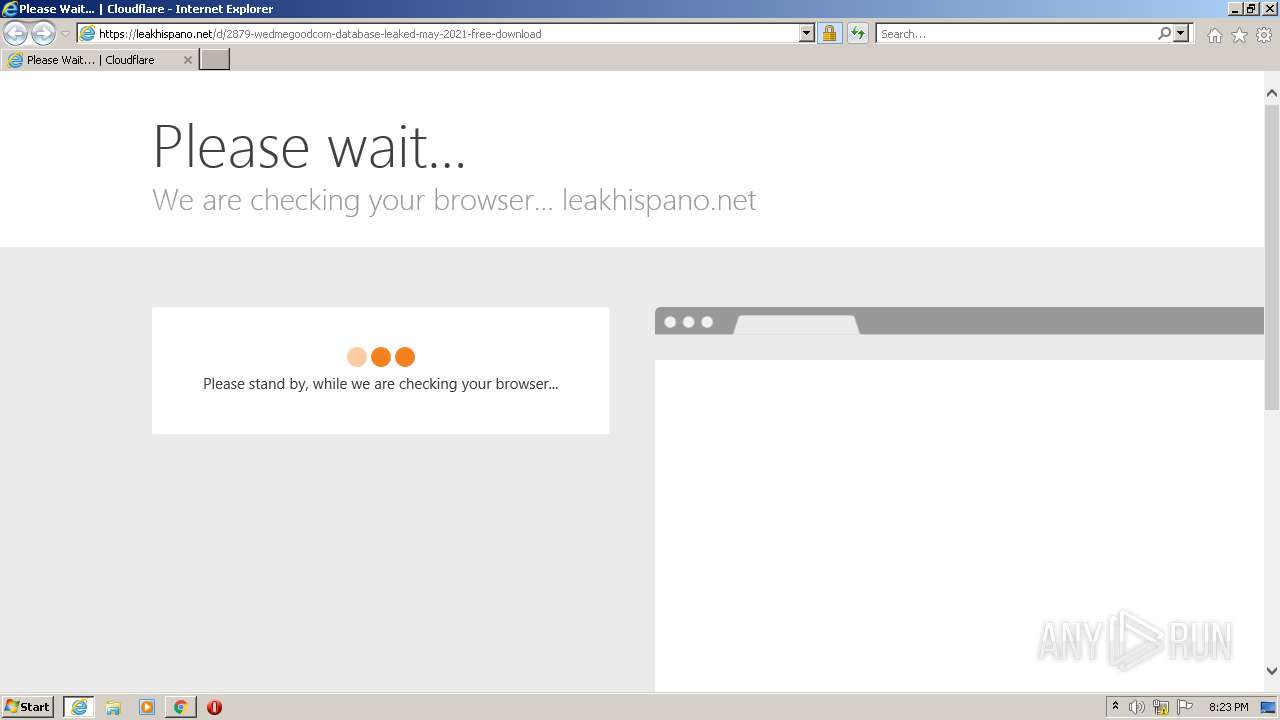
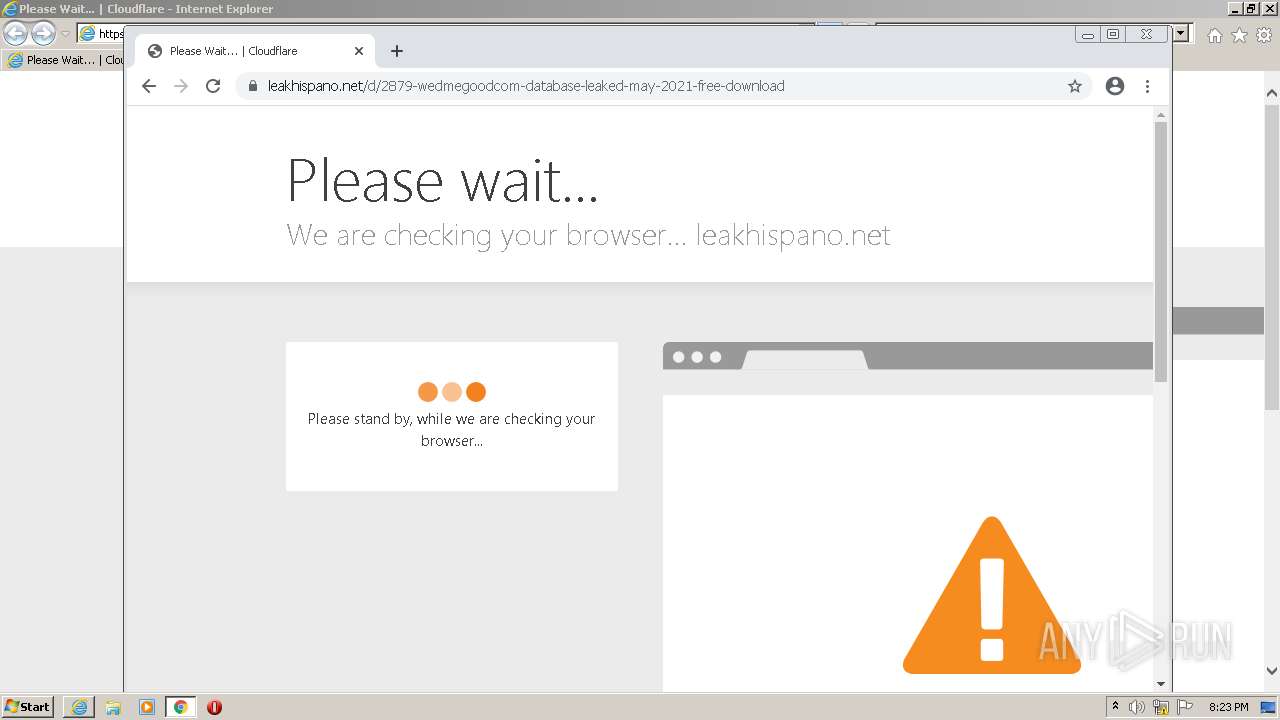
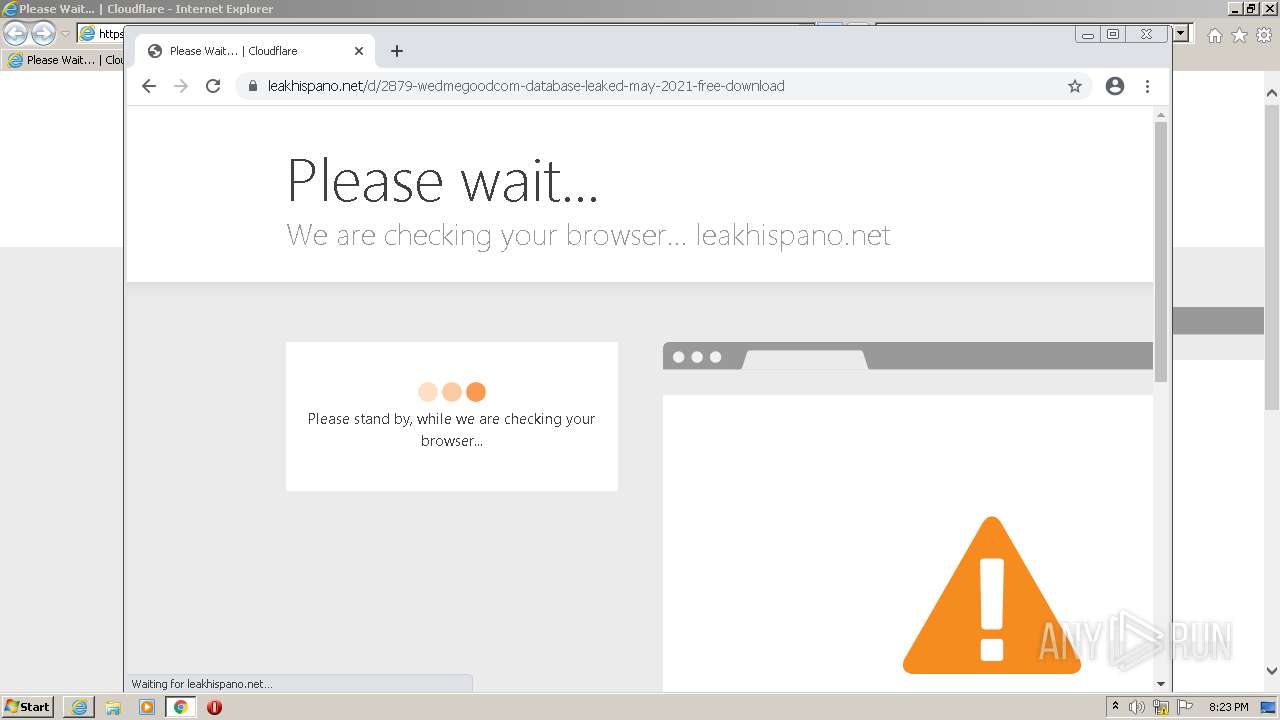
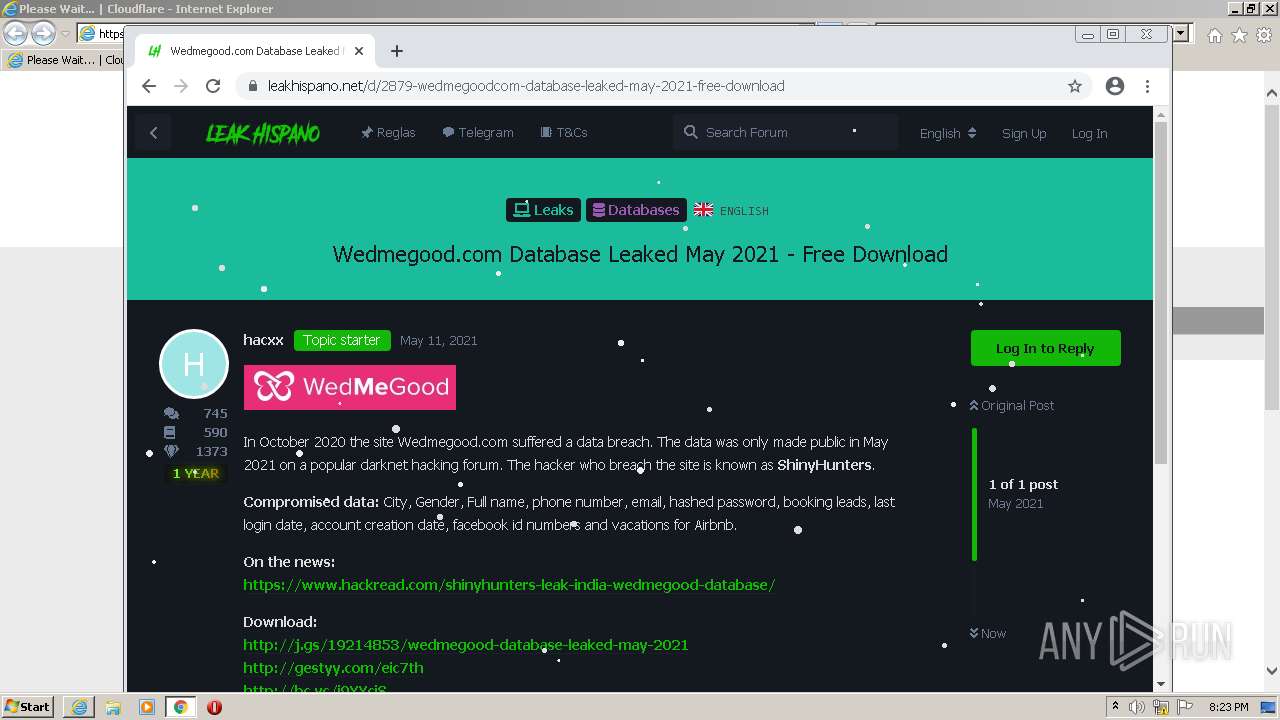
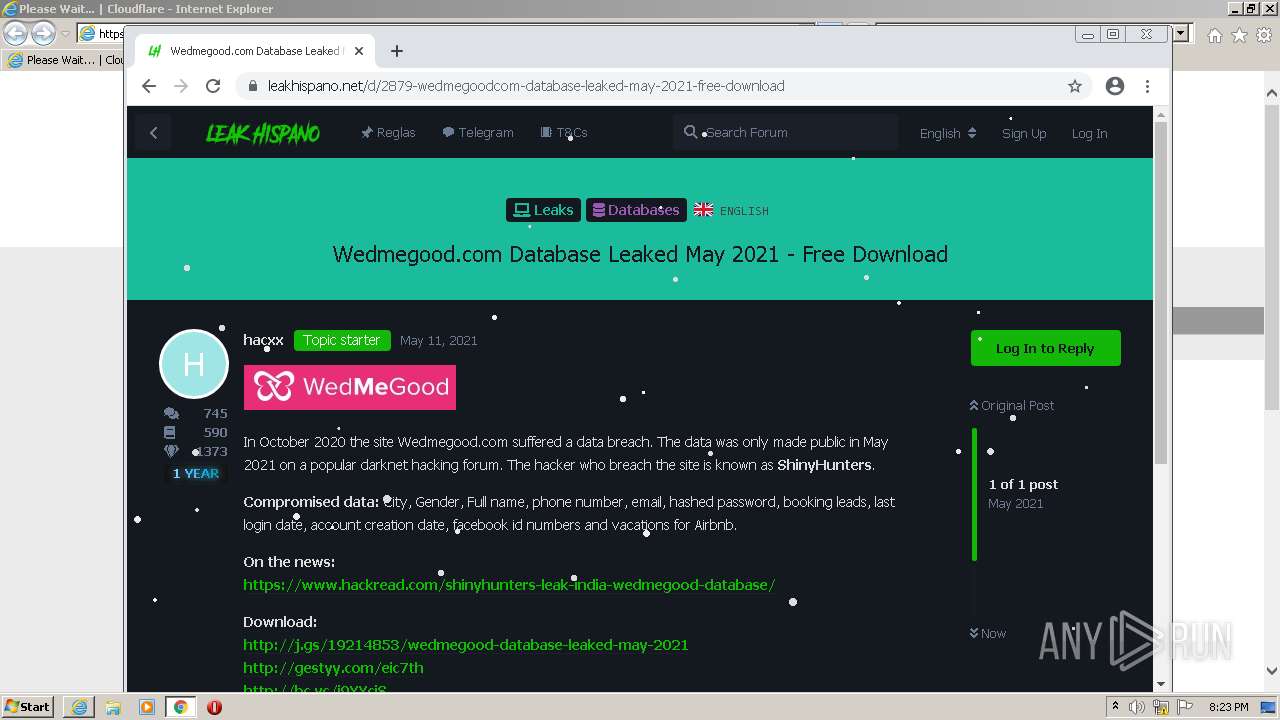
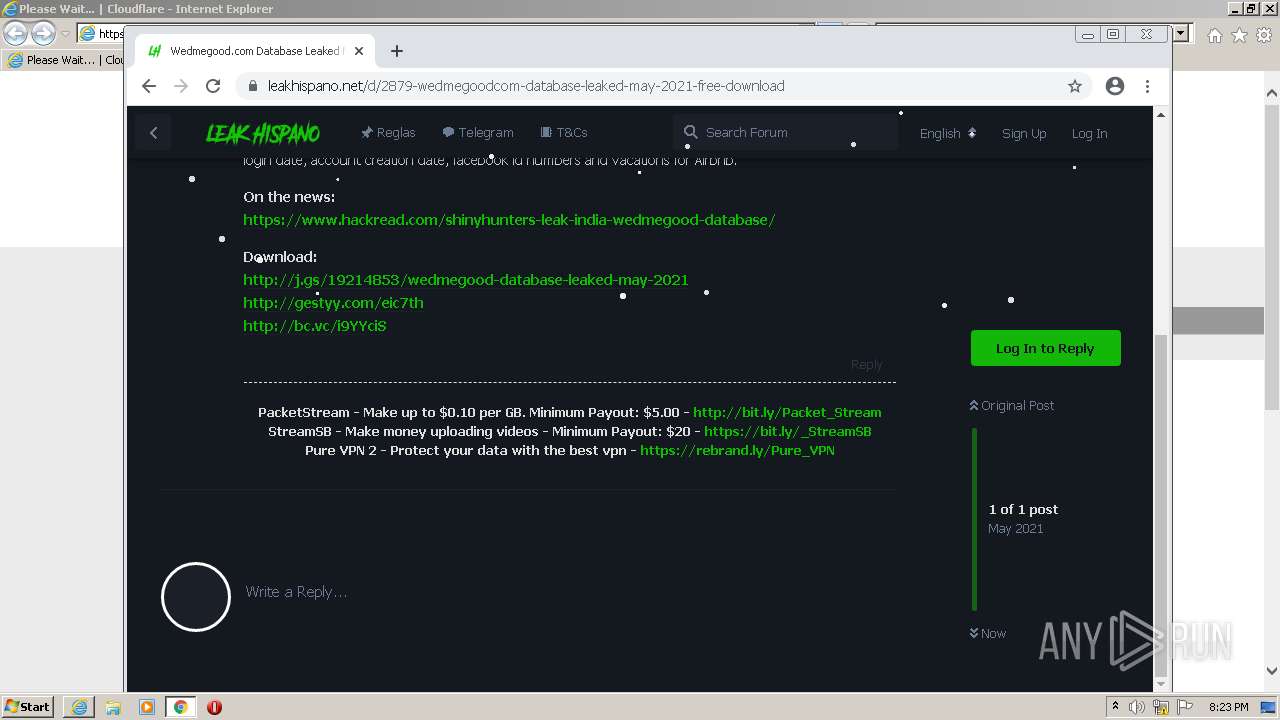
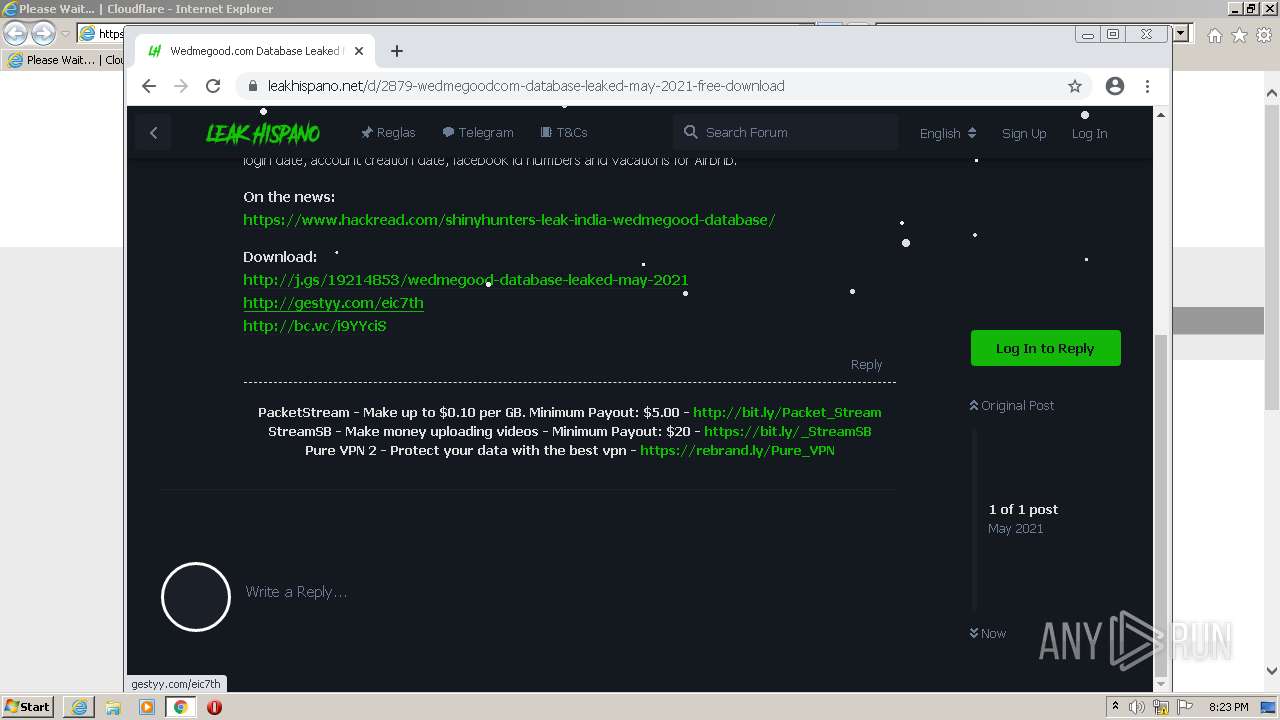
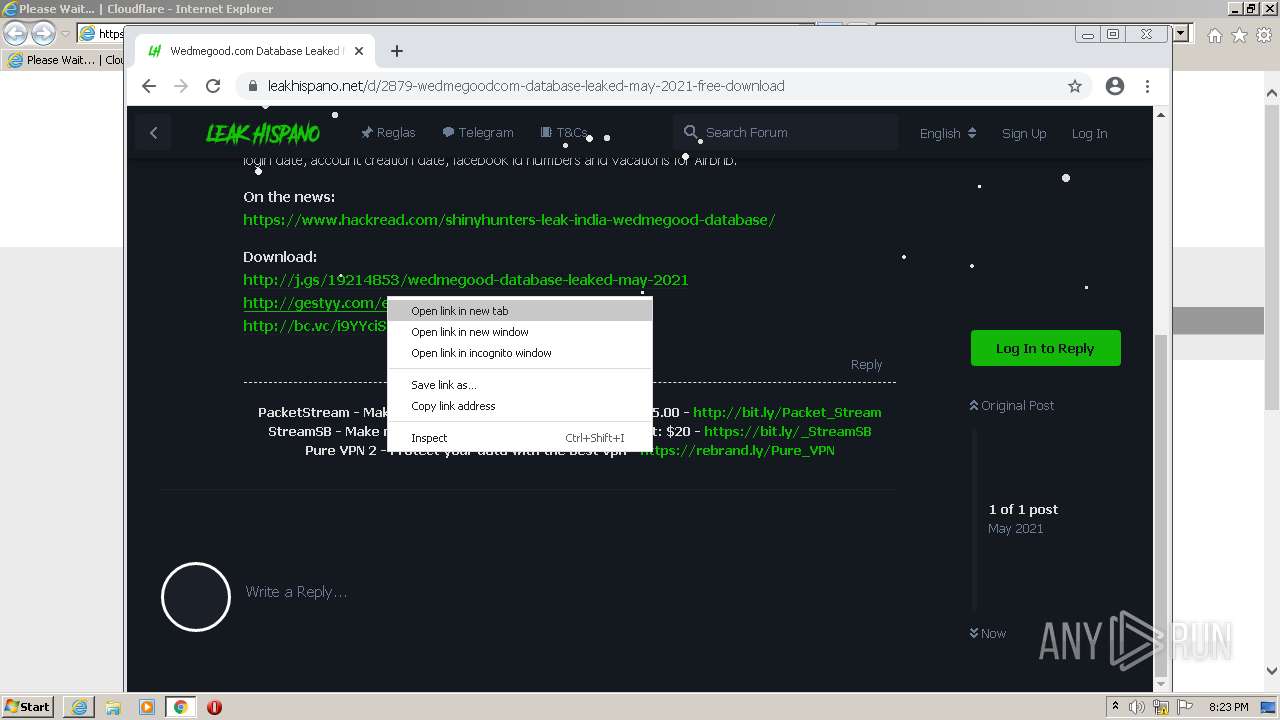
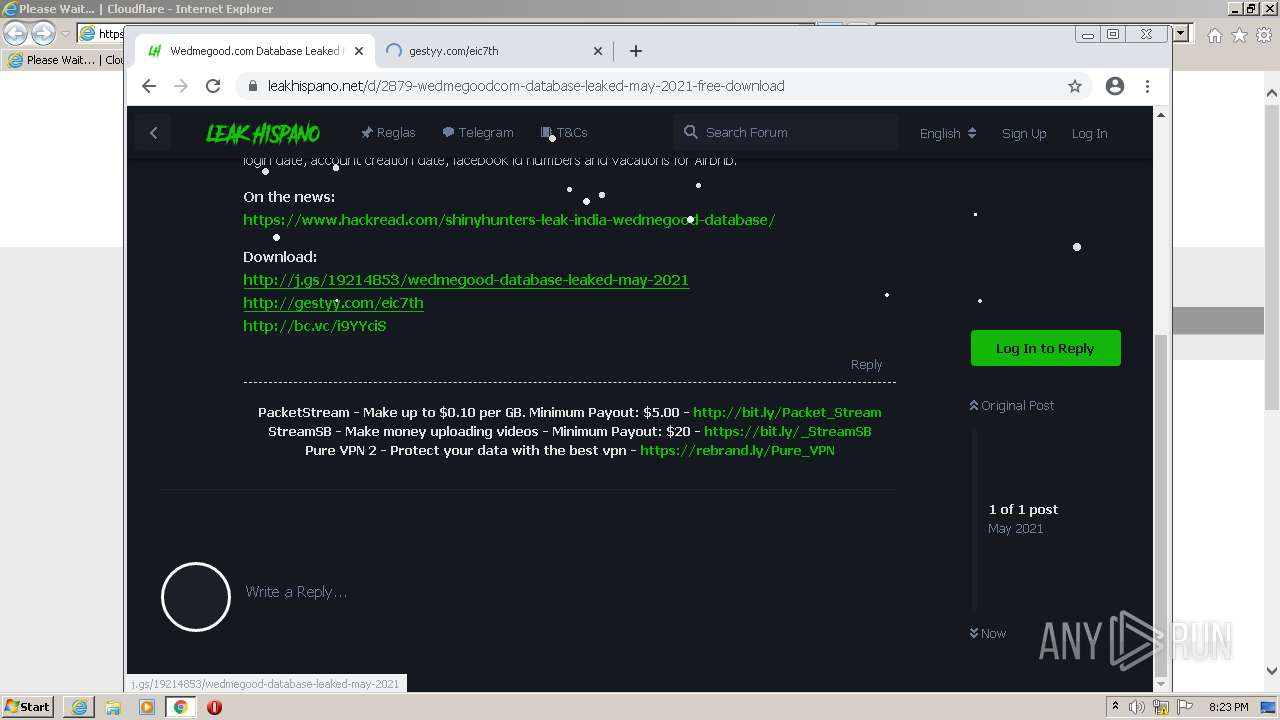
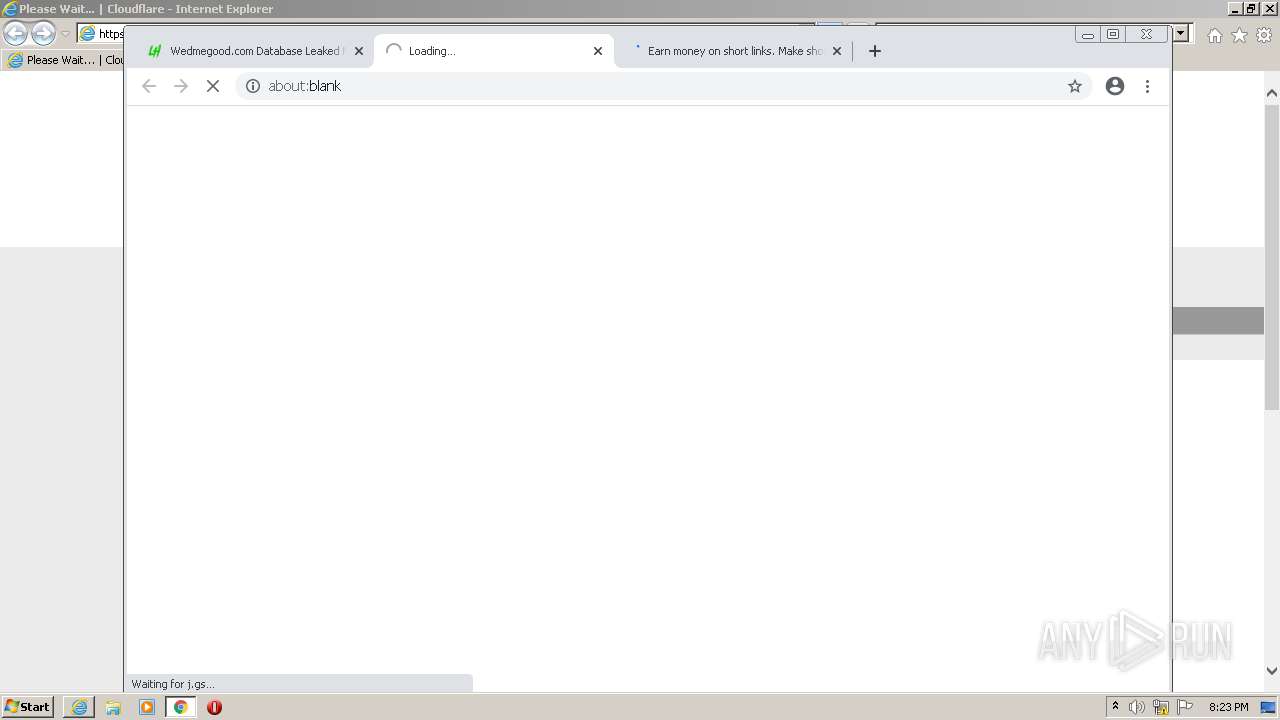
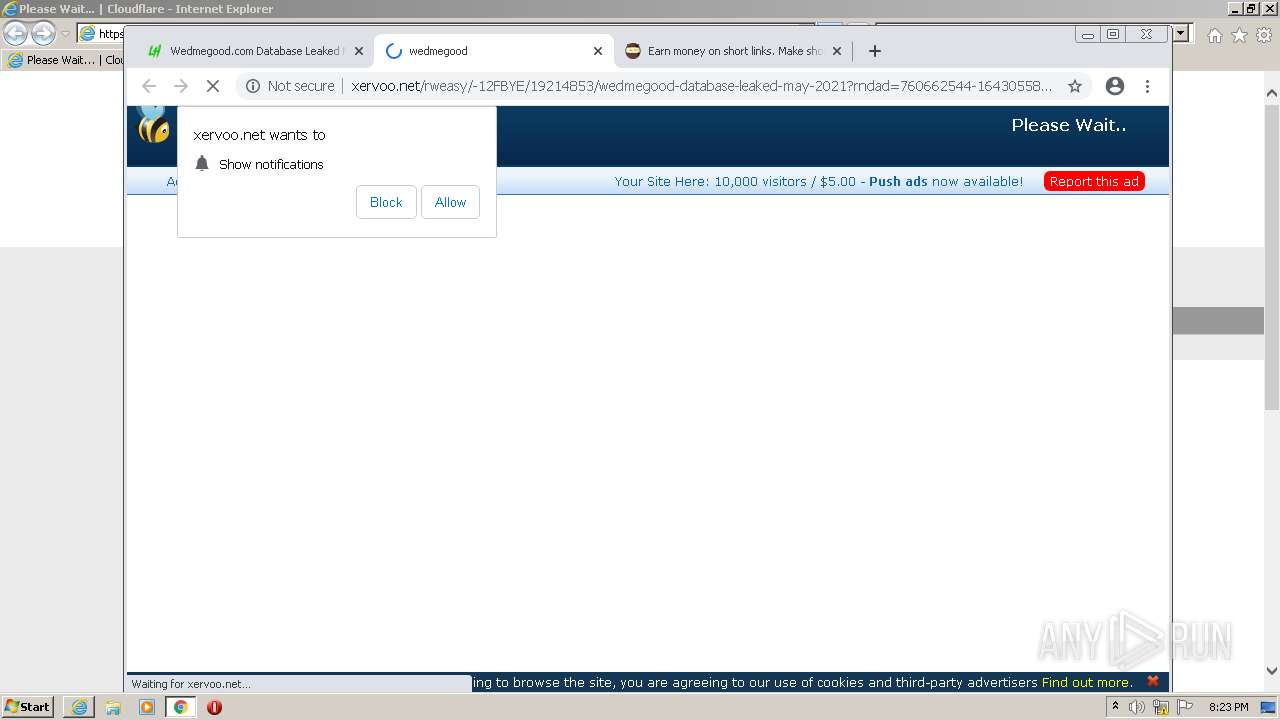
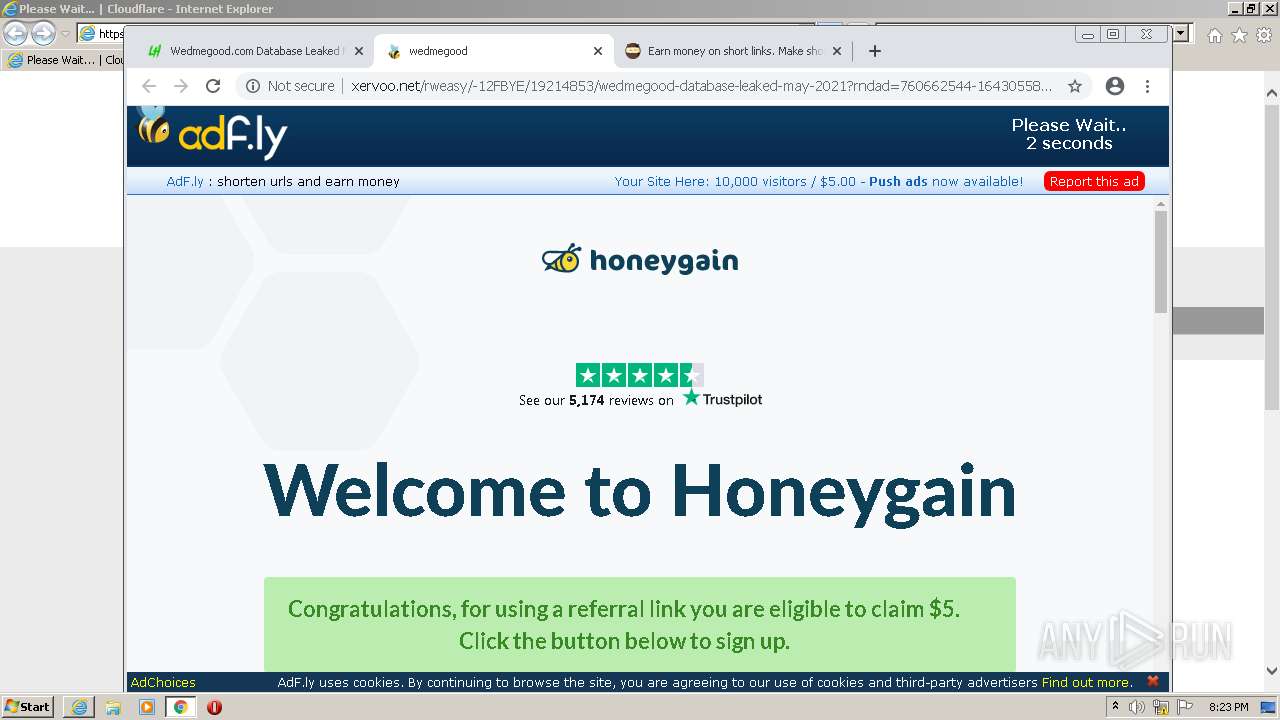
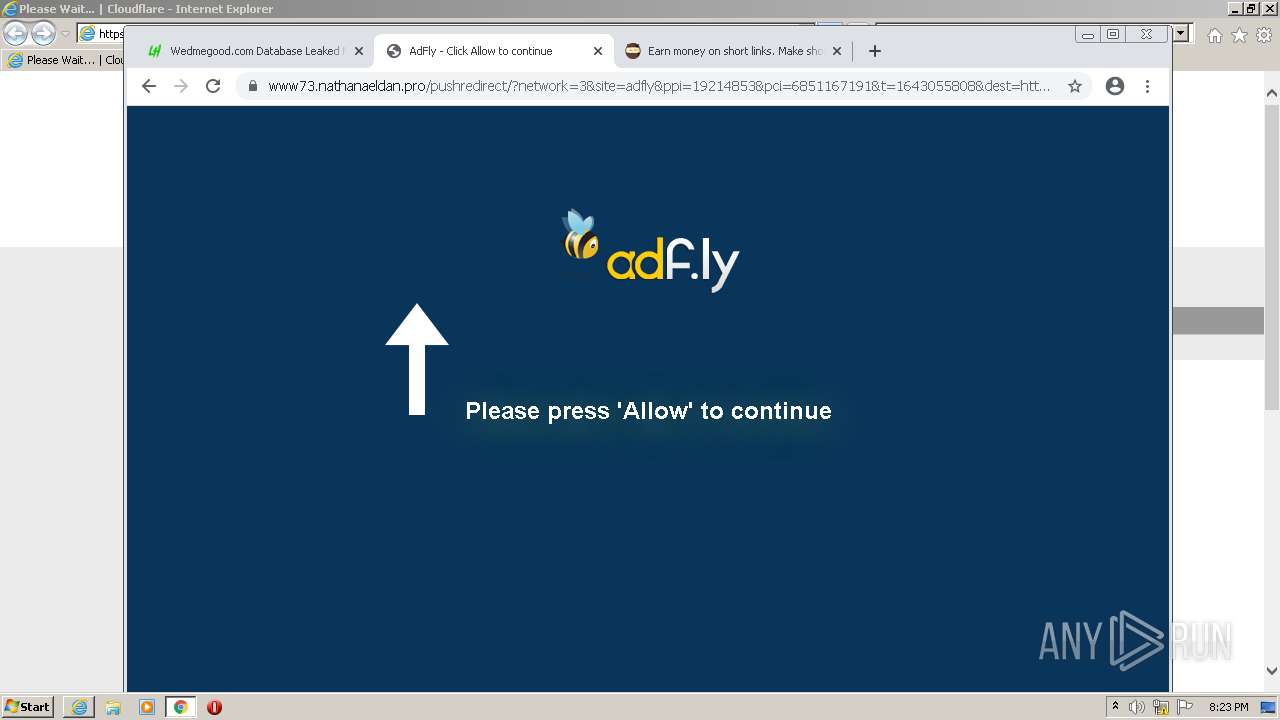
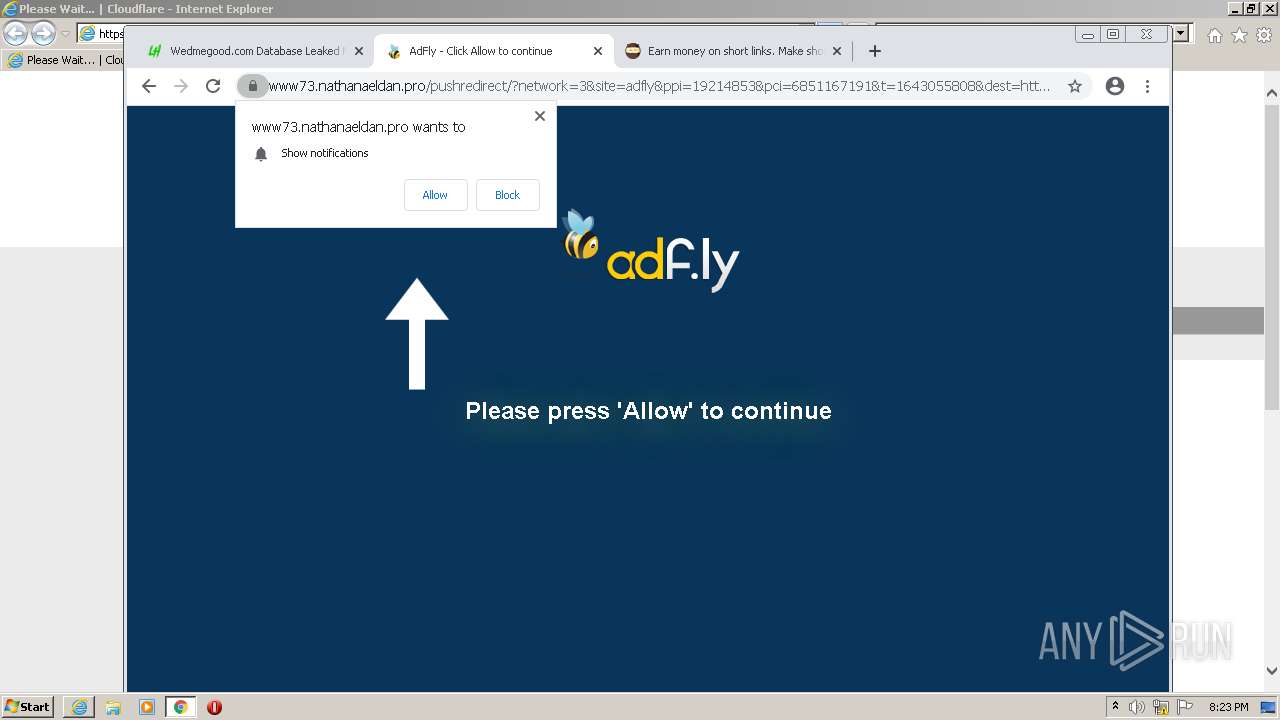
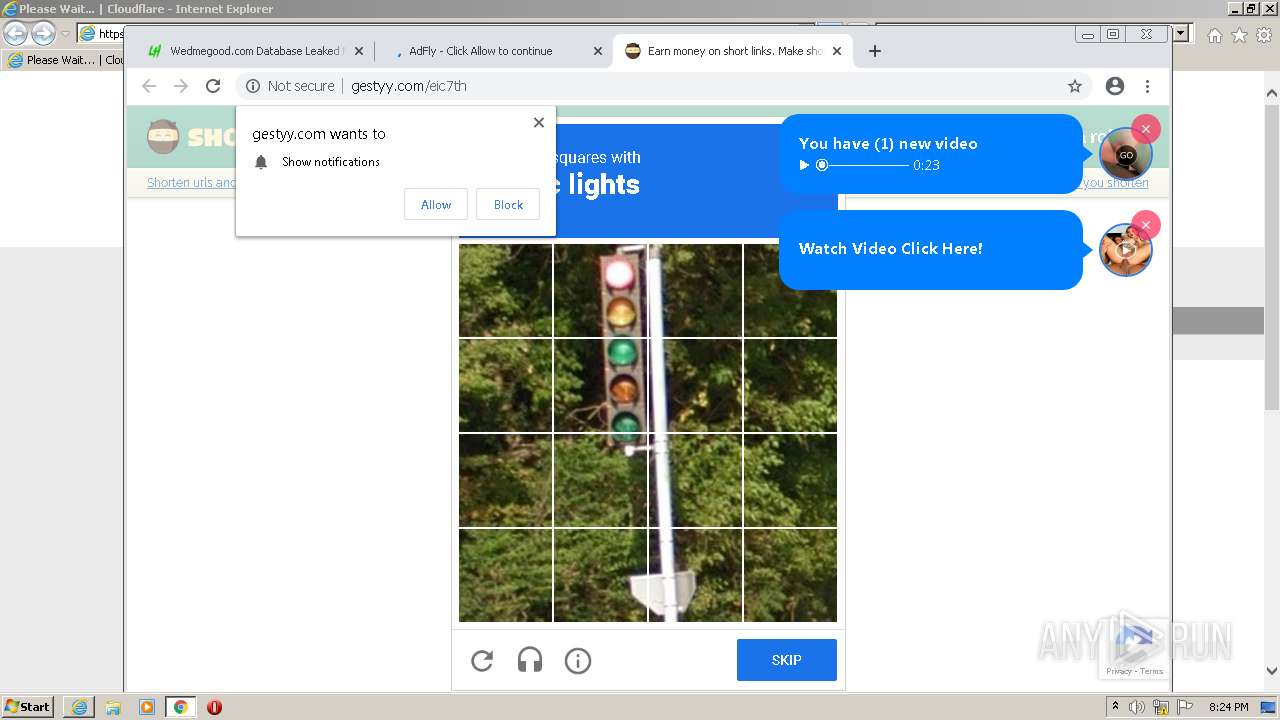
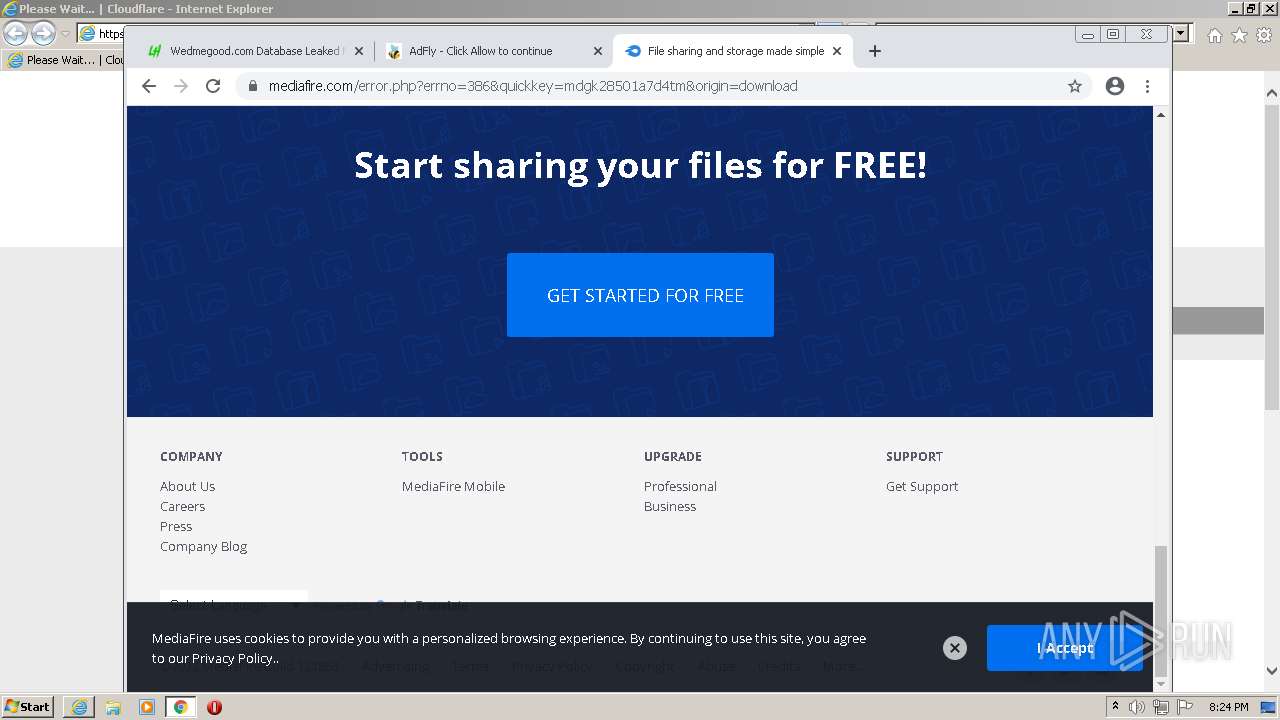
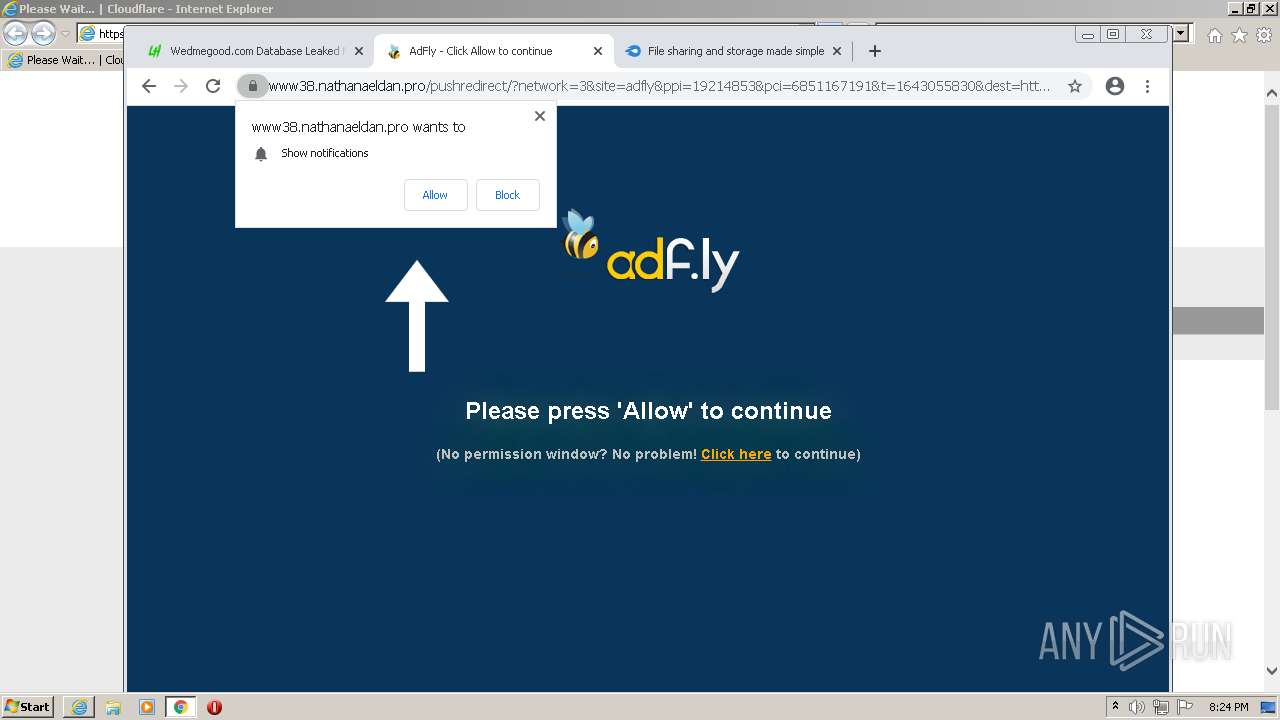
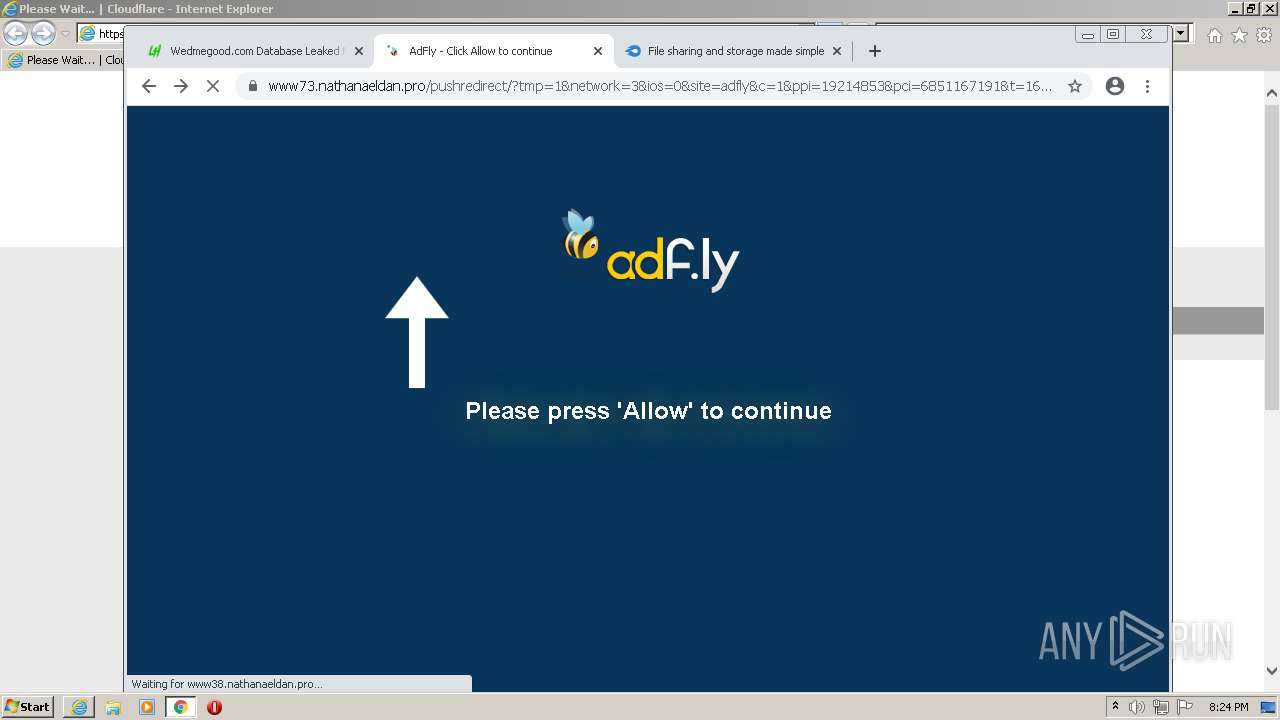
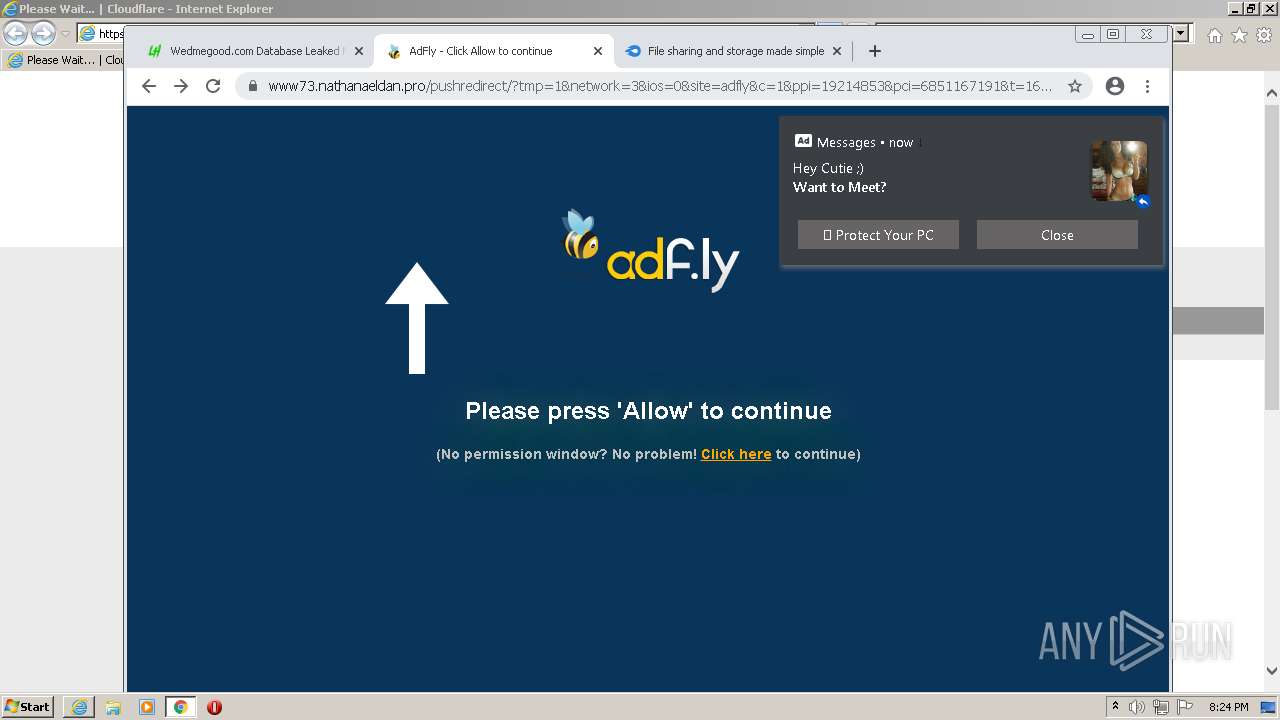
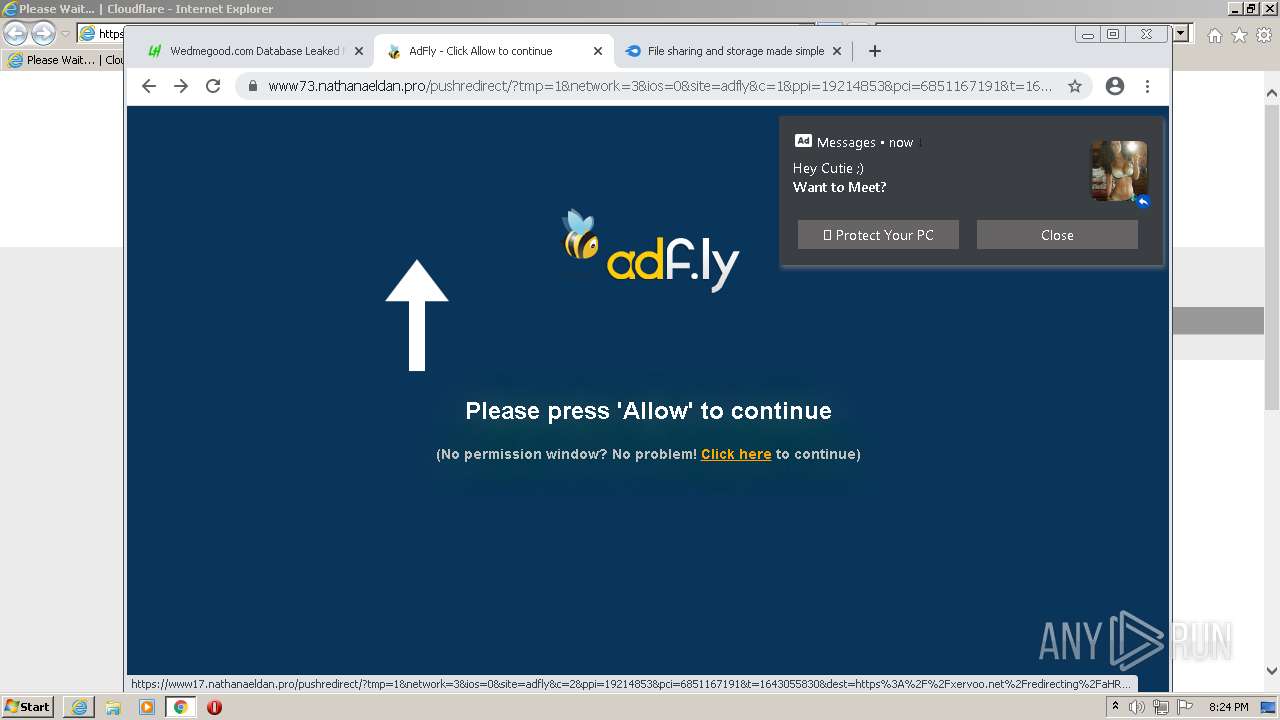
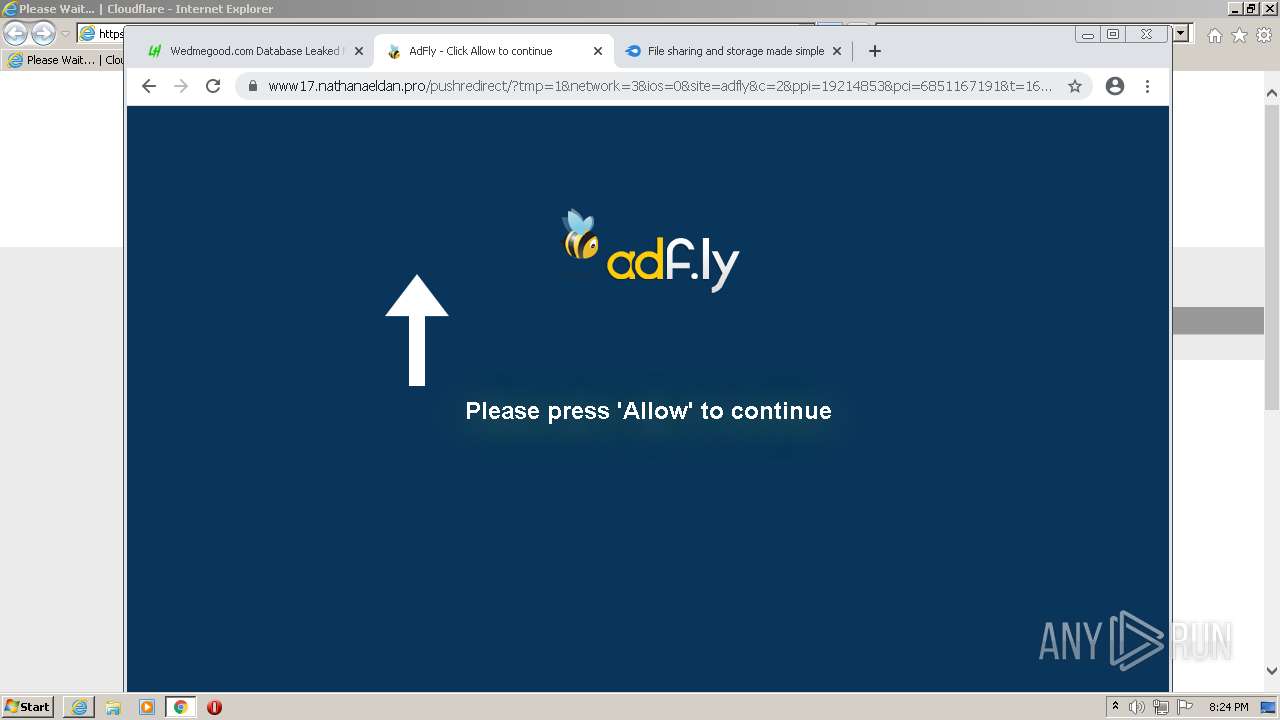
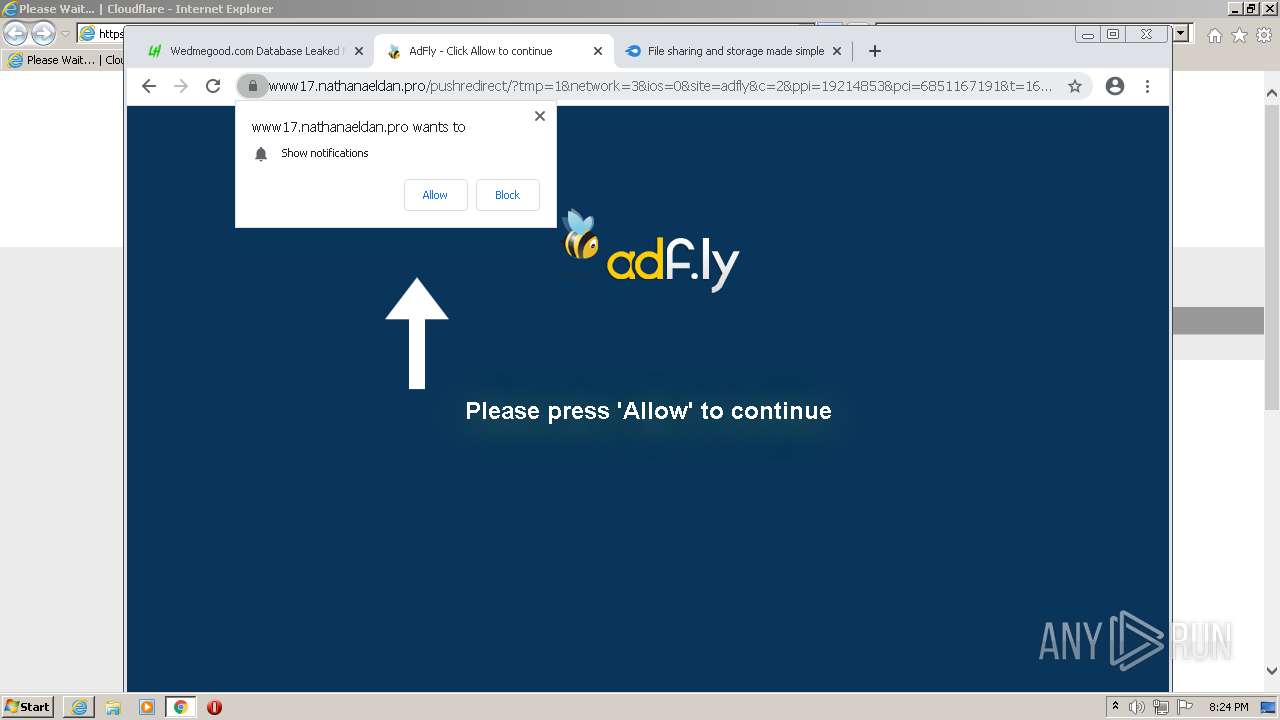
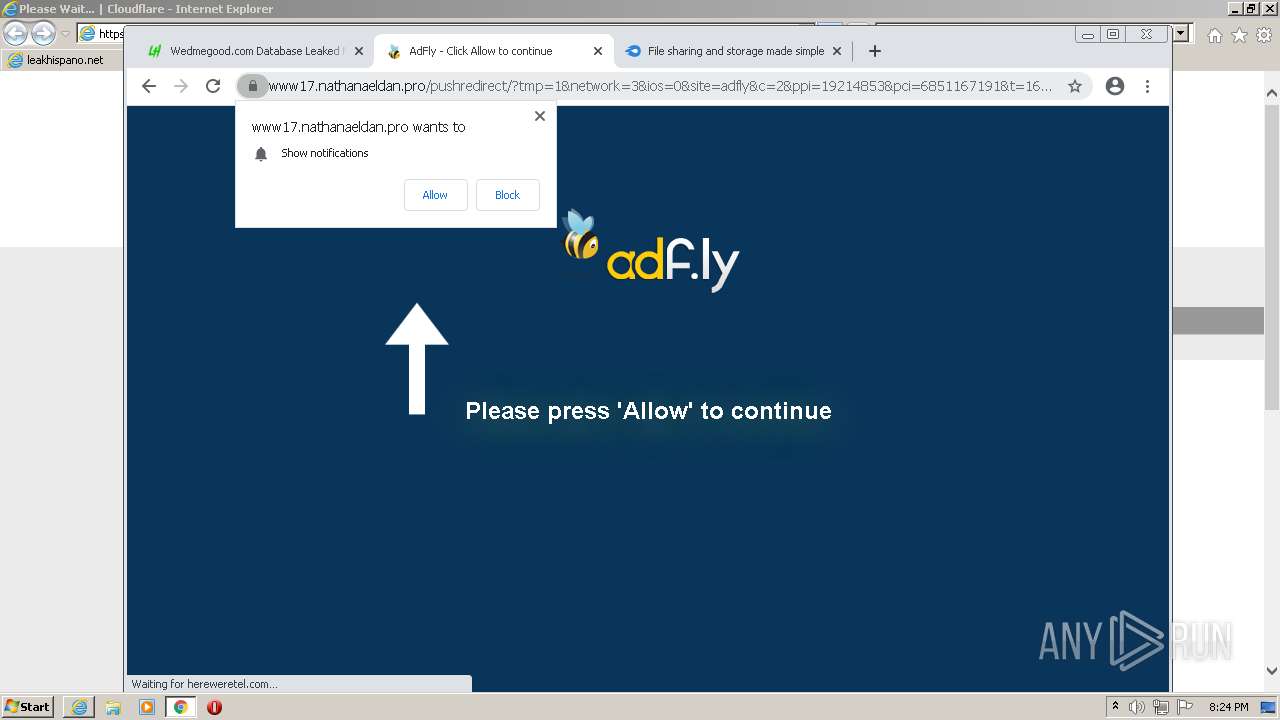
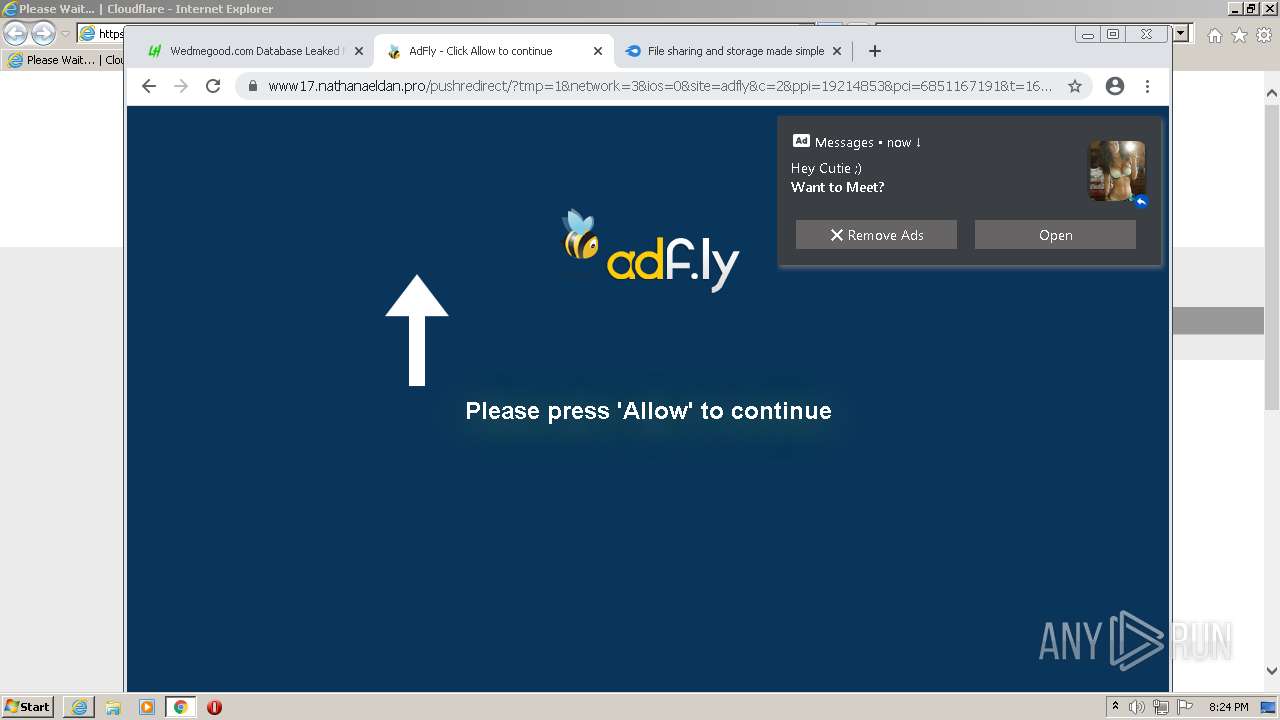
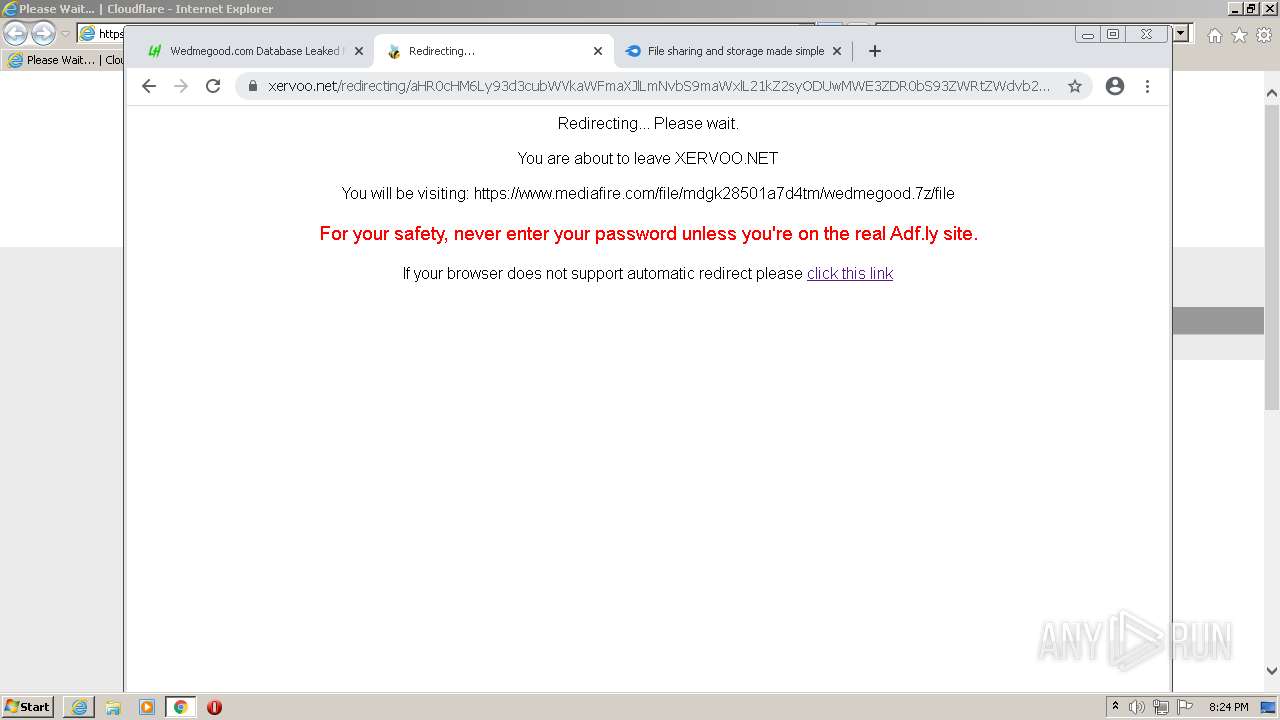
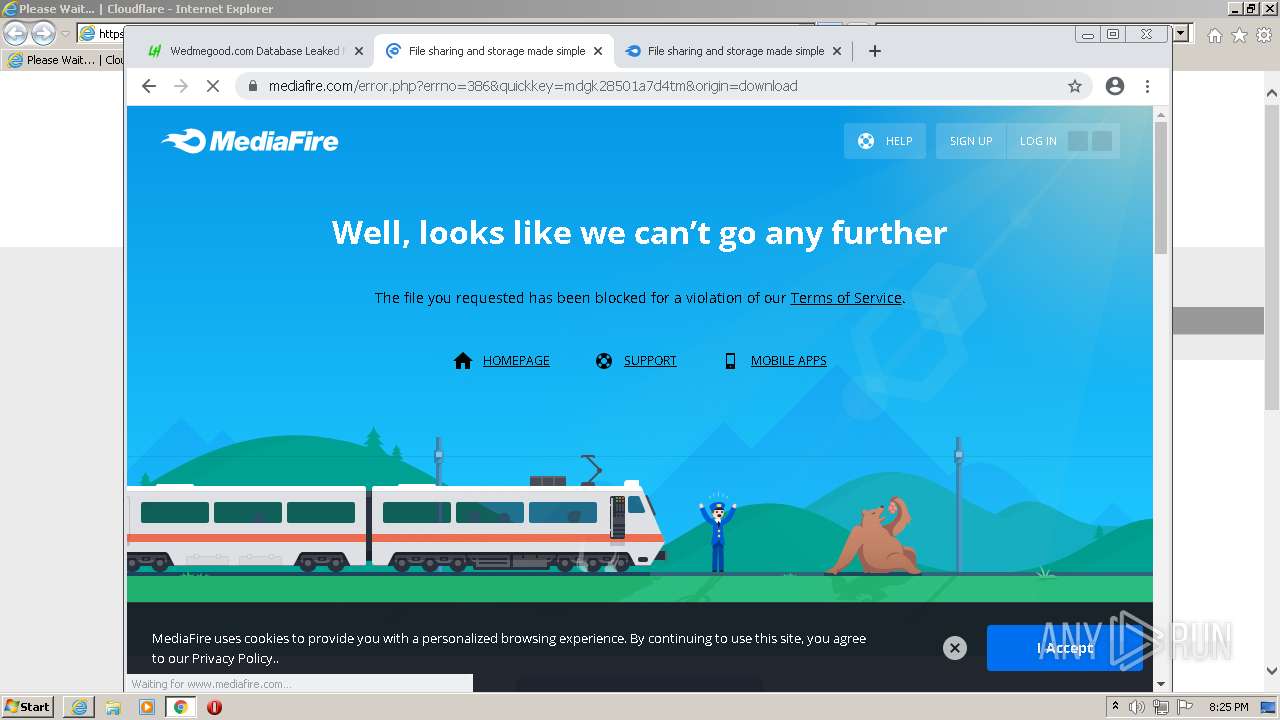
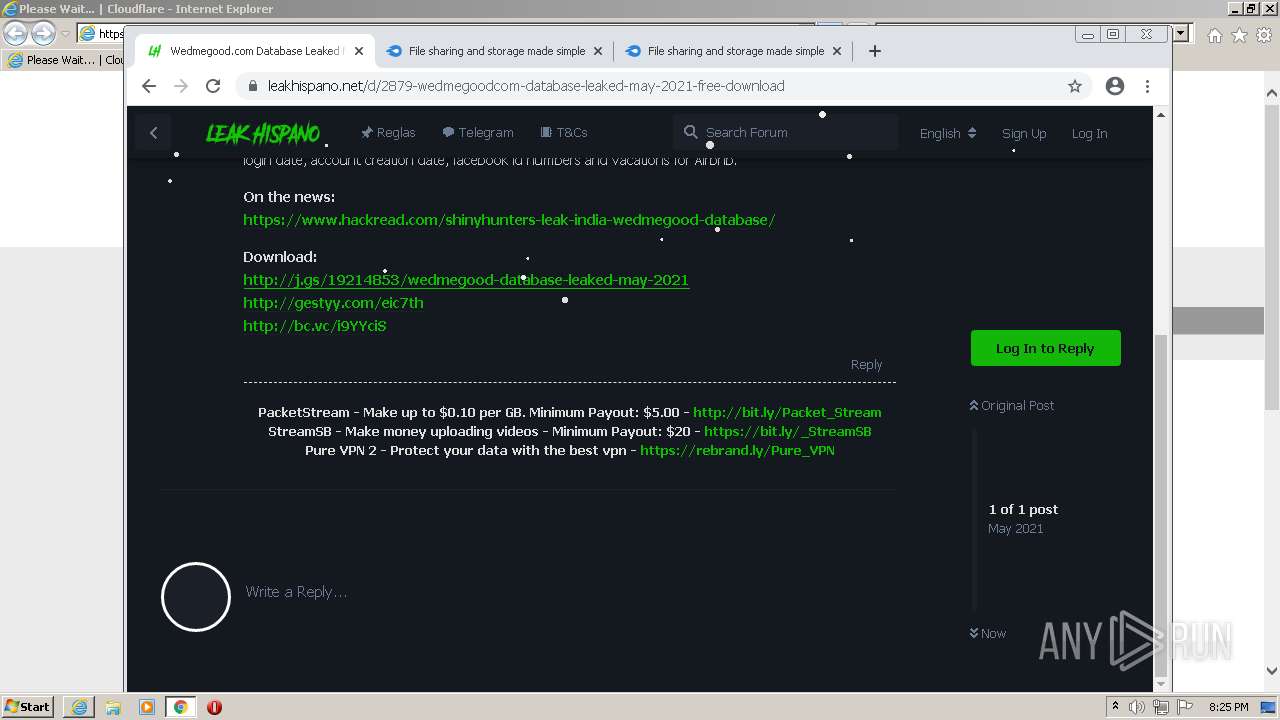
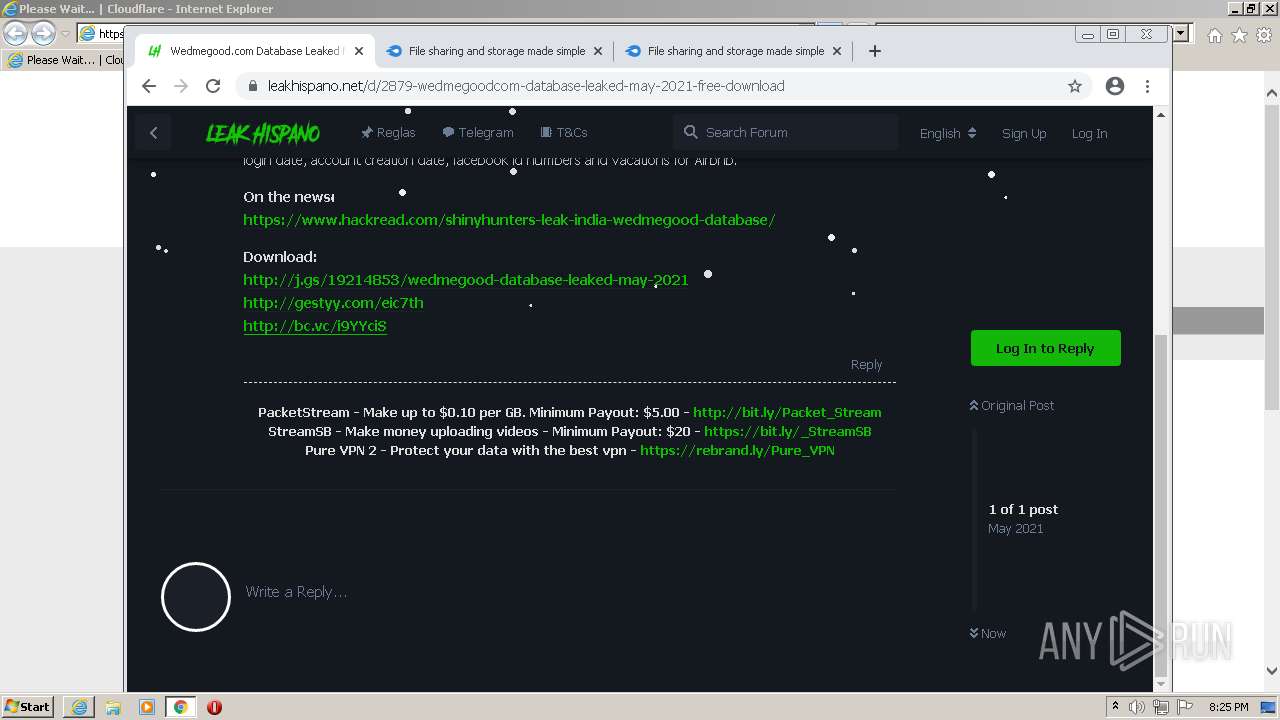
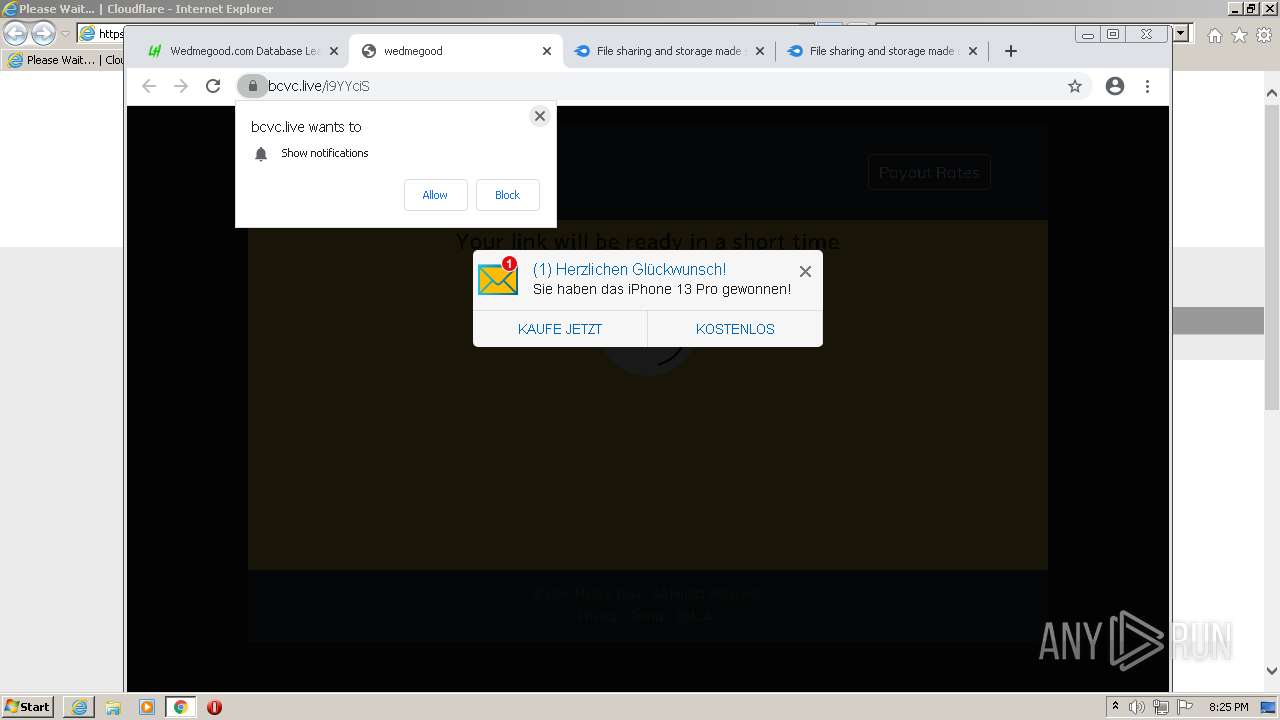
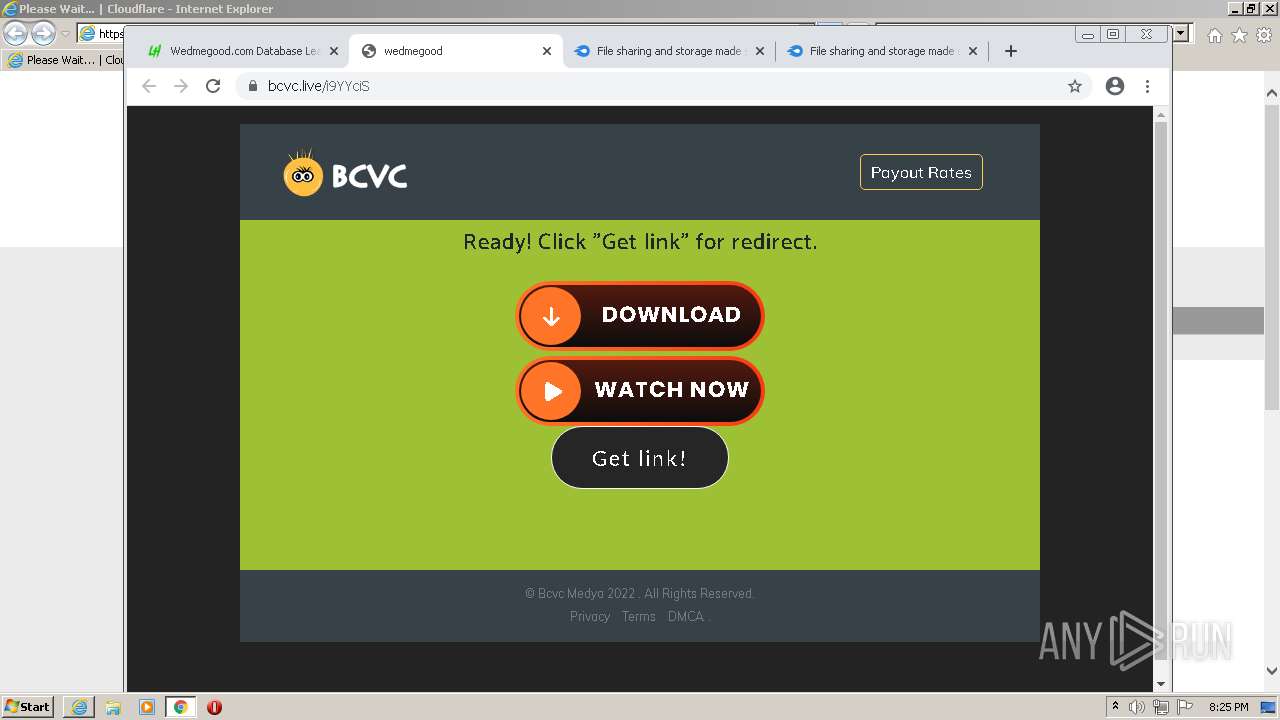
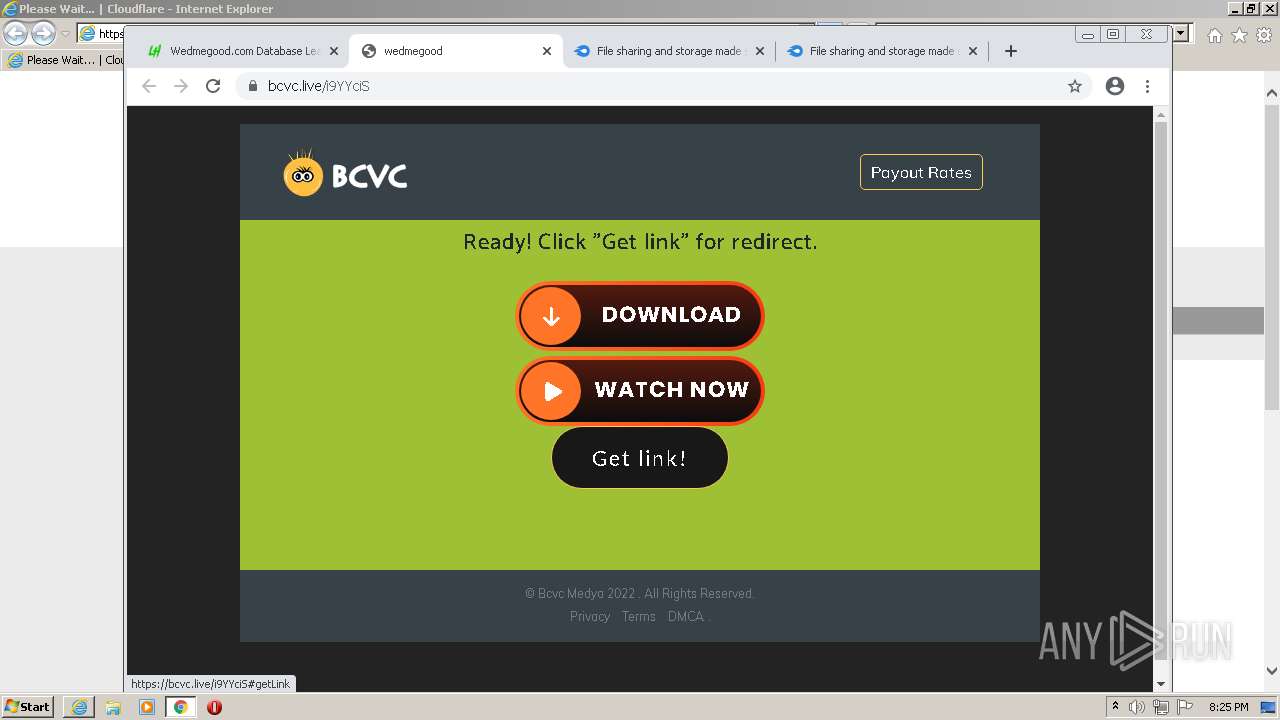
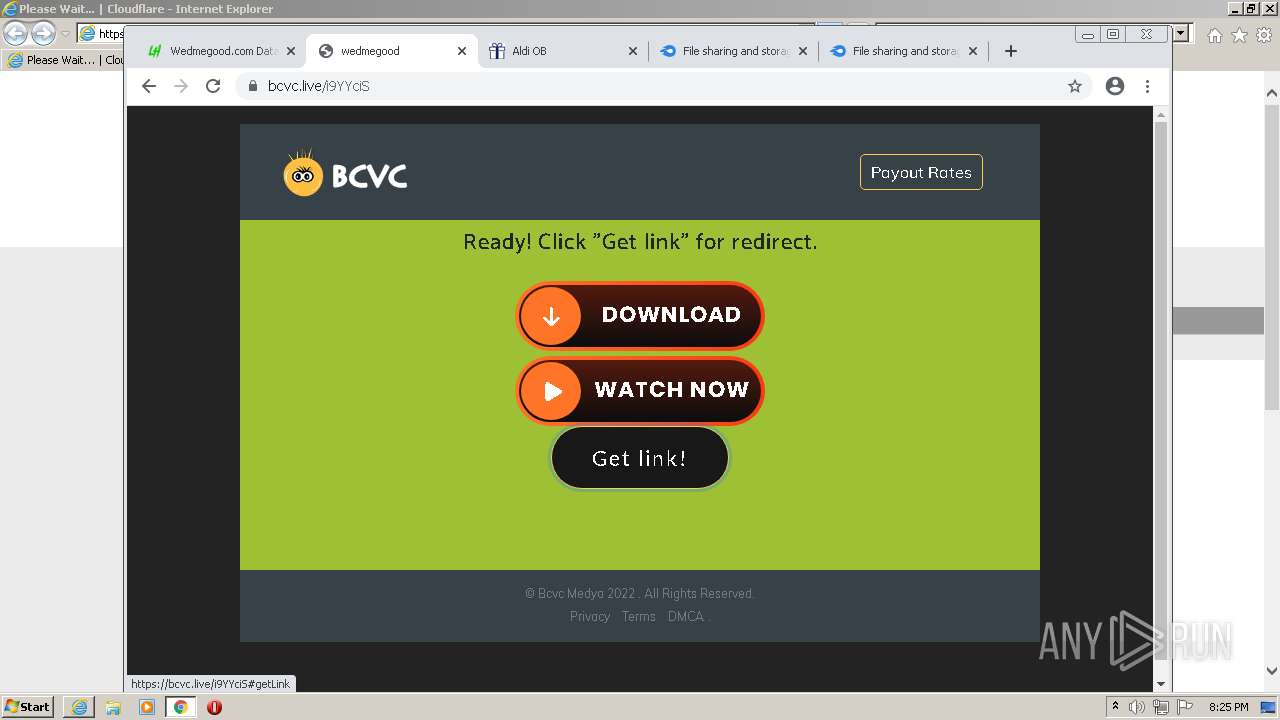
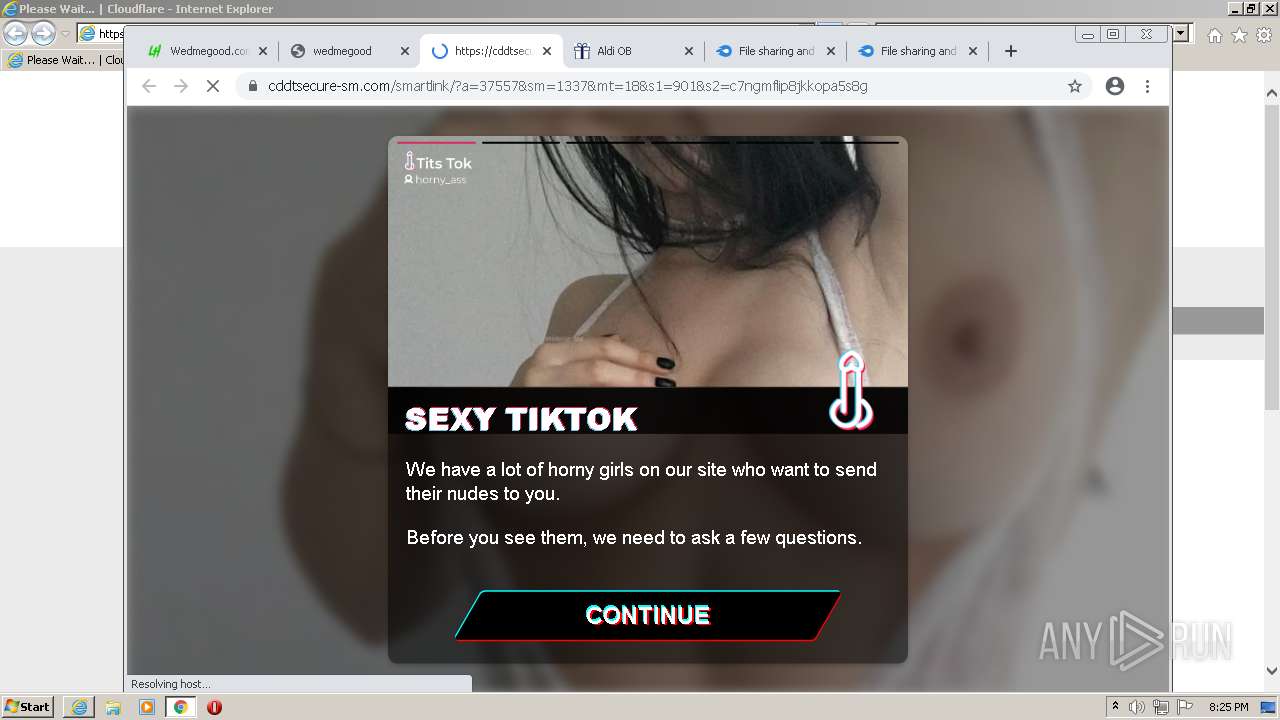
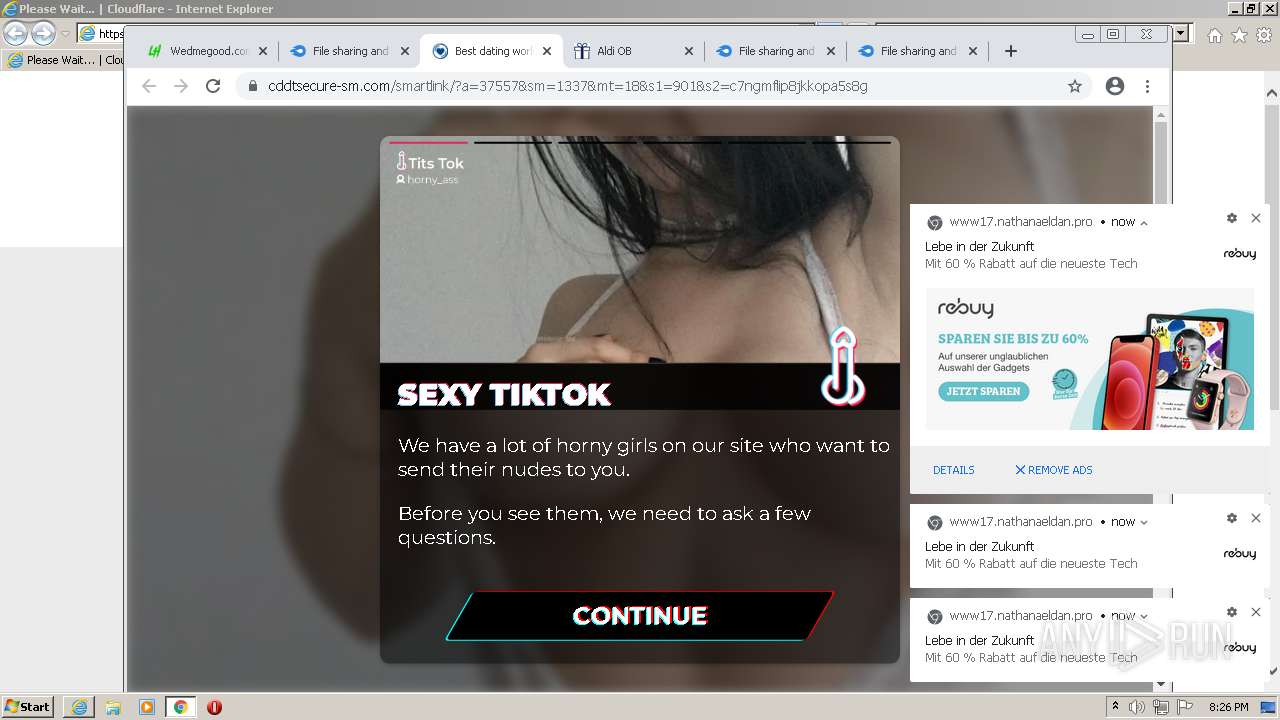
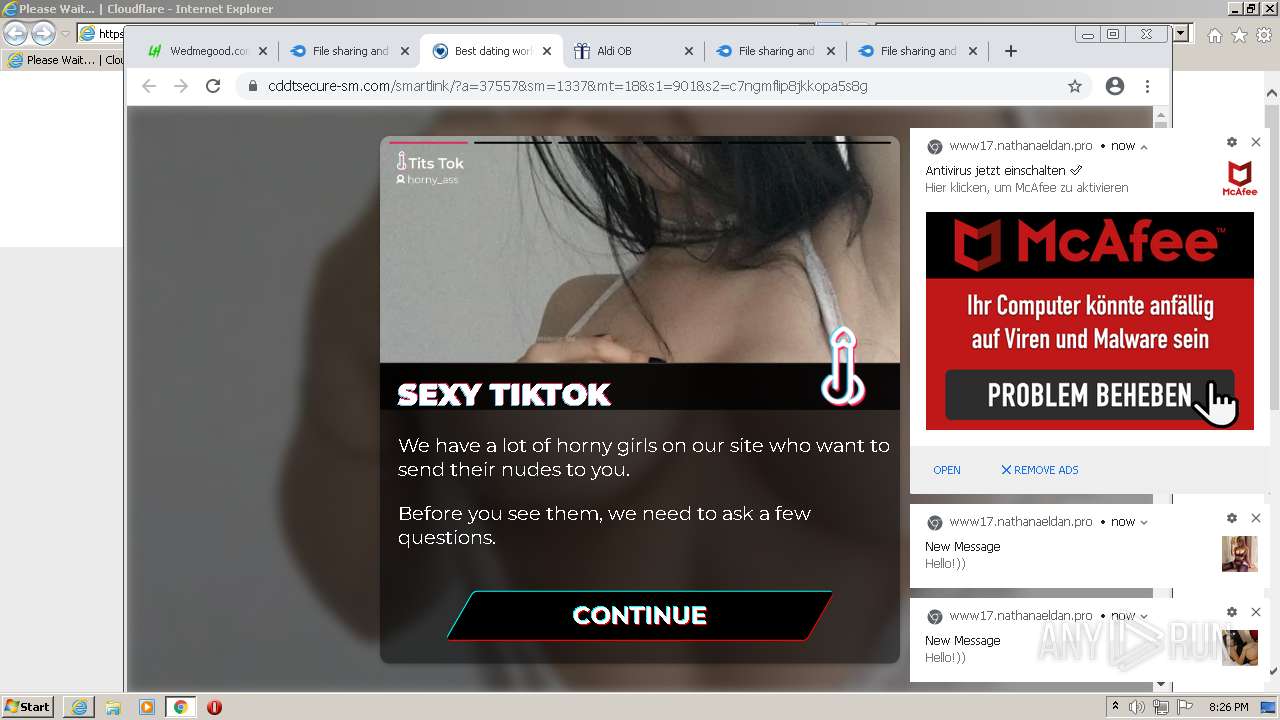
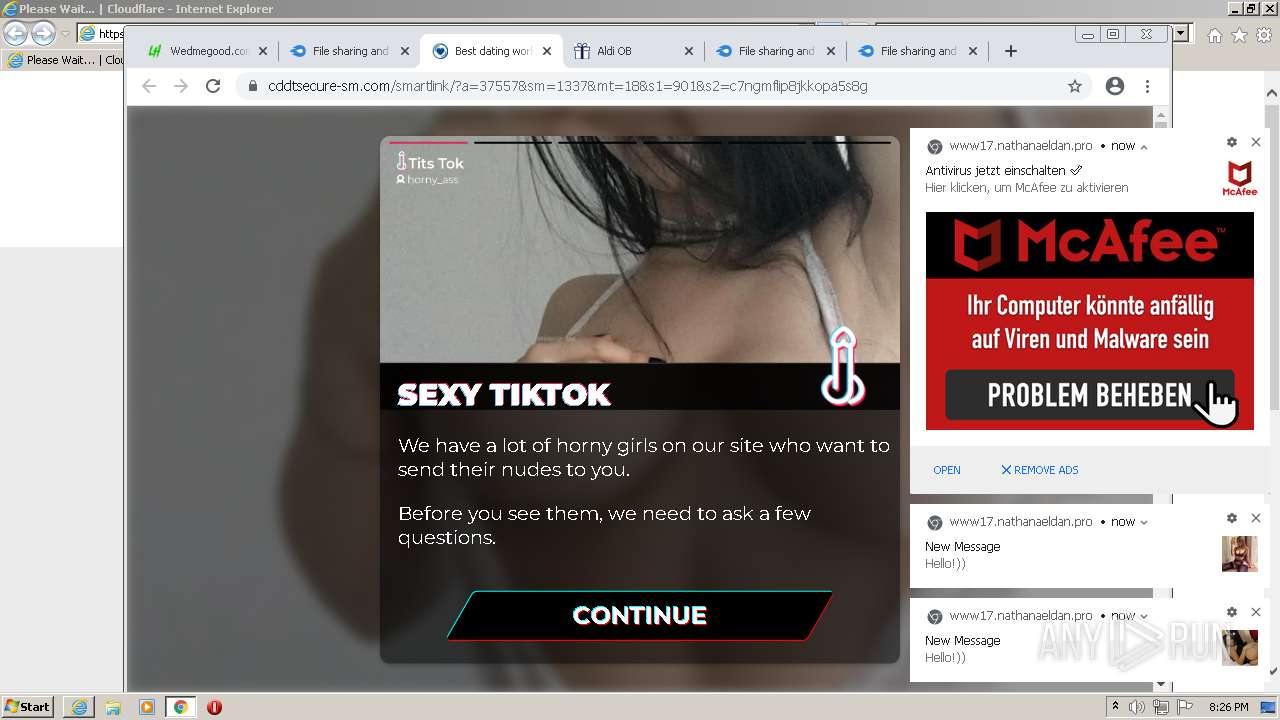
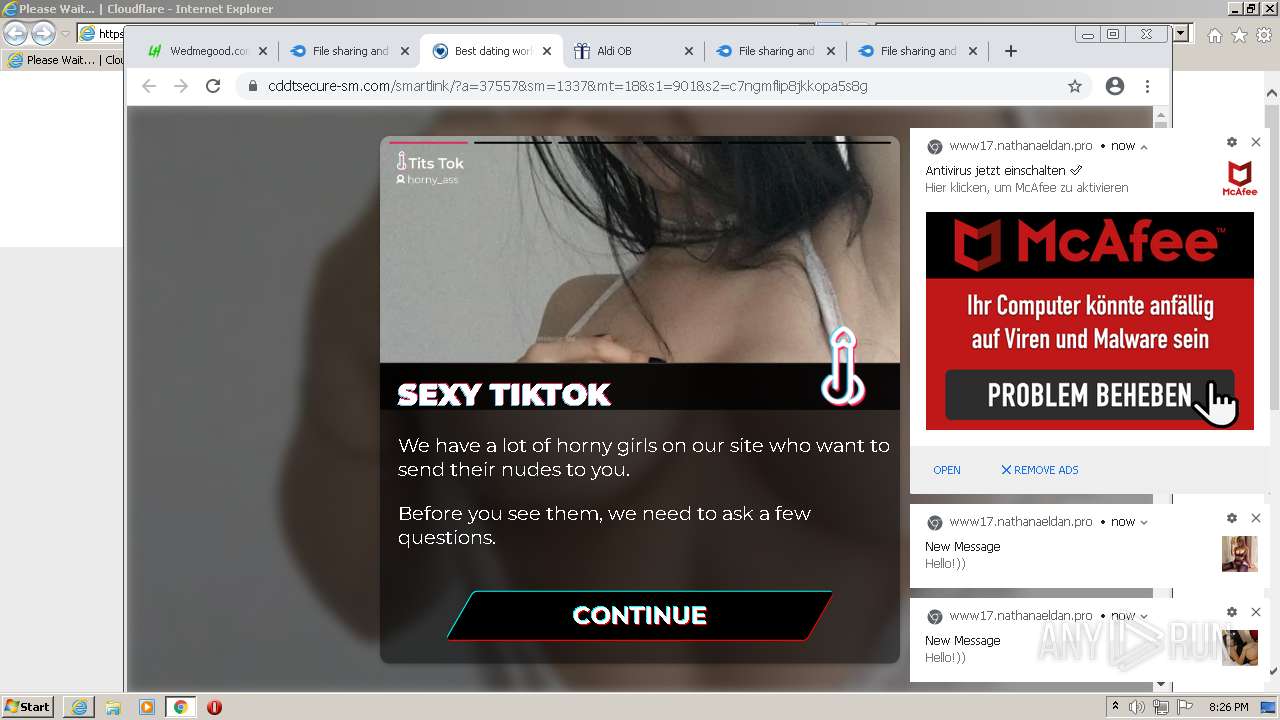
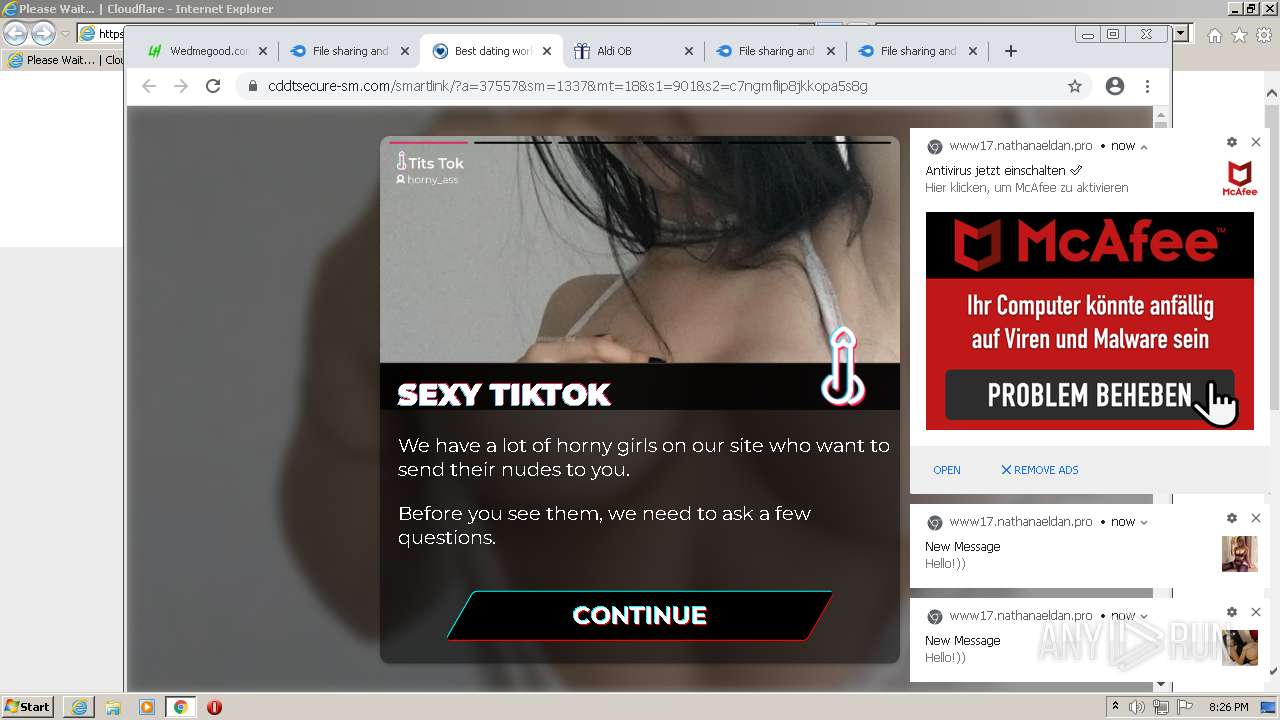
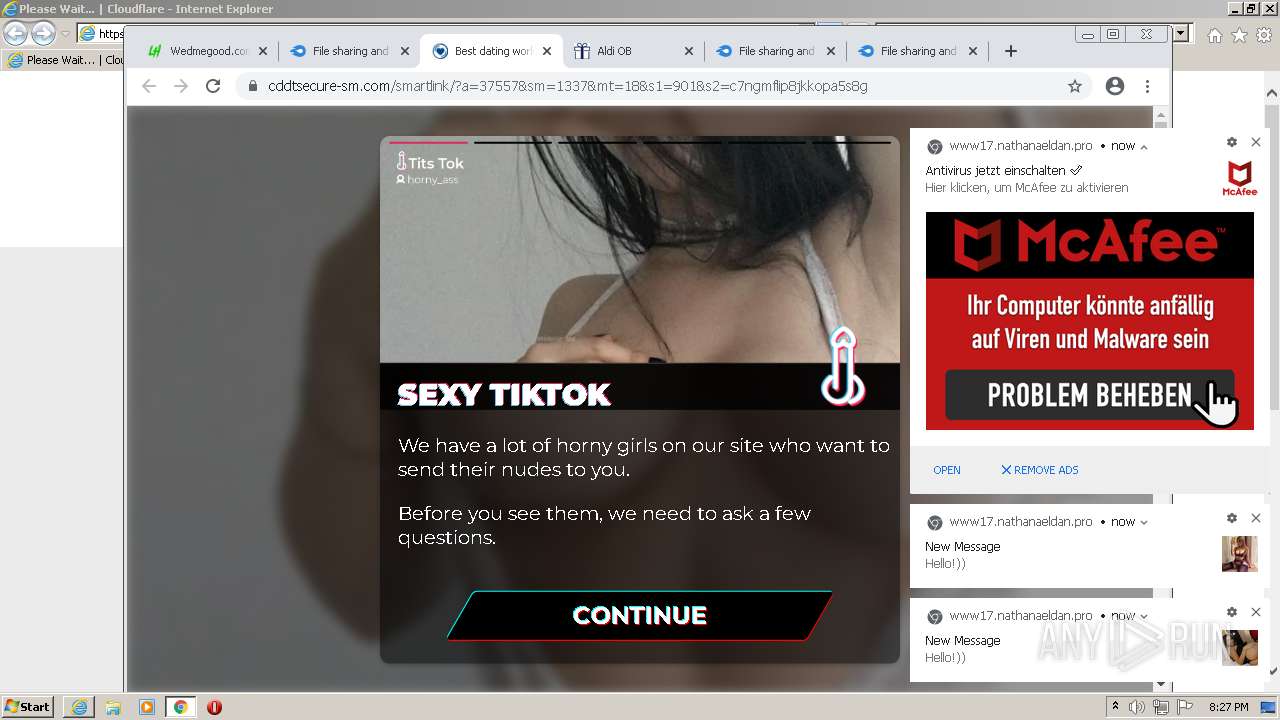
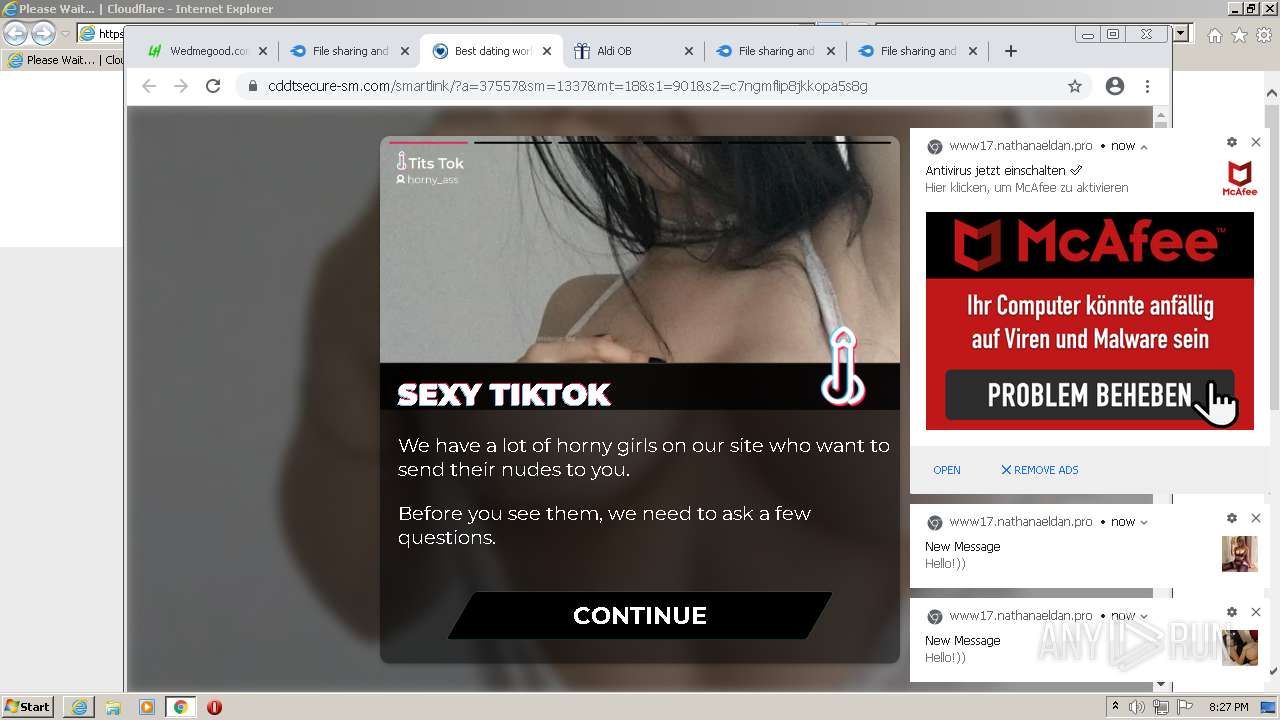
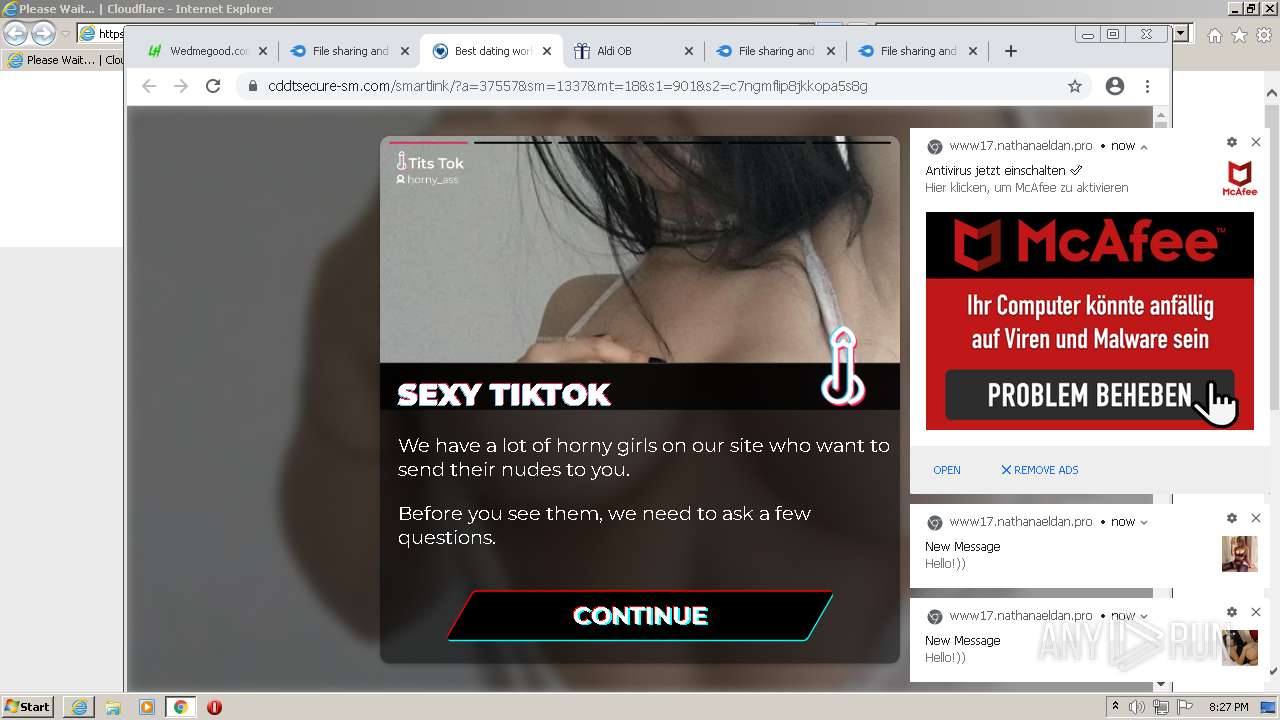
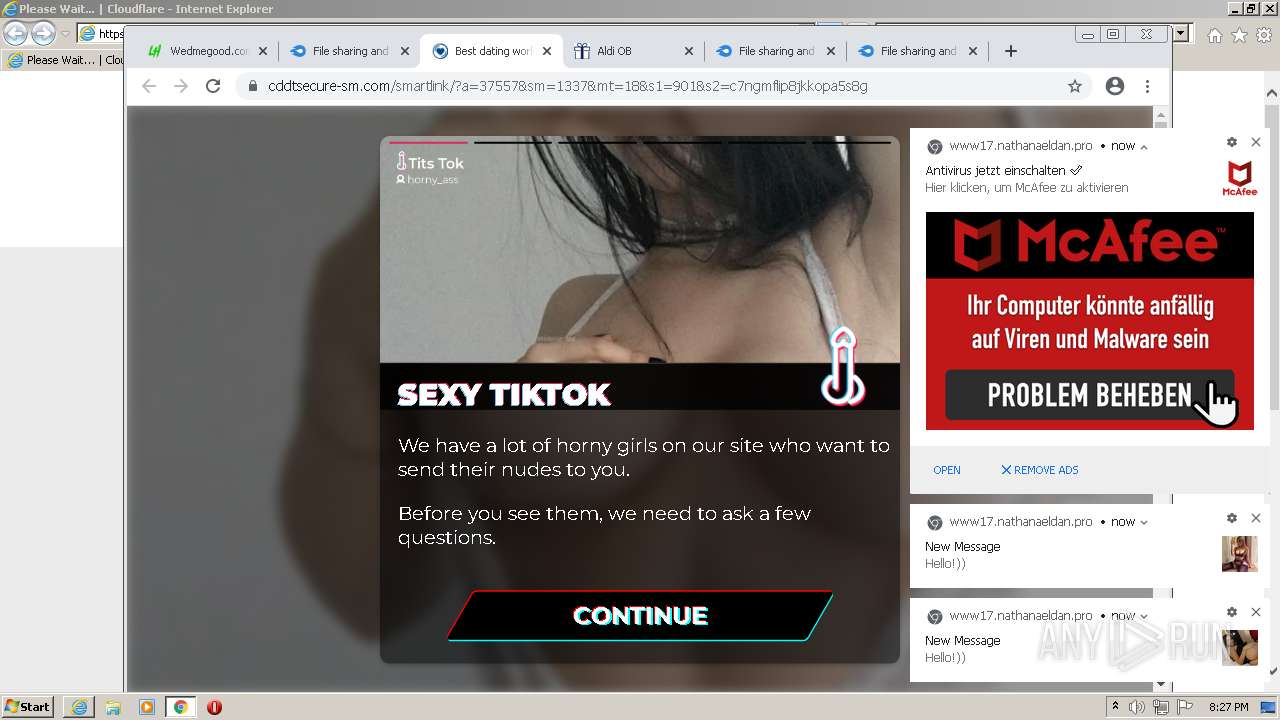
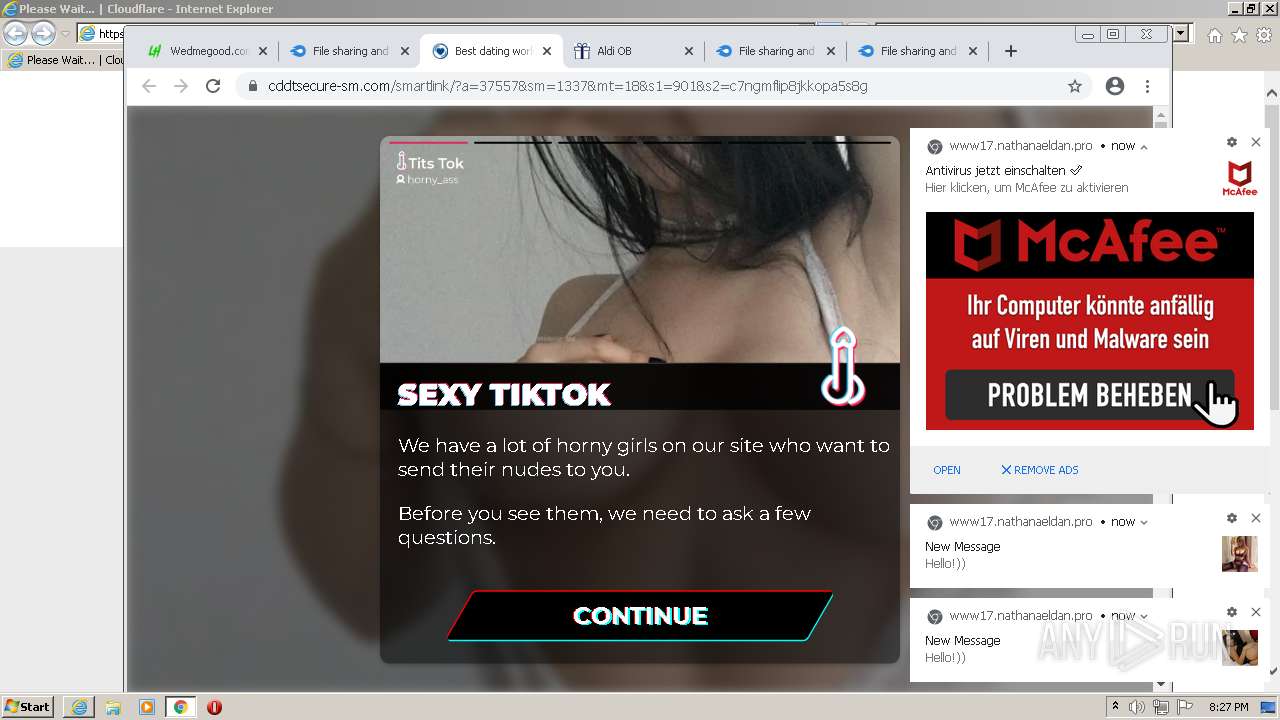
| URL: | https://leakhispano.net/d/2879-wedmegoodcom-database-leaked-may-2021-free-download |
| Full analysis: | https://app.any.run/tasks/ef7f7cf5-6d5d-49dc-a910-d8c847dc4d44 |
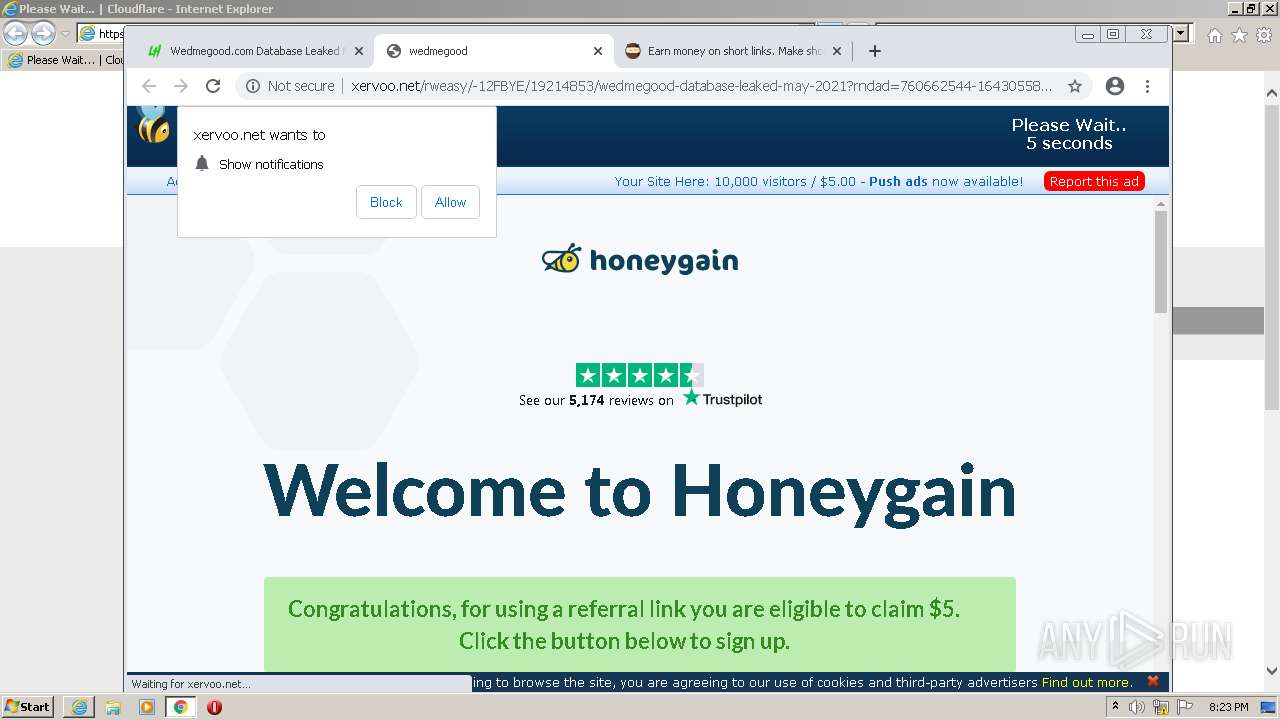
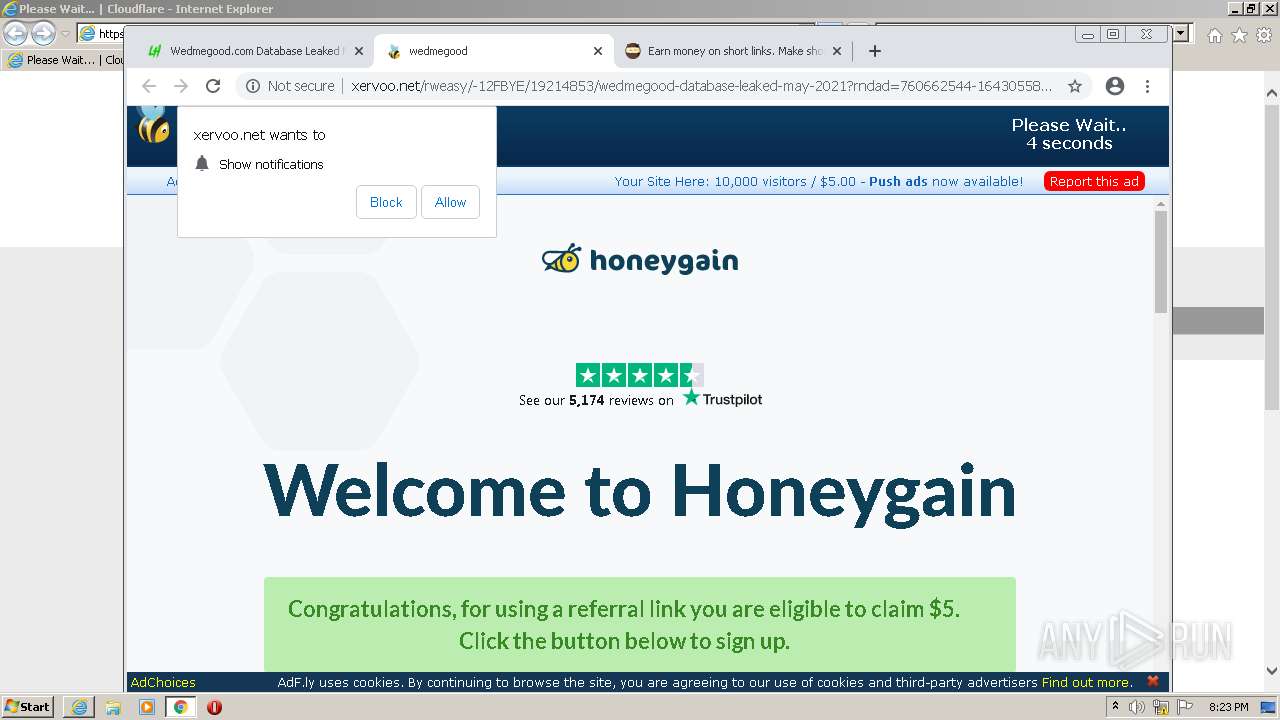
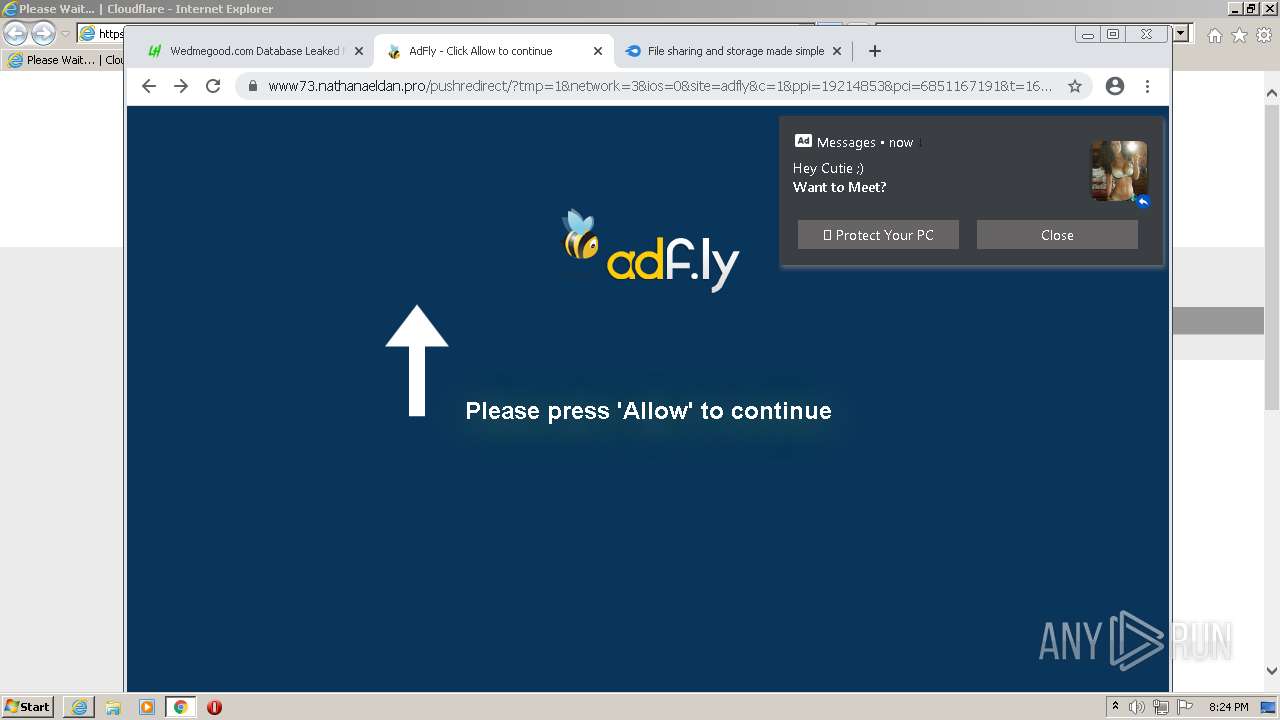
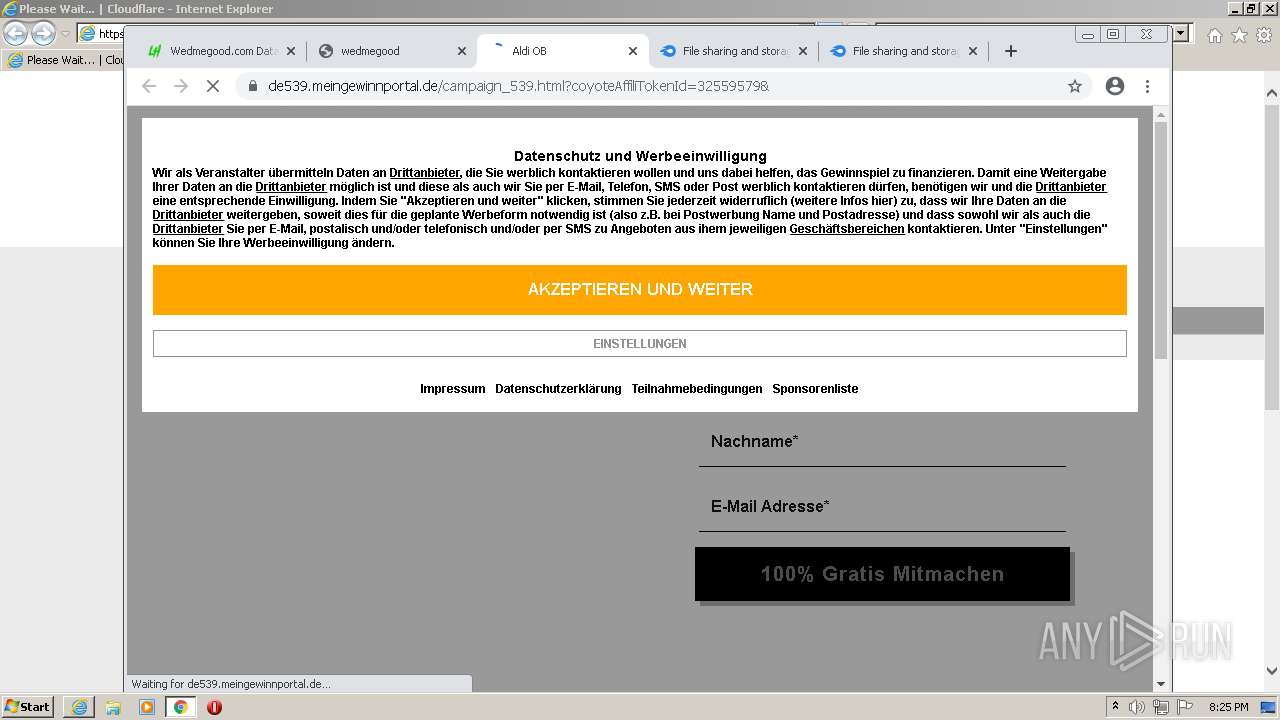
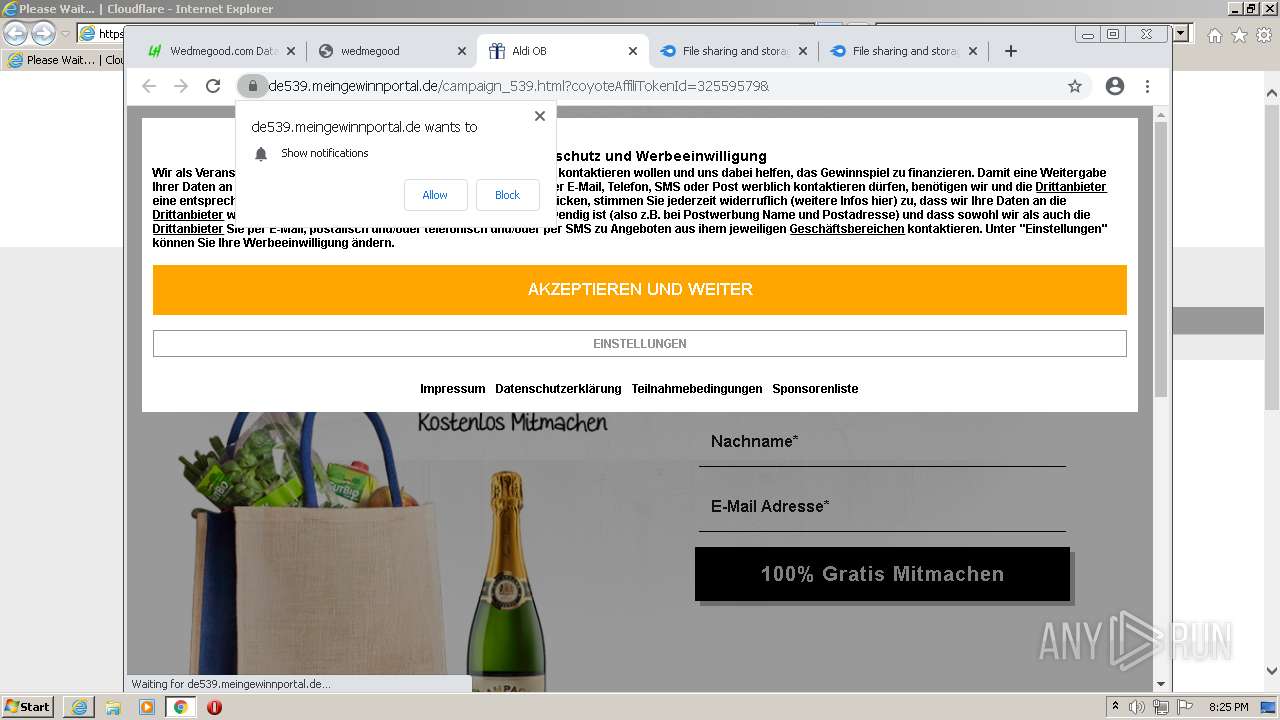
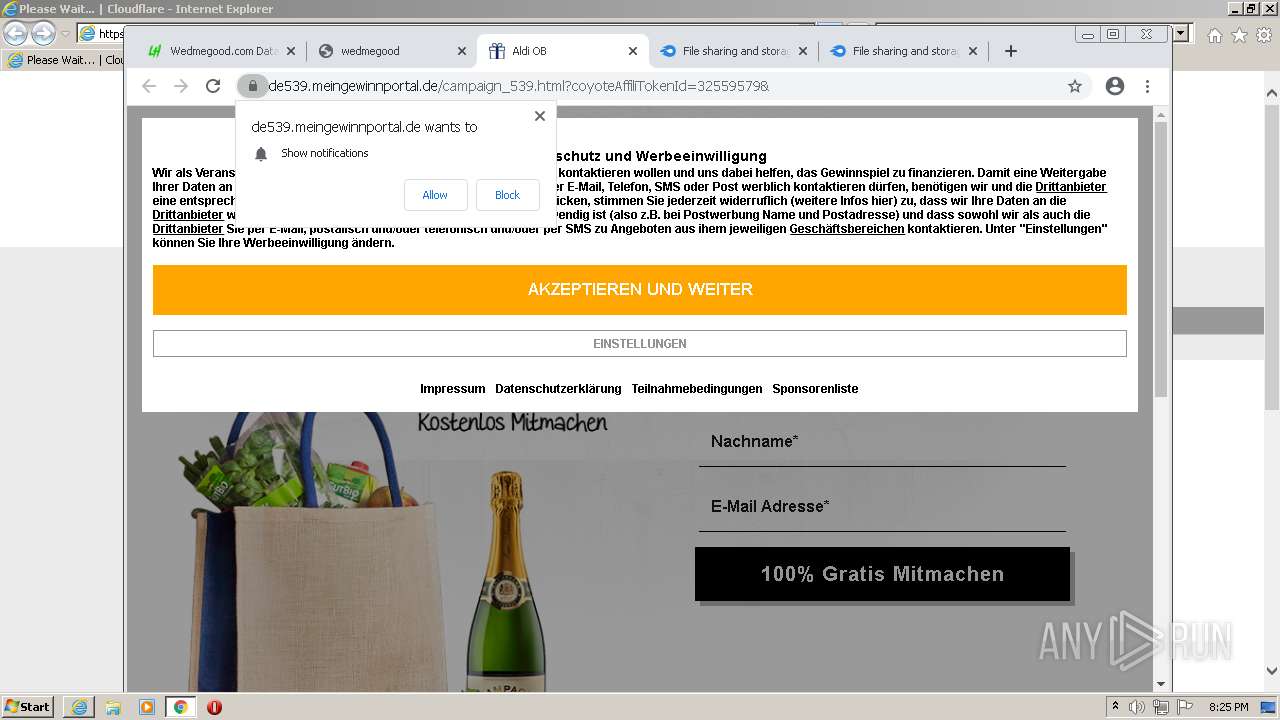
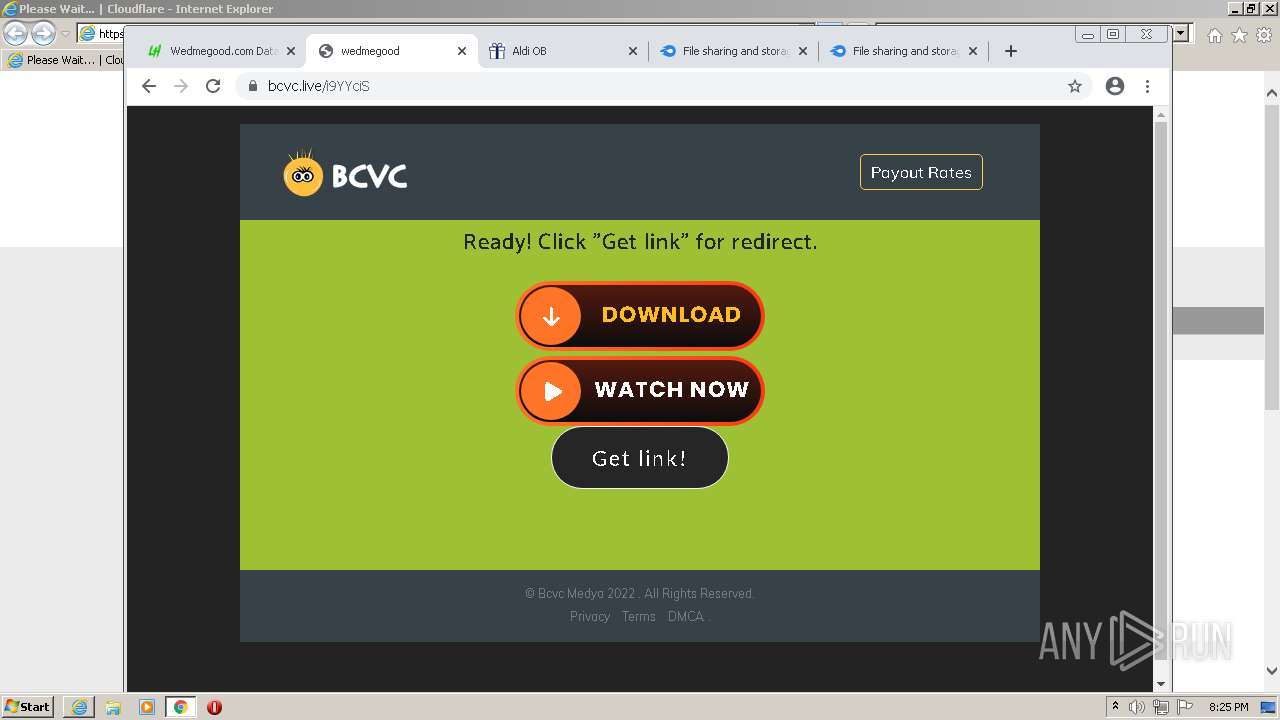
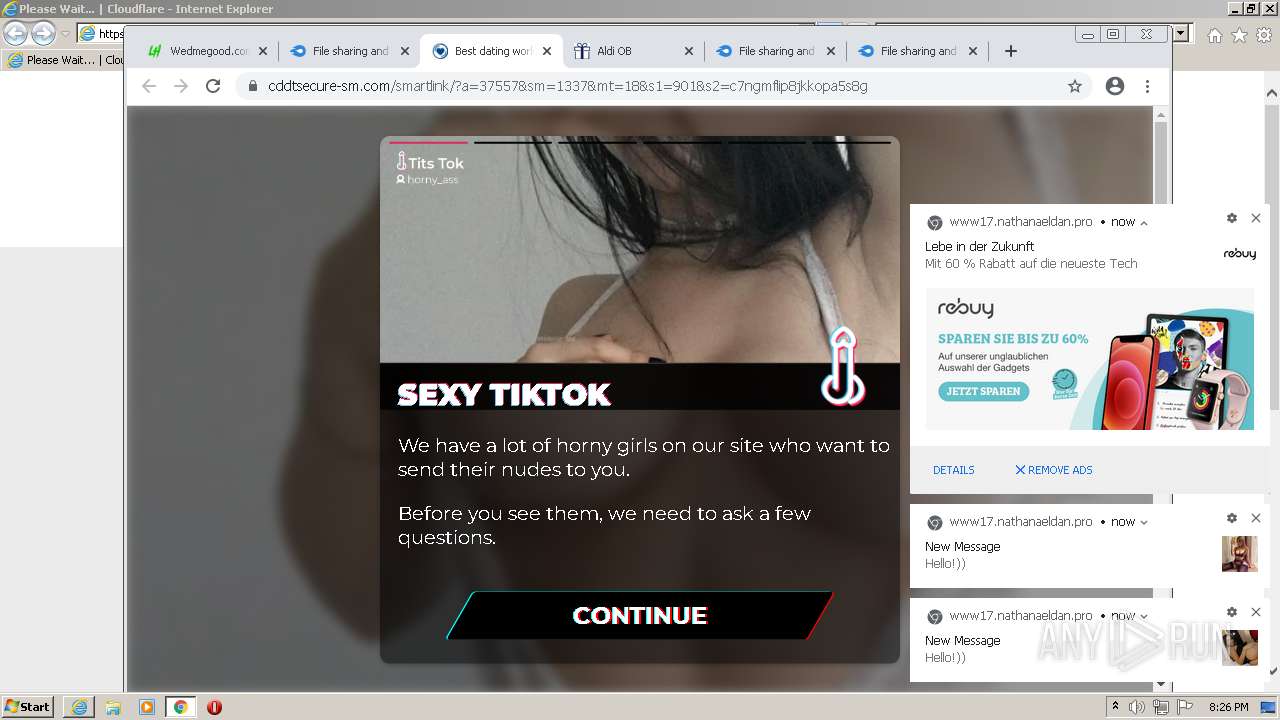
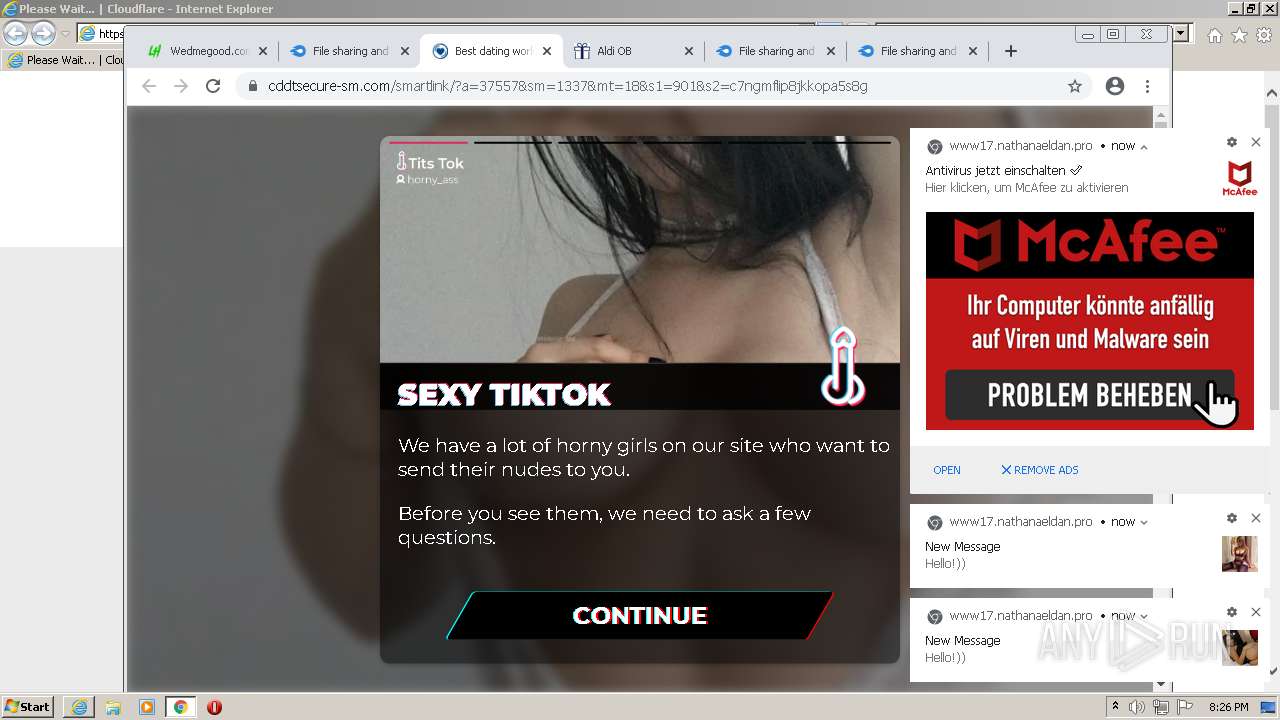
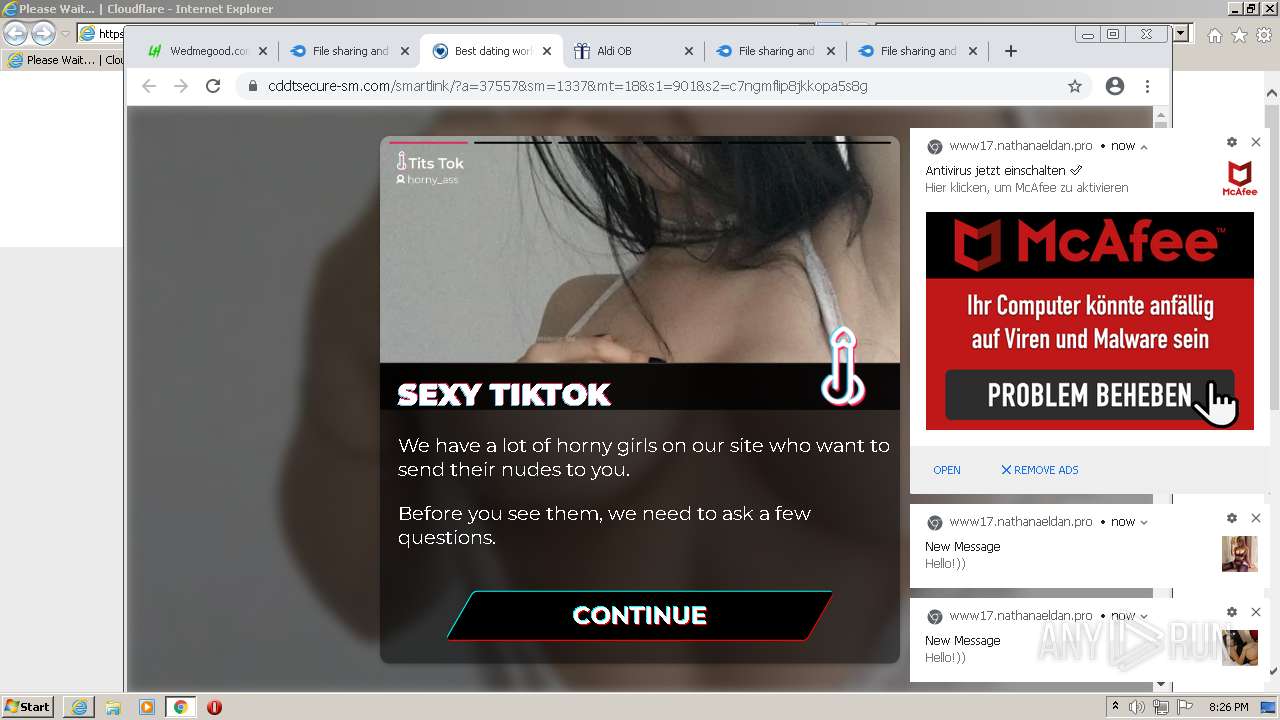
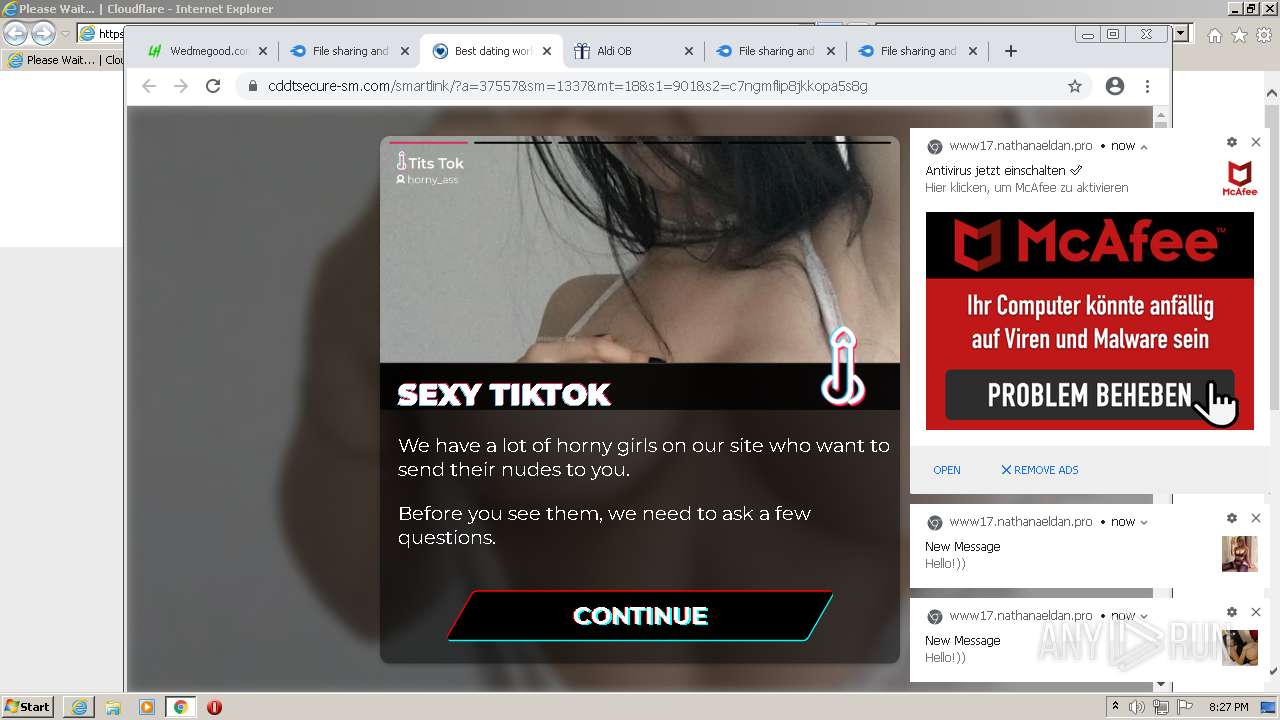
| Verdict: | Malicious activity |
| Analysis date: | January 24, 2022, 20:22:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C3E4486A945DC7CD60C0384DA25FA37F |
| SHA1: | C8E7A7ED1F3F47EE6CE3E1AFC8C187AAF8FB99D0 |
| SHA256: | 91E4A243A00D9BA722D1C4BB770DB4B1E3500318D2BE154C6C4A400DFC44258C |
| SSDEEP: | 3:N8AEvS98XJpWEVaABI5J2IWBFz:2AEzXzWhB5JvWj |
MALICIOUS
Connects to CnC server
- chrome.exe (PID: 3048)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3892)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1864)
Drops a file with a compile date too recent
- chrome.exe (PID: 1864)
INFO
Reads the computer name
- iexplore.exe (PID: 3012)
- iexplore.exe (PID: 3892)
- chrome.exe (PID: 1864)
- chrome.exe (PID: 3048)
- chrome.exe (PID: 1792)
- chrome.exe (PID: 3656)
- chrome.exe (PID: 3220)
- chrome.exe (PID: 2756)
- chrome.exe (PID: 1920)
- chrome.exe (PID: 3464)
- chrome.exe (PID: 3588)
- chrome.exe (PID: 2972)
- chrome.exe (PID: 2980)
Checks supported languages
- iexplore.exe (PID: 3012)
- iexplore.exe (PID: 3892)
- chrome.exe (PID: 1864)
- chrome.exe (PID: 2788)
- chrome.exe (PID: 3048)
- chrome.exe (PID: 1792)
- chrome.exe (PID: 4048)
- chrome.exe (PID: 484)
- chrome.exe (PID: 3944)
- chrome.exe (PID: 3576)
- chrome.exe (PID: 3476)
- chrome.exe (PID: 3656)
- chrome.exe (PID: 3220)
- chrome.exe (PID: 3748)
- chrome.exe (PID: 2756)
- chrome.exe (PID: 2512)
- chrome.exe (PID: 2328)
- chrome.exe (PID: 304)
- chrome.exe (PID: 3268)
- chrome.exe (PID: 2004)
- chrome.exe (PID: 2400)
- chrome.exe (PID: 1444)
- chrome.exe (PID: 3832)
- chrome.exe (PID: 3104)
- chrome.exe (PID: 1920)
- chrome.exe (PID: 3464)
- chrome.exe (PID: 3400)
- chrome.exe (PID: 756)
- chrome.exe (PID: 3184)
- chrome.exe (PID: 3856)
- chrome.exe (PID: 684)
- chrome.exe (PID: 2600)
- chrome.exe (PID: 860)
- chrome.exe (PID: 3716)
- chrome.exe (PID: 3820)
- chrome.exe (PID: 1284)
- chrome.exe (PID: 2060)
- chrome.exe (PID: 1108)
- chrome.exe (PID: 2796)
- chrome.exe (PID: 352)
- chrome.exe (PID: 3588)
- chrome.exe (PID: 928)
- chrome.exe (PID: 1344)
- chrome.exe (PID: 3572)
- chrome.exe (PID: 1984)
- chrome.exe (PID: 2428)
- chrome.exe (PID: 2980)
- chrome.exe (PID: 1112)
- chrome.exe (PID: 2212)
- chrome.exe (PID: 2972)
- chrome.exe (PID: 2360)
- chrome.exe (PID: 548)
- chrome.exe (PID: 2792)
- chrome.exe (PID: 872)
- chrome.exe (PID: 2480)
- chrome.exe (PID: 4076)
- chrome.exe (PID: 572)
- chrome.exe (PID: 628)
- chrome.exe (PID: 2960)
- chrome.exe (PID: 2276)
- chrome.exe (PID: 2664)
- chrome.exe (PID: 2032)
- chrome.exe (PID: 2584)
- chrome.exe (PID: 1592)
- chrome.exe (PID: 4048)
- chrome.exe (PID: 3936)
- chrome.exe (PID: 3464)
- chrome.exe (PID: 3388)
- chrome.exe (PID: 1924)
Application launched itself
- iexplore.exe (PID: 3012)
- chrome.exe (PID: 1864)
Changes internet zones settings
- iexplore.exe (PID: 3012)
Checks Windows Trust Settings
- iexplore.exe (PID: 3012)
- iexplore.exe (PID: 3892)
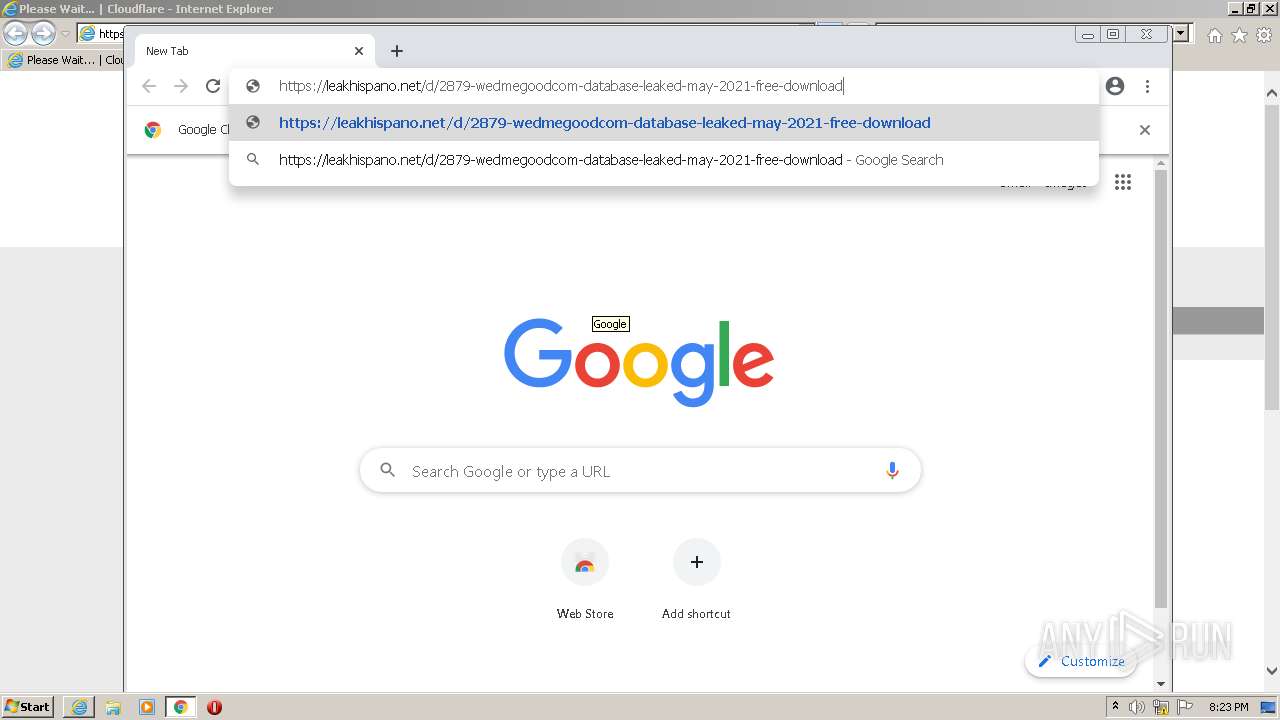
Manual execution by user
- chrome.exe (PID: 1864)
Reads internet explorer settings
- iexplore.exe (PID: 3892)
Reads settings of System Certificates
- iexplore.exe (PID: 3012)
- chrome.exe (PID: 3048)
- iexplore.exe (PID: 3892)
Reads the hosts file
- chrome.exe (PID: 3048)
- chrome.exe (PID: 1864)
Creates files in the user directory
- iexplore.exe (PID: 3892)
- iexplore.exe (PID: 3012)
Changes settings of System certificates
- iexplore.exe (PID: 3012)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3012)
Reads the date of Windows installation
- chrome.exe (PID: 3464)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 1864)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
105
Monitored processes
69
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,3315253830100147579,17746079845989621163,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3500 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,3315253830100147579,17746079845989621163,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1668 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 484 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,3315253830100147579,17746079845989621163,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2252 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1056,3315253830100147579,17746079845989621163,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1124 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,3315253830100147579,17746079845989621163,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=54 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2336 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,3315253830100147579,17746079845989621163,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=55 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,3315253830100147579,17746079845989621163,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=30 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4028 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1056,3315253830100147579,17746079845989621163,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3740 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 860 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,3315253830100147579,17746079845989621163,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=32 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1572 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,3315253830100147579,17746079845989621163,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=52 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3884 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
35 095
Read events
34 767
Write events
318
Delete events
10
Modification events
| (PID) Process: | (3012) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3012) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 473477760 | |||
| (PID) Process: | (3012) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30937440 | |||
| (PID) Process: | (3012) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 773643385 | |||
| (PID) Process: | (3012) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30937440 | |||
| (PID) Process: | (3012) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3012) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3012) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3012) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3012) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
426
Text files
330
Unknown types
26
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61EF0A9B-748.pma | — | |
MD5:— | SHA256:— | |||
| 3012 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 3012 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3012 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 3048 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\index | binary | |
MD5:— | SHA256:— | |||
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 3012 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 1864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 3012 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 1864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF11a277.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
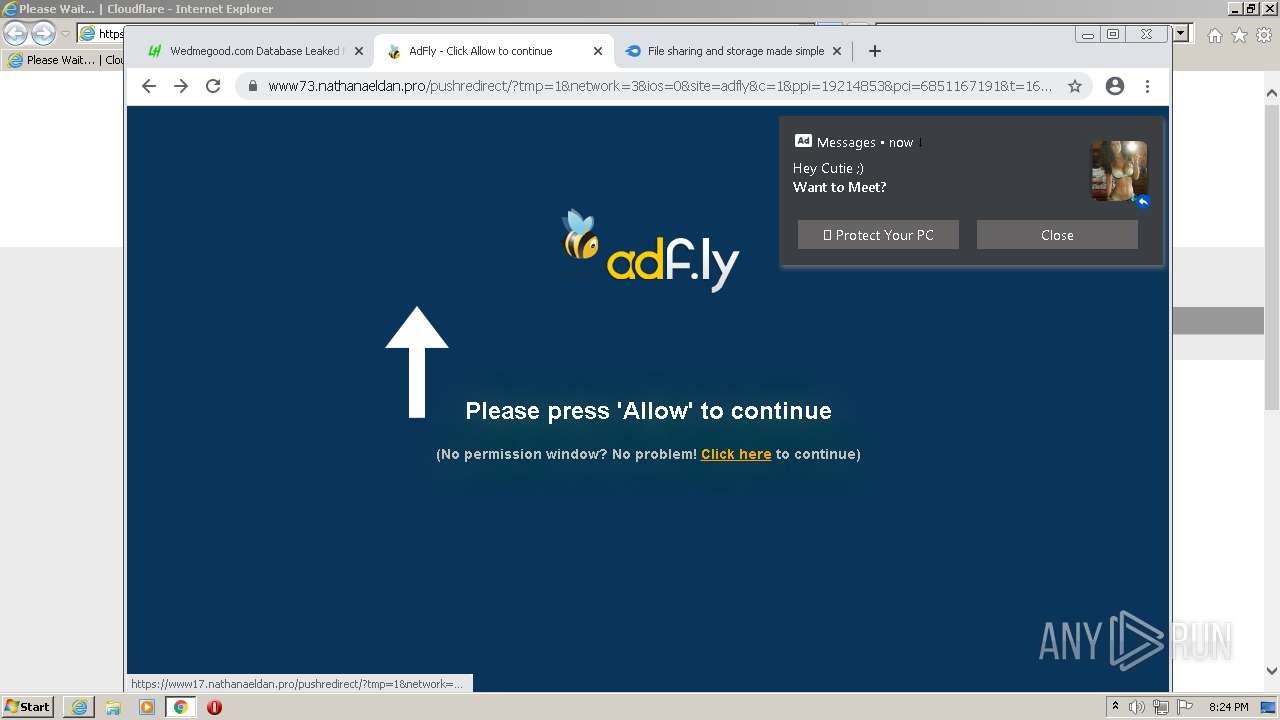
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
94
TCP/UDP connections
236
DNS requests
169
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
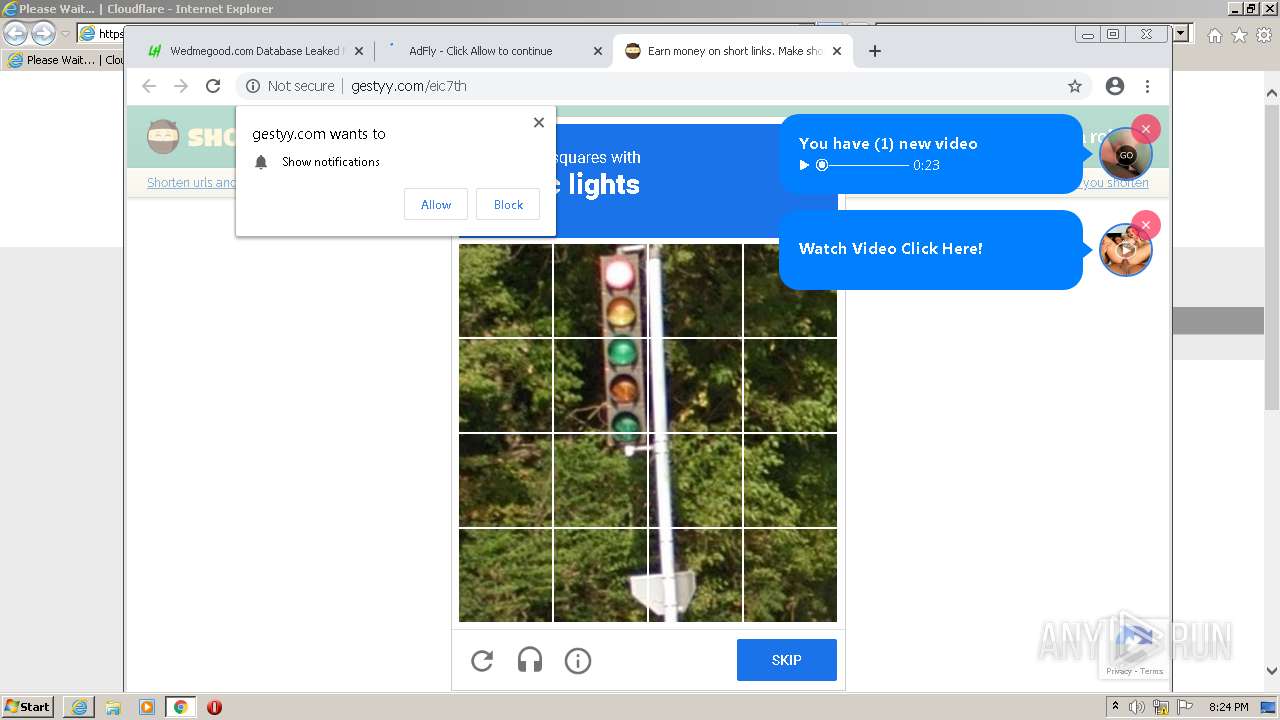
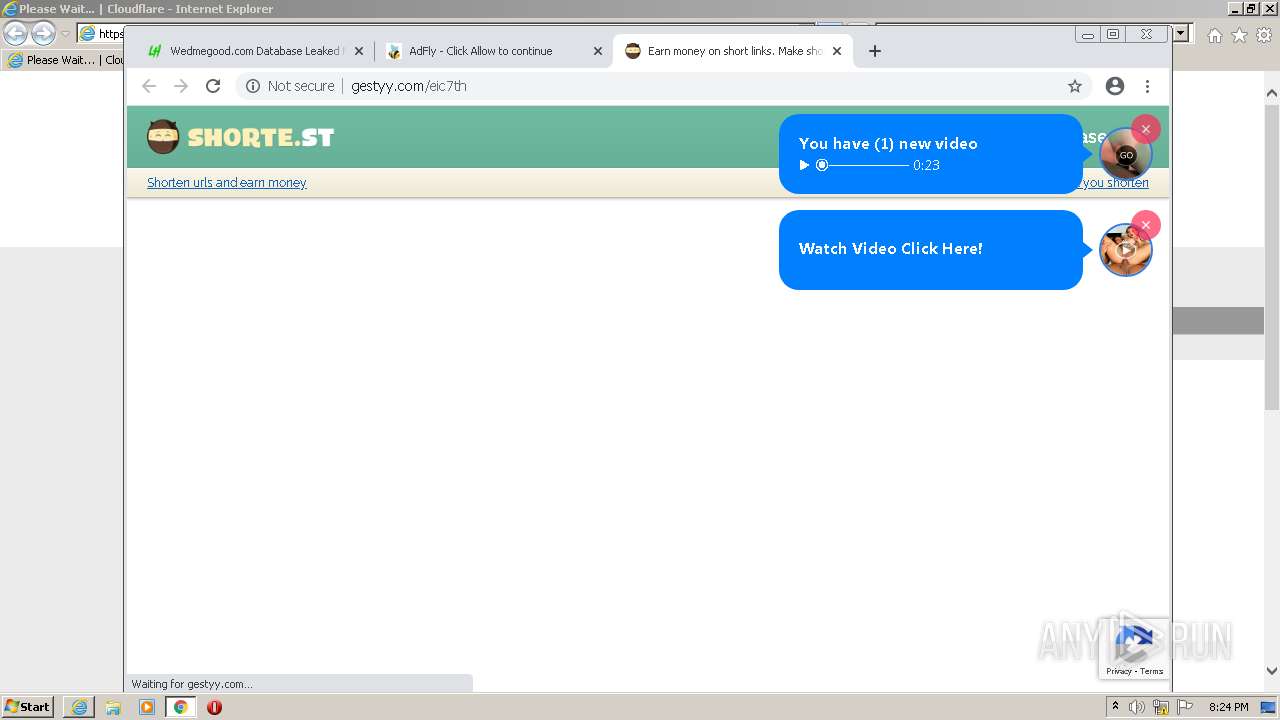
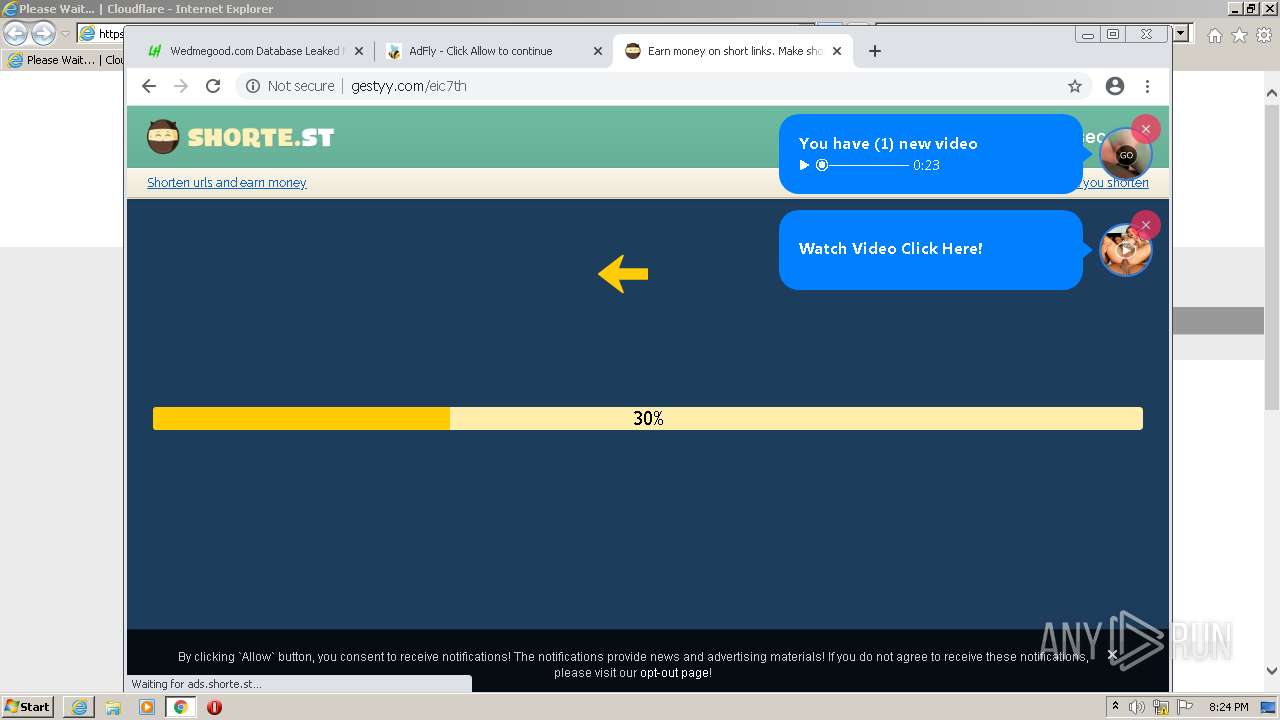
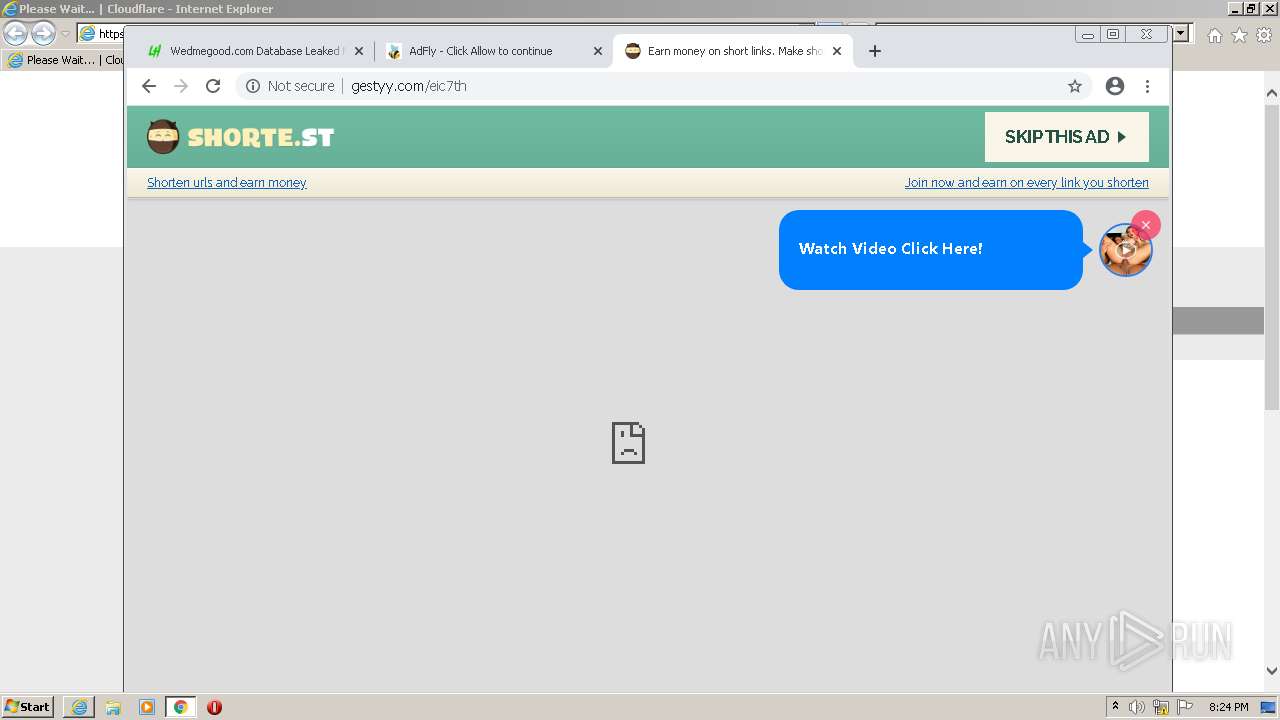
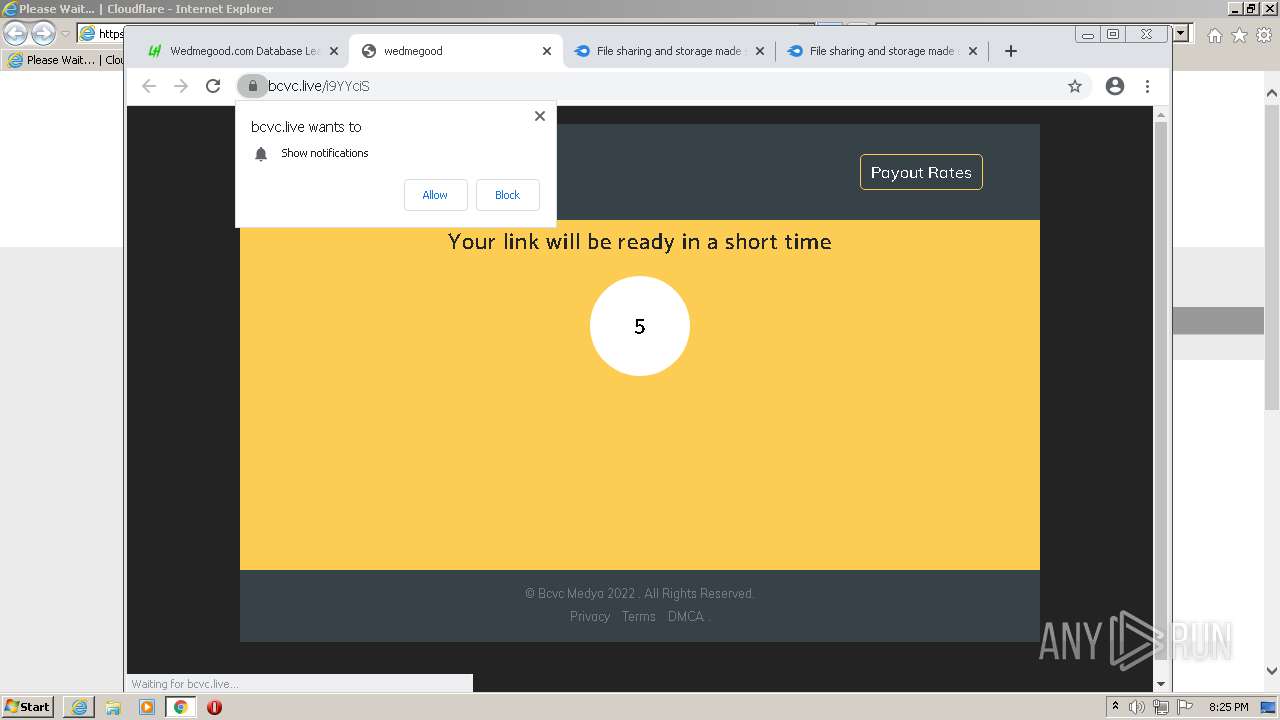
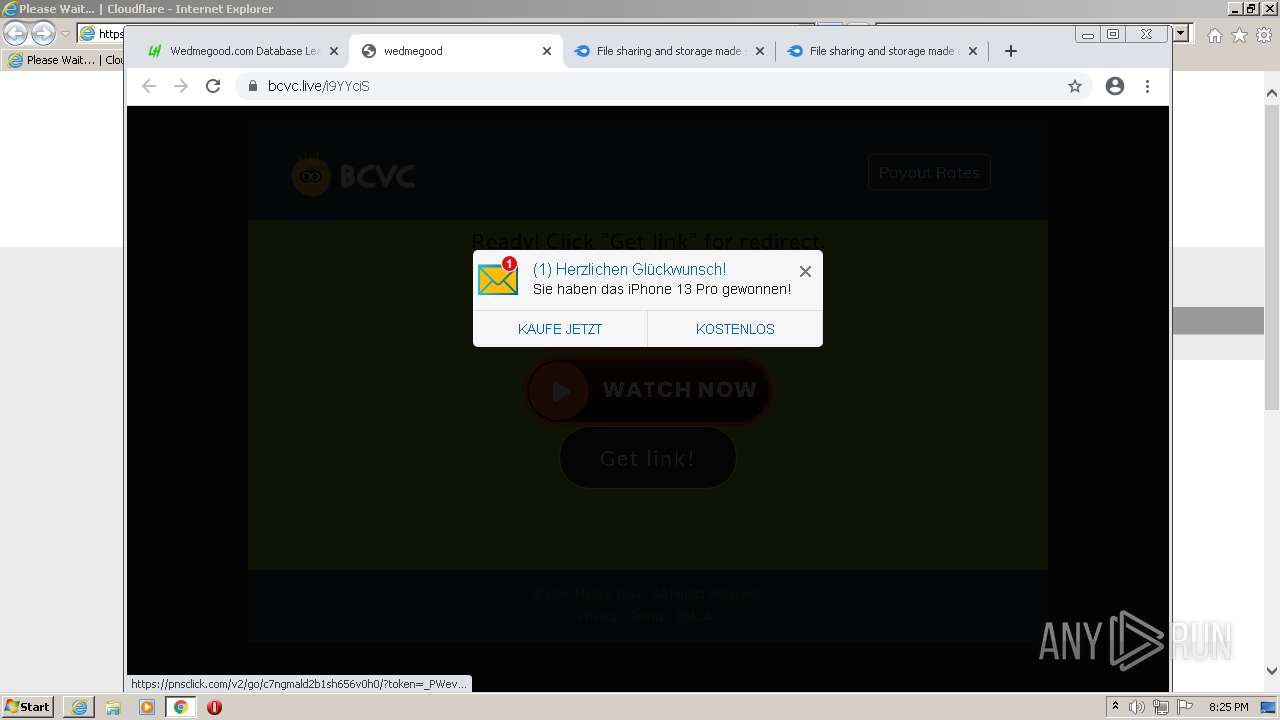
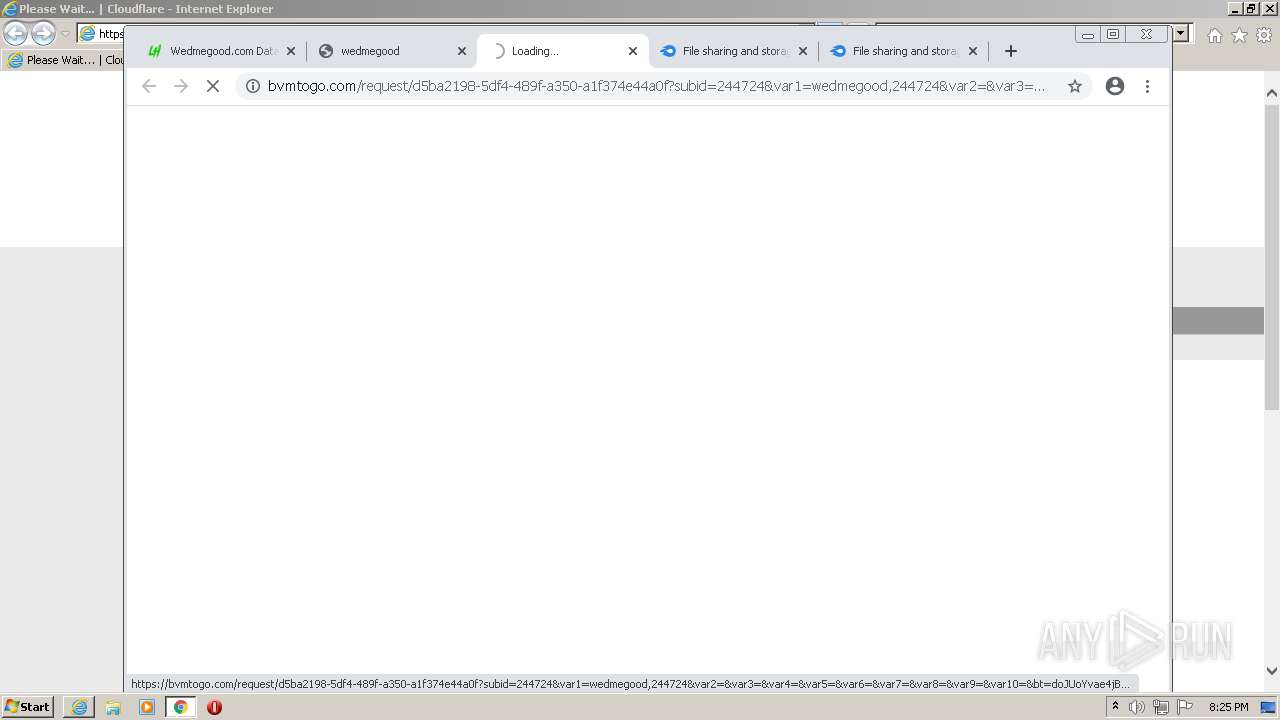
3048 | chrome.exe | GET | 200 | 172.67.68.51:80 | http://gestyy.com/bundles/advertisement/img/tracking.gif?test=49b0535210481c53646be1e8f90d8798b4775f1b | US | — | — | whitelisted |
3048 | chrome.exe | GET | 403 | 192.243.59.20:80 | http://attendedimitationsurrender.com/59/9c/c8/599cc889b672d4d71332545891e4b532.js | US | — | — | malicious |
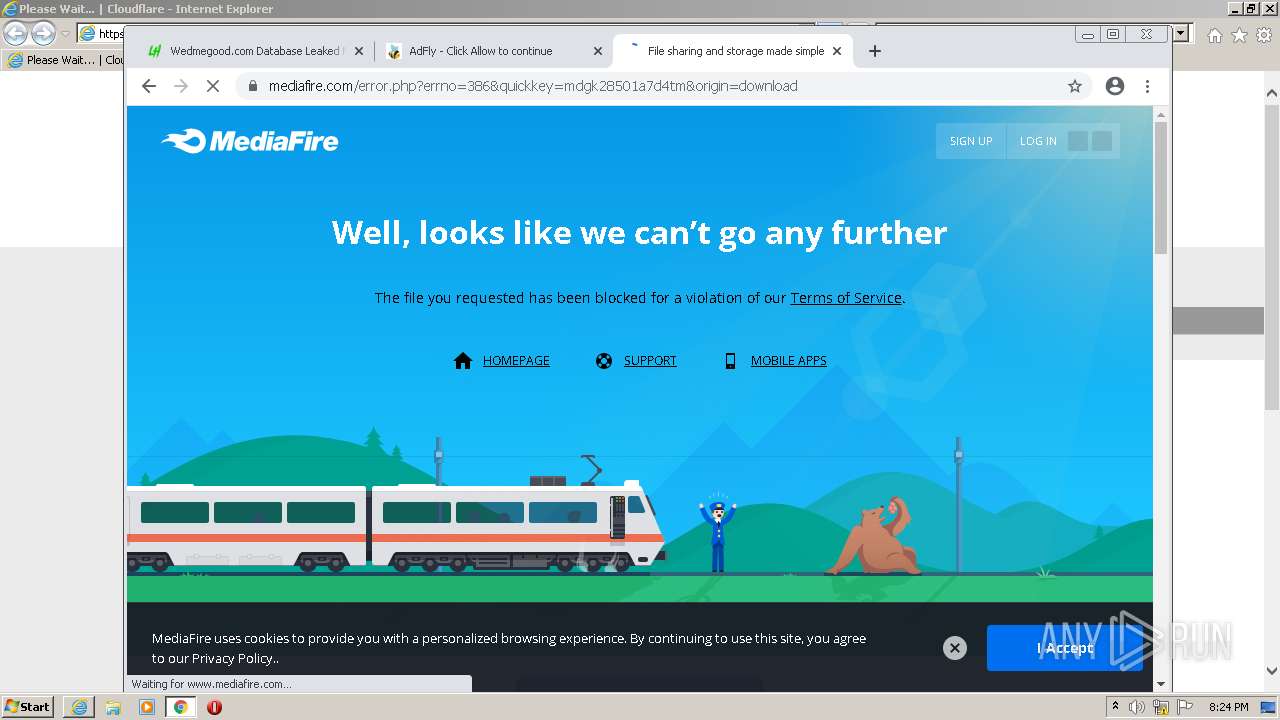
3048 | chrome.exe | GET | 301 | 104.21.5.11:80 | http://j.gs/19214853/wedmegood-database-leaked-may-2021 | US | — | — | malicious |
3892 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
3048 | chrome.exe | GET | 302 | 142.250.184.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 555 b | whitelisted |
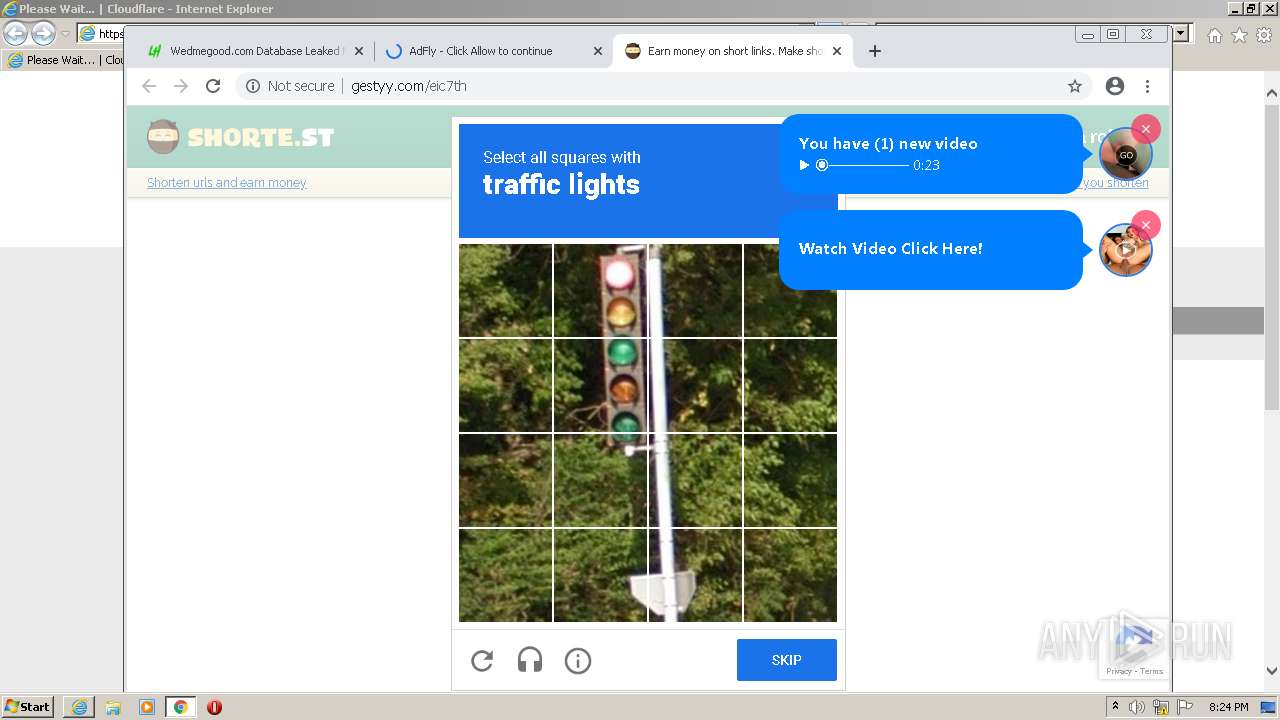
3048 | chrome.exe | GET | 200 | 172.67.68.51:80 | http://gestyy.com/eic7th | US | html | 25.6 Kb | whitelisted |
3048 | chrome.exe | GET | 200 | 172.67.68.250:80 | http://static.sh.st/js/packed/interstitial-page.js?2022-01-18.0 | US | text | 23.8 Kb | unknown |
3012 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
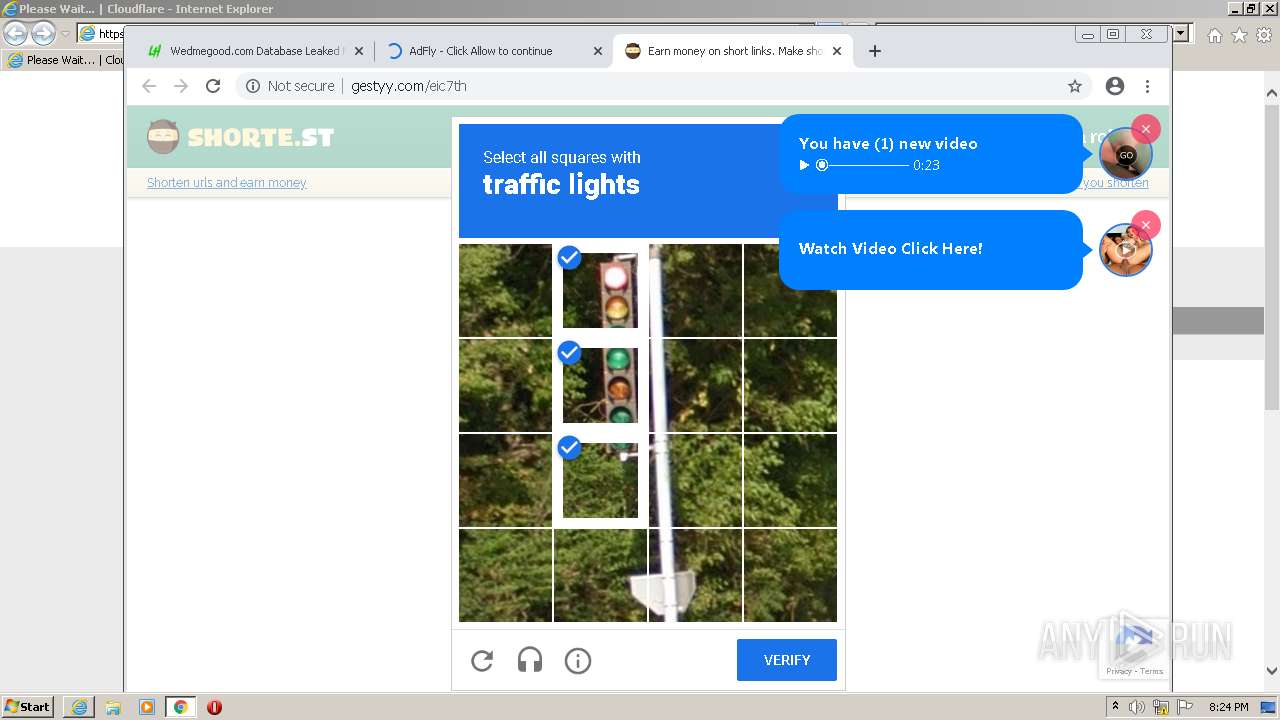
3048 | chrome.exe | OPTIONS | 403 | 104.26.5.107:80 | http://analytics.shorte.st/captcha-displayed | US | html | 1.28 Kb | whitelisted |
3048 | chrome.exe | OPTIONS | 403 | 104.26.5.107:80 | http://analytics.shorte.st/displayed | US | html | 1.28 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3012 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
3892 | iexplore.exe | 188.114.96.7:443 | leakhispano.net | Cloudflare Inc | US | malicious |
3012 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3048 | chrome.exe | 216.58.212.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3048 | chrome.exe | 142.250.185.237:443 | accounts.google.com | Google Inc. | US | suspicious |
3048 | chrome.exe | 142.250.185.78:443 | clients2.google.com | Google Inc. | US | whitelisted |
3048 | chrome.exe | 142.250.185.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3048 | chrome.exe | 142.250.185.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3048 | chrome.exe | 142.250.186.142:443 | apis.google.com | Google Inc. | US | whitelisted |
3892 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
leakhispano.net |
| malicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
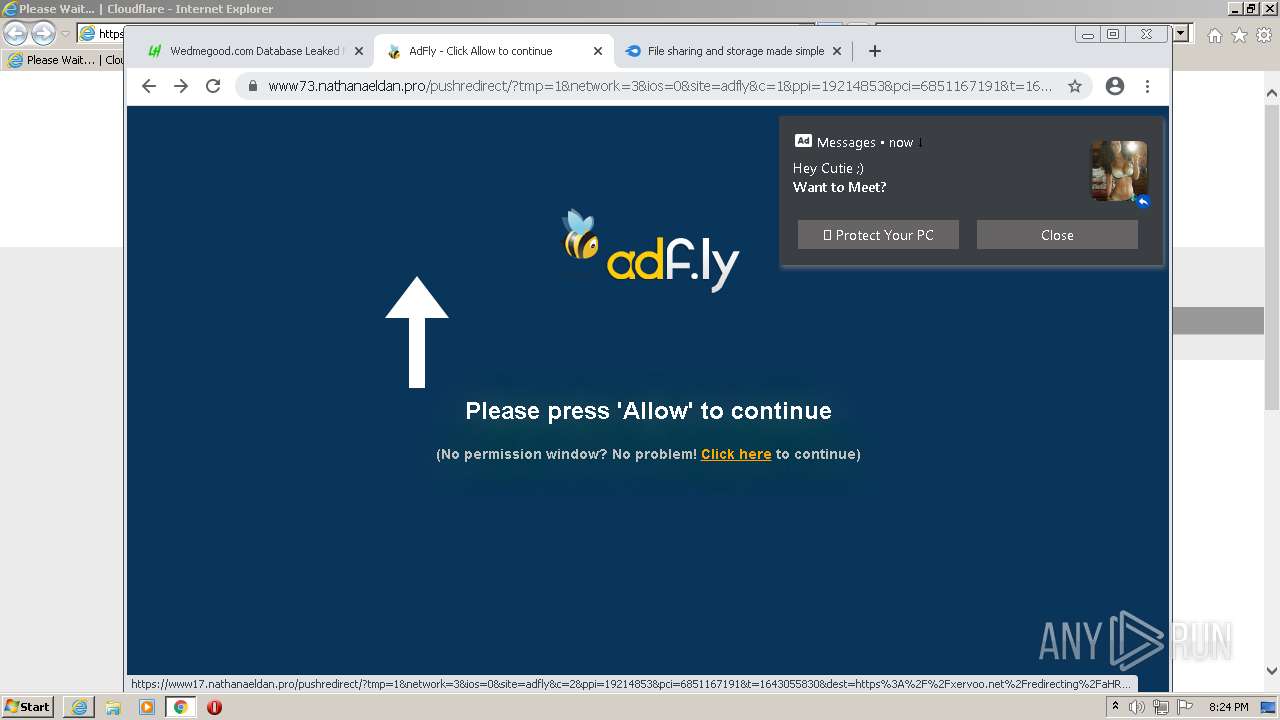
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET DNS Query for .to TLD |
3048 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
3048 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
3048 | chrome.exe | Misc Attack | ET Threatview.io High Confidence Cobalt Strike C2 IP group 1 |