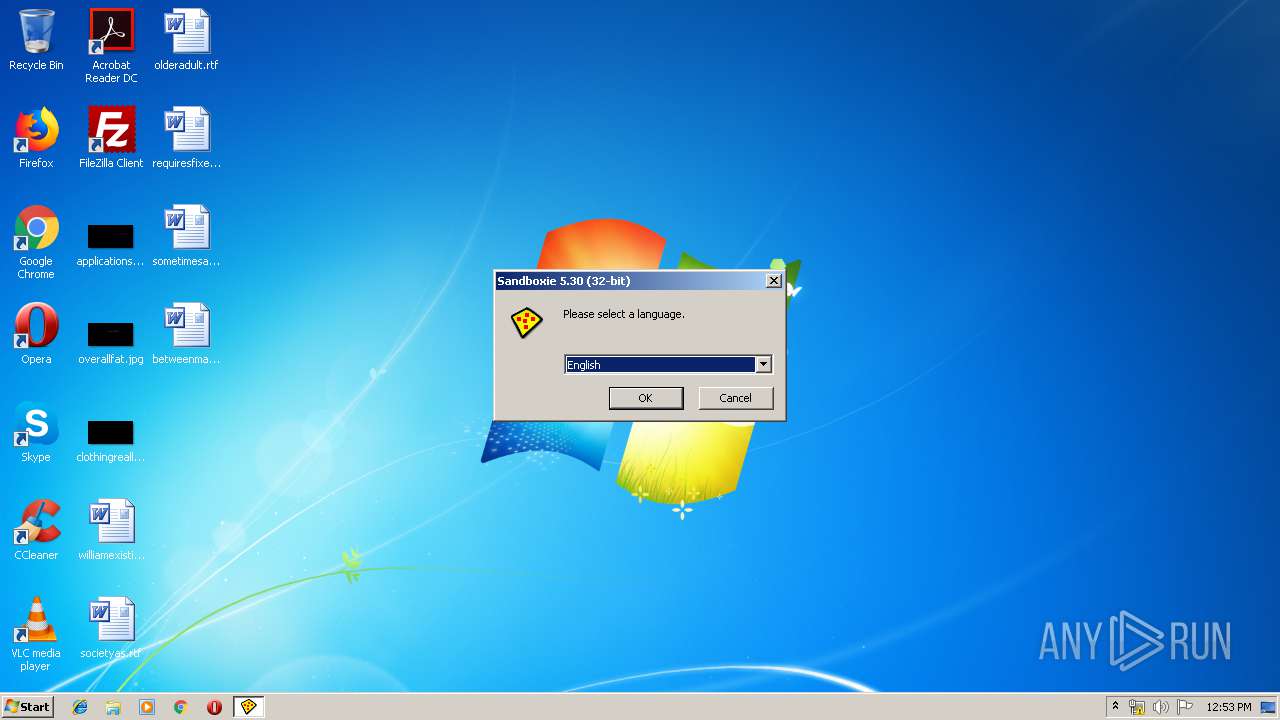
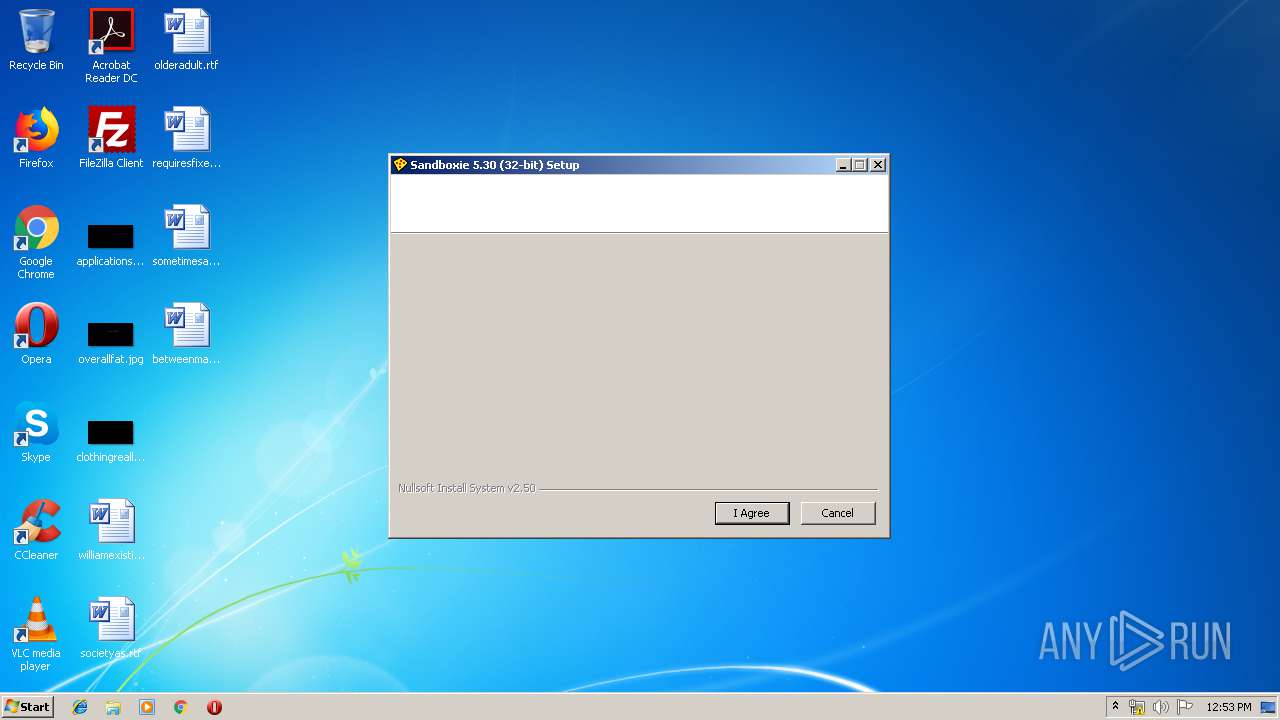
| File name: | Sandboxie.v5.30.exe |
| Full analysis: | https://app.any.run/tasks/da1c02b2-78e8-46d9-9d08-8393d8bb0435 |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2019, 11:52:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B683407B3DCDBE53EB7C72AA53419840 |
| SHA1: | 1432E2151E1D9E9C1A1980A80CADCC43EF96C31C |
| SHA256: | 92622500E31D5F103F96FAADF2A93C8E1F7F9C2EFD90FCE02794FD4EEFDC3142 |
| SSDEEP: | 98304:HbVSoDLZWFpiY/kGoQT2JcLS5v6+MyoclvgD3F8yUNZWCRXdSVR+lSUs0ZG/0iRv:ZRL/qFgi+nopF8XZpXd0wlJ4aa39Mw |
MALICIOUS
Loads dropped or rewritten executable
- sbie32inst.exe (PID: 2940)
- Sandboxie.v5.30.exe (PID: 3460)
- KmdUtil.exe (PID: 1824)
- KmdUtil.exe (PID: 3612)
- SbieSvc.exe (PID: 1248)
- KmdUtil.exe (PID: 3428)
- Start.exe (PID: 2792)
- KmdUtil.exe (PID: 3496)
- KmdUtil.exe (PID: 1736)
- KmdUtil.exe (PID: 3116)
- License.exe (PID: 2980)
- License.exe (PID: 936)
- SbieCtrl.exe (PID: 3560)
- SbieCtrl.exe (PID: 2668)
Application was dropped or rewritten from another process
- sbie32inst.exe (PID: 2940)
- KmdUtil.exe (PID: 3496)
- KmdUtil.exe (PID: 1824)
- KmdUtil.exe (PID: 3612)
- Start.exe (PID: 2792)
- KmdUtil.exe (PID: 1736)
- KmdUtil.exe (PID: 3116)
- KmdUtil.exe (PID: 3428)
- SbieSvc.exe (PID: 1248)
- sbiekg.exe (PID: 2856)
- License.exe (PID: 936)
- SbieCtrl.exe (PID: 2668)
- SbieCtrl.exe (PID: 3560)
- License.exe (PID: 2980)
SUSPICIOUS
Executable content was dropped or overwritten
- sbie32inst.exe (PID: 2940)
- Sandboxie.v5.30.exe (PID: 3460)
Creates or modifies windows services
- sbie32inst.exe (PID: 2940)
- KmdUtil.exe (PID: 1736)
- Sandboxie.v5.30.exe (PID: 3460)
Creates files in the program directory
- sbie32inst.exe (PID: 2940)
- Sandboxie.v5.30.exe (PID: 3460)
Creates a software uninstall entry
- sbie32inst.exe (PID: 2940)
Removes files from Windows directory
- SbieSvc.exe (PID: 1248)
Creates files in the Windows directory
- SbieSvc.exe (PID: 1248)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:02:24 20:19:59+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 28672 |
| InitializedDataSize: | 445952 |
| UninitializedDataSize: | 16896 |
| EntryPoint: | 0x39e3 |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.30.0.0 |
| ProductVersionNumber: | 5.30.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | Sandboxie Holdings, LLC |
| FileDescription: | Sandboxie v5.30 |
| FileVersion: | 5.30.0.0 |
| LegalCopyright: | © Sandboxie Holdings, LLC |
| ProductName: | Sandboxie v5.30 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Feb-2012 19:19:59 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | Sandboxie Holdings, LLC |
| FileDescription: | Sandboxie v5.30 |
| FileVersion: | 5.30.0.0 |
| LegalCopyright: | © Sandboxie Holdings, LLC |
| ProductName: | Sandboxie v5.30 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 24-Feb-2012 19:19:59 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006F10 | 0x00007000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.49816 |
.rdata | 0x00008000 | 0x00002A92 | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.39389 |
.data | 0x0000B000 | 0x00067EBC | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.47278 |
.ndata | 0x00073000 | 0x000A1000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00114000 | 0x00010E10 | 0x00011000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.93635 |
.reloc | 0x00125000 | 0x00000F8A | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 7.88751 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.22222 | 968 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.71741 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 3.05563 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 3.49446 | 2216 | UNKNOWN | English - United States | RT_ICON |
5 | 0 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 0 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 0 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 2.89248 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.54849 | 244 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.88287 | 272 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
49
Monitored processes
16
Malicious processes
3
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
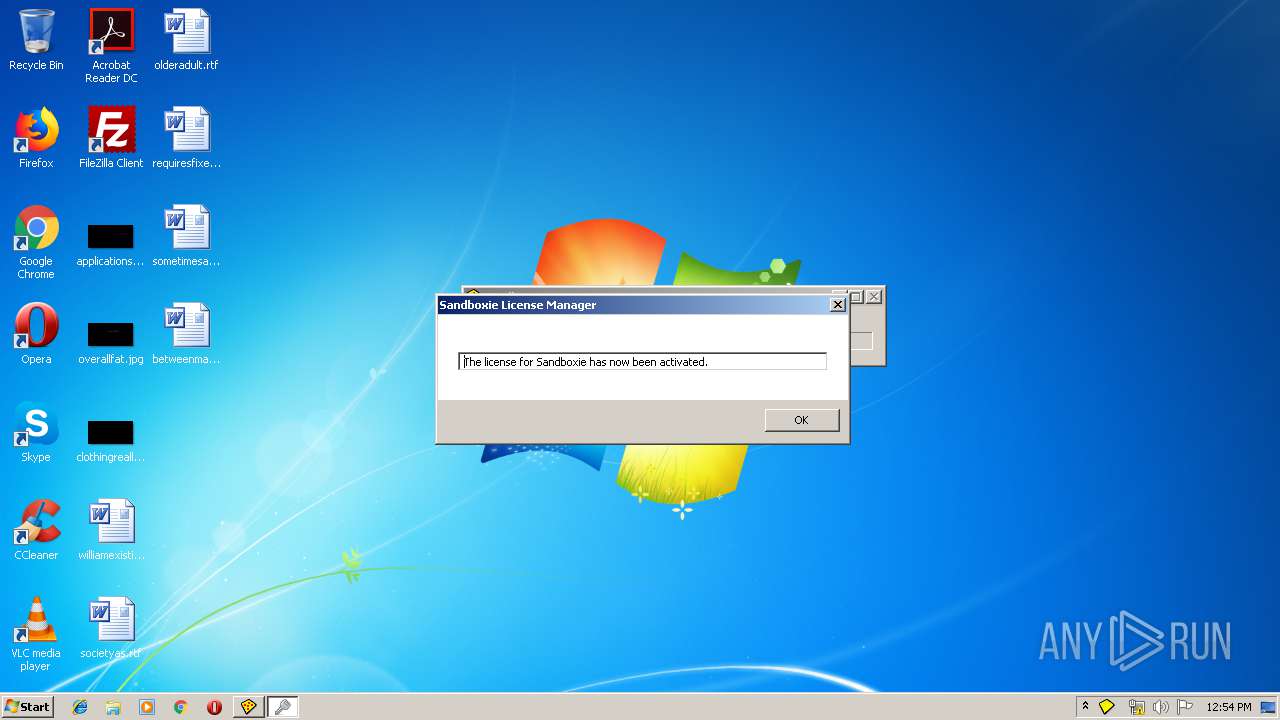
| 936 | License.exe activate NP89ZT93PEXF53691MY2DK5B50IV1JTENWQY7O7A205I2NQV9PQUQKPXO3BAHB5KQK681N67FRLX6SNH9BRH14HQOQWC6Z39N1E7DRODLRWX52Y7J24P3JVF7E8TRIV8W5FP97OV6UR4VRE87MSC2Z1EF8CZDM1GPIF26A2XYFLXDMYIP0I5MZEMIHH6OY11HPYZN4JDK3RUWPM1U3M3JPFUNIMCTUAPDFL9J4YI8W9U4VG2EWNXU712JNZ3JL8JG6LHF7O85YBDSSPLJYSRUD5YX3SZLMJOYNJQUESTK786XM0JECD4YVYKET5L388F88UH02UFXWNI6UIJPKKS9J0OIOPSCU199CQ8WO3TMJDU3U4UCJGW6FI1SC45EOYHCZY27CIBE4N4 | C:\Program Files\Sandboxie\License.exe | — | sbiekg.exe | |||||||||||
User: admin Company: Sandboxie Holdings, LLC Integrity Level: HIGH Description: Sandboxie License Manager Exit code: 0 Version: 5.30 Modules
| |||||||||||||||
| 1248 | "C:\Program Files\Sandboxie\SbieSvc.exe" | C:\Program Files\Sandboxie\SbieSvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Sandboxie Holdings, LLC Integrity Level: SYSTEM Description: Sandboxie Service Exit code: 0 Version: 5.30 Modules
| |||||||||||||||
| 1736 | "C:\Users\admin\AppData\Local\Temp\nsr1DD3.tmp\KmdUtil.exe" /lang=1033 install SbieDrv "C:\Program Files\Sandboxie\SbieDrv.sys" type=kernel start=demand "msgfile=C:\Program Files\Sandboxie\SbieMsg.dll" altitude=86900 | C:\Users\admin\AppData\Local\Temp\nsr1DD3.tmp\KmdUtil.exe | — | sbie32inst.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1824 | "C:\Users\admin\AppData\Local\Temp\nsr1DD3.tmp\KmdUtil.exe" /lang=1033 stop SbieSvc | C:\Users\admin\AppData\Local\Temp\nsr1DD3.tmp\KmdUtil.exe | — | sbie32inst.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2440 | "C:\Users\admin\AppData\Local\Temp\Sandboxie.v5.30.exe" | C:\Users\admin\AppData\Local\Temp\Sandboxie.v5.30.exe | — | explorer.exe | |||||||||||
User: admin Company: Sandboxie Holdings, LLC Integrity Level: MEDIUM Description: Sandboxie v5.30 Exit code: 3221226540 Version: 5.30.0.0 Modules
| |||||||||||||||
| 2668 | "C:\Program Files\Sandboxie\SbieCtrl.exe" | C:\Program Files\Sandboxie\SbieCtrl.exe | — | Sandboxie.v5.30.exe | |||||||||||
User: admin Company: Sandboxie Holdings, LLC Integrity Level: HIGH Description: Sandboxie Control Exit code: 0 Version: 5.30 Modules
| |||||||||||||||
| 2792 | "C:\Program Files\Sandboxie\Start.exe" run_sbie_ctrl | C:\Program Files\Sandboxie\Start.exe | — | sbie32inst.exe | |||||||||||
User: admin Company: Sandboxie Holdings, LLC Integrity Level: HIGH Description: Sandboxie Start Exit code: 0 Version: 5.30 Modules
| |||||||||||||||
| 2856 | C:\Users\admin\AppData\Local\Temp\nsy9BE.tmp\sbiekg.exe | C:\Users\admin\AppData\Local\Temp\nsy9BE.tmp\sbiekg.exe | — | Sandboxie.v5.30.exe | |||||||||||
User: admin Company: UUK Integrity Level: HIGH Description: Keygen for Sandboxie Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 2940 | C:\Users\admin\AppData\Local\Temp\nsy9BE.tmp\sbie32inst.exe | C:\Users\admin\AppData\Local\Temp\nsy9BE.tmp\sbie32inst.exe | Sandboxie.v5.30.exe | ||||||||||||
User: admin Company: Sandboxie Holdings, LLC Integrity Level: HIGH Description: Sandboxie Installer Exit code: 0 Version: 5.30 Modules
| |||||||||||||||
| 2980 | "C:\Program Files\Sandboxie\License.exe" print syscode | C:\Program Files\Sandboxie\License.exe | — | Sandboxie.v5.30.exe | |||||||||||
User: admin Company: Sandboxie Holdings, LLC Integrity Level: HIGH Description: Sandboxie License Manager Exit code: 0 Version: 5.30 Modules
| |||||||||||||||
Total events
753
Read events
711
Write events
42
Delete events
0
Modification events
| (PID) Process: | (3460) Sandboxie.v5.30.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3460) Sandboxie.v5.30.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2940) sbie32inst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\sbie32inst_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2940) sbie32inst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\sbie32inst_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2940) sbie32inst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\sbie32inst_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2940) sbie32inst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\sbie32inst_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2940) sbie32inst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\sbie32inst_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2940) sbie32inst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\sbie32inst_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2940) sbie32inst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\sbie32inst_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2940) sbie32inst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\sbie32inst_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
31
Suspicious files
18
Text files
39
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3460 | Sandboxie.v5.30.exe | C:\Users\admin\AppData\Local\Temp\nsy9BE.tmp\sbiekg.exe | executable | |
MD5:— | SHA256:— | |||
| 2940 | sbie32inst.exe | C:\Users\admin\AppData\Local\Temp\nsr1DD3.tmp\ioSpecial.ini | text | |
MD5:— | SHA256:— | |||
| 3460 | Sandboxie.v5.30.exe | C:\Users\admin\AppData\Local\Temp\nsy9BE.tmp\sbie64inst.exe | executable | |
MD5:— | SHA256:— | |||
| 3460 | Sandboxie.v5.30.exe | C:\Users\admin\AppData\Local\Temp\nsy9BE.tmp\sbie32inst.exe | executable | |
MD5:— | SHA256:— | |||
| 3460 | Sandboxie.v5.30.exe | C:\Users\admin\AppData\Local\Temp\nsy9BE.tmp\newadvsplash.dll | executable | |
MD5:55A723E125AFBC9B3A41D46F41749068 | SHA256:0A70CC4B93D87ECD93E538CFBED7C9A4B8B5C6F1042C6069757BDA0D1279ED06 | |||
| 2940 | sbie32inst.exe | C:\Users\admin\AppData\Local\Temp\nsr1DD3.tmp\SbieMsg.dll | executable | |
MD5:— | SHA256:— | |||
| 3460 | Sandboxie.v5.30.exe | C:\Users\admin\AppData\Local\Temp\nsy9BE.tmp\System.dll | executable | |
MD5:BF712F32249029466FA86756F5546950 | SHA256:7851CB12FA4131F1FEE5DE390D650EF65CAC561279F1CFE70AD16CC9780210AF | |||
| 2940 | sbie32inst.exe | C:\Program Files\Sandboxie\SbieMsg.dll | executable | |
MD5:— | SHA256:— | |||
| 2940 | sbie32inst.exe | C:\Program Files\Sandboxie\SbieSvc.exe | executable | |
MD5:— | SHA256:— | |||
| 2940 | sbie32inst.exe | C:\Users\admin\AppData\Local\Temp\nsr1DD3.tmp\SbieDll.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
8
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2940 | sbie32inst.exe | 13.35.253.49:443 | www.sandboxie.com | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.sandboxie.com |
| shared |