| File name: | SazInjector - Linkvertise Downloader_3701738712.exe |
| Full analysis: | https://app.any.run/tasks/125816f4-0be3-43e6-a907-ed7b82a4615f |
| Verdict: | Malicious activity |
| Analysis date: | August 08, 2020, 09:22:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 7E4D78B44CB943949F9655B031658908 |
| SHA1: | 0DAF80D6A08753DC10FB657BE9DE846535D3BB54 |
| SHA256: | 9273CD1A86B5D86886C1AB90D57B32C21EBDAFB18290E01E7D58BB14EFEC17E7 |
| SSDEEP: | 98304:u6jxRY2Mcf9nBjKUq/L8LcnIaIOTDS1/+MIiJ8EWOgz5:5iaf9BjKxL8DaIO/S1/+oJEOgV |
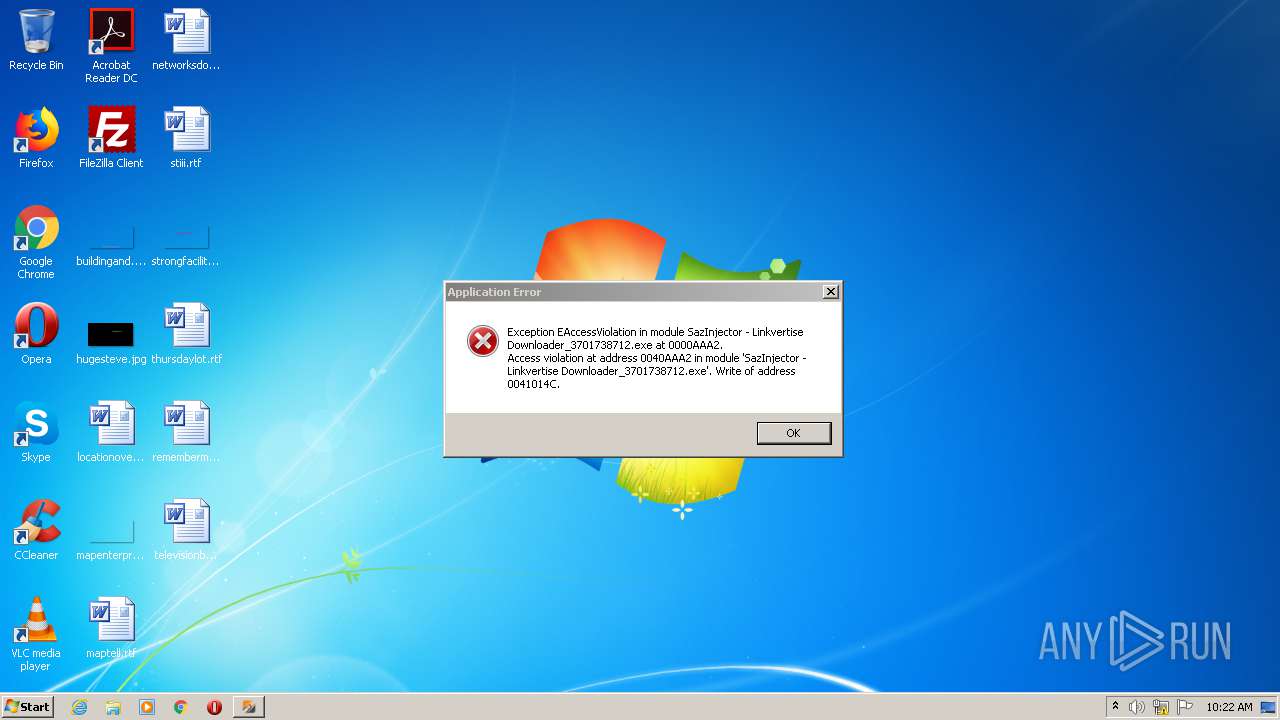
MALICIOUS
No malicious indicators.SUSPICIOUS
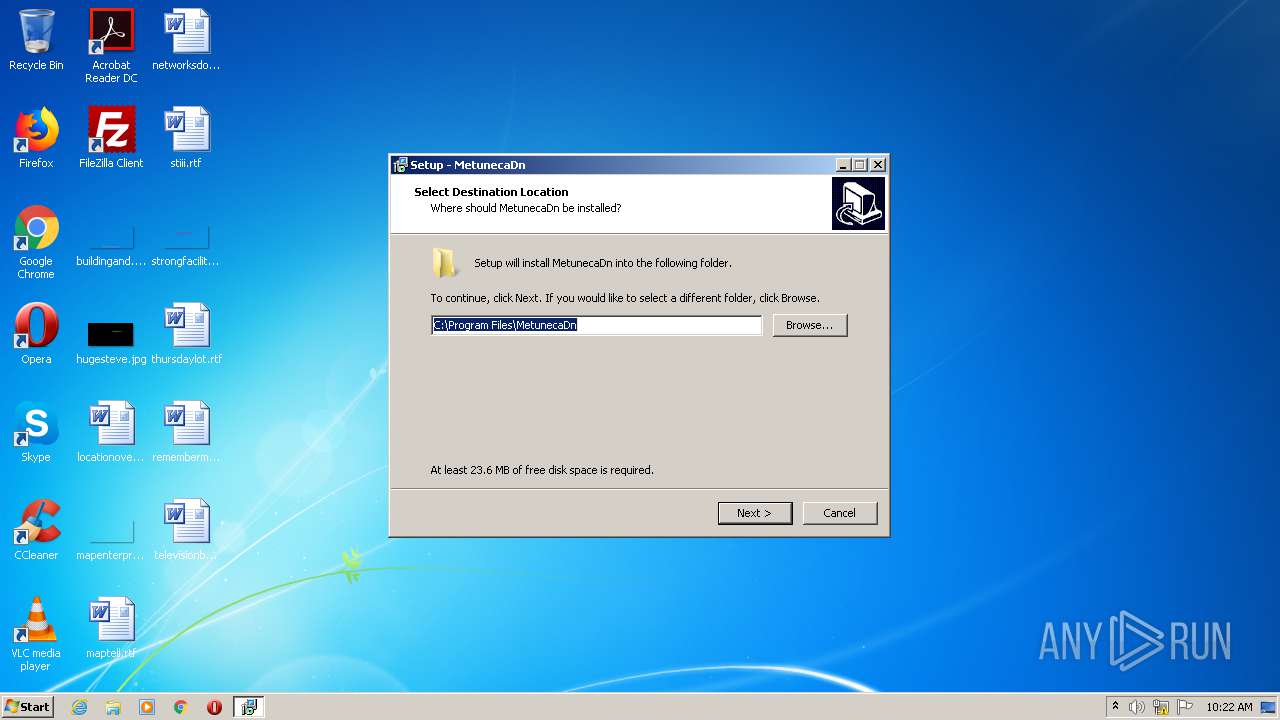
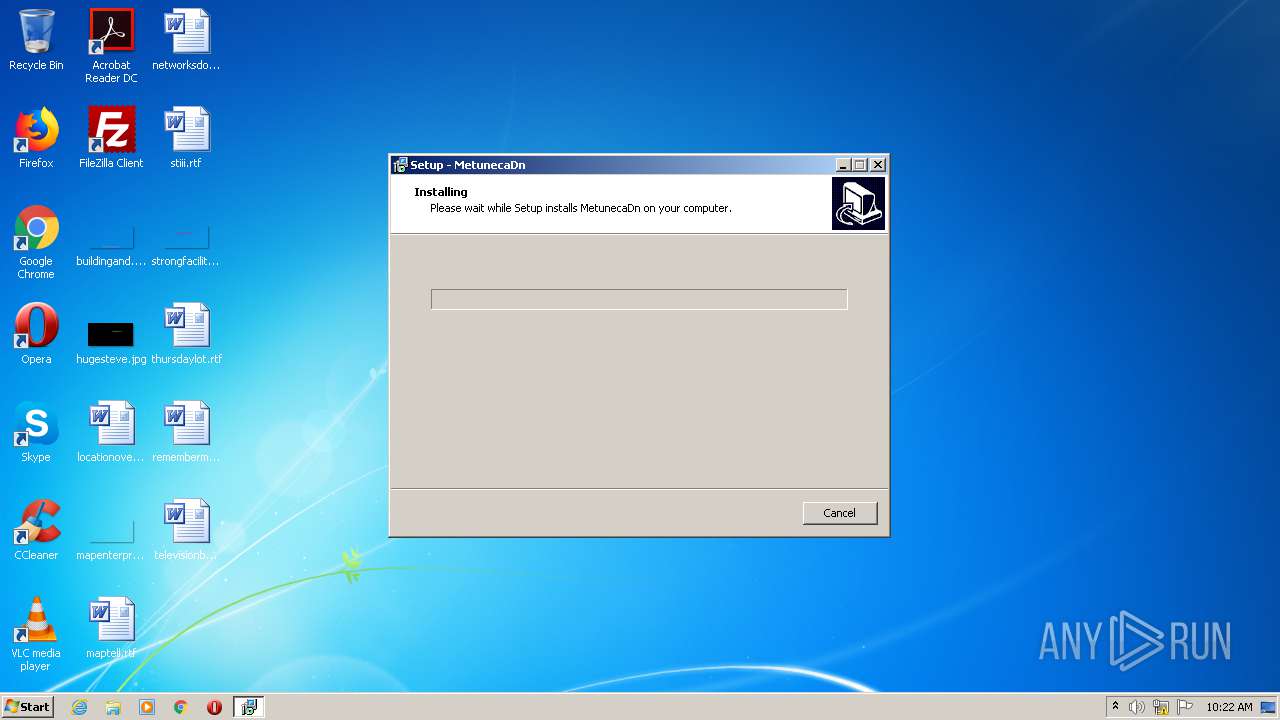
Executable content was dropped or overwritten
- SazInjector - Linkvertise Downloader_3701738712.exe (PID: 2712)
- SazInjector - Linkvertise Downloader_3701738712.exe (PID: 4088)
- SazInjector - Linkvertise Downloader_3701738712.tmp (PID: 2540)
Reads Windows owner or organization settings
- SazInjector - Linkvertise Downloader_3701738712.tmp (PID: 2540)
Reads the Windows organization settings
- SazInjector - Linkvertise Downloader_3701738712.tmp (PID: 2540)
INFO
Application was dropped or rewritten from another process
- SazInjector - Linkvertise Downloader_3701738712.tmp (PID: 1972)
- SazInjector - Linkvertise Downloader_3701738712.tmp (PID: 2540)
Creates files in the program directory
- SazInjector - Linkvertise Downloader_3701738712.tmp (PID: 2540)
Creates a software uninstall entry
- SazInjector - Linkvertise Downloader_3701738712.tmp (PID: 2540)
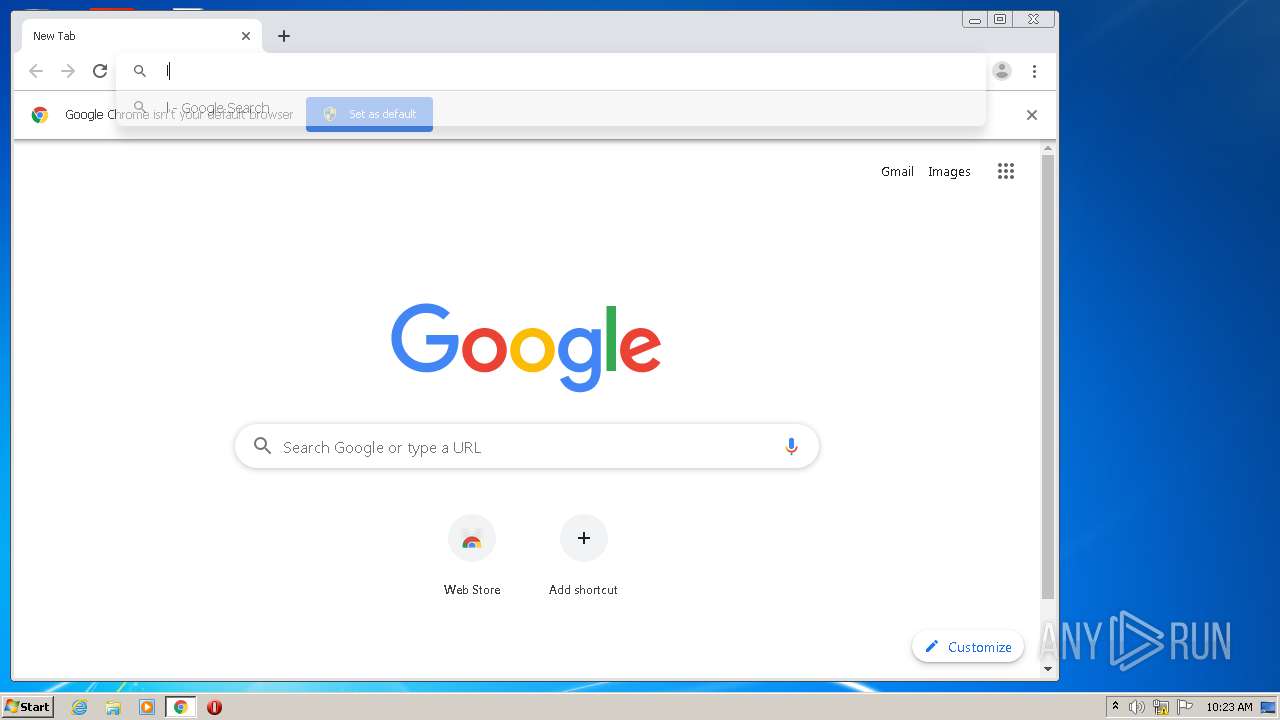
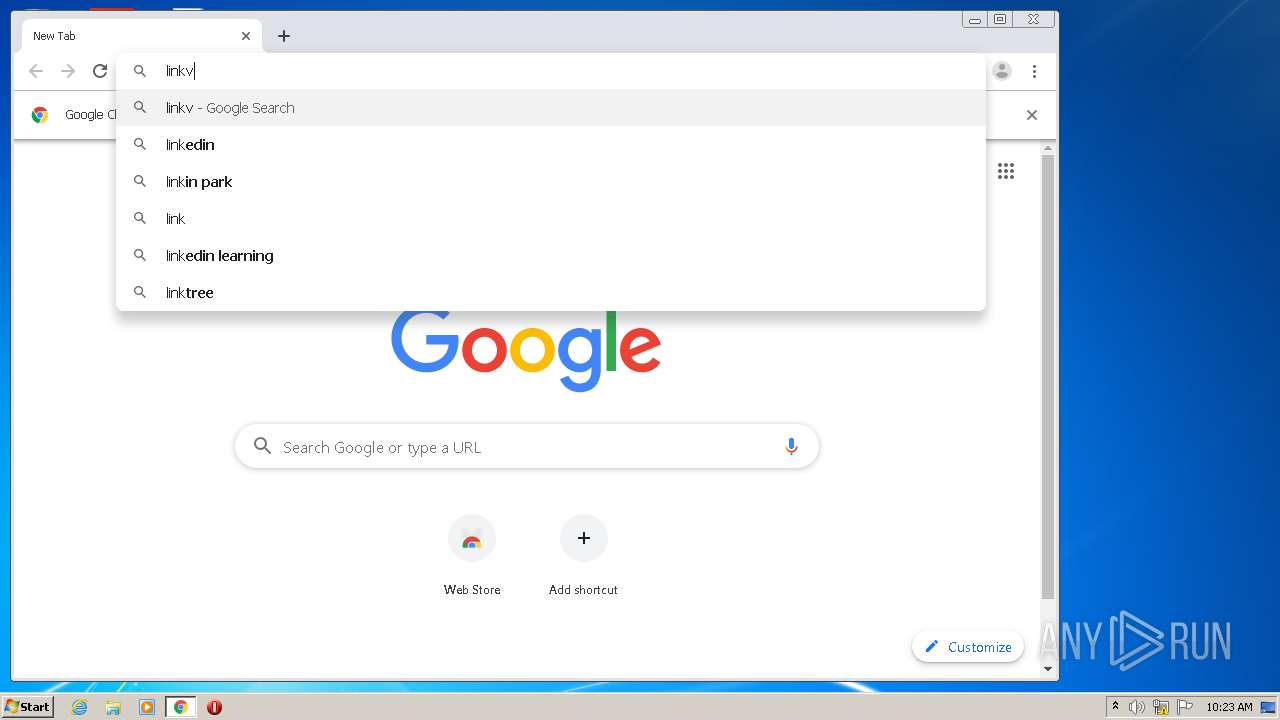
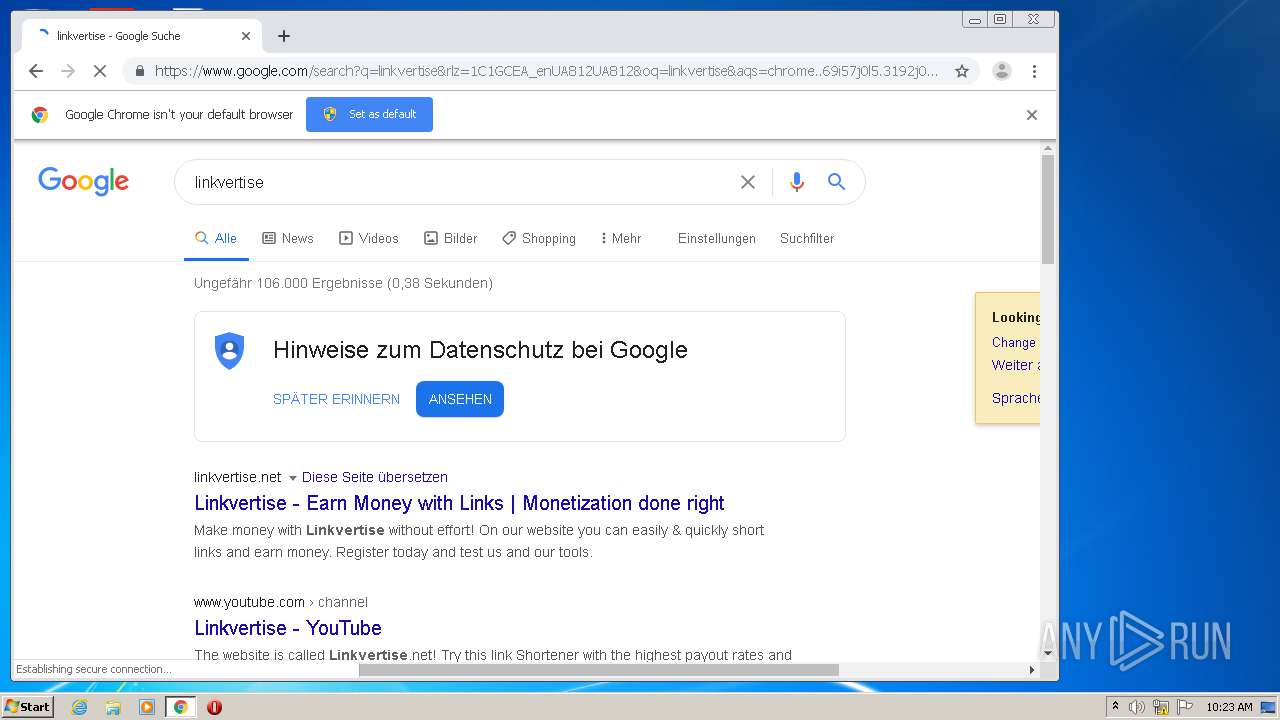
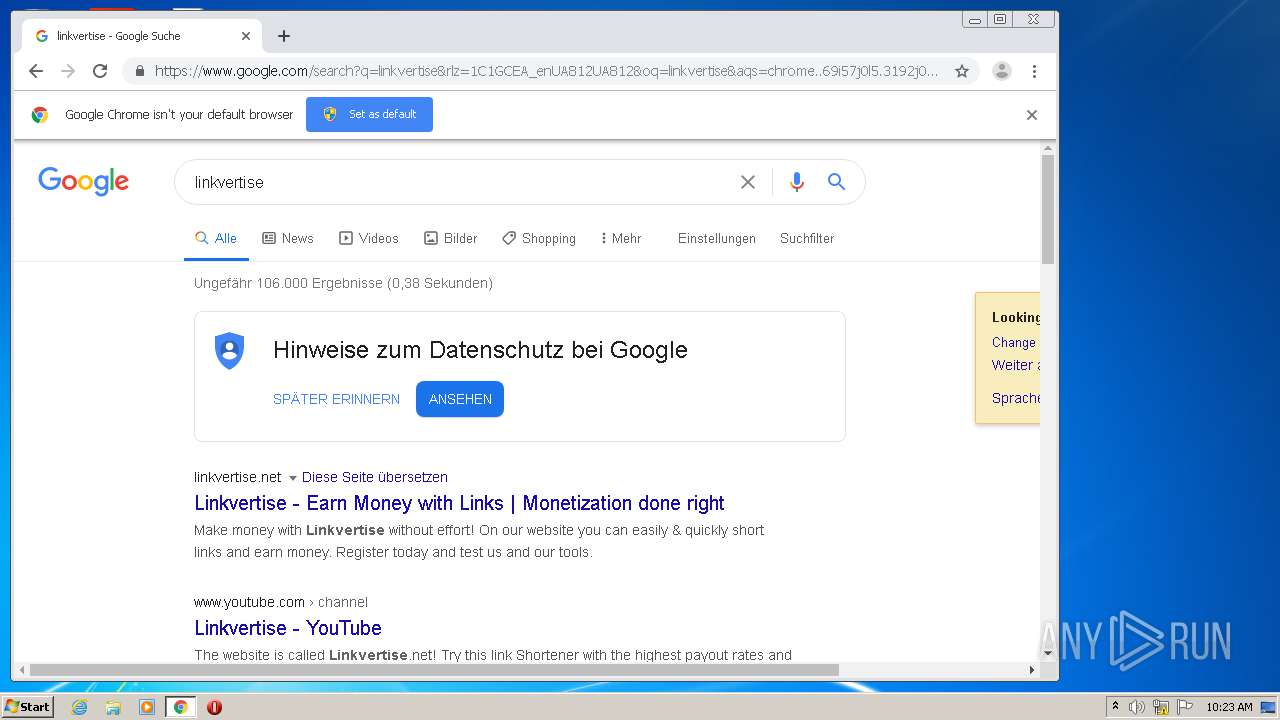
Manual execution by user
- chrome.exe (PID: 996)
Reads the hosts file
- chrome.exe (PID: 996)
- chrome.exe (PID: 2184)
Application launched itself
- chrome.exe (PID: 996)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (57.2) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (18.2) |
| .exe | | | Win16/32 Executable Delphi generic (8.3) |
| .exe | | | Generic Win/DOS Executable (8) |
| .exe | | | DOS Executable Generic (8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:06 16:39:04+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 66560 |
| InitializedDataSize: | 341504 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x117dc |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Galukur |
| FileDescription: | Kagate Setup |
| FileVersion: | |
| LegalCopyright: | Bog |
| ProductName: | Kagate |
| ProductVersion: | 5.8 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Apr-2016 14:39:04 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Galukur |
| FileDescription: | Kagate Setup |
| FileVersion: | - |
| LegalCopyright: | Bog |
| ProductName: | Kagate |
| ProductVersion: | 5.8 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 06-Apr-2016 14:39:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F244 | 0x0000F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.38613 |
.itext | 0x00011000 | 0x00000F64 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.73357 |
.data | 0x00012000 | 0x00000C88 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.29672 |
.bss | 0x00013000 | 0x000056BC | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00019000 | 0x00000E04 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.59781 |
.tls | 0x0001A000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001C000 | 0x000514B4 | 0x00051600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.79984 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.68674 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.48566 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.15192 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 4.97988 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 4.74381 | 38056 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 4.59278 | 67624 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 4.47543 | 152104 | Latin 1 / Western European | English - United States | RT_ICON |
4091 | 2.56031 | 104 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4092 | 3.25287 | 212 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
60
Monitored processes
19
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,1798433016403614856,11273094041747593199,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3494293623881336900 --mojo-platform-channel-handle=3588 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,1798433016403614856,11273094041747593199,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11607276384465600914 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3784 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,1798433016403614856,11273094041747593199,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4341882104102871966 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2484 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1044,1798433016403614856,11273094041747593199,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=14379230961341396597 --mojo-platform-channel-handle=3656 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1972 | "C:\Users\admin\AppData\Local\Temp\is-1L0V9.tmp\SazInjector - Linkvertise Downloader_3701738712.tmp" /SL5="$30136,3705830,409088,C:\Users\admin\AppData\Local\Temp\SazInjector - Linkvertise Downloader_3701738712.exe" | C:\Users\admin\AppData\Local\Temp\is-1L0V9.tmp\SazInjector - Linkvertise Downloader_3701738712.tmp | — | SazInjector - Linkvertise Downloader_3701738712.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 1 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,1798433016403614856,11273094041747593199,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7434056100346696273 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2188 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,1798433016403614856,11273094041747593199,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=6617655549655400933 --mojo-platform-channel-handle=1624 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2208 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,1798433016403614856,11273094041747593199,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15164014156031799603 --mojo-platform-channel-handle=3340 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2220 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,1798433016403614856,11273094041747593199,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18320444579660141886 --mojo-platform-channel-handle=3428 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
732
Read events
641
Write events
80
Delete events
11
Modification events
| (PID) Process: | (2540) SazInjector - Linkvertise Downloader_3701738712.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: EC09000072441C78656DD601 | |||
| (PID) Process: | (2540) SazInjector - Linkvertise Downloader_3701738712.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 5E52F773FE18DF8A5C9A51C141CCCFA39939C0C309A35825AF6D0E90F8CAADB8 | |||
| (PID) Process: | (2540) SazInjector - Linkvertise Downloader_3701738712.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2540) SazInjector - Linkvertise Downloader_3701738712.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\MetunecaDn\Bosuku.exe | |||
| (PID) Process: | (2540) SazInjector - Linkvertise Downloader_3701738712.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 61E47854A7B02CE4F6E831E6991C8193E982B6CC5C5F2C5A96B7E93AE206484E | |||
| (PID) Process: | (2540) SazInjector - Linkvertise Downloader_3701738712.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MetunecaDn_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.5.9 (u) | |||
| (PID) Process: | (2540) SazInjector - Linkvertise Downloader_3701738712.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MetunecaDn_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\MetunecaDn | |||
| (PID) Process: | (2540) SazInjector - Linkvertise Downloader_3701738712.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MetunecaDn_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\MetunecaDn\ | |||
| (PID) Process: | (2540) SazInjector - Linkvertise Downloader_3701738712.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MetunecaDn_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: MetunecaDn | |||
| (PID) Process: | (2540) SazInjector - Linkvertise Downloader_3701738712.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MetunecaDn_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
Executable files
3
Suspicious files
41
Text files
55
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2540 | SazInjector - Linkvertise Downloader_3701738712.tmp | C:\Program Files\MetunecaDn\is-2B61Q.tmp | — | |
MD5:— | SHA256:— | |||
| 2540 | SazInjector - Linkvertise Downloader_3701738712.tmp | C:\Program Files\MetunecaDn\is-KG121.tmp | — | |
MD5:— | SHA256:— | |||
| 2540 | SazInjector - Linkvertise Downloader_3701738712.tmp | C:\Program Files\MetunecaDn\is-V1NFD.tmp | — | |
MD5:— | SHA256:— | |||
| 2540 | SazInjector - Linkvertise Downloader_3701738712.tmp | C:\Program Files\MetunecaDn\is-2DSFF.tmp | — | |
MD5:— | SHA256:— | |||
| 2540 | SazInjector - Linkvertise Downloader_3701738712.tmp | C:\Program Files\MetunecaDn\is-2I623.tmp | — | |
MD5:— | SHA256:— | |||
| 2540 | SazInjector - Linkvertise Downloader_3701738712.tmp | C:\Program Files\MetunecaDn\is-M7GQD.tmp | — | |
MD5:— | SHA256:— | |||
| 2540 | SazInjector - Linkvertise Downloader_3701738712.tmp | C:\Program Files\MetunecaDn\is-1KKS7.tmp | — | |
MD5:— | SHA256:— | |||
| 2540 | SazInjector - Linkvertise Downloader_3701738712.tmp | C:\Program Files\MetunecaDn\is-2IOEH.tmp | — | |
MD5:— | SHA256:— | |||
| 2540 | SazInjector - Linkvertise Downloader_3701738712.tmp | C:\Program Files\MetunecaDn\is-R8UOC.tmp | — | |
MD5:— | SHA256:— | |||
| 2540 | SazInjector - Linkvertise Downloader_3701738712.tmp | C:\Program Files\MetunecaDn\is-1CCGR.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
19
DNS requests
14
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2184 | chrome.exe | 172.217.16.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
2184 | chrome.exe | 172.217.23.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2184 | chrome.exe | 216.58.207.36:443 | www.google.com | Google Inc. | US | whitelisted |
2184 | chrome.exe | 172.217.23.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2184 | chrome.exe | 172.217.21.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2184 | chrome.exe | 172.217.22.110:443 | apis.google.com | Google Inc. | US | whitelisted |
2184 | chrome.exe | 172.217.18.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
2184 | chrome.exe | 172.217.22.35:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2184 | chrome.exe | 172.217.21.238:443 | ogs.google.com | Google Inc. | US | whitelisted |
2184 | chrome.exe | 172.64.97.24:443 | linkvertise.net | Cloudflare Inc | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
consent.google.com |
| shared |