| download: | wps_office_inst.exe |
| Full analysis: | https://app.any.run/tasks/e5c6c2e8-aa57-4301-a695-752502748307 |
| Verdict: | Malicious activity |
| Analysis date: | August 28, 2019, 01:23:06 |
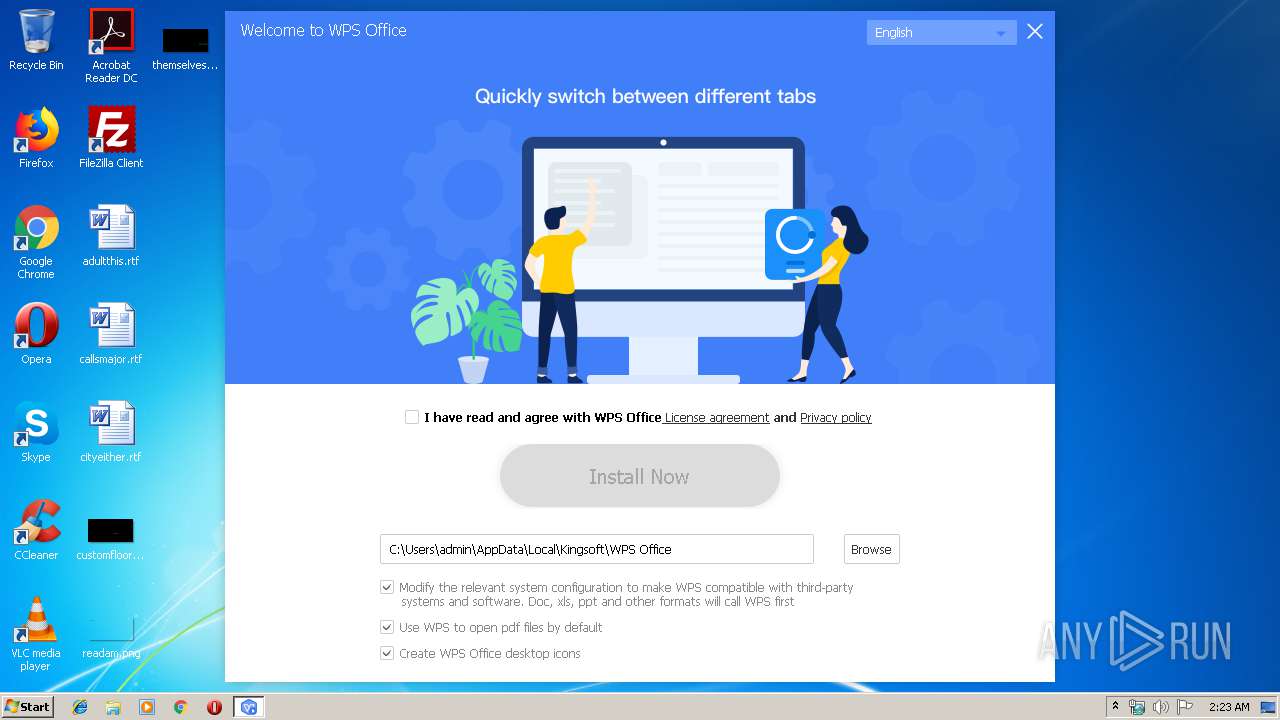
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 6A17BA16E84C08A8B165C632C43737BF |
| SHA1: | 9BC916FDBED4A1045409AD9B73804A017FC4F8E0 |
| SHA256: | 92068B17BC93EF8F0C97C768664B6DE0EB48DCD857CF4280D5D82B1263F3917D |
| SSDEEP: | 24576:VPOqEMPl99bbWCoTBfA5acLDwFLFVlnZ2AzPFGCyES8ooqixIUs/G9MxESK3dyEg:VtWxiacPwFLFvfJyJoqPUsREJ3YEte |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the user directory
- wps_office_inst.exe (PID: 3708)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (17.3) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (4.1) |
| .exe | | | Win32 Executable (generic) (2.8) |
| .exe | | | Generic Win/DOS Executable (1.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:08:16 08:43:52+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 1171456 |
| InitializedDataSize: | 669184 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xf732b |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | Zhuhai Kingsoft Office Software Co.,Ltd |
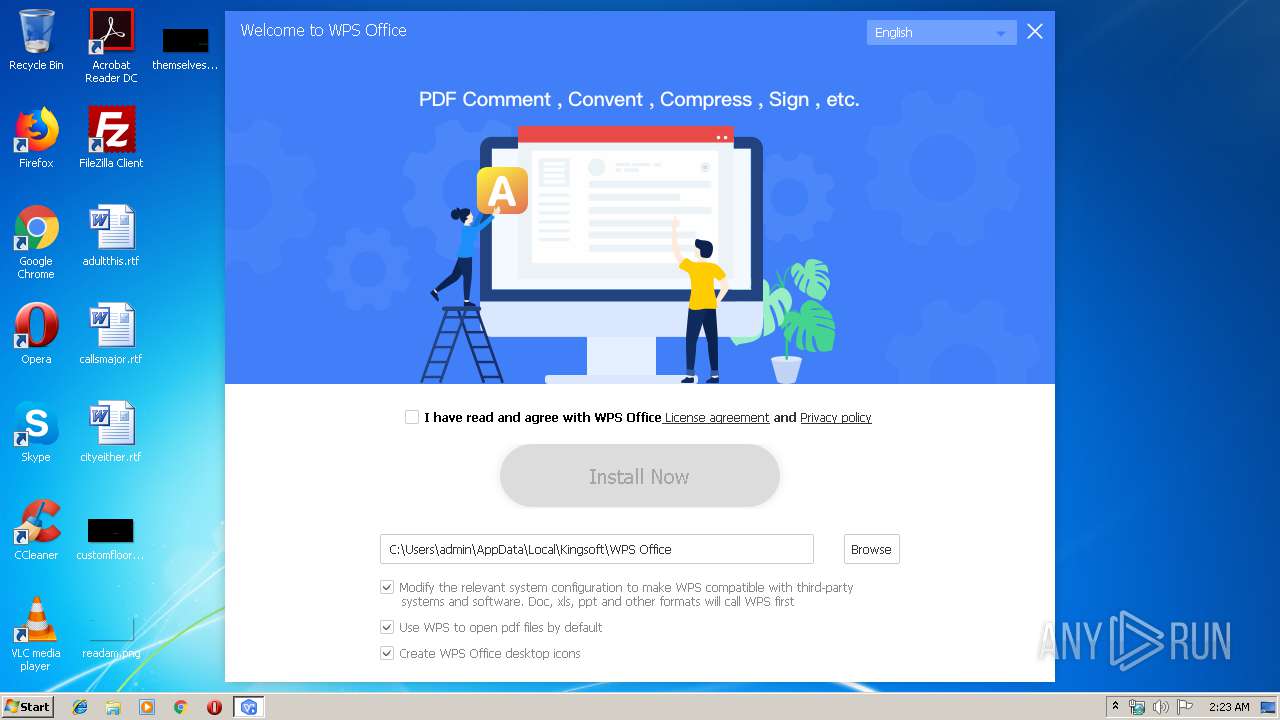
| FileDescription: | WPS Office Setup |
| FileVersion: | 0,0,0,0 |
| InternalName: | konlinesetup_xa |
| LegalCopyright: | Copyright©1988-2018 Kingsoft Corporation. All rights reserved. |
| OriginalFileName: | konlinesetup_xa.exe |
| ProductName: | WPS Office |
| ProductVersion: | 0,0,0,0 |
| MIMEType: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-Aug-2019 06:43:52 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Zhuhai Kingsoft Office Software Co.,Ltd |
| FileDescription: | WPS Office Setup |
| FileVersion: | 0,0,0,0 |
| InternalName: | konlinesetup_xa |
| LegalCopyright: | Copyright©1988-2018 Kingsoft Corporation. All rights reserved. |
| OriginalFilename: | konlinesetup_xa.exe |
| ProductName: | WPS Office |
| ProductVersion: | 0,0,0,0 |
| MIMEType: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 16-Aug-2019 06:43:52 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0011DFF5 | 0x0011E000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.19699 |
.rdata | 0x0011F000 | 0x000286C4 | 0x00028800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.08053 |
.data | 0x00148000 | 0x0000FBC0 | 0x0000C200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.31225 |
.rsrc | 0x00158000 | 0x00062204 | 0x00062400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.22984 |
.reloc | 0x001BB000 | 0x0000C6C4 | 0x0000C800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.25222 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.04637 | 885 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.21516 | 1128 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
3 | 4.59644 | 2440 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
4 | 7.95999 | 15814 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
5 | 4.41725 | 4264 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
6 | 3.87235 | 9640 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
7 | 3.57405 | 38056 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
101 | 7.99742 | 260267 | Latin 1 / Western European | Chinese - PRC | ZIPRES |
102 | 2.91176 | 104 | Latin 1 / Western European | Chinese - PRC | RT_GROUP_ICON |
Imports
KERNEL32.dll |
SHLWAPI.dll (delay-loaded) |
Total processes
33
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3708 | "C:\Users\admin\AppData\Local\Temp\wps_office_inst.exe" | C:\Users\admin\AppData\Local\Temp\wps_office_inst.exe | explorer.exe | ||||||||||||
User: admin Company: Zhuhai Kingsoft Office Software Co.,Ltd Integrity Level: MEDIUM Description: WPS Office Setup Exit code: 0 Version: 0,0,0,0 Modules
| |||||||||||||||
Total events
33
Read events
19
Write events
14
Delete events
0
Modification events
| (PID) Process: | (3708) wps_office_inst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wps_office_inst_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3708) wps_office_inst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wps_office_inst_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3708) wps_office_inst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wps_office_inst_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3708) wps_office_inst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wps_office_inst_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3708) wps_office_inst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wps_office_inst_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3708) wps_office_inst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wps_office_inst_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3708) wps_office_inst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wps_office_inst_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3708) wps_office_inst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wps_office_inst_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3708) wps_office_inst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wps_office_inst_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3708) wps_office_inst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wps_office_inst_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3708 | wps_office_inst.exe | C:\Users\admin\AppData\Roaming\konlinesetup\down\index.ini | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
6
DNS requests
3
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3708 | wps_office_inst.exe | GET | 200 | 52.193.251.216:80 | http://haiwai-ic.ksosoft.com/infos.ads?v=D1S1E1&d=ZG09L3dwcy9jbGllbnQva29ubGluZXNldHVwJmFjdGlvbj1rb25saW5lc2V0dXAmcG51bT02JnAwPUFEQkM4RkJBMDA5QzQ0NTk5RkQ5Mjk0M0FGRDQ2QjVCfDhCOUZFMEU1MDFCQzhBOUQ2OEQwMzQ2MUQxODVDMTA1fGFlMGU4NmRjYTU4NzMxOGYwYjUyZTBhYmNiNDRhZTg3JnAxPTAuMC4wLjAmcDI9MTAwLjEwMDEmcDM9JnA0PWJ0bl9jbGljayZwNT1zdGFydA== | JP | — | — | unknown |
3708 | wps_office_inst.exe | HEAD | 200 | 47.246.43.227:80 | http://wdl1.pcfg.cache.wpscdn.com/wpsdl/wpsoffice/onlinesetup/distsrc/100.1001/index.ini | US | — | — | malicious |
3708 | wps_office_inst.exe | HEAD | 200 | 47.246.43.227:80 | http://wdl1.pcfg.cache.wpscdn.com/wpsdl/wpsoffice/onlinesetup/package/setup_XA_mui_Free.exe | US | — | — | malicious |
3708 | wps_office_inst.exe | GET | — | 47.246.43.227:80 | http://wdl1.pcfg.cache.wpscdn.com/wpsdl/wpsoffice/onlinesetup/package/setup_XA_mui_Free.exe | US | — | — | malicious |
3708 | wps_office_inst.exe | GET | 200 | 52.193.251.216:80 | http://haiwai-ic.ksosoft.com/infos.ads?v=D1S1E1&d=ZG09L3dwcy9jbGllbnQva29ubGluZXNldHVwJmFjdGlvbj1rb25saW5lc2V0dXAmcG51bT02JnAwPUFEQkM4RkJBMDA5QzQ0NTk5RkQ5Mjk0M0FGRDQ2QjVCfDhCOUZFMEU1MDFCQzhBOUQ2OEQwMzQ2MUQxODVDMTA1fGFlMGU4NmRjYTU4NzMxOGYwYjUyZTBhYmNiNDRhZTg3JnAxPTAuMC4wLjAmcDI9MTAwLjEwMDEmcDM9JnA0PXN0YXJ0dXBfbW9kZSZwNT1lbGV2YXRlV2hlbk5lY2Vzc2FyeQ== | JP | — | — | unknown |
3708 | wps_office_inst.exe | GET | 200 | 52.193.251.216:80 | http://haiwai-ic.ksosoft.com/infos.ads?v=D1S1E1&d=ZG09L3dwcy9jbGllbnQva29ubGluZXNldHVwJmFjdGlvbj1rb25saW5lc2V0dXAmcG51bT01JnAwPUFEQkM4RkJBMDA5QzQ0NTk5RkQ5Mjk0M0FGRDQ2QjVCfDhCOUZFMEU1MDFCQzhBOUQ2OEQwMzQ2MUQxODVDMTA1fGFlMGU4NmRjYTU4NzMxOGYwYjUyZTBhYmNiNDRhZTg3JnAxPTAuMC4wLjAmcDI9MTAwLjEwMDEmcDM9JnA0PXNob3c= | JP | — | — | unknown |
3708 | wps_office_inst.exe | GET | 200 | 47.246.43.227:80 | http://wdl1.pcfg.cache.wpscdn.com/wpsdl/wpsoffice/onlinesetup/distsrc/100.1001/index.ini | US | text | 2.21 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3708 | wps_office_inst.exe | 52.193.251.216:80 | haiwai-ic.ksosoft.com | Amazon.com, Inc. | JP | unknown |
3708 | wps_office_inst.exe | 47.246.43.227:80 | wdl1.pcfg.cache.wpscdn.com | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
haiwai-ic.ksosoft.com |
| unknown |
wdl1.pcfg.cache.wpscdn.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3708 | wps_office_inst.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |