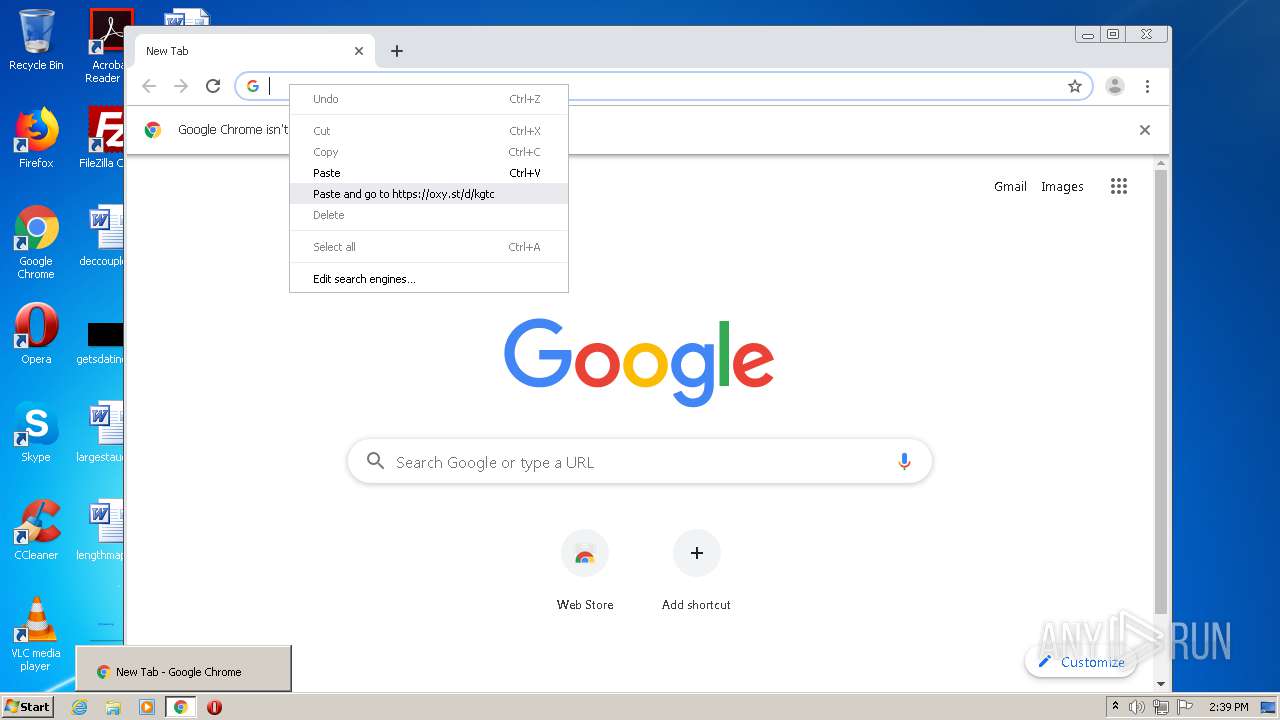
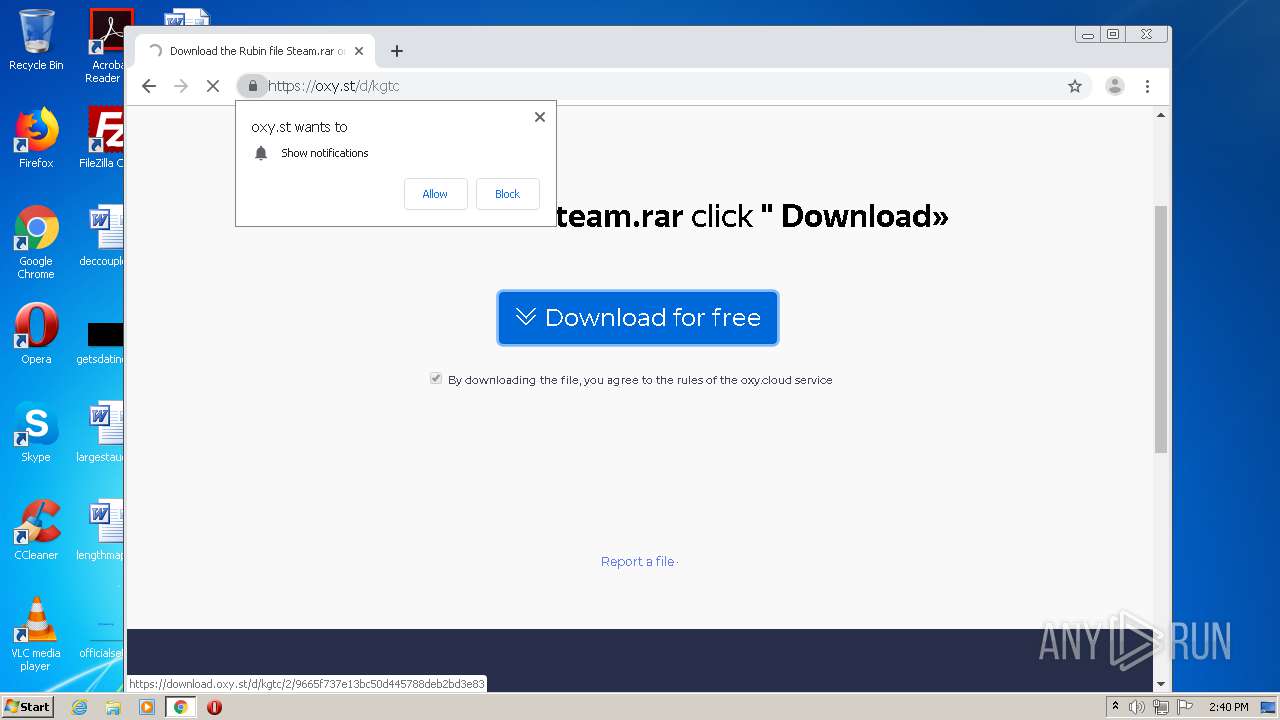
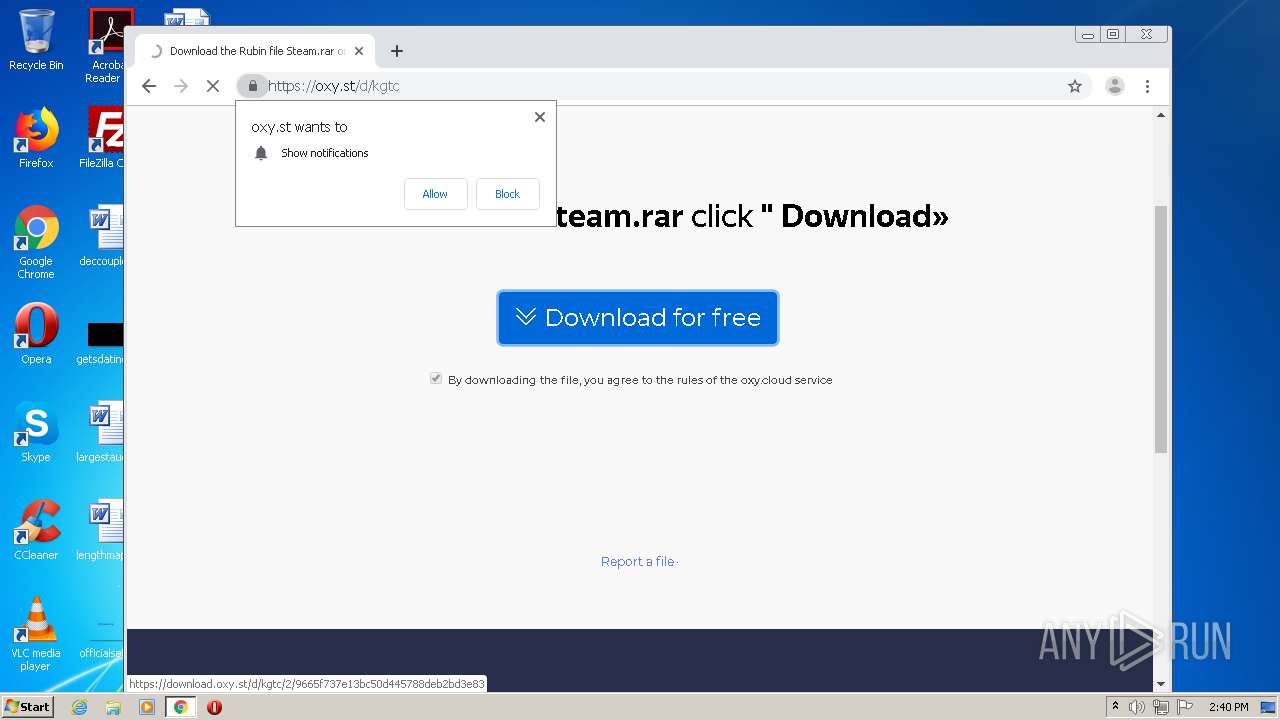
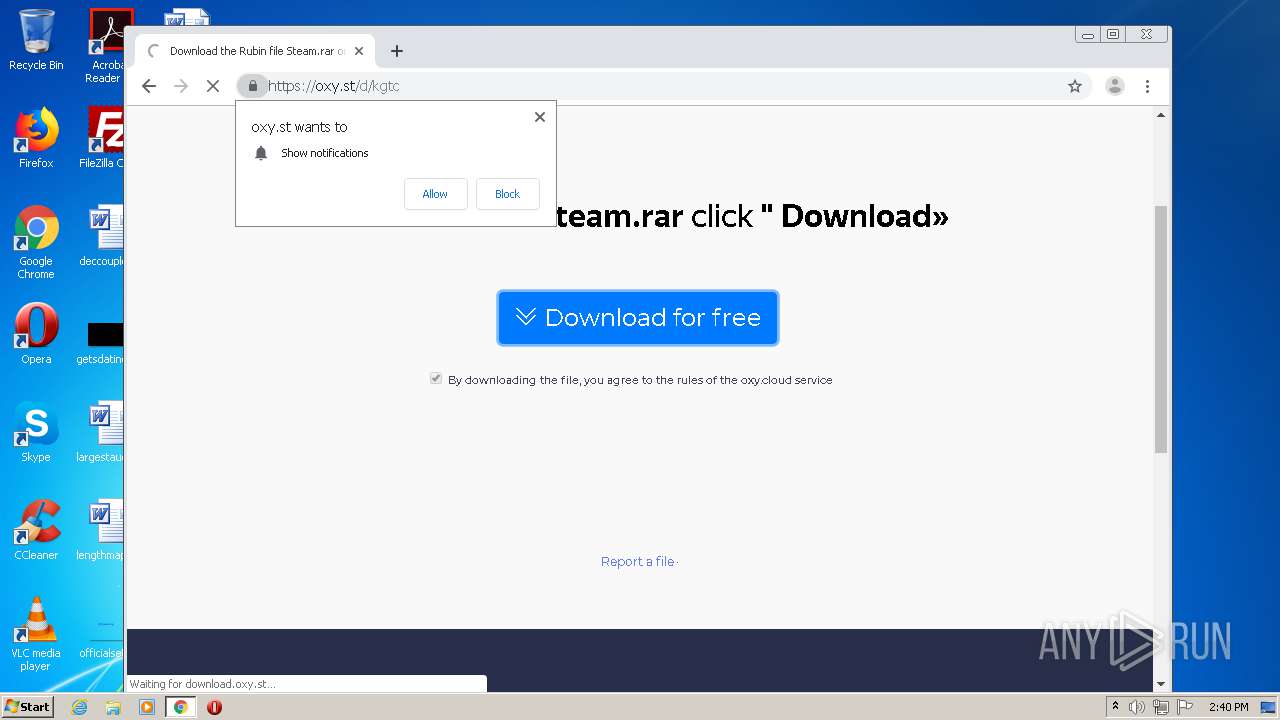
| download: | kgtc |
| Full analysis: | https://app.any.run/tasks/4534116c-ba90-4bc9-a045-ee03a0750327 |
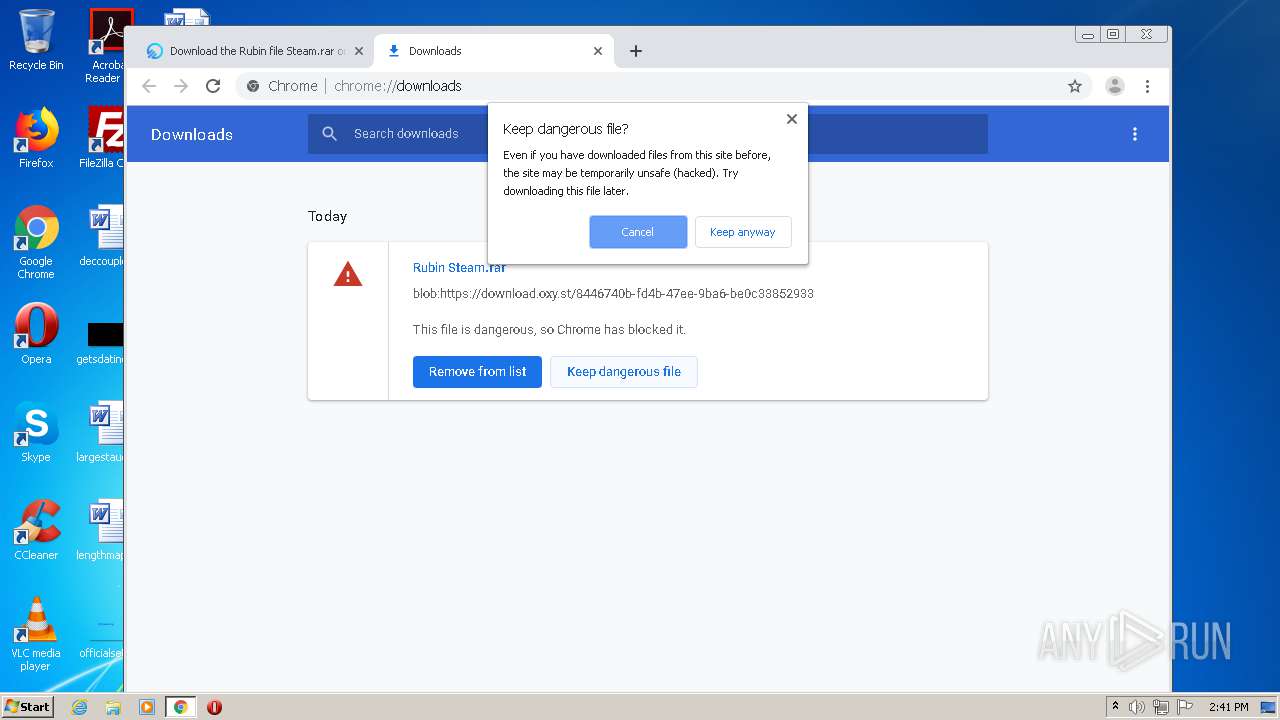
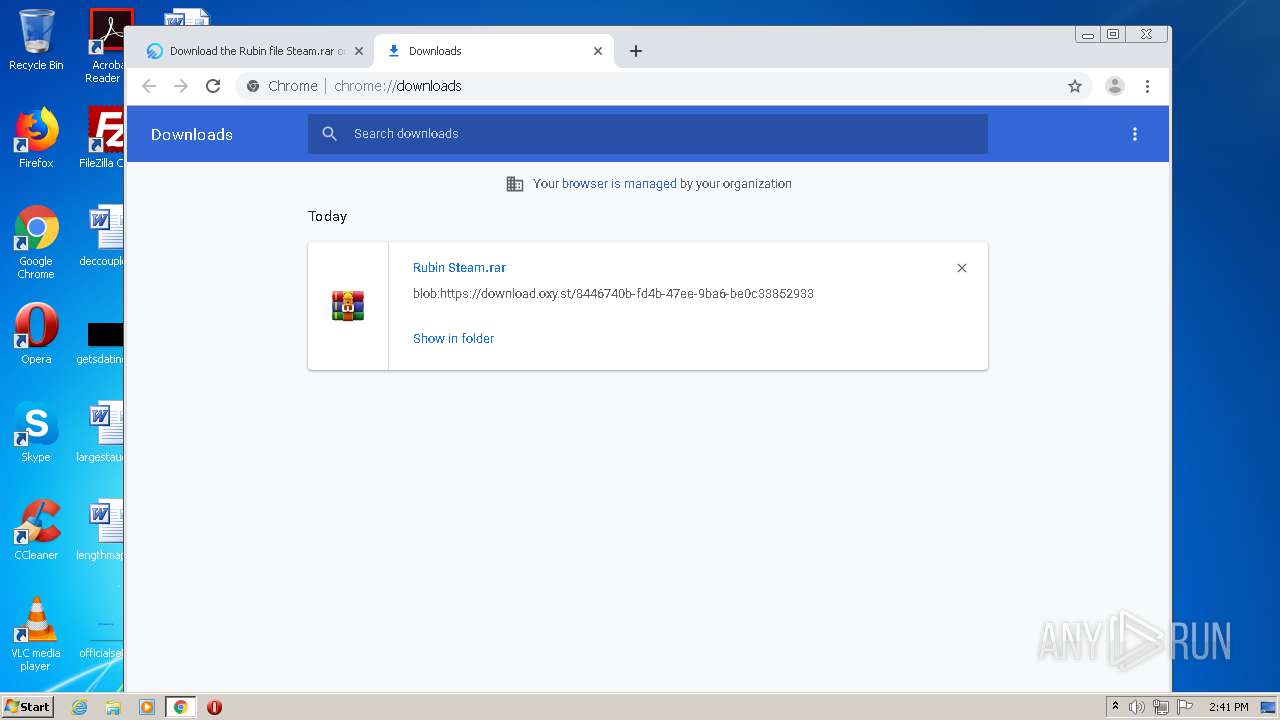
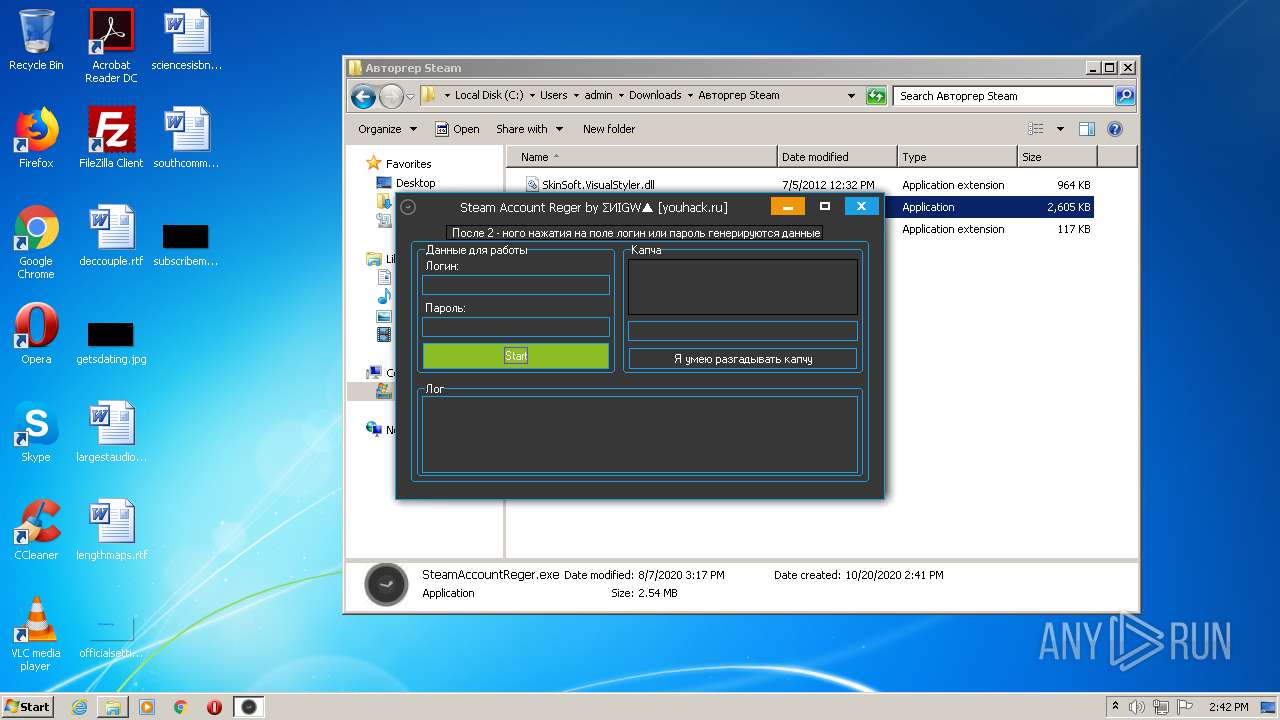
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
| Analysis date: | October 20, 2020, 13:39:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
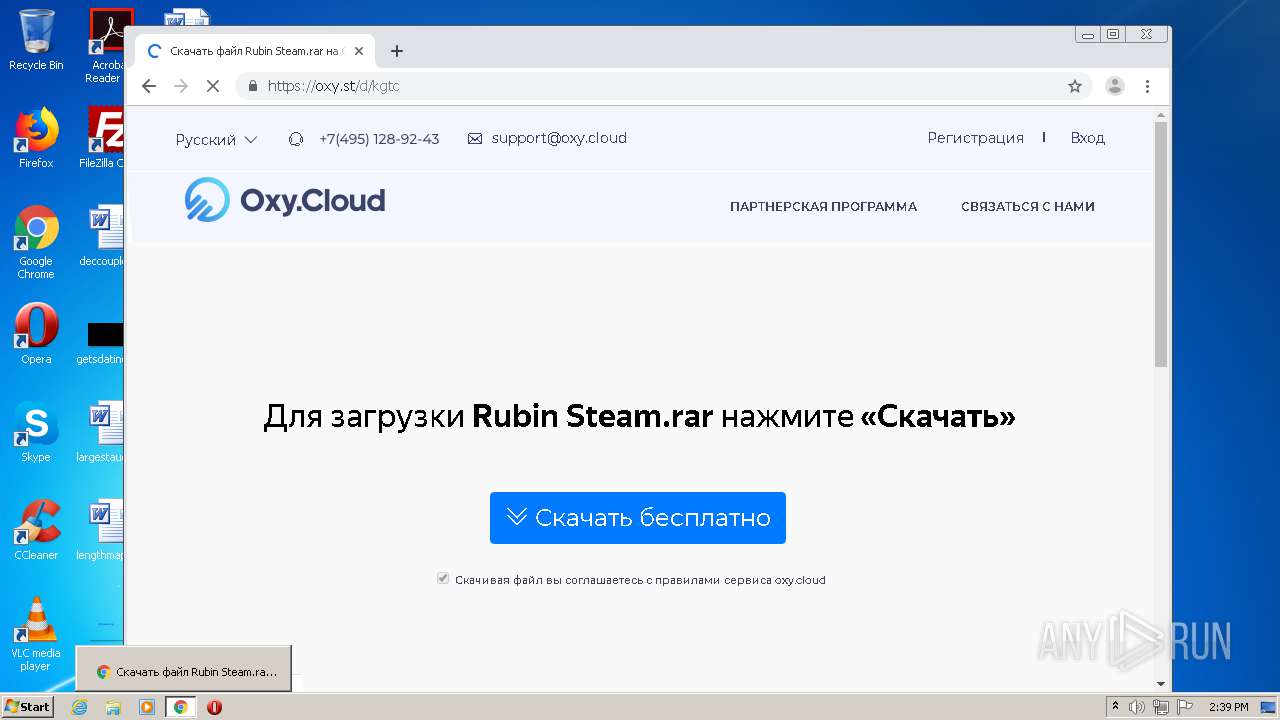
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines |
| MD5: | F560974B46C589303F62A6182F7D85AB |
| SHA1: | F0BAE118F86B0D2A67C76EF9CDDDB3CBD56ABDF4 |
| SHA256: | 92A4751E363452F9221558B4ACE46A30CC3A9CCE9D7295B3A69415D54A1A685B |
| SSDEEP: | 1536:IBHXereGT8R+7pRJTXErAGl3Npu2X1fhd+N4xMhwNXbwMpQGDZmMu1Wv:2tNpLXdhd+Nf6NXbwMpQGDZmMu1Wv |
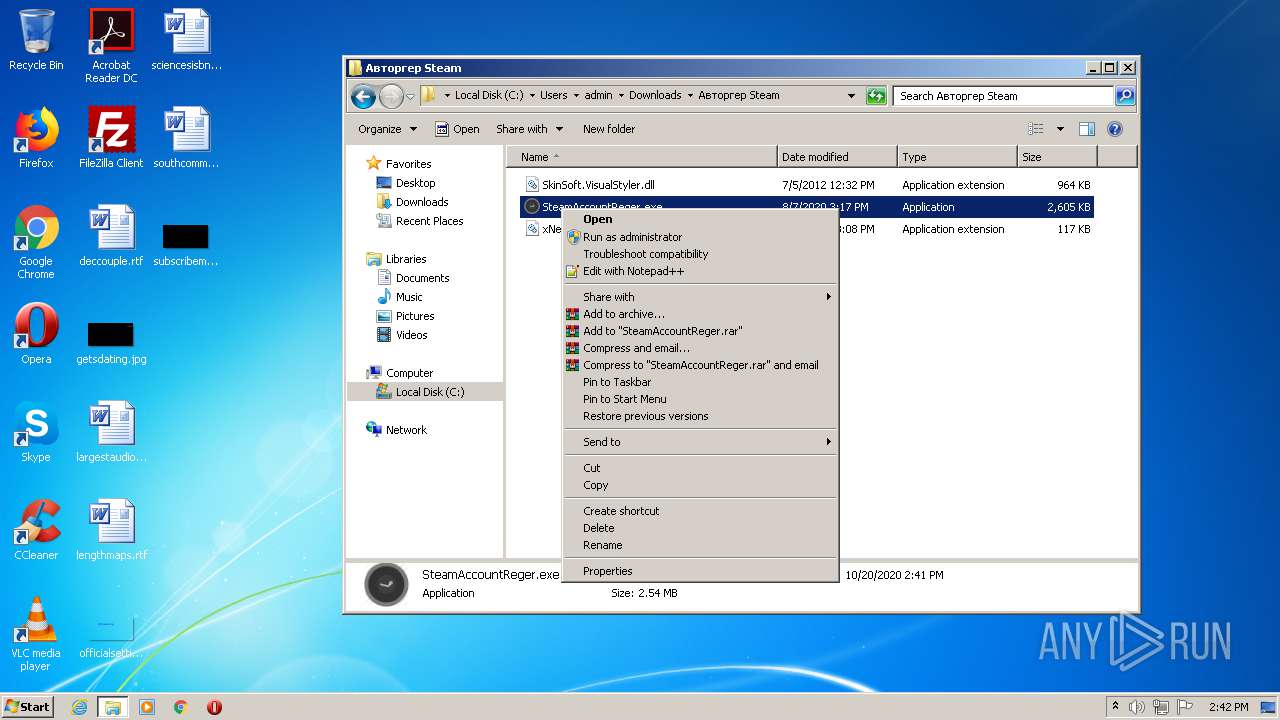
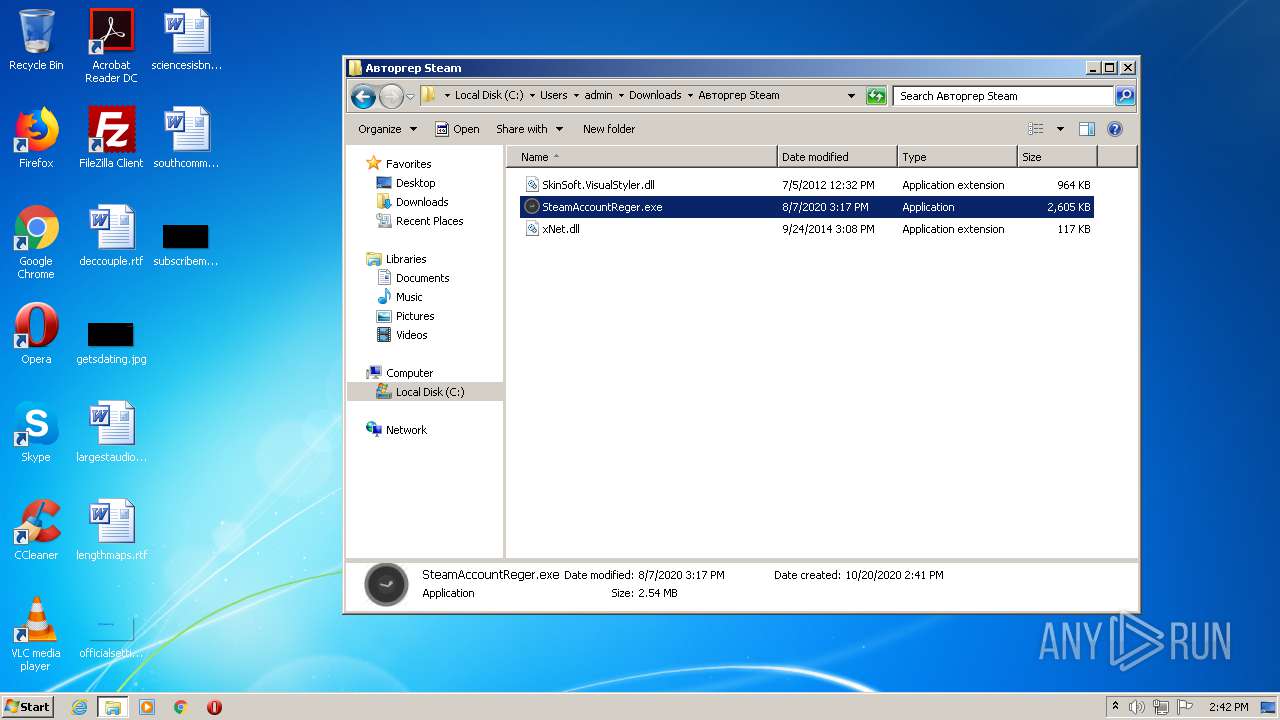
MALICIOUS
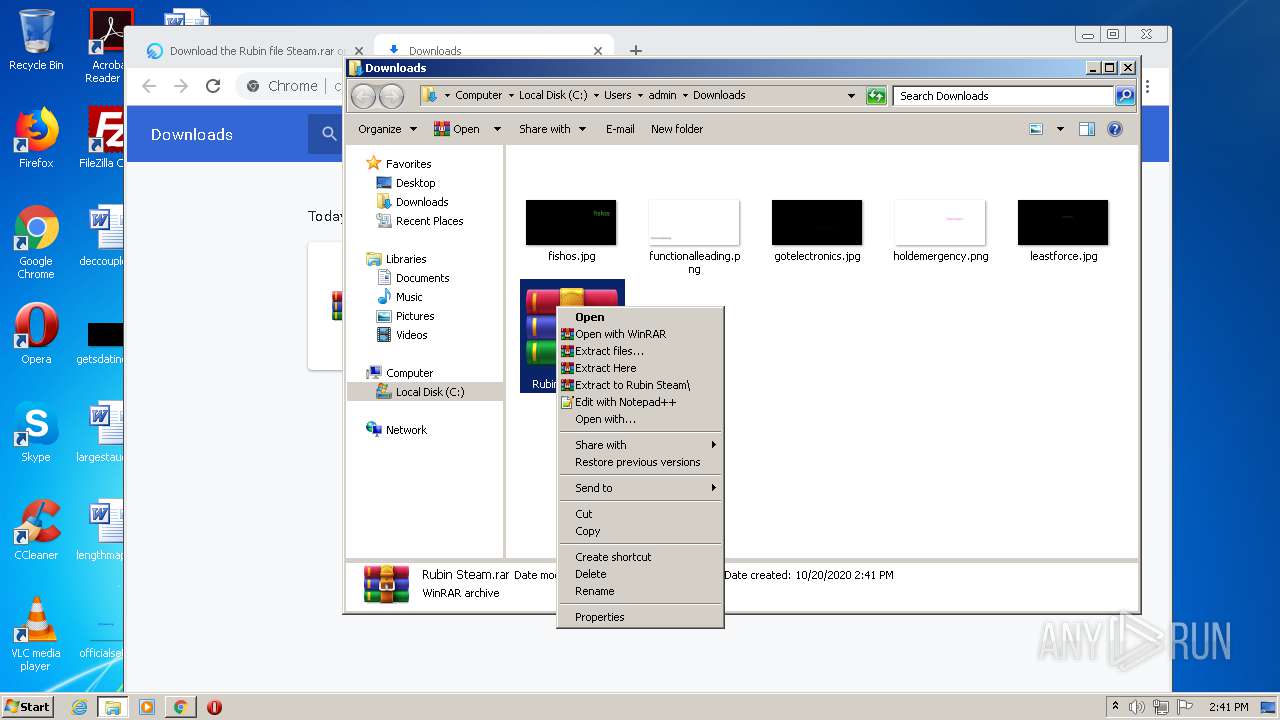
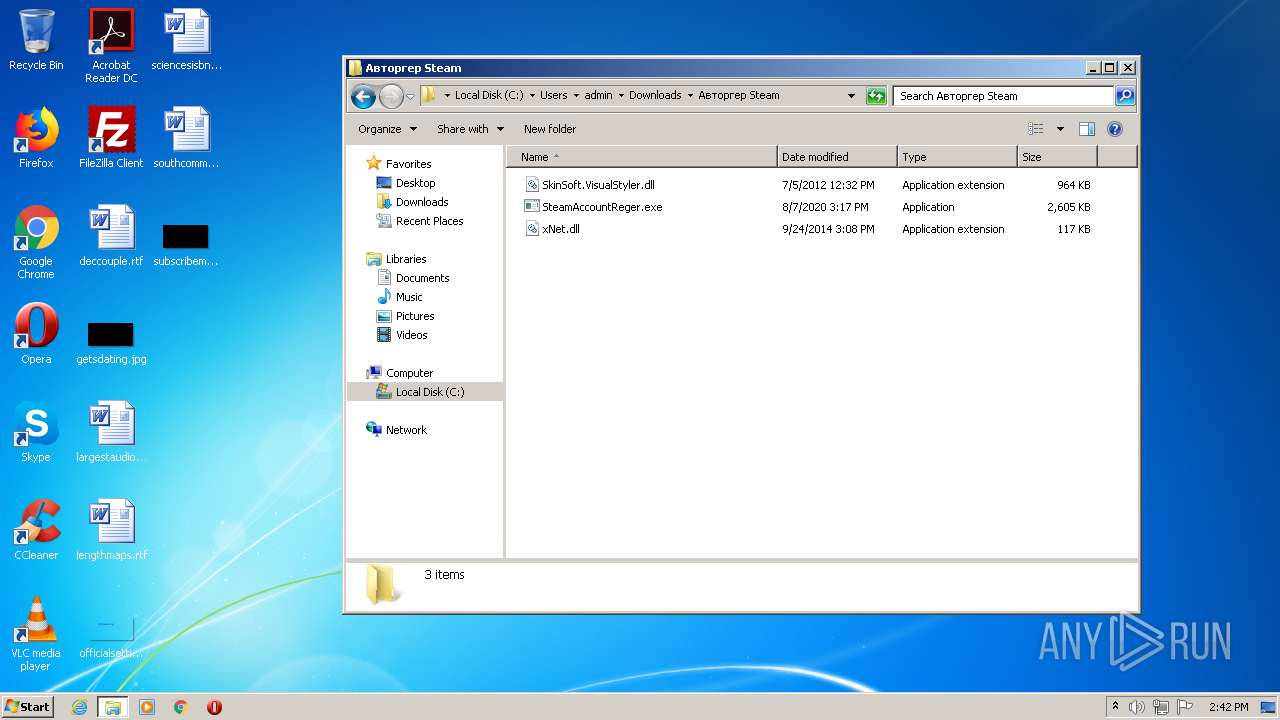
Application was dropped or rewritten from another process
- SteamAccountReger.exe (PID: 2708)
- SteamAccountReger.exe (PID: 2812)
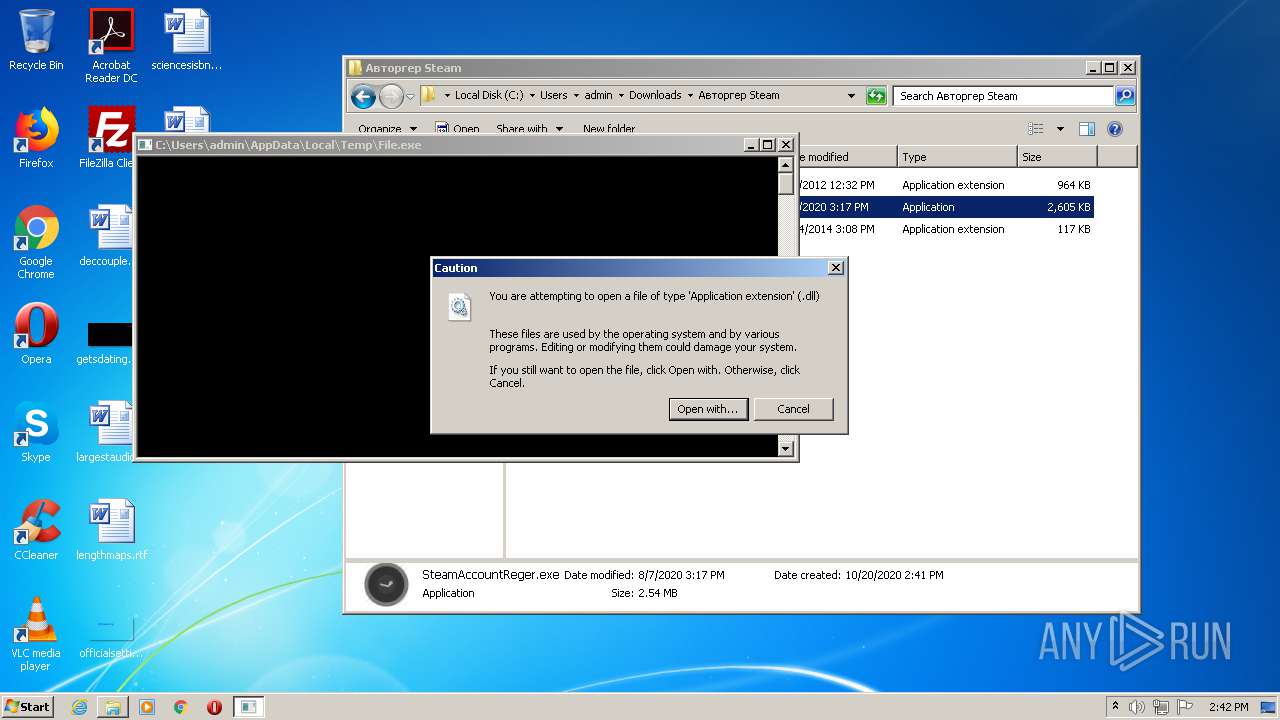
- File.exe (PID: 804)
Loads dropped or rewritten executable
- SteamAccountReger.exe (PID: 2812)
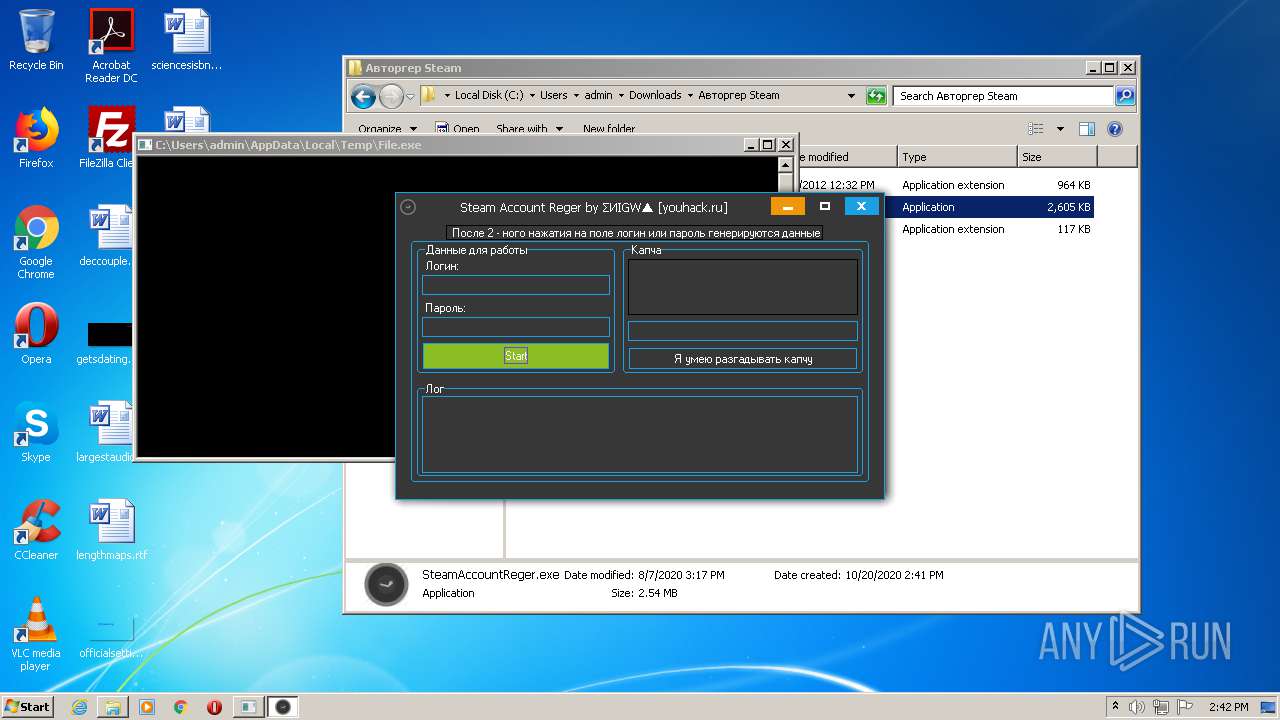
Stealing of credential data
- File.exe (PID: 804)
Actions looks like stealing of personal data
- File.exe (PID: 804)
SUSPICIOUS
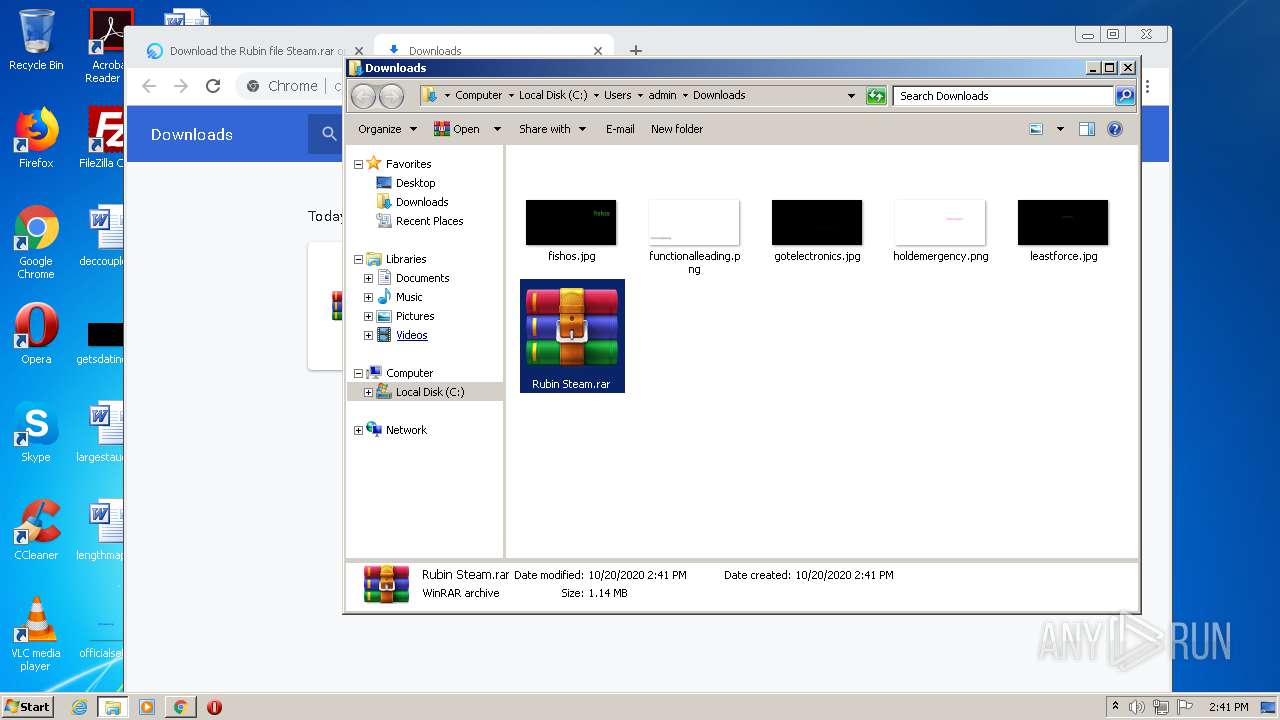
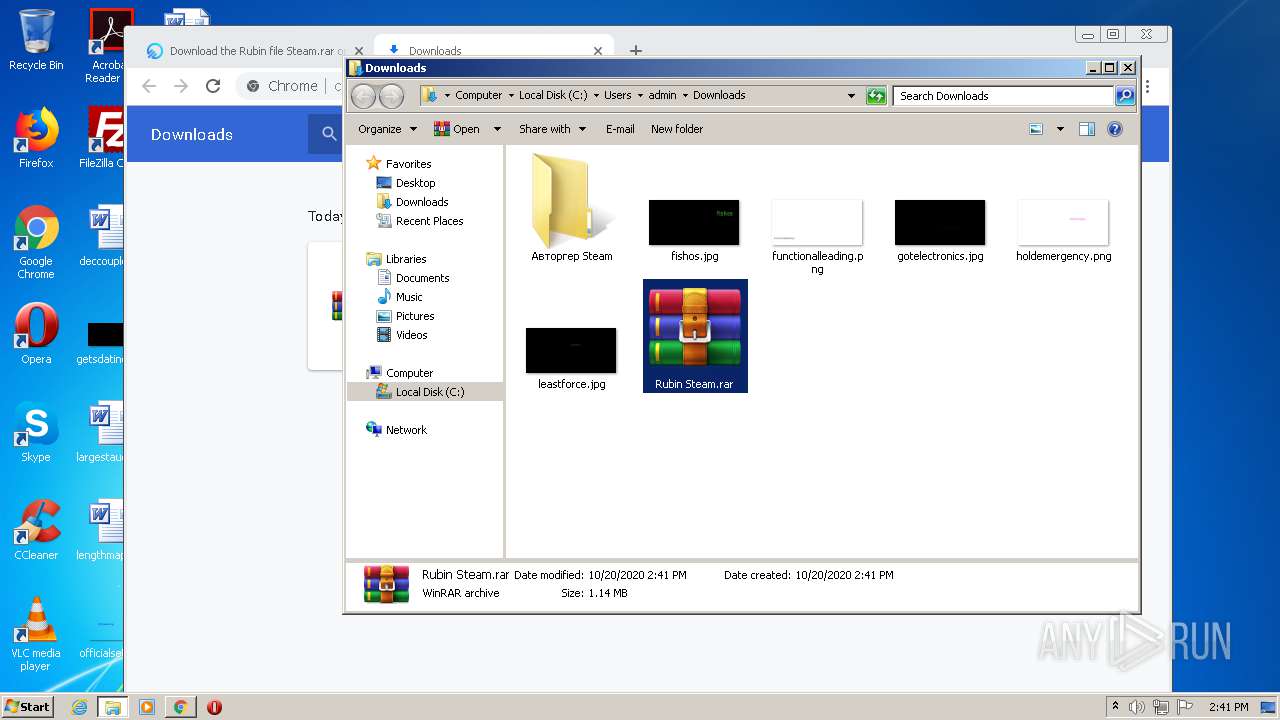
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4028)
- SteamAccountReger.exe (PID: 2708)
- SteamAccountReger.exe (PID: 2812)
Uses RUNDLL32.EXE to load library
- SteamAccountReger.exe (PID: 2708)
Reads Environment values
- File.exe (PID: 804)
Creates files in the user directory
- File.exe (PID: 804)
Starts CMD.EXE for commands execution
- File.exe (PID: 804)
Checks for external IP
- File.exe (PID: 804)
Reads the cookies of Mozilla Firefox
- File.exe (PID: 804)
Searches for installed software
- File.exe (PID: 804)
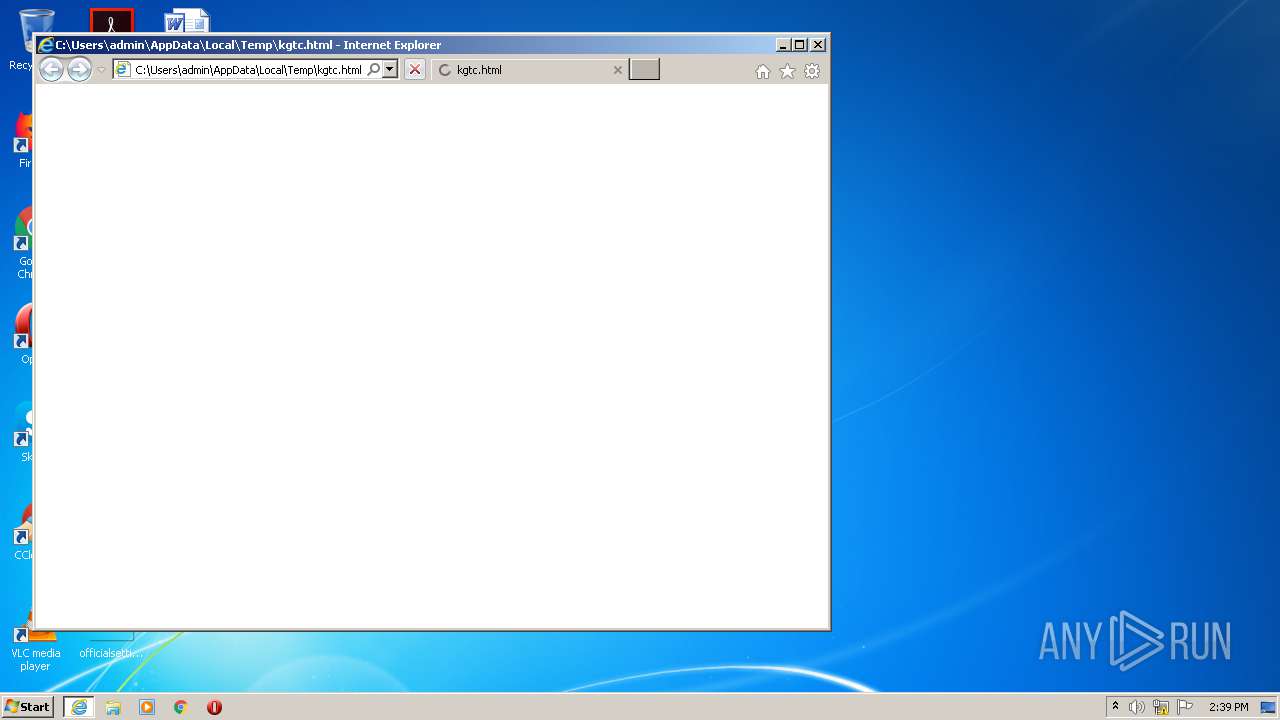
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 2516)
Application launched itself
- iexplore.exe (PID: 2516)
- chrome.exe (PID: 3080)
Changes settings of System certificates
- iexplore.exe (PID: 584)
Adds / modifies Windows certificates
- iexplore.exe (PID: 584)
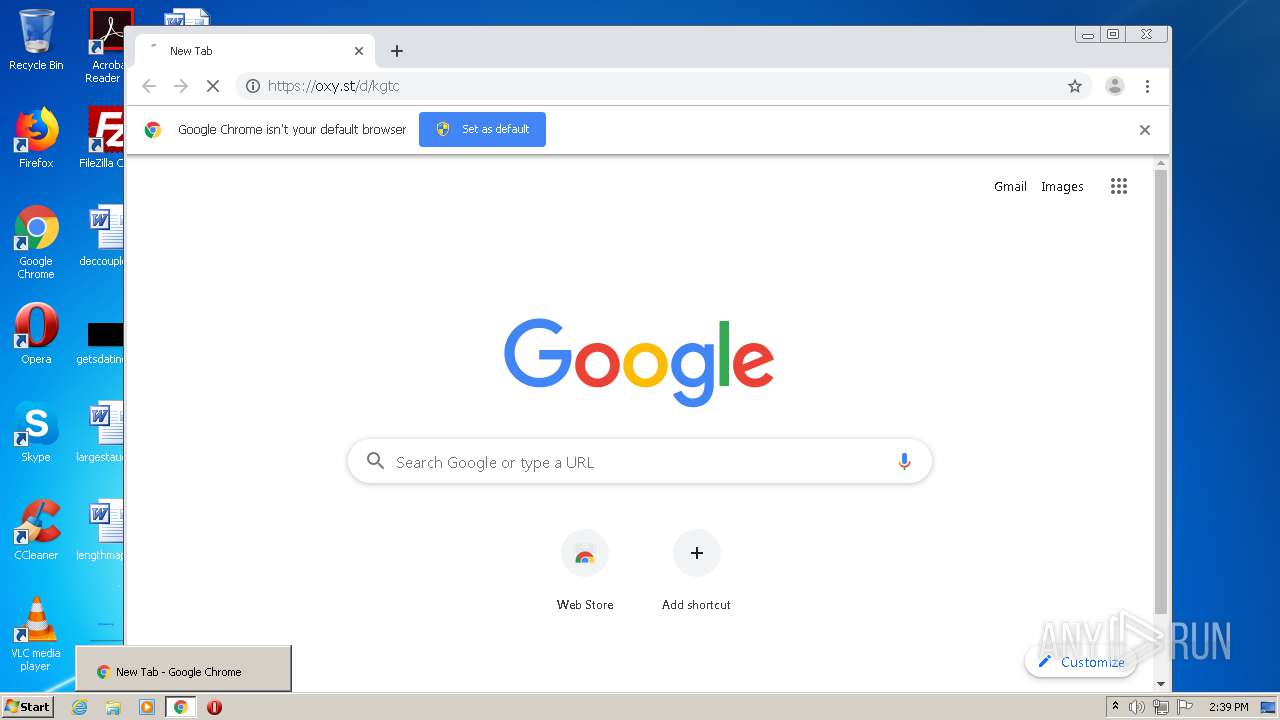
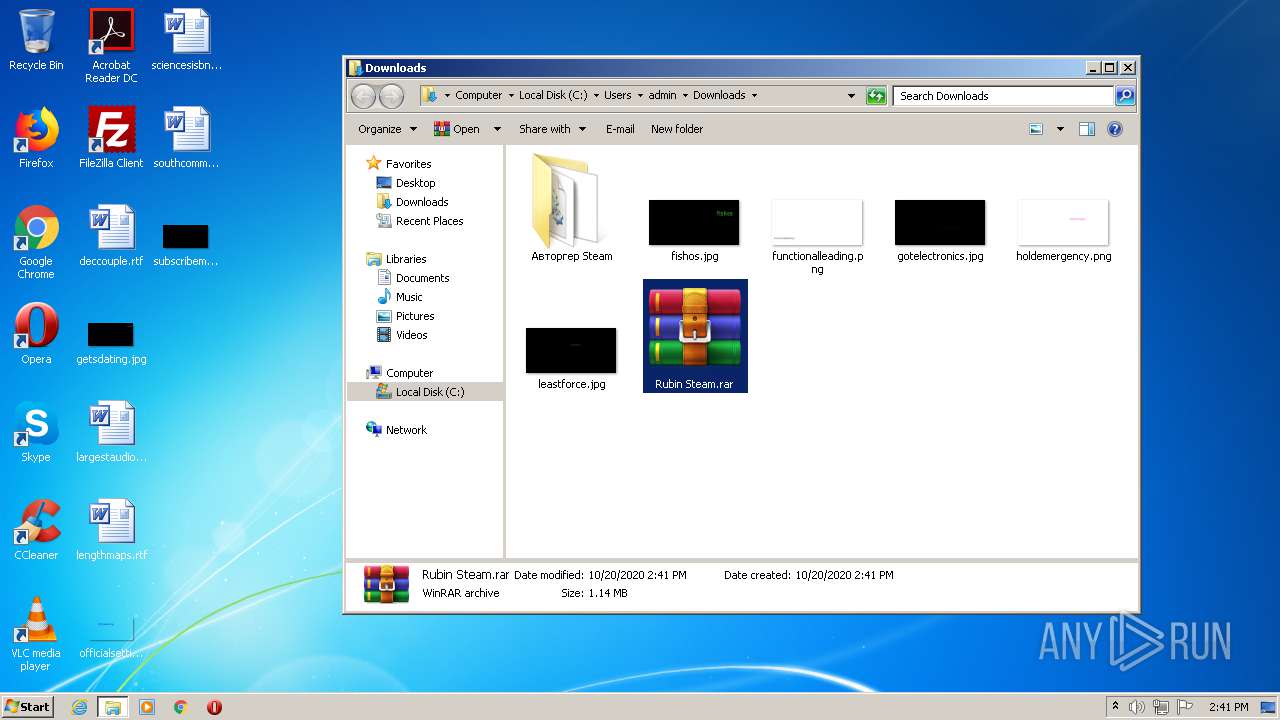
Manual execution by user
- chrome.exe (PID: 3080)
- SteamAccountReger.exe (PID: 2708)
- WinRAR.exe (PID: 4028)
Reads internet explorer settings
- iexplore.exe (PID: 584)
Reads the hosts file
- chrome.exe (PID: 3080)
- chrome.exe (PID: 3896)
Changes internet zones settings
- iexplore.exe (PID: 2516)
Reads settings of System Certificates
- chrome.exe (PID: 3896)
- File.exe (PID: 804)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
EXIF
HTML
| viewport: | width=device-width, initial-scale=1, shrink-to-fit=no |
|---|---|
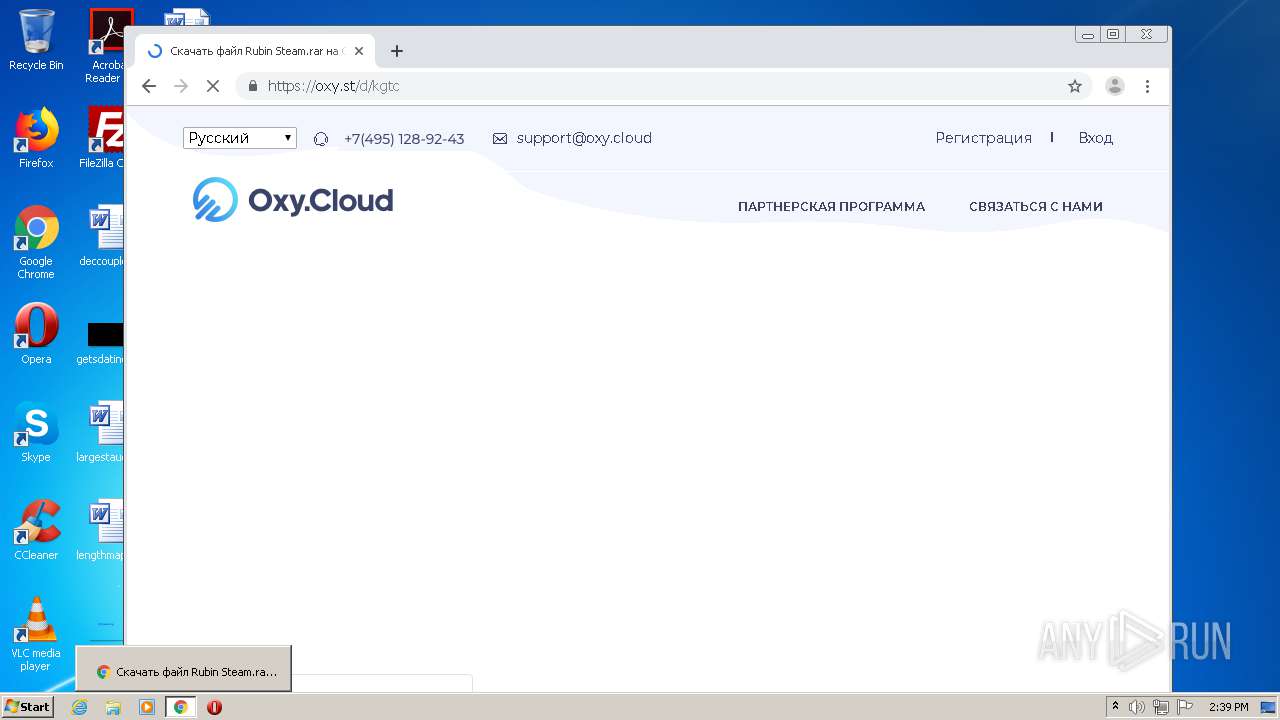
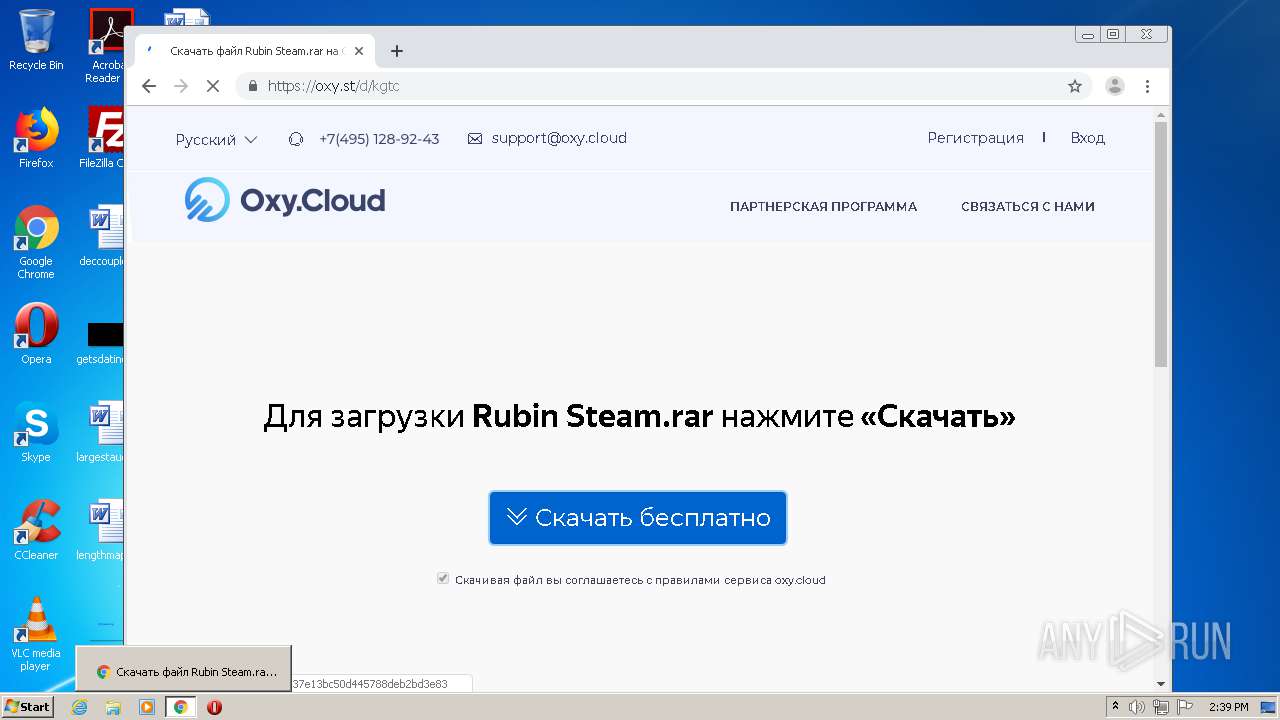
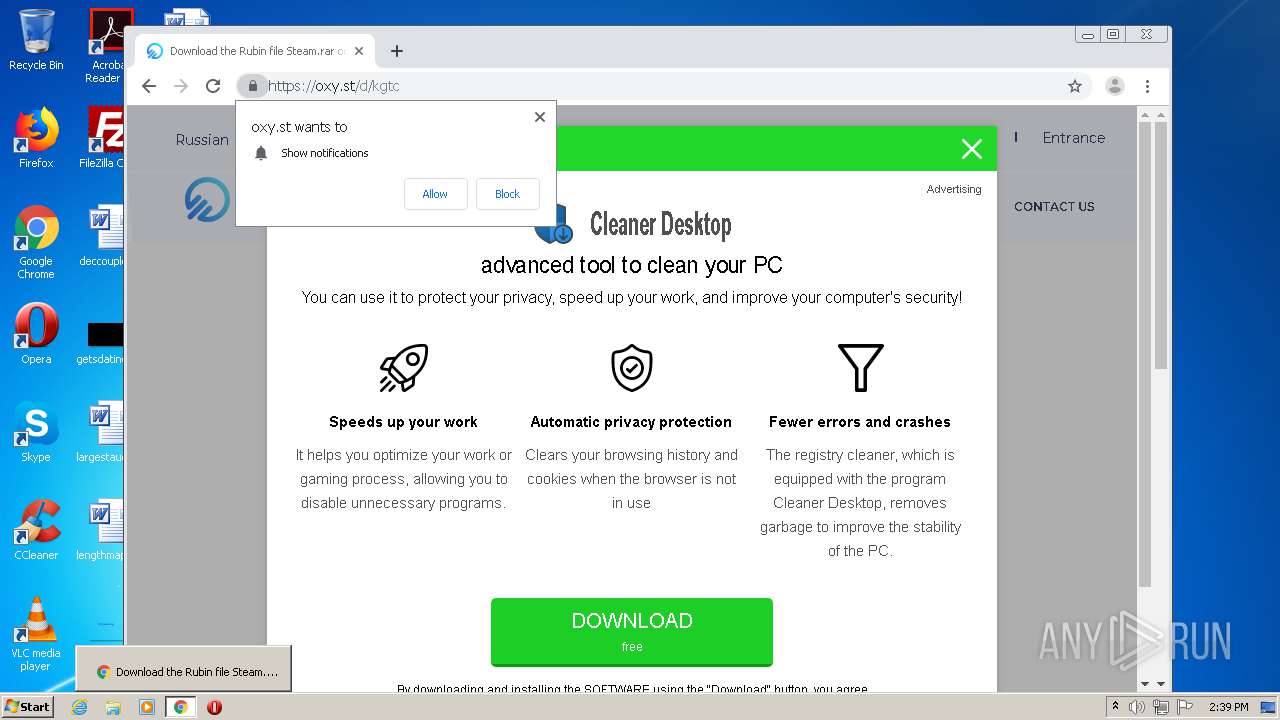
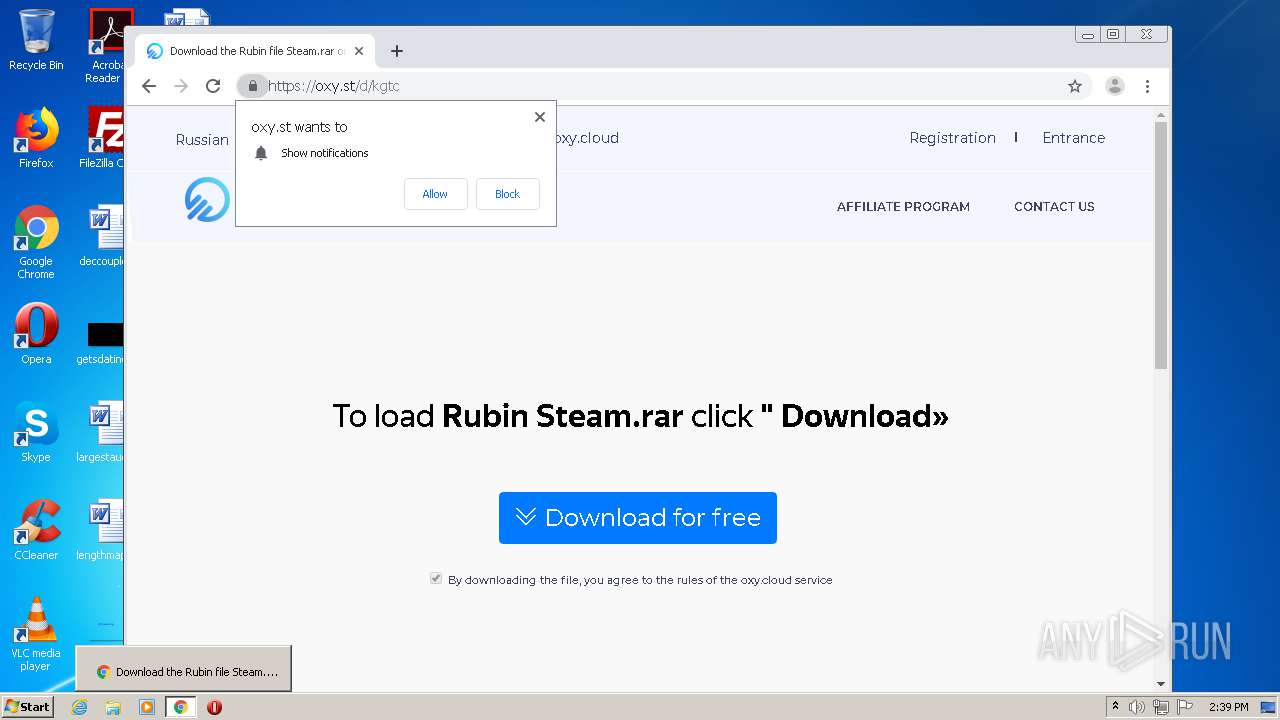
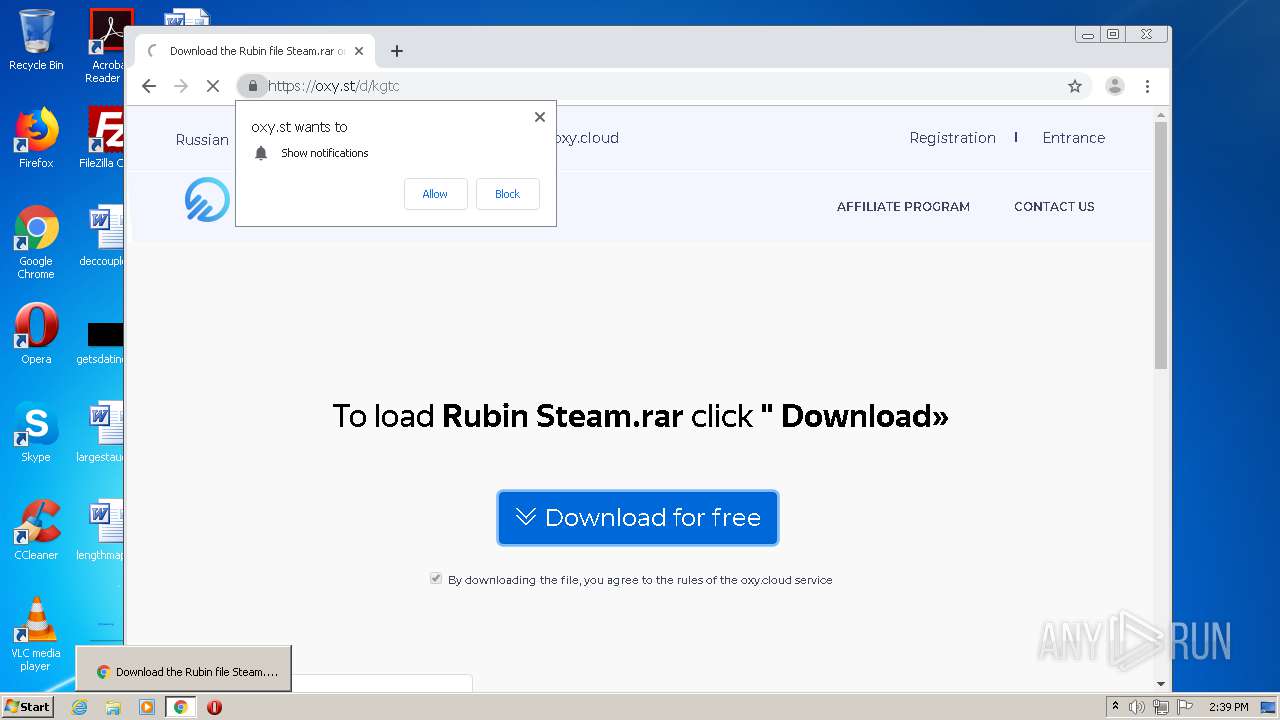
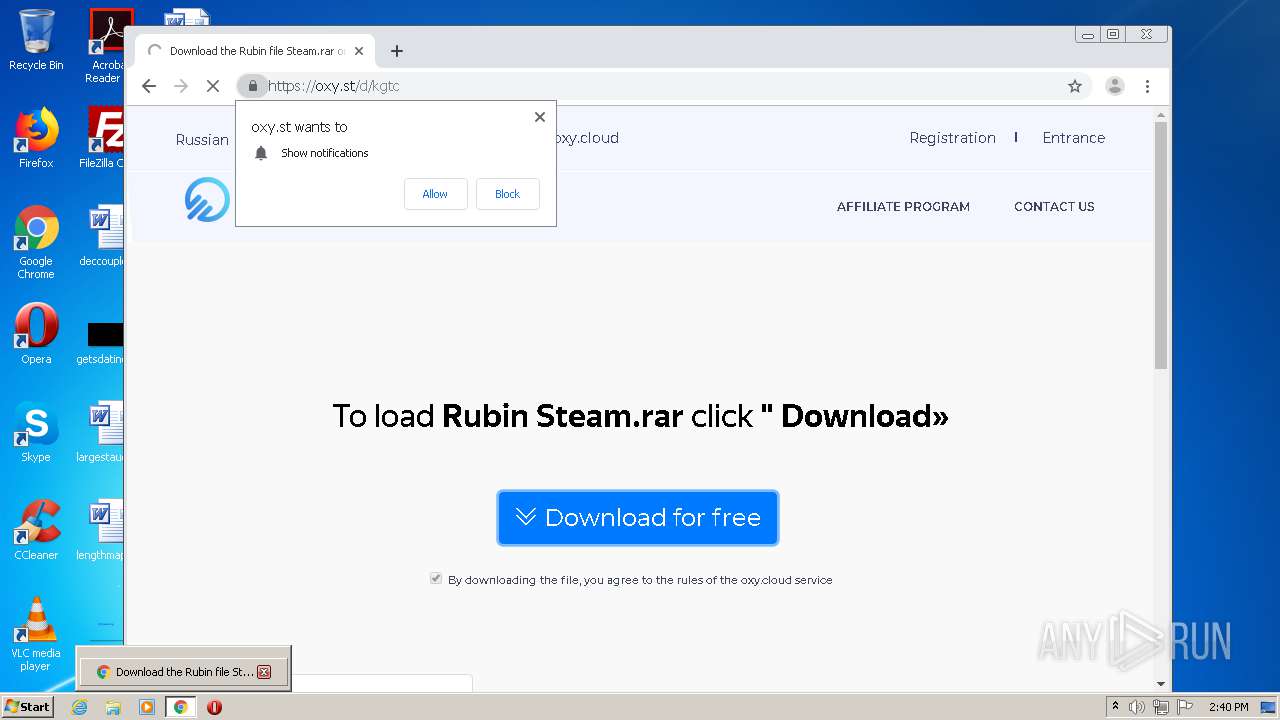
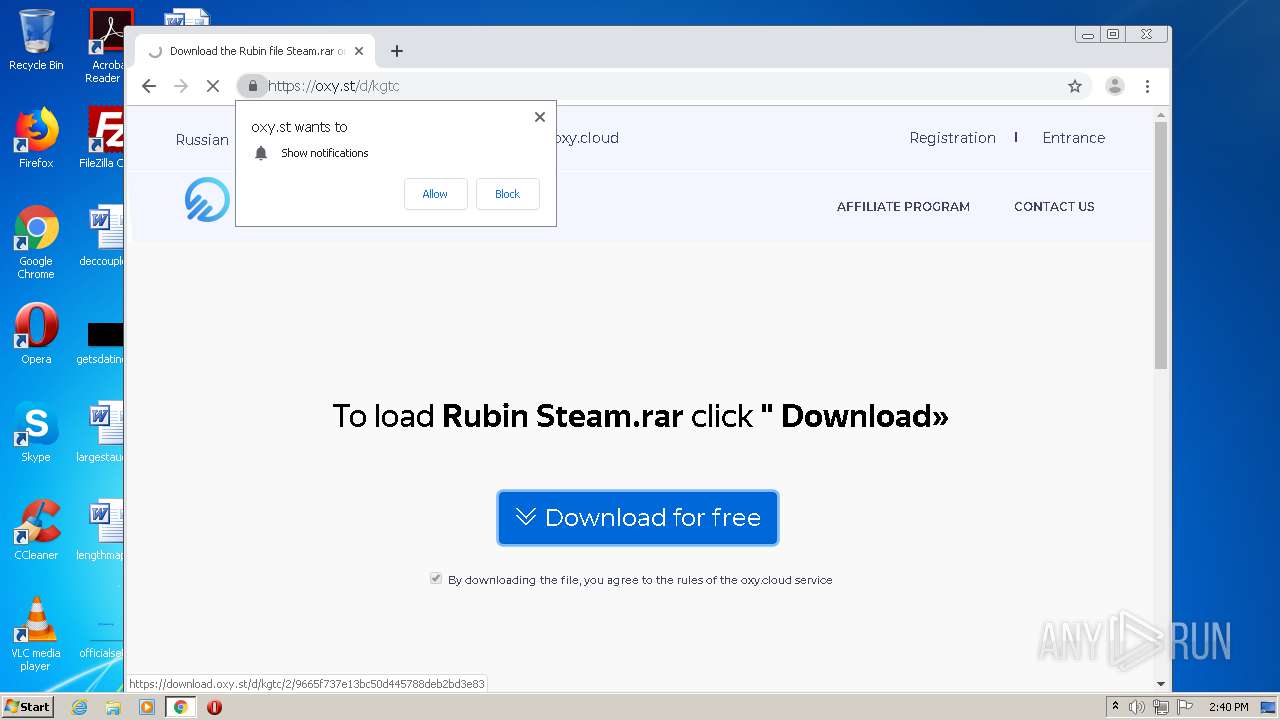
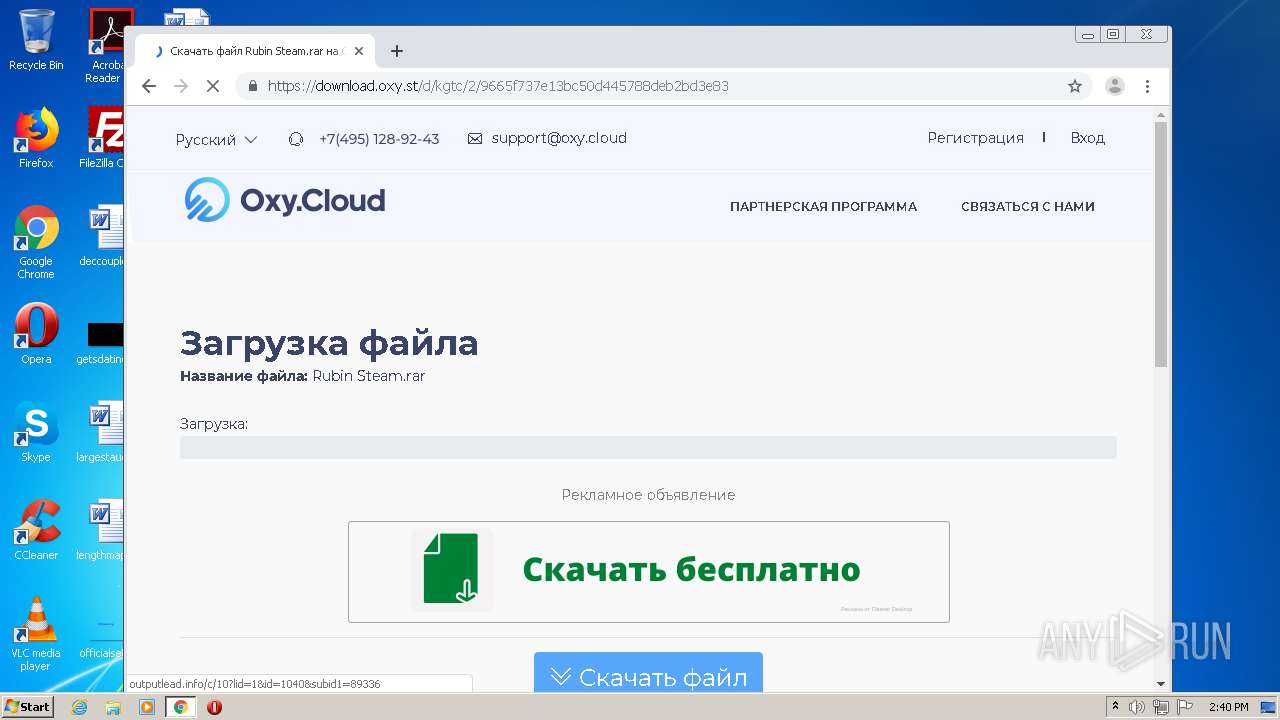
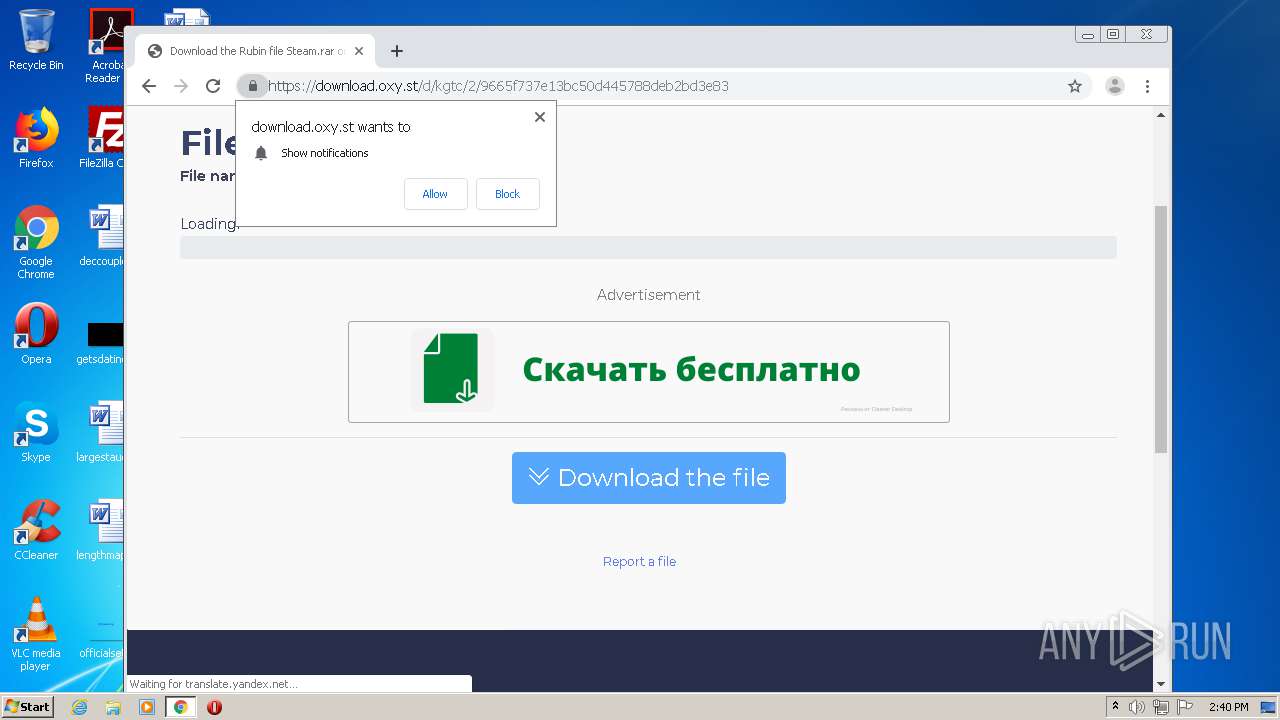
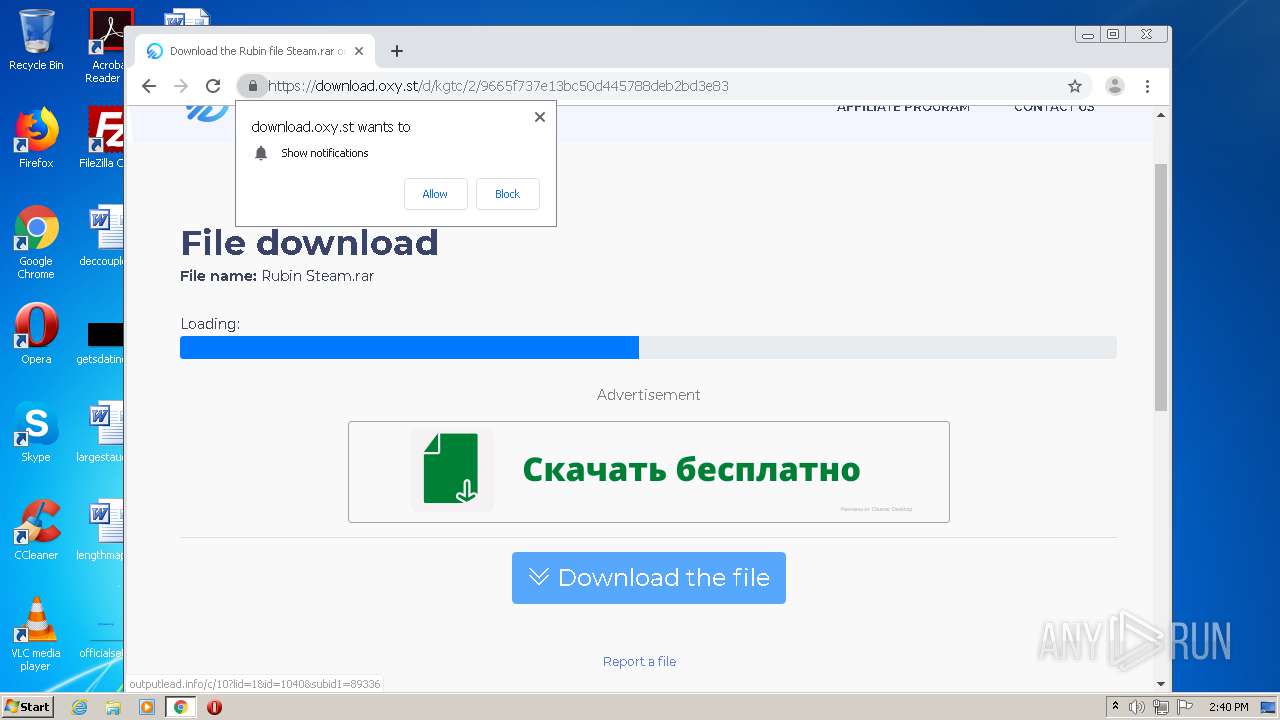
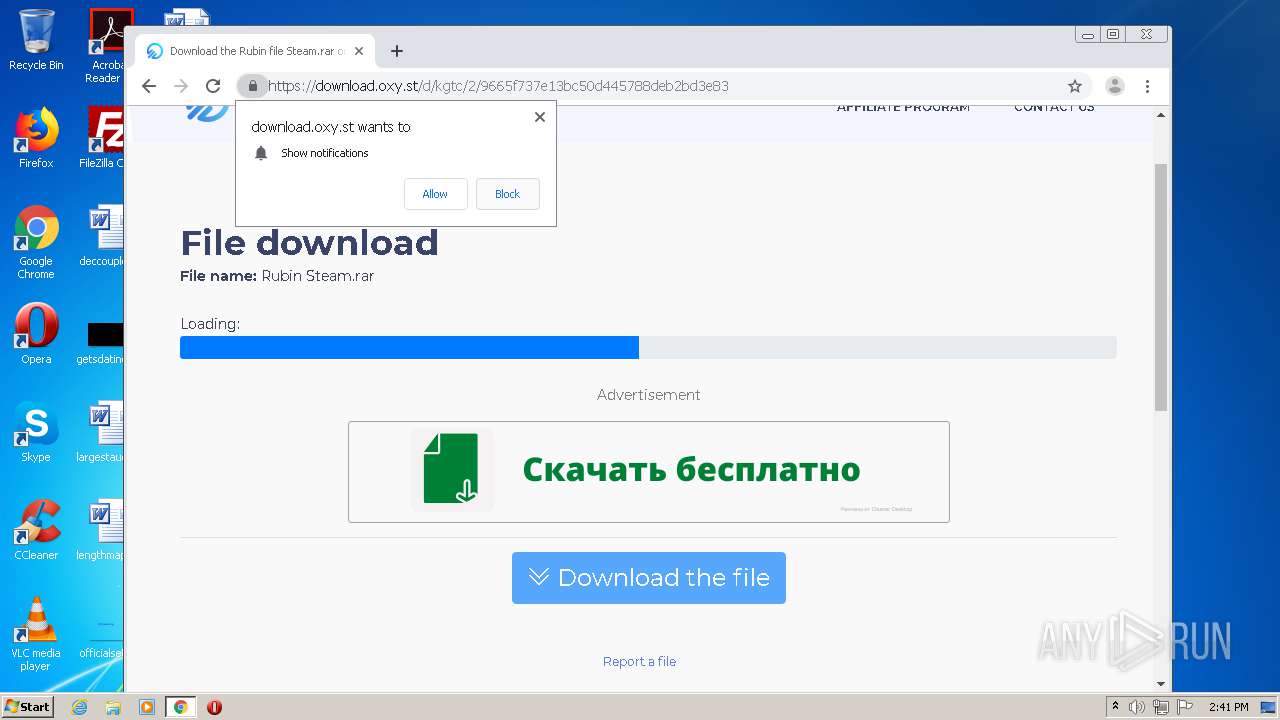
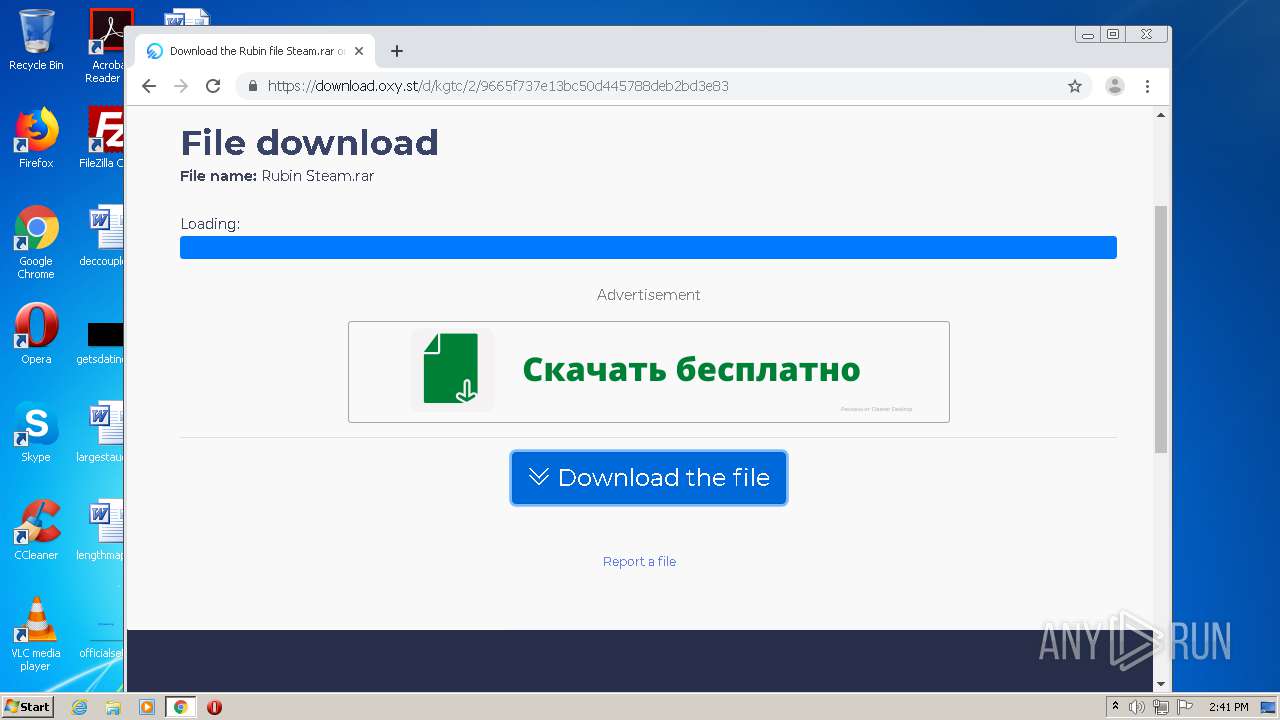
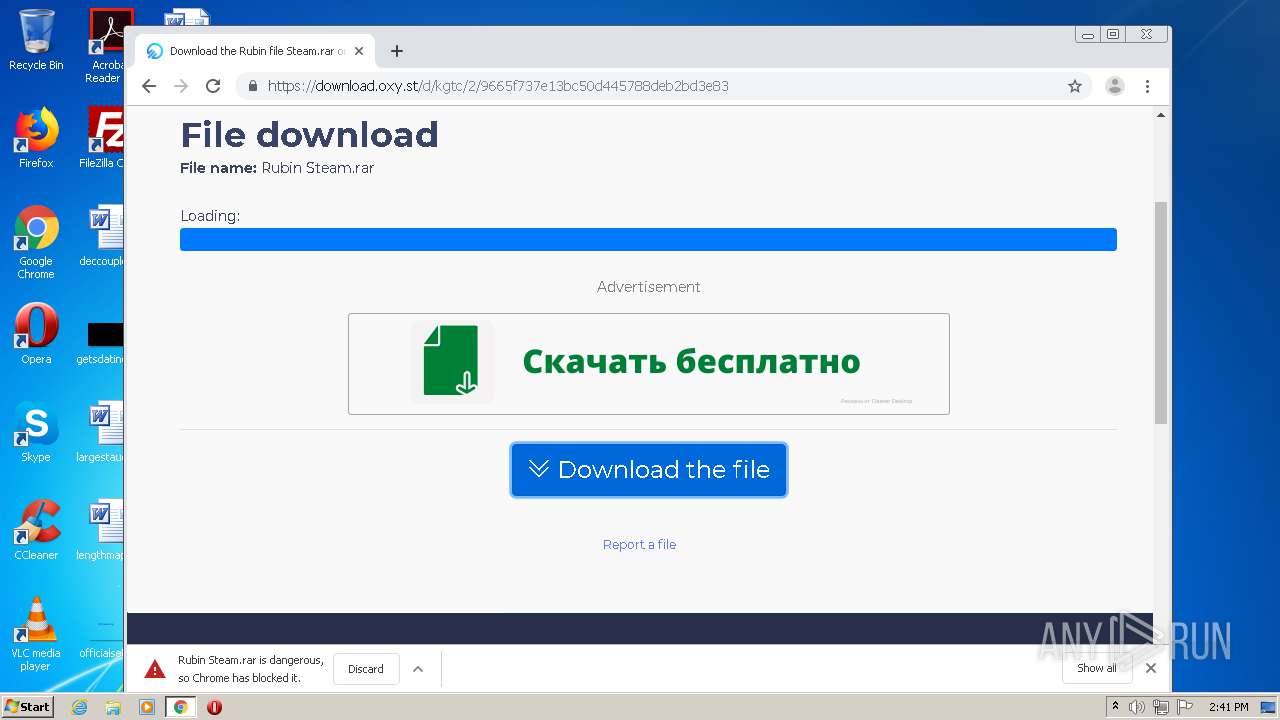
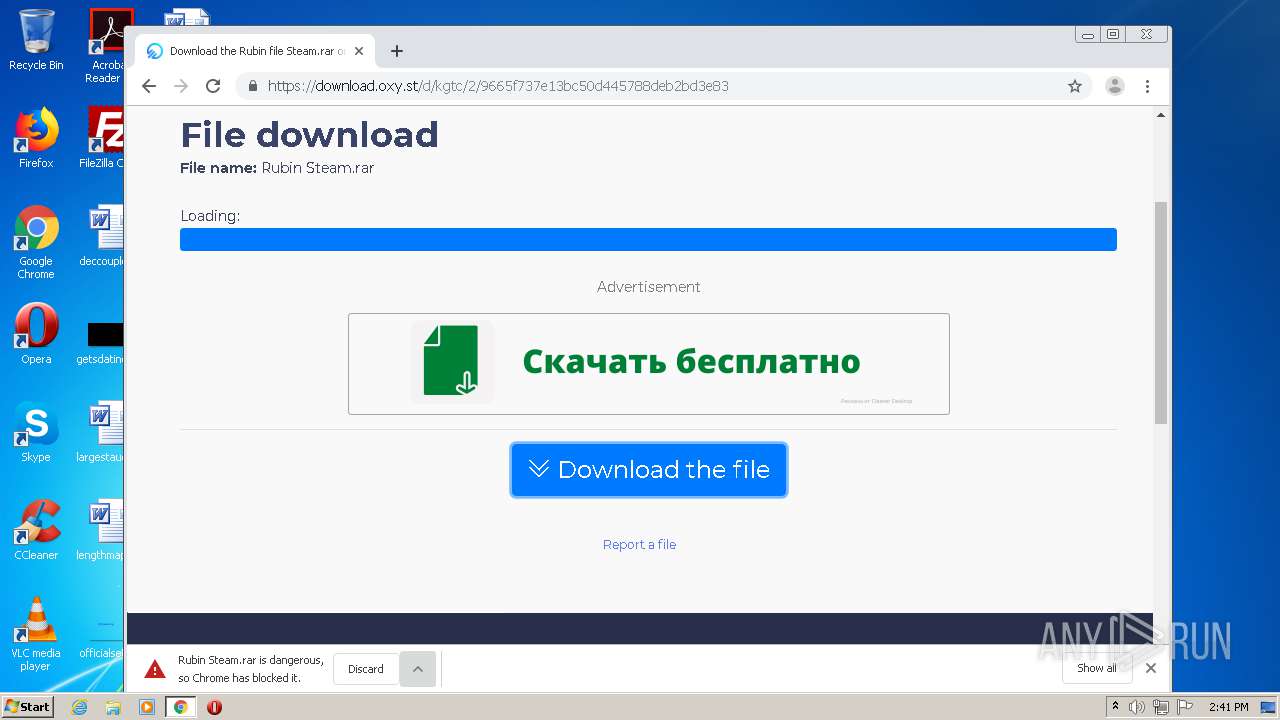
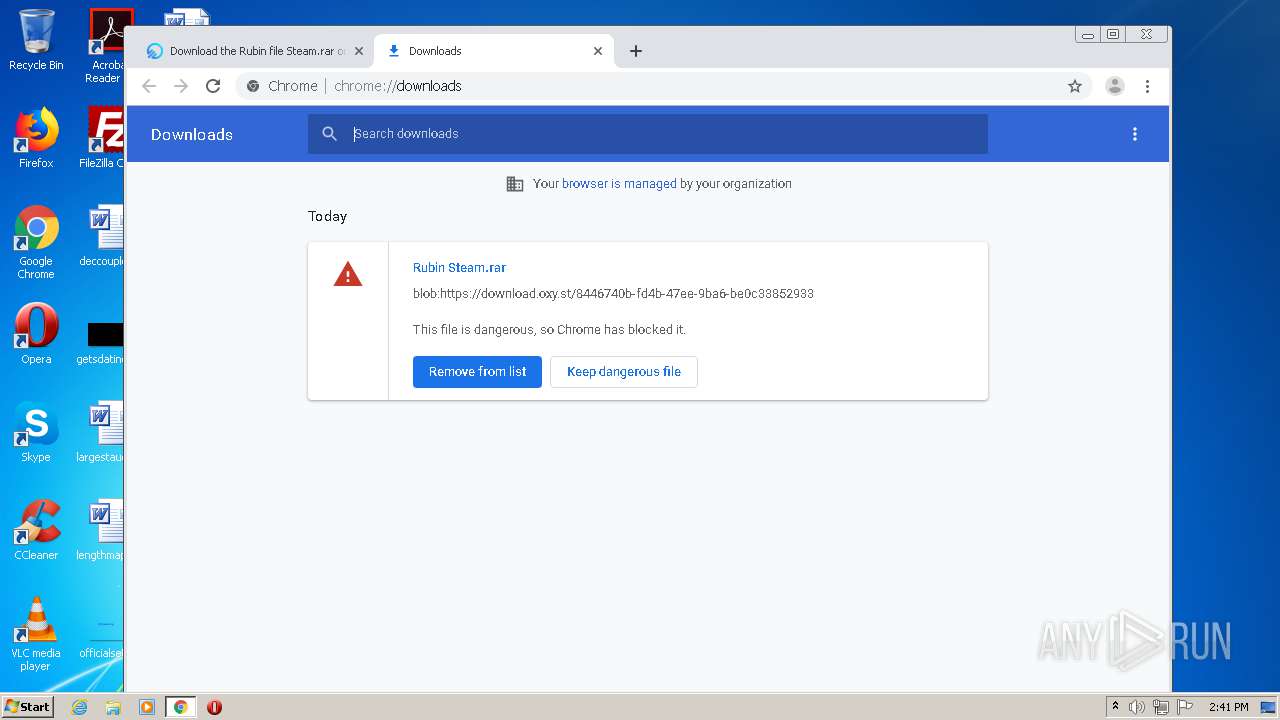
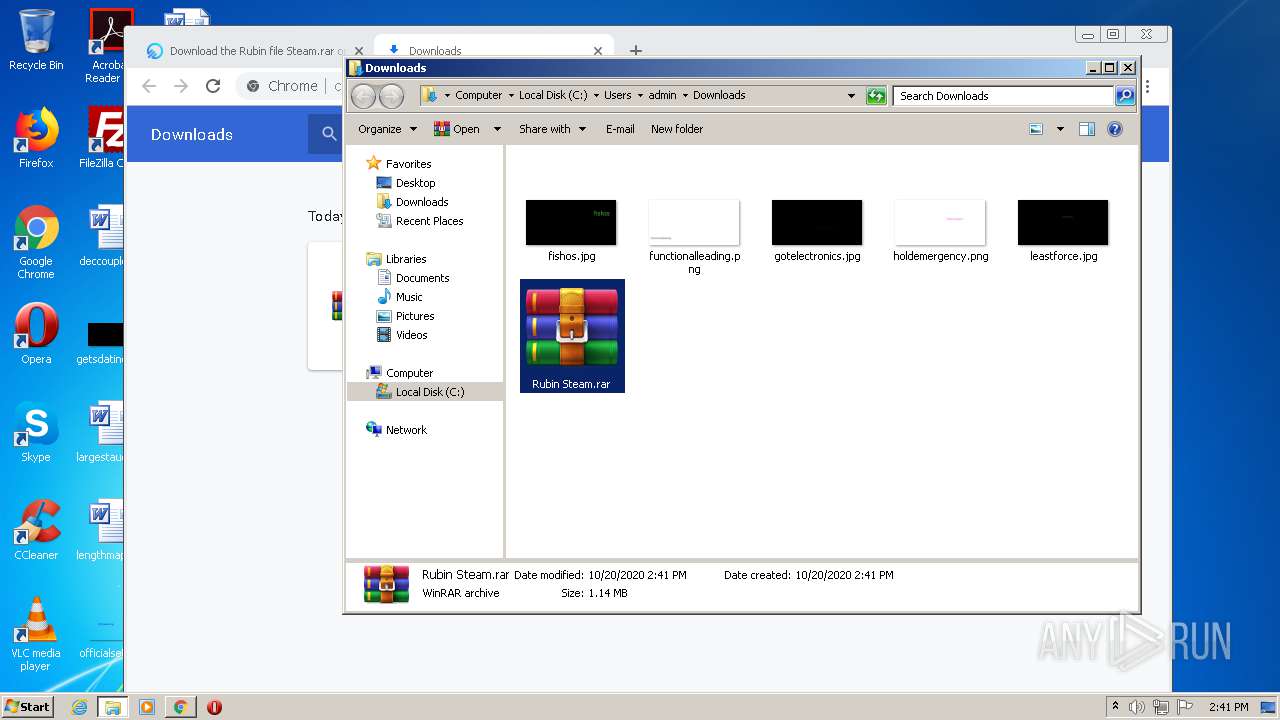
| Title: | Скачать файл Rubin Steam.rar на Oxy.Cloud |
| Description: | Скачать файл Rubin Steam.rar на Oxy.Cloud бесплатно на высокой скорости |
Total processes
77
Monitored processes
34
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=988,18191149372357046069,9399619266437159227,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=10872914131908130631 --mojo-platform-channel-handle=1348 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 584 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2516 CREDAT:144385 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 632 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,18191149372357046069,9399619266437159227,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=5389919129097112335 --mojo-platform-channel-handle=3600 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 804 | "C:\Users\admin\AppData\Local\Temp\File.exe" | C:\Users\admin\AppData\Local\Temp\File.exe | SteamAccountReger.exe | ||||||||||||
User: admin Company: Intel plugin Integrity Level: MEDIUM Description: Intel plugin Exit code: 0 Version: 2.0.0.0 Modules
| |||||||||||||||
| 884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,18191149372357046069,9399619266437159227,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6278645289026748046 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2440 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1000 | cmd /c ""C:\Users\admin\AppData\Local\Temp\tmpE71F.tmp.cmd"" | C:\Windows\system32\cmd.exe | — | File.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,18191149372357046069,9399619266437159227,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3210299645766185514 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3336 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1880 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,18191149372357046069,9399619266437159227,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13116585240774553105 --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2052 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,18191149372357046069,9399619266437159227,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=17319135153818932398 --mojo-platform-channel-handle=3476 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,18191149372357046069,9399619266437159227,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16830400379241261526 --mojo-platform-channel-handle=3540 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 685
Read events
2 451
Write events
227
Delete events
7
Modification events
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2105335284 | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30844646 | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
8
Suspicious files
120
Text files
159
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2516 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFB5DF1F774E593959.TMP | — | |
MD5:— | SHA256:— | |||
| 2516 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF8C6A22FE6D8F0A14.TMP | — | |
MD5:— | SHA256:— | |||
| 2516 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3080 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F8EE894-C08.pma | — | |
MD5:— | SHA256:— | |||
| 584 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab5F8A.tmp | — | |
MD5:— | SHA256:— | |||
| 584 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar5F8B.tmp | — | |
MD5:— | SHA256:— | |||
| 3080 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3080 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3080 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c2fcd0ca-2c16-4fba-b917-44ab3618022a.tmp | — | |
MD5:— | SHA256:— | |||
| 2516 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\RecoveryStore.{42A7EDC2-DE02-11E9-92C0-5254004A04AF}.dat | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
82
DNS requests
46
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
804 | File.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/xml | unknown | xml | 453 b | malicious |
804 | File.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/xml | unknown | xml | 453 b | malicious |
2516 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
804 | File.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/xml | unknown | xml | 453 b | malicious |
804 | File.exe | POST | 200 | 89.44.168.214:80 | http://gfs270n073.userstorage.mega.co.nz/ul/3yw75JIcO7u3XwIEFBUOK-WiFV_462UsJPzrVANZRyuSToq61oRUBsXUSbHssgowMRF7F5YFW04uuw-yJwLgRQ/0 | LU | text | 36 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2516 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 216.58.208.35:137 | www.gstatic.com | Google Inc. | US | whitelisted |
3896 | chrome.exe | 172.217.18.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
3896 | chrome.exe | 172.217.23.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3896 | chrome.exe | 172.217.16.132:443 | www.google.com | Google Inc. | US | whitelisted |
584 | iexplore.exe | 178.154.131.217:443 | yastatic.net | YANDEX LLC | RU | whitelisted |
584 | iexplore.exe | 172.217.18.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
584 | iexplore.exe | 104.17.79.107:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | suspicious |
4 | System | 216.58.208.35:445 | www.gstatic.com | Google Inc. | US | whitelisted |
584 | iexplore.exe | 172.217.22.67:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
yastatic.net |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
804 | File.exe | Misc activity | SUSPICIOUS [PTsecurity] ipify.org External IP Check |
804 | File.exe | Misc activity | SUSPICIOUS [PTsecurity] ipify.org External IP Check |
804 | File.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
804 | File.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
804 | File.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
804 | File.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
804 | File.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
804 | File.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
804 | File.exe | Potential Corporate Privacy Violation | ET POLICY HTTP POST to MEGA Userstorage |
804 | File.exe | A Network Trojan was detected | STEALER [PTsecurity] Agensla.gen |
1 ETPRO signatures available at the full report