| File name: | SecuriteInfo.com.Trojan.Agent.17255.18625 |
| Full analysis: | https://app.any.run/tasks/121d4b59-1524-48ff-bbd5-26cfe5257fd3 |
| Verdict: | Malicious activity |
| Analysis date: | August 11, 2024, 05:19:16 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 2566586C4346E124EF6C80DB76120A08 |
| SHA1: | 217326B3B8142B08FB02DDEA13DAF8C382DB3B2F |
| SHA256: | 9289F86329607258C2FC7F51C0685A94290551D7D00F69AAE4D74F5D80FB5183 |
| SSDEEP: | 393216:yxTIx6sPHz2tjcnFnlr4i+mBFkAQu1jlVQOvAnER4SfMlKSdwB9nxWwW:yxT9sPHym1ii+mPF0OvAnEyKS1wW |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks Windows Trust Settings
- SecuriteInfo.com.Trojan.Agent.17255.18625.exe (PID: 6356)
- SecuriteInfo.com.Trojan.Agent.17255.18625.exe (PID: 5656)
- msiexec.exe (PID: 6476)
Drops the executable file immediately after the start
- SecuriteInfo.com.Trojan.Agent.17255.18625.exe (PID: 6356)
- SecuriteInfo.com.Trojan.Agent.17255.18625.exe (PID: 5656)
- msiexec.exe (PID: 6476)
Reads security settings of Internet Explorer
- SecuriteInfo.com.Trojan.Agent.17255.18625.exe (PID: 6356)
- SecuriteInfo.com.Trojan.Agent.17255.18625.exe (PID: 5656)
Reads the Windows owner or organization settings
- SecuriteInfo.com.Trojan.Agent.17255.18625.exe (PID: 6356)
- SecuriteInfo.com.Trojan.Agent.17255.18625.exe (PID: 5656)
- msiexec.exe (PID: 6476)
Process drops legitimate windows executable
- SecuriteInfo.com.Trojan.Agent.17255.18625.exe (PID: 6356)
- SecuriteInfo.com.Trojan.Agent.17255.18625.exe (PID: 5656)
- msiexec.exe (PID: 6476)
Executable content was dropped or overwritten
- SecuriteInfo.com.Trojan.Agent.17255.18625.exe (PID: 6356)
- SecuriteInfo.com.Trojan.Agent.17255.18625.exe (PID: 5656)
Application launched itself
- SecuriteInfo.com.Trojan.Agent.17255.18625.exe (PID: 6356)
Adds/modifies Windows certificates
- SecuriteInfo.com.Trojan.Agent.17255.18625.exe (PID: 5656)
Executes as Windows Service
- VSSVC.exe (PID: 4296)
Reads the date of Windows installation
- SecuriteInfo.com.Trojan.Agent.17255.18625.exe (PID: 6356)
The process creates files with name similar to system file names
- SecuriteInfo.com.Trojan.Agent.17255.18625.exe (PID: 6356)
- msiexec.exe (PID: 6476)
The process drops C-runtime libraries
- SecuriteInfo.com.Trojan.Agent.17255.18625.exe (PID: 6356)
- msiexec.exe (PID: 6476)
INFO
Checks supported languages
- SecuriteInfo.com.Trojan.Agent.17255.18625.exe (PID: 6356)
- msiexec.exe (PID: 6476)
- msiexec.exe (PID: 6616)
- SecuriteInfo.com.Trojan.Agent.17255.18625.exe (PID: 5656)
- msiexec.exe (PID: 4592)
- msiexec.exe (PID: 6876)
Reads Environment values
- SecuriteInfo.com.Trojan.Agent.17255.18625.exe (PID: 6356)
- msiexec.exe (PID: 6616)
- SecuriteInfo.com.Trojan.Agent.17255.18625.exe (PID: 5656)
- msiexec.exe (PID: 4592)
- msiexec.exe (PID: 6876)
Creates files or folders in the user directory
- SecuriteInfo.com.Trojan.Agent.17255.18625.exe (PID: 6356)
Reads the computer name
- SecuriteInfo.com.Trojan.Agent.17255.18625.exe (PID: 6356)
- msiexec.exe (PID: 6476)
- msiexec.exe (PID: 6616)
- SecuriteInfo.com.Trojan.Agent.17255.18625.exe (PID: 5656)
- msiexec.exe (PID: 6876)
- msiexec.exe (PID: 4592)
Reads the machine GUID from the registry
- SecuriteInfo.com.Trojan.Agent.17255.18625.exe (PID: 6356)
- SecuriteInfo.com.Trojan.Agent.17255.18625.exe (PID: 5656)
- msiexec.exe (PID: 6476)
Reads the software policy settings
- SecuriteInfo.com.Trojan.Agent.17255.18625.exe (PID: 6356)
- SecuriteInfo.com.Trojan.Agent.17255.18625.exe (PID: 5656)
- msiexec.exe (PID: 6476)
Checks proxy server information
- SecuriteInfo.com.Trojan.Agent.17255.18625.exe (PID: 6356)
Create files in a temporary directory
- SecuriteInfo.com.Trojan.Agent.17255.18625.exe (PID: 6356)
- SecuriteInfo.com.Trojan.Agent.17255.18625.exe (PID: 5656)
- msiexec.exe (PID: 6876)
Process checks computer location settings
- SecuriteInfo.com.Trojan.Agent.17255.18625.exe (PID: 6356)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6476)
Creates a software uninstall entry
- msiexec.exe (PID: 6476)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 EXE PECompact compressed (generic) (83) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (9) |
| .exe | | | Generic Win/DOS Executable (3.9) |
| .exe | | | DOS Executable Generic (3.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:06:13 11:24:52+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.39 |
| CodeSize: | 2891776 |
| InitializedDataSize: | 1172992 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x230270 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.2.553.0 |
| ProductVersionNumber: | 4.2.553.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
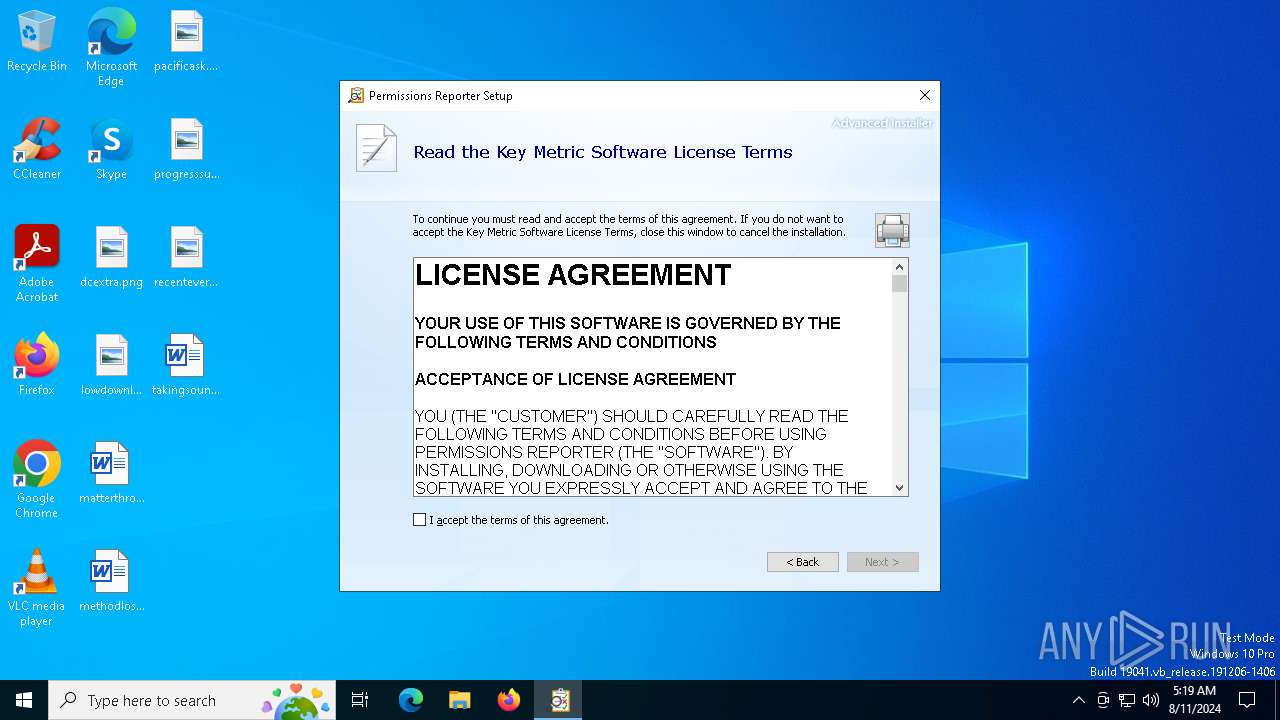
| CompanyName: | Key Metric Software |
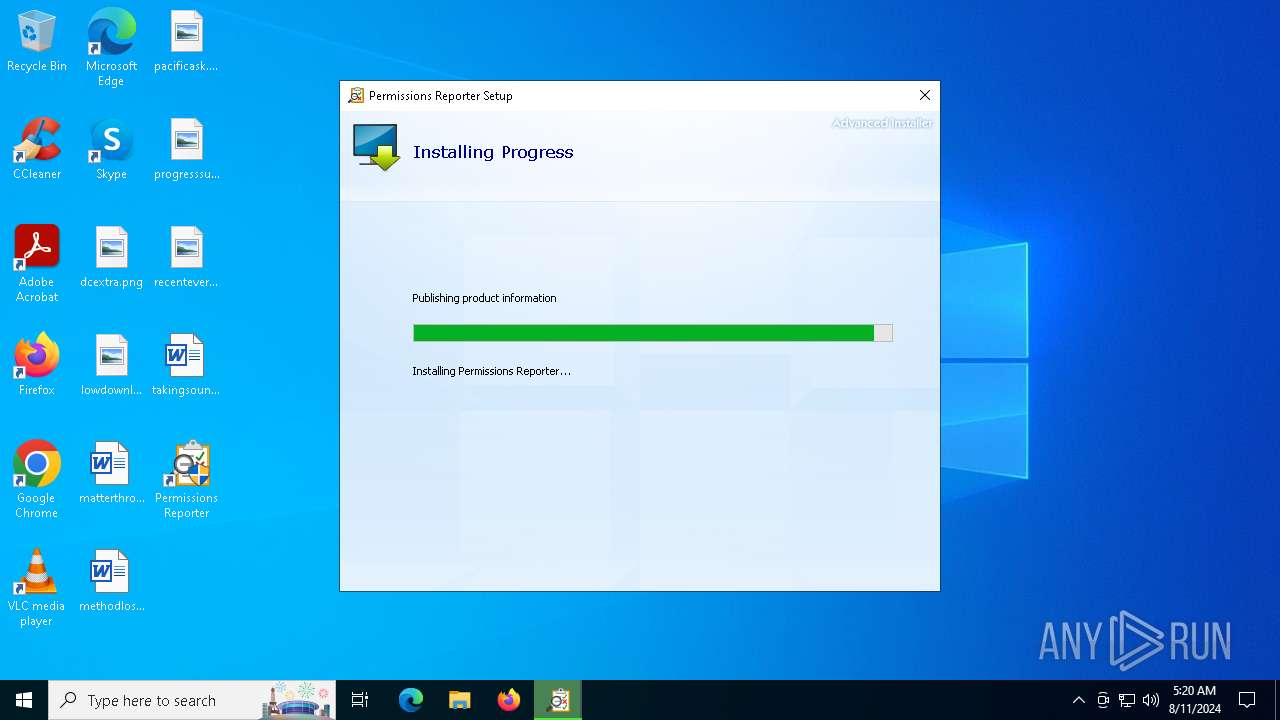
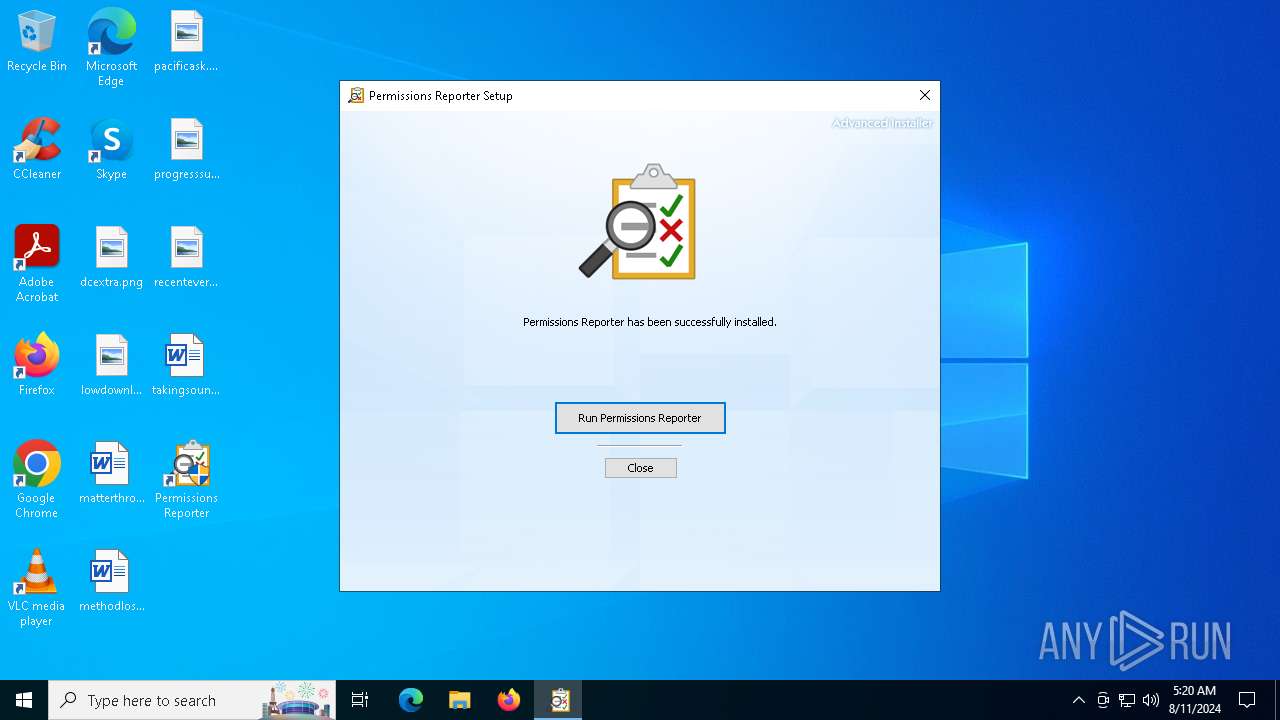
| FileDescription: | Permissions Reporter Installer |
| FileVersion: | 4.2.553.0 |
| InternalName: | pr-setup |
| LegalCopyright: | Copyright (C) 2024 Key Metric Software |
| OriginalFileName: | pr-setup.exe |
| ProductName: | Permissions Reporter |
| ProductVersion: | 4.2.553.0 |
Total processes
143
Monitored processes
9
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1700 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4296 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4592 | C:\Windows\syswow64\MsiExec.exe -Embedding 7BE13FC0ED1B4092A26EB69B1D93BD3F E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | msiexec.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
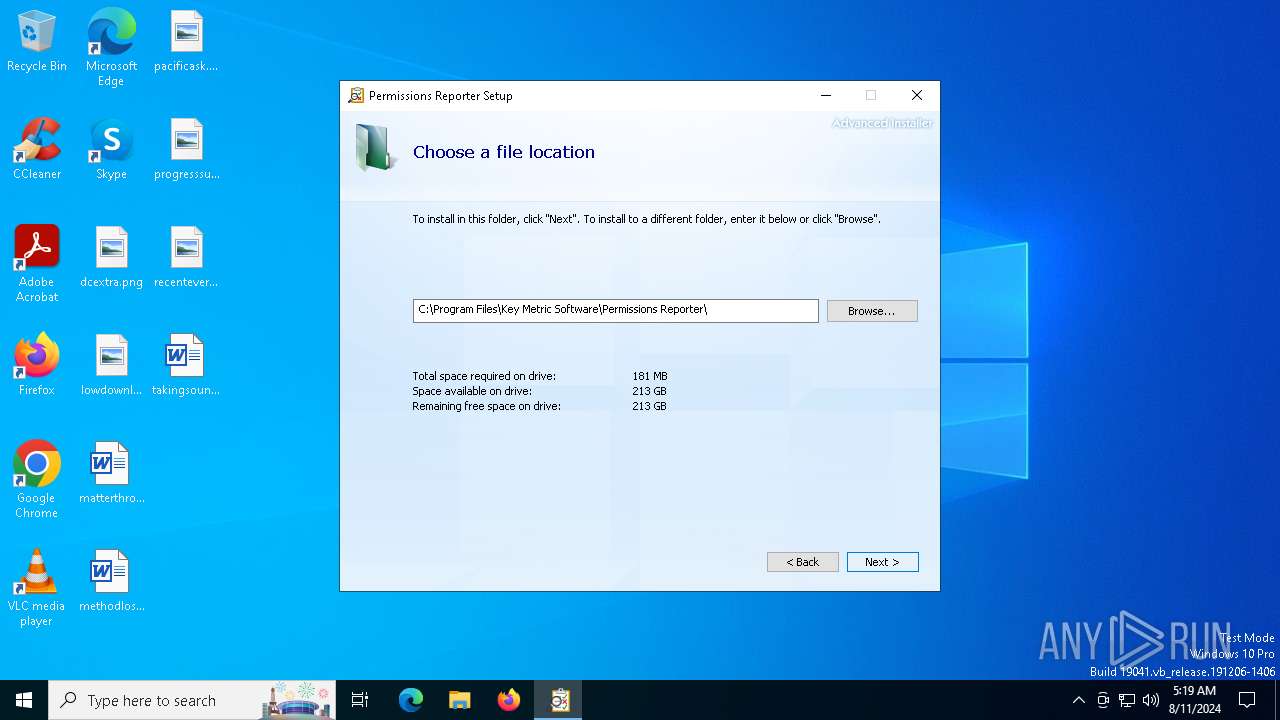
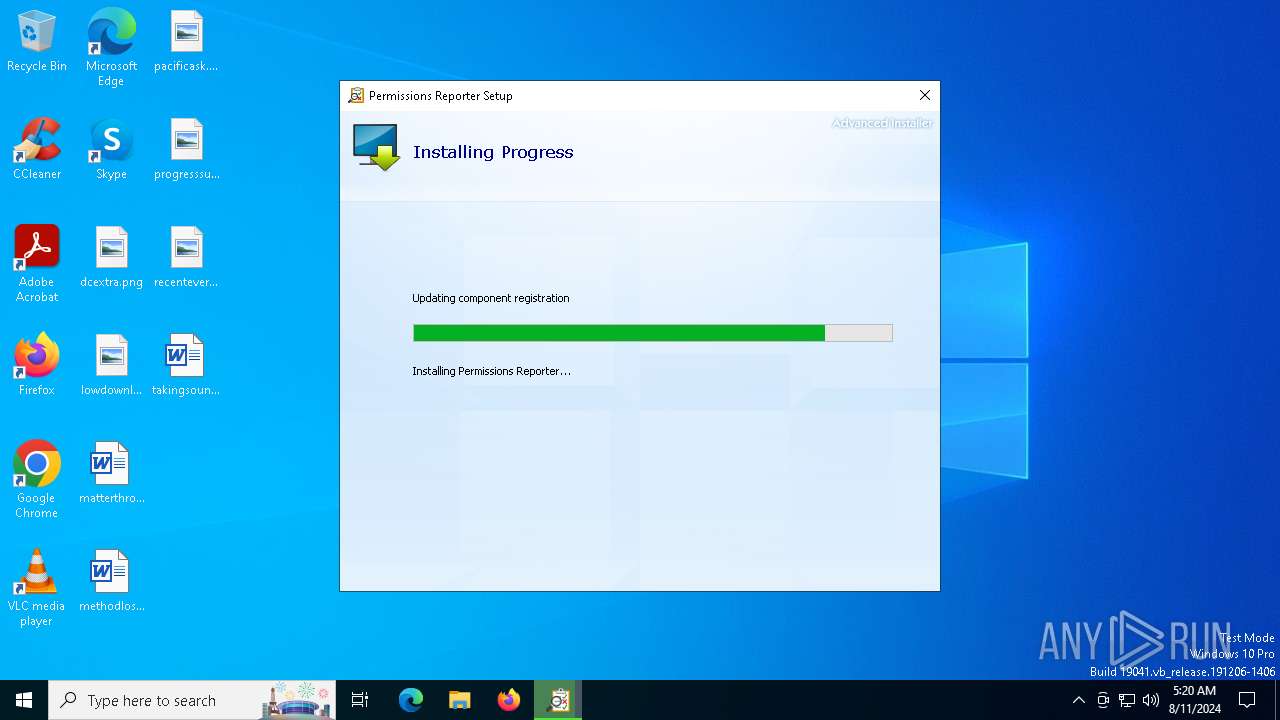
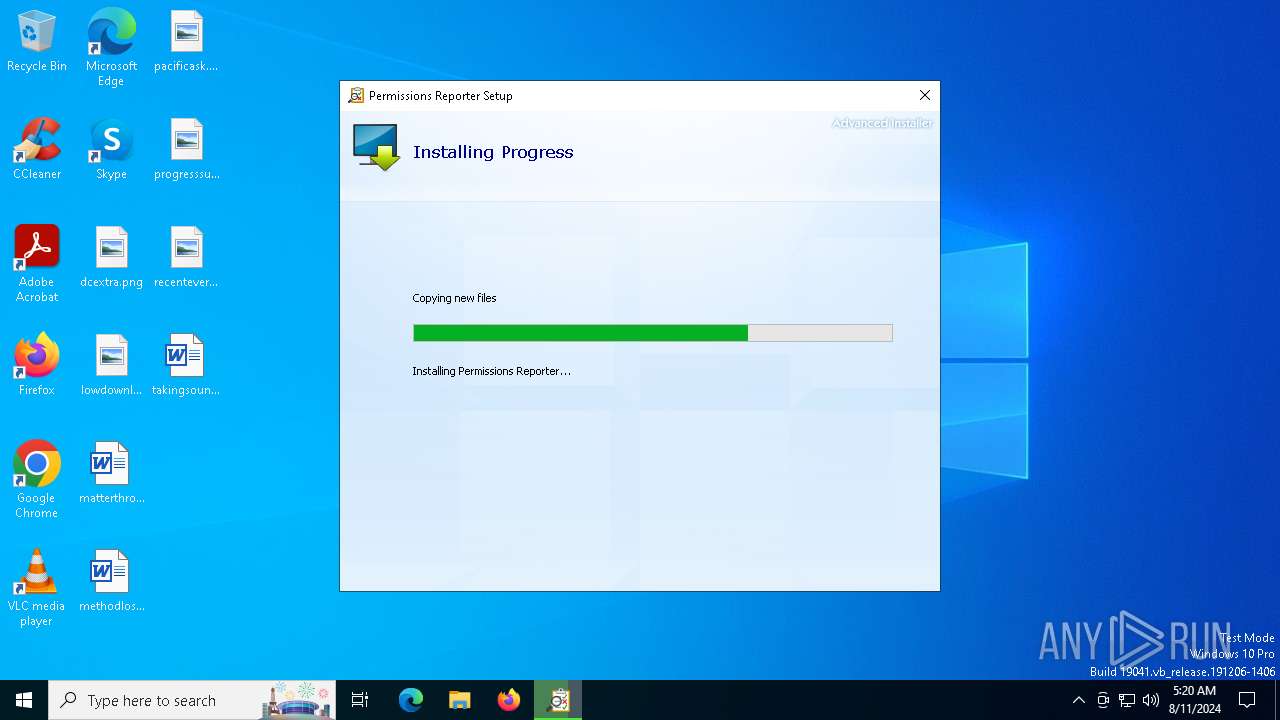
| 5656 | "C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.Trojan.Agent.17255.18625.exe" /i "C:\Users\admin\AppData\Roaming\Key Metric Software\Permissions Reporter 4.2.553.0\install\2B8F380\PermissionsReporter.x64.msi" AI_EUIMSI=1 SHORTCUTDIR="C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Permissions Reporter" APPDIR="C:\Program Files\Key Metric Software\Permissions Reporter" SECONDSEQUENCE="1" CLIENTPROCESSID="6356" CHAINERUIPROCESSID="6356Chainer" ACTION="INSTALL" EXECUTEACTION="INSTALL" CLIENTUILEVEL="0" ADDLOCAL="AI64BitFiles,AIOtherFiles,MainFeature" PRIMARYFOLDER="APPDIR" ROOTDRIVE="C:\" AI_DETECTED_ADMIN_USER="1" AI_SETUPEXEPATH="C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.Trojan.Agent.17255.18625.exe" SETUPEXEDIR="C:\Users\admin\AppData\Local\Temp\" EXE_CMD_LINE="/exenoupdates /forcecleanup /wintime 1723352631 " AI_SETUPEXEPATH_ORIGINAL="C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.Trojan.Agent.17255.18625.exe" TARGETDIR="C:\" AI_INSTALL="1" | C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.Trojan.Agent.17255.18625.exe | SecuriteInfo.com.Trojan.Agent.17255.18625.exe | ||||||||||||
User: admin Company: Key Metric Software Integrity Level: HIGH Description: Permissions Reporter Installer Exit code: 0 Version: 4.2.553.0 Modules
| |||||||||||||||
| 6284 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6356 | "C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.Trojan.Agent.17255.18625.exe" | C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.Trojan.Agent.17255.18625.exe | explorer.exe | ||||||||||||
User: admin Company: Key Metric Software Integrity Level: MEDIUM Description: Permissions Reporter Installer Exit code: 0 Version: 4.2.553.0 Modules
| |||||||||||||||
| 6476 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6616 | C:\Windows\syswow64\MsiExec.exe -Embedding BED27B3B911B351502FEE16494EF0FA8 C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6876 | C:\Windows\syswow64\MsiExec.exe -Embedding DEB37B6C1547FD85341219609FA2677B | C:\Windows\SysWOW64\msiexec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
21 883
Read events
21 262
Write events
597
Delete events
24
Modification events
| (PID) Process: | (6356) SecuriteInfo.com.Trojan.Agent.17255.18625.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6356) SecuriteInfo.com.Trojan.Agent.17255.18625.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6356) SecuriteInfo.com.Trojan.Agent.17255.18625.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6356) SecuriteInfo.com.Trojan.Agent.17255.18625.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (5656) SecuriteInfo.com.Trojan.Agent.17255.18625.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates |
| Operation: | delete value | Name: | F40042E2E5F7E8EF8189FED15519AECE42C3BFA2 |
Value: | |||
| (PID) Process: | (5656) SecuriteInfo.com.Trojan.Agent.17255.18625.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\F40042E2E5F7E8EF8189FED15519AECE42C3BFA2 |
| Operation: | write | Name: | Blob |
Value: 040000000100000010000000BE954F16012122448CA8BC279602ACF50F000000010000003000000041CE925678DFE0CCAA8089263C242B897CA582089D14E5EB685FCA967F36DBD334E97E81FD0E64815F851F914ADE1A1E030000000100000014000000F40042E2E5F7E8EF8189FED15519AECE42C3BFA21D0000000100000010000000E78921F81CEA4D4105D2B5F4AFAE0C78140000000100000014000000C87ED26A852A1BCA1998040727CF50104F68A8A2090000000100000016000000301406082B0601050507030306082B060105050703086200000001000000200000005367F20C7ADE0E2BCA790915056D086B720C33C1FA2A2661ACF787E3292E12700B00000001000000800000004D006900630072006F0073006F006600740020004900640065006E007400690074007900200056006500720069006600690063006100740069006F006E00200052006F006F007400200043006500720074006900660069006300610074006500200041007500740068006F0072006900740079002000320030003200300000001900000001000000100000009F687581F7EF744ECFC12B9CEE6238F12000000001000000D0050000308205CC308203B4A00302010202105498D2D1D45B1995481379C811C08799300D06092A864886F70D01010C05003077310B3009060355040613025553311E301C060355040A13154D6963726F736F667420436F72706F726174696F6E314830460603550403133F4D6963726F736F6674204964656E7469747920566572696669636174696F6E20526F6F7420436572746966696361746520417574686F726974792032303230301E170D3230303431363138333631365A170D3435303431363138343434305A3077310B3009060355040613025553311E301C060355040A13154D6963726F736F667420436F72706F726174696F6E314830460603550403133F4D6963726F736F6674204964656E7469747920566572696669636174696F6E20526F6F7420436572746966696361746520417574686F72697479203230323030820222300D06092A864886F70D01010105000382020F003082020A0282020100B3912A07830667FD9E9DE0C7C0B7A4E642047F0FA6DB5FFBD55AD745A0FB770BF080F3A66D5A4D7953D8A08684574520C7A254FBC7A2BF8AC76E35F3A215C42F4EE34A8596490DFFBE99D814F6BC2707EE429B2BF50B9206E4FD691365A89172F29884EB833D0EE4D771124821CB0DEDF64749B79BF9C9C717B6844FFFB8AC9AD773674985E386BD3740D02586D4DEB5C26D626AD5A978BC2D6F49F9E56C1414FD14C7D3651637DECB6EBC5E298DFD629B152CD605E6B9893233A362C7D7D6526708C42EF4562B9E0B87CCECA7B4A6AAEB05CD1957A53A0B04271C91679E2D622D2F1EBEDAC020CB0419CA33FB89BE98E272A07235BE79E19C836FE46D176F90F33D008675388ED0E0499ABBDBD3F830CAD55788684D72D3BF6D7F71D8FDBD0DAE926448B75B6F7926B5CD9B952184D1EF0F323D7B578CF345074C7CE05E180E35768B6D9ECB3674AB05F8E0735D3256946797250AC6353D9497E7C1448B80FDC1F8F47419E530F606FB21573E061C8B6B158627497B8293CA59E87547E83F38F4C75379A0B6B4E25C51EFBD5F38C113E6780C955A2EC5405928CC0F24C0ECBA0977239938A6B61CDAC7BA20B6D737D87F37AF08E33B71DB6E731B7D9972B0E486335974B516007B506DC68613DAFDC439823D24009A60DABA94C005512C34AC50991387BBB30580B24D30025CB826835DB46373EFAE23954F6028BE37D55BA50203010001A3543052300E0603551D0F0101FF040403020186300F0603551D130101FF040530030101FF301D0603551D0E04160414C87ED26A852A1BCA1998040727CF50104F68A8A2301006092B06010401823715010403020100300D06092A864886F70D01010C05000382020100AF6ADDE619E72D9443194ECBE9509564A50391028BE236803B15A252C21619B66A5A5D744330F49BFF607409B1211E90166DC5248F5C668863F44FCC7DF2124C40108B019FDAA9C8AEF2951BCF9D05EB493E74A0685BE5562C651C827E53DA56D94617799245C4103608522917CB2FA6F27ED469248A1E8FB0730DCC1C4AABB2AAEDA79163016422A832B87E3228B367732D91B4DC31010BF7470AA6F1D74AED5660C42C08A37B40B0BC74275287D6BE88DD378A896E67881DF5C95DA0FEB6AB3A80D71A973C173622411EAC4DD583E63C38BD4F30E954A9D3B604C3327661BBB018C52B18B3C080D5B795B05E514D22FCEC58AAE8D894B4A52EED92DEE7187C2157DD5563F7BF6DCD1FD2A6772870C7E25B3A5B08D25B4EC80096B3E18336AF860A655C74F6EAEC7A6A74A0F04BEEEF94A3AC50F287EDD73A3083C9FB7D57BEE5E3F841CAE564AEB3A3EC58EC859ACCEFB9EAF35618B95C739AAFC577178359DB371A187254A541D2B62375A3439AE5777C9679B7418DBFECDC80A09FD17775585F3513E0251A670B7DCE25FA070AE46121D8D41CE507C63699F496D0C615FE4ECDD7AE8B9DDB16FD04C692BDD488E6A9A3AABBF764383B5FCC0CD035BE741903A6C5AA4CA26136823E1DF32BBC975DDB4B783B2DF53BEF6023E8F5EC0B233695AF9866BF53D37BB8694A2A966669C494C6F45F6EAC98788880065CA2B2EDA2 | |||
| (PID) Process: | (5656) SecuriteInfo.com.Trojan.Agent.17255.18625.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\F40042E2E5F7E8EF8189FED15519AECE42C3BFA2 |
| Operation: | write | Name: | Blob |
Value: 5C0000000100000004000000001000001900000001000000100000009F687581F7EF744ECFC12B9CEE6238F10B00000001000000800000004D006900630072006F0073006F006600740020004900640065006E007400690074007900200056006500720069006600690063006100740069006F006E00200052006F006F007400200043006500720074006900660069006300610074006500200041007500740068006F0072006900740079002000320030003200300000006200000001000000200000005367F20C7ADE0E2BCA790915056D086B720C33C1FA2A2661ACF787E3292E1270090000000100000016000000301406082B0601050507030306082B06010505070308140000000100000014000000C87ED26A852A1BCA1998040727CF50104F68A8A21D0000000100000010000000E78921F81CEA4D4105D2B5F4AFAE0C78030000000100000014000000F40042E2E5F7E8EF8189FED15519AECE42C3BFA20F000000010000003000000041CE925678DFE0CCAA8089263C242B897CA582089D14E5EB685FCA967F36DBD334E97E81FD0E64815F851F914ADE1A1E040000000100000010000000BE954F16012122448CA8BC279602ACF52000000001000000D0050000308205CC308203B4A00302010202105498D2D1D45B1995481379C811C08799300D06092A864886F70D01010C05003077310B3009060355040613025553311E301C060355040A13154D6963726F736F667420436F72706F726174696F6E314830460603550403133F4D6963726F736F6674204964656E7469747920566572696669636174696F6E20526F6F7420436572746966696361746520417574686F726974792032303230301E170D3230303431363138333631365A170D3435303431363138343434305A3077310B3009060355040613025553311E301C060355040A13154D6963726F736F667420436F72706F726174696F6E314830460603550403133F4D6963726F736F6674204964656E7469747920566572696669636174696F6E20526F6F7420436572746966696361746520417574686F72697479203230323030820222300D06092A864886F70D01010105000382020F003082020A0282020100B3912A07830667FD9E9DE0C7C0B7A4E642047F0FA6DB5FFBD55AD745A0FB770BF080F3A66D5A4D7953D8A08684574520C7A254FBC7A2BF8AC76E35F3A215C42F4EE34A8596490DFFBE99D814F6BC2707EE429B2BF50B9206E4FD691365A89172F29884EB833D0EE4D771124821CB0DEDF64749B79BF9C9C717B6844FFFB8AC9AD773674985E386BD3740D02586D4DEB5C26D626AD5A978BC2D6F49F9E56C1414FD14C7D3651637DECB6EBC5E298DFD629B152CD605E6B9893233A362C7D7D6526708C42EF4562B9E0B87CCECA7B4A6AAEB05CD1957A53A0B04271C91679E2D622D2F1EBEDAC020CB0419CA33FB89BE98E272A07235BE79E19C836FE46D176F90F33D008675388ED0E0499ABBDBD3F830CAD55788684D72D3BF6D7F71D8FDBD0DAE926448B75B6F7926B5CD9B952184D1EF0F323D7B578CF345074C7CE05E180E35768B6D9ECB3674AB05F8E0735D3256946797250AC6353D9497E7C1448B80FDC1F8F47419E530F606FB21573E061C8B6B158627497B8293CA59E87547E83F38F4C75379A0B6B4E25C51EFBD5F38C113E6780C955A2EC5405928CC0F24C0ECBA0977239938A6B61CDAC7BA20B6D737D87F37AF08E33B71DB6E731B7D9972B0E486335974B516007B506DC68613DAFDC439823D24009A60DABA94C005512C34AC50991387BBB30580B24D30025CB826835DB46373EFAE23954F6028BE37D55BA50203010001A3543052300E0603551D0F0101FF040403020186300F0603551D130101FF040530030101FF301D0603551D0E04160414C87ED26A852A1BCA1998040727CF50104F68A8A2301006092B06010401823715010403020100300D06092A864886F70D01010C05000382020100AF6ADDE619E72D9443194ECBE9509564A50391028BE236803B15A252C21619B66A5A5D744330F49BFF607409B1211E90166DC5248F5C668863F44FCC7DF2124C40108B019FDAA9C8AEF2951BCF9D05EB493E74A0685BE5562C651C827E53DA56D94617799245C4103608522917CB2FA6F27ED469248A1E8FB0730DCC1C4AABB2AAEDA79163016422A832B87E3228B367732D91B4DC31010BF7470AA6F1D74AED5660C42C08A37B40B0BC74275287D6BE88DD378A896E67881DF5C95DA0FEB6AB3A80D71A973C173622411EAC4DD583E63C38BD4F30E954A9D3B604C3327661BBB018C52B18B3C080D5B795B05E514D22FCEC58AAE8D894B4A52EED92DEE7187C2157DD5563F7BF6DCD1FD2A6772870C7E25B3A5B08D25B4EC80096B3E18336AF860A655C74F6EAEC7A6A74A0F04BEEEF94A3AC50F287EDD73A3083C9FB7D57BEE5E3F841CAE564AEB3A3EC58EC859ACCEFB9EAF35618B95C739AAFC577178359DB371A187254A541D2B62375A3439AE5777C9679B7418DBFECDC80A09FD17775585F3513E0251A670B7DCE25FA070AE46121D8D41CE507C63699F496D0C615FE4ECDD7AE8B9DDB16FD04C692BDD488E6A9A3AABBF764383B5FCC0CD035BE741903A6C5AA4CA26136823E1DF32BBC975DDB4B783B2DF53BEF6023E8F5EC0B233695AF9866BF53D37BB8694A2A966669C494C6F45F6EAC98788880065CA2B2EDA2 | |||
| (PID) Process: | (6476) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000DC5D6A18AEEBDA014C19000020090000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6476) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000DC5D6A18AEEBDA014C19000020090000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6476) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000B51DAD18AEEBDA014C19000020090000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
564
Suspicious files
34
Text files
33
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6356 | SecuriteInfo.com.Trojan.Agent.17255.18625.exe | C:\Users\admin\AppData\Roaming\Key Metric Software\Permissions Reporter 4.2.553.0\install\holder0.aiph | — | |
MD5:— | SHA256:— | |||
| 6356 | SecuriteInfo.com.Trojan.Agent.17255.18625.exe | C:\Users\admin\AppData\Roaming\Key Metric Software\Permissions Reporter 4.2.553.0\install\2B8F380\PermissionsReporter.msi | — | |
MD5:— | SHA256:— | |||
| 6356 | SecuriteInfo.com.Trojan.Agent.17255.18625.exe | C:\Users\admin\AppData\Roaming\Key Metric Software\Permissions Reporter 4.2.553.0\install\2B8F380\PermissionsReporter.x64.msi | — | |
MD5:— | SHA256:— | |||
| 6356 | SecuriteInfo.com.Trojan.Agent.17255.18625.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77003E887FC21E505B9E28CBA30E18ED_8ACE642DC0A43382FABA7AE806561A50 | der | |
MD5:8213165A0457FE8541A1F51A05EF7C2A | SHA256:FA16F0D2D854C869263151E5062D96172F94032ED28E322179C7ADDEFA436408 | |||
| 6356 | SecuriteInfo.com.Trojan.Agent.17255.18625.exe | C:\Users\admin\AppData\Local\Temp\MSI7963.tmp | executable | |
MD5:3604517A3E6E69BA339239CF82FC94A5 | SHA256:BDD1D14C9CB54B19F6A7F37ADBC7537CE8FD2F6FA59A74A4A90B08C7979708D2 | |||
| 6356 | SecuriteInfo.com.Trojan.Agent.17255.18625.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\86844F70250DD8EF225D6B4178798C21_44AD5D0C299F1D4EE038B125B5E5863A | der | |
MD5:1302EAB1ADAA81D42C79375B43771CF7 | SHA256:13EBCBE4E3EE68BC3AD32E251AEB69BC58CBBBE9E8EB9A21C85670309775BC08 | |||
| 6356 | SecuriteInfo.com.Trojan.Agent.17255.18625.exe | C:\Users\admin\AppData\Local\Temp\MSI7A8E.tmp | executable | |
MD5:3604517A3E6E69BA339239CF82FC94A5 | SHA256:BDD1D14C9CB54B19F6A7F37ADBC7537CE8FD2F6FA59A74A4A90B08C7979708D2 | |||
| 6356 | SecuriteInfo.com.Trojan.Agent.17255.18625.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\94D97B1EC1F43DD6ED4FE7AB95E144BC_EB06E3DC6894488BC5C3911CE887708B | binary | |
MD5:700C73967DE6A5AA5BFAB091E61939C4 | SHA256:4953C36AE4489667C8C2D3E8516C2D3B223189C86926DF435792177D48112BAB | |||
| 6356 | SecuriteInfo.com.Trojan.Agent.17255.18625.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\94D97B1EC1F43DD6ED4FE7AB95E144BC_EB06E3DC6894488BC5C3911CE887708B | der | |
MD5:BFB6AF74DDFA970E6703EE91EA24B41D | SHA256:6053508FFC3DEEA2A8763B4D6A79B7FF317B205E55A42766988EE86CC5036E27 | |||
| 6356 | SecuriteInfo.com.Trojan.Agent.17255.18625.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77003E887FC21E505B9E28CBA30E18ED_8ACE642DC0A43382FABA7AE806561A50 | binary | |
MD5:A5C43FBD4AAD136FDFF4BD528A60B03E | SHA256:9B31F569F9AE4A56216F6A20A4444B6755DD0B5381E4C8066F8B5D358CD6542F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
47
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6356 | SecuriteInfo.com.Trojan.Agent.17255.18625.exe | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBTDHsfuqfubd3pihvq4mgQVWgHWNwQUyH7SaoUqG8oZmAQHJ89QEE9oqKICEzMAAAAHh6M0o3uljhwAAAAAAAc%3D | unknown | — | — | whitelisted |
6356 | SecuriteInfo.com.Trojan.Agent.17255.18625.exe | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBTOQYLFSE5GO%2FpaRVfYu7d9gZEbQAQU2UEpsA8PY2zvadf1zSmepEhqMOYCEzMAAAAHN4xbodlbjNQAAAAAAAc%3D | unknown | — | — | whitelisted |
6356 | SecuriteInfo.com.Trojan.Agent.17255.18625.exe | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRBq81UG1MnDOVNKqff0SSEz6JuZwQU6IPEM9fcnwycdpoKptTfh6ZeWO4CEzMAAUj4gkpgdxsS41oAAAABSPg%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1248 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6980 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6940 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5152 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6356 | SecuriteInfo.com.Trojan.Agent.17255.18625.exe | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
876 | svchost.exe | 20.106.86.13:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
5336 | SearchApp.exe | 2.23.209.181:443 | www.bing.com | Akamai International B.V. | GB | unknown |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
th.bing.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
Threats
Process | Message |
|---|---|
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |