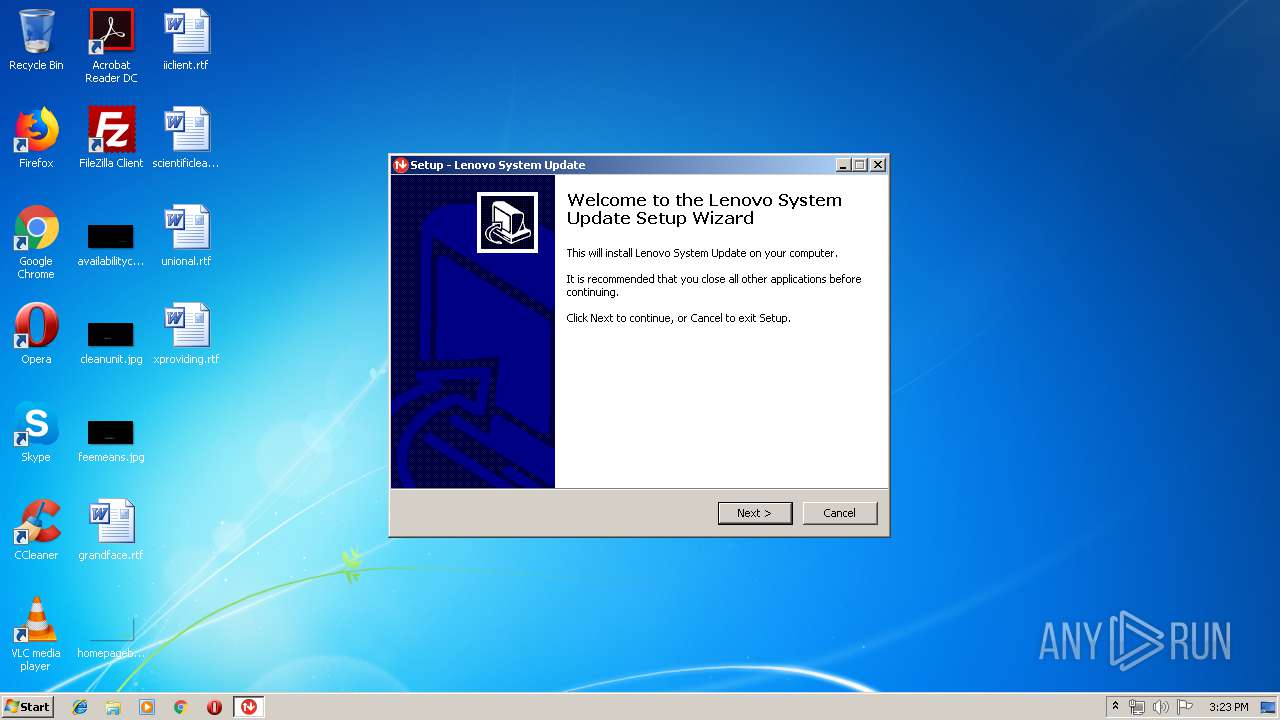
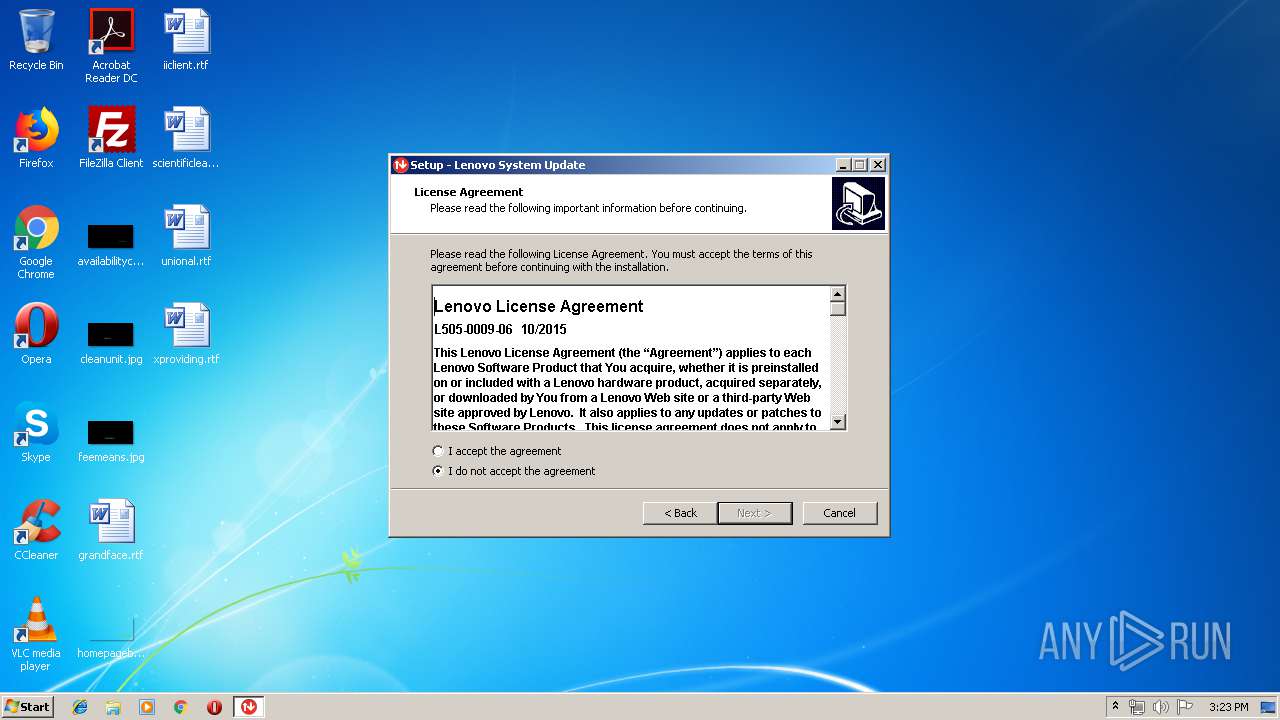
| File name: | systemupdate507-2019-05-24.exe |
| Full analysis: | https://app.any.run/tasks/1123246e-1adb-4f8f-94a5-ec917d7d3f37 |
| Verdict: | Malicious activity |
| Analysis date: | August 12, 2019, 14:23:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 7CEA5E559C865CA880AD1F028689B176 |
| SHA1: | 6D71A2D1018051CC7708F7D895FEFF8155FF99CE |
| SHA256: | 91F7D666EA076138E6188888DD898B9F72996432132244CCA8C2365788E1F93E |
| SSDEEP: | 196608:000yvn5aHD9VQZ26IJpozb7WhkQM/tl+fZad/KsTrBfOB:0LyfcH5VQenSXWhkz/KZad/lhmB |
MALICIOUS
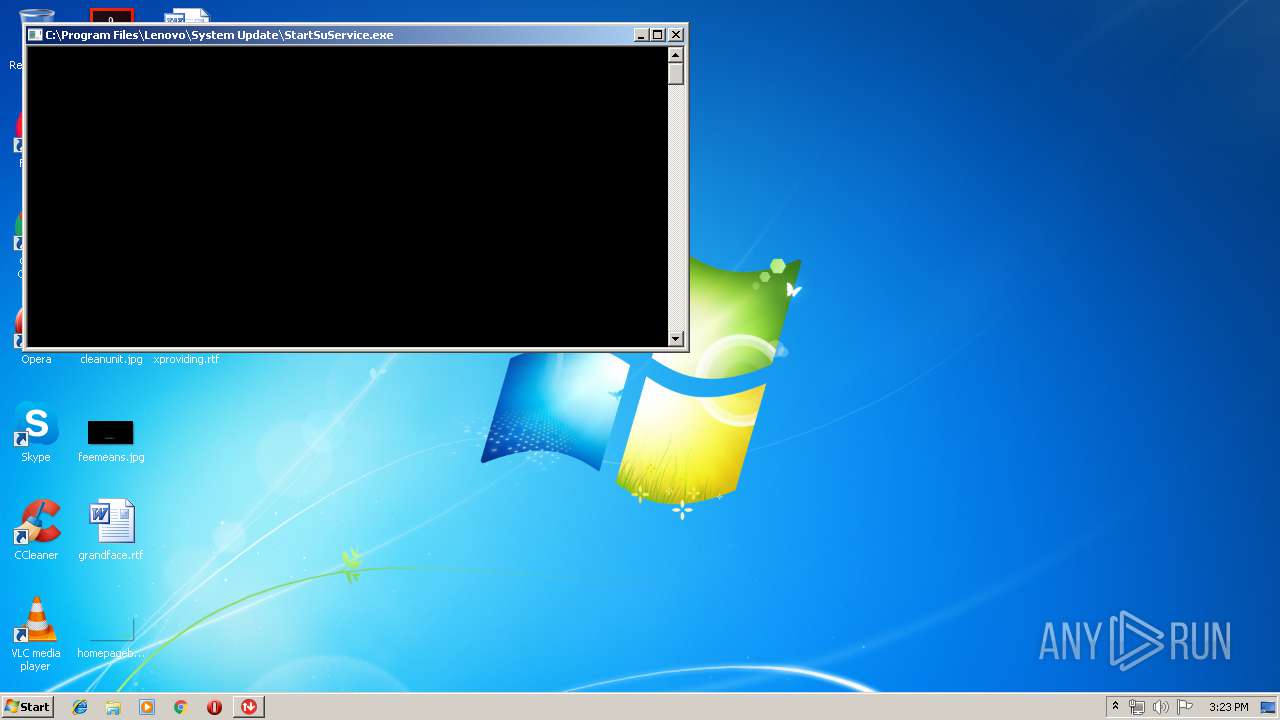
Application was dropped or rewritten from another process
- StartSuService.exe (PID: 2976)
- ConfigScheduledTask.exe (PID: 3316)
- SUService.exe (PID: 876)
- TVSU2DirAllowWriting.exe (PID: 3128)
- uncsetting.exe (PID: 1128)
- susetsched.exe (PID: 1672)
- ConfigService.exe (PID: 2152)
- tvsu.exe (PID: 1412)
- TvsuCommandLauncher.exe (PID: 3128)
- ConfigService.exe (PID: 3900)
- uncserver.exe (PID: 804)
- TvsuCommandLauncher.exe (PID: 1748)
- Tvsukernel.exe (PID: 2052)
- uncsetting.exe (PID: 3676)
- UACSdk.exe (PID: 2092)
- ConfigService.exe (PID: 796)
- ia.exe (PID: 1860)
- ia.exe (PID: 2452)
- ConfigService.exe (PID: 2172)
Loads dropped or rewritten executable
- SUService.exe (PID: 876)
- InstallUtil.exe (PID: 3268)
- ConfigScheduledTask.exe (PID: 3316)
- TvsuCommandLauncher.exe (PID: 3128)
- TvsuCommandLauncher.exe (PID: 1748)
- uncserver.exe (PID: 804)
- Tvsukernel.exe (PID: 2052)
- ia.exe (PID: 1860)
- ia.exe (PID: 2452)
Loads the Task Scheduler COM API
- susetsched.exe (PID: 1672)
- schtasks.exe (PID: 2884)
- schtasks.exe (PID: 3976)
Uses Task Scheduler to run other applications
- ConfigScheduledTask.exe (PID: 3316)
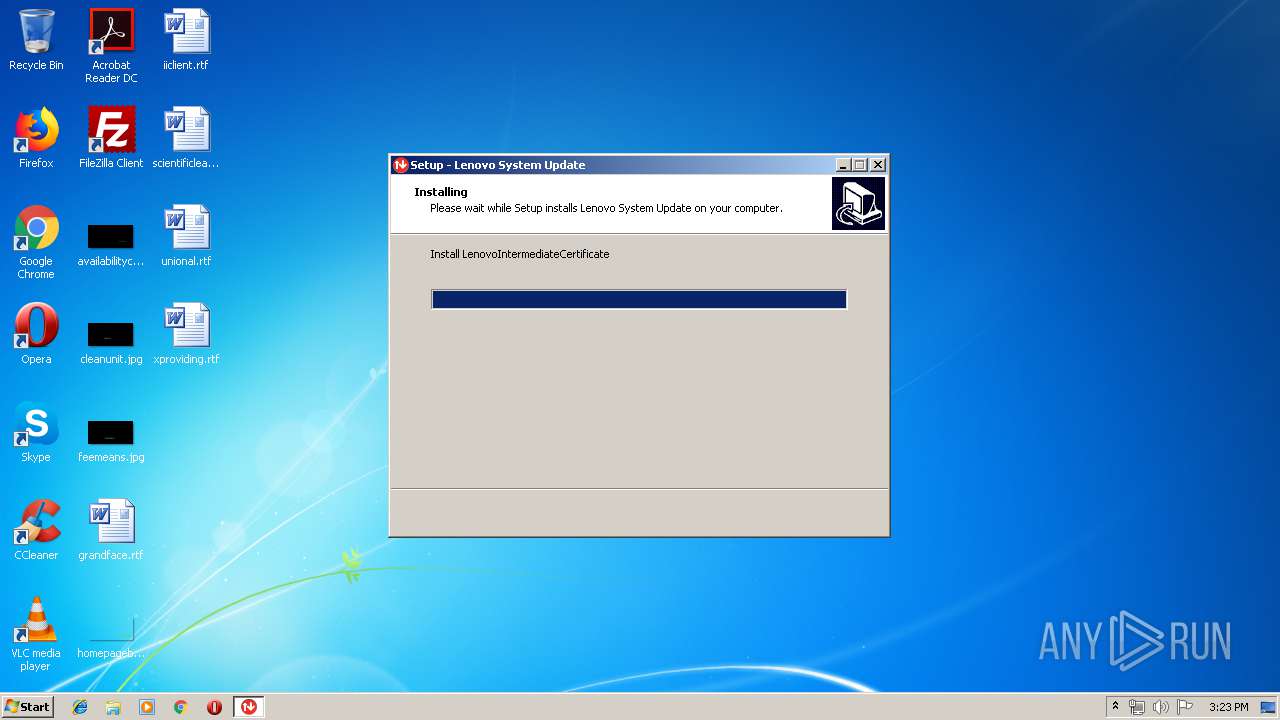
Changes settings of System certificates
- certutil.exe (PID: 3956)
- SUService.exe (PID: 876)
- certutil.exe (PID: 3672)
SUSPICIOUS
Reads Windows owner or organization settings
- systemupdate507-2019-05-24.tmp (PID: 2352)
Reads the Windows organization settings
- systemupdate507-2019-05-24.tmp (PID: 2352)
Application launched itself
- cmd.exe (PID: 3640)
Executable content was dropped or overwritten
- systemupdate507-2019-05-24.exe (PID: 724)
- systemupdate507-2019-05-24.exe (PID: 3984)
- systemupdate507-2019-05-24.tmp (PID: 2352)
Reads Environment values
- systemupdate507-2019-05-24.tmp (PID: 2352)
- Tvsukernel.exe (PID: 2052)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 3640)
- systemupdate507-2019-05-24.tmp (PID: 2352)
Creates files in the Windows directory
- systemupdate507-2019-05-24.tmp (PID: 2352)
- InstallUtil.exe (PID: 3268)
- certutil.exe (PID: 3672)
- certutil.exe (PID: 3956)
- SUService.exe (PID: 876)
- ia.exe (PID: 1860)
Creates files in the program directory
- StartSuService.exe (PID: 2976)
- InstallUtil.exe (PID: 3268)
- SUService.exe (PID: 876)
- ConfigScheduledTask.exe (PID: 3316)
- Tvsukernel.exe (PID: 2052)
- ia.exe (PID: 1860)
- ia.exe (PID: 2452)
Creates or modifies windows services
- InstallUtil.exe (PID: 3268)
Modifies the open verb of a shell class
- systemupdate507-2019-05-24.tmp (PID: 2352)
Executed as Windows Service
- SUService.exe (PID: 876)
Removes files from Windows directory
- certutil.exe (PID: 3672)
- certutil.exe (PID: 3956)
- systemupdate507-2019-05-24.tmp (PID: 2352)
- SUService.exe (PID: 876)
Uses ICACLS.EXE to modify access control list
- SUService.exe (PID: 876)
- ConfigScheduledTask.exe (PID: 3316)
- TvsuCommandLauncher.exe (PID: 3128)
- TvsuCommandLauncher.exe (PID: 1748)
- Tvsukernel.exe (PID: 2052)
Reads Internet Cache Settings
- Tvsukernel.exe (PID: 2052)
Checks supported languages
- Tvsukernel.exe (PID: 2052)
Searches for installed software
- ia.exe (PID: 2452)
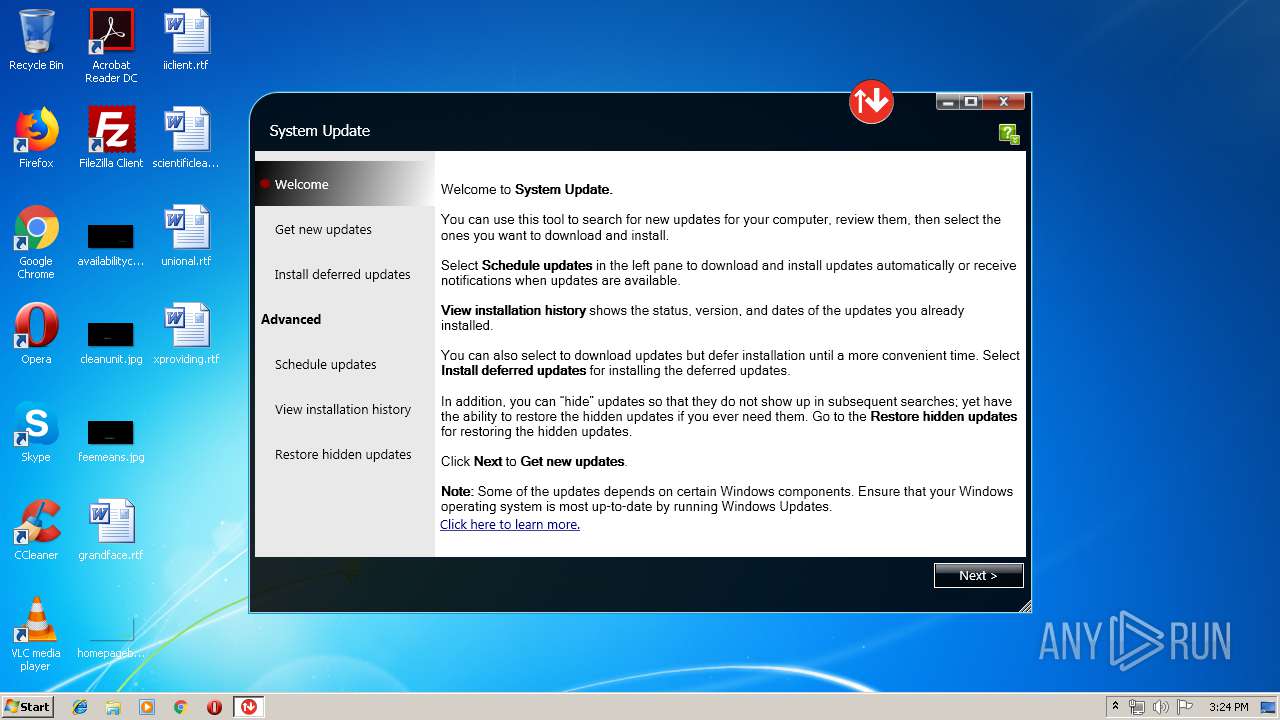
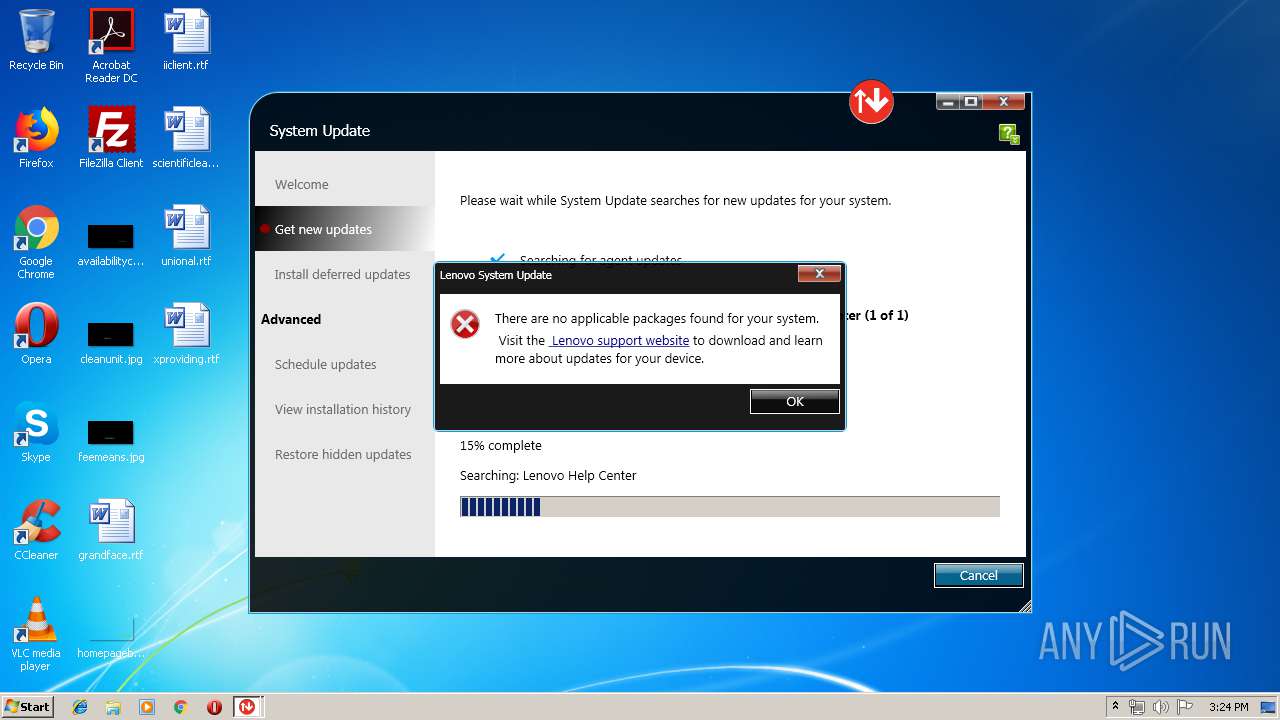
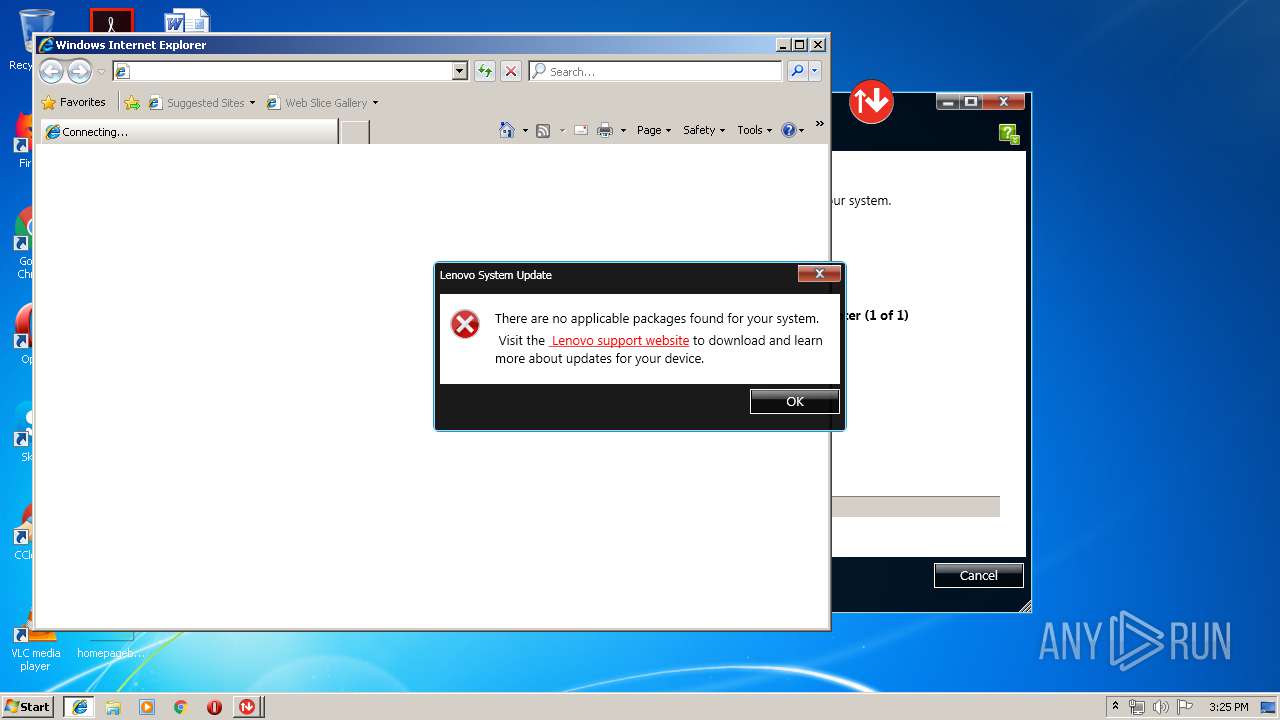
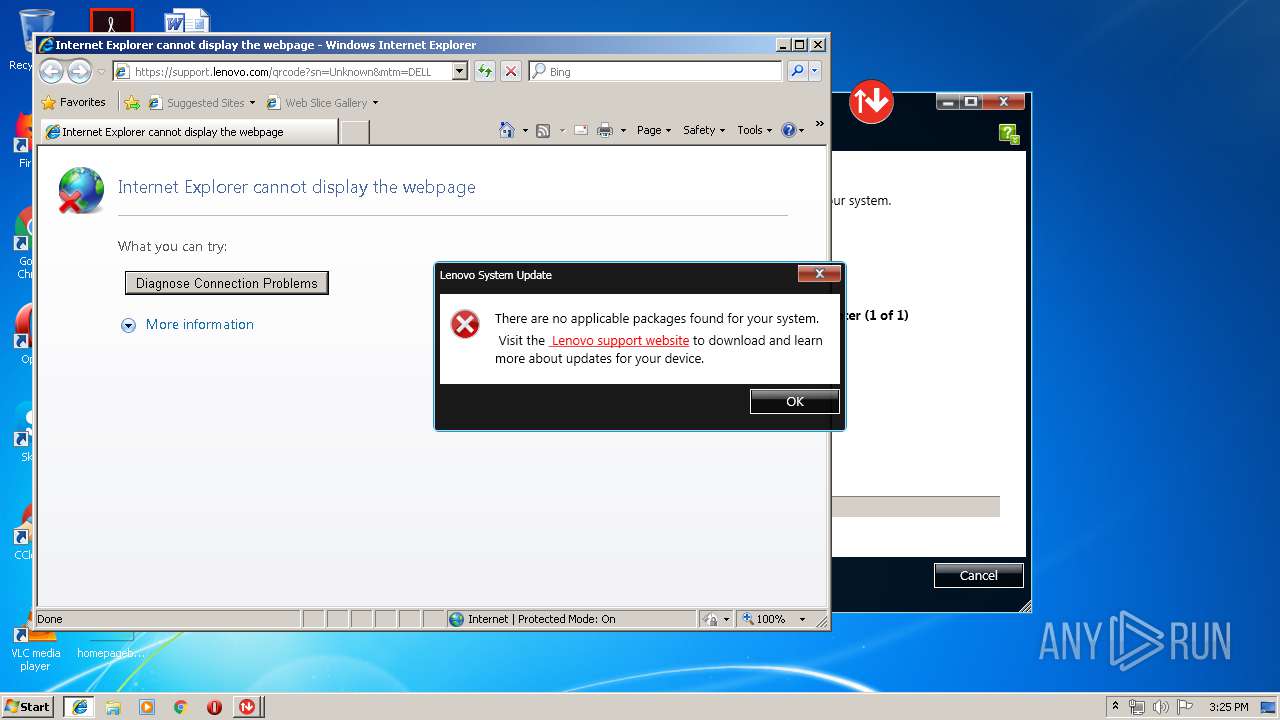
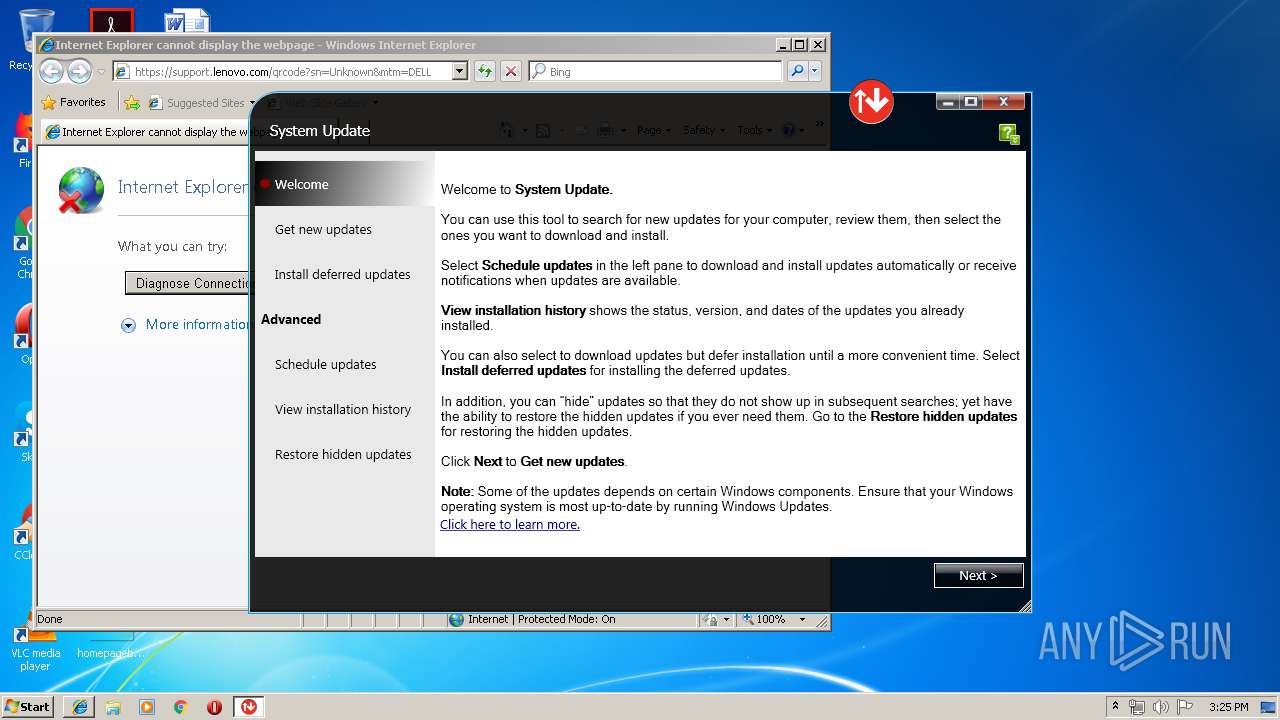
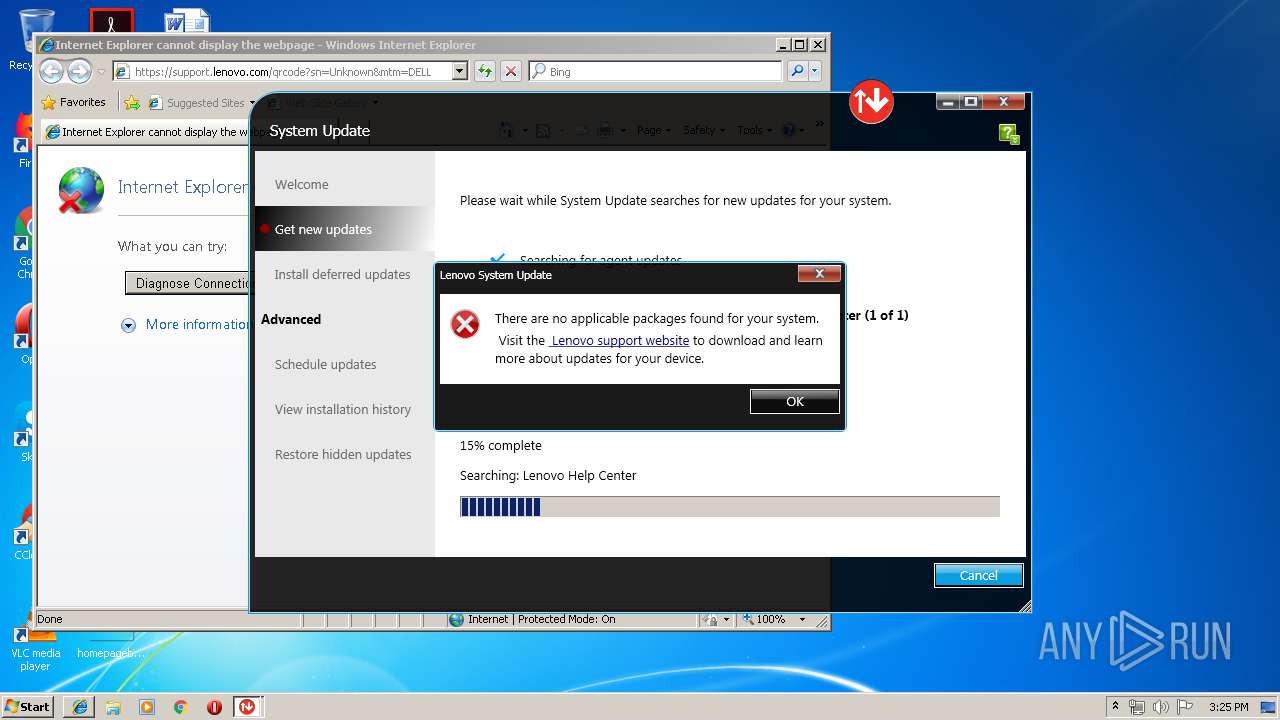
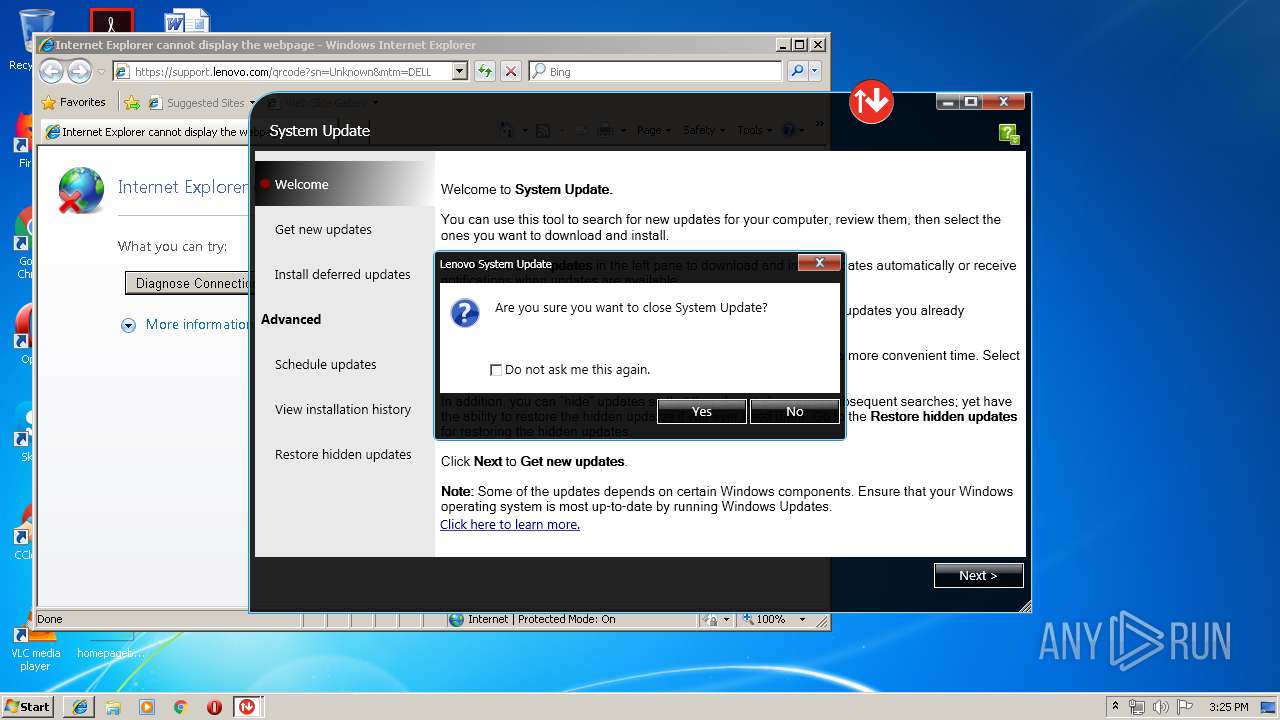
Starts Internet Explorer
- uncserver.exe (PID: 804)
Creates files in the user directory
- ia.exe (PID: 2452)
Uses NETSH.EXE for network configuration
- uncsetting.exe (PID: 1128)
INFO
Application was dropped or rewritten from another process
- systemupdate507-2019-05-24.tmp (PID: 4092)
- systemupdate507-2019-05-24.tmp (PID: 2352)
Creates a software uninstall entry
- systemupdate507-2019-05-24.tmp (PID: 2352)
Creates files in the program directory
- systemupdate507-2019-05-24.tmp (PID: 2352)
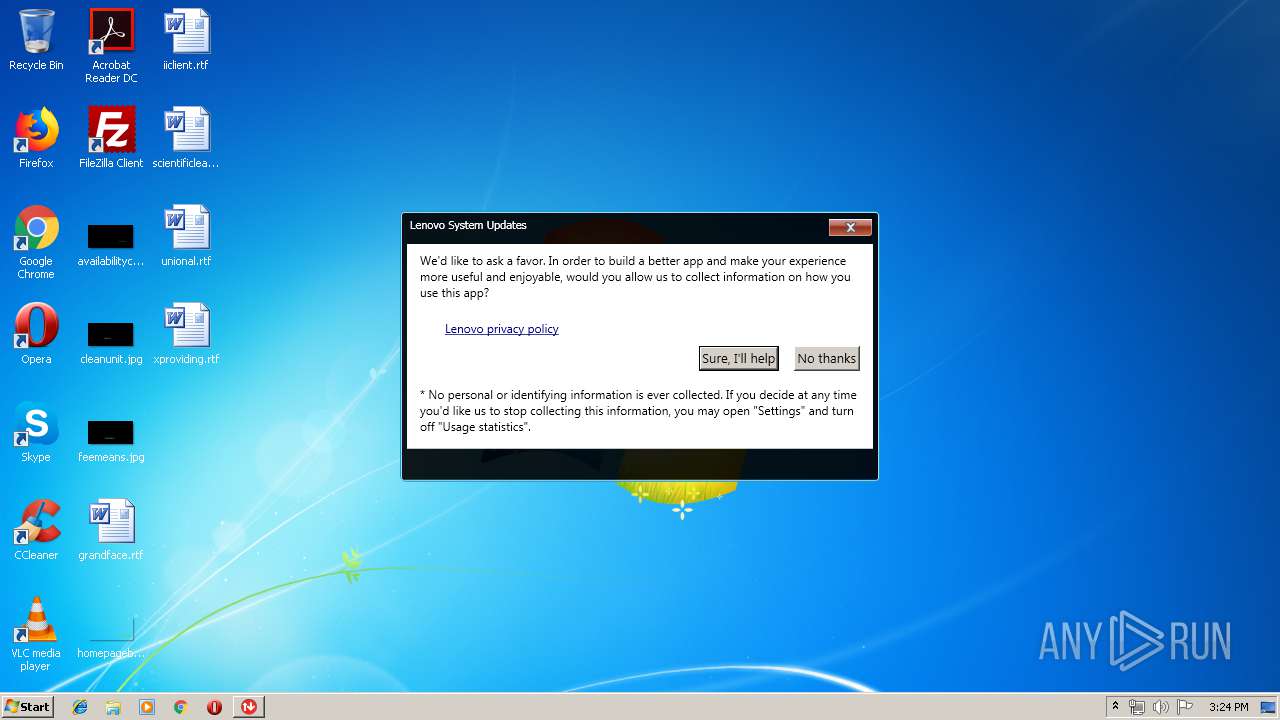
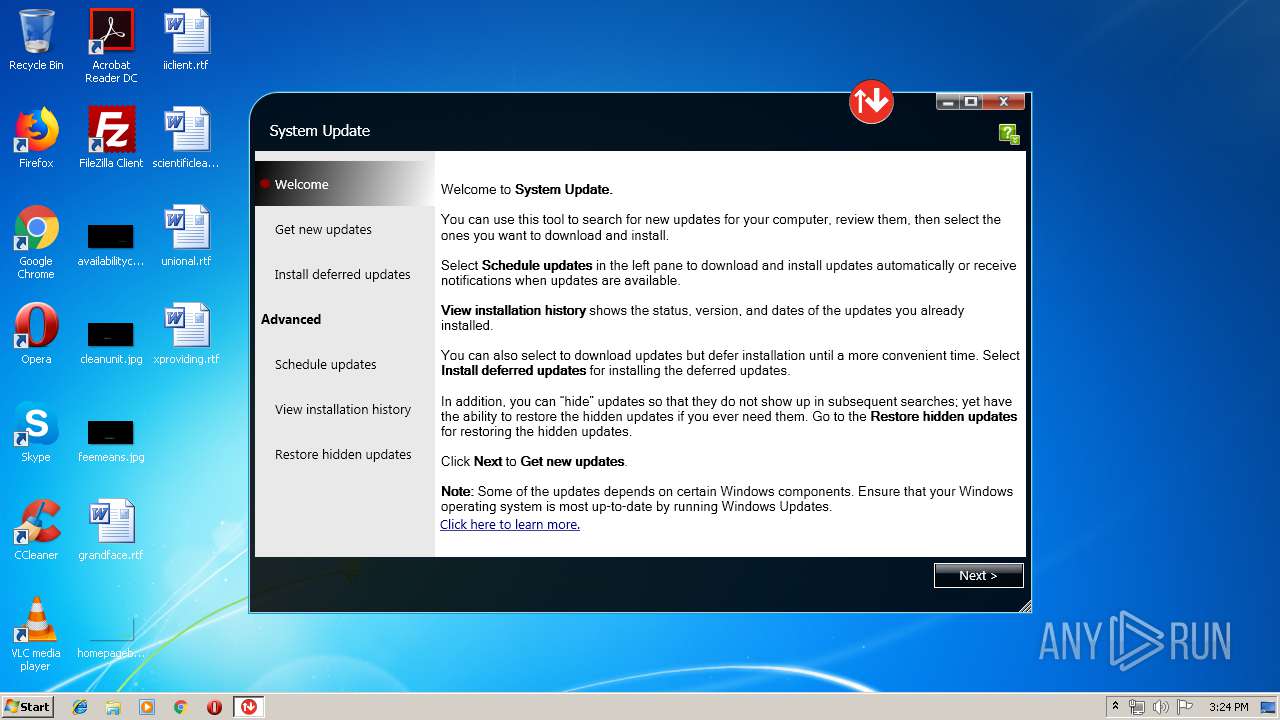
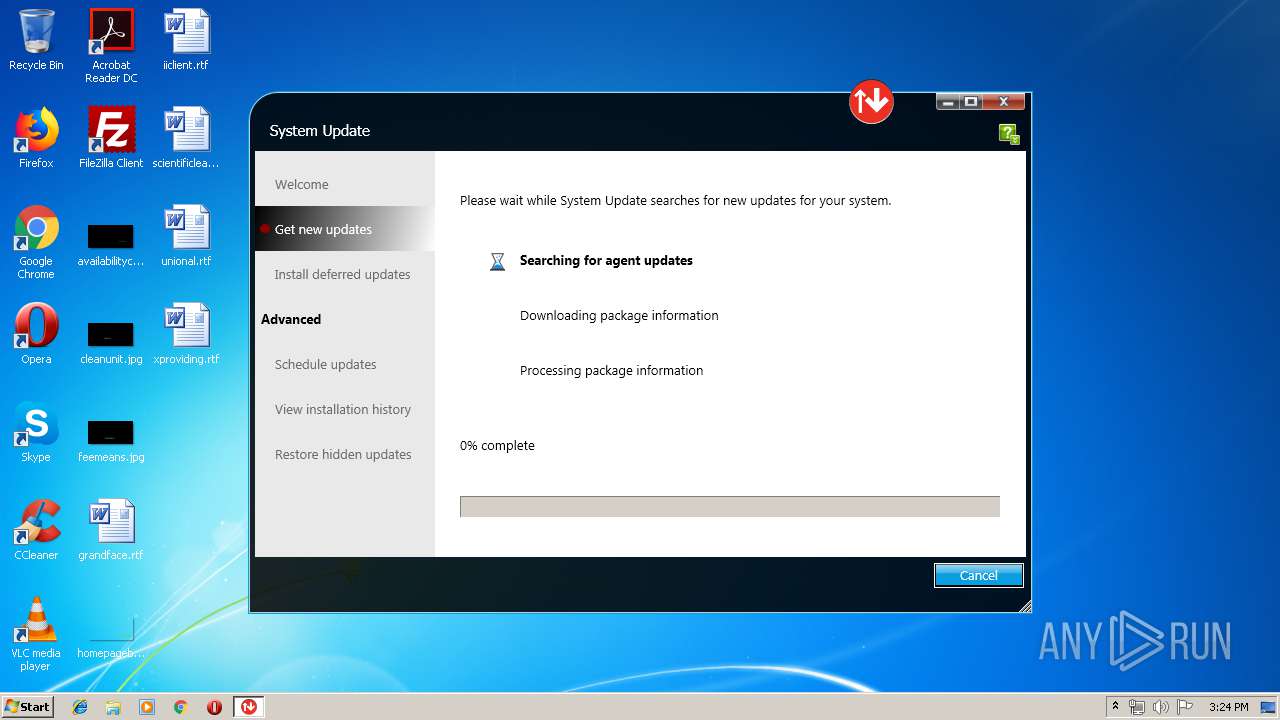
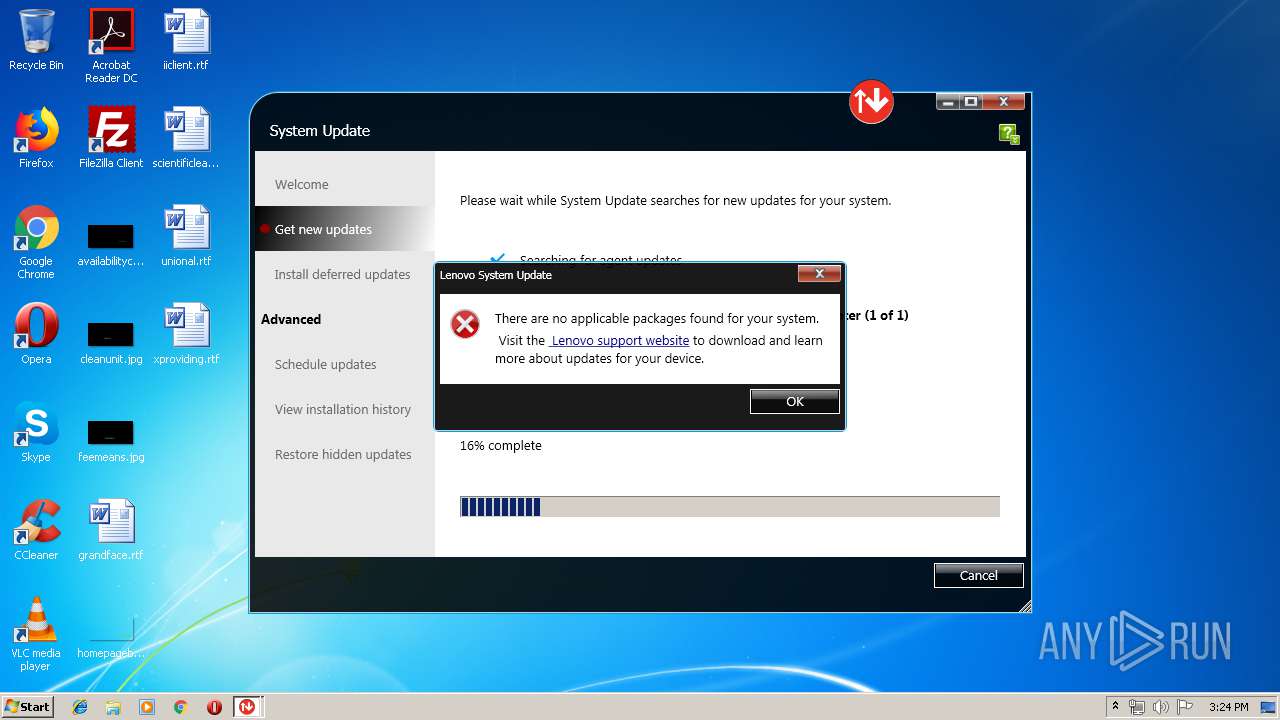
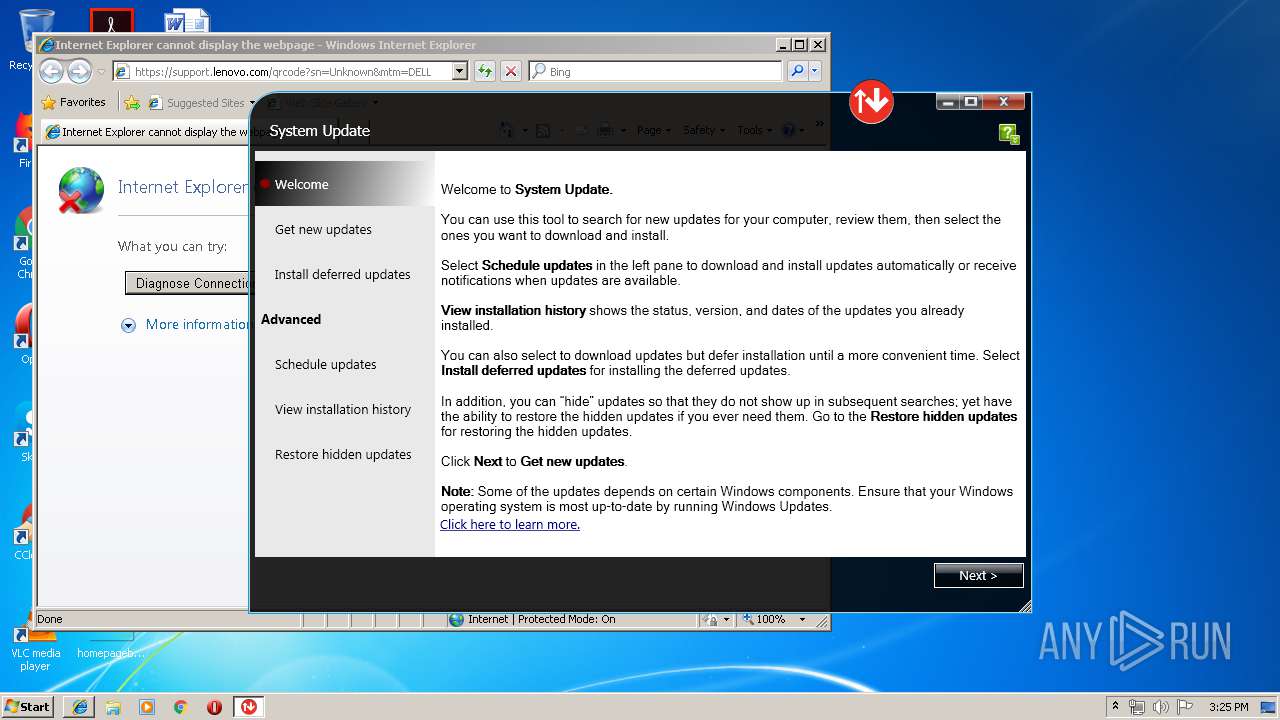
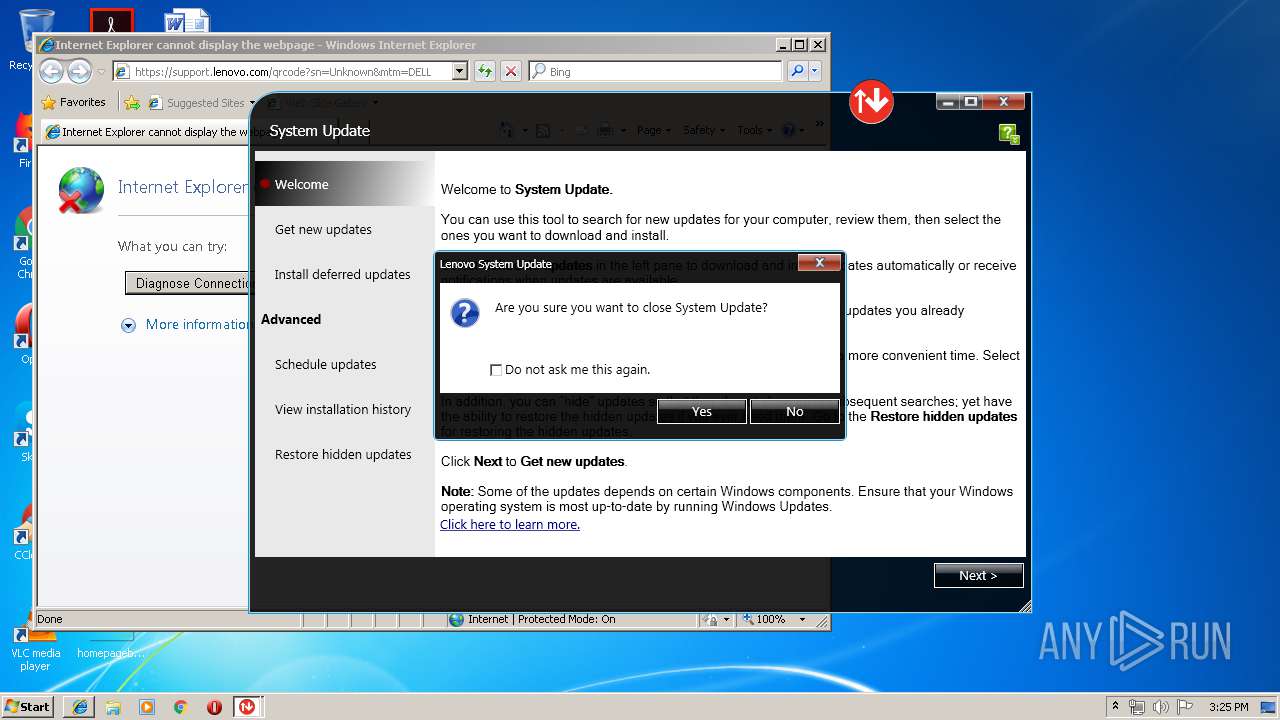
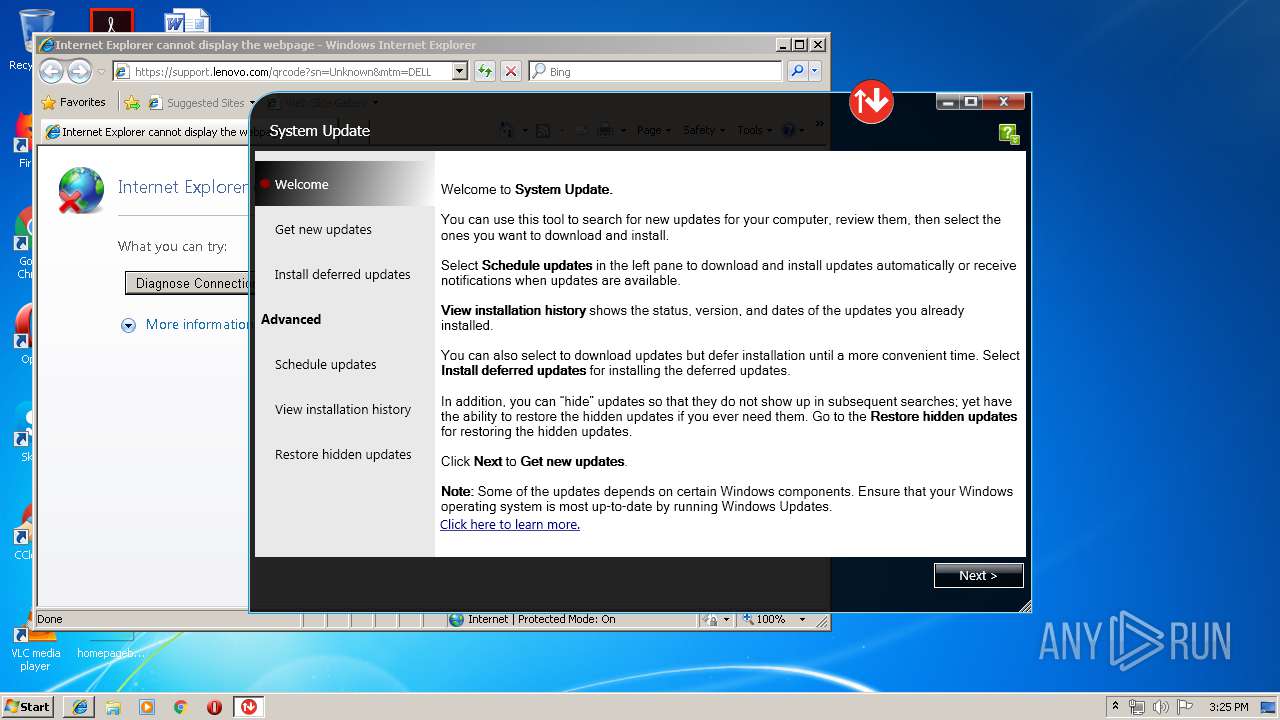
Manual execution by user
- tvsu.exe (PID: 1412)
Reads settings of System Certificates
- SUService.exe (PID: 876)
- Tvsukernel.exe (PID: 2052)
Dropped object may contain Bitcoin addresses
- ia.exe (PID: 2452)
Reads Internet Cache Settings
- iexplore.exe (PID: 2416)
Changes internet zones settings
- iexplore.exe (PID: 1252)
Reads internet explorer settings
- iexplore.exe (PID: 2416)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (57.2) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (18.2) |
| .exe | | | Win16/32 Executable Delphi generic (8.3) |
| .exe | | | Generic Win/DOS Executable (8) |
| .exe | | | DOS Executable Generic (8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:06 16:39:04+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 66560 |
| InitializedDataSize: | 283648 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x117dc |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.7.84.0 |
| ProductVersionNumber: | 5.7.84.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Lenovo |
| FileDescription: | Lenovo System Update Setup |
| FileVersion: | 5.07.0084 |
| LegalCopyright: | |
| ProductName: | Lenovo System Update |
| ProductVersion: | 5.07.0084 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Apr-2016 14:39:04 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Lenovo |
| FileDescription: | Lenovo System Update Setup |
| FileVersion: | 5.07.0084 |
| LegalCopyright: | - |
| ProductName: | Lenovo System Update |
| ProductVersion: | 5.07.0084 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 06-Apr-2016 14:39:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F244 | 0x0000F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.37521 |
.itext | 0x00011000 | 0x00000F64 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.7322 |
.data | 0x00012000 | 0x00000C88 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.29672 |
.bss | 0x00013000 | 0x000056BC | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00019000 | 0x00000E04 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.59781 |
.tls | 0x0001A000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001C000 | 0x00043384 | 0x00043400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.0915 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.30618 | 304 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 2.47581 | 176 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 7.73695 | 4201 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 2.79096 | 1640 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 3.20638 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 3.31916 | 488 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 3.25564 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 7.93819 | 11287 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 4.47867 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
103
Monitored processes
44
Malicious processes
14
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 724 | "C:\Users\admin\AppData\Local\Temp\systemupdate507-2019-05-24.exe" | C:\Users\admin\AppData\Local\Temp\systemupdate507-2019-05-24.exe | explorer.exe | ||||||||||||
User: admin Company: Lenovo Integrity Level: MEDIUM Description: Lenovo System Update Setup Exit code: 0 Version: 5.07.0084 Modules
| |||||||||||||||
| 796 | "C:\Program Files\Lenovo\System Update\ConfigService.exe" settrigger | C:\Program Files\Lenovo\System Update\ConfigService.exe | — | Tvsukernel.exe | |||||||||||
User: admin Integrity Level: HIGH Description: ConfigService Application Exit code: 0 Version: 5, 7, 0, 84 Modules
| |||||||||||||||
| 804 | "C:\Program Files\Lenovo\System Update\uncserver.exe" | C:\Program Files\Lenovo\System Update\uncserver.exe | — | tvsu.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: UNCServer Exit code: 0 Version: 5.7.0.84 Modules
| |||||||||||||||
| 876 | "C:\Program Files\Lenovo\System Update\SUService.exe" | C:\Program Files\Lenovo\System Update\SUService.exe | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Description: Lenovo System Update Service Exit code: 0 Version: 5.7.0.84 Modules
| |||||||||||||||
| 1052 | "C:\Windows\system32\netsh.exe" advfirewall firewall add rule name="TvsuUNCServer" dir=out action=allow program="C:\Program Files\Lenovo\System Update\uncserver.exe" enable=yes profile=any protocol=UDP | C:\Windows\system32\netsh.exe | — | uncsetting.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1128 | "C:\Program Files\Lenovo\System Update\uncsetting.exe" | C:\Program Files\Lenovo\System Update\uncsetting.exe | — | SUService.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Description: uncsetting Exit code: 0 Version: 5.7.0.84 Modules
| |||||||||||||||
| 1252 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | uncserver.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1412 | "C:\Program Files\Lenovo\System Update\tvsu.exe" | C:\Program Files\Lenovo\System Update\tvsu.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Lenovo System Update Exit code: 0 Version: 5, 7, 0, 84 Modules
| |||||||||||||||
| 1672 | "C:\Program Files\Lenovo\System Update\susetsched.exe" create | C:\Program Files\Lenovo\System Update\susetsched.exe | — | SUService.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Description: susetsched Application Exit code: 0 Version: 5, 7, 0, 84 Modules
| |||||||||||||||
| 1748 | "C:\Program Files\Lenovo\System Update\TvsuCommandLauncher.exe" 1 | C:\Program Files\Lenovo\System Update\TvsuCommandLauncher.exe | — | tvsu.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Lenovo System Update TvsuCommandLauncher Exit code: 2147483648 Version: 5.7.0.84 Modules
| |||||||||||||||
Total events
2 124
Read events
1 731
Write events
388
Delete events
5
Modification events
| (PID) Process: | (2352) systemupdate507-2019-05-24.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 300900003CAC41801951D501 | |||
| (PID) Process: | (2352) systemupdate507-2019-05-24.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: A9C7C7AB8D491923634233A36A9CD01357013E355372657D0FD353E4509E178B | |||
| (PID) Process: | (2352) systemupdate507-2019-05-24.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2352) systemupdate507-2019-05-24.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: CB53041D445E5AE67F99FEFDD6ABAC0163B2E2CC9C9ECF629C3C57751DABC148 | |||
| (PID) Process: | (2352) systemupdate507-2019-05-24.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\App Paths\tvsu.exe |
| Operation: | write | Name: | |
Value: C:\Program Files\Lenovo\System Update\tvsu.exe | |||
| (PID) Process: | (2352) systemupdate507-2019-05-24.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\App Paths\tvsu.exe |
| Operation: | write | Name: | Path |
Value: C:\Program Files\Lenovo\System Update\ | |||
| (PID) Process: | (2352) systemupdate507-2019-05-24.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\App Paths\tvsu_install.exe |
| Operation: | write | Name: | |
Value: C:\swtools\readyapps\appinstall.exe -tvsu | |||
| (PID) Process: | (2352) systemupdate507-2019-05-24.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\App Paths\tvsu_install.exe |
| Operation: | write | Name: | Path |
Value: C:\swtools\readyapps\tvsu | |||
| (PID) Process: | (2352) systemupdate507-2019-05-24.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\App Paths\tvsu_install.exe |
| Operation: | write | Name: | Version |
Value: 5.07 | |||
| (PID) Process: | (2352) systemupdate507-2019-05-24.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\App Paths\tvsu_install.exe |
| Operation: | write | Name: | W7_CmdInst |
Value: setuptvsu.exe | |||
Executable files
102
Suspicious files
20
Text files
210
Unknown types
31
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2352 | systemupdate507-2019-05-24.tmp | C:\Program Files\Lenovo\System Update\is-850KM.tmp | — | |
MD5:— | SHA256:— | |||
| 2352 | systemupdate507-2019-05-24.tmp | C:\Program Files\Lenovo\System Update\is-0UETD.tmp | — | |
MD5:— | SHA256:— | |||
| 2352 | systemupdate507-2019-05-24.tmp | C:\Program Files\Lenovo\System Update\is-09997.tmp | — | |
MD5:— | SHA256:— | |||
| 2352 | systemupdate507-2019-05-24.tmp | C:\Program Files\Lenovo\System Update\is-51K5G.tmp | — | |
MD5:— | SHA256:— | |||
| 2352 | systemupdate507-2019-05-24.tmp | C:\Program Files\Lenovo\System Update\is-1FLP4.tmp | — | |
MD5:— | SHA256:— | |||
| 2352 | systemupdate507-2019-05-24.tmp | C:\Program Files\Lenovo\System Update\is-S9TQK.tmp | — | |
MD5:— | SHA256:— | |||
| 2352 | systemupdate507-2019-05-24.tmp | C:\Program Files\Lenovo\System Update\is-KODUA.tmp | — | |
MD5:— | SHA256:— | |||
| 2352 | systemupdate507-2019-05-24.tmp | C:\Program Files\Lenovo\System Update\is-ITDU1.tmp | — | |
MD5:— | SHA256:— | |||
| 2352 | systemupdate507-2019-05-24.tmp | C:\Program Files\Lenovo\System Update\is-DQ2UR.tmp | — | |
MD5:— | SHA256:— | |||
| 2352 | systemupdate507-2019-05-24.tmp | C:\Program Files\Lenovo\System Update\is-45TE6.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
15
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
876 | SUService.exe | GET | 200 | 23.37.43.27:80 | http://s.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ%2FYHKj6JjF6UBieQioTYpFsuEriQQUtnf6aUhHn1MS1cLqBzJ2B9GXBxkCEHwbNTVK59t050FfEWnKa6g%3D | NL | der | 1.68 Kb | shared |
876 | SUService.exe | GET | 200 | 23.37.43.27:80 | http://ts-ocsp.ws.symantec.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQd11mpyHEqFCSocj4SCu93CBydHAQUr2PWyqNOhXLgp7xB8ymiOH%2BAdWICEHvU5a%2B6zAc%2FoQEjBCJBTRI%3D | NL | der | 1.55 Kb | whitelisted |
2052 | Tvsukernel.exe | GET | 200 | 23.37.43.27:80 | http://ts-ocsp.ws.symantec.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQd11mpyHEqFCSocj4SCu93CBydHAQUr2PWyqNOhXLgp7xB8ymiOH%2BAdWICEHvU5a%2B6zAc%2FoQEjBCJBTRI%3D | NL | der | 1.55 Kb | whitelisted |
876 | SUService.exe | GET | 200 | 23.37.43.27:80 | http://rb.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTDRSYViRCZTxmZjLENmnwVjLly9QQU1MAGIknrOUvdk%2BJcobhHdglyA1gCEGZYxb%2BG6ZEk%2BZdIsKegFUw%3D | NL | der | 1.58 Kb | whitelisted |
2052 | Tvsukernel.exe | GET | 200 | 23.37.43.27:80 | http://s.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ%2FYHKj6JjF6UBieQioTYpFsuEriQQUtnf6aUhHn1MS1cLqBzJ2B9GXBxkCEHsFsdRJaFFE98mJ0pwZnRI%3D | NL | der | 1.68 Kb | shared |
2052 | Tvsukernel.exe | GET | 200 | 23.37.43.27:80 | http://rb.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTDRSYViRCZTxmZjLENmnwVjLly9QQU1MAGIknrOUvdk%2BJcobhHdglyA1gCEGZYxb%2BG6ZEk%2BZdIsKegFUw%3D | NL | der | 1.58 Kb | whitelisted |
876 | SUService.exe | GET | 200 | 23.37.43.27:80 | http://s.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ%2FYHKj6JjF6UBieQioTYpFsuEriQQUtnf6aUhHn1MS1cLqBzJ2B9GXBxkCEHsFsdRJaFFE98mJ0pwZnRI%3D | NL | der | 1.68 Kb | shared |
876 | SUService.exe | GET | 200 | 93.184.220.29:80 | http://rb.symcb.com/rb.crl | US | der | 7.45 Kb | whitelisted |
2052 | Tvsukernel.exe | GET | 200 | 23.37.43.27:80 | http://s.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ%2FYHKj6JjF6UBieQioTYpFsuEriQQUtnf6aUhHn1MS1cLqBzJ2B9GXBxkCEHwbNTVK59t050FfEWnKa6g%3D | NL | der | 1.68 Kb | shared |
1252 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
876 | SUService.exe | 23.37.43.27:80 | s.symcd.com | Akamai Technologies, Inc. | NL | whitelisted |
876 | SUService.exe | 93.184.220.29:80 | rb.symcb.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
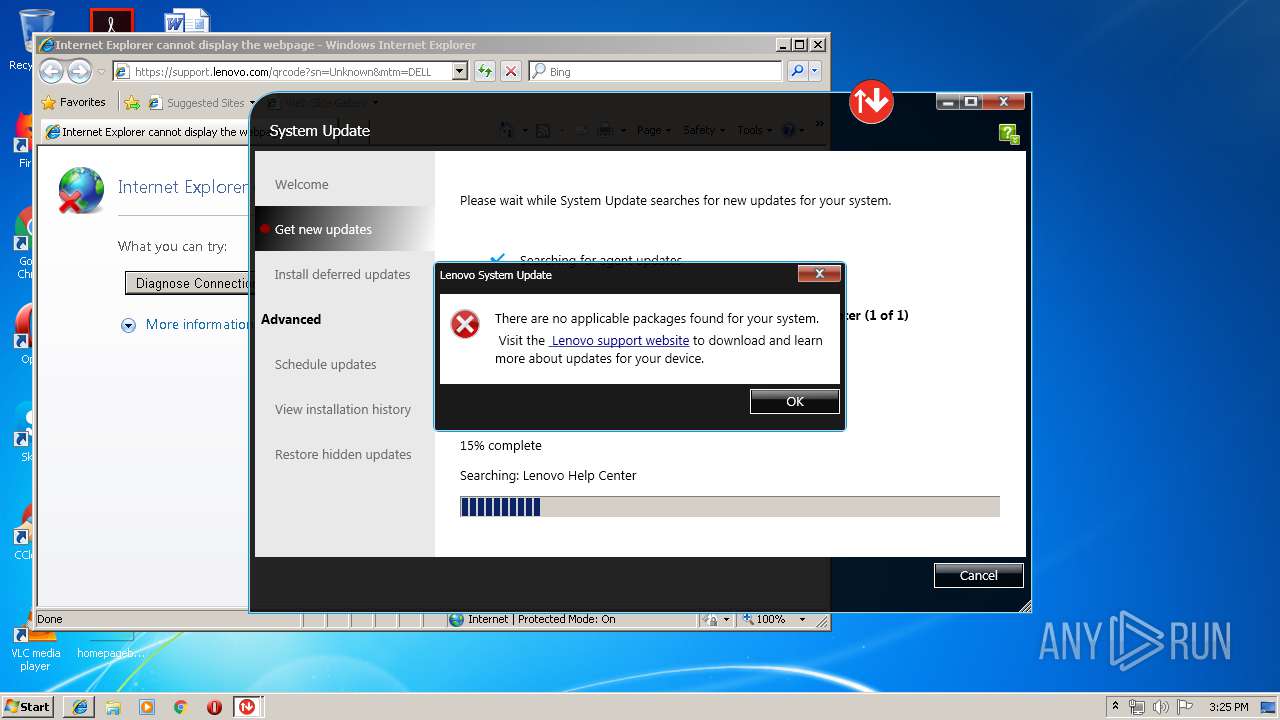
2052 | Tvsukernel.exe | 2.18.232.126:443 | download.lenovo.com | Akamai International B.V. | — | whitelisted |
2052 | Tvsukernel.exe | 38.106.231.204:443 | chifsr.lenovomm.com | Cogent Communications | US | unknown |
— | — | 104.108.51.17:443 | support.lenovo.com | Akamai Technologies, Inc. | NL | whitelisted |
1252 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2052 | Tvsukernel.exe | 23.37.43.27:80 | s.symcd.com | Akamai Technologies, Inc. | NL | whitelisted |
2416 | iexplore.exe | 104.108.51.17:443 | support.lenovo.com | Akamai Technologies, Inc. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
s.symcd.com |
| shared |
rb.symcd.com |
| whitelisted |
rb.symcb.com |
| whitelisted |
ts-ocsp.ws.symantec.com |
| whitelisted |
download.lenovo.com |
| suspicious |
filedownload.lenovo.com |
| suspicious |
chifsr.lenovomm.com |
| whitelisted |
www.bing.com |
| whitelisted |
support.lenovo.com |
| suspicious |