| File name: | Sample_5bb36afd69669c70e827d804.bin |
| Full analysis: | https://app.any.run/tasks/d13a5d5f-9acd-4d71-adf9-bfe09ae7fd3c |
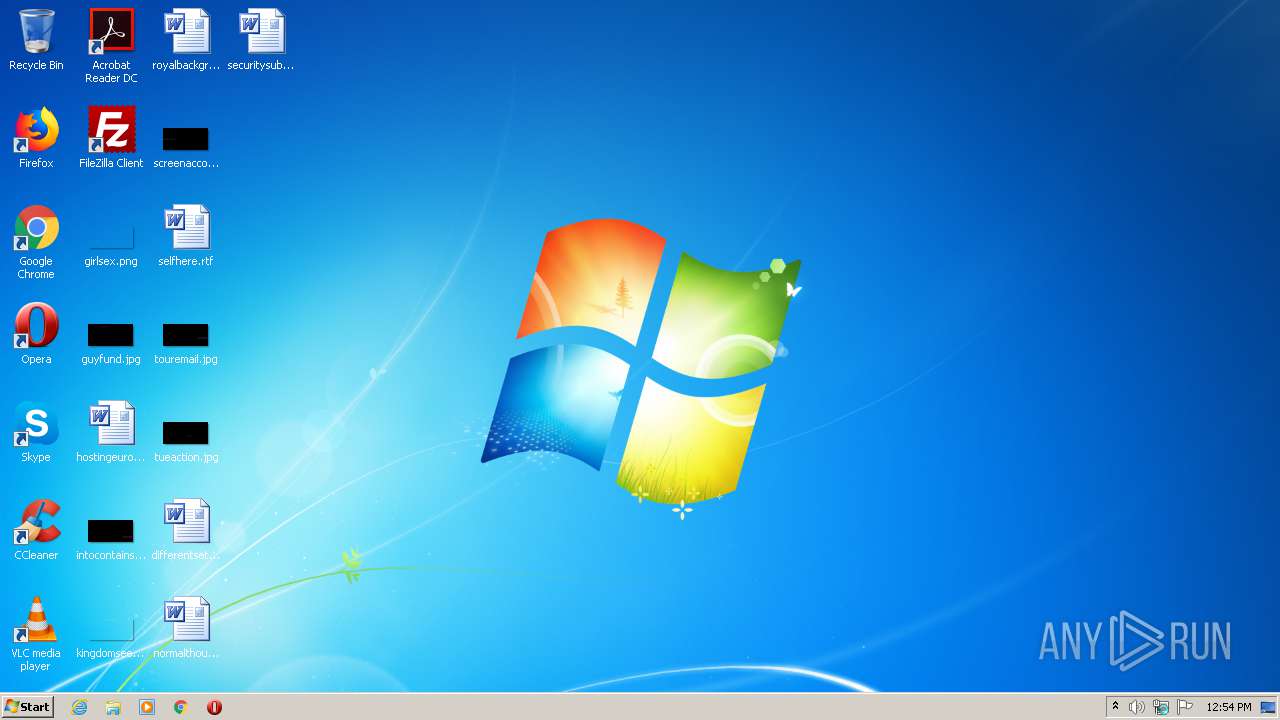
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2020, 11:54:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 1D4FFF59EAA40773284E76D9371DD701 |
| SHA1: | 2485BF86561F6A206FE58CD56631B83CB6E5FBA9 |
| SHA256: | 91D138EF6F0D9FE740D7E69EB7F2E462E1E342C51716C0B3E898E8CB559C14DF |
| SSDEEP: | 12288:GCdOy3vVrKxR5CXbNjAOxK/j2n+4YG/6c1mFFja3mXgcjfRlgsUBgaYbXRQ:GCdxte/80jYLT3U1jfsWaYbRQ |
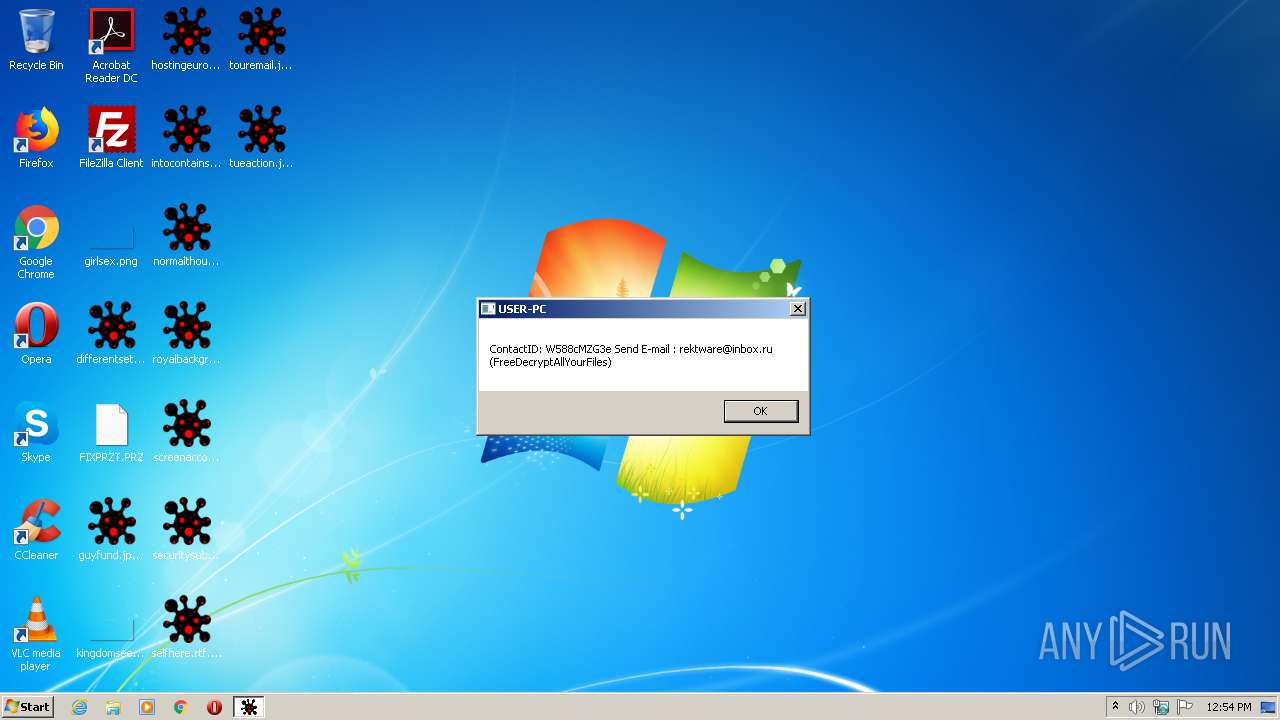
MALICIOUS
Actions looks like stealing of personal data
- Sample_5bb36afd69669c70e827d804.bin.exe (PID: 3260)
SUSPICIOUS
Creates files in the program directory
- Sample_5bb36afd69669c70e827d804.bin.exe (PID: 3260)
Modifies the open verb of a shell class
- Sample_5bb36afd69669c70e827d804.bin.exe (PID: 3260)
Creates files in the user directory
- Sample_5bb36afd69669c70e827d804.bin.exe (PID: 3260)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:09:14 19:36:44+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 581120 |
| InitializedDataSize: | 274944 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x27f4a |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Sep-2018 17:36:44 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 14-Sep-2018 17:36:44 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0008DD2E | 0x0008DE00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.67588 |
.rdata | 0x0008F000 | 0x0002E10E | 0x0002E200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.76073 |
.data | 0x000BE000 | 0x00008F74 | 0x00005200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.19881 |
.rsrc | 0x000C7000 | 0x00008A1C | 0x00008C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.79605 |
.reloc | 0x000D0000 | 0x00007130 | 0x00007200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.78238 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.39264 | 1018 | Latin 1 / Western European | English - United Kingdom | RT_MANIFEST |
2 | 1.8522 | 9640 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
7 | 3.34702 | 1428 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
8 | 3.2817 | 1674 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
9 | 3.28849 | 1168 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
10 | 3.28373 | 1532 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
11 | 3.26322 | 1628 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
12 | 3.25812 | 1126 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
99 | 2.0815 | 20 | Latin 1 / Western European | English - United Kingdom | RT_GROUP_ICON |
169 | 1.84274 | 20 | Latin 1 / Western European | English - United Kingdom | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
MPR.dll |
OLEAUT32.dll |
PSAPI.DLL |
SHELL32.dll |
Total processes
39
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2724 | "C:\Users\admin\AppData\Local\Temp\Sample_5bb36afd69669c70e827d804.bin.exe" | C:\Users\admin\AppData\Local\Temp\Sample_5bb36afd69669c70e827d804.bin.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3260 | "C:\Users\admin\AppData\Local\Temp\Sample_5bb36afd69669c70e827d804.bin.exe" | C:\Users\admin\AppData\Local\Temp\Sample_5bb36afd69669c70e827d804.bin.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
33
Read events
26
Write events
7
Delete events
0
Modification events
| (PID) Process: | (3260) Sample_5bb36afd69669c70e827d804.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.8P8g2Om |
| Operation: | write | Name: | (default) |
Value: 8P8g2Omfile | |||
| (PID) Process: | (3260) Sample_5bb36afd69669c70e827d804.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\8P8g2Omfile |
| Operation: | write | Name: | (default) |
Value: ISbjjyFVN9qtr9p6XplzZm03dBxtZ61P4Pyo0hz53h6X7g0InE6dr6r5gWR26513vwi6s3nTtMeM8kDGu7vP43N91NFwFwNKrN4ET93oci850zTD88i4HGlo047XwOKAf8uGcNrlePhgYGi8sBpGsuVefPy6g34U4tRs6U7hc0Cp4qSecoD614Gf2uR9ddUCM0ghe51LSy06n3ILc8PHFLZCftYUWy8W8uPmRjbhCgRwH2t2aSgohJA4qy5fYTBHn94v9rfP48c2Oks7oXYukN598aPQALYYX3qPJg8wze4Q | |||
| (PID) Process: | (3260) Sample_5bb36afd69669c70e827d804.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\8P8g2Omfile\shell\Open\Command |
| Operation: | write | Name: | (default) |
Value: C:\Users\admin\AppData\Local\Temp\Sample_5bb36afd69669c70e827d804.bin.exe "%1" | |||
| (PID) Process: | (3260) Sample_5bb36afd69669c70e827d804.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\8P8g2Omfile\shell |
| Operation: | write | Name: | (default) |
Value: Open | |||
| (PID) Process: | (3260) Sample_5bb36afd69669c70e827d804.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\8P8g2Omfile\shell\Open\Command |
| Operation: | write | Name: | oldcmd |
Value: C:\Users\admin\AppData\Local\Temp\Sample_5bb36afd69669c70e827d804.bin.exe "%1" | |||
| (PID) Process: | (3260) Sample_5bb36afd69669c70e827d804.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\8P8g2Omfile\DefaultIcon |
| Operation: | write | Name: | (default) |
Value: C:\Users\admin\AppData\Local\Temp\Sample_5bb36afd69669c70e827d804.bin.exe | |||
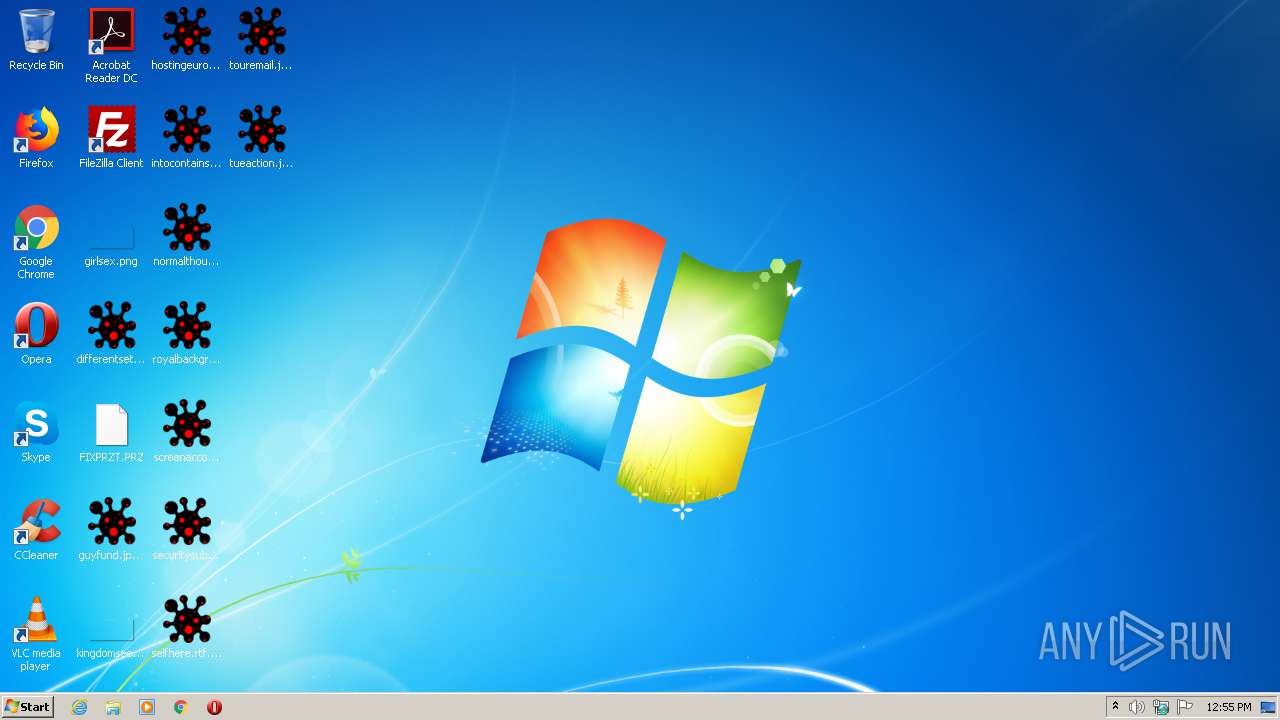
Executable files
0
Suspicious files
82
Text files
5
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3260 | Sample_5bb36afd69669c70e827d804.bin.exe | C:\Users\admin\AppData\Roaming\Network\PRZT1.PRZ | — | |
MD5:— | SHA256:— | |||
| 3260 | Sample_5bb36afd69669c70e827d804.bin.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PRZT2.PRZ | — | |
MD5:— | SHA256:— | |||
| 3260 | Sample_5bb36afd69669c70e827d804.bin.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\previews_opt_out.db.8P8g2Om | binary | |
MD5:— | SHA256:— | |||
| 3260 | Sample_5bb36afd69669c70e827d804.bin.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\databases\Databases.db.8P8g2Om | binary | |
MD5:— | SHA256:— | |||
| 3260 | Sample_5bb36afd69669c70e827d804.bin.exe | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_Calendar_2_1345B2AFA8CE7740BD41B19E133369EB.dat.8P8g2Om | binary | |
MD5:— | SHA256:— | |||
| 3260 | Sample_5bb36afd69669c70e827d804.bin.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\RecoveryStore.{42A7EDC2-DE02-11E9-92C0-5254004A04AF}.dat.8P8g2Om | binary | |
MD5:— | SHA256:— | |||
| 3260 | Sample_5bb36afd69669c70e827d804.bin.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\MSIMGSIZ.DAT.8P8g2Om | binary | |
MD5:— | SHA256:— | |||
| 3260 | Sample_5bb36afd69669c70e827d804.bin.exe | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_AvailabilityOptions_2_23FD1CF2FAF3F94682CAD351A9FDDEA2.dat.8P8g2Om | binary | |
MD5:— | SHA256:— | |||
| 3260 | Sample_5bb36afd69669c70e827d804.bin.exe | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_AvailabilityOptions_2_CD58CB9DEEE452498F56DC1A846E5975.dat.8P8g2Om | binary | |
MD5:— | SHA256:— | |||
| 3260 | Sample_5bb36afd69669c70e827d804.bin.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\{6D3D0B08-0153-11EB-9060-12A9866C77DE}.dat.8P8g2Om | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report