| URL: | http://yayasanrumahkita.com/eqdx/TKWBN-cOKlwF3Cuuj2YoP_DIjOiVfii-suE/ |
| Full analysis: | https://app.any.run/tasks/d0b00074-4d47-4948-8651-9485e8af039a |
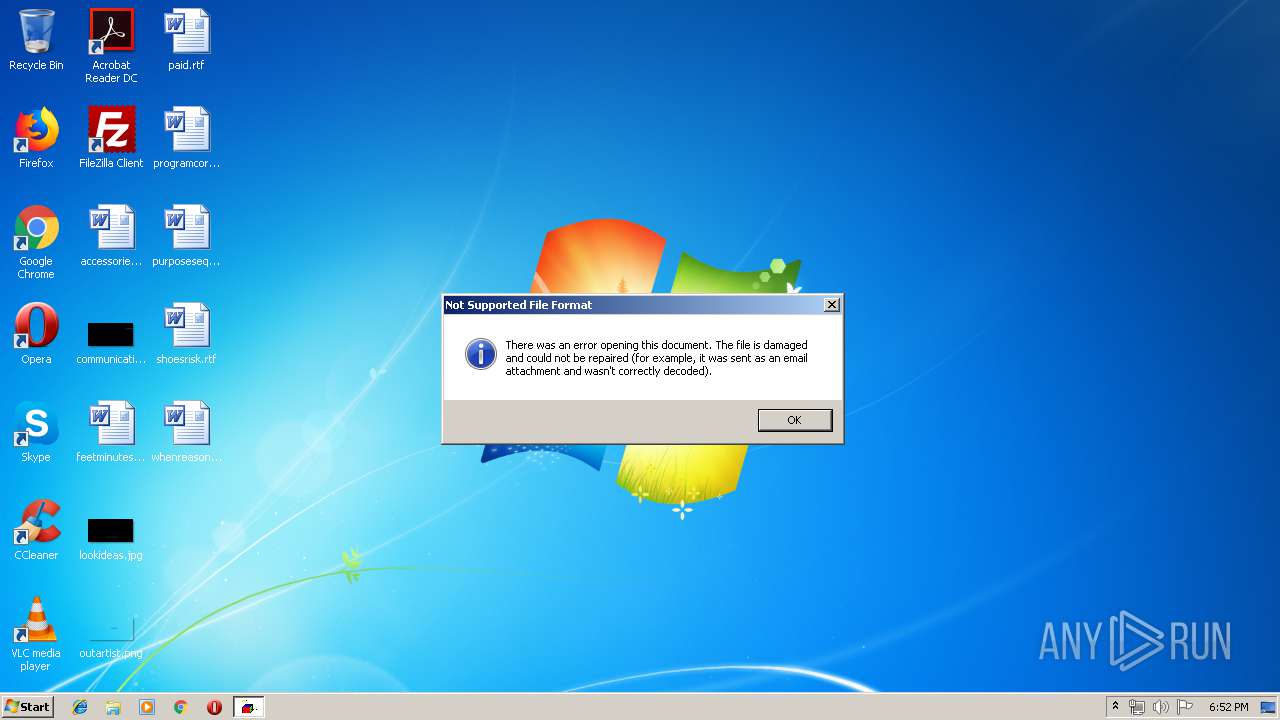
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | April 23, 2019, 17:52:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 0C19CC5126BF6AF1A792CBFE712970A6 |
| SHA1: | 7BF2082102B675AAFE341BECF68D51686AF9E327 |
| SHA256: | 923E95C3698C31DC62E7002870AB0489BA560087074A74B12E55402AAC6B7776 |
| SSDEEP: | 3:N1KHAqjbTKsFcMcjHPcQMJn:CgSlcj0b |
MALICIOUS
Application was dropped or rewritten from another process
- gvg7puwk9.exe (PID: 3176)
- gvg7puwk9.exe (PID: 2752)
- soundser.exe (PID: 2368)
- soundser.exe (PID: 2696)
- 8ihwMIAoKIsX9g.exe (PID: 2512)
- 8ihwMIAoKIsX9g.exe (PID: 3520)
- soundser.exe (PID: 3804)
- soundser.exe (PID: 3360)
EMOTET was detected
- soundser.exe (PID: 2696)
- soundser.exe (PID: 3360)
Connects to CnC server
- soundser.exe (PID: 2696)
- soundser.exe (PID: 3360)
Emotet process was detected
- soundser.exe (PID: 2368)
- soundser.exe (PID: 3804)
Changes the autorun value in the registry
- soundser.exe (PID: 2696)
- soundser.exe (PID: 3360)
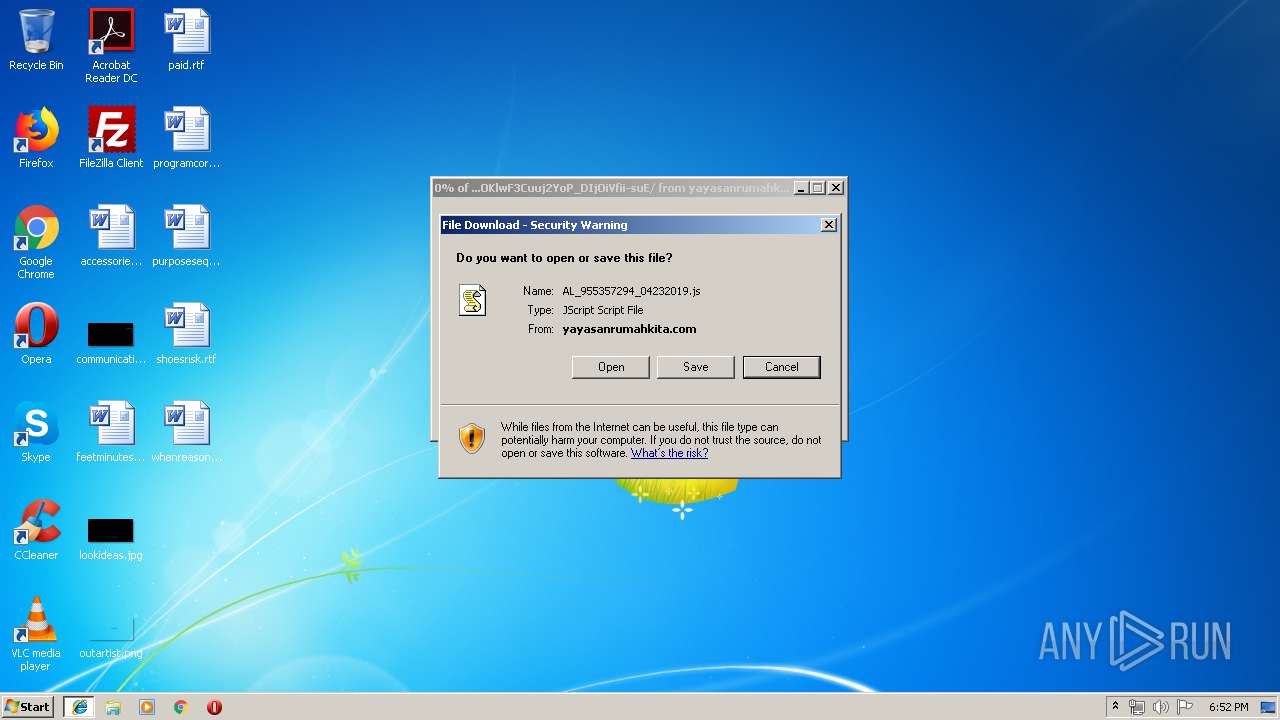
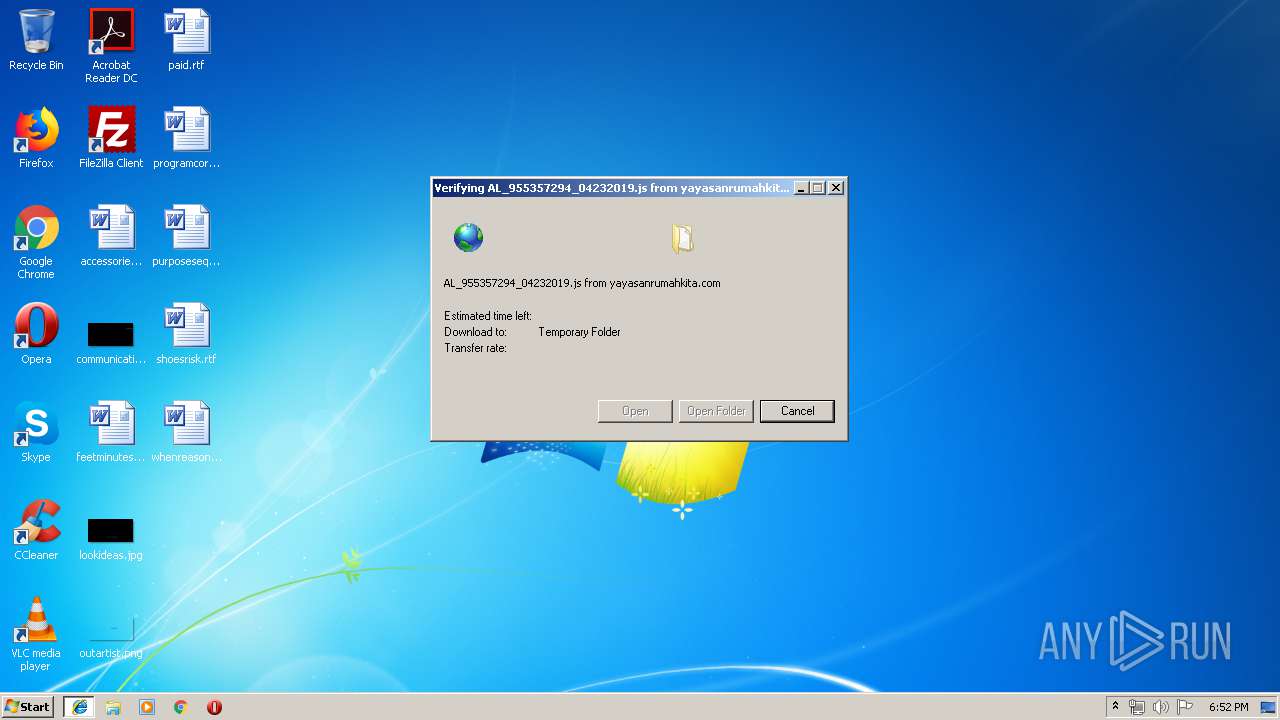
Downloads executable files from the Internet
- WScript.exe (PID: 2392)
SUSPICIOUS
Starts itself from another location
- gvg7puwk9.exe (PID: 2752)
- 8ihwMIAoKIsX9g.exe (PID: 3520)
Executable content was dropped or overwritten
- gvg7puwk9.exe (PID: 2752)
- soundser.exe (PID: 2696)
- 8ihwMIAoKIsX9g.exe (PID: 3520)
- WScript.exe (PID: 2392)
Connects to server without host name
- soundser.exe (PID: 2696)
- soundser.exe (PID: 3360)
Creates files in the user directory
- WScript.exe (PID: 2392)
Application launched itself
- 8ihwMIAoKIsX9g.exe (PID: 2512)
- soundser.exe (PID: 3804)
- gvg7puwk9.exe (PID: 3176)
Executes scripts
- iexplore.exe (PID: 3896)
INFO
Application launched itself
- iexplore.exe (PID: 3896)
Creates files in the user directory
- iexplore.exe (PID: 4012)
Reads Internet Cache Settings
- iexplore.exe (PID: 4012)
Changes internet zones settings
- iexplore.exe (PID: 3896)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
41
Monitored processes
11
Malicious processes
10
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2368 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | gvg7puwk9.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2392 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\TKWBN-cOKlwF3Cuuj2YoP_DIjOiVfii-suE[1].js" | C:\Windows\System32\WScript.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2512 | "C:\Users\admin\AppData\Local\soundser\8ihwMIAoKIsX9g.exe" | C:\Users\admin\AppData\Local\soundser\8ihwMIAoKIsX9g.exe | — | soundser.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Device Properties Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2696 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2752 | --16cc3c05 | C:\Users\admin\AppData\Local\Temp\gvg7puwk9.exe | gvg7puwk9.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3176 | "C:\Users\admin\AppData\Local\Temp\gvg7puwk9.exe" | C:\Users\admin\AppData\Local\Temp\gvg7puwk9.exe | — | WScript.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3360 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Device Properties Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3520 | --ee2f59e2 | C:\Users\admin\AppData\Local\soundser\8ihwMIAoKIsX9g.exe | 8ihwMIAoKIsX9g.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Device Properties Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3804 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | 8ihwMIAoKIsX9g.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Device Properties Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3896 | "C:\Program Files\Internet Explorer\iexplore.exe" http://yayasanrumahkita.com/eqdx/TKWBN-cOKlwF3Cuuj2YoP_DIjOiVfii-suE/ | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 098
Read events
1 023
Write events
74
Delete events
1
Modification events
| (PID) Process: | (3896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000071000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {8F5B5B5D-65F0-11E9-A370-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (3896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E307040002001700110034001D006802 | |||
Executable files
4
Suspicious files
1
Text files
15
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3896 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF1F4E7CAC8C14F619.TMP | — | |
MD5:— | SHA256:— | |||
| 3896 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3896 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3896 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFF07A59E5ECE56D1D.TMP | — | |
MD5:— | SHA256:— | |||
| 3896 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{8F5B5B5D-65F0-11E9-A370-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 4012 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 3896 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Feeds Cache\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 4012 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 4012 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5ZY2L76A\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 4012 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\RRN1Z14U\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
5
DNS requests
3
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2392 | WScript.exe | GET | 200 | 164.52.146.13:80 | http://potterspots.com/cgi-bin/8MnY/ | US | executable | 77.5 Kb | suspicious |
3360 | soundser.exe | POST | 200 | 24.150.44.53:80 | http://24.150.44.53/site/arizona/ringin/ | CA | binary | 148 b | malicious |
4012 | iexplore.exe | GET | 200 | 139.99.19.224:80 | http://yayasanrumahkita.com/eqdx/TKWBN-cOKlwF3Cuuj2YoP_DIjOiVfii-suE/ | SG | text | 8.64 Kb | unknown |
2696 | soundser.exe | POST | 200 | 24.150.44.53:80 | http://24.150.44.53/add/ | CA | fli | 142 Kb | malicious |
3896 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4012 | iexplore.exe | 139.99.19.224:80 | yayasanrumahkita.com | OVH SAS | SG | unknown |
3896 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2392 | WScript.exe | 164.52.146.13:80 | potterspots.com | Latisys-Denver, LLC | US | suspicious |
2696 | soundser.exe | 24.150.44.53:80 | — | Cogeco Cable | CA | malicious |
3360 | soundser.exe | 24.150.44.53:80 | — | Cogeco Cable | CA | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
yayasanrumahkita.com |
| unknown |
www.bing.com |
| whitelisted |
potterspots.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2392 | WScript.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
2392 | WScript.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2392 | WScript.exe | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from MSXMLHTTP non-exe extension M2 |
2392 | WScript.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2696 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3360 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
6 ETPRO signatures available at the full report