| File name: | u.exe.6.dr |
| Full analysis: | https://app.any.run/tasks/667978dc-fe2f-468d-8e39-17cf0c5fb974 |
| Verdict: | Malicious activity |
| Analysis date: | May 01, 2021, 13:38:02 |
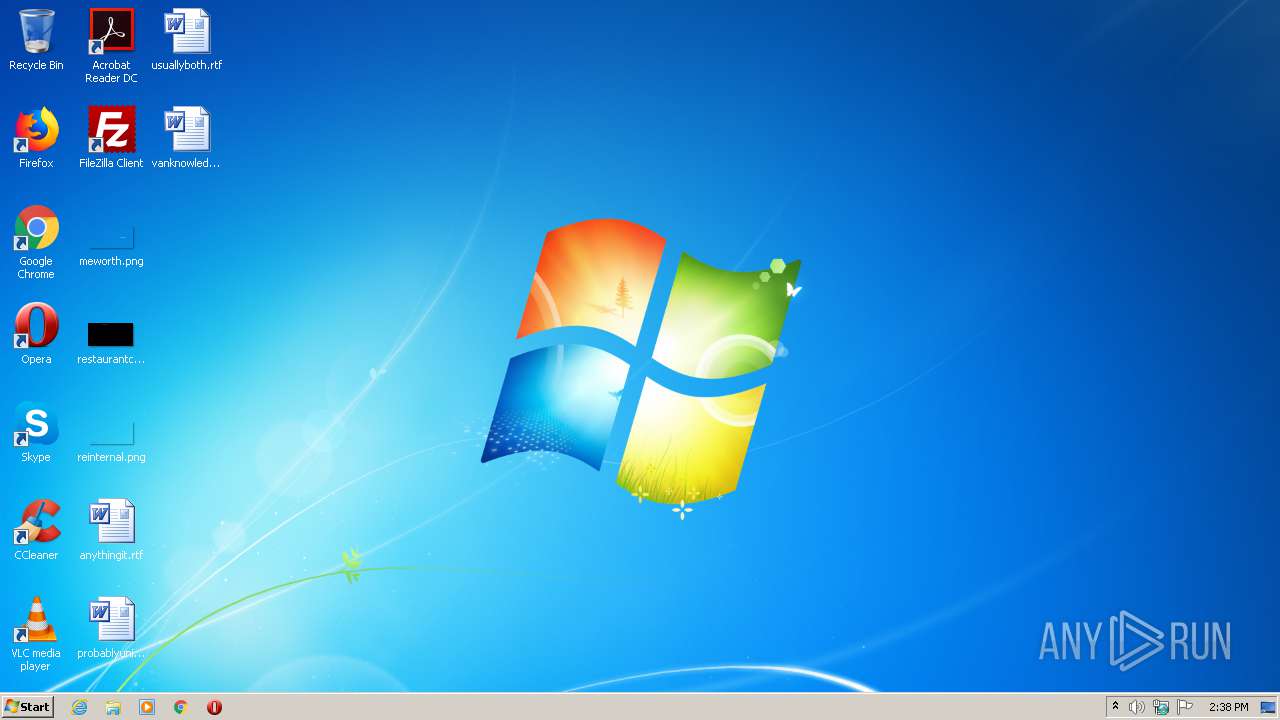
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows, UPX compressed |
| MD5: | 4FFE0C34306DCAF1D08F9208DC59439D |
| SHA1: | 20B8BC062FD6B9D3974F953CE48D5AFF063C9C35 |
| SHA256: | 91D3770AC0D4463CB356327DB2C492F1CBCE42715DBCAE11D8768F4BF2FB2C98 |
| SSDEEP: | 49152:QdMuktFMGWmRG5WHTk3rkKxbLjPlmZW/AICICqjXoFkDD4ecPL9KLESyz4wZSLK:QdMLtFLtQ3rkyPVoIC0qkQecPhKwSWY |
MALICIOUS
Changes settings of System certificates
- u.exe.6.dr.exe (PID: 2892)
SUSPICIOUS
Executed via COM
- DllHost.exe (PID: 2952)
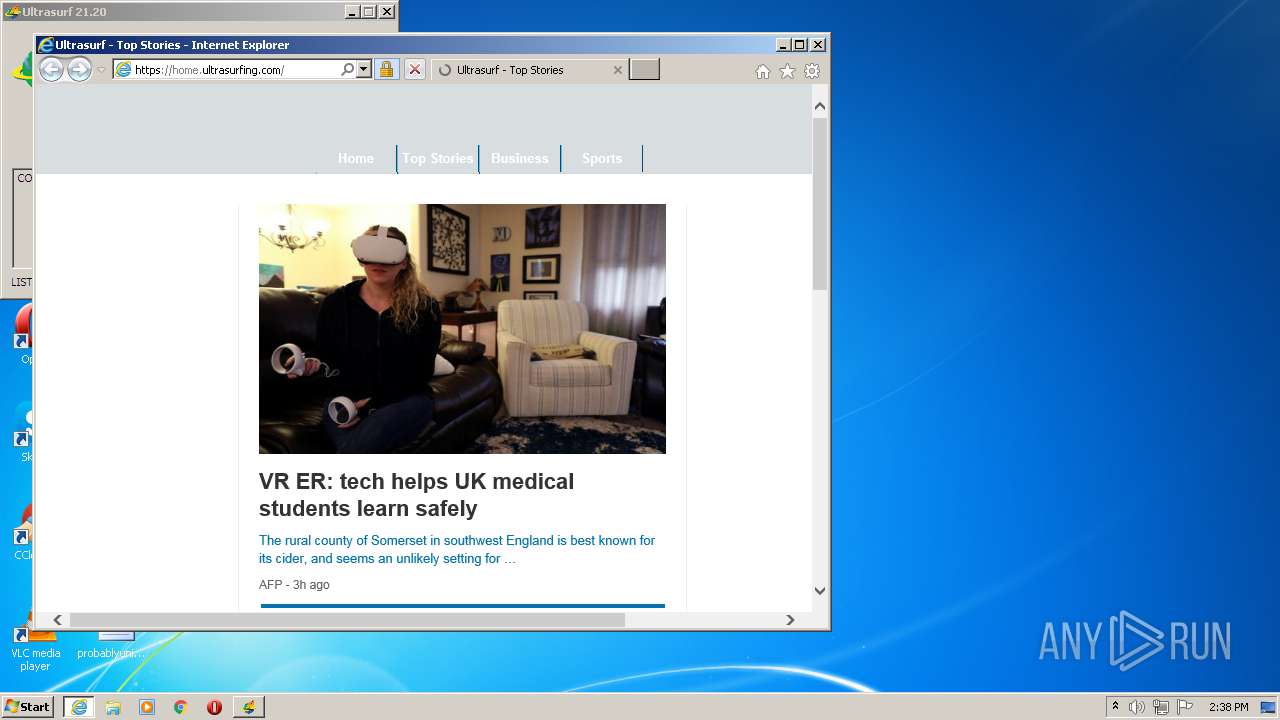
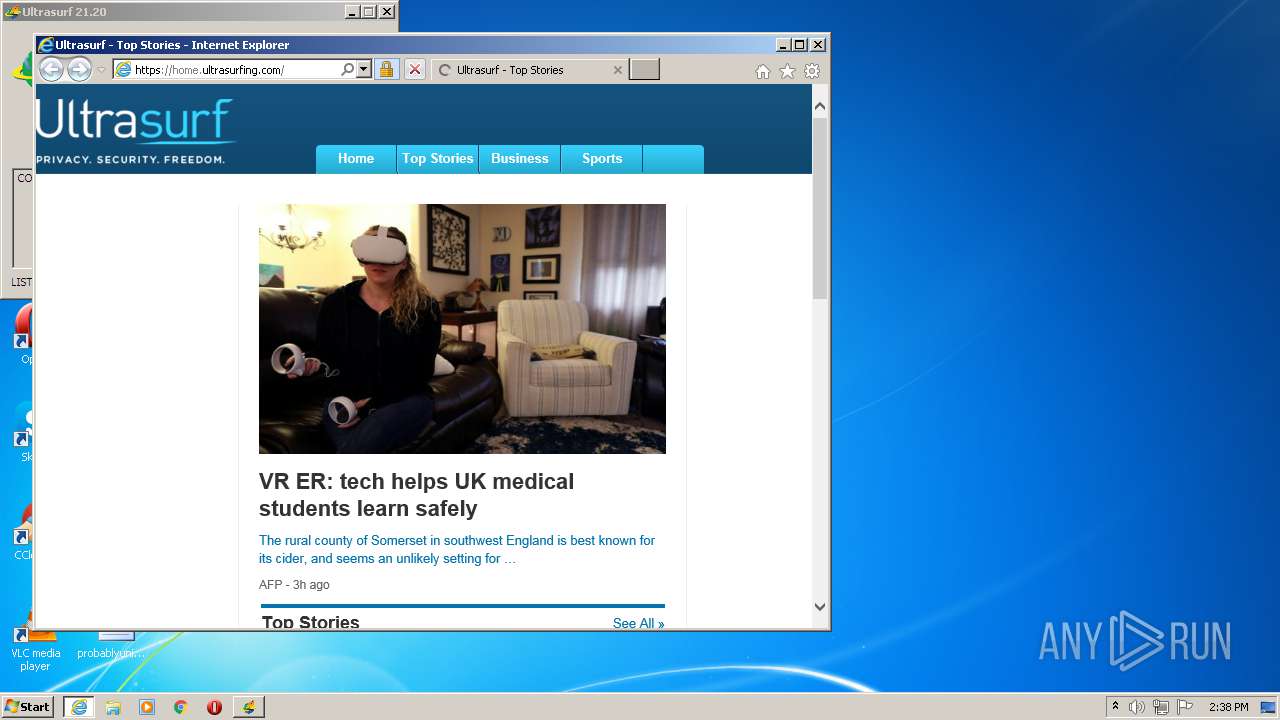
Starts Internet Explorer
- rundll32.exe (PID: 3752)
Uses RUNDLL32.EXE to load library
- u.exe.6.dr.exe (PID: 2892)
Adds / modifies Windows certificates
- u.exe.6.dr.exe (PID: 2892)
INFO
Application launched itself
- iexplore.exe (PID: 924)
Changes internet zones settings
- iexplore.exe (PID: 924)
Reads settings of System Certificates
- iexplore.exe (PID: 924)
Changes settings of System certificates
- iexplore.exe (PID: 924)
Reads internet explorer settings
- iexplore.exe (PID: 2876)
Adds / modifies Windows certificates
- iexplore.exe (PID: 924)
Creates files in the user directory
- iexplore.exe (PID: 924)
- iexplore.exe (PID: 2876)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5.1 |
| ImageVersion: | 1 |
| OSVersion: | 5.1 |
| EntryPoint: | 0xc1d7a0 |
| UninitializedDataSize: | 9728000 |
| InitializedDataSize: | 155648 |
| CodeSize: | 2977792 |
| LinkerVersion: | 3 |
| PEType: | PE32 |
| TimeStamp: | 0000:00:00 00:00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Jan-1970 00:00:00 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0004 |
| Size of header: | 0x0000 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x008B |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 01-Jan-1970 00:00:00 |
| Pointer to Symbol Table: | 0x00B83E00 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00947000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00948000 | 0x002D7000 | 0x002D6400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99992 |
.rsrc | 0x00C1F000 | 0x00026000 | 0x00025800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.50967 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25784 | 828 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.47164 | 152104 | UNKNOWN | English - United States | RT_ICON |
3 | 2.22322 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
KERNEL32.DLL |
Total processes
41
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
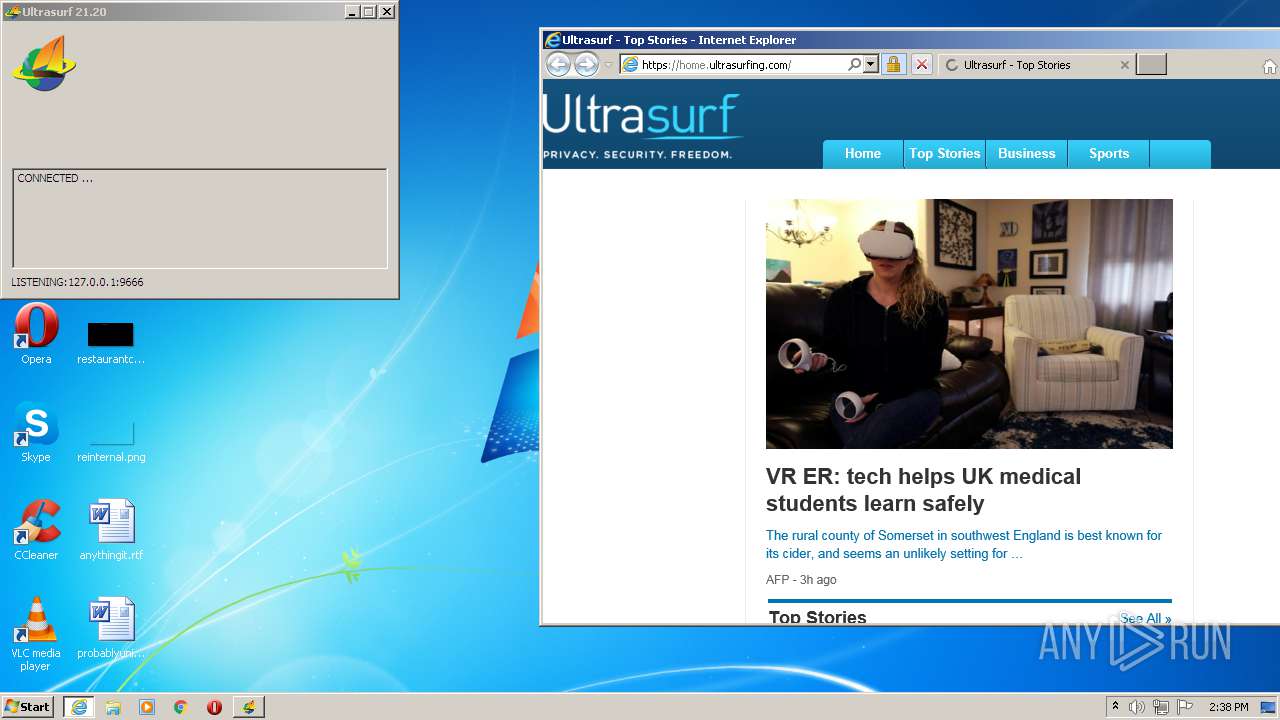
| 924 | "C:\Program Files\Internet Explorer\iexplore.exe" https://home.ultrasurfing.com/ | C:\Program Files\Internet Explorer\iexplore.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2876 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:924 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2892 | "C:\Users\admin\AppData\Local\Temp\u.exe.6.dr.exe" | C:\Users\admin\AppData\Local\Temp\u.exe.6.dr.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2952 | C:\Windows\system32\DllHost.exe /Processid:{F9717507-6651-4EDB-BFF7-AE615179BCCF} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3752 | rundll32 url.dll,FileProtocolHandler https://home.ultrasurfing.com | C:\Windows\system32\rundll32.exe | — | u.exe.6.dr.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
531
Read events
412
Write events
115
Delete events
4
Modification events
| (PID) Process: | (2952) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A6000000030000000E0000003132372E302E302E313A3936363600000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2952) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | DefaultConnectionSettings |
Value: 4600000008000000030000000E0000003132372E302E302E313A3936363600000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2892) u.exe.6.dr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyServer |
Value: 127.0.0.1:9666 | |||
| (PID) Process: | (2892) u.exe.6.dr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 1 | |||
| (PID) Process: | (2892) u.exe.6.dr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A7000000030000000E0000003132372E302E302E313A3936363600000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2892) u.exe.6.dr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A8000000030000000E0000003132372E302E302E313A3936363600000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2892) u.exe.6.dr.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2892) u.exe.6.dr.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\p2pcollab.dll,-8042 |
Value: Peer to Peer Trust | |||
| (PID) Process: | (2892) u.exe.6.dr.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\qagentrt.dll,-10 |
Value: System Health Authentication | |||
| (PID) Process: | (2892) u.exe.6.dr.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dnsapi.dll,-103 |
Value: Domain Name System (DNS) Server Trust | |||
Executable files
0
Suspicious files
44
Text files
35
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2876 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab3988.tmp | — | |
MD5:— | SHA256:— | |||
| 2876 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar3989.tmp | — | |
MD5:— | SHA256:— | |||
| 2876 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C8408FE5CA4467EE4DA84A76EF238FE3 | der | |
MD5:— | SHA256:— | |||
| 2876 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\644B8874112055B5E195ECB0E8F243A4 | der | |
MD5:— | SHA256:— | |||
| 2876 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:— | SHA256:— | |||
| 2876 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\MSIMGSIZ.DAT | smt | |
MD5:— | SHA256:— | |||
| 2876 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\AB07B6D94AE8D8C14957C88E5208BABA | binary | |
MD5:— | SHA256:— | |||
| 2876 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\style2[1].css | text | |
MD5:— | SHA256:— | |||
| 2876 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\644B8874112055B5E195ECB0E8F243A4 | binary | |
MD5:— | SHA256:— | |||
| 2876 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\C8408FE5CA4467EE4DA84A76EF238FE3 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
12
DNS requests
5
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2892 | u.exe.6.dr.exe | 9.9.9.11:443 | — | — | US | unknown |
2892 | u.exe.6.dr.exe | 149.112.112.11:443 | — | Packet Clearing House | US | unknown |
2892 | u.exe.6.dr.exe | 151.139.69.12:443 | — | netDNA | US | unknown |
2892 | u.exe.6.dr.exe | 151.139.81.23:443 | — | netDNA | US | unknown |
2892 | u.exe.6.dr.exe | 72.52.87.62:443 | — | Hurricane Electric, Inc. | US | unknown |
2892 | u.exe.6.dr.exe | 74.82.60.48:443 | — | Hurricane Electric, Inc. | US | unknown |
2892 | u.exe.6.dr.exe | 45.95.98.170:443 | — | — | — | unknown |
2892 | u.exe.6.dr.exe | 45.95.98.53:443 | — | — | — | unknown |
— | — | 104.22.0.17:46358 | — | Cloudflare Inc | US | unknown |
2892 | u.exe.6.dr.exe | 74.82.60.71:443 | — | Hurricane Electric, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
home.ultrasurfing.com |
| malicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |