| File name: | _91d15b3e6836b112cc7507af46553e95fcb40960c6d71494a20513ce3d552d94.exe |
| Full analysis: | https://app.any.run/tasks/0a0adeed-9532-424f-a5e9-adf3052c8ffe |
| Verdict: | Malicious activity |
| Analysis date: | April 03, 2026, 02:50:25 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
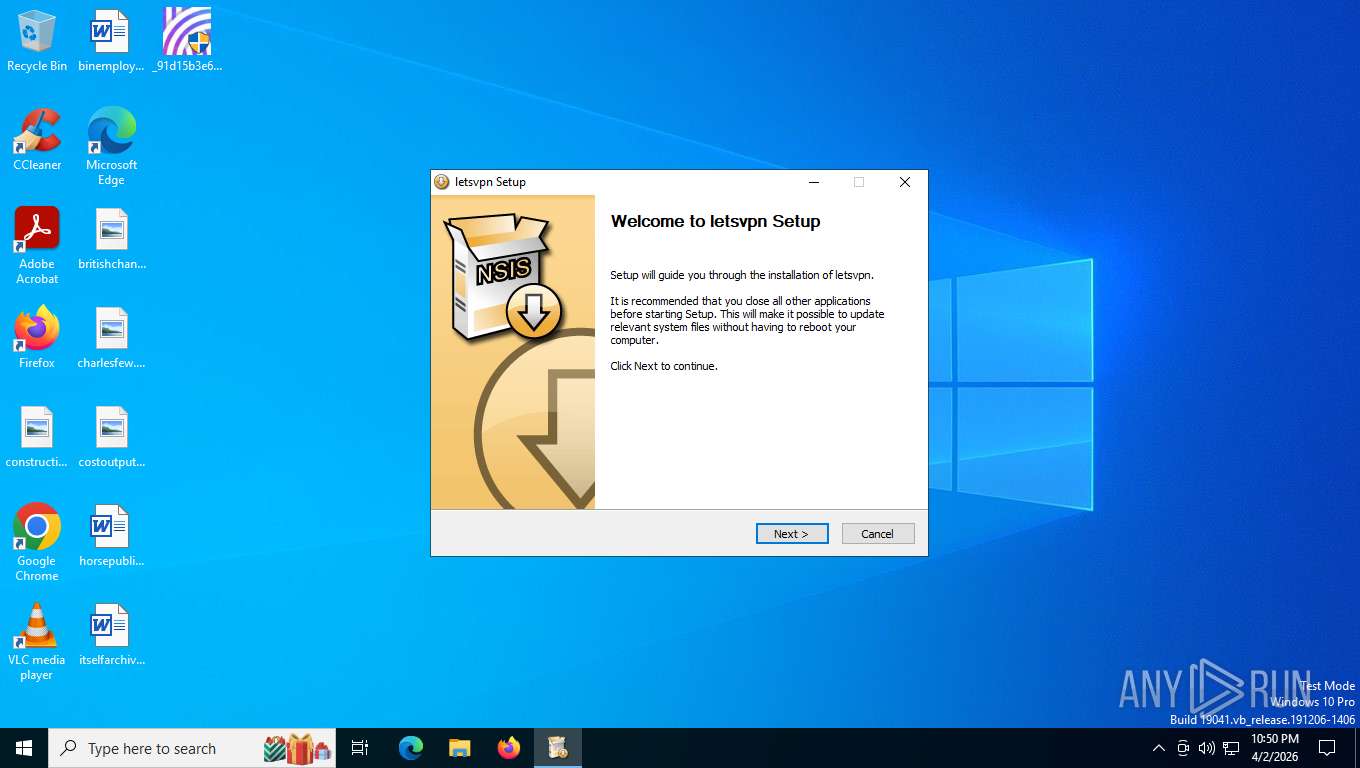
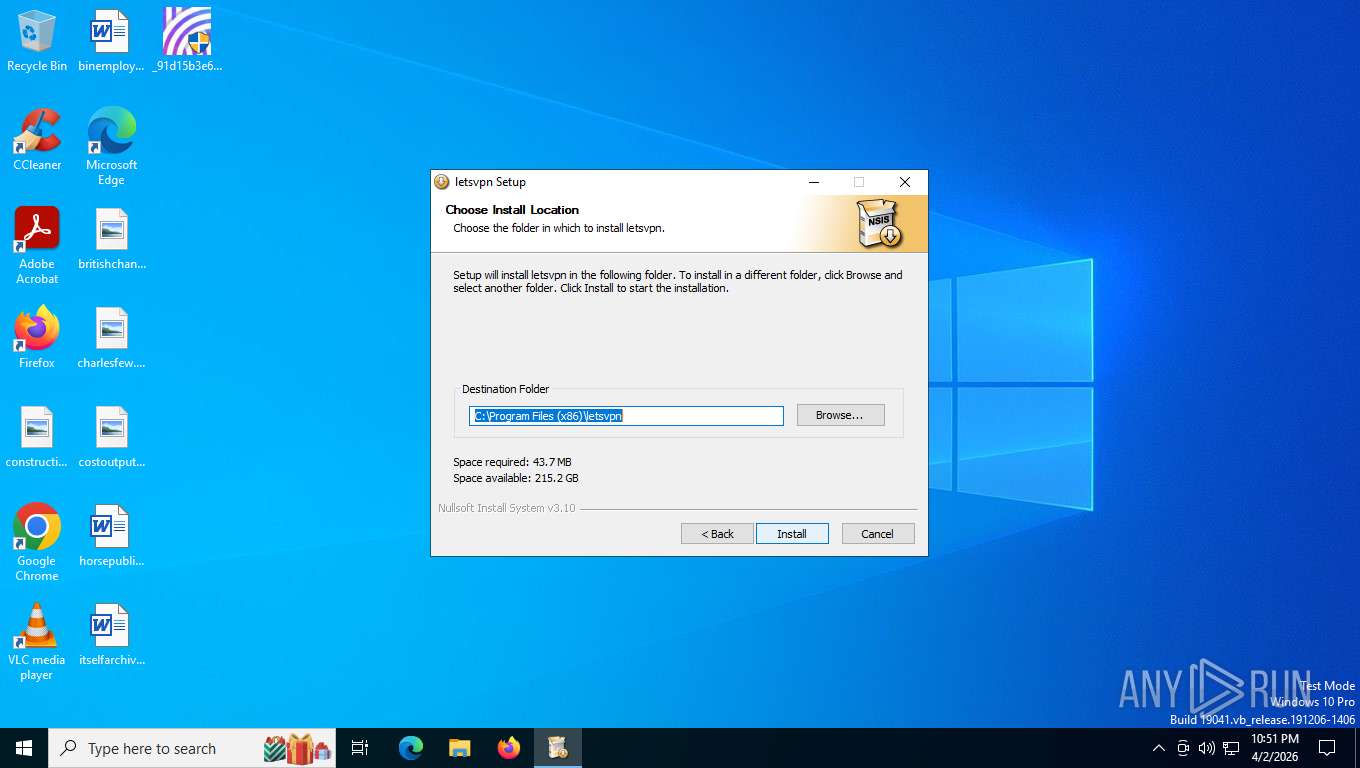
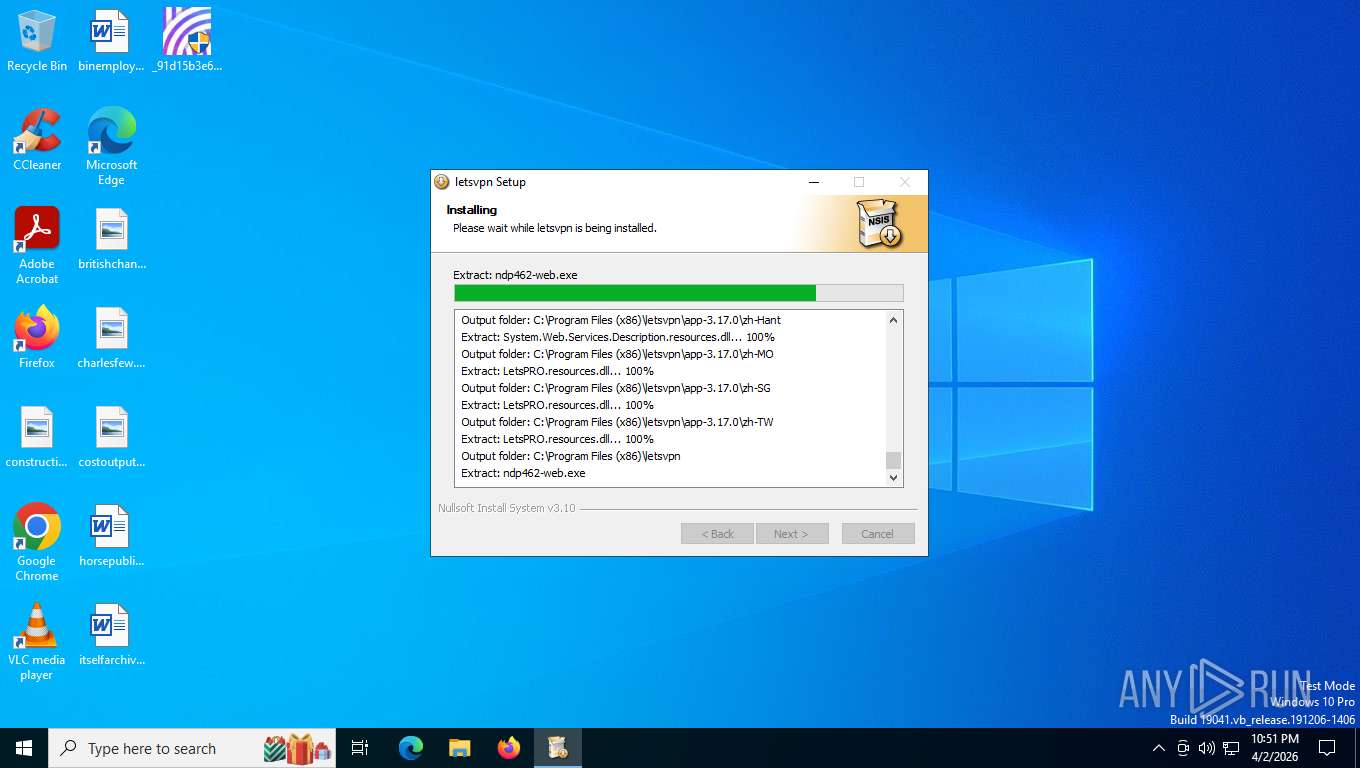
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | 0F778361E2ABAC4672F9D823E6714221 |
| SHA1: | AC9C89931480B682AE3F958D30DB7E889541ACCC |
| SHA256: | 91D15B3E6836B112CC7507AF46553E95FCB40960C6D71494A20513CE3D552D94 |
| SSDEEP: | 98304:EypLNieM+OAteJAIOkY+WgxgzS6EdT92JQpUSv7Pz1CRINgsU5PKZ8d6AMmCh+ic:EUfpQWLYvGhzNoCWCQ1UaFbW64rOaw6 |
MALICIOUS
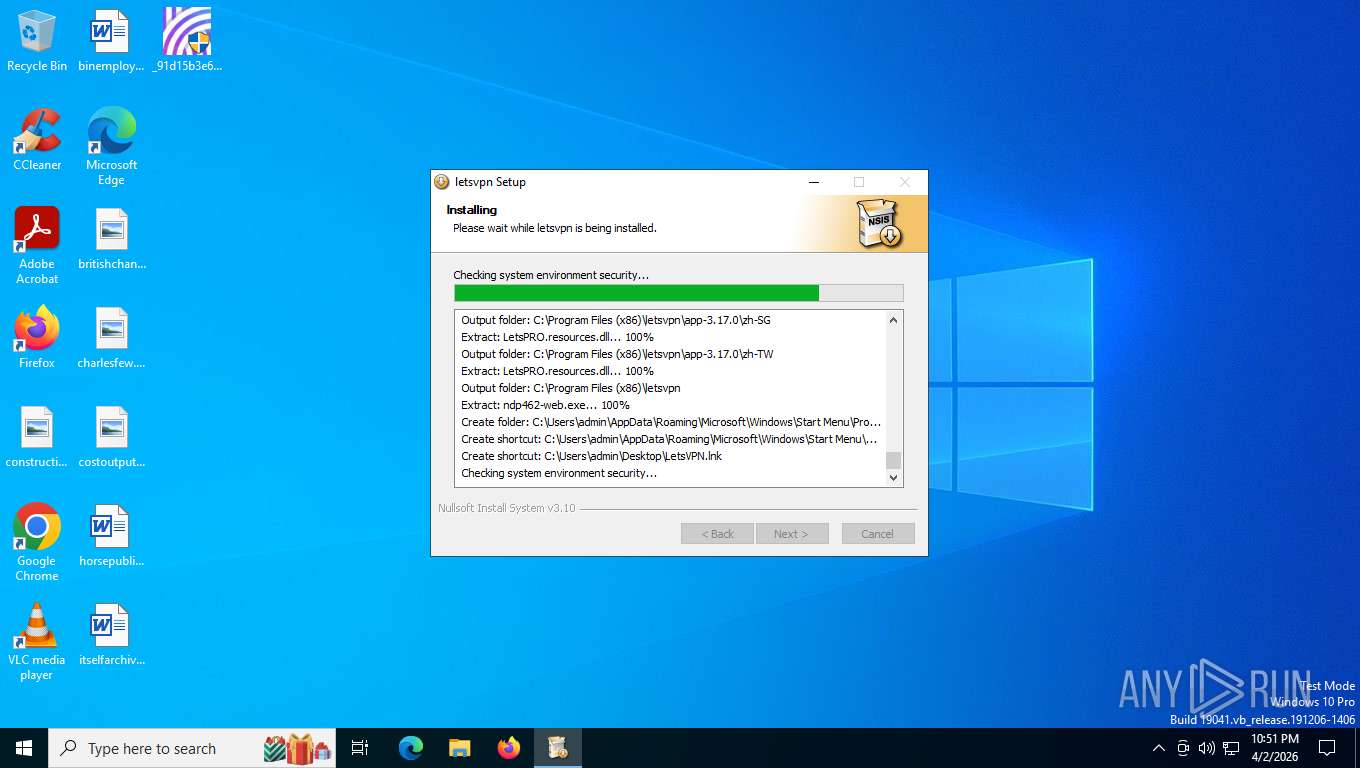
Changes powershell execution policy (Bypass)
- 1111.exe (PID: 2456)
SUSPICIOUS
Creates scheduled task with highest privileges
- schtasks.exe (PID: 7772)
Executable content was dropped or overwritten
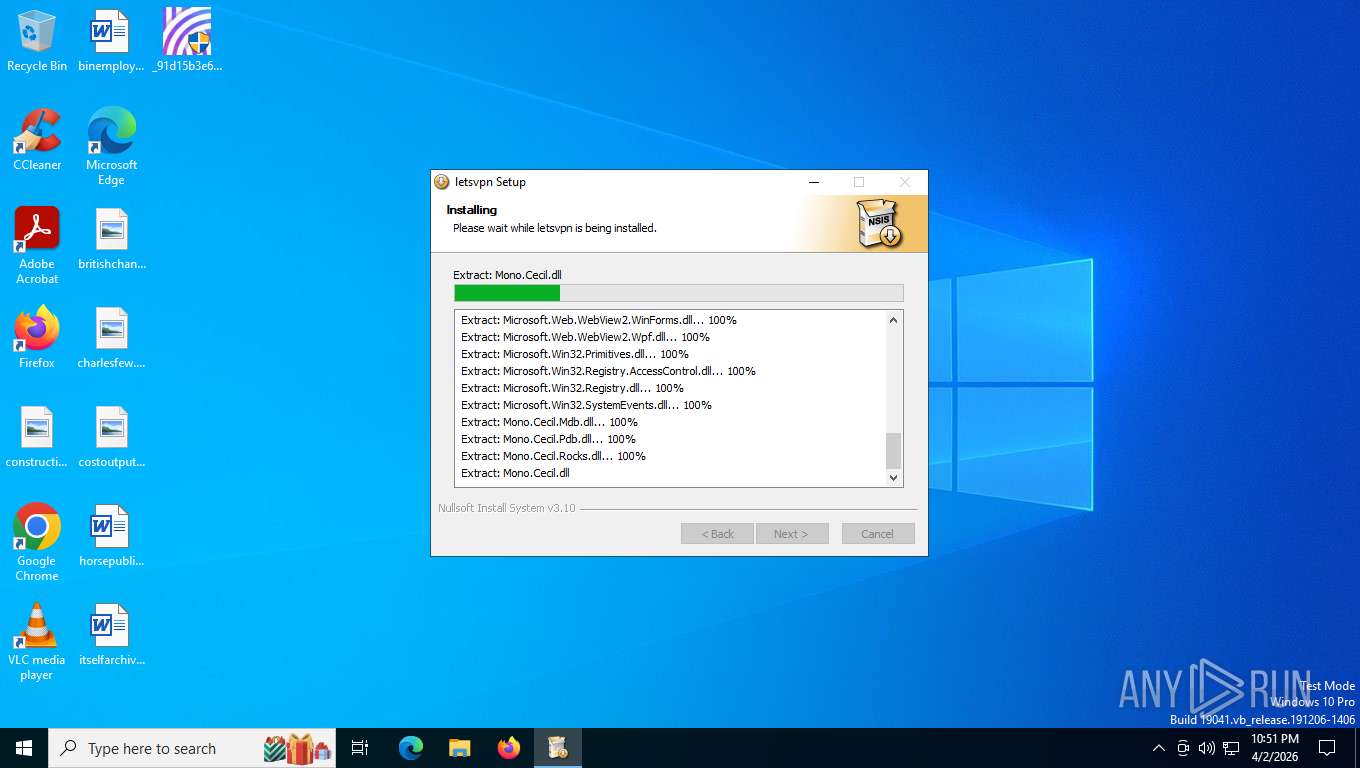
- _91d15b3e6836b112cc7507af46553e95fcb40960c6d71494a20513ce3d552d94.exe (PID: 756)
- 1111.exe (PID: 2456)
- tapinstall.exe (PID: 8124)
Creates scheduled task with ONLOGON parameter
- _91d15b3e6836b112cc7507af46553e95fcb40960c6d71494a20513ce3d552d94.exe (PID: 756)
The process creates files with name similar to system file names
- 1111.exe (PID: 2456)
Malware-specific behavior (creating "System.dll" in Temp)
- 1111.exe (PID: 2456)
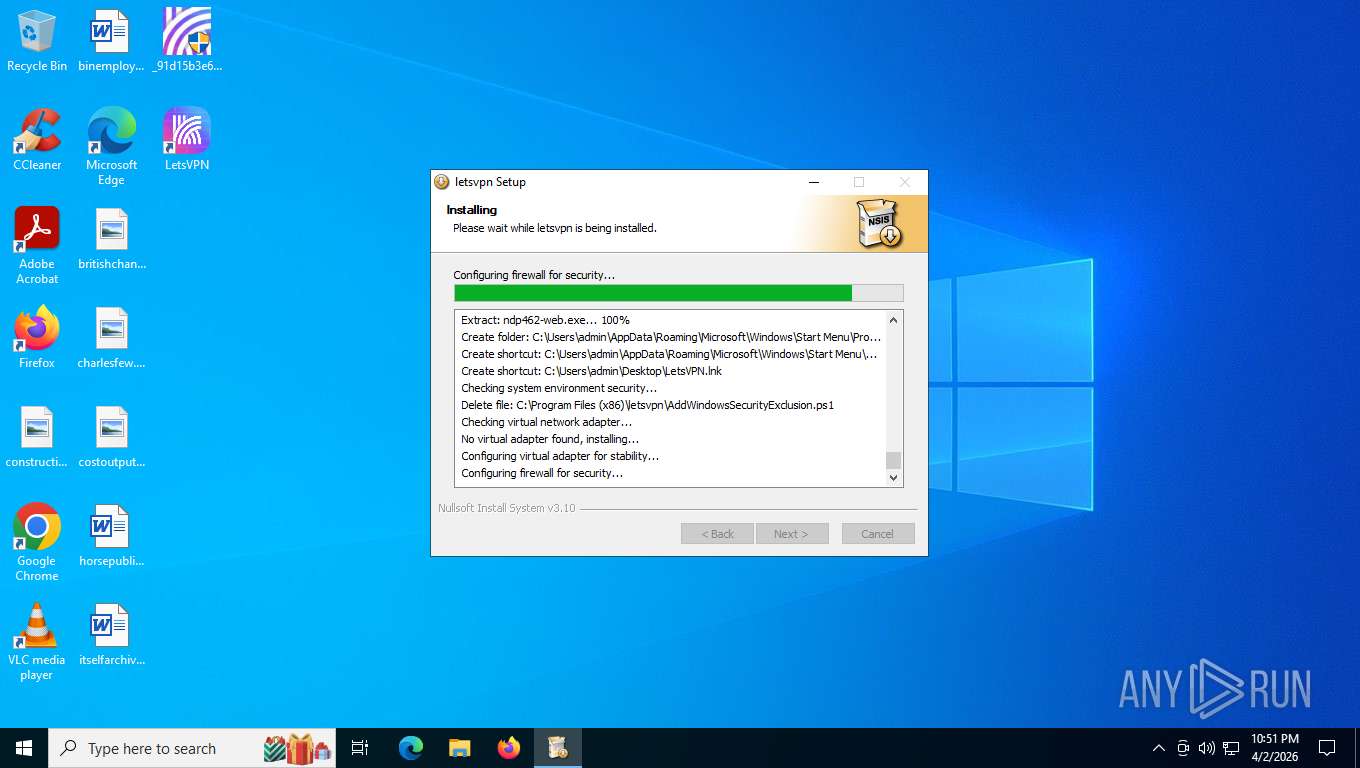
Drops a system driver (possible attempt to evade defenses)
- 1111.exe (PID: 2456)
- tapinstall.exe (PID: 8124)
- drvinst.exe (PID: 1036)
- drvinst.exe (PID: 4596)
Starts POWERSHELL.EXE for commands execution
- 1111.exe (PID: 2456)
Bypass execution policy to execute commands
- powershell.exe (PID: 1932)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- cmd.exe (PID: 6792)
- cmd.exe (PID: 2548)
- cmd.exe (PID: 4804)
- cmd.exe (PID: 7672)
- cmd.exe (PID: 8144)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 6792)
- cmd.exe (PID: 2548)
- cmd.exe (PID: 4804)
- cmd.exe (PID: 7672)
- cmd.exe (PID: 8144)
INFO
Checks supported languages
- _91d15b3e6836b112cc7507af46553e95fcb40960c6d71494a20513ce3d552d94.exe (PID: 756)
- mesedge.exe (PID: 1872)
- 1111.exe (PID: 2456)
- tapinstall.exe (PID: 8124)
- tapinstall.exe (PID: 5216)
- mesedge.exe (PID: 8044)
- drvinst.exe (PID: 4596)
- drvinst.exe (PID: 1036)
- tapinstall.exe (PID: 4104)
- LetsPRO.exe (PID: 7540)
- LetsPRO.exe (PID: 8444)
Create files in a temporary directory
- _91d15b3e6836b112cc7507af46553e95fcb40960c6d71494a20513ce3d552d94.exe (PID: 756)
- 1111.exe (PID: 2456)
- tapinstall.exe (PID: 8124)
Creates a software uninstall entry
- _91d15b3e6836b112cc7507af46553e95fcb40960c6d71494a20513ce3d552d94.exe (PID: 756)
- 1111.exe (PID: 2456)
Uses Task Scheduler to autorun other applications (AUTOMATE)
- _91d15b3e6836b112cc7507af46553e95fcb40960c6d71494a20513ce3d552d94.exe (PID: 756)
The sample compiled with english language support
- _91d15b3e6836b112cc7507af46553e95fcb40960c6d71494a20513ce3d552d94.exe (PID: 756)
- 1111.exe (PID: 2456)
- tapinstall.exe (PID: 8124)
- drvinst.exe (PID: 1036)
- drvinst.exe (PID: 4596)
Reads the computer name
- 1111.exe (PID: 2456)
- mesedge.exe (PID: 1872)
- mesedge.exe (PID: 8044)
- tapinstall.exe (PID: 8124)
- drvinst.exe (PID: 1036)
- drvinst.exe (PID: 4596)
- LetsPRO.exe (PID: 7540)
There is functionality for taking screenshot (YARA)
- 1111.exe (PID: 2456)
- mesedge.exe (PID: 8044)
- mesedge.exe (PID: 1872)
Creates files or folders in the user directory
- 1111.exe (PID: 2456)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 1932)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 1932)
Manual execution by a user
- mesedge.exe (PID: 8044)
Reads the machine GUID from the registry
- drvinst.exe (PID: 1036)
- tapinstall.exe (PID: 8124)
- LetsPRO.exe (PID: 7540)
Reads security settings of Internet Explorer
- tapinstall.exe (PID: 8124)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:08:01 02:42:47+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 118784 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x3312 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
182
Monitored processes
35
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 756 | "C:\Users\admin\Desktop\_91d15b3e6836b112cc7507af46553e95fcb40960c6d71494a20513ce3d552d94.exe" | C:\Users\admin\Desktop\_91d15b3e6836b112cc7507af46553e95fcb40960c6d71494a20513ce3d552d94.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1036 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{1b284ff2-2ee0-8341-9ef7-23ba7ffee94d}\oemvista.inf" "9" "4d14a44ff" "00000000000001E8" "WinSta0\Default" "00000000000001DC" "208" "c:\program files (x86)\letsvpn\driver" | C:\Windows\System32\drvinst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1320 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1368 | netsh advfirewall firewall Delete rule name=LetsPRO | C:\Windows\SysWOW64\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1524 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | tapinstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1824 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1836 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1872 | C:\ProgramData\messedge\mesedge.exe | C:\ProgramData\messedge\mesedge.exe | _91d15b3e6836b112cc7507af46553e95fcb40960c6d71494a20513ce3d552d94.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 1932 | powershell -inputformat none -ExecutionPolicy Bypass -File "C:\Program Files (x86)\letsvpn\AddWindowsSecurityExclusion.ps1" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | 1111.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2340 | "C:\Users\admin\Desktop\_91d15b3e6836b112cc7507af46553e95fcb40960c6d71494a20513ce3d552d94.exe" | C:\Users\admin\Desktop\_91d15b3e6836b112cc7507af46553e95fcb40960c6d71494a20513ce3d552d94.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
20 264
Read events
20 193
Write events
64
Delete events
7
Modification events
| (PID) Process: | (756) _91d15b3e6836b112cc7507af46553e95fcb40960c6d71494a20513ce3d552d94.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\lets |
| Operation: | write | Name: | DisplayName |
Value: lets 12.0.6 | |||
| (PID) Process: | (756) _91d15b3e6836b112cc7507af46553e95fcb40960c6d71494a20513ce3d552d94.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\lets |
| Operation: | write | Name: | UninstallString |
Value: C:\ProgramData\messedge\uninst.exe | |||
| (PID) Process: | (756) _91d15b3e6836b112cc7507af46553e95fcb40960c6d71494a20513ce3d552d94.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\lets |
| Operation: | write | Name: | InstallLocation |
Value: C:\ProgramData\messedge | |||
| (PID) Process: | (756) _91d15b3e6836b112cc7507af46553e95fcb40960c6d71494a20513ce3d552d94.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\lets |
| Operation: | write | Name: | DisplayIcon |
Value: C:\ProgramData\messedge\mesedge.exe | |||
| (PID) Process: | (756) _91d15b3e6836b112cc7507af46553e95fcb40960c6d71494a20513ce3d552d94.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\lets |
| Operation: | write | Name: | DisplayVersion |
Value: 12.0.6 | |||
| (PID) Process: | (756) _91d15b3e6836b112cc7507af46553e95fcb40960c6d71494a20513ce3d552d94.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\lets |
| Operation: | write | Name: | Publisher |
Value: geek | |||
| (PID) Process: | (756) _91d15b3e6836b112cc7507af46553e95fcb40960c6d71494a20513ce3d552d94.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\lets |
| Operation: | write | Name: | URLInfoAbout |
Value: http://www.fanyi.com | |||
| (PID) Process: | (2456) 1111.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\lets |
| Operation: | write | Name: | InstallTimeStamp |
Value: 20260402225129.408 | |||
| (PID) Process: | (2456) 1111.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\lets |
| Operation: | write | Name: | InstallNewVersion |
Value: 3.17.0 | |||
| (PID) Process: | (8124) tapinstall.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\SetupapiLogStatus |
| Operation: | write | Name: | setupapi.dev.log |
Value: 4096 | |||
Executable files
235
Suspicious files
16
Text files
13
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 756 | _91d15b3e6836b112cc7507af46553e95fcb40960c6d71494a20513ce3d552d94.exe | C:\ProgramData\messedge\1111.exe | executable | |
MD5:5920FBDD4E48ACC656D358E505856066 | SHA256:84595AC8463F0372738348985D84E68259325B5BC1B01EB48E3F8759634EB1F4 | |||
| 2456 | 1111.exe | C:\Users\admin\AppData\Local\Temp\nsu7231.tmp\System.dll | executable | |
MD5:192639861E3DC2DC5C08BB8F8C7260D5 | SHA256:23D618A0293C78CE00F7C6E6DD8B8923621DA7DD1F63A070163EF4C0EC3033D6 | |||
| 756 | _91d15b3e6836b112cc7507af46553e95fcb40960c6d71494a20513ce3d552d94.exe | C:\ProgramData\messedge\uninst.exe | executable | |
MD5:568E60CEA2C9AF3C0C9C8962DFEDC72B | SHA256:99144DD6993F97279C1DB051DC0917C59F0312671191D01883B63148F5CDCF74 | |||
| 2456 | 1111.exe | C:\Users\admin\AppData\Local\Temp\nsu7231.tmp\modern-header.bmp | image | |
MD5:5ACF495828FEAE7F85E006B7774AF497 | SHA256:6CFEBB59F0BA1B9F1E8D7AA6387F223A468EB2FF74A9ED3C3F4BB688C2B6455E | |||
| 2456 | 1111.exe | C:\Program Files (x86)\letsvpn\driver\tap0901.cat | binary | |
MD5:F73AC62E8DF97FAF3FC8D83E7F71BF3F | SHA256:CC74CDB88C198EB00AEF4CAA20BF1FDA9256917713A916E6B94435CD4DCB7F7B | |||
| 2456 | 1111.exe | C:\Users\admin\AppData\Local\Temp\nsu7231.tmp\modern-wizard.bmp | image | |
MD5:7F8E1969B0874C8FB9AB44FC36575380 | SHA256:076221B4527FF13C3E1557ABBBD48B0CB8E5F7D724C6B9171C6AADADB80561DD | |||
| 2456 | 1111.exe | C:\Users\admin\AppData\Local\Temp\nsu7231.tmp\nsDialogs.dll | executable | |
MD5:B7D61F3F56ABF7B7FF0D4E7DA3AD783D | SHA256:89A82C4849C21DFE765052681E1FAD02D2D7B13C8B5075880C52423DCA72A912 | |||
| 756 | _91d15b3e6836b112cc7507af46553e95fcb40960c6d71494a20513ce3d552d94.exe | C:\Users\admin\AppData\Local\Temp\nsu7195.tmp\nsExec.dll | executable | |
MD5:09C2E27C626D6F33018B8A34D3D98CB6 | SHA256:114C6941A8B489416C84563E94FD266EA5CAD2B518DB45CD977F1F9761E00CB1 | |||
| 2456 | 1111.exe | C:\Program Files (x86)\letsvpn\LetsPRO.exe | executable | |
MD5:D9375ACA792295FAE46E0EECDF5AF24B | SHA256:D402534B4FE63D398A684CB58FAFB847BD06DAD2051517994210DD632F7FD960 | |||
| 2456 | 1111.exe | C:\Program Files (x86)\letsvpn\driver\tap0901.sys | executable | |
MD5:C10CCDEC5D7AF458E726A51BB3CDC732 | SHA256:589C5667B1602837205DA8EA8E92FE13F8C36048B293DF931C99B39641052253 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
79
TCP/UDP connections
77
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
5780 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
5780 | svchost.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
— | — | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
2312 | slui.exe | POST | 500 | 48.192.1.65:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | US | text | 512 b | whitelisted |
2312 | slui.exe | POST | 500 | 48.192.1.65:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | US | text | 512 b | whitelisted |
3292 | svchost.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | US | binary | 814 b | whitelisted |
3292 | svchost.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | US | binary | 400 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
— | — | 23.216.77.28:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
5780 | svchost.exe | 23.216.77.28:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
6768 | MoUsoCoreWorker.exe | 23.216.77.28:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
5780 | svchost.exe | 23.52.181.212:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
— | — | 23.52.181.212:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 23.52.181.212:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ks1.tianqi-1.com |
| unknown |
activation-v2.sls.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |