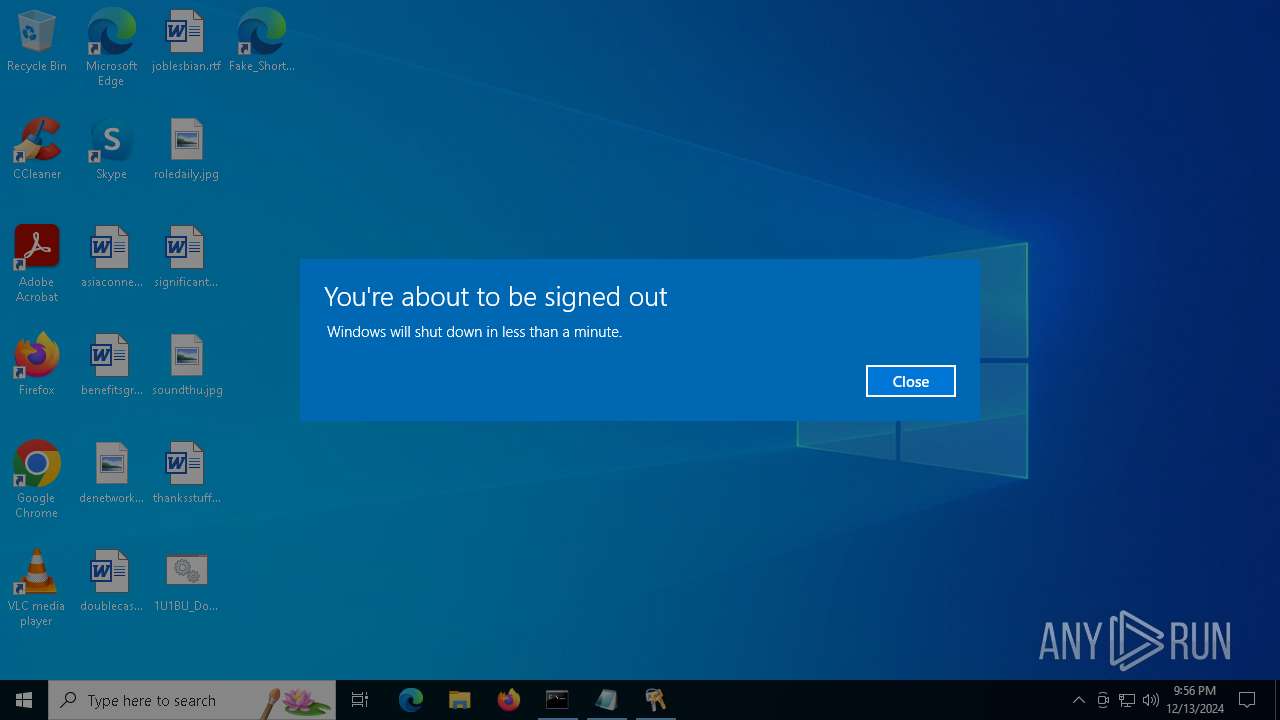
The system shut down or reboot
- cmd.exe (PID: 3612)
Uses NETSH.EXE to change the status of the firewall
- cmd.exe (PID: 3612)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 3612)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
164
Monitored processes
46
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
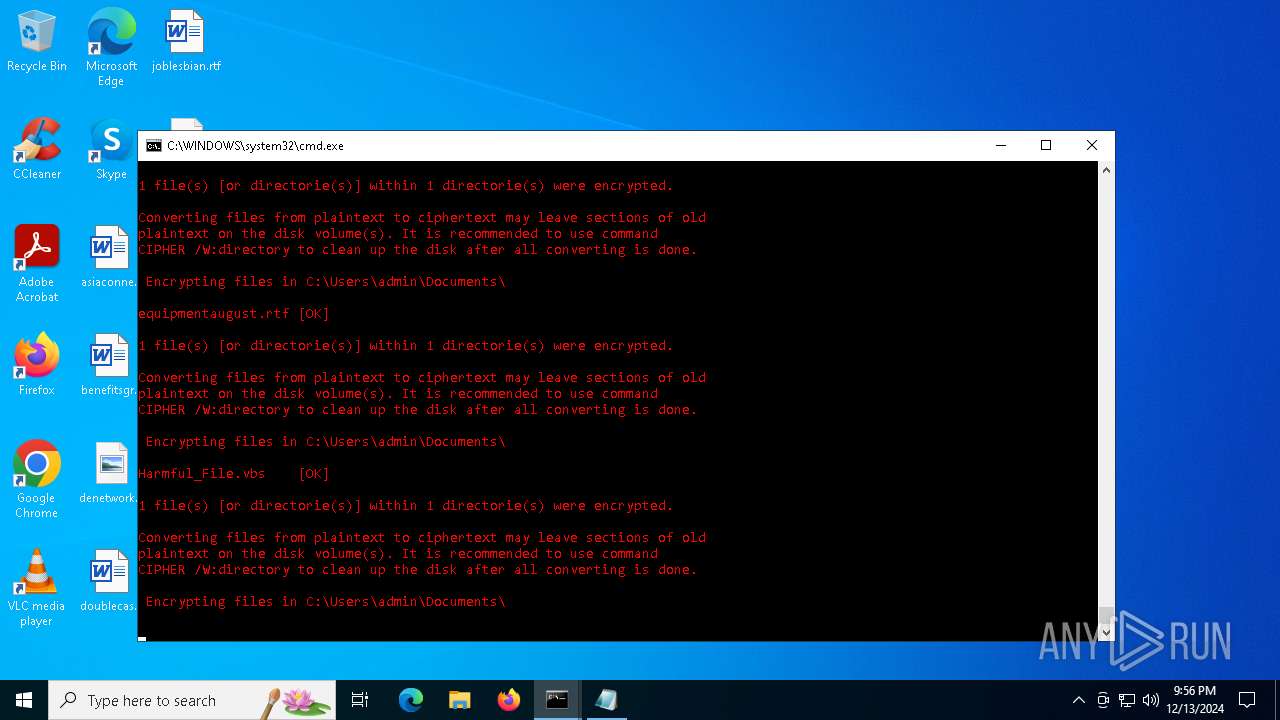
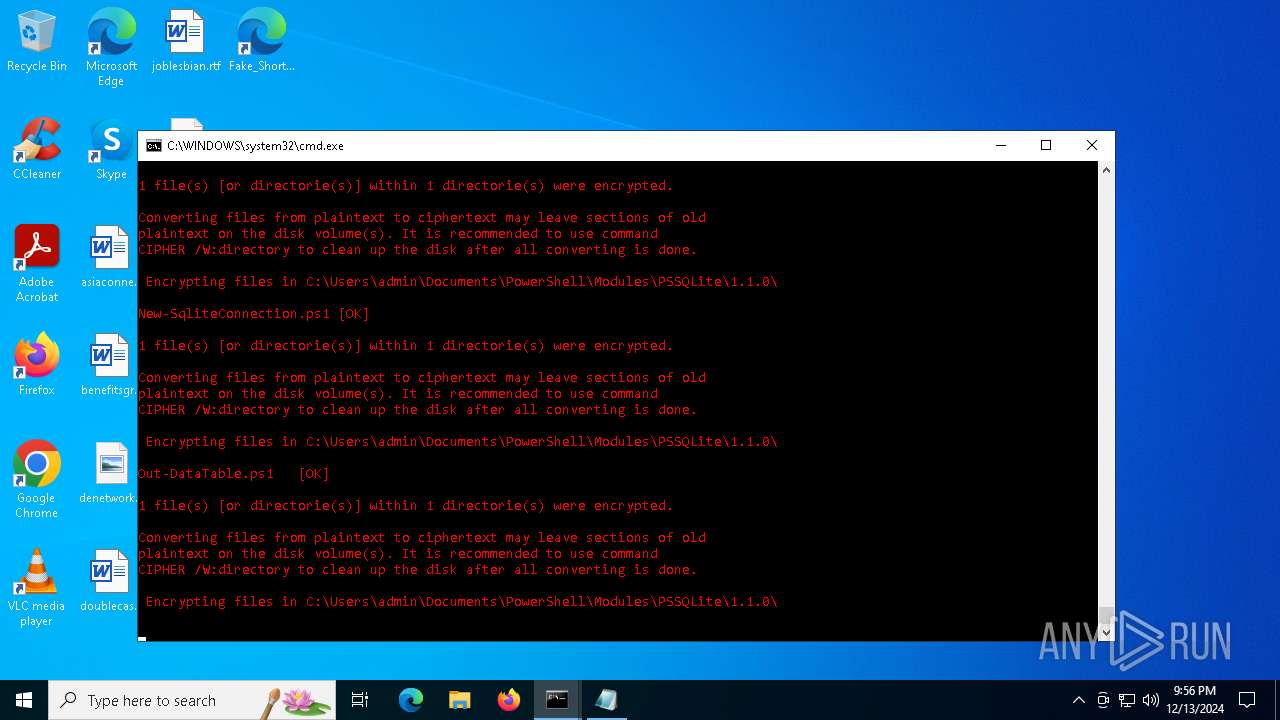
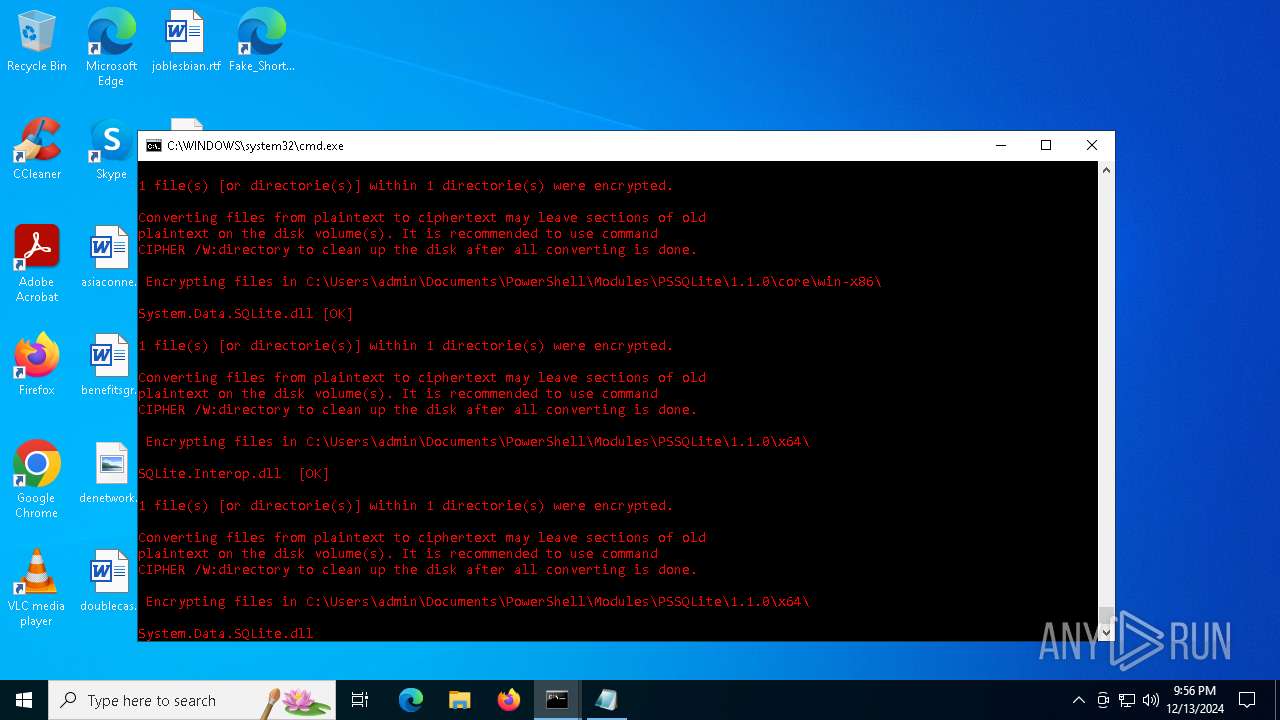
| 244 | cipher /e "C:\Users\admin\Documents\PowerShell\Modules\PSSQLite\1.1.0\x64\SQLite.Interop.dll" | C:\Windows\System32\cipher.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: File Encryption Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 444 | C:\WINDOWS\system32\cmd.exe /S /D /c" echo Y " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 540 | cipher /e "C:\Users\admin\Documents\PowerShell\Modules\PSSQLite\1.1.0\Invoke-SqliteBulkCopy.ps1" | C:\Windows\System32\cipher.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: File Encryption Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 556 | cipher /e "C:\Users\admin\Documents\PowerShell\Modules\PSSQLite\1.1.0\Out-DataTable.ps1" | C:\Windows\System32\cipher.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: File Encryption Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 628 | cipher /e "C:\Users\admin\Documents\PowerShell\Modules\PSSQLite\1.1.0\core\win-x86\SQLite.Interop.dll" | C:\Windows\System32\cipher.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: File Encryption Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 644 | cipher /e "C:\Users\admin\Documents\PowerShell\Modules\PSSQLite\1.1.0\x86\SQLite.Interop.dll" | C:\Windows\System32\cipher.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: File Encryption Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 716 | cipher /e "C:\Users\admin\Documents\PowerShell\Modules\PSSQLite\1.1.0\core\win-x64\System.Data.SQLite.dll" | C:\Windows\System32\cipher.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: File Encryption Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1224 | cipher /e "C:\Users\admin\Documents\PowerShell\Modules\PSSQLite\1.1.0\x64\System.Data.SQLite.dll" | C:\Windows\System32\cipher.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: File Encryption Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1512 | cipher /e "C:\Users\admin\Documents\PowerShell\Modules\PSSQLite\1.1.0\core\osx-x64\SQLite.Interop.dll" | C:\Windows\System32\cipher.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: File Encryption Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1556 | cipher /e "C:\Users\admin\Documents\PowerShell\Modules\PSSQLite\1.1.0\core\linux-x64\System.Data.SQLite.dll" | C:\Windows\System32\cipher.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: File Encryption Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 375
Read events
1 374
Write events
1
Delete events
0
Modification events
| (PID) Process: | (2440) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MaliciousProgram |
Value: C:\Users\admin\AppData\Roaming\hidden_process.bat | |||
Executable files
1
Suspicious files
0
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3612 | cmd.exe | C:\Users\admin\Desktop\Fake_Shortcut.url | text | |
MD5:6B2ACB5DA930B408E1ADD6D7B794EAD7 | SHA256:98A1D62E94AEDDCF26A30D0B356B0B48DFDFF0A09FFF298E716F789070BE2479 | |||
| 3612 | cmd.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\malicious_script.bat | text | |
MD5:A4E4B7B3C75C041658836CE71010E43C | SHA256:92B6A564FDF9E056D3EA53E7FFAB933A3E2610CC4B0F5F5BD72A345908C0C3DF | |||
| 3612 | cmd.exe | C:\Users\admin\Documents\Harmful_File.vbs | text | |
MD5:8777F010746D4DF021E355EF9C68B651 | SHA256:0F8B8991AD0AA4030619A349B0BC48D1DB802C9B6091A5F403B379B4C7BB49D0 | |||
| 3612 | cmd.exe | C:\Users\admin\AppData\Roaming\hidden_process.bat | text | |
MD5:73BF5980F27931716AFD01764EBDE901 | SHA256:57D3A94BAAB67674EAD66C967EE24BD2F6C0435E541CBE2955F69700B9138597 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
22
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.32.238.153:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2624 | svchost.exe | GET | 200 | 23.32.238.153:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2624 | svchost.exe | GET | 200 | 23.215.121.133:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.215.121.133:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 204 | 2.19.80.27:443 | https://www.bing.com/threshold/xls.aspx | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2624 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2624 | svchost.exe | 23.32.238.153:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.32.238.153:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2624 | svchost.exe | 23.215.121.133:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.215.121.133:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3976 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |