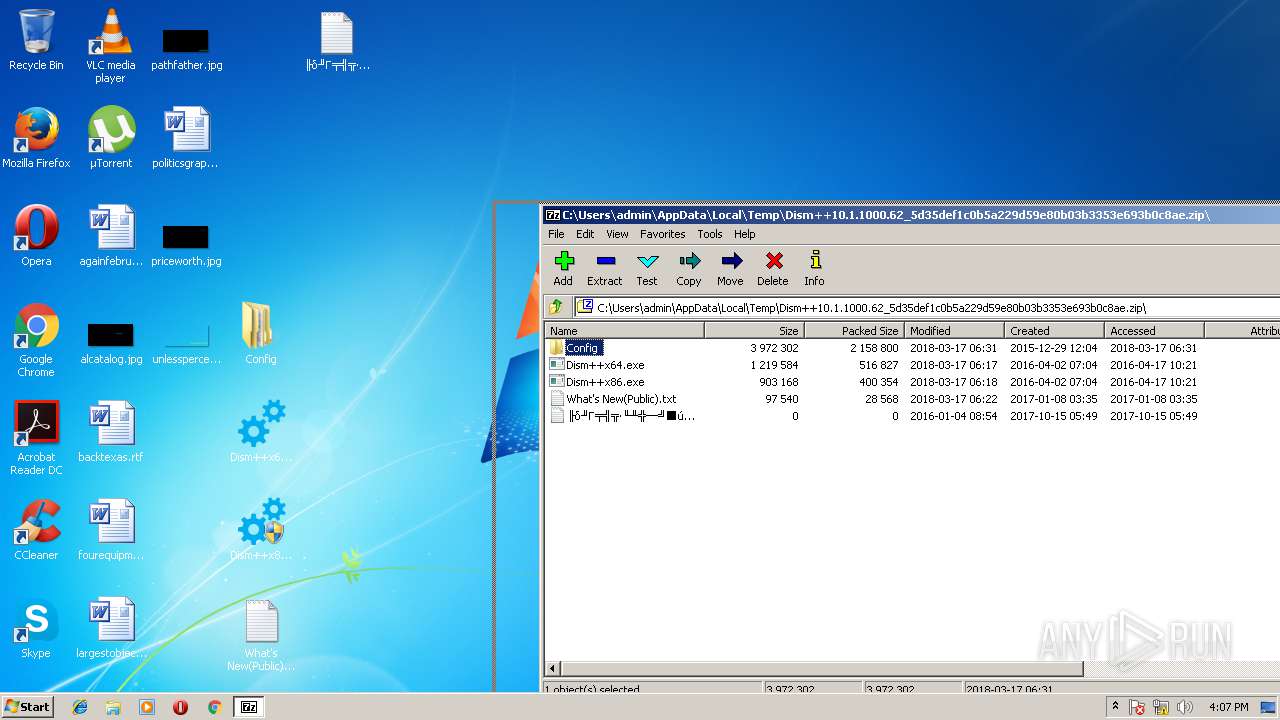
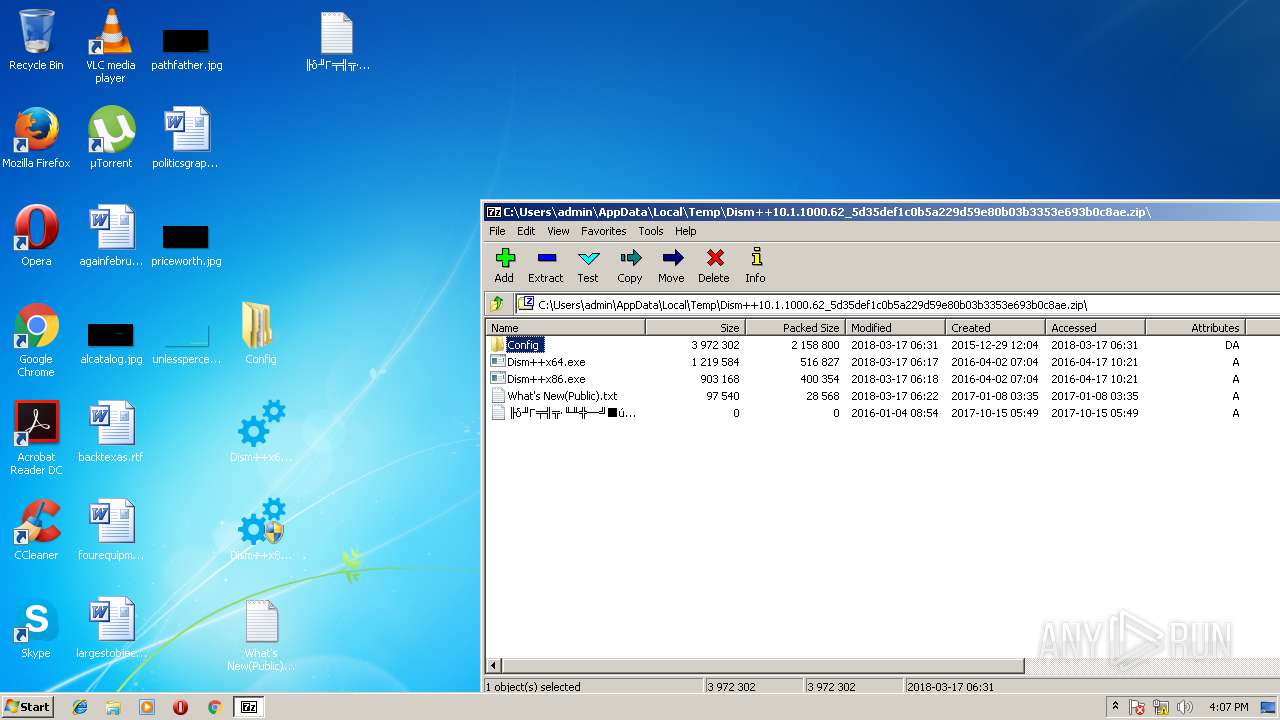
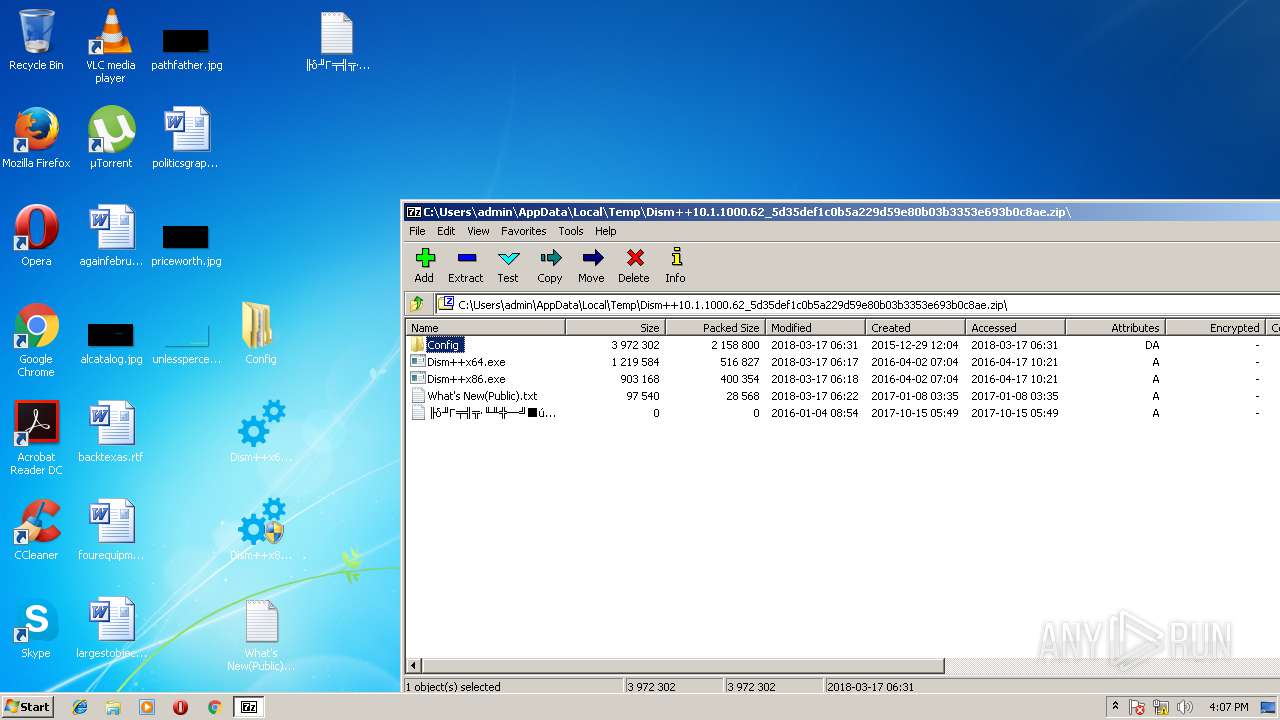
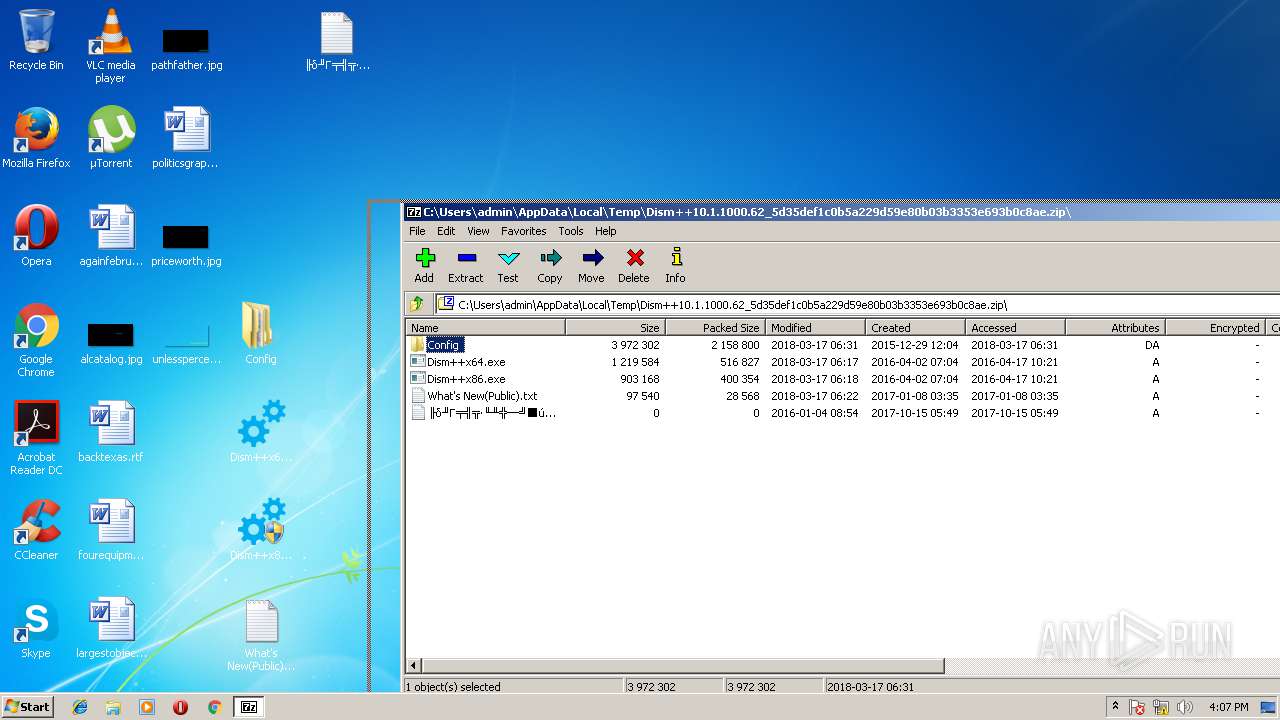
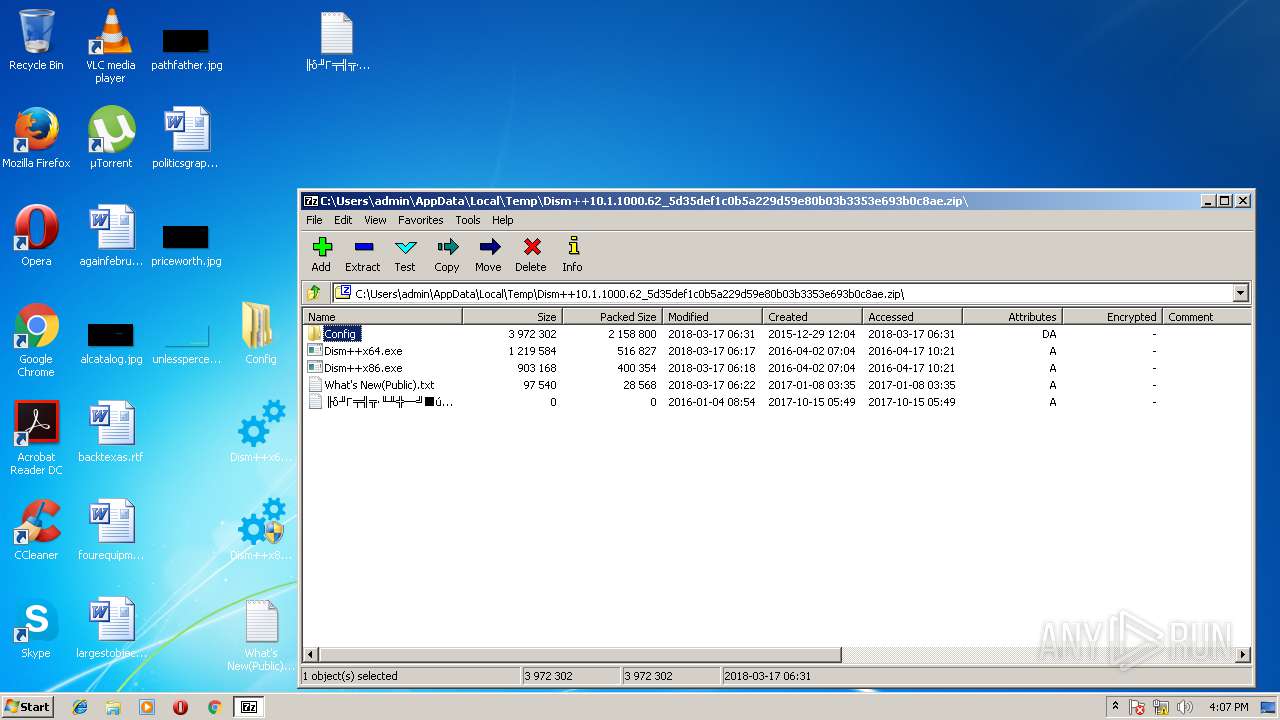
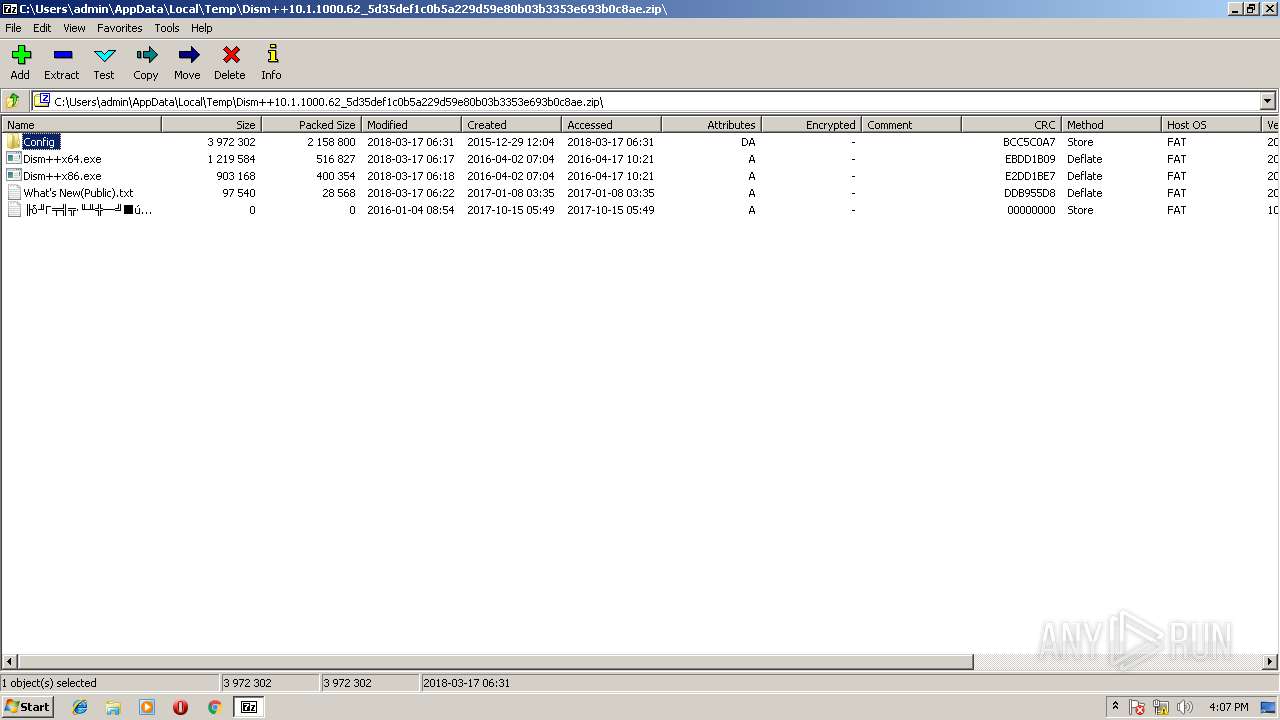
| download: | Dism++10.1.1000.62_5d35def1c0b5a229d59e80b03b3353e693b0c8ae.zip |
| Full analysis: | https://app.any.run/tasks/08f91807-1402-43e7-9b49-96329827e81b |
| Verdict: | Malicious activity |
| Analysis date: | March 18, 2018, 16:06:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | C80E5927B92CBB250BDDF59561F954E5 |
| SHA1: | 5D35DEF1C0B5A229D59E80B03B3353E693B0C8AE |
| SHA256: | 92376874A5C1AD6F97E4828E65F497E541D99B3E2DB409DE7606B1816694572E |
| SSDEEP: | 49152:3KtXTQzT6J6H4lc8gDnkguofPPN7o6LrlAMpiPOqV+NWmN1d+bvqF7zc1YGxodUY:3KtQSETJnkgdriQTe+NbNGSNzc1YSoKO |
MALICIOUS
Application was dropped or rewritten from another process
- Dism++x86.exe (PID: 3720)
- Dism++x86.exe (PID: 3792)
Application loaded dropped or rewritten executable
- Dism++x86.exe (PID: 3792)
- rundll32.exe (PID: 2368)
- SearchProtocolHost.exe (PID: 2008)
Loads the Task Scheduler COM API
- explorer.exe (PID: 1884)
- explorer.exe (PID: 3060)
SUSPICIOUS
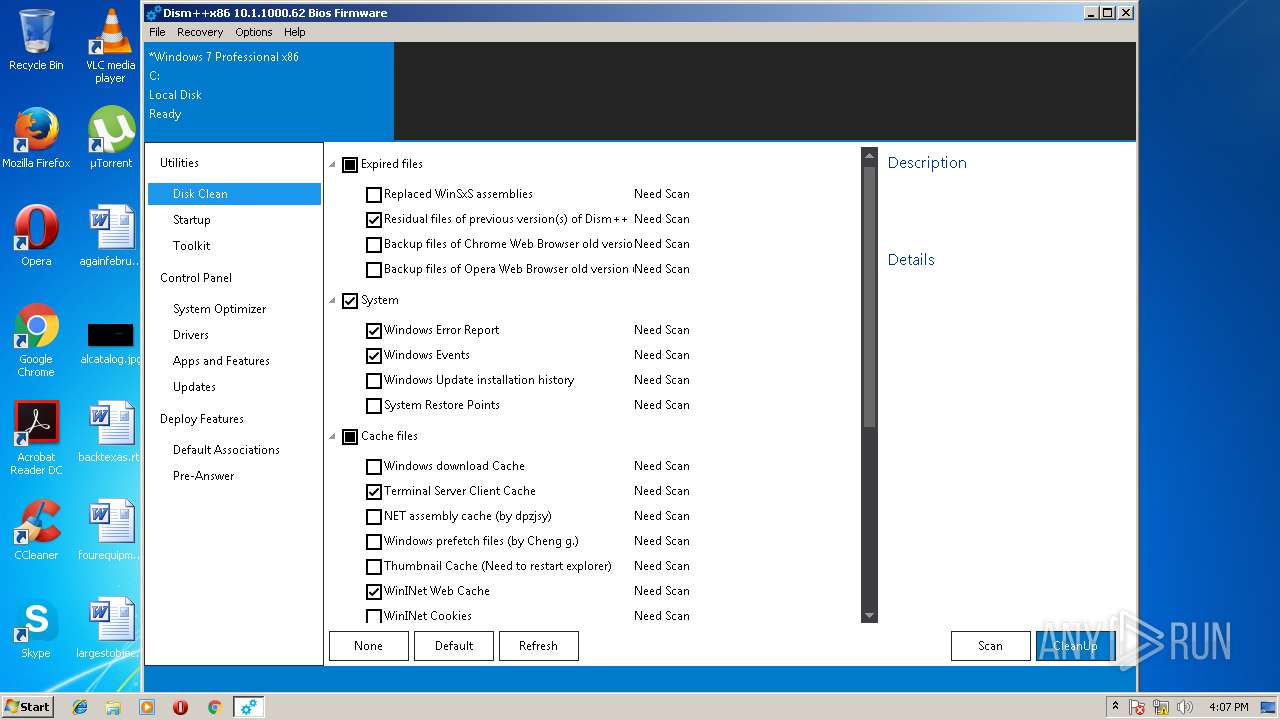
Creates files in the user directory
- Dism++x86.exe (PID: 3792)
Modifies files in the system directory
- TrustedInstaller.exe (PID: 3108)
- vssvc.exe (PID: 3008)
Creates files in the Windows directory
- TrustedInstaller.exe (PID: 3108)
- Dism++x86.exe (PID: 3792)
Creates or modifies windows services
- DllHost.exe (PID: 2680)
- Dism++x86.exe (PID: 3792)
- DllHost.exe (PID: 2600)
- vssvc.exe (PID: 3008)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3008)
Writes to a desktop.ini file (may be used to cloak folders)
- explorer.exe (PID: 3060)
- explorer.exe (PID: 1884)
Removes files from Windows directory
- Dism++x86.exe (PID: 3792)
- rundll32.exe (PID: 2368)
INFO
Dropped object may contain URL's
- 7zFM.exe (PID: 3000)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2018:03:17 14:31:10 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Config/ |
Total processes
54
Monitored processes
11
Malicious processes
7
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1884 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | Dism++x86.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2008 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe6_ Global\UsGthrCtrlFltPipeMssGthrPipe6 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2368 | rundll32 "C:\Users\admin\Desktop\Config\x86\CBSHost.dll",RunCbsHost {d46a92b7-0cd2-4077-86a0-e017ef5e23fb} "C:" "\\?\C:\Windows\Temp\\" 000000A8 4 | C:\Windows\System32\rundll32.exe | — | Dism++x86.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2600 | C:\Windows\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2680 | C:\Windows\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
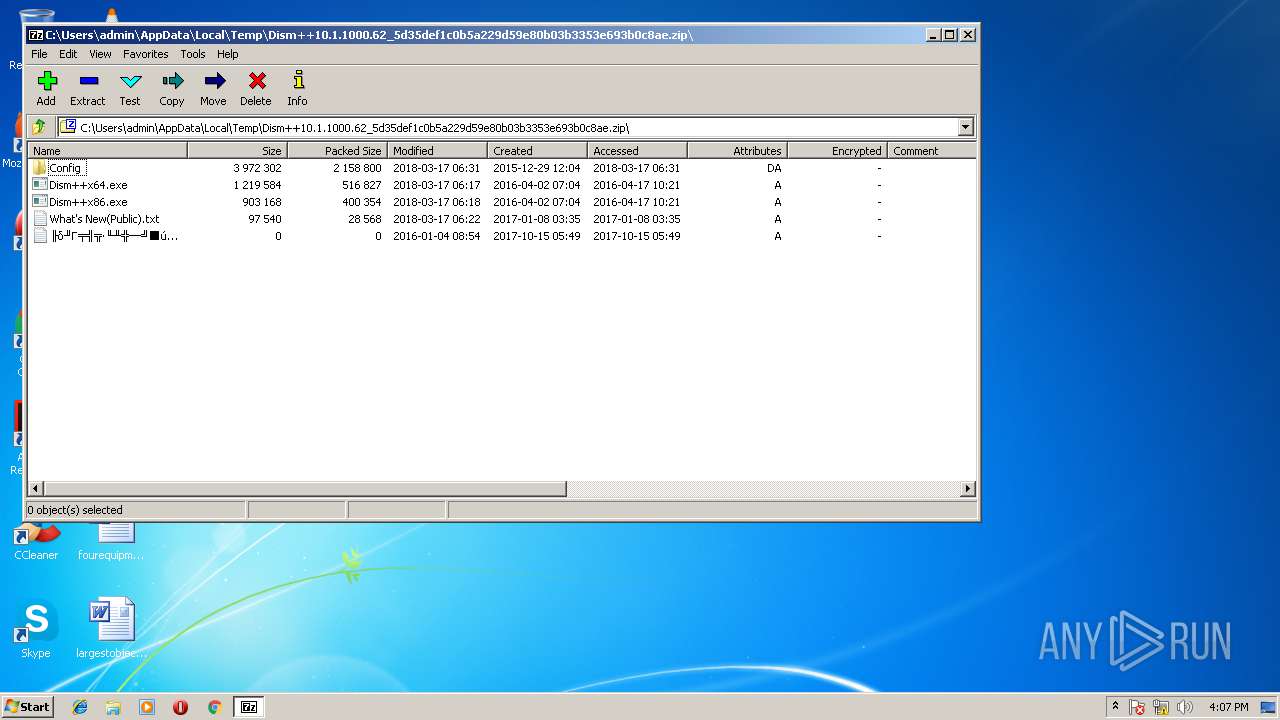
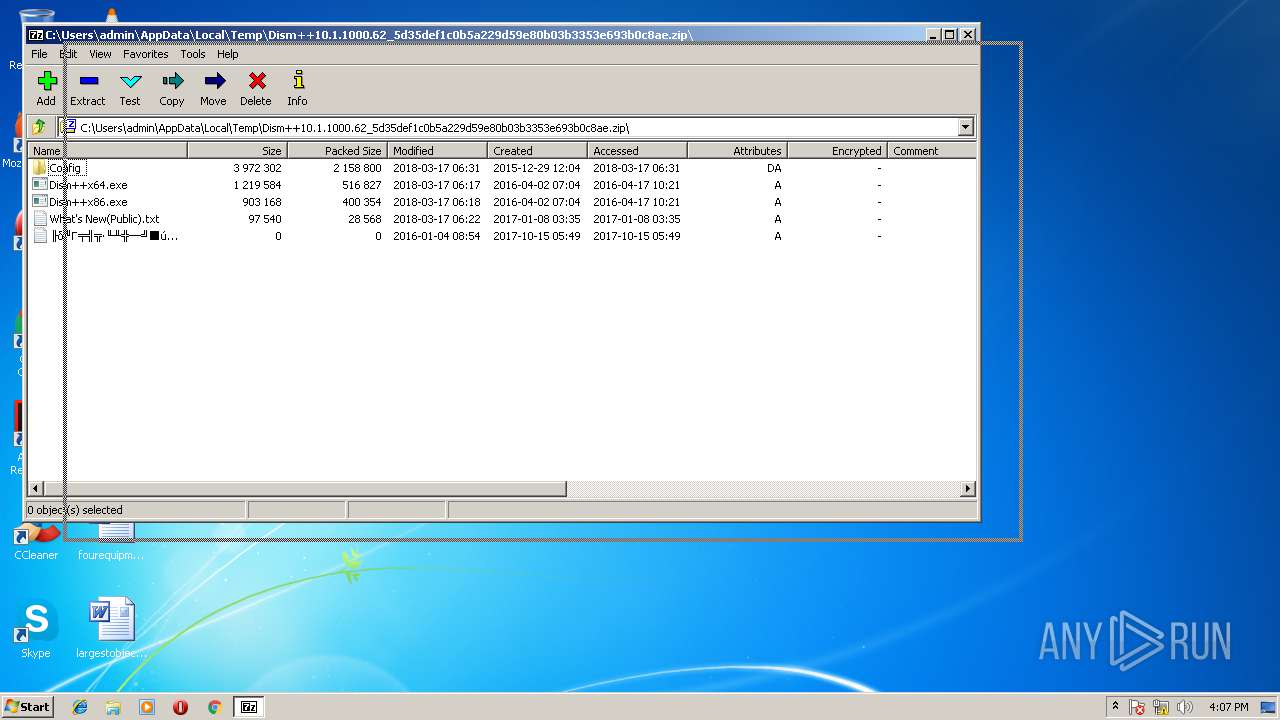
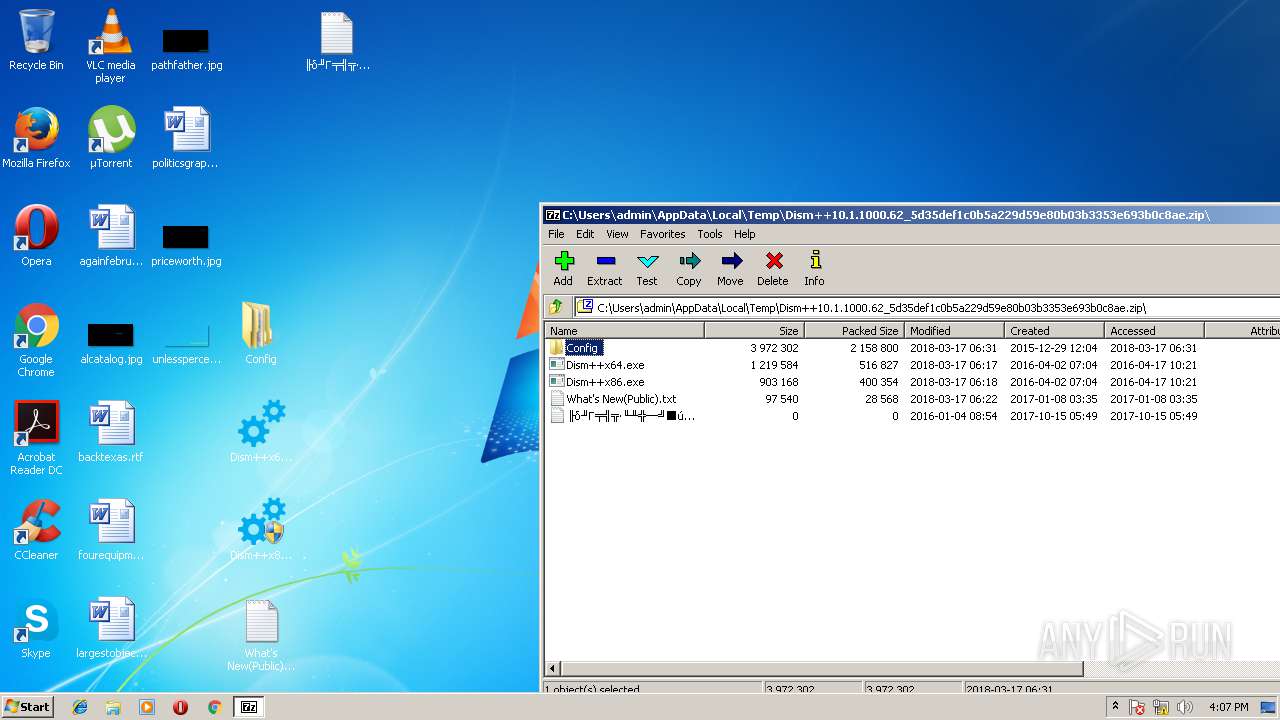
| 3000 | "C:\Program Files\7-Zip\7zFM.exe" "C:\Users\admin\AppData\Local\Temp\Dism++10.1.1000.62_5d35def1c0b5a229d59e80b03b3353e693b0c8ae.zip" | C:\Program Files\7-Zip\7zFM.exe | explorer.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip File Manager Exit code: 0 Version: 16.04 Modules
| |||||||||||||||
| 3008 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3060 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | Dism++x86.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3108 | C:\Windows\servicing\TrustedInstaller.exe | C:\Windows\servicing\TrustedInstaller.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Modules Installer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
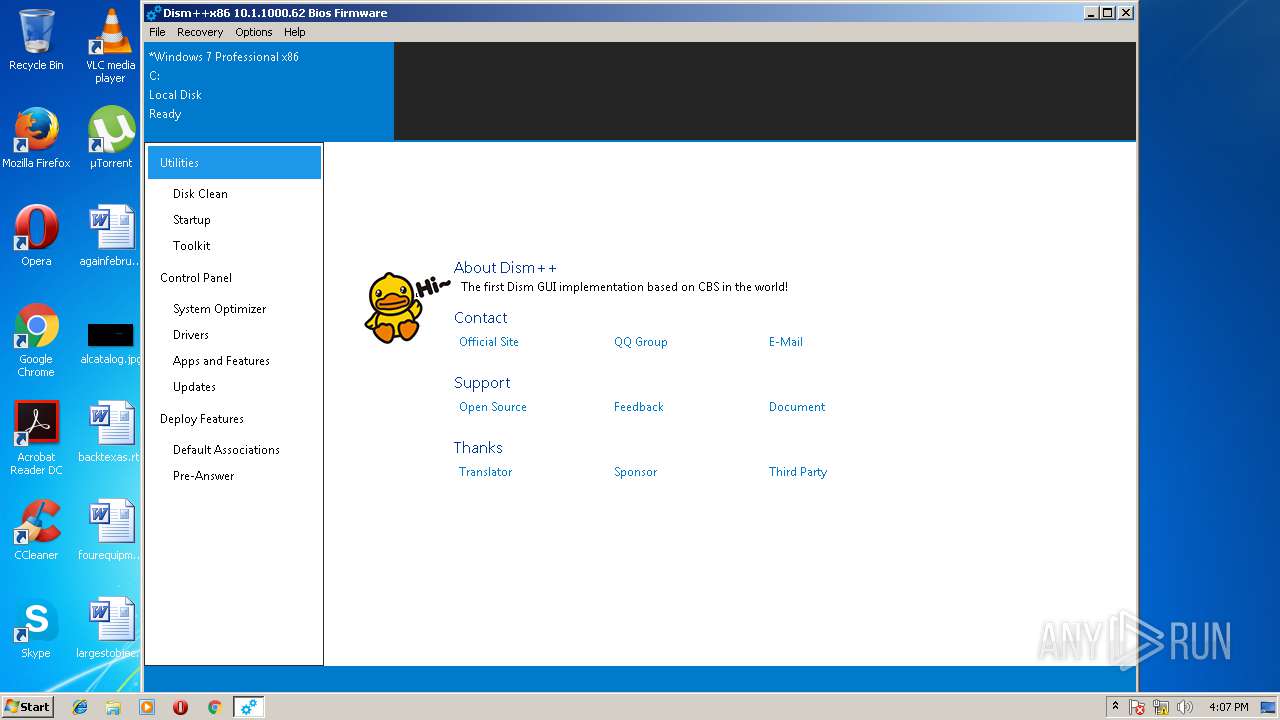
| 3720 | "C:\Users\admin\Desktop\Dism++x86.exe" | C:\Users\admin\Desktop\Dism++x86.exe | — | explorer.exe | |||||||||||
User: admin Company: Chuyu Team Integrity Level: MEDIUM Description: Dism++主程序 Exit code: 3221226540 Version: 10.1.1000.62 Modules
| |||||||||||||||
Total events
9 608
Read events
8 826
Write events
775
Delete events
7
Modification events
| (PID) Process: | (2008) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\8F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2008) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\8F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\notepad.exe,-469 |
Value: Text Document | |||
| (PID) Process: | (3000) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM |
| Operation: | write | Name: | FolderShortcuts |
Value: | |||
| (PID) Process: | (3000) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM |
| Operation: | write | Name: | FolderHistory |
Value: 43003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C004400690073006D002B002B00310030002E0031002E0031003000300030002E00360032005F0035006400330035006400650066003100630030006200350061003200320039006400350039006500380030006200300033006200330033003500330065003600390033006200300063003800610065002E007A00690070005C000000 | |||
| (PID) Process: | (3000) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM |
| Operation: | write | Name: | PanelPath0 |
Value: C:\Users\admin\AppData\Local\Temp\ | |||
| (PID) Process: | (3000) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM |
| Operation: | write | Name: | FlatViewArc0 |
Value: 0 | |||
| (PID) Process: | (3000) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM |
| Operation: | write | Name: | PanelPath1 |
Value: | |||
| (PID) Process: | (3000) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM |
| Operation: | write | Name: | FlatViewArc1 |
Value: 0 | |||
| (PID) Process: | (3000) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM |
| Operation: | write | Name: | ListMode |
Value: 771 | |||
| (PID) Process: | (3000) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM |
| Operation: | write | Name: | Position |
Value: 1B010000B6000000DB040000AB02000001000000 | |||
Executable files
7
Suspicious files
30
Text files
40
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3000 | 7zFM.exe | C:\Users\admin\AppData\Local\Temp\7zE8BBF62E2\Config\amd64\CBSHost.dll | executable | |
MD5:— | SHA256:— | |||
| 3000 | 7zFM.exe | C:\Users\admin\AppData\Local\Temp\7zE8BBF62E2\Config\Languages\de.zip | compressed | |
MD5:— | SHA256:— | |||
| 3000 | 7zFM.exe | C:\Users\admin\AppData\Local\Temp\7zE8BBF62E2\Config\amd64\wimgapi.dll | executable | |
MD5:— | SHA256:— | |||
| 3000 | 7zFM.exe | C:\Users\admin\AppData\Local\Temp\7zE8BBF62E2\Config\Languages\en.zip | compressed | |
MD5:— | SHA256:— | |||
| 3000 | 7zFM.exe | C:\Users\admin\AppData\Local\Temp\7zE8BBF62E2\Config\Plugins\FrogPlugins_Pcn7FMvReAsVWfCQBfRJCw\PluginRes.dll | — | |
MD5:— | SHA256:— | |||
| 3000 | 7zFM.exe | C:\Users\admin\AppData\Local\Temp\7zE8BBF62E2\Config\UpdateInfo.zip | — | |
MD5:— | SHA256:— | |||
| 3000 | 7zFM.exe | C:\Users\admin\AppData\Local\Temp\7zE8BBF62E2\Config\x86\bcdboot.exe | — | |
MD5:— | SHA256:— | |||
| 3000 | 7zFM.exe | C:\Users\admin\AppData\Local\Temp\7zE8BBF62E2\Config\x86\CBSHost.dll | — | |
MD5:— | SHA256:— | |||
| 3000 | 7zFM.exe | C:\Users\admin\AppData\Local\Temp\7zE8BBF62E2\Config\x86\NCleaner.dll | — | |
MD5:— | SHA256:— | |||
| 3000 | 7zFM.exe | C:\Users\admin\AppData\Local\Temp\7zE8BBF62E2\Config\x86\wimgapi.dll | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | POST | 200 | 111.206.47.207:80 | http://web1612151818153.bj01.bdysite.com/chuyu-analysis/client_update.php | CN | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 111.206.47.207:80 | web1612151818153.bj01.bdysite.com | China Unicom Beijing Province Network | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
web1612151818153.bj01.bdysite.com |
| malicious |