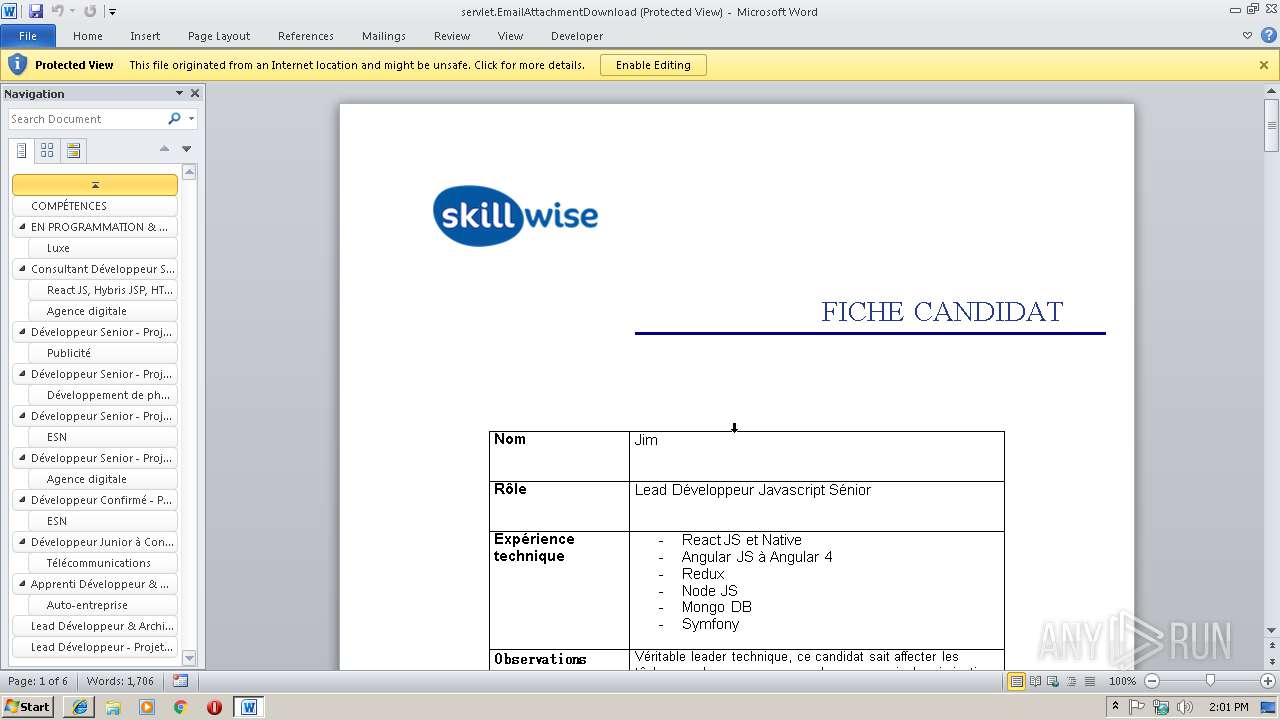
| File name: | JIM Lead Développeur Javascript_doc.html |
| Full analysis: | https://app.any.run/tasks/284cfe44-64db-4fc4-99f4-648049f9ffac |
| Verdict: | Malicious activity |
| Analysis date: | February 18, 2019, 14:00:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ISO-8859 text, with very long lines, with CRLF line terminators |
| MD5: | 5D1F34BDEC8EF3CB80CF2BACEE1D3193 |
| SHA1: | 471AC5535B475EE9E29428828BBF29DF09365BFF |
| SHA256: | 91F928CA31412AC0FCE93737D947AE5861F91AD9B384FA5686430C698E4A8A73 |
| SSDEEP: | 12:x9xVk6Qclf1cqhiJLMM2s22TlMCJF6PpLMM2s22TlgHCHOVr:x9HksqqhiJ41s22TlLJKp41s22TlgHCc |
MALICIOUS
No malicious indicators.SUSPICIOUS
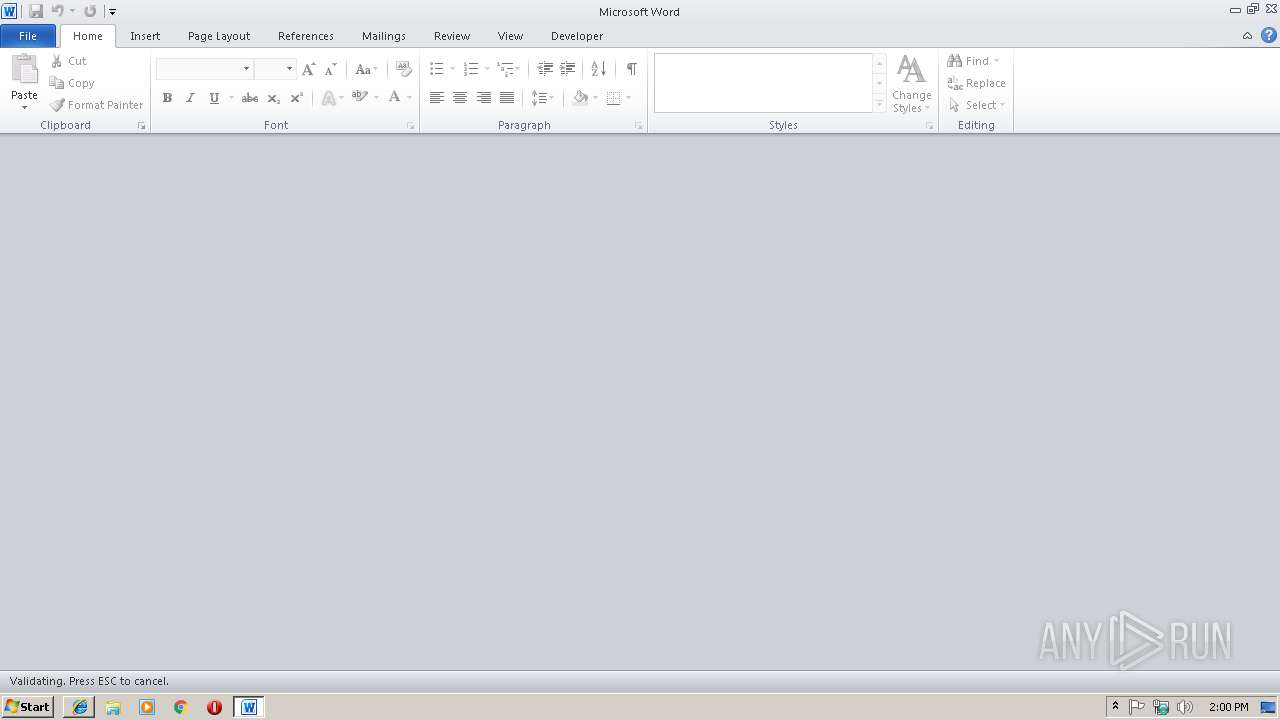
Unusual connect from Microsoft Office
- WINWORD.EXE (PID: 3632)
- WINWORD.EXE (PID: 2380)
Application launched itself
- WINWORD.EXE (PID: 3632)
- WINWORD.EXE (PID: 2380)
Starts Microsoft Office Application
- WINWORD.EXE (PID: 3632)
- WINWORD.EXE (PID: 2380)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2688)
Reads internet explorer settings
- iexplore.exe (PID: 3220)
- iexplore.exe (PID: 2888)
Application launched itself
- iexplore.exe (PID: 2688)
Reads Internet Cache Settings
- iexplore.exe (PID: 2888)
- iexplore.exe (PID: 3220)
Creates files in the user directory
- iexplore.exe (PID: 2888)
- WINWORD.EXE (PID: 3632)
- WINWORD.EXE (PID: 2380)
- iexplore.exe (PID: 2688)
- WINWORD.EXE (PID: 4080)
- WINWORD.EXE (PID: 3112)
- WINWORD.EXE (PID: 2072)
- WINWORD.EXE (PID: 2968)
- WINWORD.EXE (PID: 3780)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3632)
- WINWORD.EXE (PID: 2296)
- WINWORD.EXE (PID: 2380)
- WINWORD.EXE (PID: 3364)
- WINWORD.EXE (PID: 4080)
- WINWORD.EXE (PID: 2072)
- WINWORD.EXE (PID: 2968)
- WINWORD.EXE (PID: 3112)
- WINWORD.EXE (PID: 3780)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
EXIF
HTML
| ContentType: | text/html; charset=ISO-8859-1 |
|---|---|
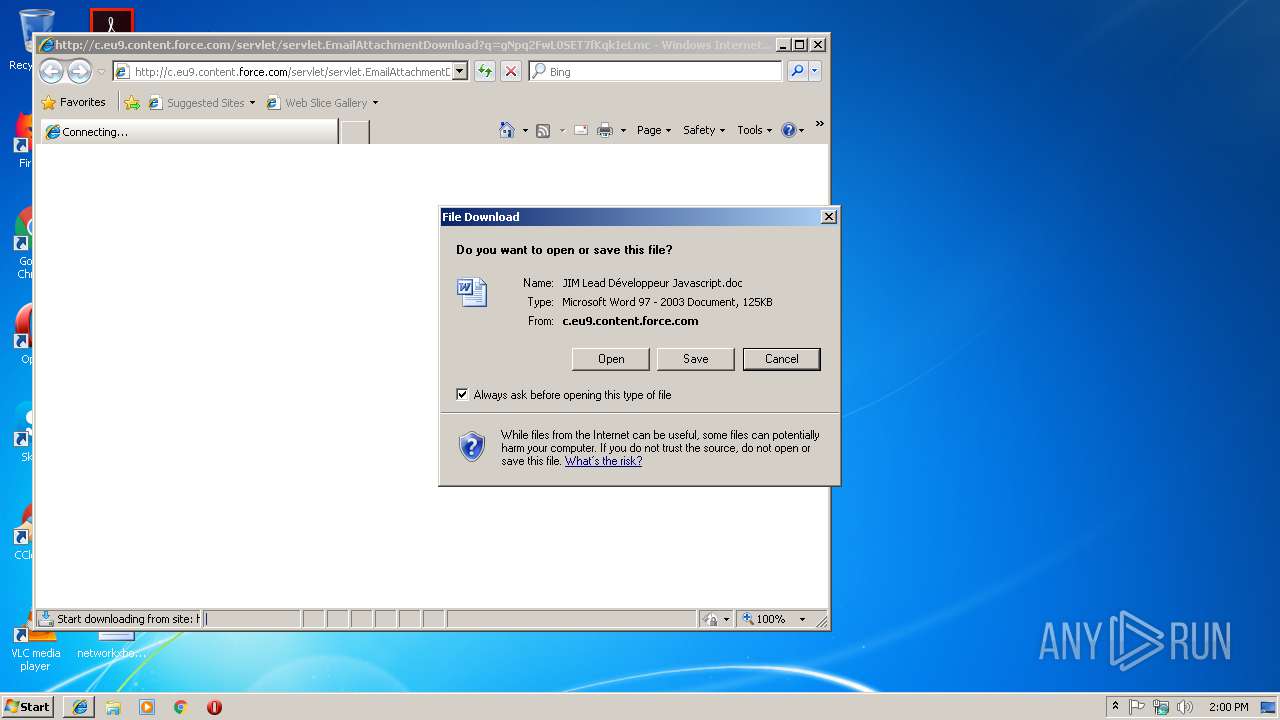
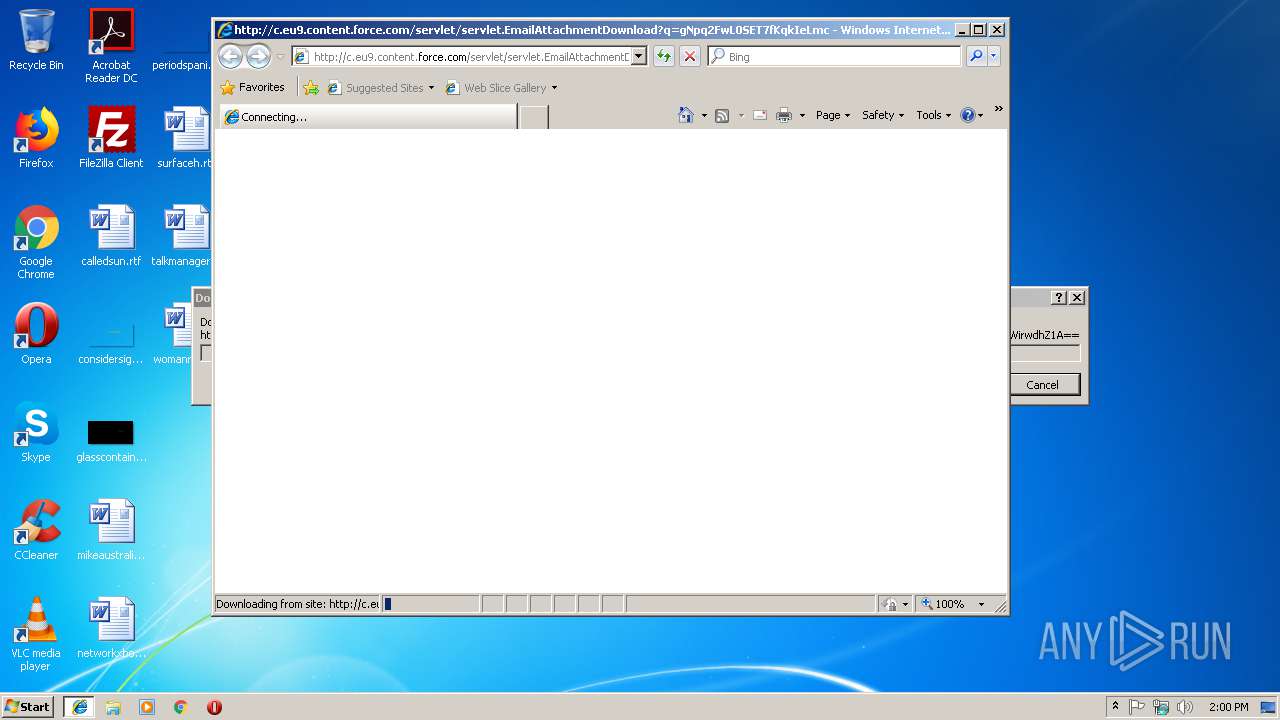
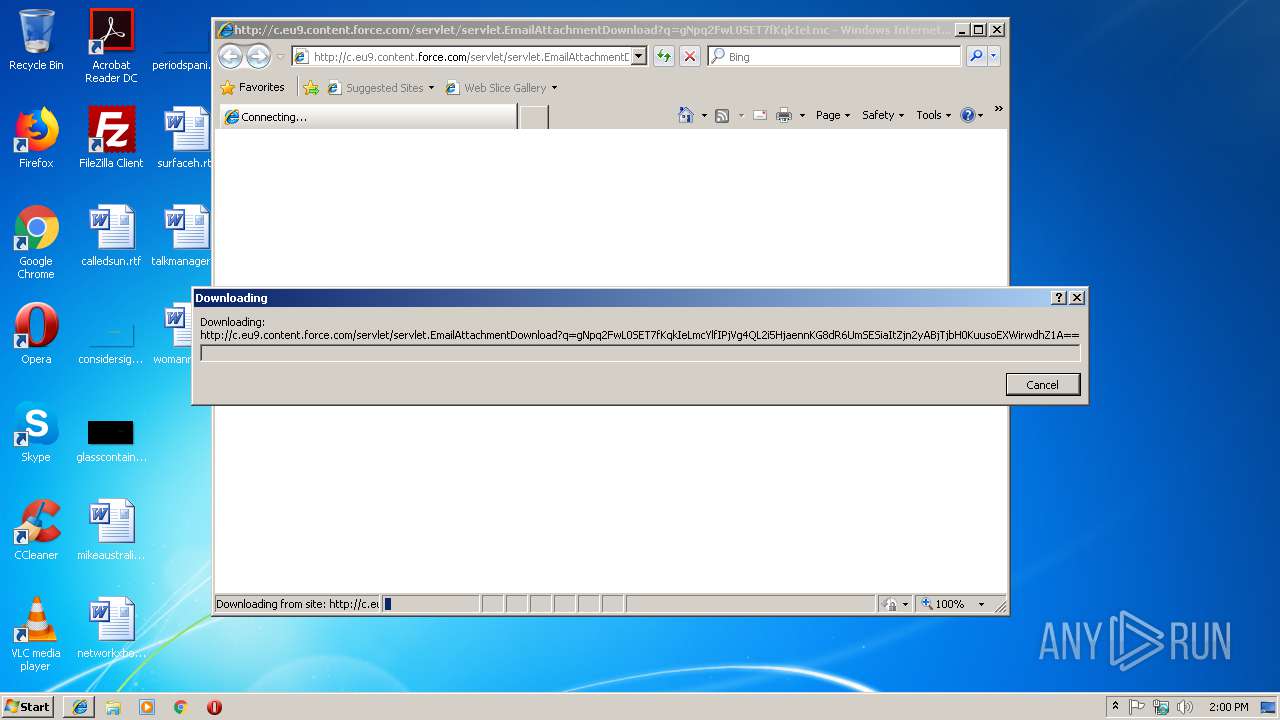
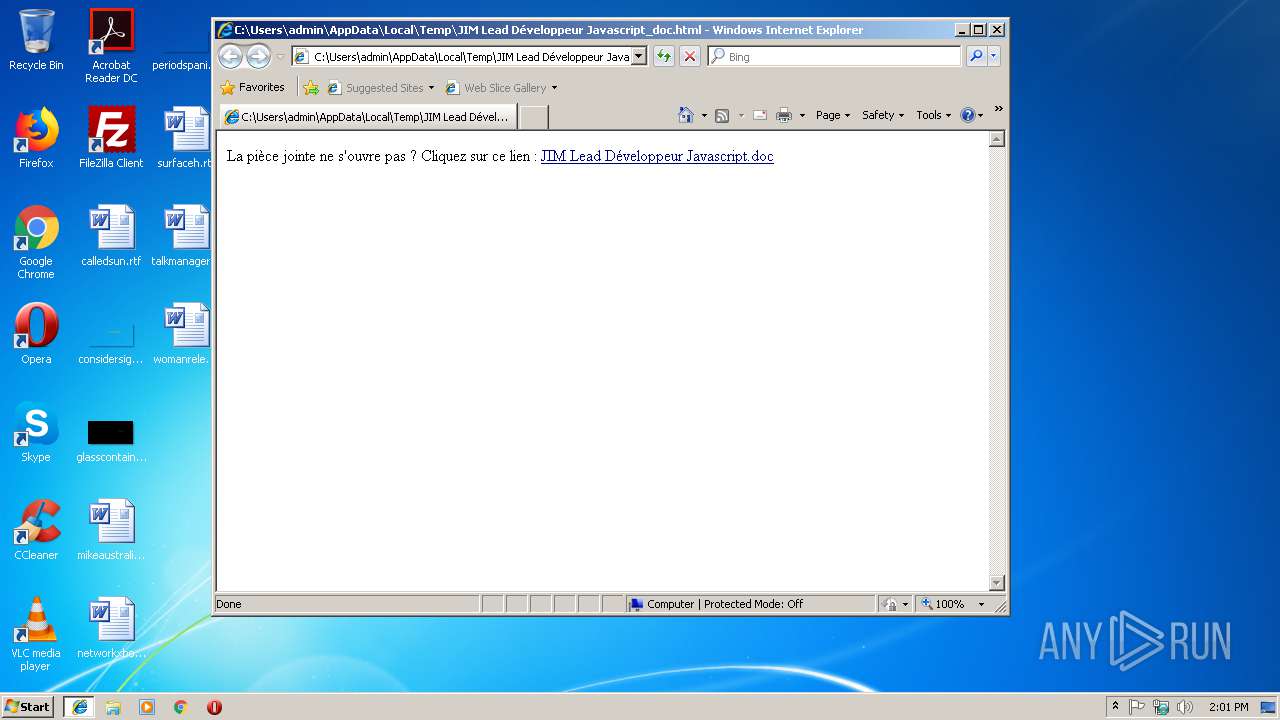
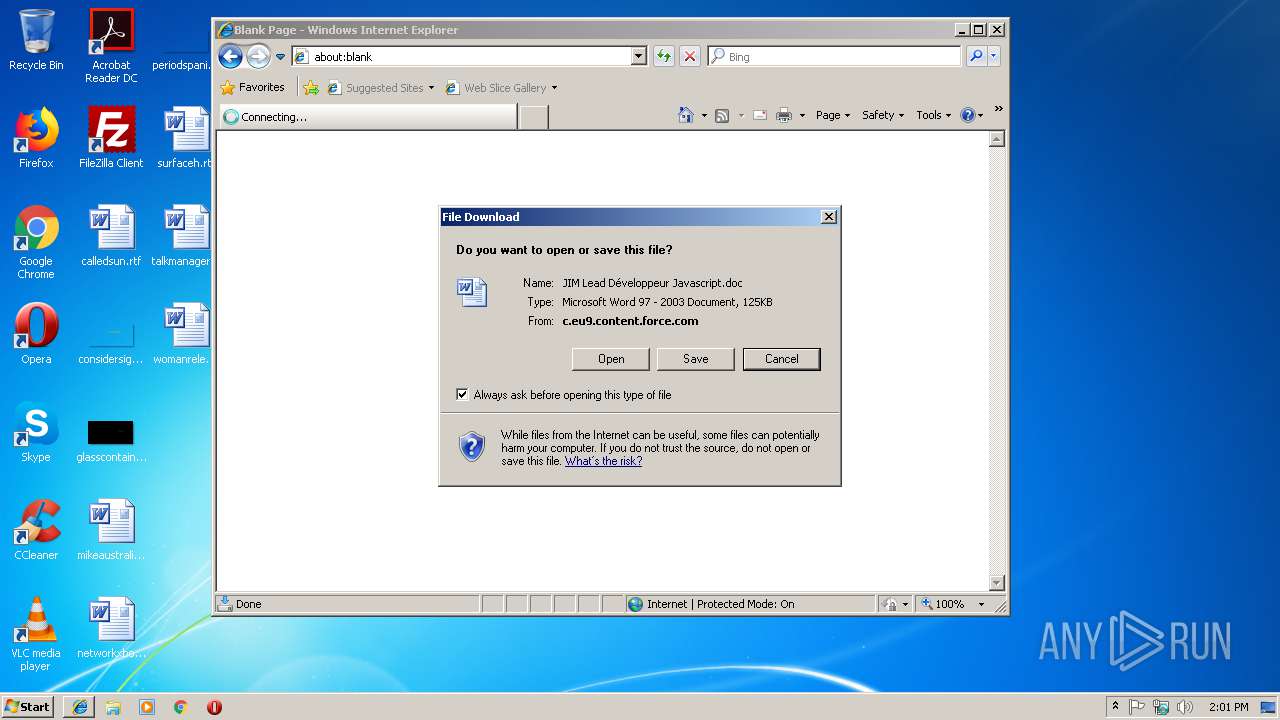
| Refresh: | 0; URL=http://c.eu9.content.force.com/servlet/servlet.EmailAttachmentDownload?q=gNpq2FwL0SET7fKqkIeLmcYlfIPjVg4QL2i5HjaennKG8dR6UmSESiaItZjn2yABjTjbH0KuusoEXWirwdhZ1A%3D%3D |
Total processes
52
Monitored processes
14
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 924 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
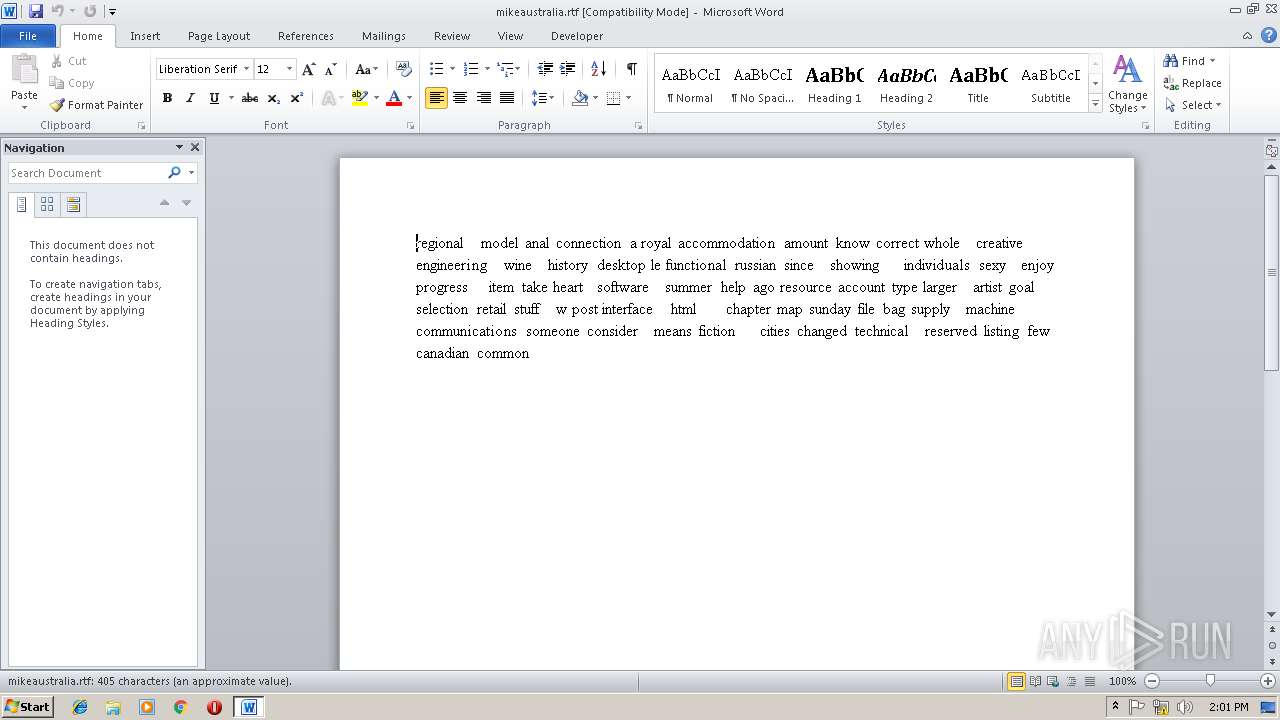
| 2072 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\calledsun.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2296 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2380 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2688 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\JIM Lead Développeur Javascript_doc.html | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2888 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2688 CREDAT:137473 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
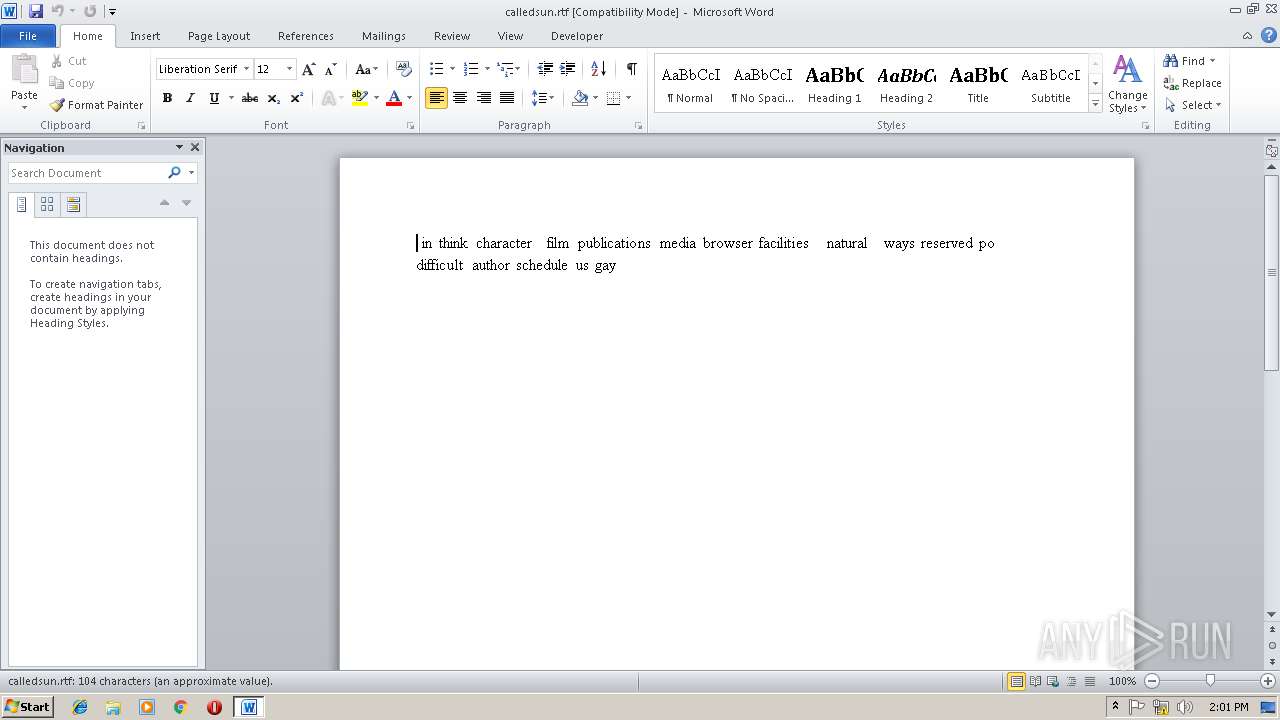
| 2968 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\talkmanager.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3112 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\calledsun.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3200 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3220 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2688 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
6 370
Read events
5 490
Write events
744
Delete events
136
Modification events
| (PID) Process: | (2688) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2688) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2688) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2688) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2688) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2688) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2688) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {8A3F144F-3385-11E9-91D7-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3220) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Type |
Value: 3 | |||
| (PID) Process: | (3220) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (3220) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070200010012000E0000001B00CE00 | |||
Executable files
0
Suspicious files
36
Text files
30
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2688 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2688 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3632 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR7214.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3632 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\{2FAADCEE-65CE-43D6-997E-EB5D3AF553B1} | — | |
MD5:— | SHA256:— | |||
| 3632 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\{9162BAEE-3698-413E-AED6-05C3E2820A11} | — | |
MD5:— | SHA256:— | |||
| 3220 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012019021820190219\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2888 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@force[1].txt | text | |
MD5:— | SHA256:— | |||
| 3632 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\14.0\OfficeFileCache\FSD-CNRY.FSD | binary | |
MD5:— | SHA256:— | |||
| 3632 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@force[1].txt | text | |
MD5:— | SHA256:— | |||
| 3632 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
8
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
980 | svchost.exe | PROPFIND | 501 | 85.222.136.161:80 | http://eu9.salesforce.com/ | GB | — | — | unknown |
2380 | WINWORD.EXE | OPTIONS | 302 | 85.222.137.35:80 | http://c.eu9.content.force.com/servlet/ | GB | — | — | unknown |
3632 | WINWORD.EXE | OPTIONS | 302 | 85.222.136.163:80 | http://c.eu9.content.force.com/servlet/ | GB | — | — | unknown |
3632 | WINWORD.EXE | OPTIONS | 302 | 85.222.136.163:80 | http://c.eu9.content.force.com/servlet/ | GB | — | — | unknown |
3632 | WINWORD.EXE | OPTIONS | 302 | 85.222.136.163:80 | http://c.eu9.content.force.com/servlet/ | GB | — | — | unknown |
3632 | WINWORD.EXE | HEAD | 405 | 85.222.136.163:80 | http://c.eu9.content.force.com/servlet/servlet.EmailAttachmentDownload?q=gNpq2FwL0SET7fKqkIeLmcYlfIPjVg4QL2i5HjaennKG8dR6UmSESiaItZjn2yABjTjbH0KuusoEXWirwdhZ1A%3D%3D | GB | — | — | unknown |
980 | svchost.exe | OPTIONS | 302 | 85.222.137.35:80 | http://c.eu9.content.force.com/servlet | GB | — | — | unknown |
980 | svchost.exe | OPTIONS | 200 | 85.222.136.161:80 | http://eu9.salesforce.com/servlet | GB | — | — | unknown |
980 | svchost.exe | PROPFIND | 501 | 85.222.136.161:80 | http://eu9.salesforce.com/servlet | GB | — | — | unknown |
980 | svchost.exe | PROPFIND | 302 | 85.222.137.35:80 | http://c.eu9.content.force.com/servlet | GB | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2688 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2888 | iexplore.exe | 85.222.137.35:80 | c.eu9.content.force.com | Salesforce.com, Inc. | GB | unknown |
3632 | WINWORD.EXE | 85.222.136.163:80 | c.eu9.content.force.com | Salesforce.com, Inc. | GB | unknown |
980 | svchost.exe | 85.222.137.35:80 | c.eu9.content.force.com | Salesforce.com, Inc. | GB | unknown |
980 | svchost.exe | 85.222.136.161:80 | eu9.salesforce.com | Salesforce.com, Inc. | GB | unknown |
2380 | WINWORD.EXE | 85.222.137.35:80 | c.eu9.content.force.com | Salesforce.com, Inc. | GB | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
c.eu9.content.force.com |
| unknown |
eu9.salesforce.com |
| unknown |