| File name: | file.exe |
| Full analysis: | https://app.any.run/tasks/09cd0763-3182-4f63-8677-67e7320b1688 |
| Verdict: | Malicious activity |
| Analysis date: | November 10, 2020, 06:38:20 |
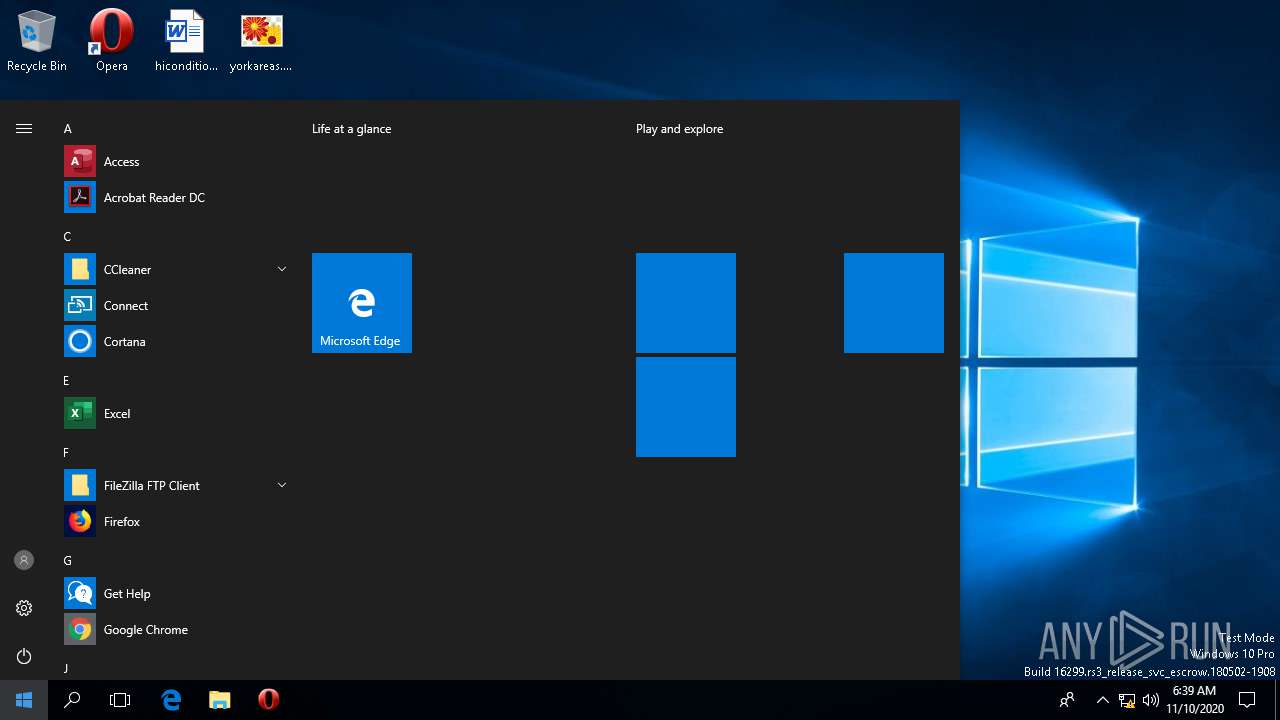
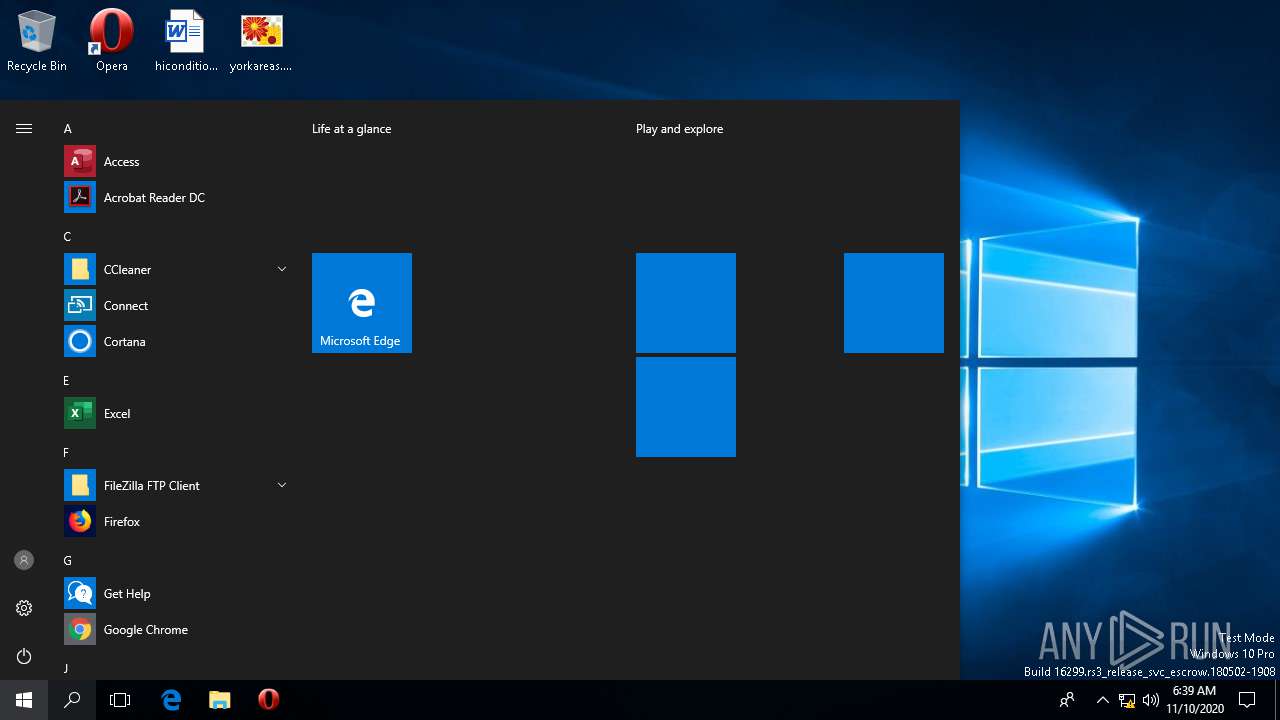
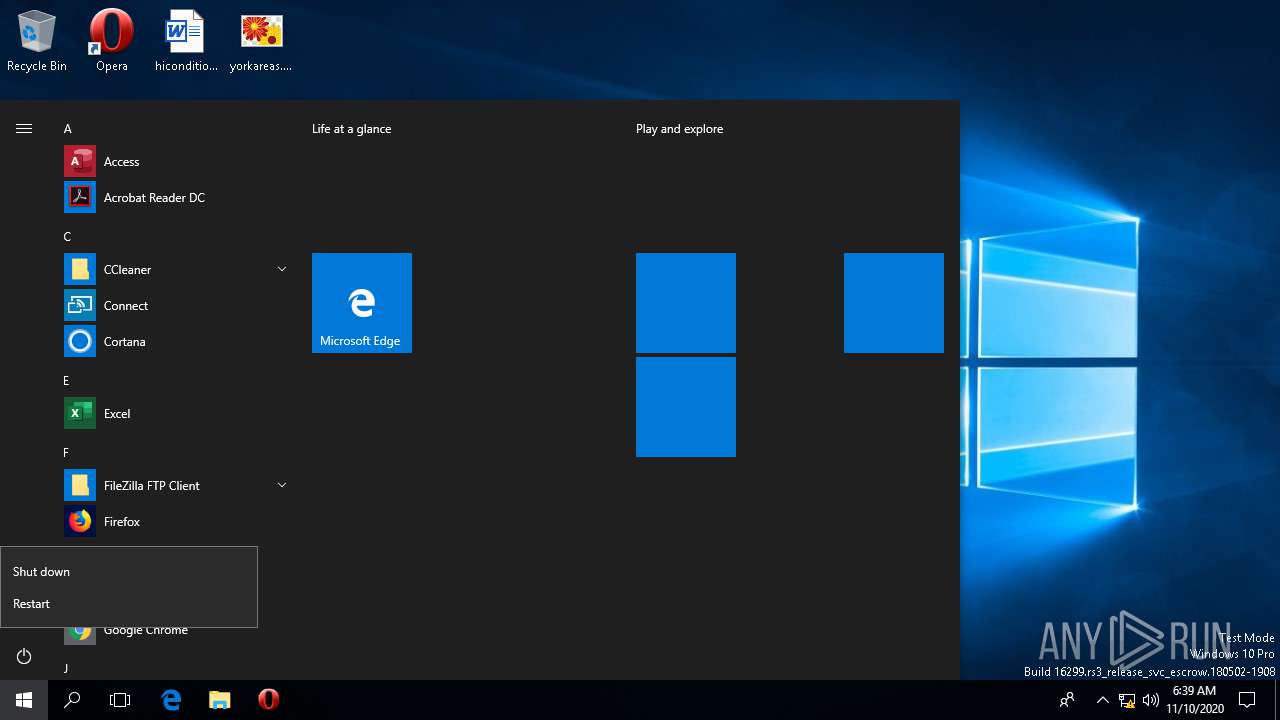
| OS: | Windows 10 Professional (build: 16299, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | BA6E450092B8ED3E5FCD4257933D9BA2 |
| SHA1: | CE9D126E84248B2236224862FAC0804B49D157C8 |
| SHA256: | 91FBC712688C9867ECF3DEC8171A4248B8C472985F297E24C4A97D1FF676B26C |
| SSDEEP: | 12288:XHunKf2G1PA7UDl5gj/gtnouecR/3rJv74F+wkFwVgqVSc5feBK9PGEYqXIME9kY:ei2Gq7etnogRdvEk1RcoGGAYM0X6g1 |
MALICIOUS
Uses Task Scheduler to run other applications
- cmd.exe (PID: 340)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 3224)
Loads the Task Scheduler DLL interface
- schtasks.exe (PID: 3224)
SUSPICIOUS
Executable content was dropped or overwritten
- file.exe (PID: 1524)
Starts CMD.EXE for commands execution
- file.exe (PID: 1524)
Executes PowerShell scripts
- MSBuild.exe (PID: 2228)
Reads the machine GUID from the registry
- MSBuild.exe (PID: 2228)
- powershell.exe (PID: 2408)
Executed via COM
- DllHost.exe (PID: 112)
- DllHost.exe (PID: 4524)
- rundll32.exe (PID: 1920)
INFO
Reads the software policy settings
- powershell.exe (PID: 2408)
Reads settings of System Certificates
- powershell.exe (PID: 2408)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:11:06 04:47:46+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 114176 |
| InitializedDataSize: | 73216 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2382 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 06-Nov-2020 03:47:46 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 06-Nov-2020 03:47:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001BD4F | 0x0001BE00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.63901 |
.rdata | 0x0001D000 | 0x00006EA2 | 0x00007000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.23779 |
.data | 0x00024000 | 0x00006D00 | 0x00006200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.68784 |
.gfids | 0x0002B000 | 0x000000E4 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.1815 |
.rsrc | 0x0002C000 | 0x00003DC8 | 0x00003E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.63788 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.65379 | 4264 | UNKNOWN | English - United States | RT_ICON |
3 | 5.3856 | 9640 | UNKNOWN | English - United States | RT_ICON |
IDI_SMALL | 2.45849 | 48 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
CRYPT32.dll |
IMM32.dll |
KERNEL32.dll |
ODBC32.dll |
USER32.dll |
ole32.dll |
pdh.dll |
Total processes
199
Monitored processes
10
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 112 | C:\WINDOWS\system32\DllHost.exe /Processid:{7966B4D8-4FDC-4126-A10B-39A3209AD251} | C:\WINDOWS\system32\DllHost.exe | — | svchost.exe | |||||||||||
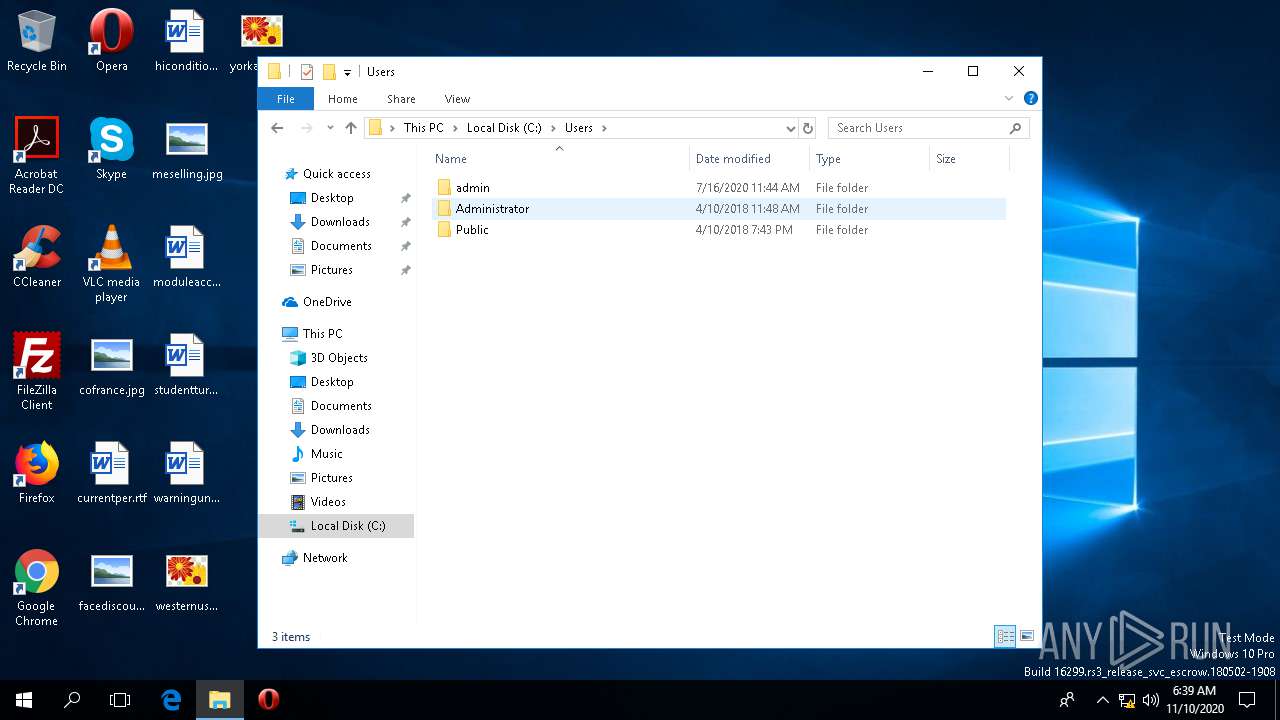
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 340 | cmd /c schtasks /Create /TN name /XML "C:\Users\admin\AppData\Local\Temp\7fca8aa0ef6341bf8788df7f5f6d2f2a.xml" | C:\WINDOWS\SysWOW64\cmd.exe | — | file.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1492 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\WINDOWS\system32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
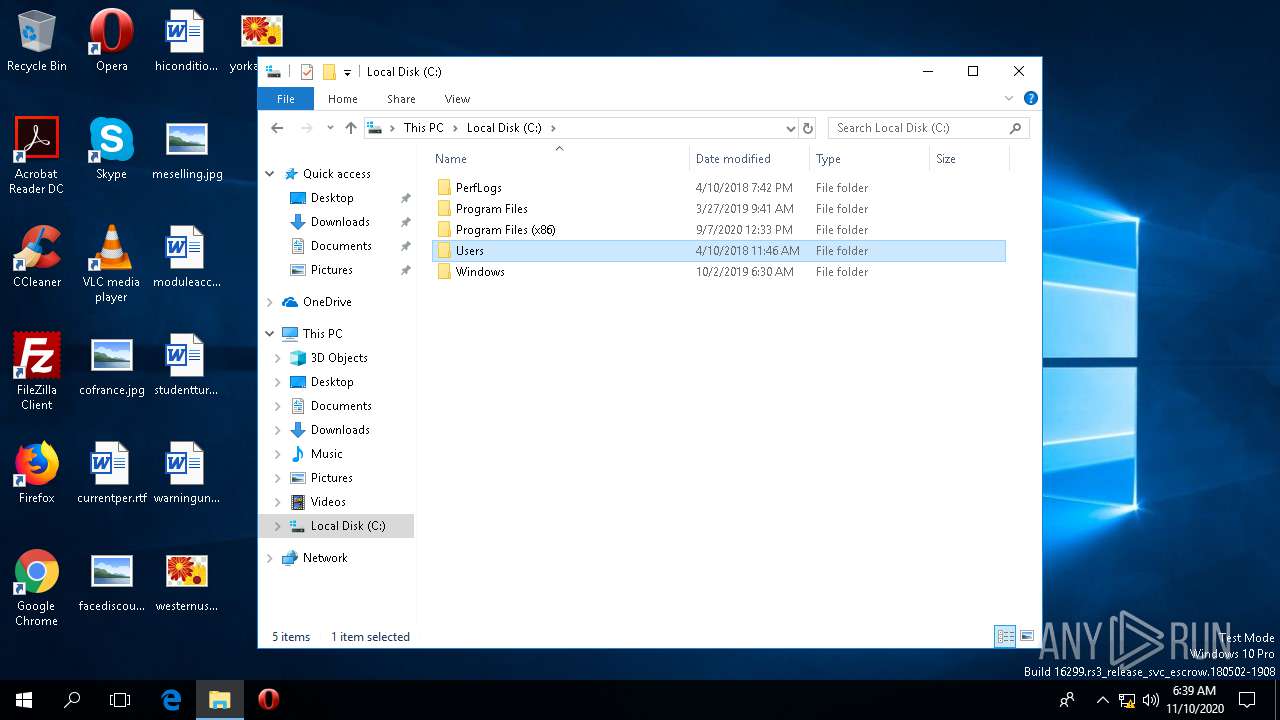
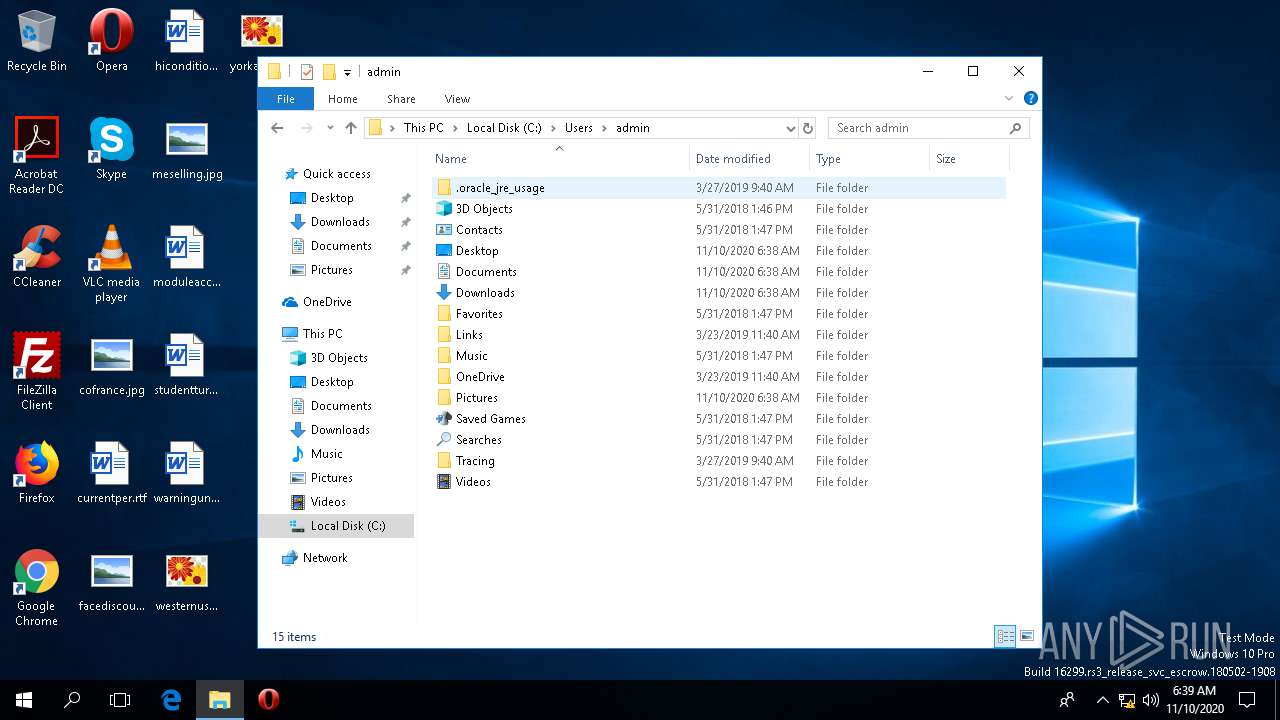
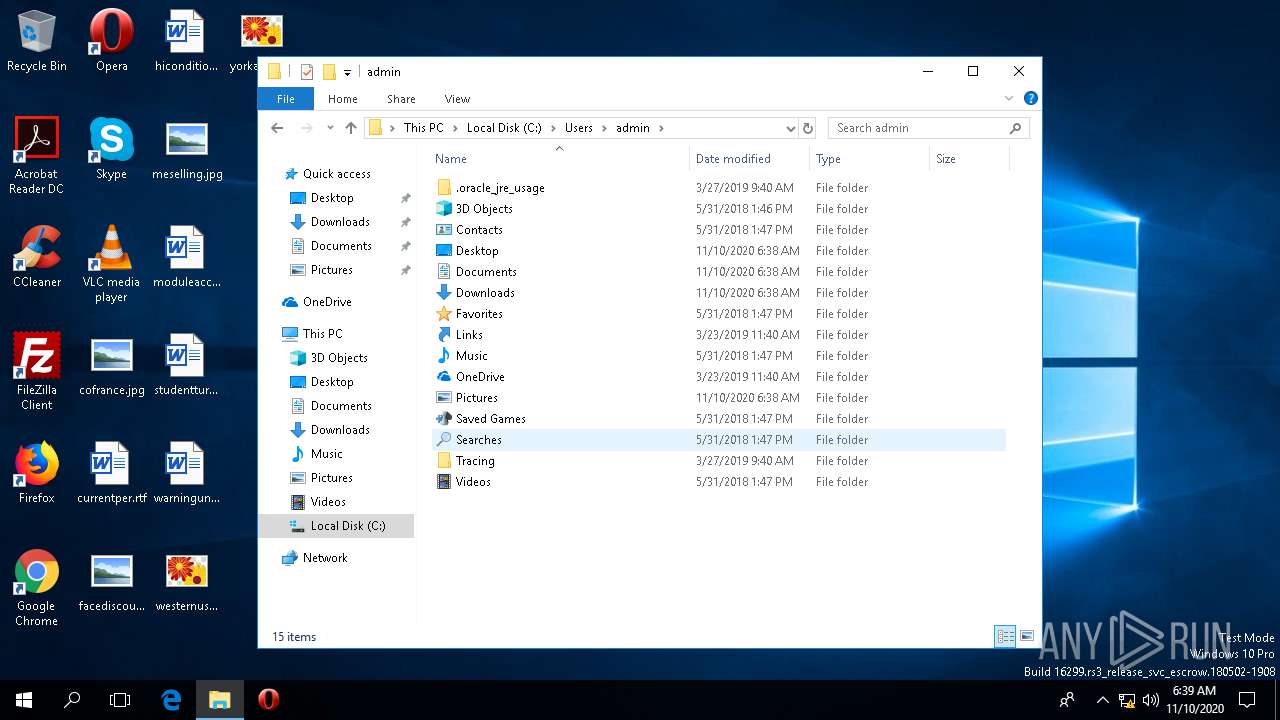
| 1524 | "C:\Users\admin\Downloads\file.exe" | C:\Users\admin\Downloads\file.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1920 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\WINDOWS\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2228 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | — | file.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Exit code: 0 Version: 4.7.2556.0 built by: NET471REL1 Modules
| |||||||||||||||
| 2408 | "powershell" Start-Sleep -Seconds 2; Remove-Item -path 'C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe' | C:\WINDOWS\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | MSBuild.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2840 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\WINDOWS\system32\conhost.exe | file.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3224 | schtasks /Create /TN name /XML "C:\Users\admin\AppData\Local\Temp\7fca8aa0ef6341bf8788df7f5f6d2f2a.xml" | C:\WINDOWS\SysWOW64\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 1 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4524 | C:\WINDOWS\system32\DllHost.exe /Processid:{973D20D7-562D-44B9-B70B-5A0F49CCDF3F} | C:\WINDOWS\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 1073807364 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
540
Read events
536
Write events
4
Delete events
0
Modification events
| (PID) Process: | (2408) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\19e\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
1
Suspicious files
5
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2408 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_fuhcs3dn.or3.ps1 | — | |
MD5:— | SHA256:— | |||
| 2408 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_a014koyj.mfm.psm1 | — | |
MD5:— | SHA256:— | |||
| 4524 | DllHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Cortana_cw5n1h2txyewy\AppData\Indexed DB\IndexedDB.edb | — | |
MD5:— | SHA256:— | |||
| 4524 | DllHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Cortana_cw5n1h2txyewy\AppData\Indexed DB\IndexedDB.jfm | — | |
MD5:— | SHA256:— | |||
| 4524 | DllHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Cortana_cw5n1h2txyewy\AppData\Indexed DB\edb.log | — | |
MD5:— | SHA256:— | |||
| 2408 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\CLR_v4.0_32\UsageLogs\powershell.exe.log | text | |
MD5:— | SHA256:— | |||
| 2228 | MSBuild.exe | C:\Users\admin\AppData\Local\Microsoft\CLR_v4.0_32\UsageLogs\MSBuild.exe.log | text | |
MD5:— | SHA256:— | |||
| 2408 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:— | SHA256:— | |||
| 4524 | DllHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Cortana_cw5n1h2txyewy\AppData\Indexed DB\edb.chk | binary | |
MD5:— | SHA256:— | |||
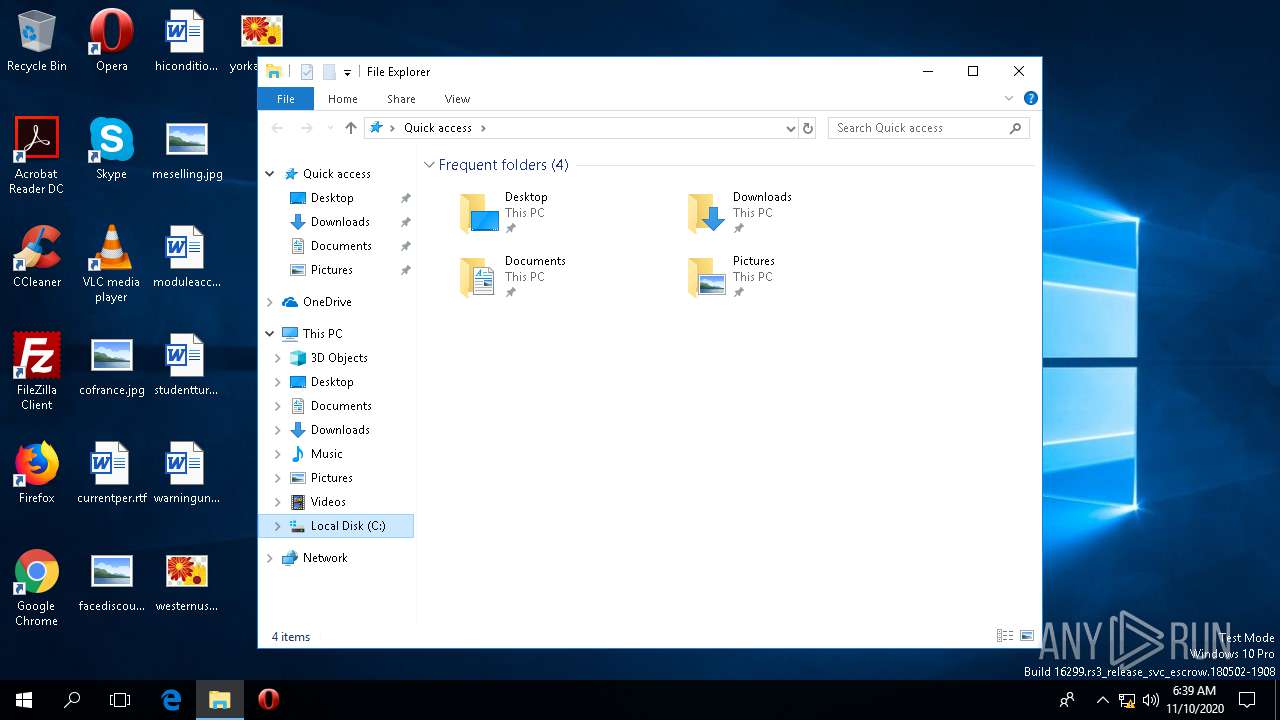
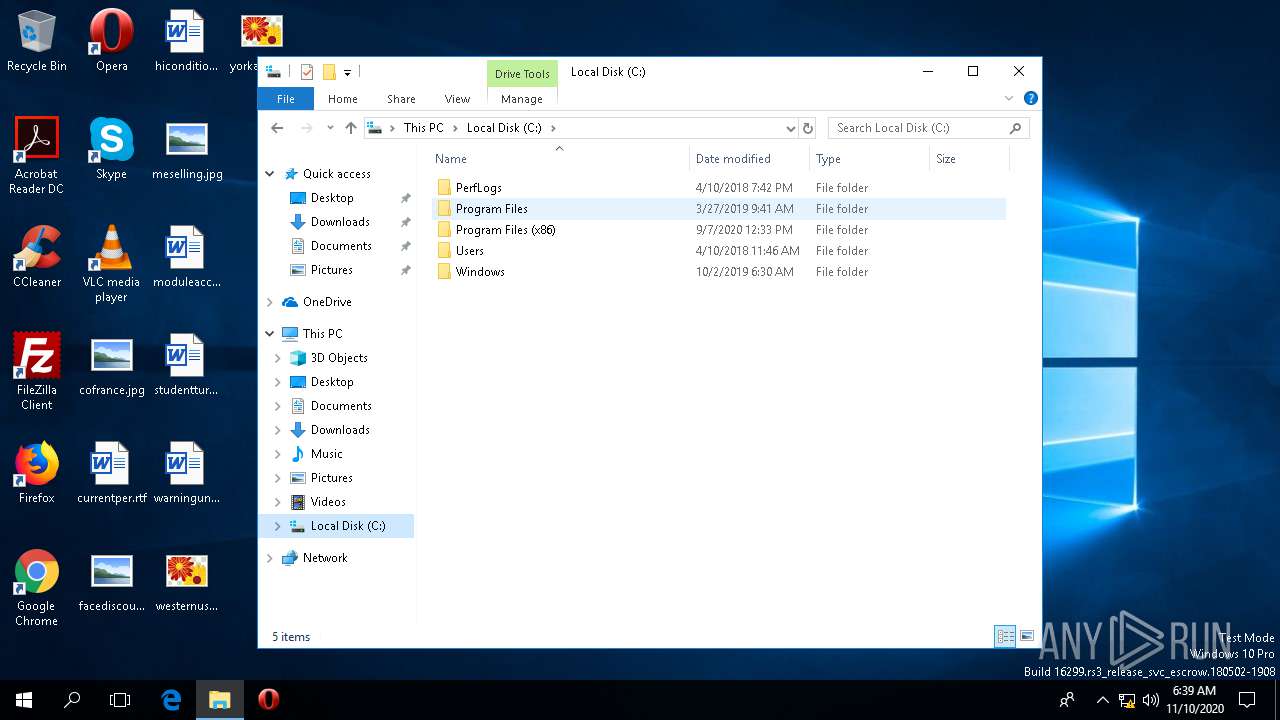
| 1524 | file.exe | C:\Users\admin\AppData\Local\Temp\folder\file.exe | executable | |
MD5:7A91C93EDA51BEE05B875B0145FE3FDD | SHA256:39692EC811314D940487A4891D0B355B46B4FA22BA3212356D16A8C5B79FEEFF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
3
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
self.events.data.microsoft.com |
| whitelisted |
config.edge.skype.com |
| malicious |
Threats
Process | Message |
|---|---|
conhost.exe | InitSideBySide failed create an activation context. Error: 1814 |