| File name: | 925d041a3644e54fe2642bd3523ba849d84ab5ff49ad3f352dce10f88b3ddfea |
| Full analysis: | https://app.any.run/tasks/7ade0052-e01a-4e49-b01c-7db41fad03ed |
| Verdict: | Malicious activity |
| Analysis date: | December 05, 2022, 17:11:20 |
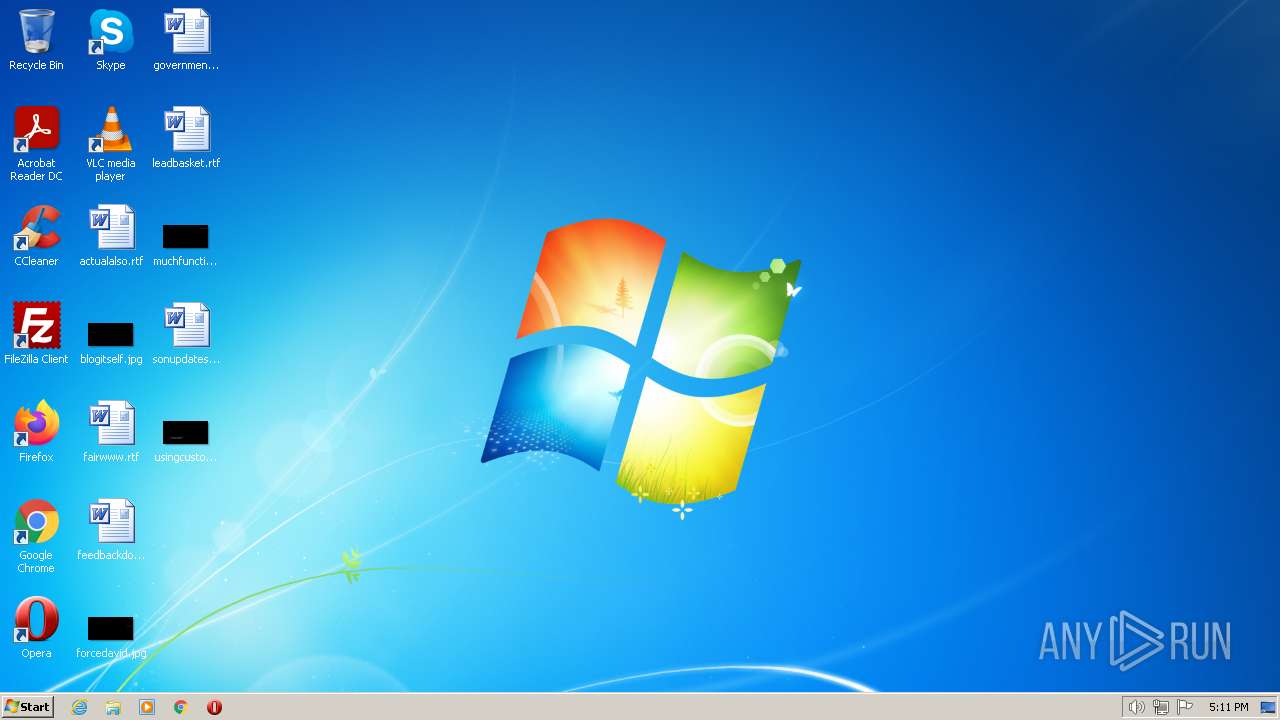
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 796AECCF02F72F83512F2EB88AA5A2D3 |
| SHA1: | D289F3AE5C8D92D25A93BF92BB90591F232A1142 |
| SHA256: | 925D041A3644E54FE2642BD3523BA849D84AB5FF49AD3F352DCE10F88B3DDFEA |
| SSDEEP: | 6144:11ePsPFKYLSCwZJOcUoSSwu5To9X08n3LD9GqBDVUrhOHkz3lKqLU05:10kPFzIOcUoSSwu5To9XvLD9pBDVU0kX |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the Internet Settings
- 925d041a3644e54fe2642bd3523ba849d84ab5ff49ad3f352dce10f88b3ddfea.exe (PID: 856)
Checks Windows Trust Settings
- 925d041a3644e54fe2642bd3523ba849d84ab5ff49ad3f352dce10f88b3ddfea.exe (PID: 856)
Reads security settings of Internet Explorer
- 925d041a3644e54fe2642bd3523ba849d84ab5ff49ad3f352dce10f88b3ddfea.exe (PID: 856)
Reads settings of System Certificates
- 925d041a3644e54fe2642bd3523ba849d84ab5ff49ad3f352dce10f88b3ddfea.exe (PID: 856)
Connects to the server without a host name
- 925d041a3644e54fe2642bd3523ba849d84ab5ff49ad3f352dce10f88b3ddfea.exe (PID: 856)
INFO
Reads the computer name
- 925d041a3644e54fe2642bd3523ba849d84ab5ff49ad3f352dce10f88b3ddfea.exe (PID: 856)
Checks supported languages
- 925d041a3644e54fe2642bd3523ba849d84ab5ff49ad3f352dce10f88b3ddfea.exe (PID: 856)
Checks proxy server information
- 925d041a3644e54fe2642bd3523ba849d84ab5ff49ad3f352dce10f88b3ddfea.exe (PID: 856)
Manual execution by a user
- explorer.exe (PID: 2992)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 2022-Nov-28 15:21:52 |
DOS Header
| e_magic: | MZ |
|---|---|
| e_cblp: | 144 |
| e_cp: | 3 |
| e_crlc: | - |
| e_cparhdr: | 4 |
| e_minalloc: | - |
| e_maxalloc: | 65535 |
| e_ss: | - |
| e_sp: | 184 |
| e_csum: | - |
| e_ip: | - |
| e_cs: | - |
| e_ovno: | - |
| e_oemid: | - |
| e_oeminfo: | - |
| e_lfanew: | 240 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| NumberofSections: | 4 |
| TimeDateStamp: | 2022-Nov-28 15:21:52 |
| PointerToSymbolTable: | - |
| NumberOfSymbols: | - |
| SizeOfOptionalHeader: | 224 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 4096 | 210947 | 211456 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.55554 |
.rdata | 217088 | 59068 | 59392 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.66304 |
.data | 278528 | 86372 | 7168 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.9467 |
.reloc | 368640 | 19450 | 19456 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.15194 |
Imports
KERNEL32.dll |
Total processes
40
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 856 | "C:\Users\admin\AppData\Local\Temp\925d041a3644e54fe2642bd3523ba849d84ab5ff49ad3f352dce10f88b3ddfea.exe" | C:\Users\admin\AppData\Local\Temp\925d041a3644e54fe2642bd3523ba849d84ab5ff49ad3f352dce10f88b3ddfea.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2992 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 428
Read events
3 379
Write events
48
Delete events
1
Modification events
| (PID) Process: | (856) 925d041a3644e54fe2642bd3523ba849d84ab5ff49ad3f352dce10f88b3ddfea.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (856) 925d041a3644e54fe2642bd3523ba849d84ab5ff49ad3f352dce10f88b3ddfea.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (856) 925d041a3644e54fe2642bd3523ba849d84ab5ff49ad3f352dce10f88b3ddfea.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (856) 925d041a3644e54fe2642bd3523ba849d84ab5ff49ad3f352dce10f88b3ddfea.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (856) 925d041a3644e54fe2642bd3523ba849d84ab5ff49ad3f352dce10f88b3ddfea.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003D010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (856) 925d041a3644e54fe2642bd3523ba849d84ab5ff49ad3f352dce10f88b3ddfea.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (856) 925d041a3644e54fe2642bd3523ba849d84ab5ff49ad3f352dce10f88b3ddfea.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (856) 925d041a3644e54fe2642bd3523ba849d84ab5ff49ad3f352dce10f88b3ddfea.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (856) 925d041a3644e54fe2642bd3523ba849d84ab5ff49ad3f352dce10f88b3ddfea.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (856) 925d041a3644e54fe2642bd3523ba849d84ab5ff49ad3f352dce10f88b3ddfea.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\{FCC67766-6201-4AD1-A6B8-2F4553C93D47} |
| Operation: | write | Name: | WpadDecisionReason |
Value: 1 | |||
Executable files
0
Suspicious files
3
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 856 | 925d041a3644e54fe2642bd3523ba849d84ab5ff49ad3f352dce10f88b3ddfea.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\0270780F846F08BEFE0DD8112D932FEF | der | |
MD5:— | SHA256:— | |||
| 856 | 925d041a3644e54fe2642bd3523ba849d84ab5ff49ad3f352dce10f88b3ddfea.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 856 | 925d041a3644e54fe2642bd3523ba849d84ab5ff49ad3f352dce10f88b3ddfea.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\0270780F846F08BEFE0DD8112D932FEF | binary | |
MD5:— | SHA256:— | |||
| 856 | 925d041a3644e54fe2642bd3523ba849d84ab5ff49ad3f352dce10f88b3ddfea.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
8
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
856 | 925d041a3644e54fe2642bd3523ba849d84ab5ff49ad3f352dce10f88b3ddfea.exe | GET | — | 116.202.6.206:80 | http://116.202.6.206/1826 | DE | — | — | malicious |
856 | 925d041a3644e54fe2642bd3523ba849d84ab5ff49ad3f352dce10f88b3ddfea.exe | GET | 200 | 93.184.220.29:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 740 b | whitelisted |
856 | 925d041a3644e54fe2642bd3523ba849d84ab5ff49ad3f352dce10f88b3ddfea.exe | GET | 200 | 13.107.4.50:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?22556e7596ad35f3 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
856 | 925d041a3644e54fe2642bd3523ba849d84ab5ff49ad3f352dce10f88b3ddfea.exe | 149.154.167.99:443 | t.me | Telegram Messenger Inc | GB | malicious |
856 | 925d041a3644e54fe2642bd3523ba849d84ab5ff49ad3f352dce10f88b3ddfea.exe | 184.30.209.160:443 | steamcommunity.com | AKAMAI-AS | DE | whitelisted |
— | — | 93.184.220.29:80 | ocsp.digicert.com | EDGECAST | GB | whitelisted |
856 | 925d041a3644e54fe2642bd3523ba849d84ab5ff49ad3f352dce10f88b3ddfea.exe | 13.107.4.50:80 | ctldl.windowsupdate.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
856 | 925d041a3644e54fe2642bd3523ba849d84ab5ff49ad3f352dce10f88b3ddfea.exe | 93.184.220.29:80 | ocsp.digicert.com | EDGECAST | GB | whitelisted |
856 | 925d041a3644e54fe2642bd3523ba849d84ab5ff49ad3f352dce10f88b3ddfea.exe | 116.202.6.206:80 | — | Hetzner Online GmbH | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
t.me |
| whitelisted |
dns.msftncsi.com |
| shared |
steamcommunity.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |