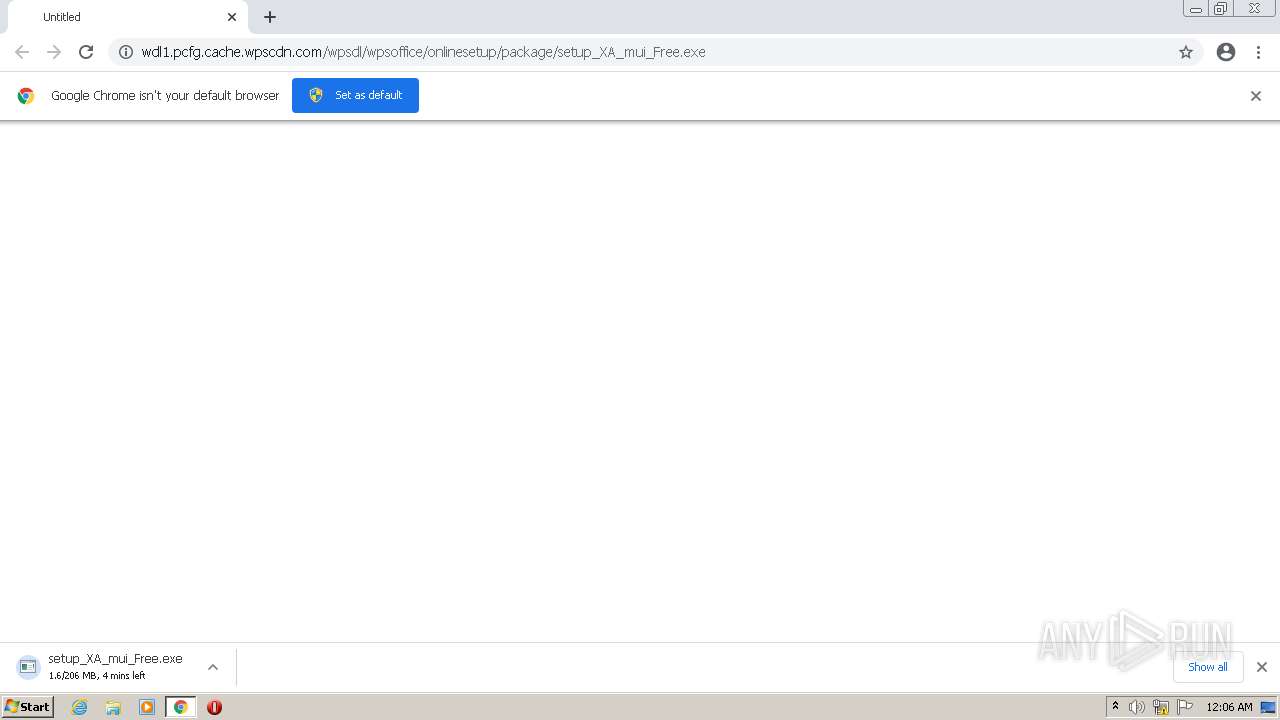
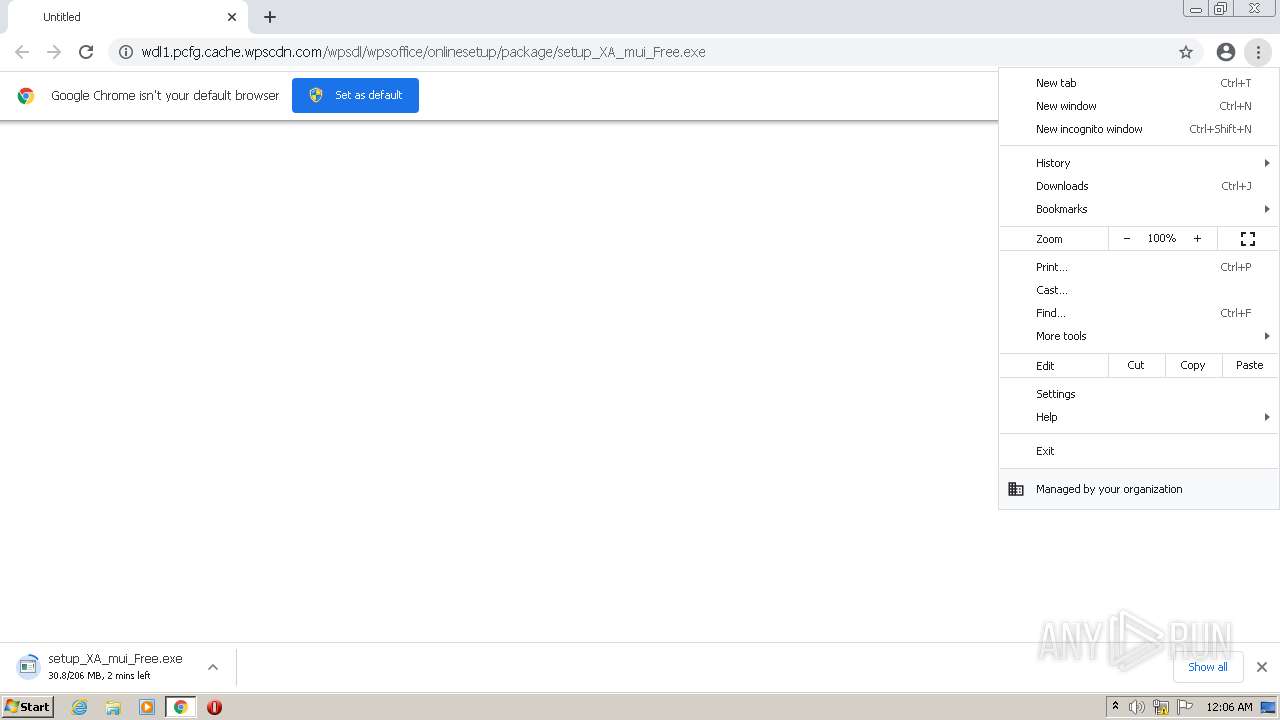
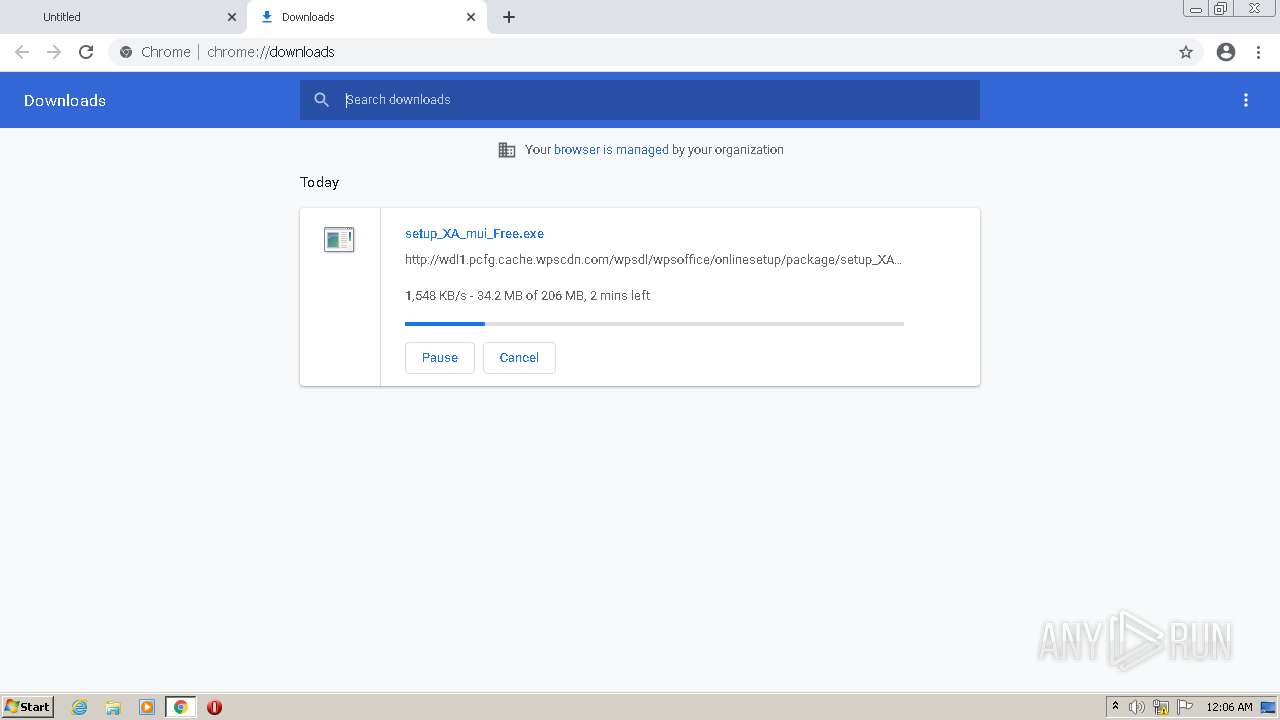
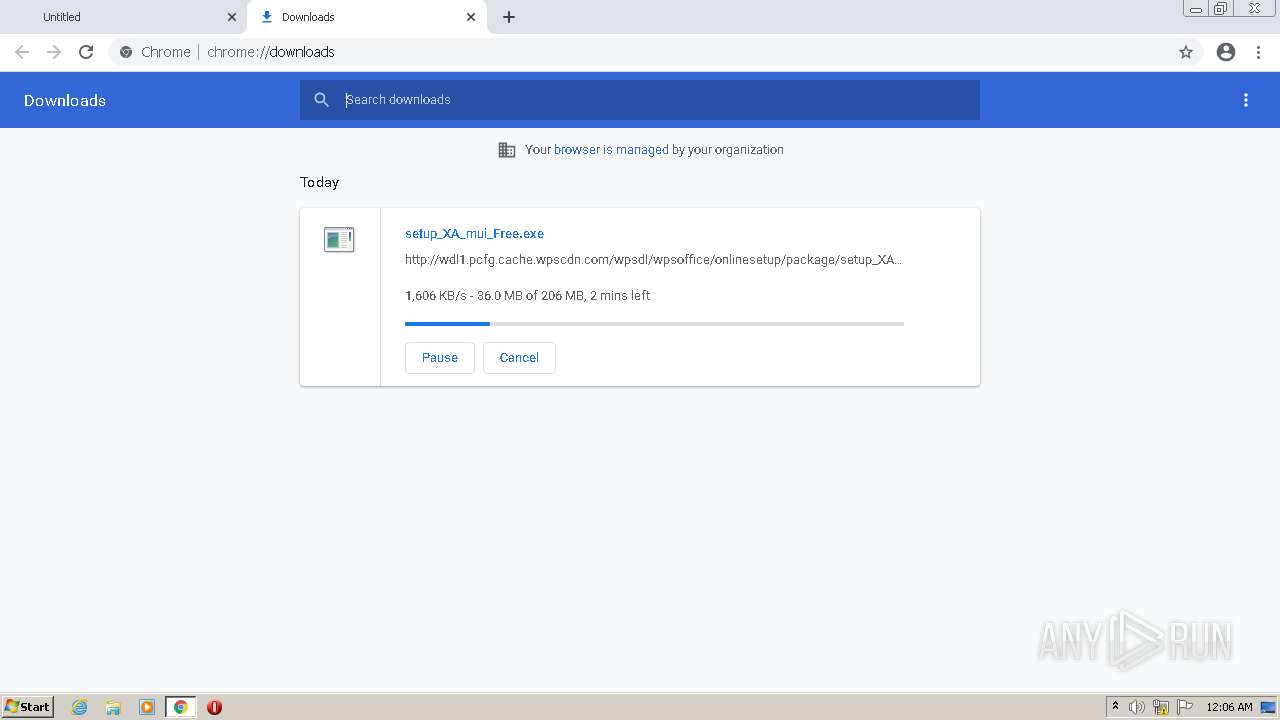
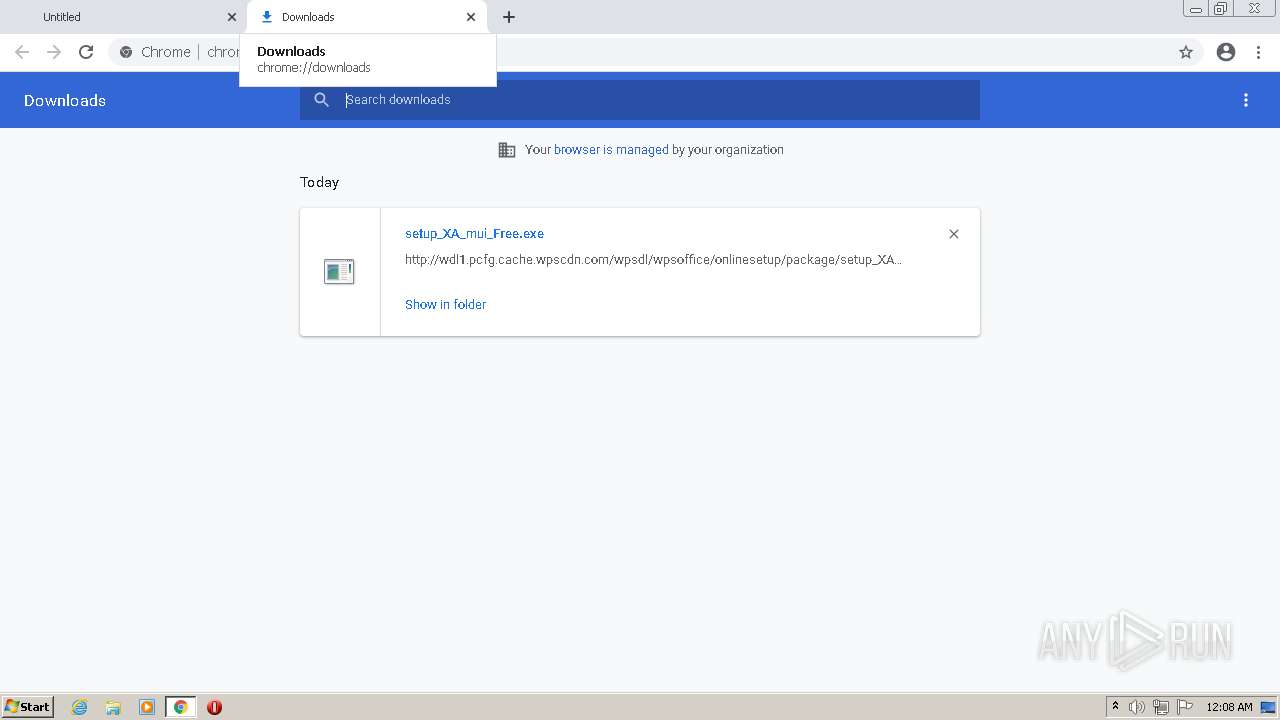
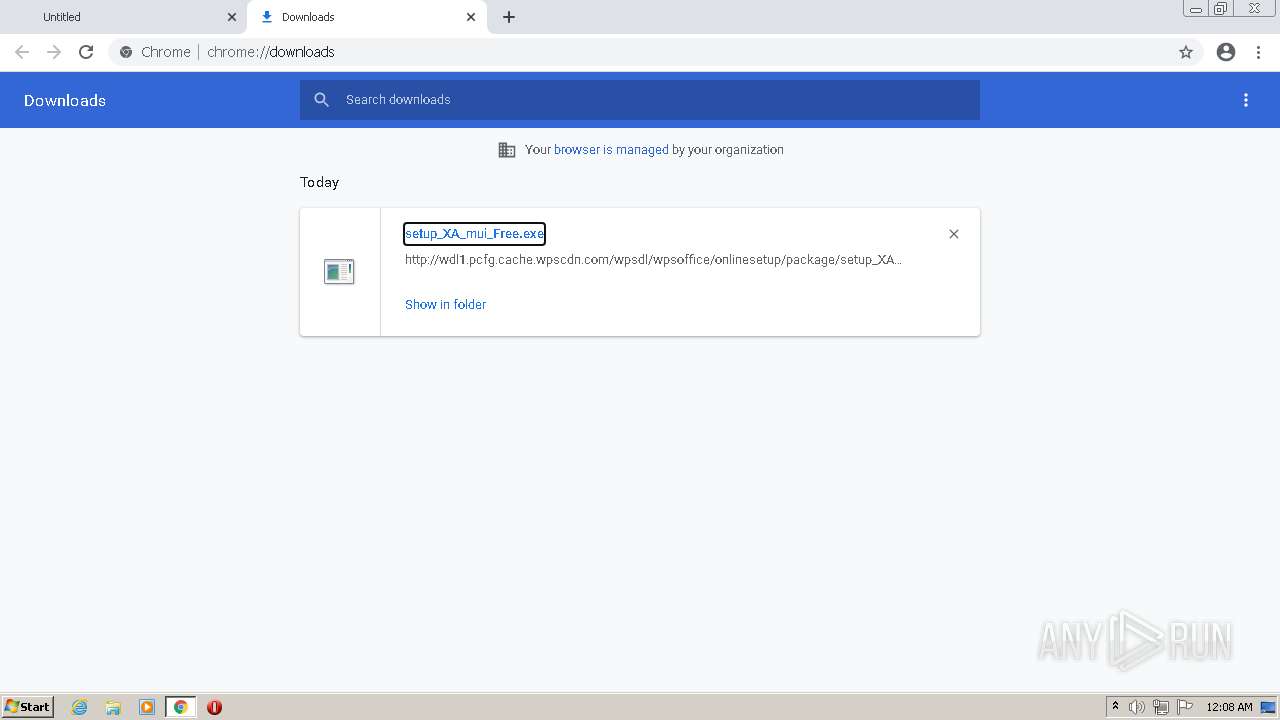
| URL: | http://wdl1.pcfg.cache.wpscdn.com/wpsdl/wpsoffice/onlinesetup/package/setup_XA_mui_Free.exe |
| Full analysis: | https://app.any.run/tasks/dbfed521-4d85-49c5-bd97-9749cfc2e73f |
| Verdict: | Malicious activity |
| Analysis date: | October 04, 2022, 23:06:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 8BE4FAA6CFDA2687C7A09B82671EFDCB |
| SHA1: | C2A658D543672A0DE1AEB0287B03C1740DF62CAF |
| SHA256: | 91E507CA8291FC29E3180E3941F485840F586C41BE9B39F66801D38BFE28B9B1 |
| SSDEEP: | 3:N1KJBaWjNRoTJVGJbWDYXZEWW76HrlJn:CSWxMVGJnXgeJ |
MALICIOUS
Drops executable file immediately after starts
- chrome.exe (PID: 3116)
- setup_XA_mui_Free.exe (PID: 3440)
- setup_XA_mui_Free.exe (PID: 1588)
- chrome.exe (PID: 3436)
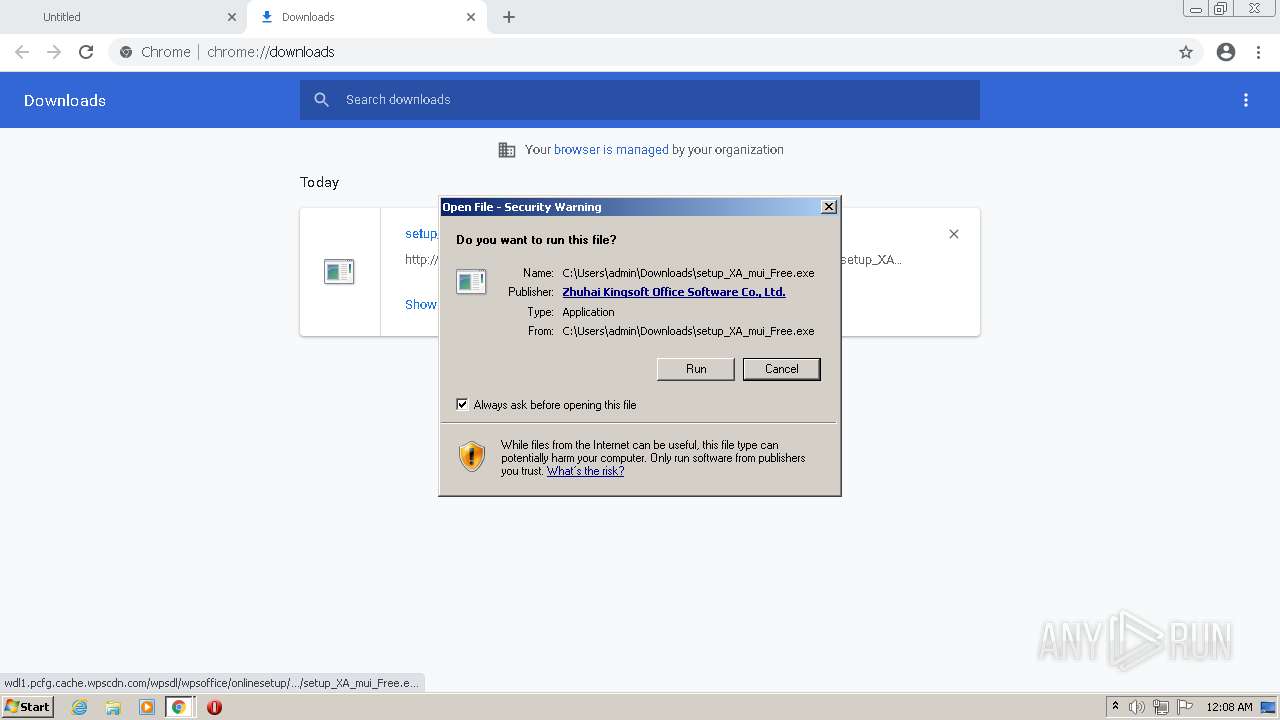
Application was dropped or rewritten from another process
- setup_XA_mui_Free.exe (PID: 3440)
- setup_XA_mui_Free.exe (PID: 1588)
Loads dropped or rewritten executable
- setup_XA_mui_Free.exe (PID: 1588)
Drops known malicious document
- setup_XA_mui_Free.exe (PID: 1588)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 3116)
- setup_XA_mui_Free.exe (PID: 1588)
- setup_XA_mui_Free.exe (PID: 3440)
- chrome.exe (PID: 3436)
Drops a file with a compile date too recent
- chrome.exe (PID: 3116)
- setup_XA_mui_Free.exe (PID: 1588)
- setup_XA_mui_Free.exe (PID: 3440)
- chrome.exe (PID: 3436)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3116)
Creates files in the user directory
- setup_XA_mui_Free.exe (PID: 3440)
- setup_XA_mui_Free.exe (PID: 1588)
Reads the computer name
- setup_XA_mui_Free.exe (PID: 3440)
- setup_XA_mui_Free.exe (PID: 1588)
Checks supported languages
- setup_XA_mui_Free.exe (PID: 1588)
- setup_XA_mui_Free.exe (PID: 3440)
Application launched itself
- setup_XA_mui_Free.exe (PID: 3440)
INFO
Checks supported languages
- chrome.exe (PID: 3368)
- chrome.exe (PID: 1856)
- chrome.exe (PID: 3700)
- chrome.exe (PID: 1788)
- chrome.exe (PID: 2564)
- chrome.exe (PID: 1716)
- chrome.exe (PID: 2092)
- chrome.exe (PID: 2264)
- chrome.exe (PID: 3116)
- chrome.exe (PID: 3988)
- chrome.exe (PID: 4008)
- chrome.exe (PID: 3404)
- chrome.exe (PID: 2792)
- chrome.exe (PID: 3108)
- chrome.exe (PID: 2628)
- chrome.exe (PID: 2904)
- chrome.exe (PID: 3108)
- chrome.exe (PID: 3216)
- chrome.exe (PID: 3264)
- chrome.exe (PID: 752)
- chrome.exe (PID: 2684)
- chrome.exe (PID: 3268)
- chrome.exe (PID: 3108)
- chrome.exe (PID: 828)
- chrome.exe (PID: 3436)
- chrome.exe (PID: 4088)
- chrome.exe (PID: 3244)
- chrome.exe (PID: 2988)
- chrome.exe (PID: 4012)
- chrome.exe (PID: 3864)
- chrome.exe (PID: 3268)
Reads the computer name
- chrome.exe (PID: 3116)
- chrome.exe (PID: 1856)
- chrome.exe (PID: 1788)
- chrome.exe (PID: 2092)
- chrome.exe (PID: 3404)
- chrome.exe (PID: 2792)
- chrome.exe (PID: 3108)
- chrome.exe (PID: 2904)
- chrome.exe (PID: 3216)
- chrome.exe (PID: 752)
- chrome.exe (PID: 3268)
Reads the hosts file
- chrome.exe (PID: 3116)
- chrome.exe (PID: 1788)
Application launched itself
- chrome.exe (PID: 3116)
Reads settings of System Certificates
- chrome.exe (PID: 1788)
- chrome.exe (PID: 3116)
- setup_XA_mui_Free.exe (PID: 1588)
Reads the date of Windows installation
- chrome.exe (PID: 2792)
Checks Windows Trust Settings
- chrome.exe (PID: 3116)
Dropped object may contain Bitcoin addresses
- setup_XA_mui_Free.exe (PID: 1588)
- setup_XA_mui_Free.exe (PID: 3440)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
73
Monitored processes
33
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --field-trial-handle=1048,324971239603130594,4489669918714025382,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3592 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1048,324971239603130594,4489669918714025382,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3680 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
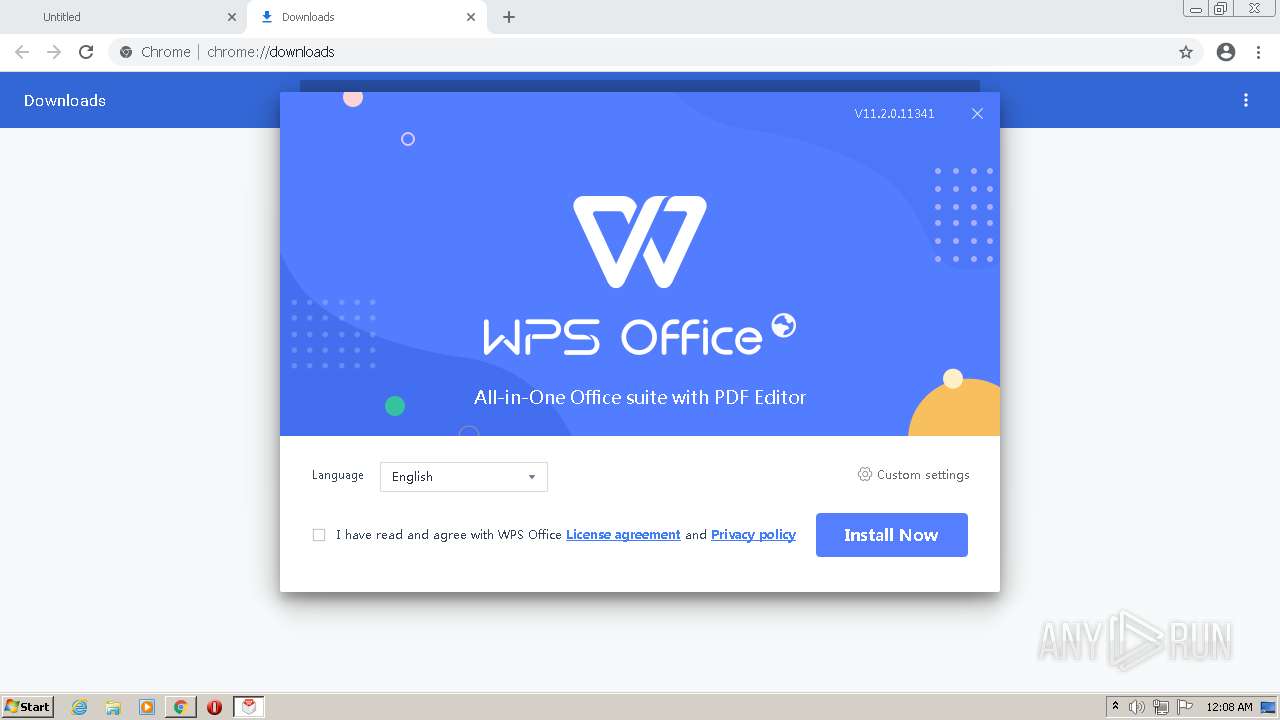
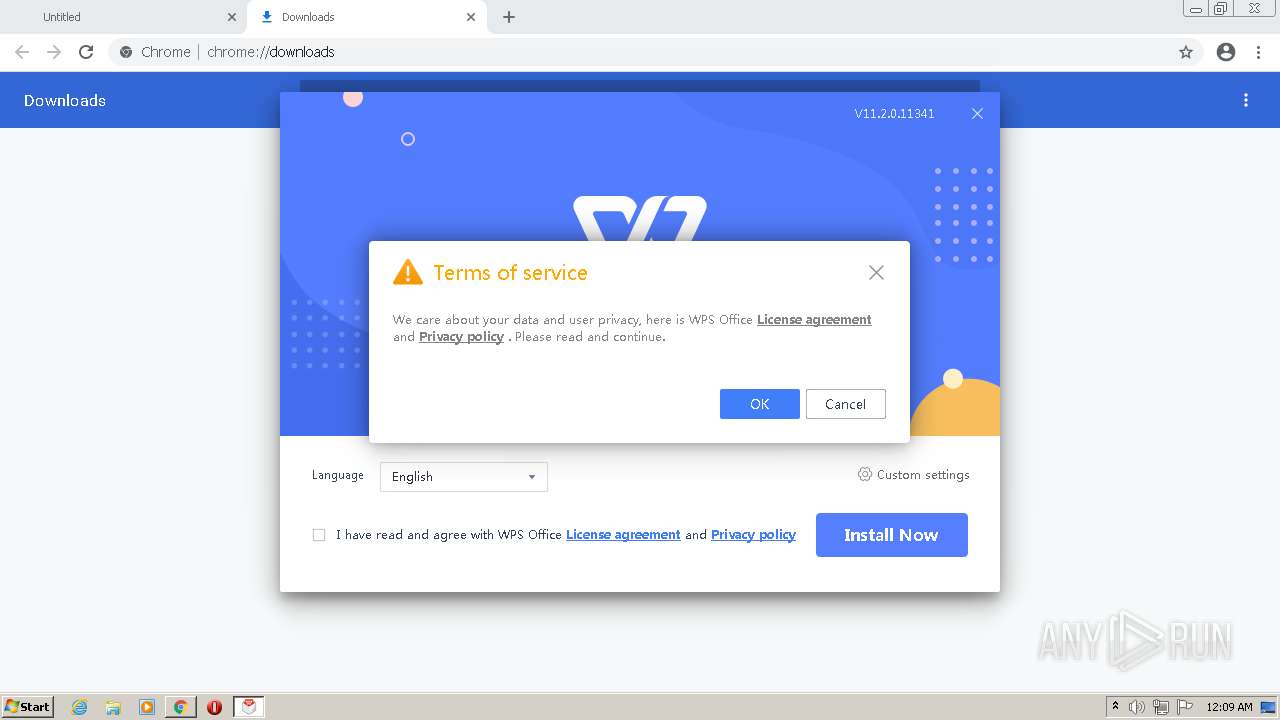
| 1588 | "C:\Users\admin\Downloads\setup_XA_mui_Free.exe" -needcommunicate -localapp="C:\Users\admin\AppData\Local" -appdata="C:\Users\admin\AppData\Roaming" -curuserpath="C:\Users\admin" -curuserdesktoppath="C:\Users\admin\Desktop" -curusertemppath="C:\Users\admin\AppData\Local\Temp" -msgwndname=wpssetup_message_159729 -assobitmap=0 -assoexts= -upgradepower | C:\Users\admin\Downloads\setup_XA_mui_Free.exe | setup_XA_mui_Free.exe | ||||||||||||
User: admin Company: Zhuhai Kingsoft Office Software Co.,Ltd Integrity Level: HIGH Description: WPS Install Application Exit code: 0 Version: 11,2,0,11341 Modules
| |||||||||||||||
| 1716 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,324971239603130594,4489669918714025382,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1832 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1788 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1048,324971239603130594,4489669918714025382,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1244 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1048,324971239603130594,4489669918714025382,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1072 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2092 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1048,324971239603130594,4489669918714025382,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1044 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2264 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1048,324971239603130594,4489669918714025382,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=2904 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,324971239603130594,4489669918714025382,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2176 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1048,324971239603130594,4489669918714025382,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2296 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
17 009
Read events
16 808
Write events
196
Delete events
5
Modification events
| (PID) Process: | (3116) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3116) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3116) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3116) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3116) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3116) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3116) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3116) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3116) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (3116) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
137
Suspicious files
241
Text files
2 469
Unknown types
86
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-633CBC6E-C2C.pma | — | |
MD5:— | SHA256:— | |||
| 3116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\71268aaa-8e9a-49f4-a307-5c53a1b3e52f.tmp | text | |
MD5:— | SHA256:— | |||
| 3116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\b2367796-4326-44b6-a7fa-1756be9a5367.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 3116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF134d87.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 3116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:995C92837E4775CAFFE387D51ADBA520 | SHA256:51247C3464FD988B72670002D01A57FBFF1348704D325DC8FF8817ED2459D0D9 | |||
| 3116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF134d77.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 3116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:EF1D5606A483BB6C72C81A3F649BEB18 | SHA256:BA083E7585ADA9936944FE56BC0141A544F18A01C3424E5C9F02375B34FE3D45 | |||
| 3116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 3116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF134e71.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
| 3116 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Extension State\LOG.old~RF1353ff.TMP | text | |
MD5:D097F8EB2230B3F32C41C5D75790508C | SHA256:ADDF87D20CD455CFB4AACB6B76719629C0277A4CF70B496343047BB73ABBAEF5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
23
DNS requests
10
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | — | — | whitelisted |
1788 | chrome.exe | GET | — | 104.17.188.189:80 | http://wdl1.pcfg.cache.wpscdn.com/wpsdl/wpsoffice/onlinesetup/package/setup_XA_mui_Free.exe | US | — | — | malicious |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | prg | 22.2 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 10.3 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 10.3 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 297 Kb | whitelisted |
— | — | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjg0QUFYSnN4MFUtaEQwNDZqVGRkVkFmZw/1.0.6.0_aemomkdncapdnfajjbbcbdebjljbpmpj.crx | US | binary | 39.8 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 87.7 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 39.8 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 10.3 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1788 | chrome.exe | 172.217.169.174:443 | clients2.google.com | GOOGLE | US | whitelisted |
1788 | chrome.exe | 142.250.186.45:443 | accounts.google.com | GOOGLE | US | suspicious |
1788 | chrome.exe | 104.17.188.189:80 | wdl1.pcfg.cache.wpscdn.com | CLOUDFLARENET | — | suspicious |
1788 | chrome.exe | 142.250.74.193:443 | clients2.googleusercontent.com | GOOGLE | US | whitelisted |
1788 | chrome.exe | 142.250.186.163:443 | ssl.gstatic.com | GOOGLE | US | whitelisted |
1788 | chrome.exe | 104.17.187.189:80 | wdl1.pcfg.cache.wpscdn.com | CLOUDFLARENET | — | suspicious |
— | — | 34.104.35.123:80 | edgedl.me.gvt1.com | GOOGLE | US | whitelisted |
1788 | chrome.exe | 142.250.184.131:443 | update.googleapis.com | GOOGLE | US | whitelisted |
1788 | chrome.exe | 142.250.187.142:443 | sb-ssl.google.com | GOOGLE | US | whitelisted |
1588 | setup_XA_mui_Free.exe | 34.89.231.242:443 | event.wps.com | GOOGLE-CLOUD-PLATFORM | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
wdl1.pcfg.cache.wpscdn.com |
| malicious |
accounts.google.com |
| shared |
clients2.googleusercontent.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
edgedl.me.gvt1.com |
| whitelisted |
clients1.google.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
event.wps.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1788 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
Process | Message |
|---|---|
setup_XA_mui_Free.exe | [kscreen] isElide:0 switchRec:0 switchRecElide:1 |
setup_XA_mui_Free.exe | QLayout: Attempting to add QLayout "" to QWidget "m_BrandAreaWidget", which already has a layout
|
setup_XA_mui_Free.exe | QLayout: Attempting to add QLayout "" to QWidget "", which already has a layout
|
setup_XA_mui_Free.exe | QLayout: Attempting to add QLayout "" to QWidget "m_customizeSettingsWidget", which already has a layout
|
setup_XA_mui_Free.exe | QLayout: Attempting to add QLayout "" to QWidget "m_customizeSettingsWidget", which already has a layout
|
setup_XA_mui_Free.exe | QLayout: Attempting to add QLayout "" to QWidget "m_customizeSettingsWidget", which already has a layout
|
setup_XA_mui_Free.exe | QLayout: Attempting to add QLayout "" to QWidget "m_customizeSettingsWidget", which already has a layout
|
setup_XA_mui_Free.exe | QLayout: Attempting to add QLayout "" to QWidget "m_customizeSettingsWidget", which already has a layout
|
setup_XA_mui_Free.exe | QLayout: Attempting to add QLayout "" to QWidget "m_customizeSettingsWidget", which already has a layout
|
setup_XA_mui_Free.exe | QLayout: Attempting to add QLayout "" to QWidget "m_customizeSettingsWidget", which already has a layout
|