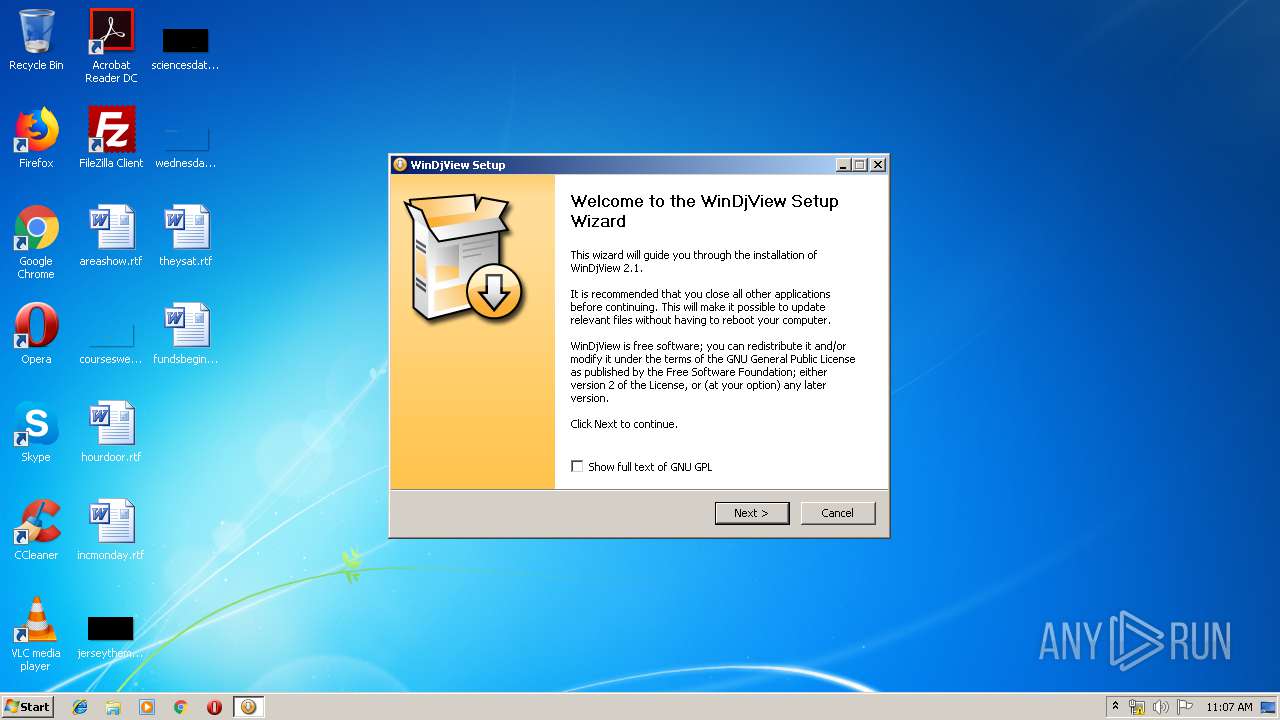
| File name: | WinDjView-2.1-Setup.exe |
| Full analysis: | https://app.any.run/tasks/a534360d-3986-46f4-b1d9-dc45ad342eb6 |
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2019, 10:07:27 |
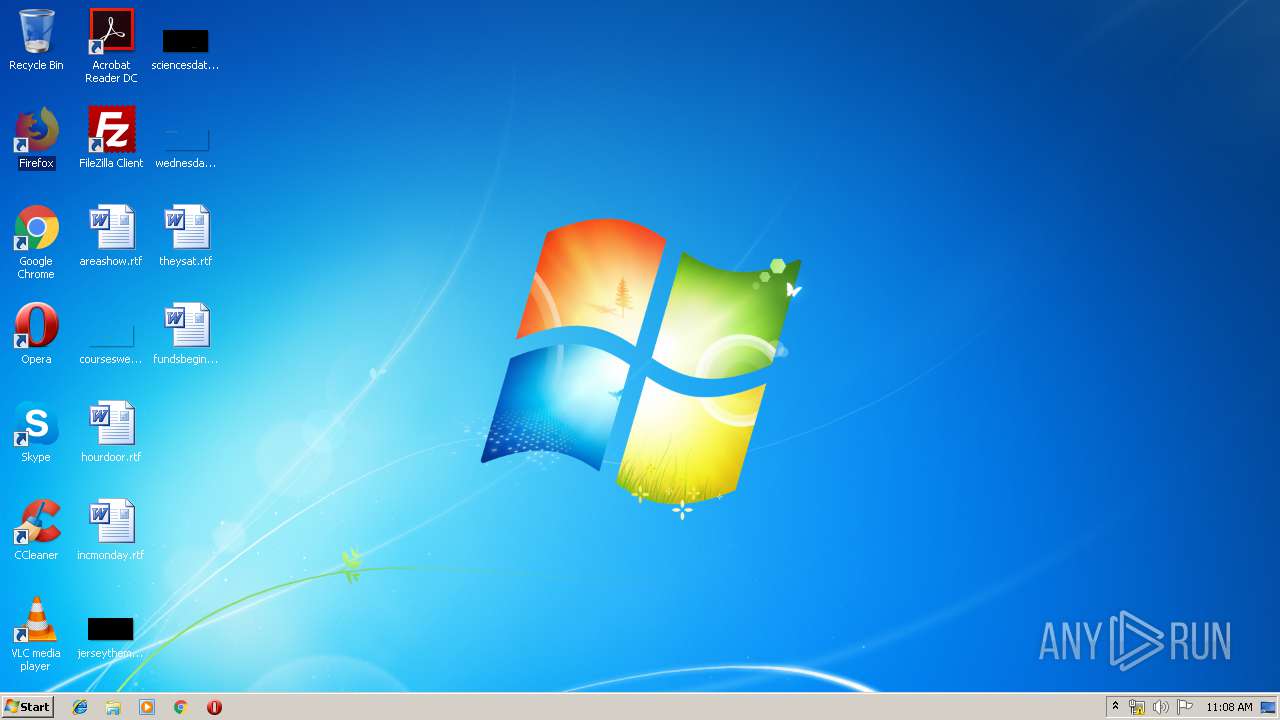
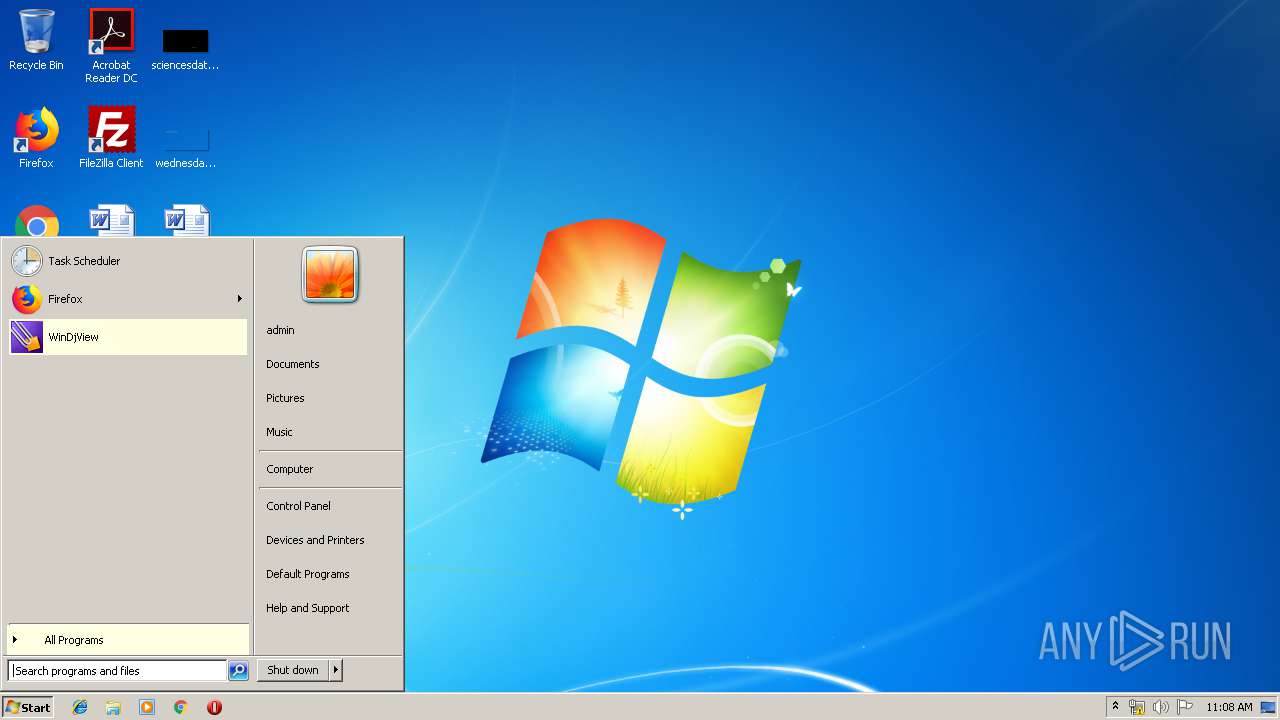
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | BE7854E8F7D922C2269FABD448D82F9E |
| SHA1: | BBF32F86DC8DB03A73C1331A04D73B41BC80C52B |
| SHA256: | 91CDE668B1F700B64677199E9B534F8DA4AE45AEF014F5439CEFDC8C532418BF |
| SSDEEP: | 49152:xjC1vb8qGFy7ZwrqttiLv7Abel1hWT6Wa+H2bI2PHm74UuGD5Tmue08jZi0:UKFyQEEv7COhX00U1TqC0 |
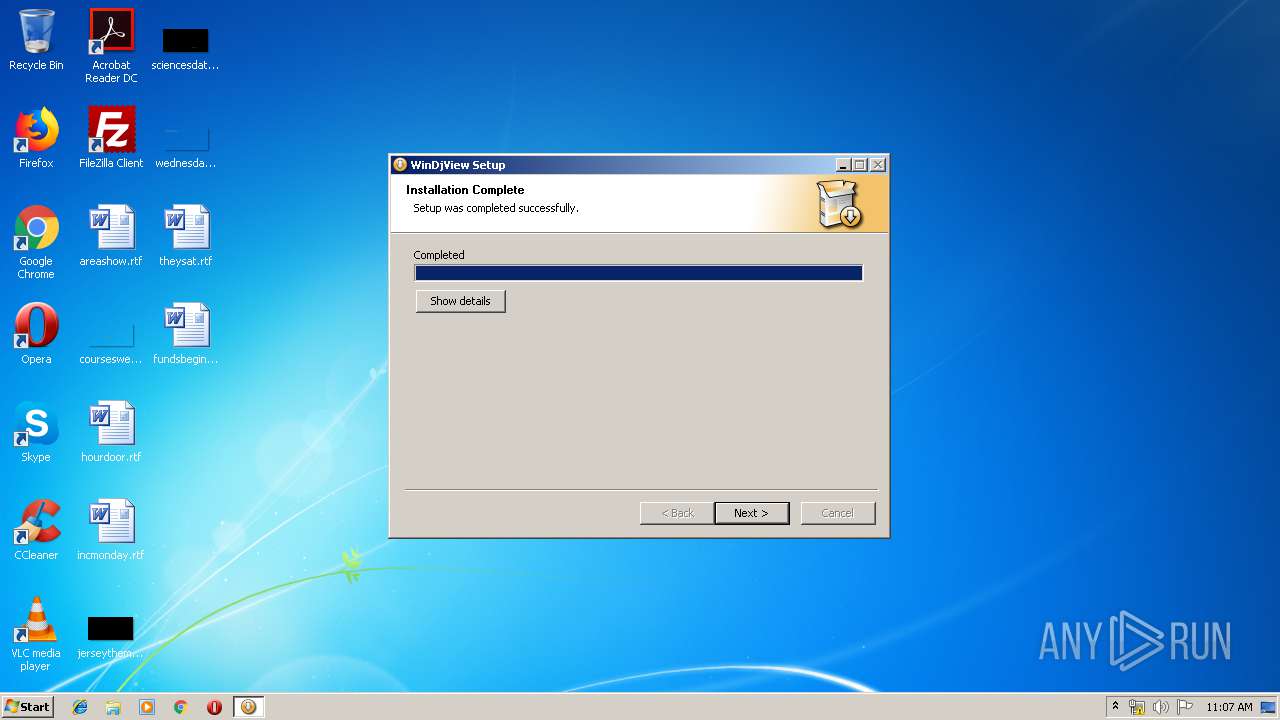
MALICIOUS
Application was dropped or rewritten from another process
- WinDjView.exe (PID: 3628)
- WinDjView.exe (PID: 2236)
- WinDjView.exe (PID: 3824)
Loads dropped or rewritten executable
- WinDjView-2.1-Setup.exe (PID: 3560)
- WinDjView-2.1-Setup.exe (PID: 2364)
SUSPICIOUS
Executable content was dropped or overwritten
- WinDjView-2.1-Setup.exe (PID: 2364)
- WinDjView-2.1-Setup.exe (PID: 3560)
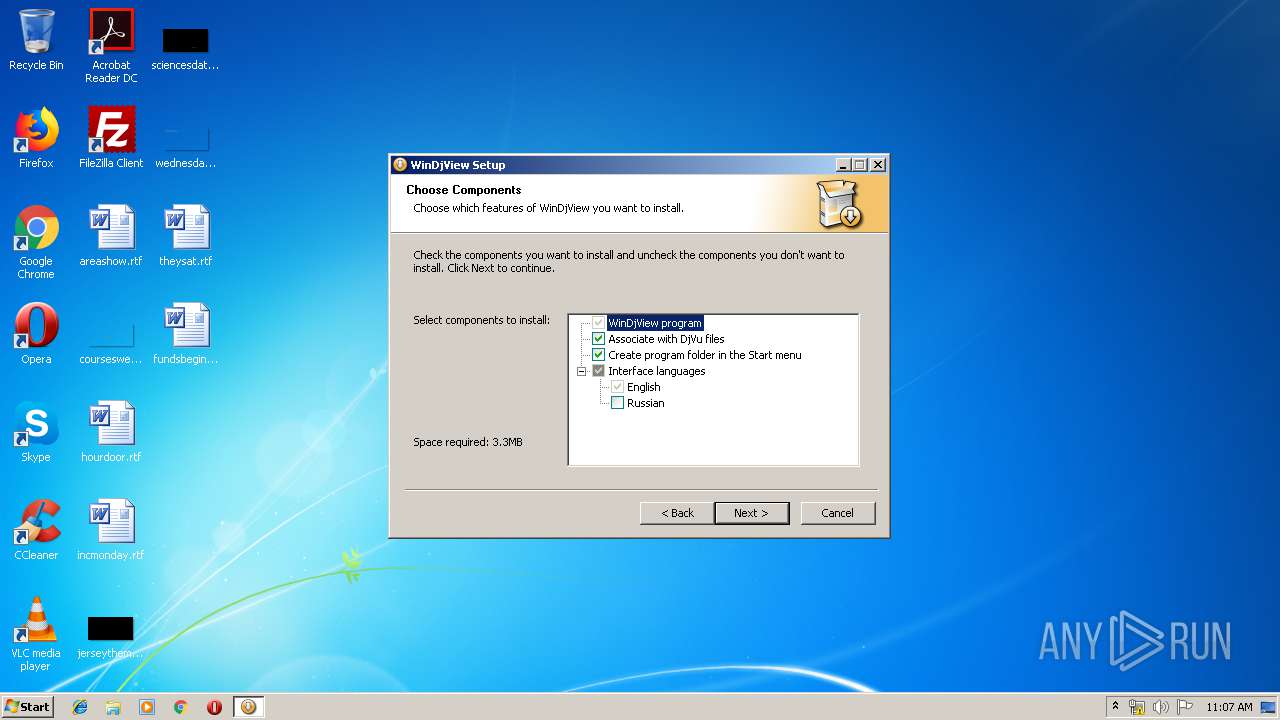
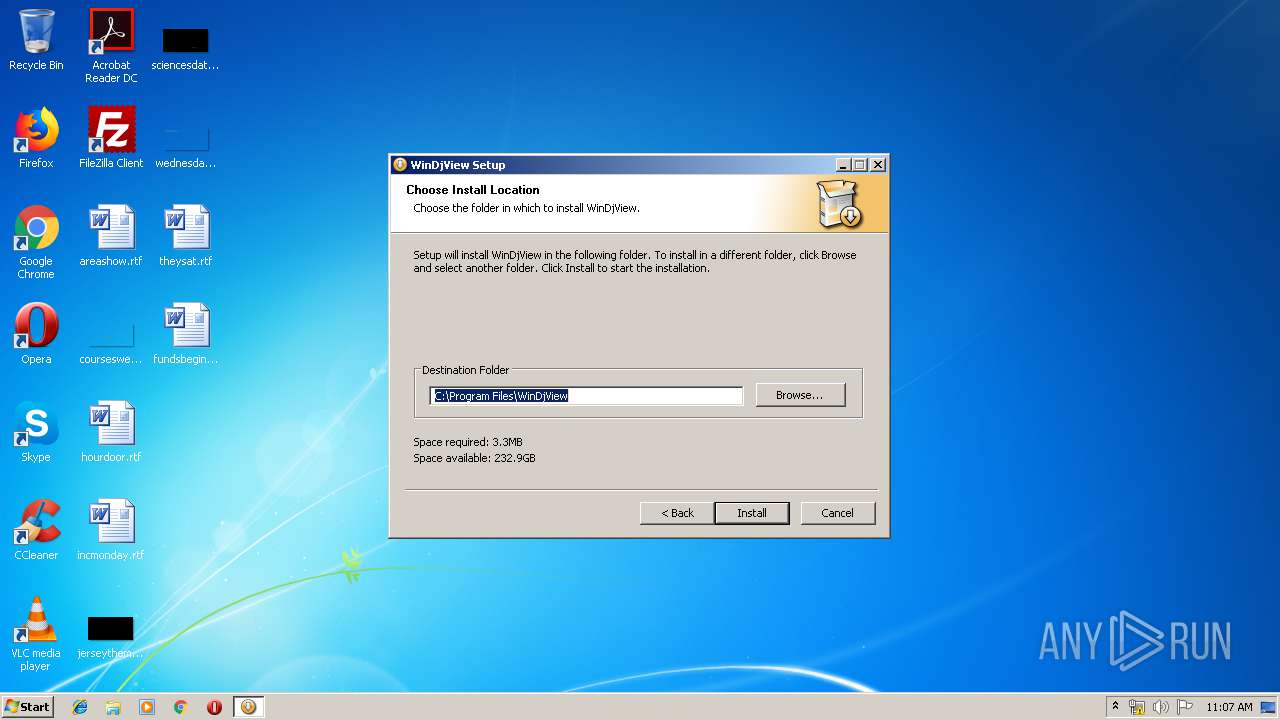
Creates files in the program directory
- WinDjView-2.1-Setup.exe (PID: 2364)
Application launched itself
- WinDjView-2.1-Setup.exe (PID: 3560)
Modifies the open verb of a shell class
- WinDjView.exe (PID: 3628)
Creates a software uninstall entry
- WinDjView-2.1-Setup.exe (PID: 2364)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 856)
Application launched itself
- chrome.exe (PID: 856)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:05 23:50:46+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23552 |
| InitializedDataSize: | 119808 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x323c |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.1.0.0 |
| ProductVersionNumber: | 2.1.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | ASCII |
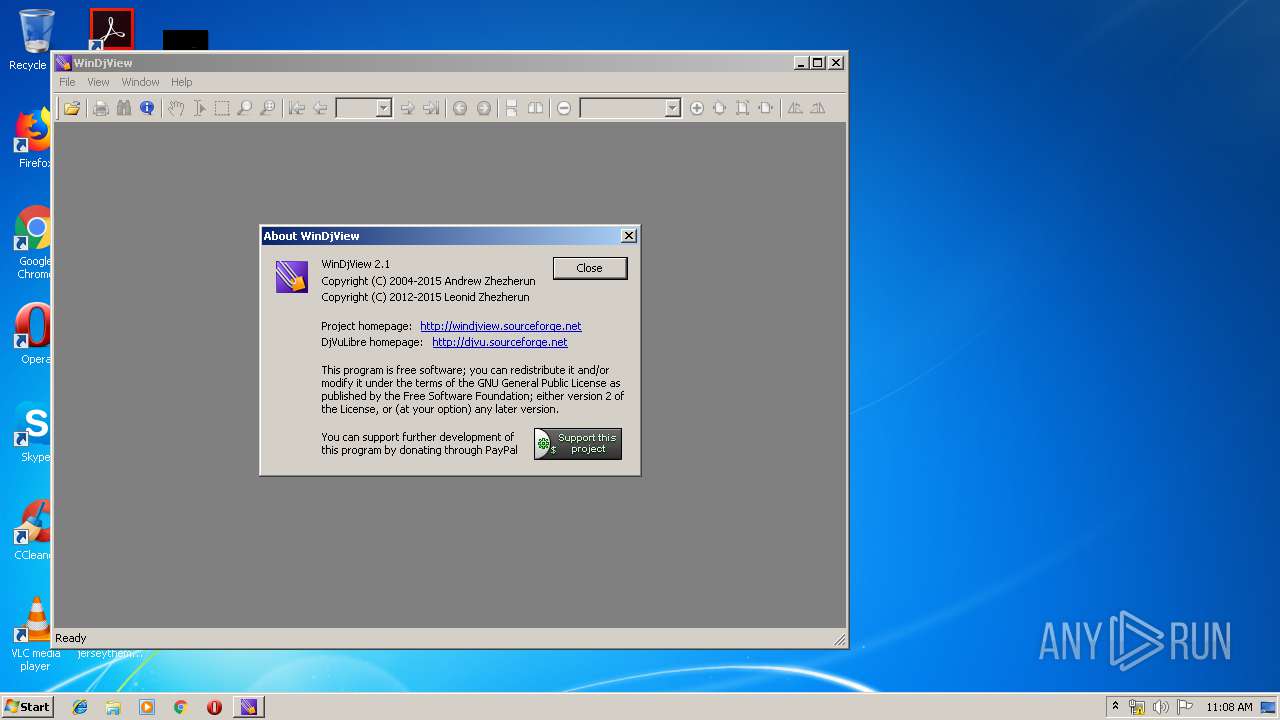
| CompanyName: | Andrew Zhezherun |
| CompanyWebsite: | http://windjview.sourceforge.net |
| FileDescription: | WinDjView Setup |
| FileVersion: | 2.1 |
| LegalCopyright: | Copyright (C) 2004-2015 Andrew Zhezherun |
| ProductName: | WinDjView Setup |
| ProductVersion: | 2.1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2009 22:50:46 |
| Detected languages: |
|
| CompanyName: | Andrew Zhezherun |
| CompanyWebsite: | http://windjview.sourceforge.net |
| FileDescription: | WinDjView Setup |
| FileVersion: | 2.1 |
| LegalCopyright: | Copyright (C) 2004-2015 Andrew Zhezherun |
| ProductName: | WinDjView Setup |
| ProductVersion: | 2.1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Dec-2009 22:50:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005A5A | 0x00005C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4177 |
.rdata | 0x00007000 | 0x00001190 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.18163 |
.data | 0x00009000 | 0x0001AF98 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.70903 |
.ndata | 0x00024000 | 0x00022000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00046000 | 0x00007A78 | 0x00007C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.63813 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.22437 | 947 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.61959 | 4264 | UNKNOWN | English - United States | RT_ICON |
3 | 4.84061 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 6.16608 | 2216 | UNKNOWN | English - United States | RT_ICON |
5 | 3.91942 | 1640 | UNKNOWN | English - United States | RT_ICON |
6 | 5.42186 | 1384 | UNKNOWN | English - United States | RT_ICON |
7 | 5.58096 | 1128 | UNKNOWN | English - United States | RT_ICON |
8 | 3.74963 | 744 | UNKNOWN | English - United States | RT_ICON |
9 | 3.01957 | 296 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
56
Monitored processes
21
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2844 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1160 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=952,2010702858100798011,15404128157228748800,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=4433766535425358432 --mojo-platform-channel-handle=972 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=952,2010702858100798011,15404128157228748800,131072 --enable-features=PasswordImport --service-pipe-token=1321129678441261494 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1321129678441261494 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1996 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1716 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6ffb0f18,0x6ffb0f28,0x6ffb0f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1808 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=952,2010702858100798011,15404128157228748800,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7777666801614445079 --mojo-platform-channel-handle=4320 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=952,2010702858100798011,15404128157228748800,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9089330306782059129 --mojo-platform-channel-handle=4004 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2056 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=952,2010702858100798011,15404128157228748800,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=5959645231929726095 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5959645231929726095 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3748 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=952,2010702858100798011,15404128157228748800,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13019305192017728339 --mojo-platform-channel-handle=4416 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2136 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=952,2010702858100798011,15404128157228748800,131072 --enable-features=PasswordImport --service-pipe-token=3909306538537669688 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3909306538537669688 --renderer-client-id=3 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2152 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
982
Read events
793
Write events
184
Delete events
5
Modification events
| (PID) Process: | (2364) WinDjView-2.1-Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\WinDjView |
| Operation: | write | Name: | InstallerLanguage |
Value: 1033 | |||
| (PID) Process: | (3628) WinDjView.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\DjVu.Document |
| Operation: | write | Name: | |
Value: DjVu Document | |||
| (PID) Process: | (3628) WinDjView.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\DjVu.Document\DefaultIcon |
| Operation: | write | Name: | |
Value: C:\Program Files\WinDjView\WinDjView.exe,0 | |||
| (PID) Process: | (3628) WinDjView.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\DjVu.Document\shell\open\ddeexec |
| Operation: | write | Name: | |
Value: [open("%1")] | |||
| (PID) Process: | (3628) WinDjView.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\DjVu.Document\shell\open\ddeexec\Application |
| Operation: | write | Name: | |
Value: WinDjView | |||
| (PID) Process: | (3628) WinDjView.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\DjVu.Document\shell\open\ddeexec\Topic |
| Operation: | write | Name: | |
Value: System | |||
| (PID) Process: | (3628) WinDjView.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\DjVu.Document\shell\open\ddeexec\IfExec |
| Operation: | write | Name: | |
Value: [rem open] | |||
| (PID) Process: | (3628) WinDjView.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\DjVu.Document\shell\open\command |
| Operation: | write | Name: | |
Value: "C:\Program Files\WinDjView\WinDjView.exe" "%1" | |||
| (PID) Process: | (3628) WinDjView.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.djvu |
| Operation: | write | Name: | |
Value: DjVu.Document | |||
| (PID) Process: | (3628) WinDjView.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.djv |
| Operation: | write | Name: | |
Value: DjVu.Document | |||
Executable files
8
Suspicious files
67
Text files
140
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2364 | WinDjView-2.1-Setup.exe | C:\Users\admin\AppData\Local\Temp\nsl653E.tmp | — | |
MD5:— | SHA256:— | |||
| 3560 | WinDjView-2.1-Setup.exe | C:\Users\admin\AppData\Local\Temp\nso5F91.tmp | — | |
MD5:— | SHA256:— | |||
| 856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFee143.TMP | — | |
MD5:— | SHA256:— | |||
| 2364 | WinDjView-2.1-Setup.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\WinDjView\WinDjView.lnk | lnk | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
20
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
856 | chrome.exe | GET | 200 | 194.9.25.78:80 | http://r3---sn-5uh5o-f5fs.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=212.7.219.109&mm=28&mn=sn-5uh5o-f5fs&ms=nvh&mt=1556013310&mv=u&pl=24&shardbypass=yes | PL | crx | 842 Kb | whitelisted |
856 | chrome.exe | GET | 302 | 216.58.206.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 508 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
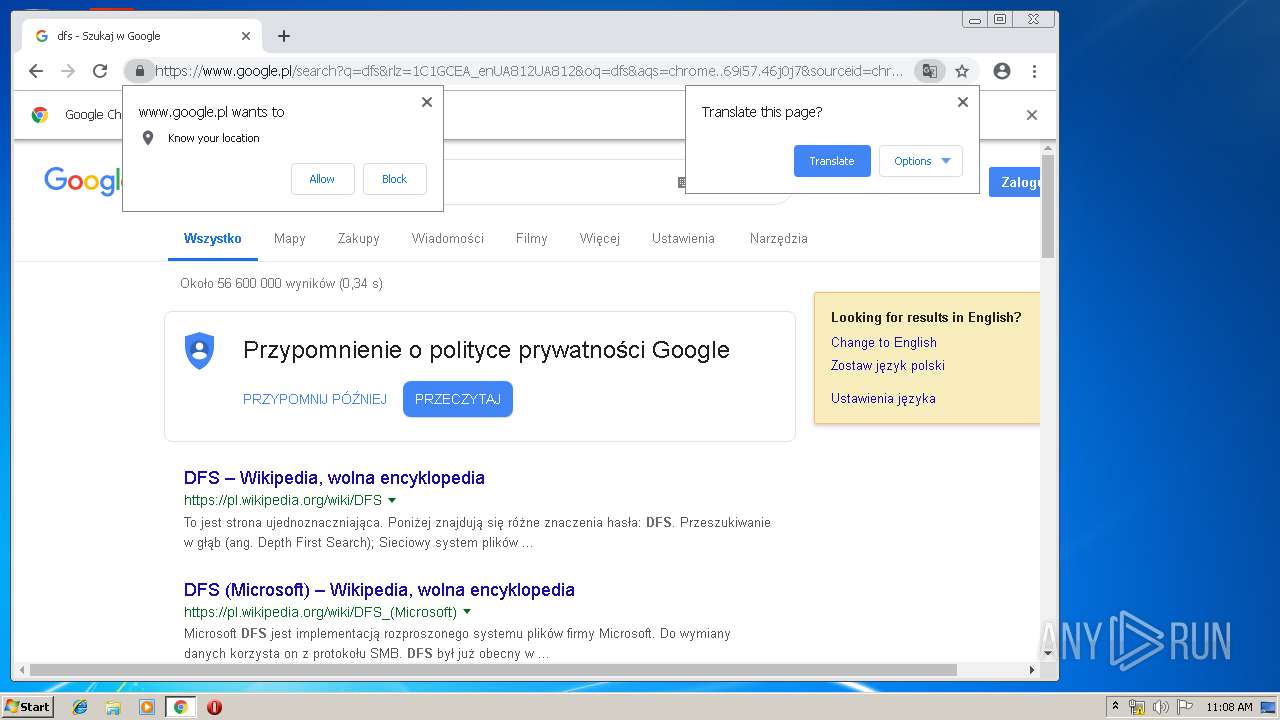
856 | chrome.exe | 172.217.21.195:443 | www.google.com.ua | Google Inc. | US | whitelisted |
856 | chrome.exe | 172.217.18.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
856 | chrome.exe | 172.217.23.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
856 | chrome.exe | 216.58.208.46:443 | clients1.google.com | Google Inc. | US | whitelisted |
856 | chrome.exe | 172.217.16.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
856 | chrome.exe | 172.217.22.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
856 | chrome.exe | 216.58.206.14:80 | consent.google.com | Google Inc. | US | whitelisted |
856 | chrome.exe | 216.58.205.238:443 | apis.google.com | Google Inc. | US | whitelisted |
856 | chrome.exe | 172.217.18.100:443 | www.google.com | Google Inc. | US | whitelisted |
856 | chrome.exe | 216.58.205.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
windjview.sourceforge.net |
| malicious |
clientservices.googleapis.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
accounts.google.com |
| shared |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
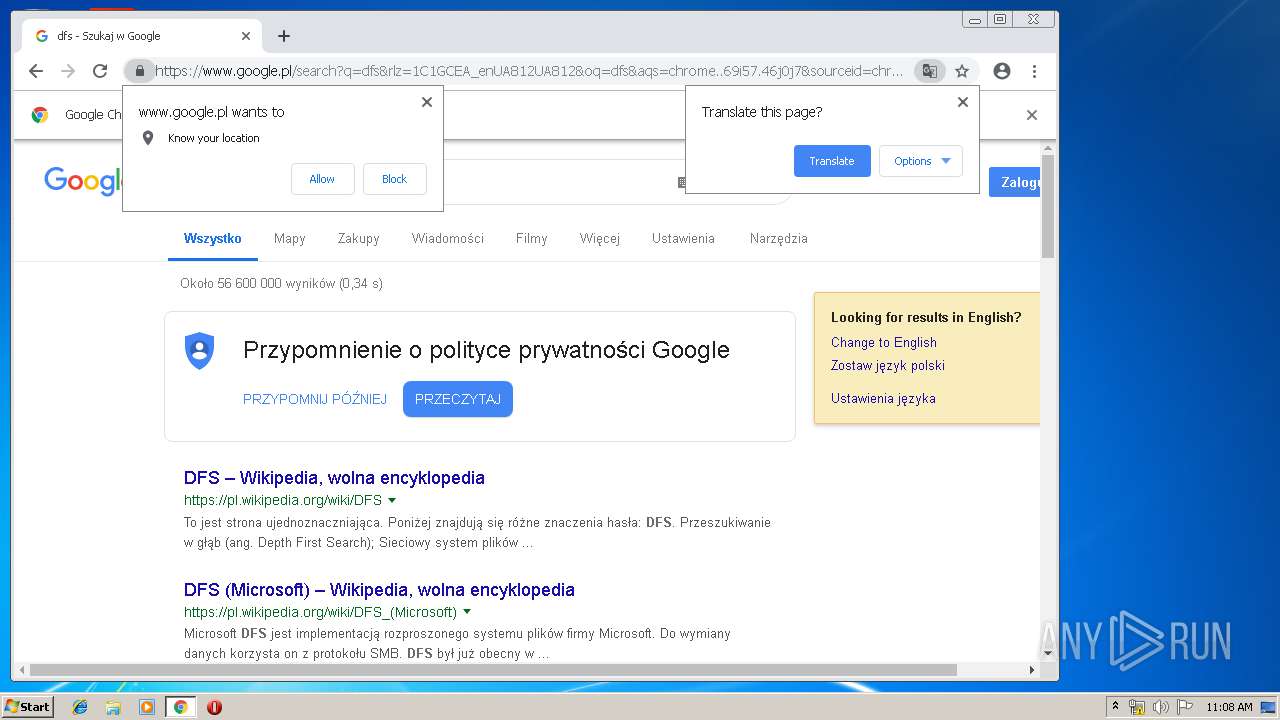
www.google.com |
| malicious |
www.google.pl |
| whitelisted |