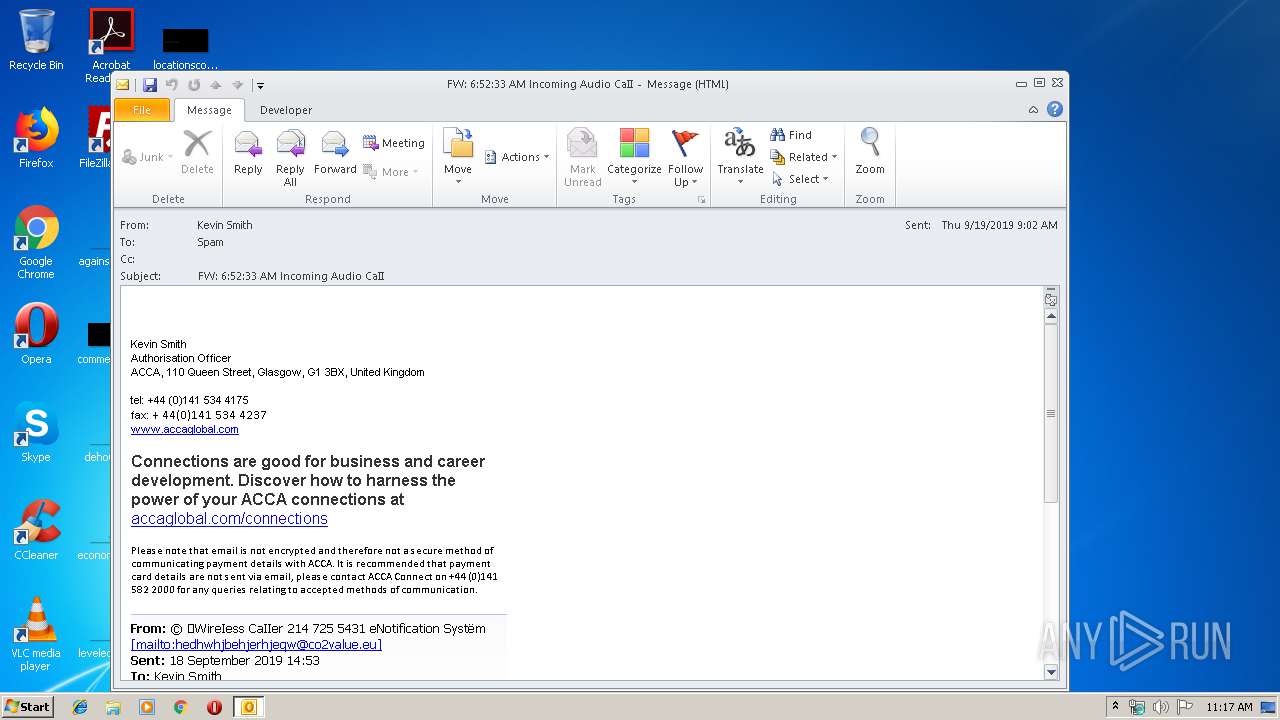
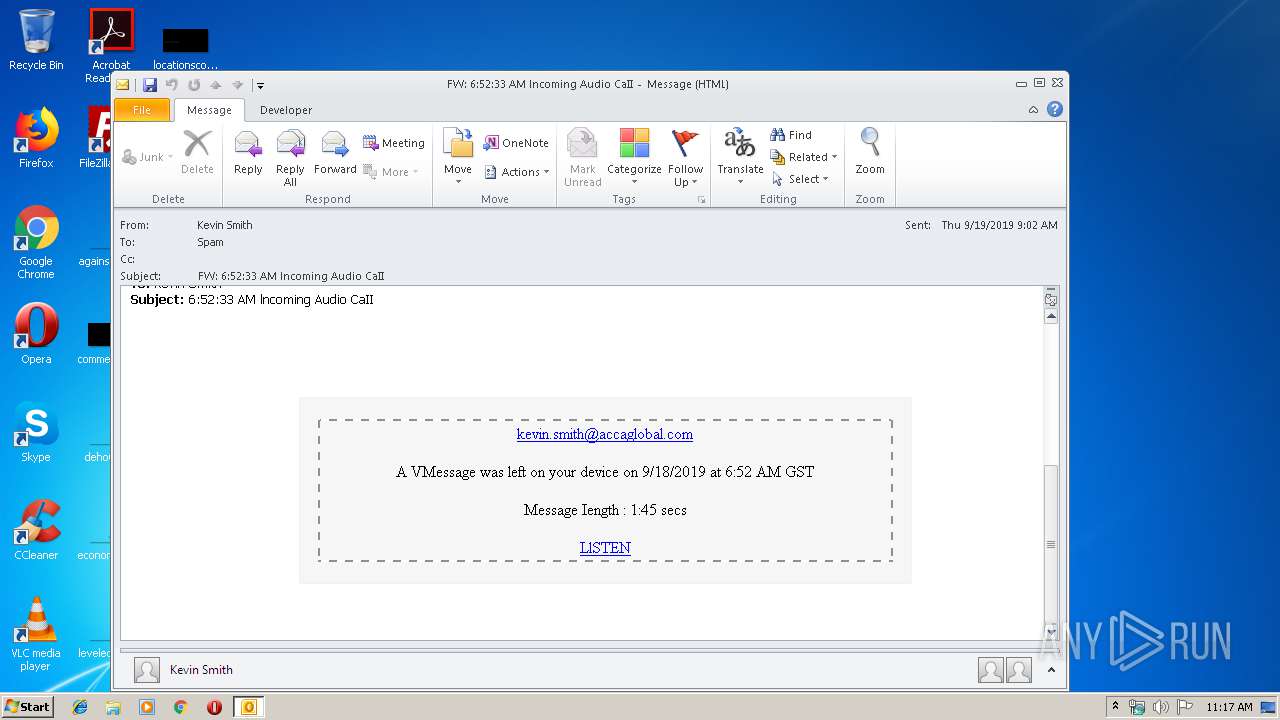
| File name: | FW 65233 AM lncoming Audio CaII.msg |
| Full analysis: | https://app.any.run/tasks/12020a69-318d-4a5b-bc20-71d3c32e125b |
| Verdict: | Malicious activity |
| Analysis date: | September 19, 2019, 10:17:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | F879B974AB3BA9CDA65EA9D3A2C550F3 |
| SHA1: | 033C4608B2DFCED2A8599B5FCD57C55BA066214B |
| SHA256: | 921D81954E4978474DB953A1DF62D3BDA0F5C35468E316F4A2E3384B027ACF51 |
| SSDEEP: | 768:mwIpUMng0chByaLE4c2jV0nSlRNsxAZ/l0H343vuABVvhDeAWsKJWsKnWsKJWsKg:engIwBpvuqhDeAWRWfWBWNcyiWxWq |
MALICIOUS
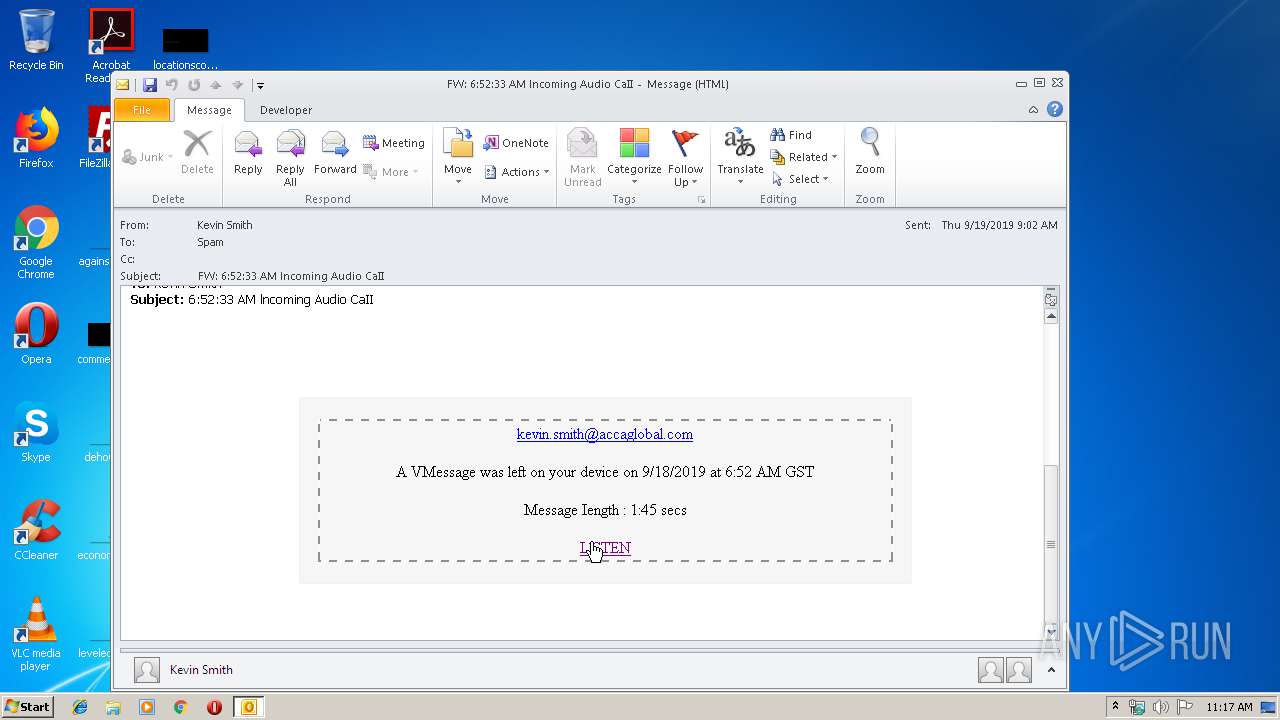
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 2892)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 2892)
Starts Internet Explorer
- OUTLOOK.EXE (PID: 2892)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2892)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2892)
Reads internet explorer settings
- iexplore.exe (PID: 3812)
Reads Internet Cache Settings
- iexplore.exe (PID: 3812)
- iexplore.exe (PID: 3184)
Changes internet zones settings
- iexplore.exe (PID: 3184)
Reads settings of System Certificates
- iexplore.exe (PID: 3184)
Changes settings of System certificates
- iexplore.exe (PID: 3184)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3184)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
36
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2892 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\FW 65233 AM lncoming Audio CaII.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
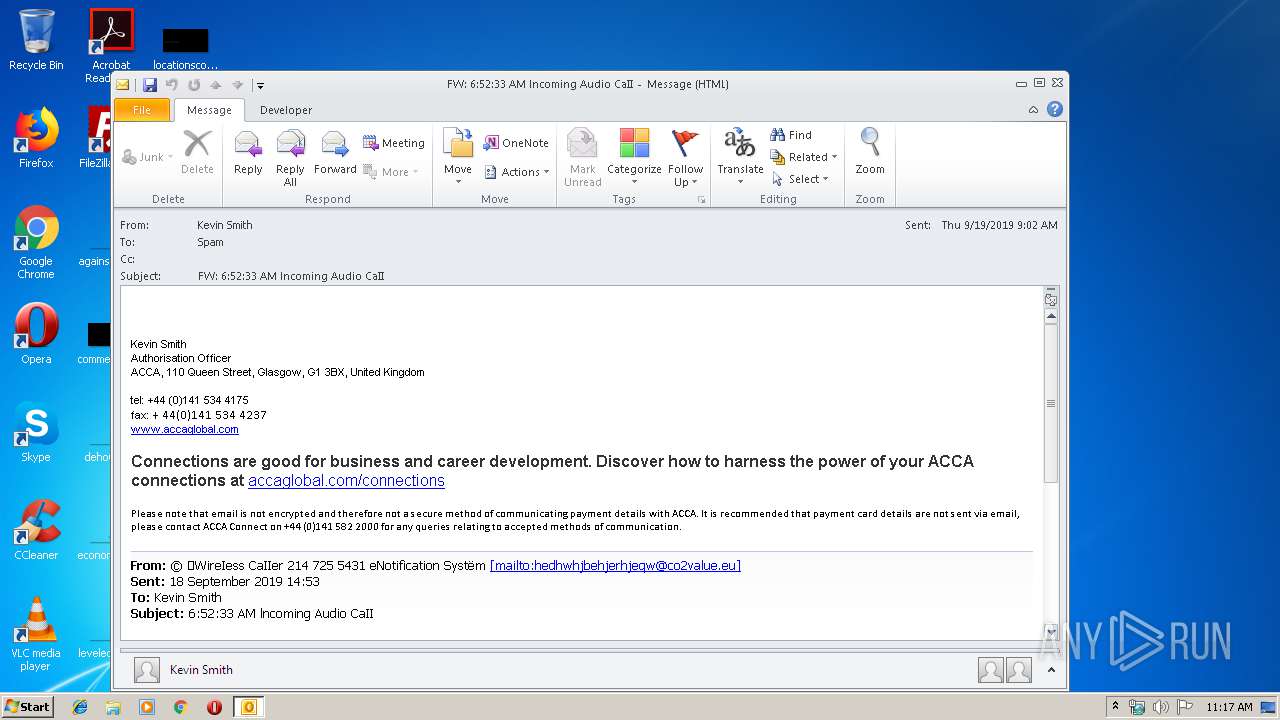
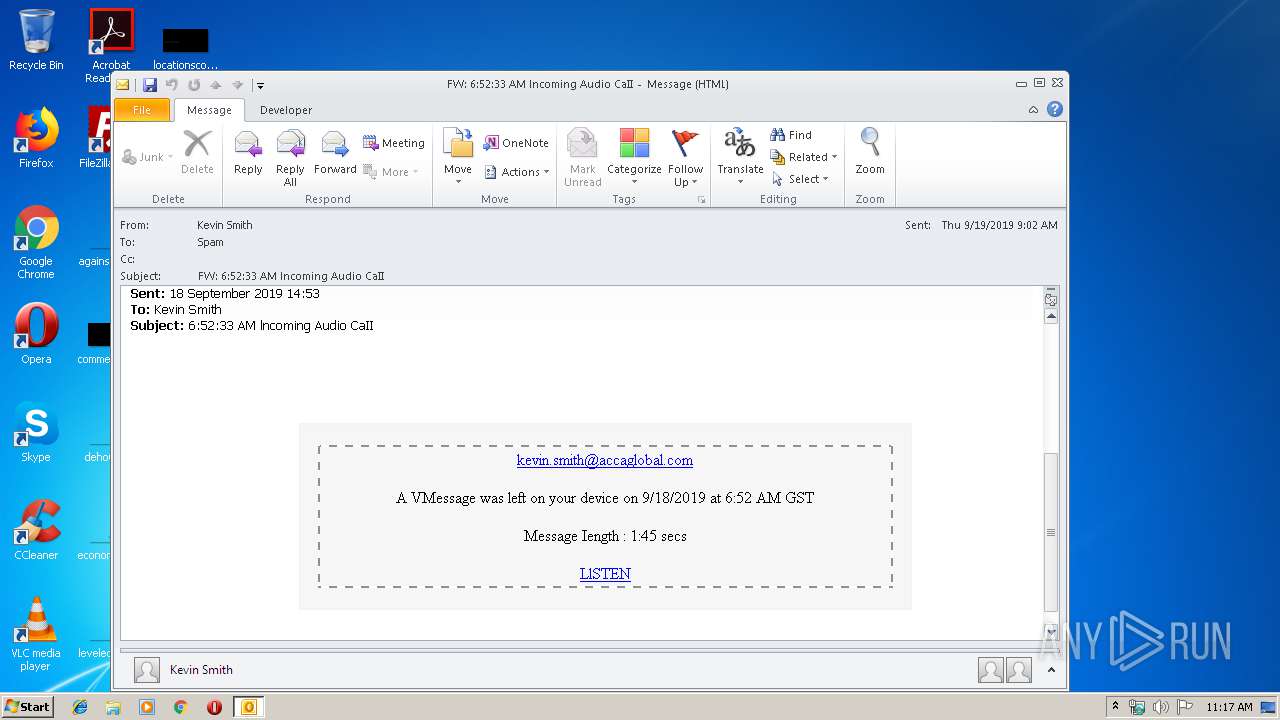
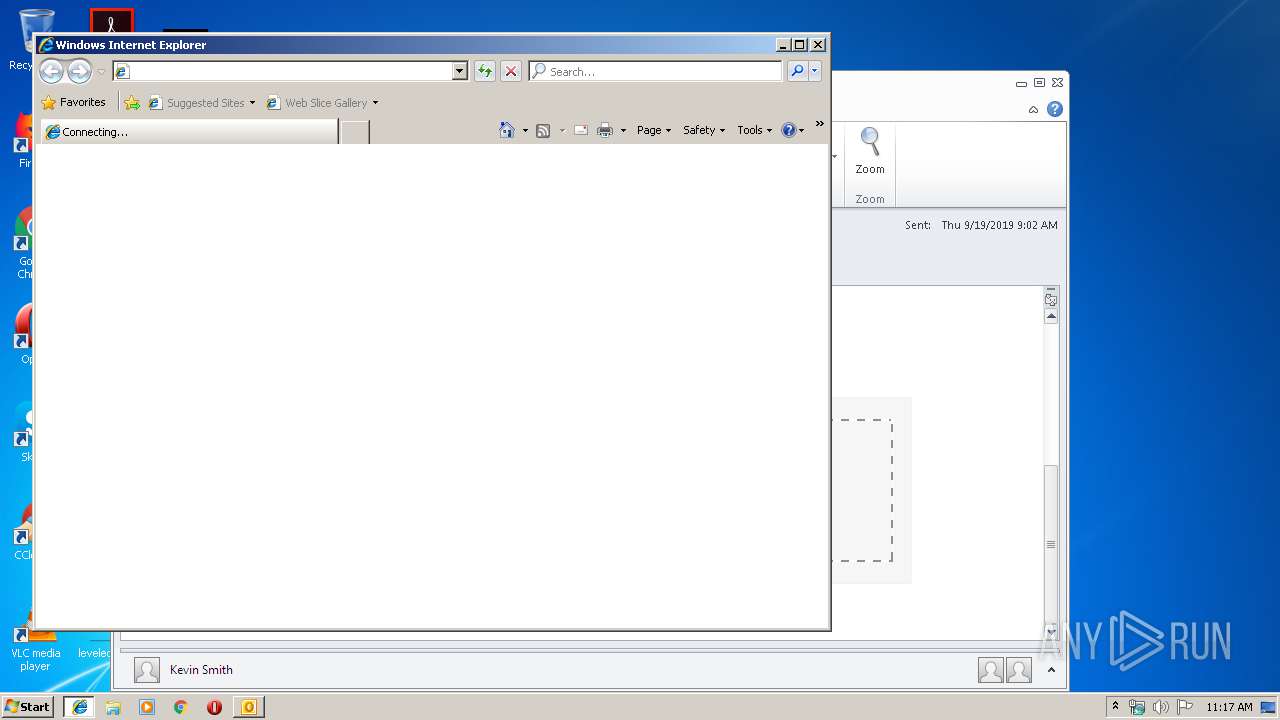
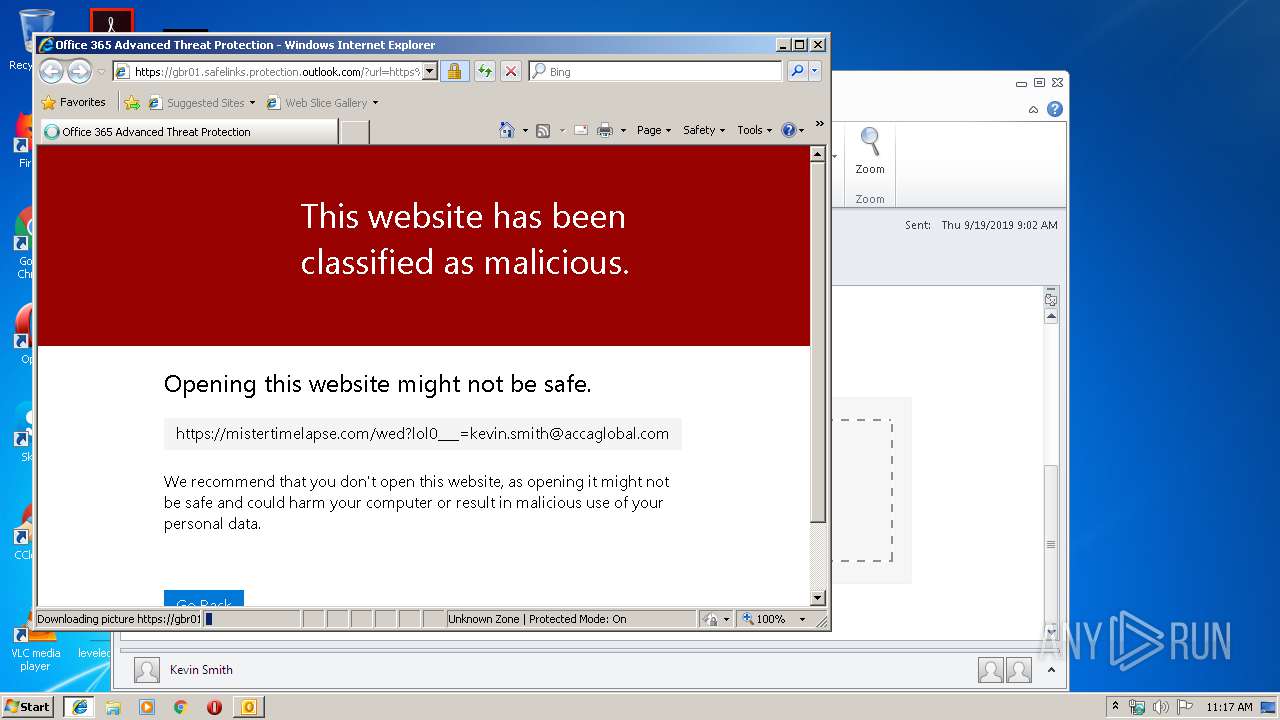
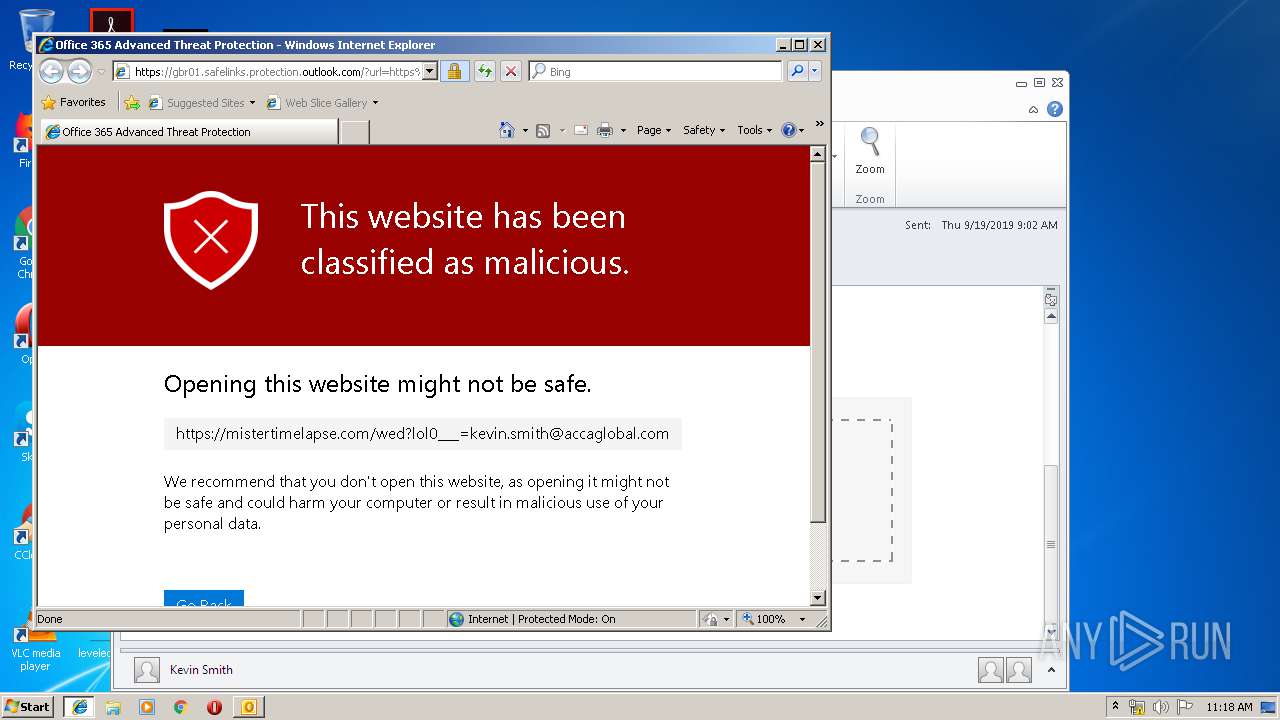
| 3184 | "C:\Program Files\Internet Explorer\iexplore.exe" https://gbr01.safelinks.protection.outlook.com/?url=https%3A%2F%2Fmistertimelapse.com%2Fwed%3Flol0___%3Dkevin.smith%40accaglobal.com&data=02%7C01%7CSpam%40accaglobal.com%7C6be8eee5be8a424065fb08d73cd7ab50%7Cf2e7de2c59ba49fe8c684cd333f96b01%7C0%7C0%7C637044769293745780&sdata=HZT19%2BwbhaAwA7wWs%2BuAAZw3%2FWgAAsd3ZaT2lQwTiUM%3D&reserved=0 | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3812 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3184 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 633
Read events
1 144
Write events
467
Delete events
22
Modification events
| (PID) Process: | (2892) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2892) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2892) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | |j! |
Value: 7C6A21004C0B0000010000000000000000000000 | |||
| (PID) Process: | (2892) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: 4C0B00001EAEA36CD36ED50100000000 | |||
| (PID) Process: | (2892) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (2892) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 220222080 | |||
| (PID) Process: | (2892) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (2892) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (2892) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (2892) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1328742421 | |||
Executable files
0
Suspicious files
0
Text files
33
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2892 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR9AED.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3184 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3184 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3812 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PUGA5MNJ\gbr01_safelinks_protection_outlook_com[1].txt | — | |
MD5:— | SHA256:— | |||
| 2892 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\StructuredQuery.log | text | |
MD5:— | SHA256:— | |||
| 3812 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3812 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\CVOO9LKX\gbr01_safelinks_protection_outlook_com[1].htm | html | |
MD5:— | SHA256:— | |||
| 3812 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3812 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PUGA5MNJ\site[1].js | text | |
MD5:— | SHA256:— | |||
| 3184 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\favicon[1].htm | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
7
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2892 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
3184 | iexplore.exe | GET | 200 | 13.107.21.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2892 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
— | — | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3812 | iexplore.exe | 104.47.20.28:443 | gbr01.safelinks.protection.outlook.com | Microsoft Corporation | GB | unknown |
3184 | iexplore.exe | 104.47.20.28:443 | gbr01.safelinks.protection.outlook.com | Microsoft Corporation | GB | unknown |
— | — | 104.47.20.28:443 | gbr01.safelinks.protection.outlook.com | Microsoft Corporation | GB | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
gbr01.safelinks.protection.outlook.com |
| whitelisted |
www.bing.com |
| whitelisted |