| File name: | TestFile.ps1 |
| Full analysis: | https://app.any.run/tasks/eb1832d5-4d9c-4c67-9f09-c556407288ee |
| Verdict: | Malicious activity |
| Analysis date: | March 24, 2025, 17:38:16 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | C69D14EFCD89A394F179E348F010720F |
| SHA1: | 3B7A0DC1D9023F1EBC8351DF3F59D1A52B196DD9 |
| SHA256: | 922EFBC798D5C70D6CCAC1B8E5970323E702D1E4DEA8DBC760C98B0119EEF550 |
| SSDEEP: | 96:HKFUuBVkDx+uy6OphNHOSSDrSSSKDU4SXDZAByg+TlkXeQo6CGefWrG/v:qFUOVk1+uyp/SD2zKDUtXDZABygKlkOJ |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 496)
SUSPICIOUS
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 496)
Starts SC.EXE for service management
- cmd.exe (PID: 8036)
- cmd.exe (PID: 7844)
- cmd.exe (PID: 7720)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 496)
- powershell.exe (PID: 1188)
- powershell.exe (PID: 1672)
- powershell.exe (PID: 5436)
Executing commands from ".cmd" file
- powershell.exe (PID: 496)
- cmd.exe (PID: 8036)
- powershell.exe (PID: 2568)
- cmd.exe (PID: 7844)
- powershell.exe (PID: 7580)
- cmd.exe (PID: 7720)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 496)
- cmd.exe (PID: 8036)
- cmd.exe (PID: 1244)
- powershell.exe (PID: 2568)
- cmd.exe (PID: 8156)
- cmd.exe (PID: 7844)
- cmd.exe (PID: 6768)
- powershell.exe (PID: 7580)
- cmd.exe (PID: 7720)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 496)
- powershell.exe (PID: 1188)
- powershell.exe (PID: 1672)
- powershell.exe (PID: 5436)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 8036)
- cmd.exe (PID: 7844)
- cmd.exe (PID: 7720)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 496)
- powershell.exe (PID: 1188)
- powershell.exe (PID: 1672)
- powershell.exe (PID: 5436)
Application launched itself
- cmd.exe (PID: 8036)
- cmd.exe (PID: 1244)
- cmd.exe (PID: 7844)
- cmd.exe (PID: 8156)
- cmd.exe (PID: 7720)
- cmd.exe (PID: 6768)
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 496)
Windows service management via SC.EXE
- sc.exe (PID: 8096)
- sc.exe (PID: 7708)
- sc.exe (PID: 7520)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 2088)
- cmd.exe (PID: 904)
- cmd.exe (PID: 1568)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 2088)
- cmd.exe (PID: 904)
- cmd.exe (PID: 1568)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2088)
- cmd.exe (PID: 8036)
- cmd.exe (PID: 904)
- cmd.exe (PID: 7844)
- cmd.exe (PID: 1568)
- cmd.exe (PID: 7720)
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 4224)
INFO
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 496)
- powershell.exe (PID: 1188)
- powershell.exe (PID: 1672)
- powershell.exe (PID: 5436)
Checks proxy server information
- powershell.exe (PID: 496)
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 496)
- powershell.exe (PID: 1188)
- powershell.exe (PID: 1672)
- powershell.exe (PID: 5436)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 496)
- powershell.exe (PID: 1188)
- powershell.exe (PID: 1672)
- powershell.exe (PID: 5436)
Disables trace logs
- powershell.exe (PID: 496)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 496)
- powershell.exe (PID: 1188)
- powershell.exe (PID: 1672)
- powershell.exe (PID: 5436)
Checks operating system version
- cmd.exe (PID: 8036)
- cmd.exe (PID: 7844)
- cmd.exe (PID: 7720)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 5512)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 5512)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 2568)
Checks supported languages
- ShellExperienceHost.exe (PID: 4224)
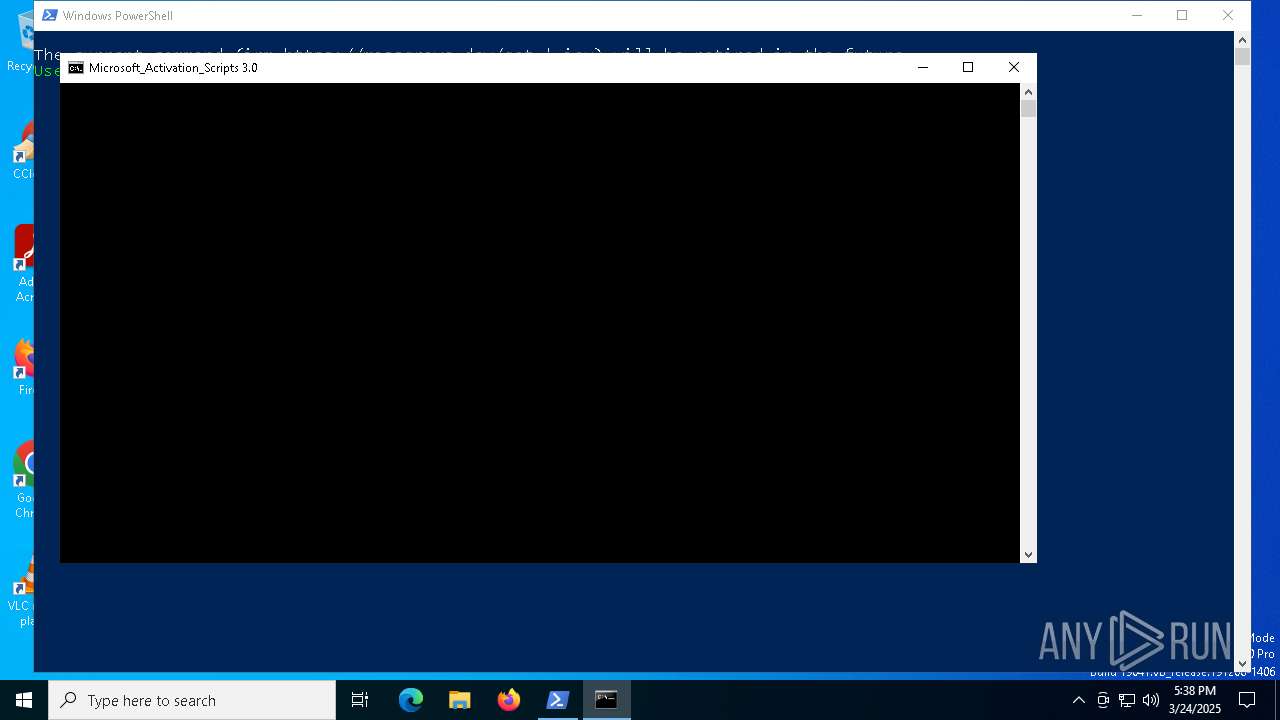
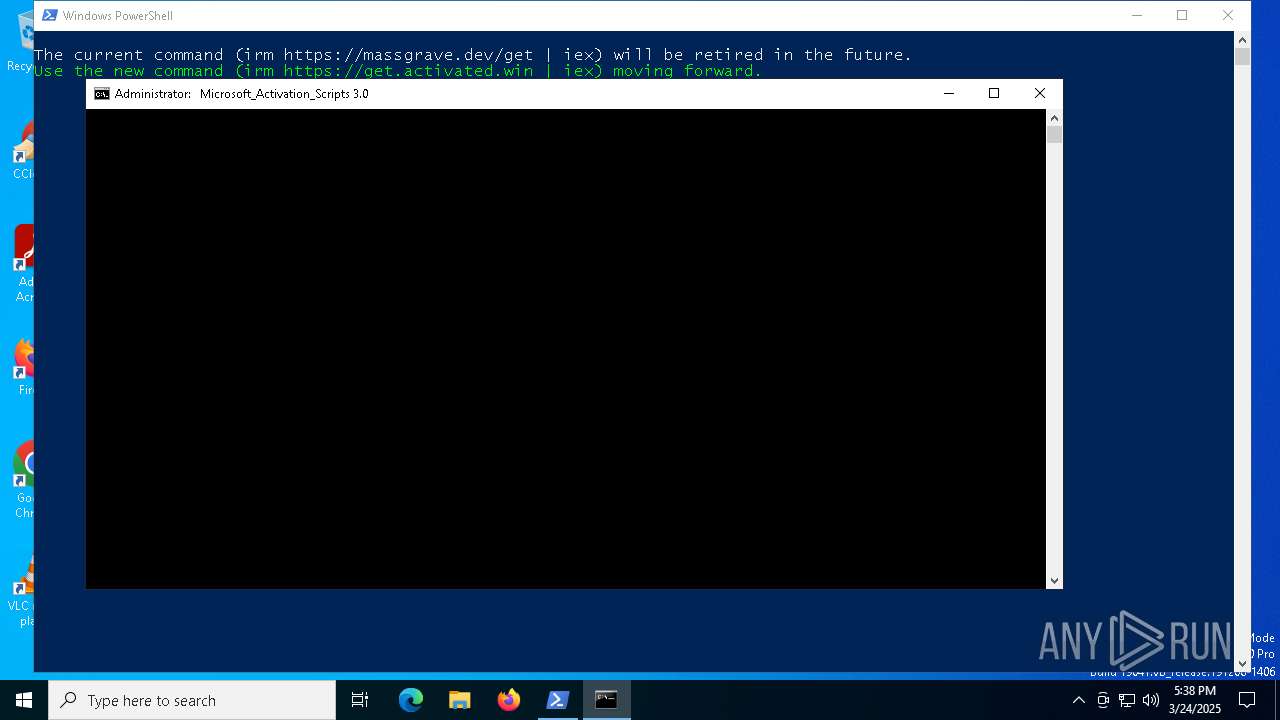
Starts MODE.COM to configure console settings
- mode.com (PID: 8040)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
229
Monitored processes
89
Malicious processes
6
Suspicious processes
9
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 496 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass C:\Users\admin\AppData\Local\Temp\TestFile.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 856 | powershell.exe "$TB = [AppDomain]::CurrentDomain.DefineDynamicAssembly(4, 1).DefineDynamicModule(2, $False).DefineType(0); [void]$TB.DefinePInvokeMethod('GetConsoleWindow', 'kernel32.dll', 22, 1, [IntPtr], @(), 1, 3).SetImplementationFlags(128); [void]$TB.DefinePInvokeMethod('SendMessageW', 'user32.dll', 22, 1, [IntPtr], @([IntPtr], [UInt32], [IntPtr], [IntPtr]), 1, 3).SetImplementationFlags(128); $hIcon = $TB.CreateType(); $hWnd = $hIcon::GetConsoleWindow(); echo $($hIcon::SendMessageW($hWnd, 127, 0, 0) -ne [IntPtr]::Zero);" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 900 | C:\WINDOWS\System32\cmd.exe /S /D /c" echo "C:\Users\admin\AppData\Local\Temp\MAS_ad68cf38-e16d-4a31-b713-328b7c88cf00.cmd" " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 904 | cmd /c "powershell.exe "$f=[io.file]::ReadAllText('C:\Users\admin\AppData\Local\Temp\MAS_ad68cf38-e16d-4a31-b713-328b7c88cf00.cmd') -split ':PStest:\s*';iex ($f[1])"" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1168 | C:\WINDOWS\System32\cmd.exe /S /D /c" echo prompt $E " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1188 | powershell.exe "$f=[io.file]::ReadAllText('C:\Users\admin\AppData\Local\Temp\MAS_ad68cf38-e16d-4a31-b713-328b7c88cf00.cmd') -split ':PStest:\s*';iex ($f[1])" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1240 | find /i "True" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1244 | C:\WINDOWS\System32\cmd.exe /c echo prompt $E | cmd | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1568 | cmd /c "powershell.exe "$f=[io.file]::ReadAllText('C:\Users\admin\AppData\Local\Temp\MAS_ad68cf38-e16d-4a31-b713-328b7c88cf00.cmd') -split ':PStest:\s*';iex ($f[1])"" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1628 | C:\WINDOWS\System32\cmd.exe /S /D /c" echo "AMD64 " " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
40 034
Read events
40 017
Write events
17
Delete events
0
Modification events
| (PID) Process: | (6964) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6964) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6964) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5512) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5512) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5512) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6640) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6640) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6640) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7912) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
0
Suspicious files
9
Text files
17
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5512 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\e0eeae8c-47e0-45ec-b91b-dfddd606c11b.down_data | — | |
MD5:— | SHA256:— | |||
| 1188 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:4DBD54EFE1270B0C4F442F27C41DC7CD | SHA256:5C02F147B53FB329349FC596AE852D670ED6769E99789B1C60AFB6372F1E440F | |||
| 1188 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_kqir3lga.qbo.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 496 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:27CC882A28396E2D65B28E788F2EBCFC | SHA256:4889DF4B54F1E736F8A7DDD3D14840E96A1E23FE5A55D538A6BDB3F7D7D35BF9 | |||
| 496 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_fhg5r23z.nuv.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5512 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\b1e00e91-f1a2-4936-bd54-38002fc25876.f83d6ac1-f904-42e4-94ac-e8bd76c2ac2c.down_meta | binary | |
MD5:6C11885B7B3B1BF004F956AAA7F1F683 | SHA256:4859C853A8AA8861721FACE49AE4C1D7CD95AFFFE47BCDDD2B6C34E6D788238F | |||
| 5512 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\MetaData\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:AB985435EBEB72A78657E277BEAD080B | SHA256:8C4C9F221DF2A0799384089AB77411E61EC80C5A2A401DA03D74B57422C79687 | |||
| 2568 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_2ysiynq5.tnc.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 496 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\69J1N0IQNTXDVZL5Z5AP.temp | binary | |
MD5:27CC882A28396E2D65B28E788F2EBCFC | SHA256:4889DF4B54F1E736F8A7DDD3D14840E96A1E23FE5A55D538A6BDB3F7D7D35BF9 | |||
| 2568 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_2khcamuw.50t.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
25
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7512 | backgroundTaskHost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2616 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2616 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5512 | BackgroundTransferHost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.158:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5496 | MoUsoCoreWorker.exe | 23.48.23.158:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4212 | RUXIMICS.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
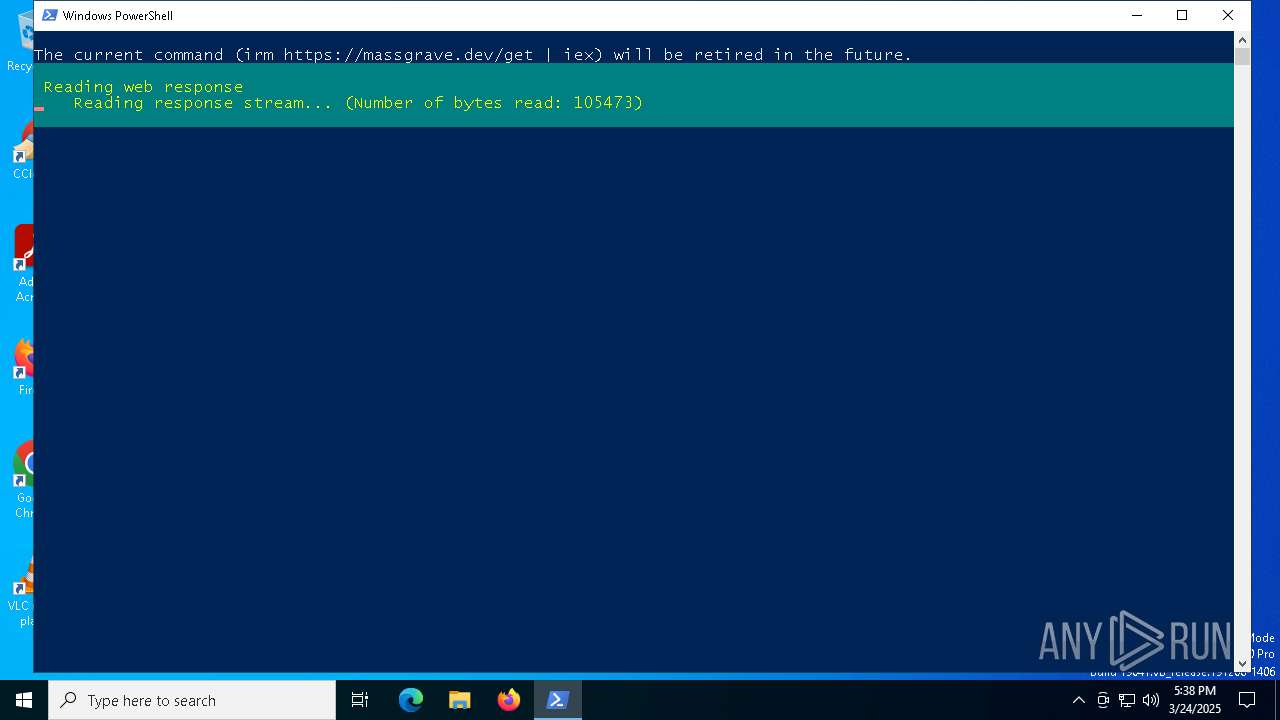
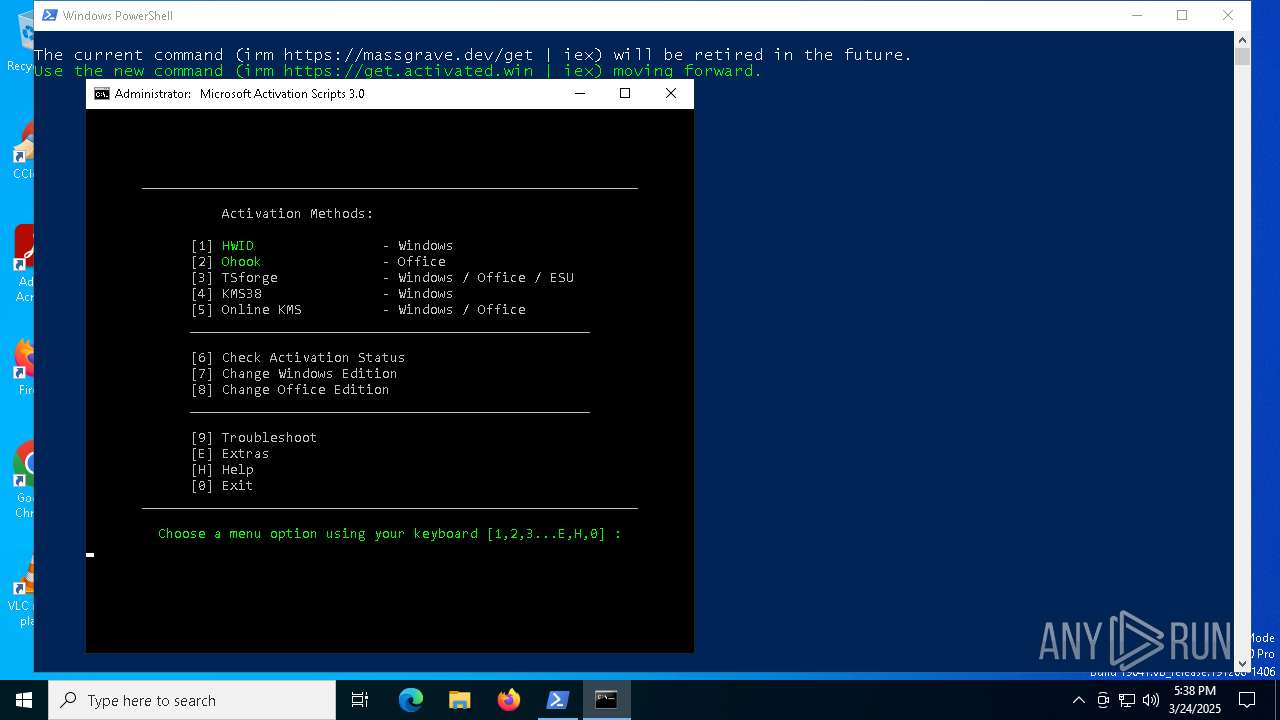
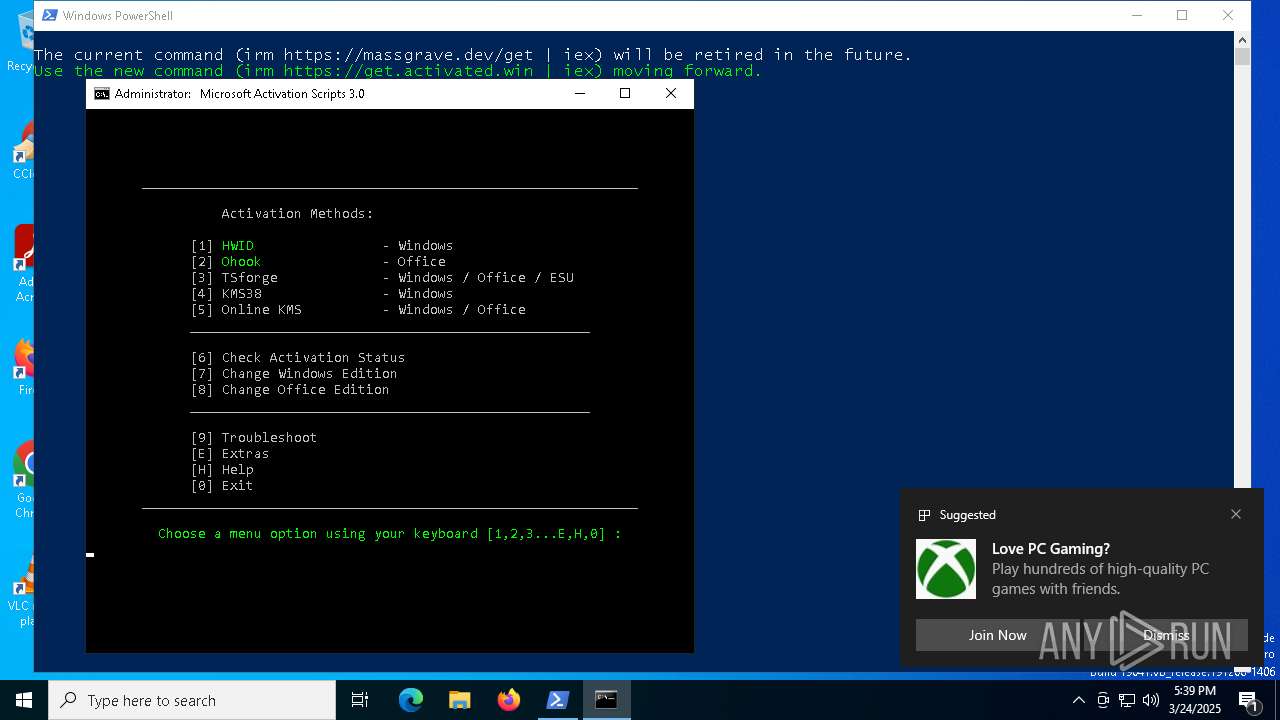
496 | powershell.exe | 172.67.219.75:443 | git.activated.win | CLOUDFLARENET | US | unknown |
3216 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.159.0:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 23.54.109.203:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
git.activated.win |
| unknown |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
activated.win |
| unknown |