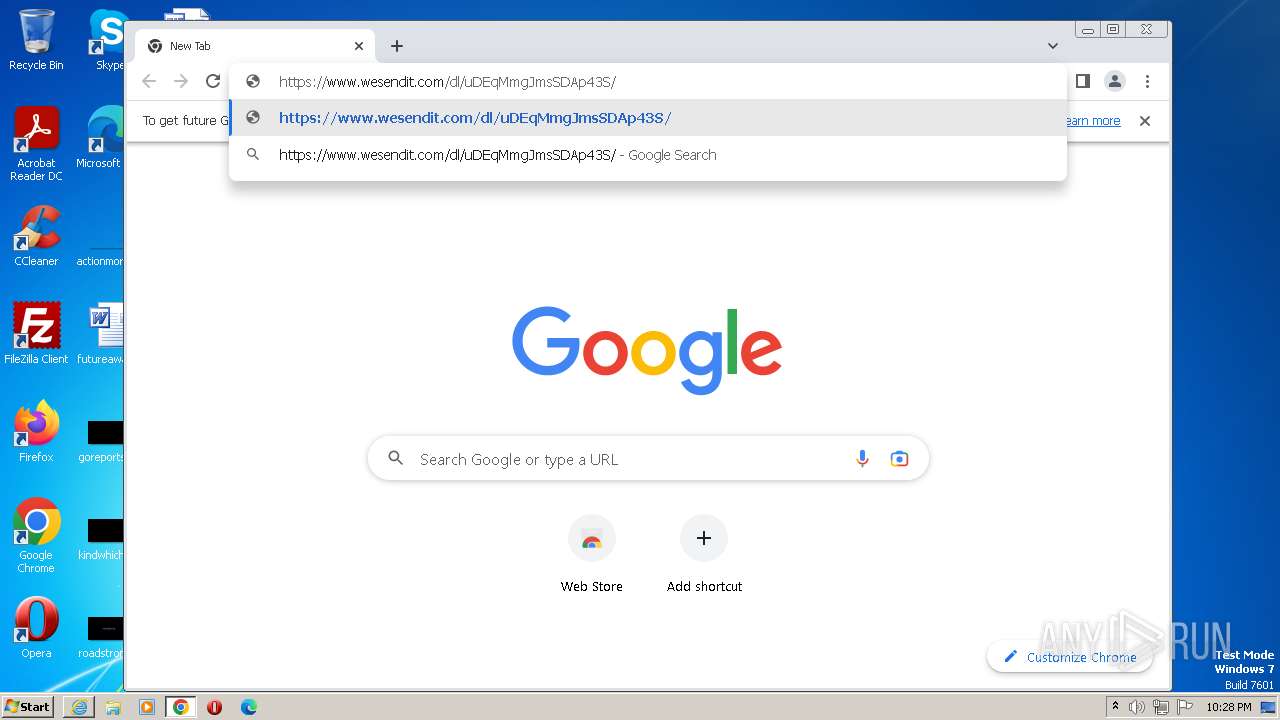
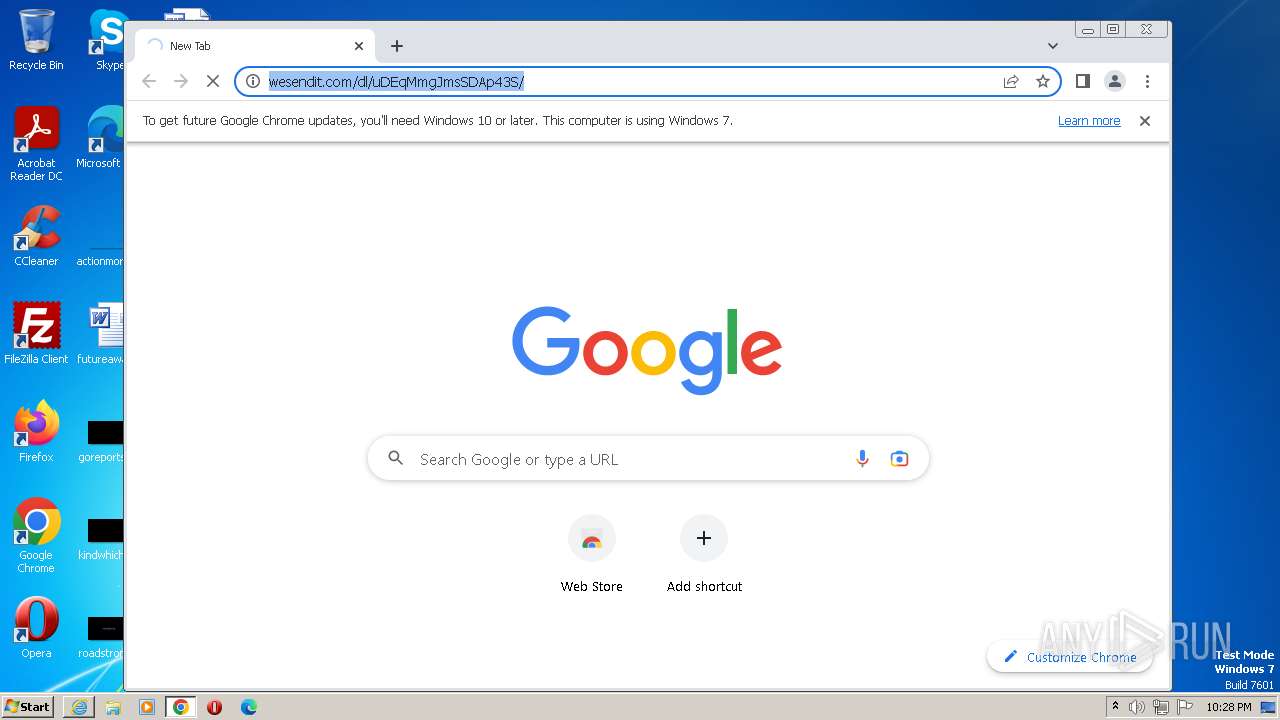
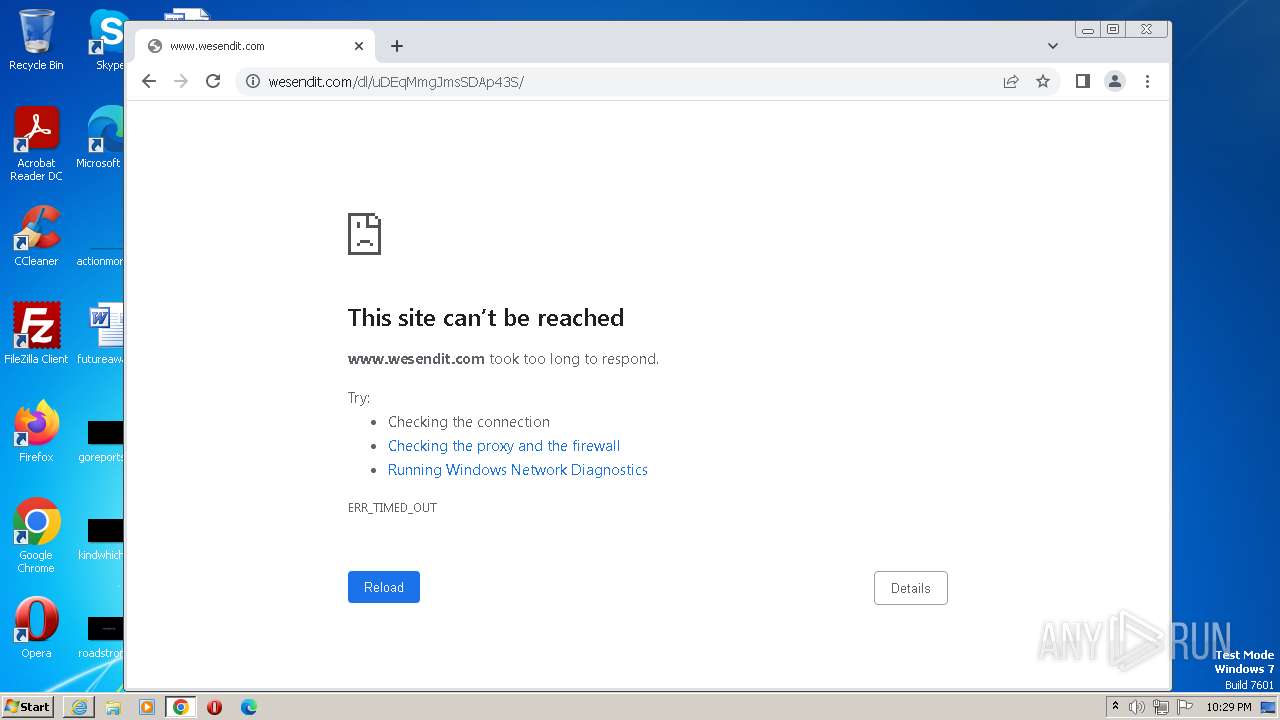
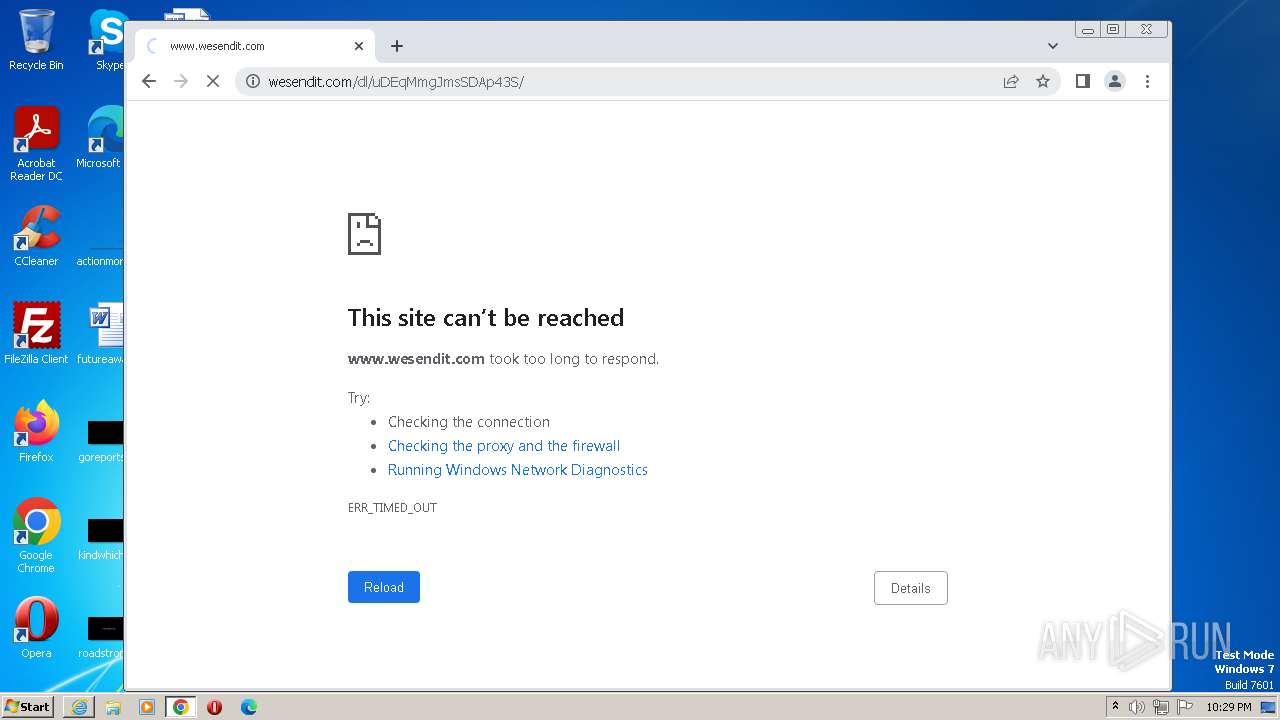
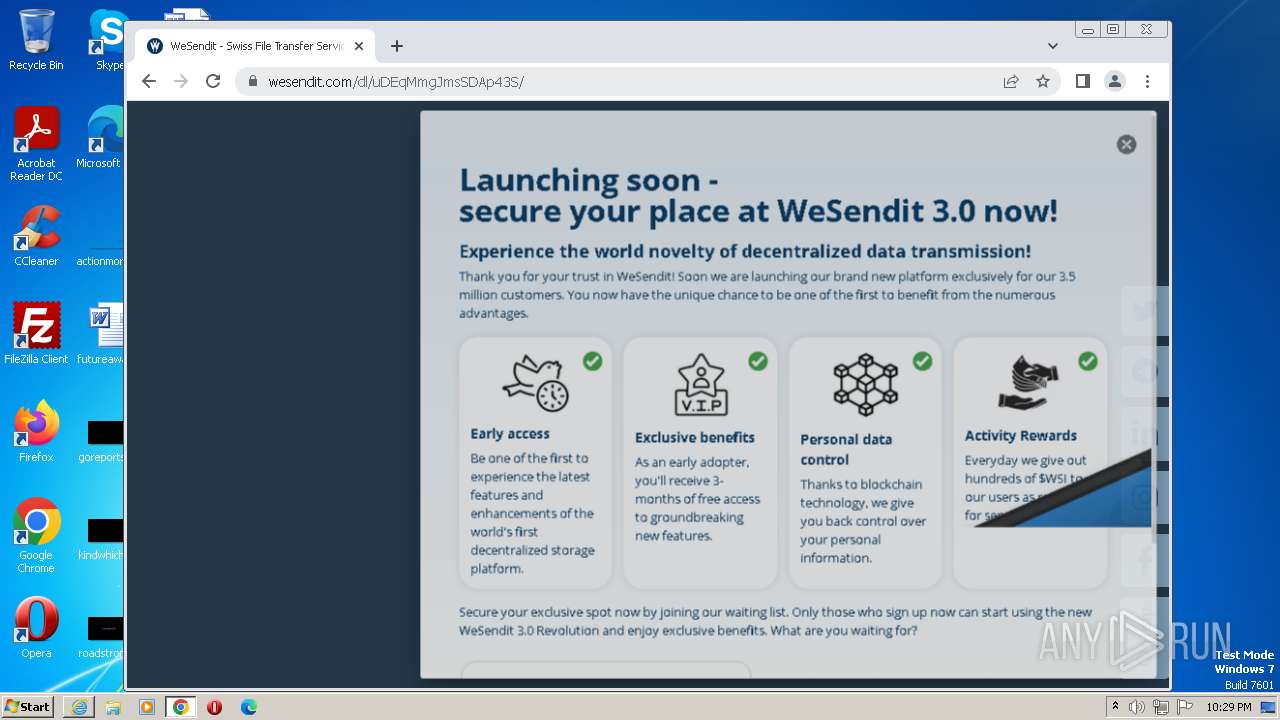
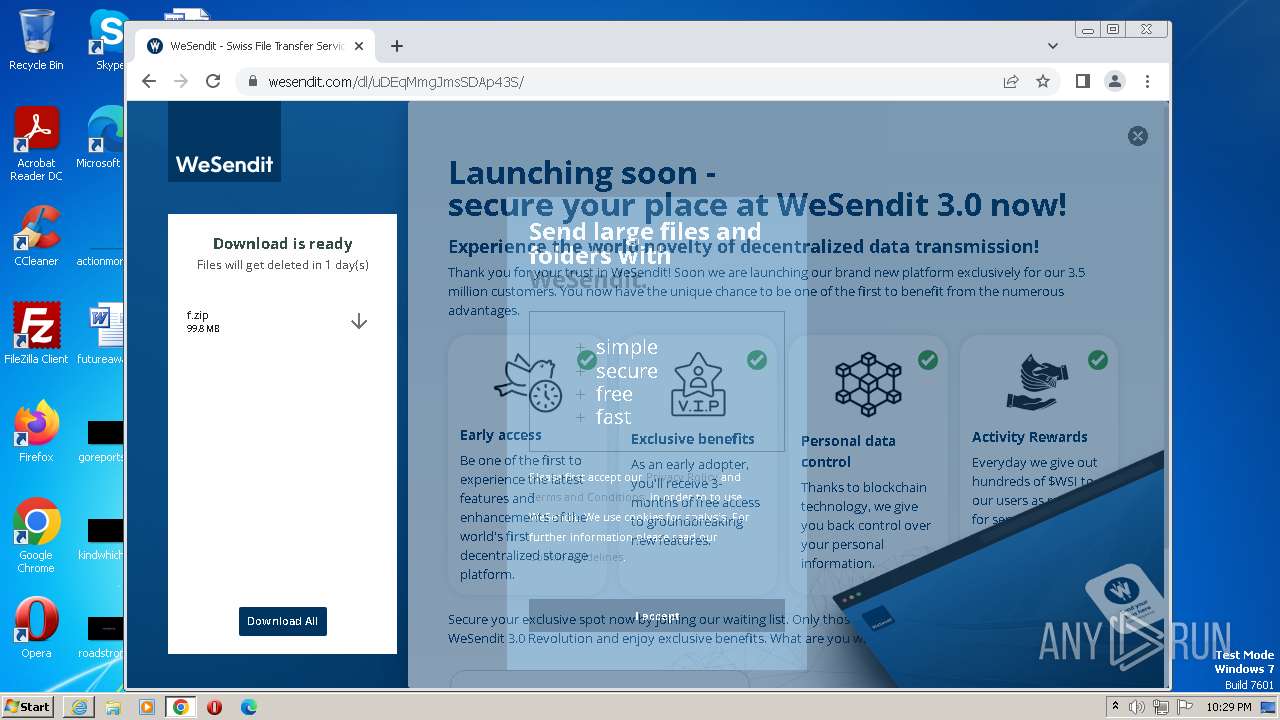
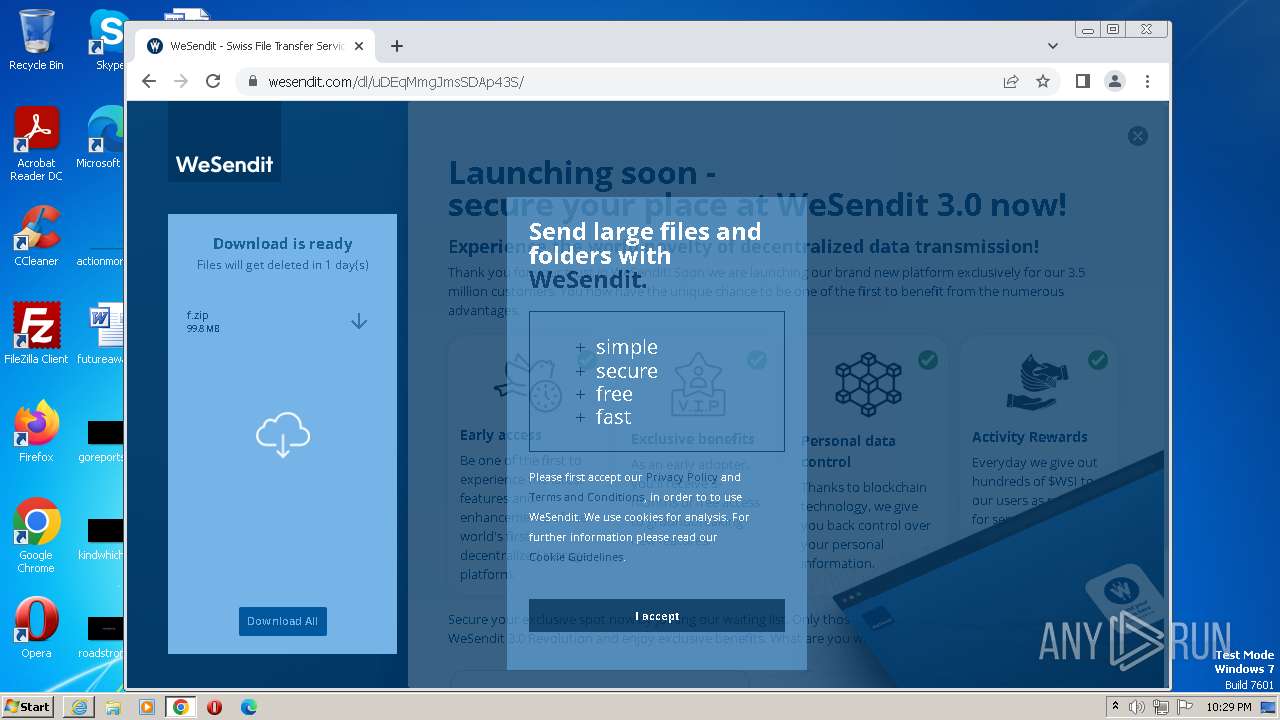
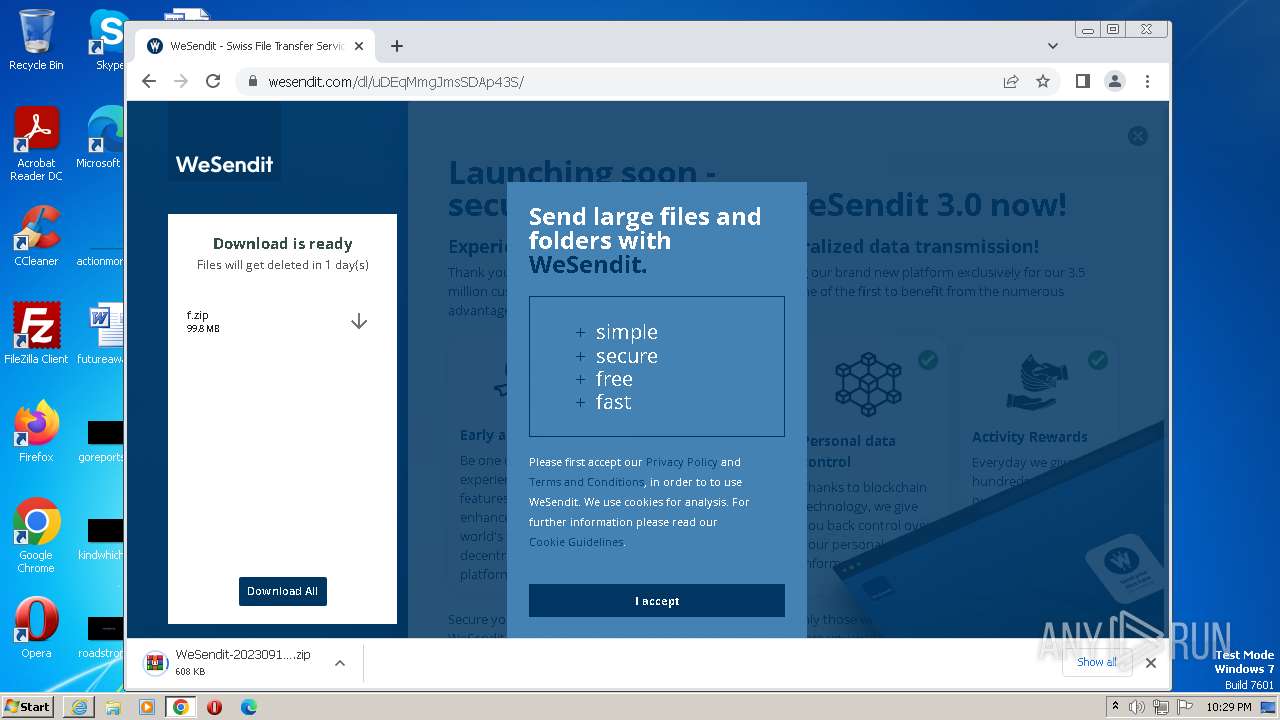
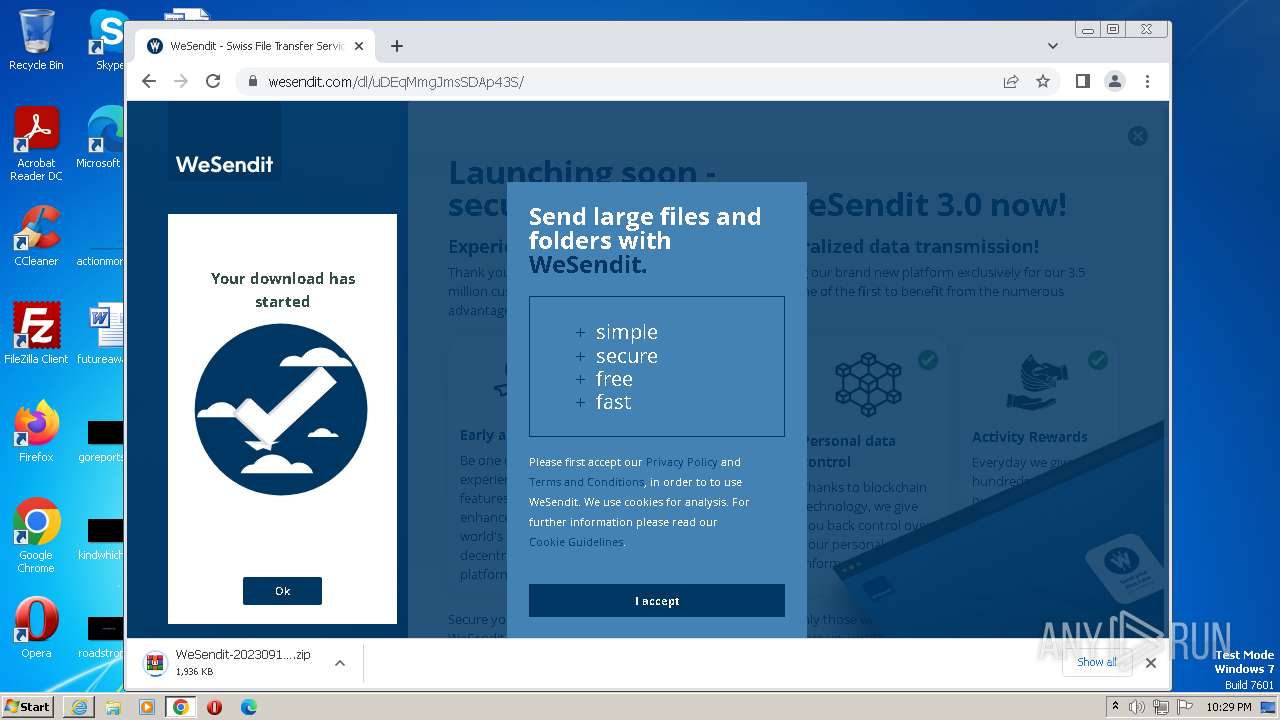
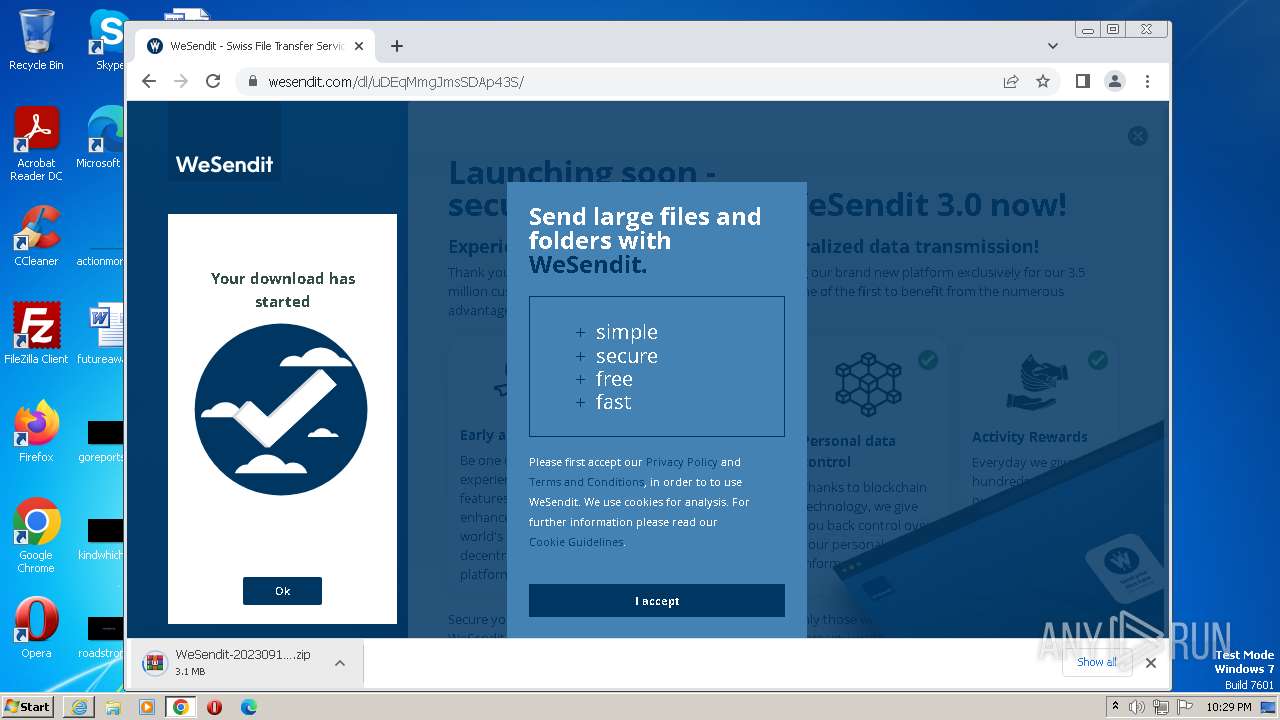
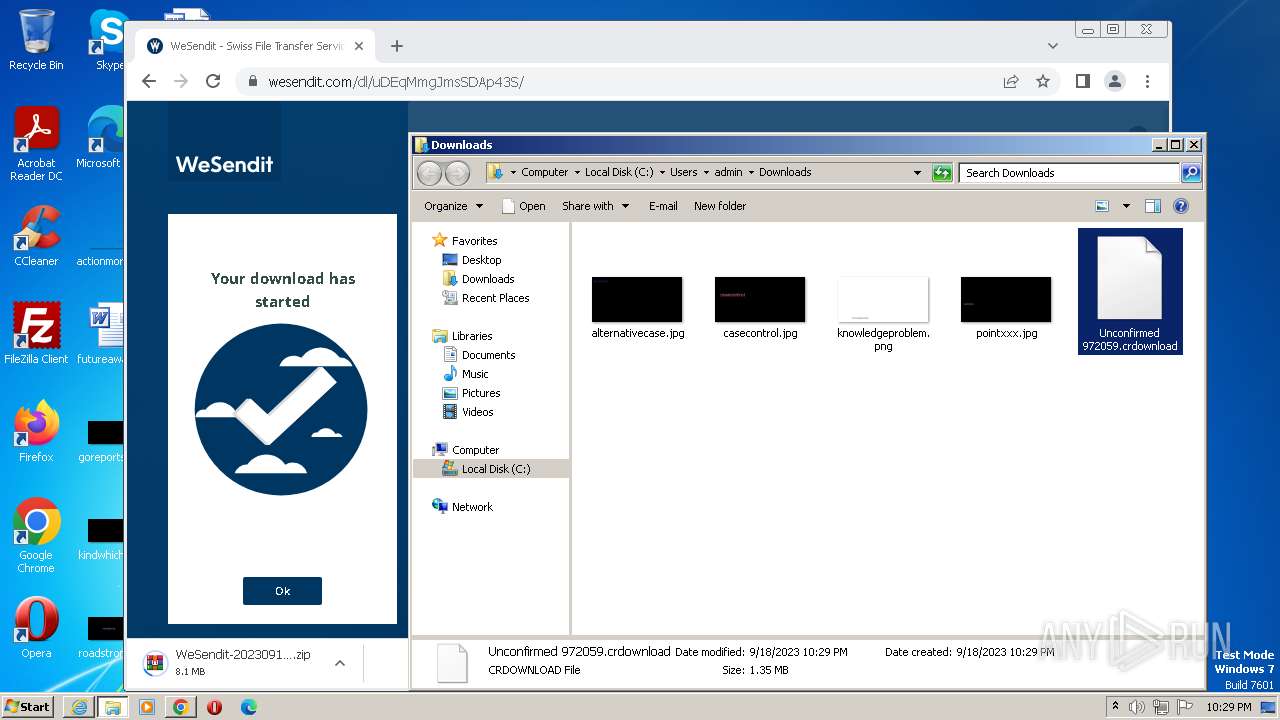
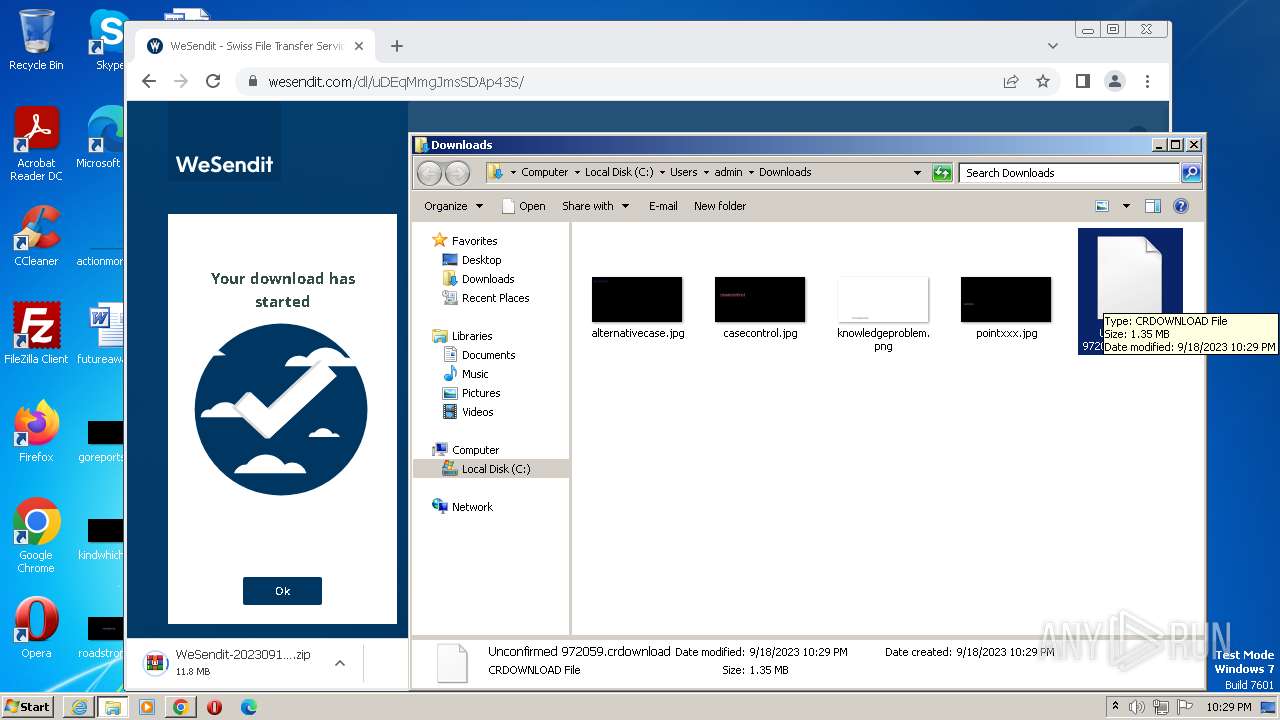
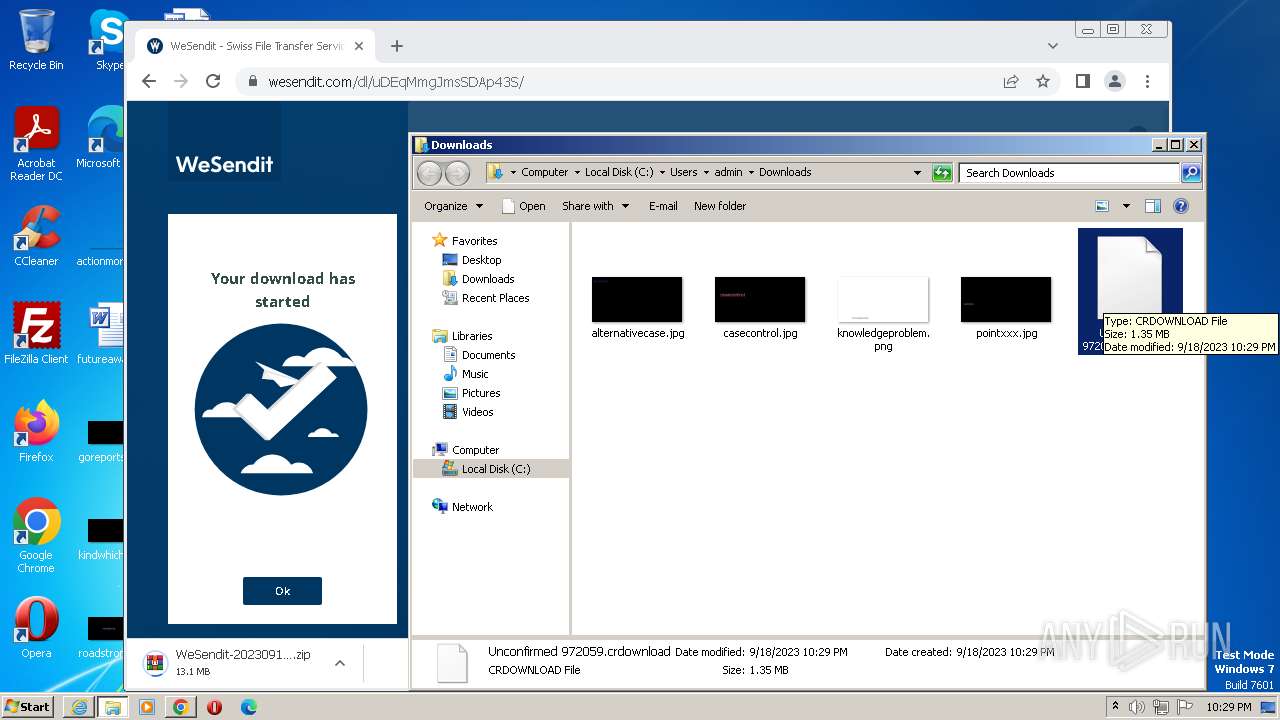
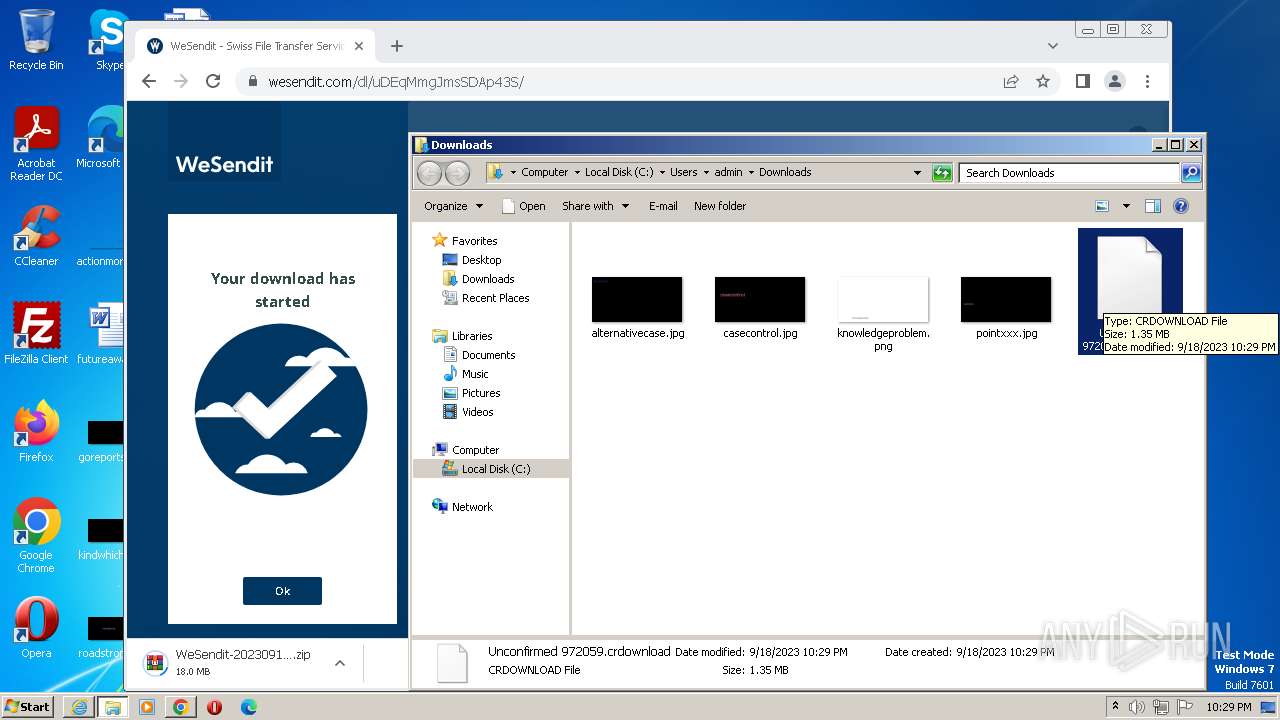
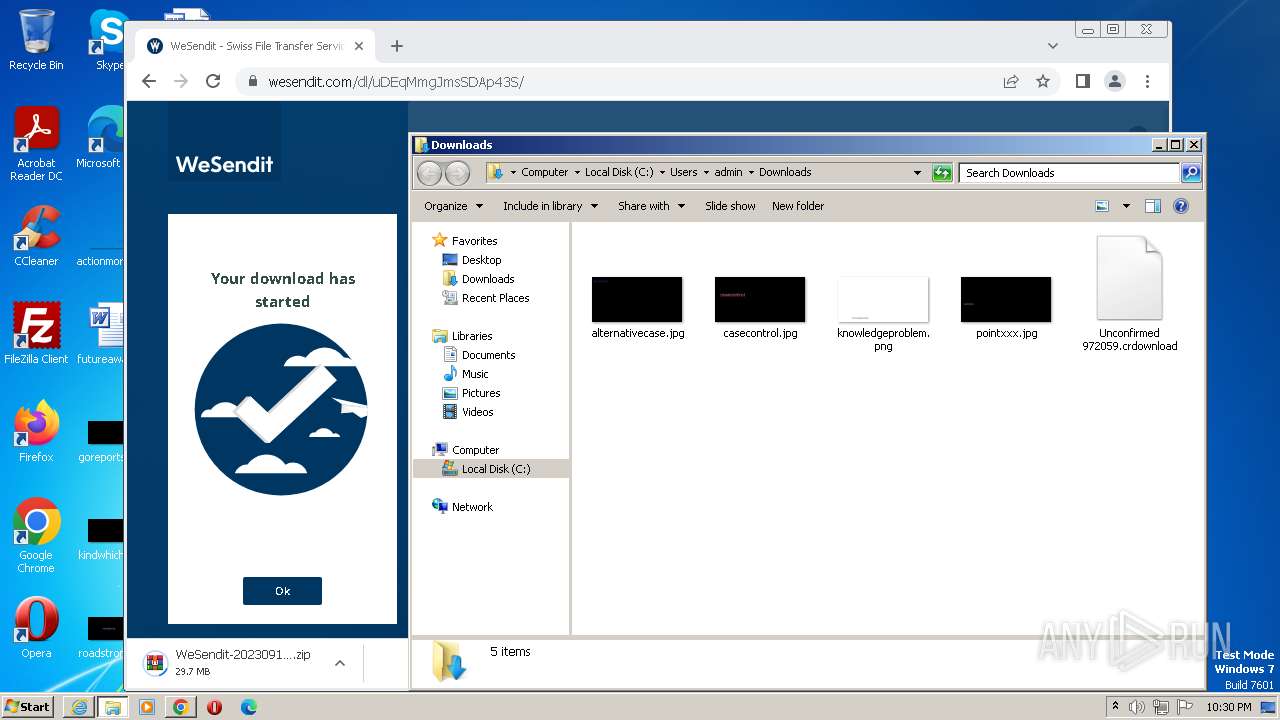
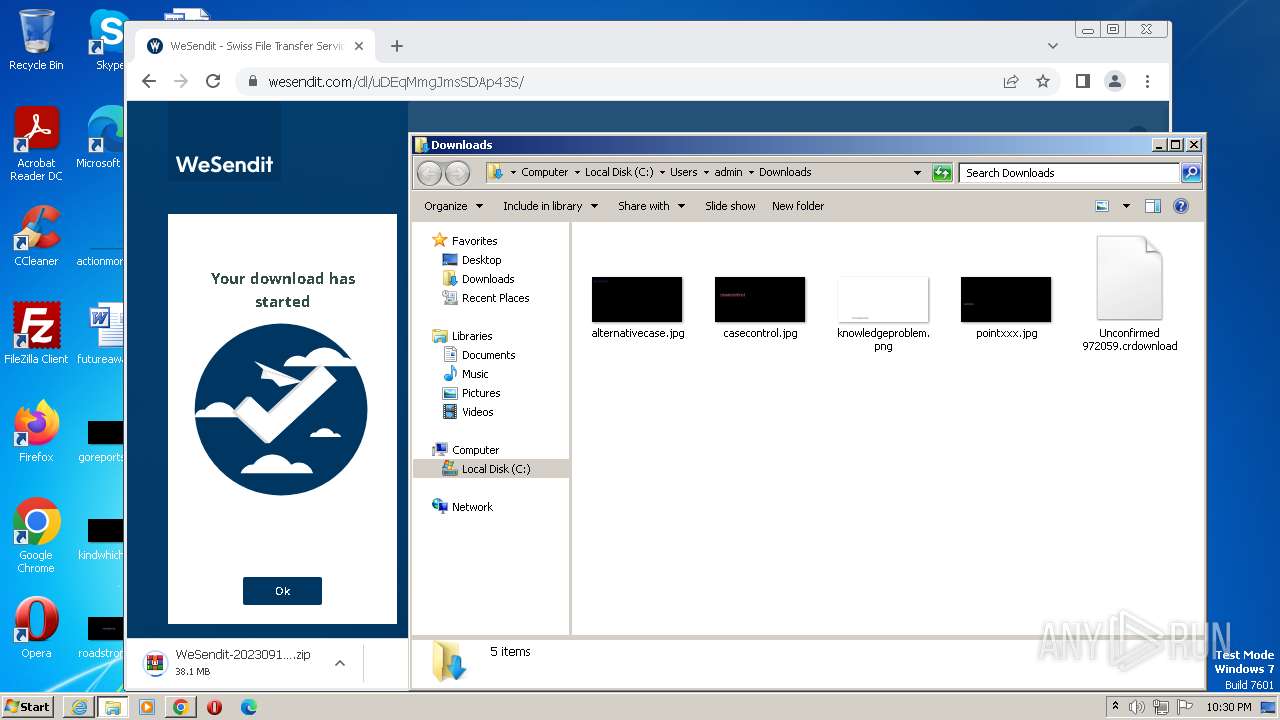
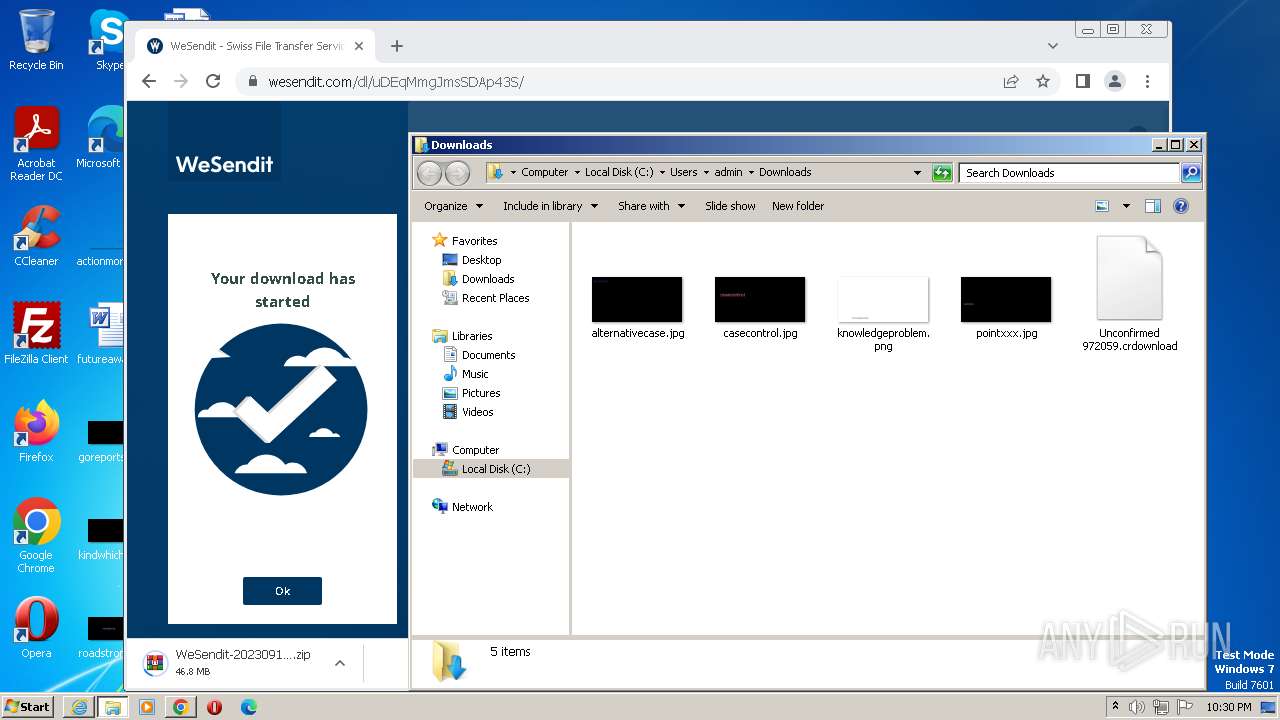
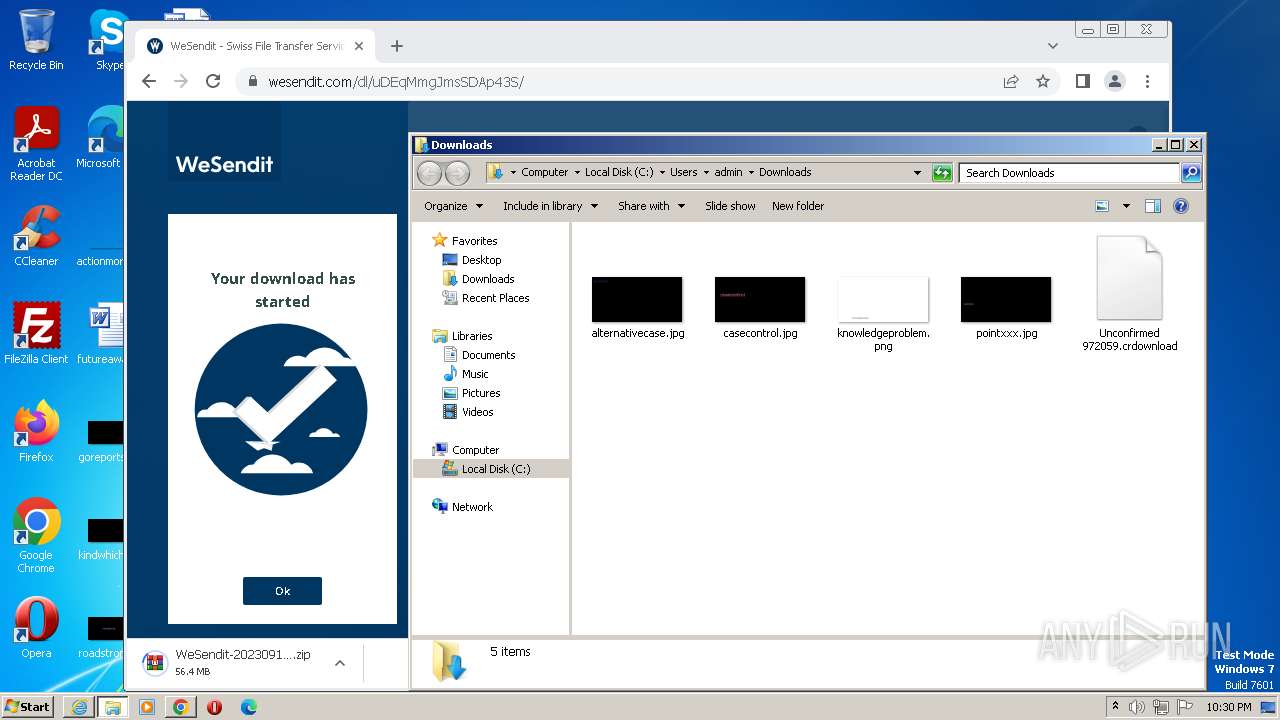
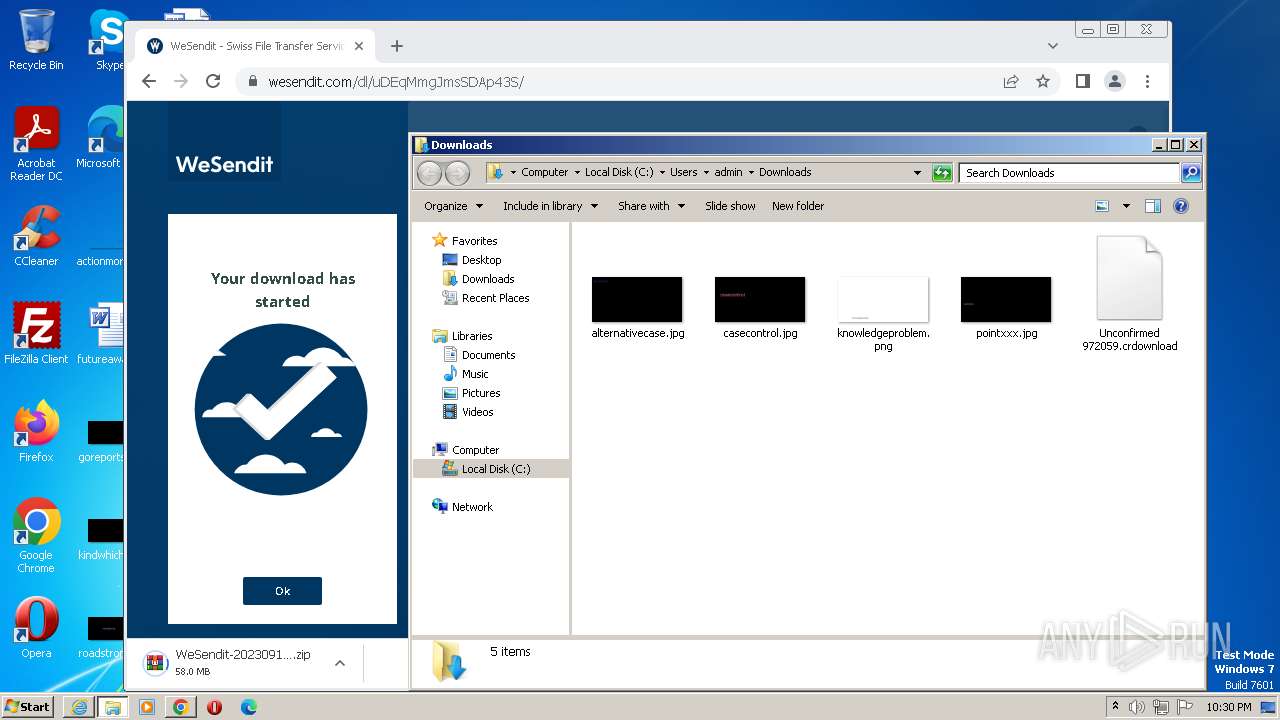
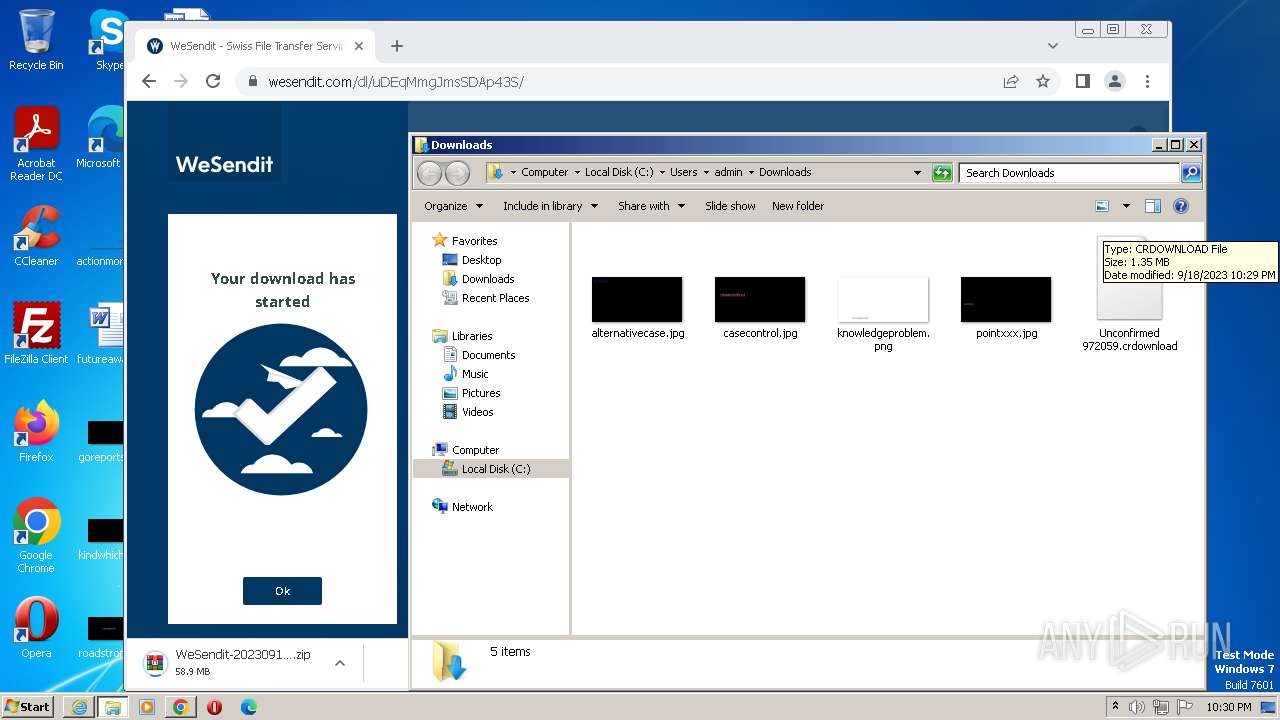
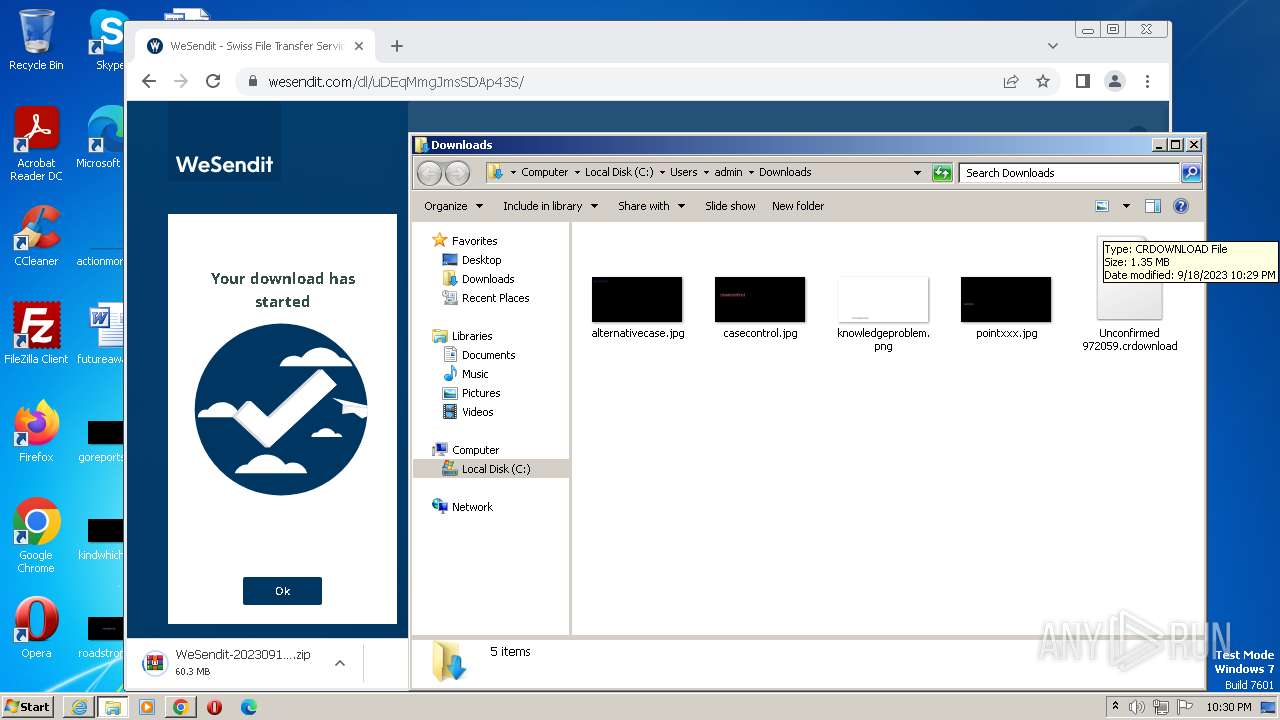
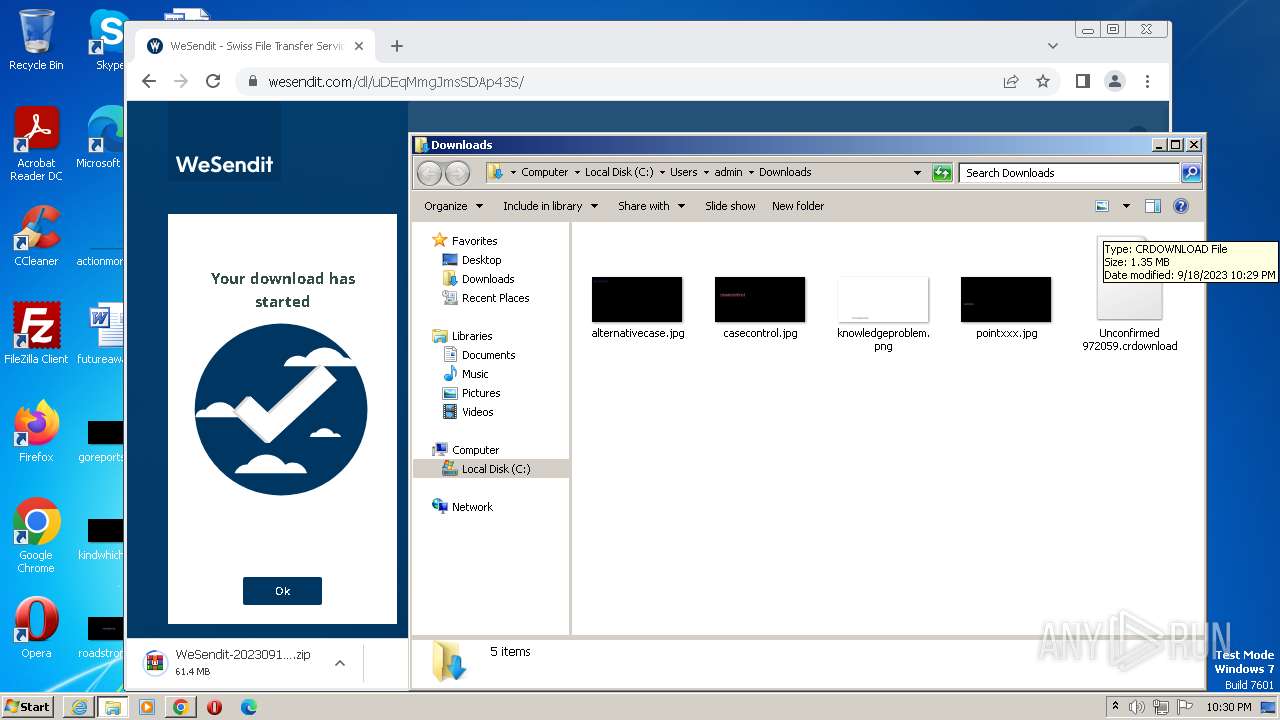
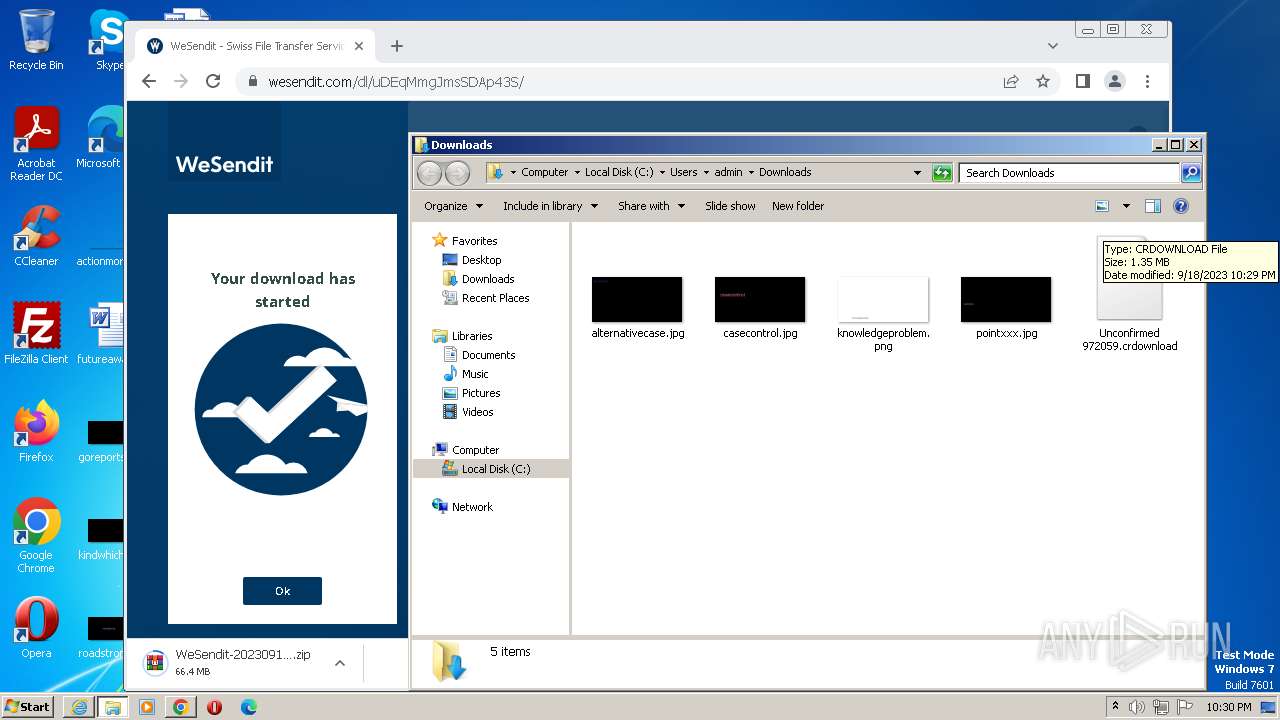
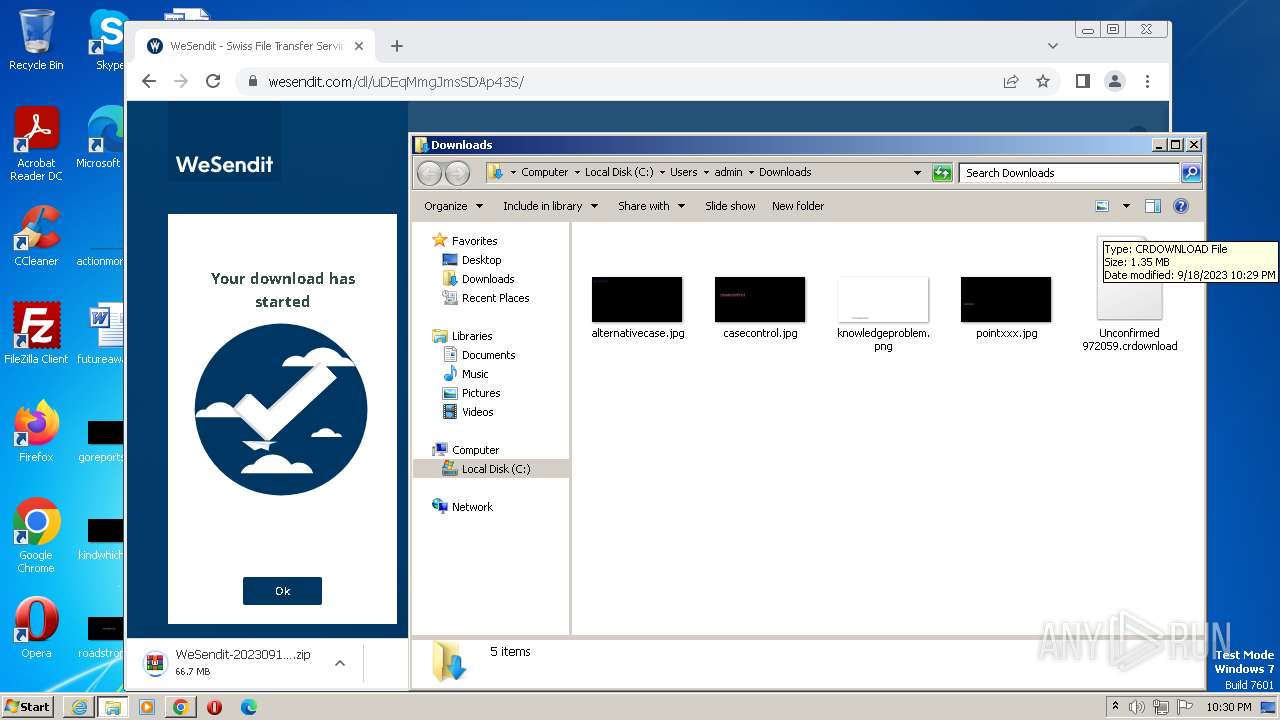
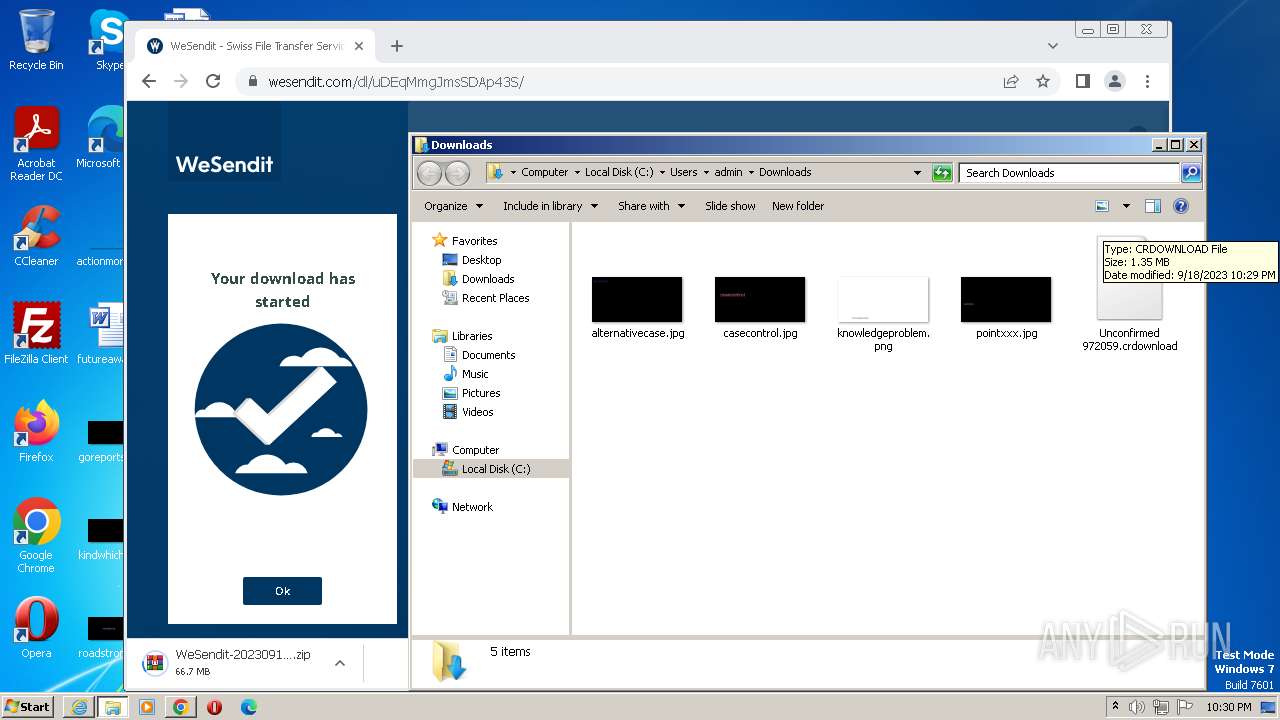
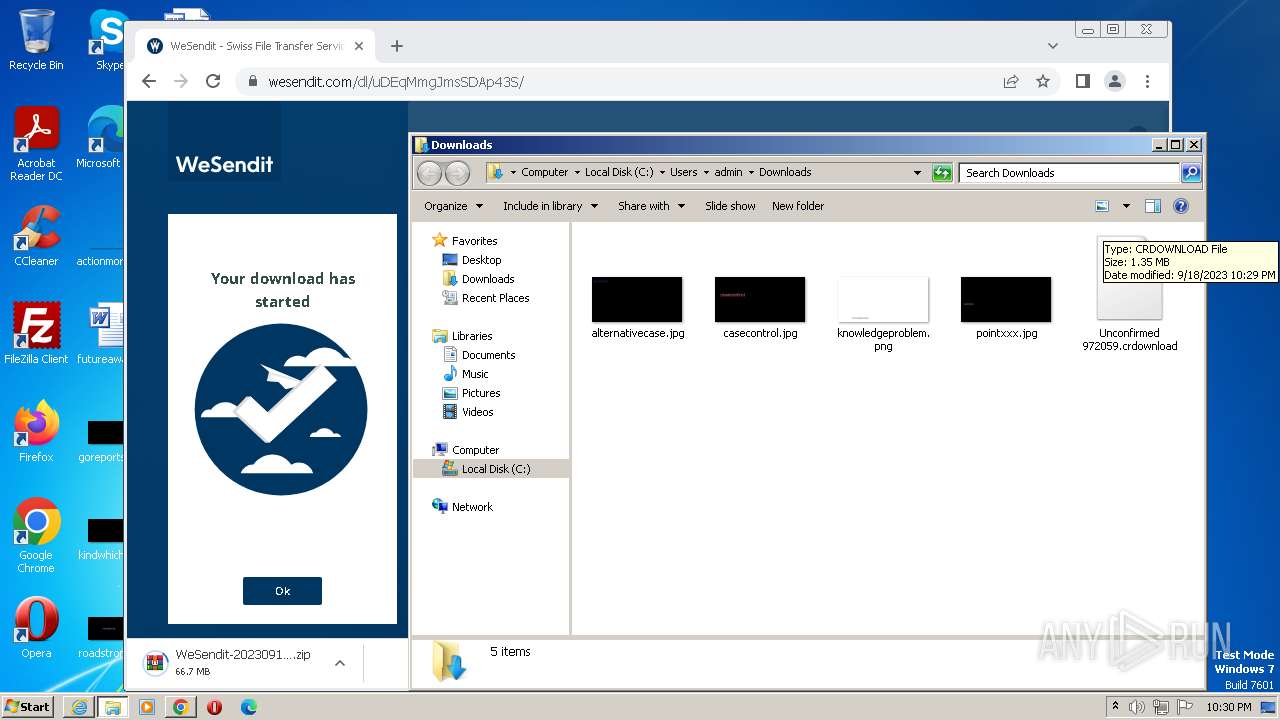
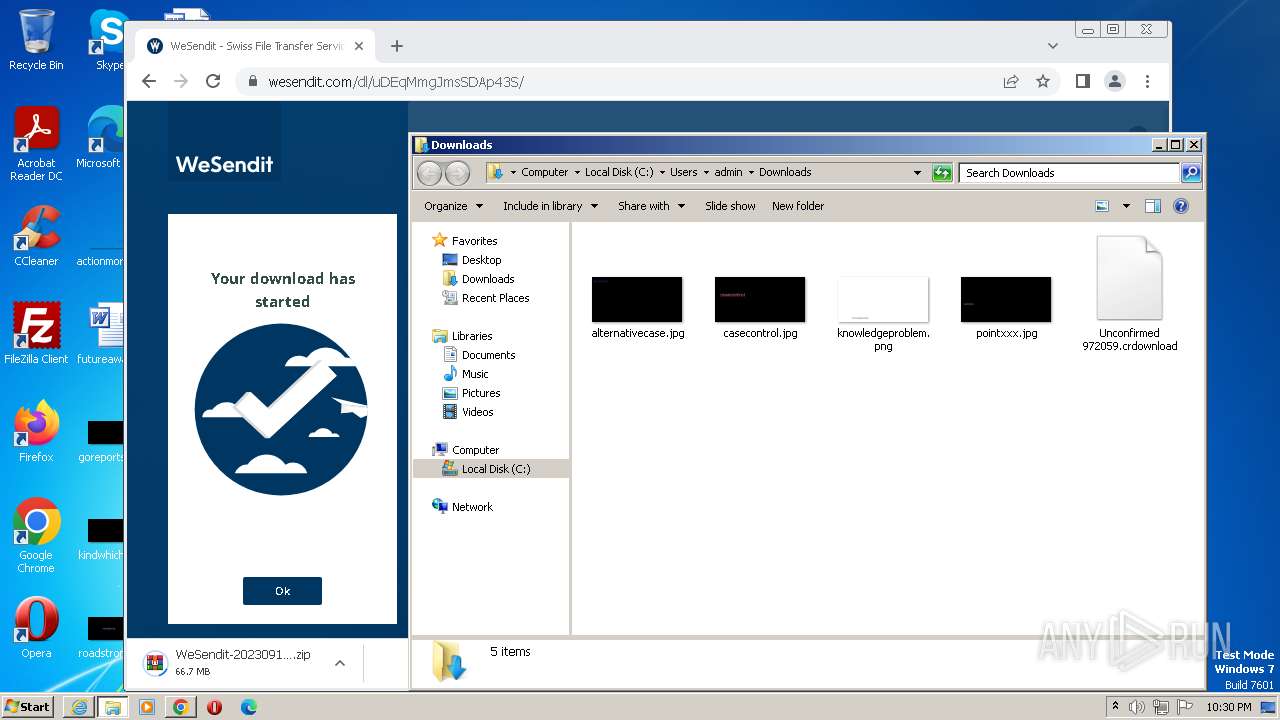
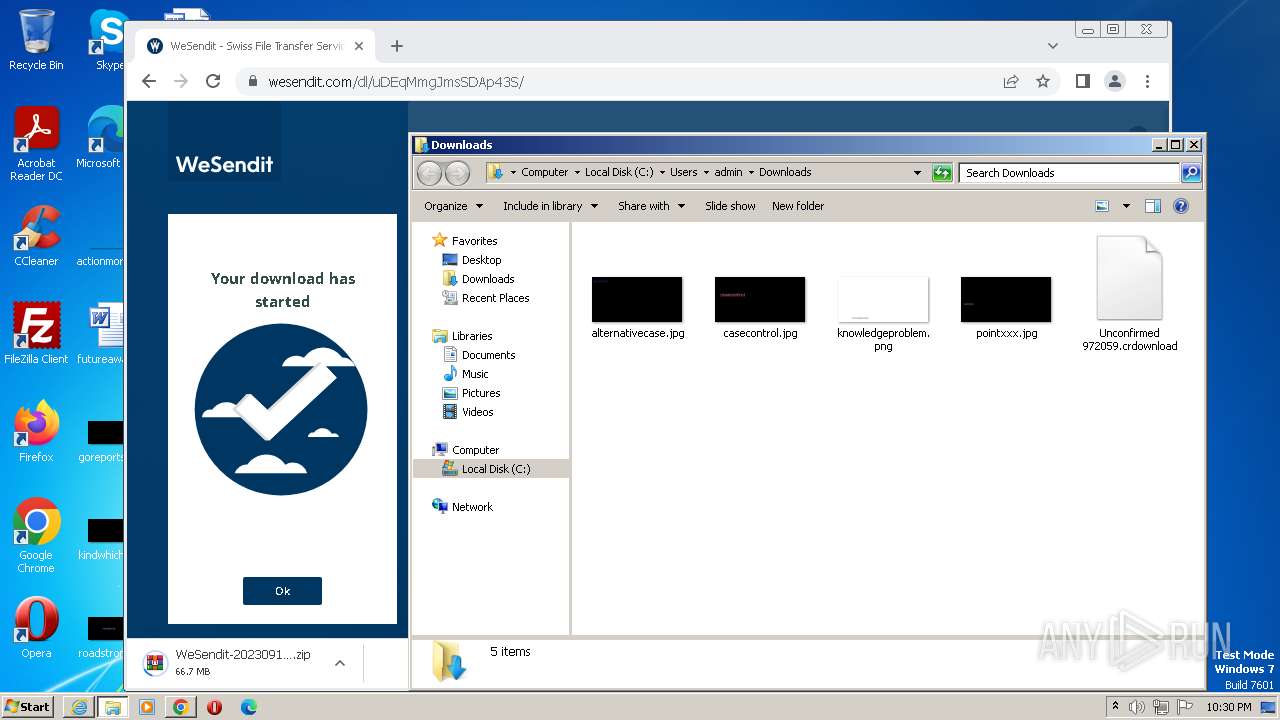
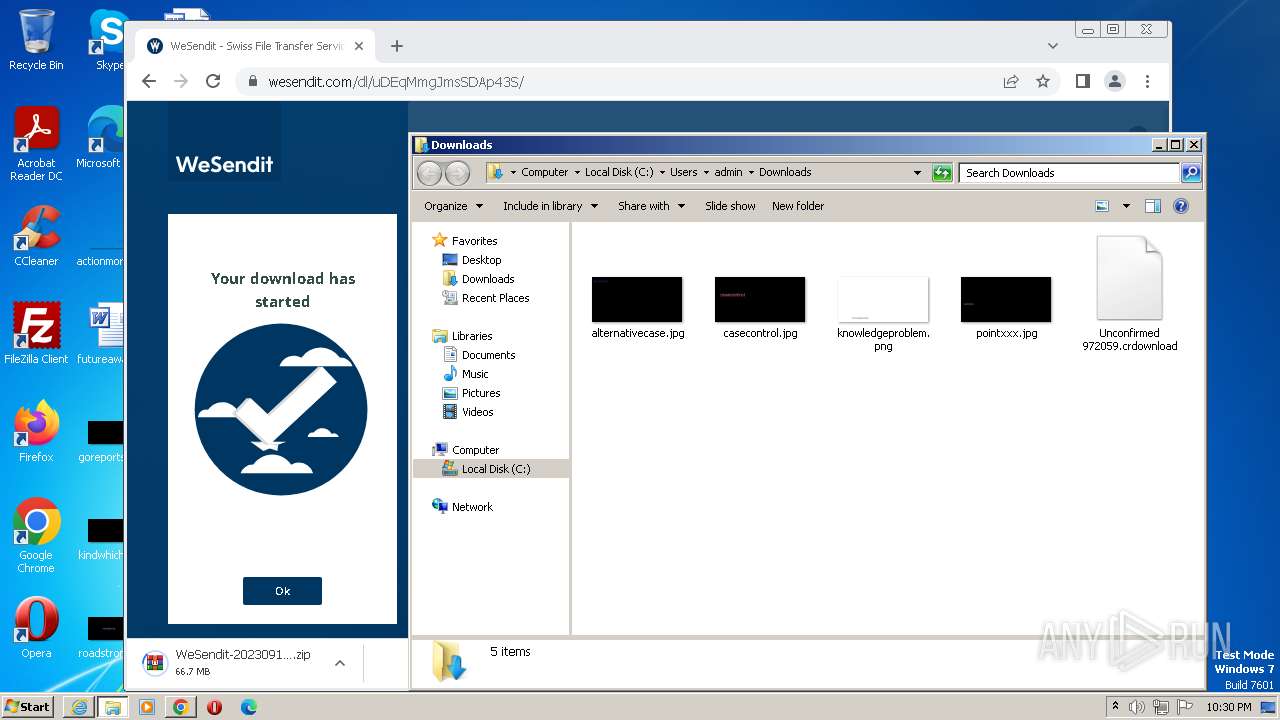
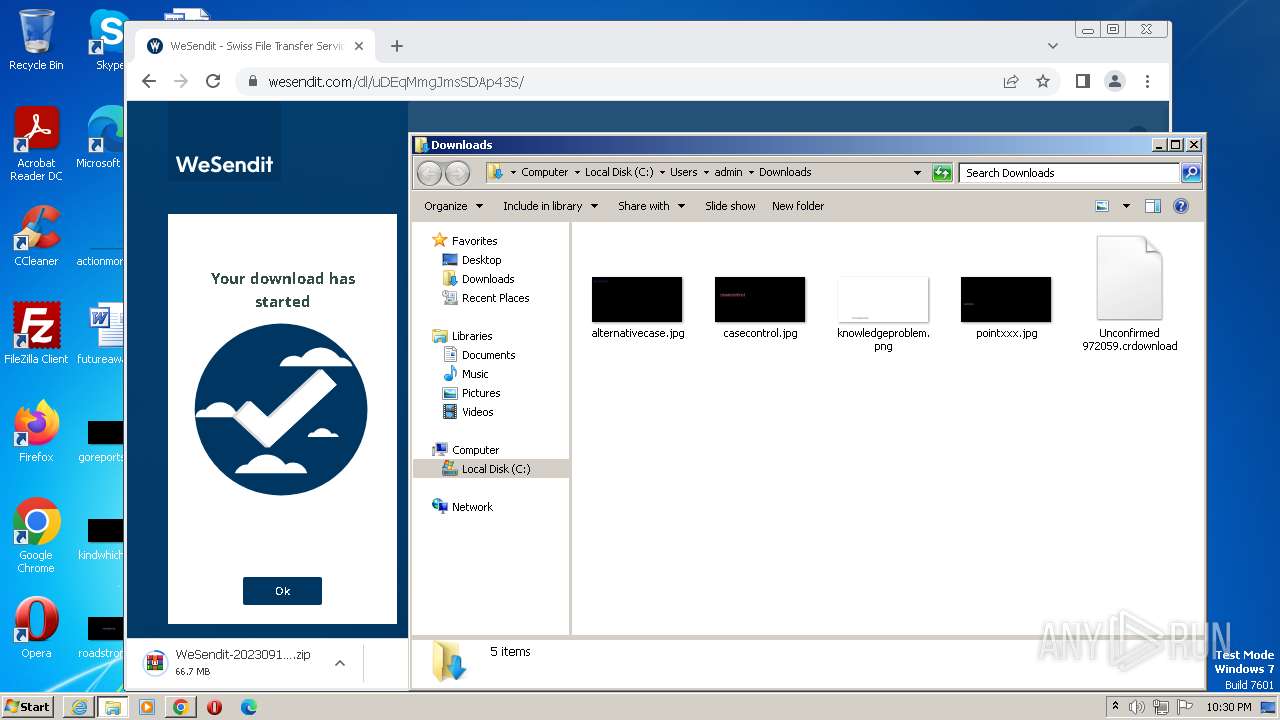
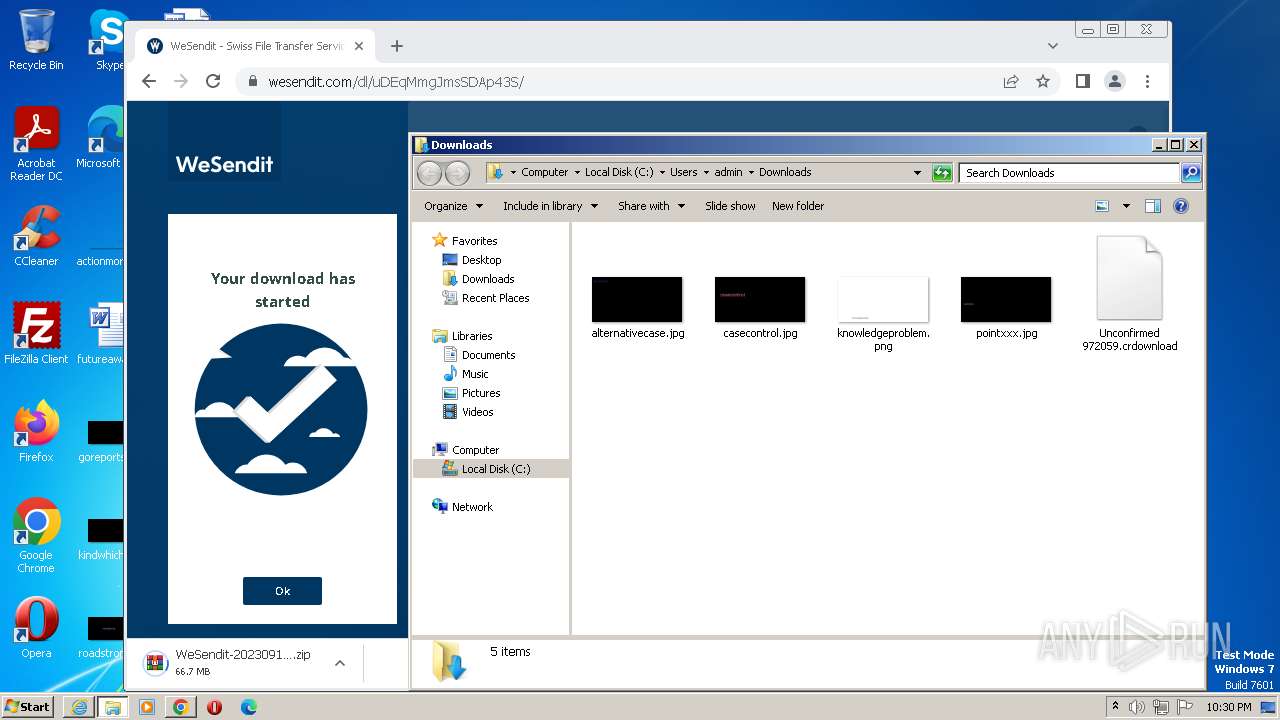
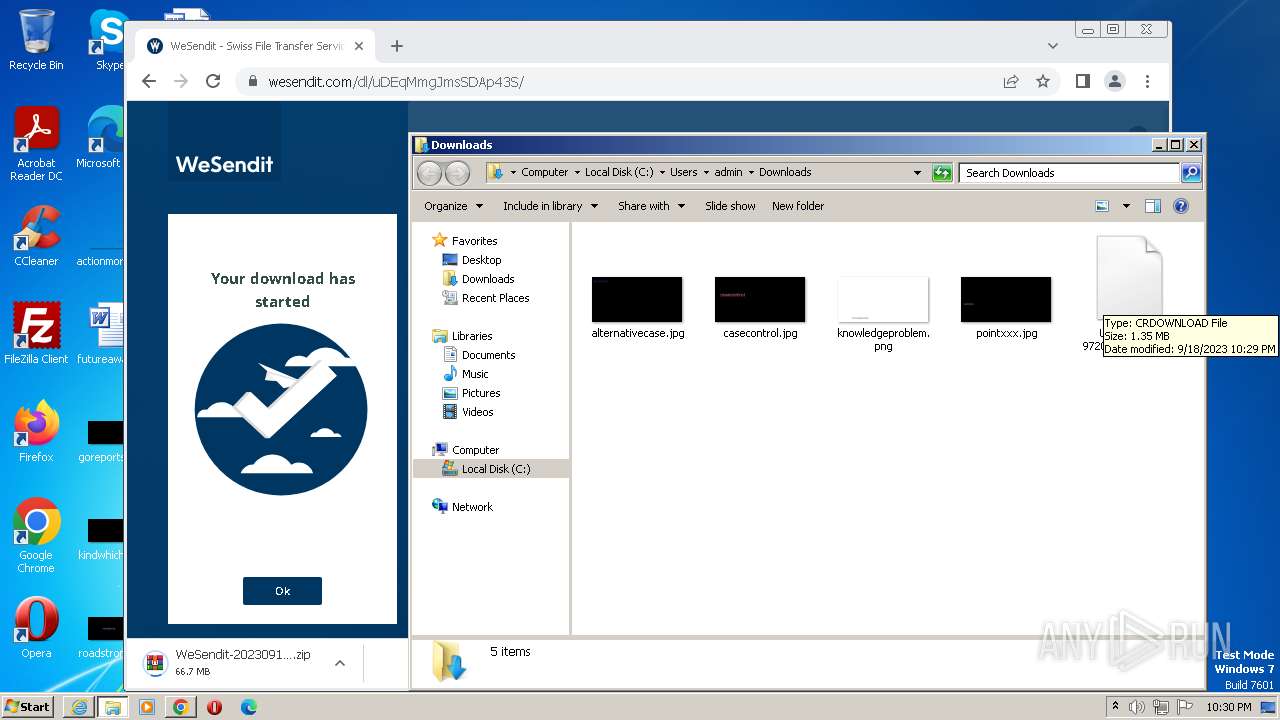
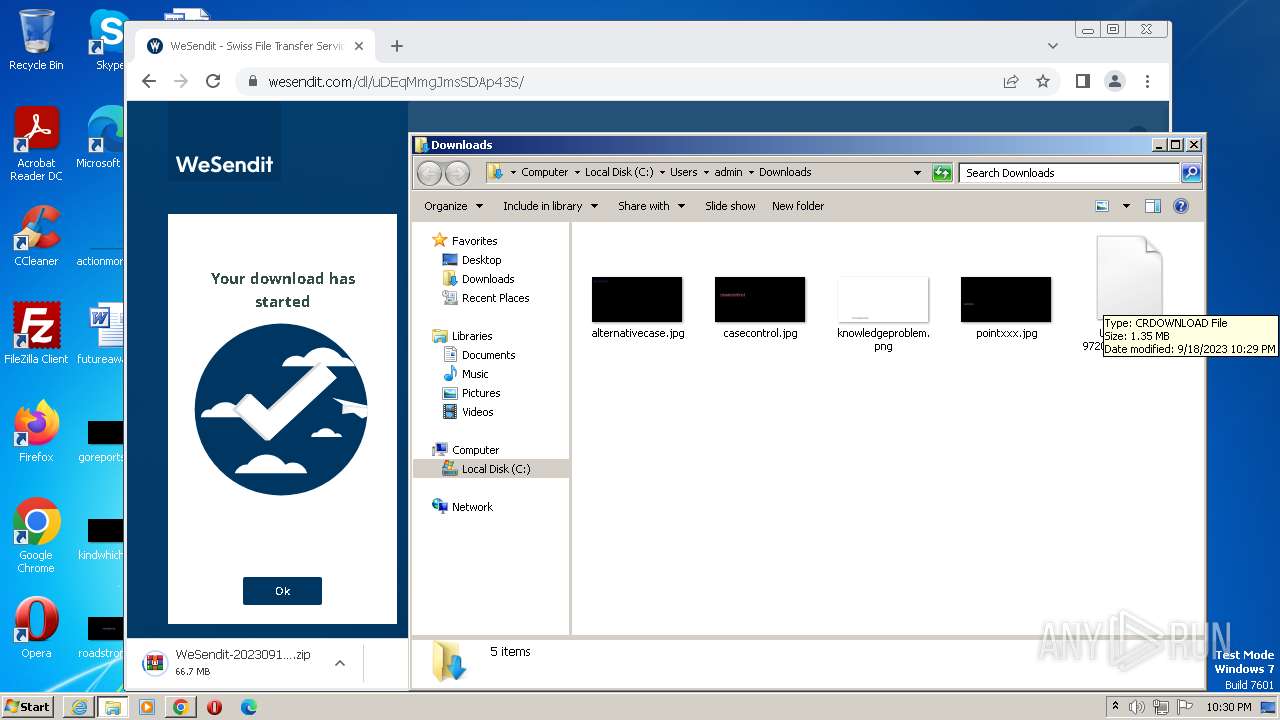
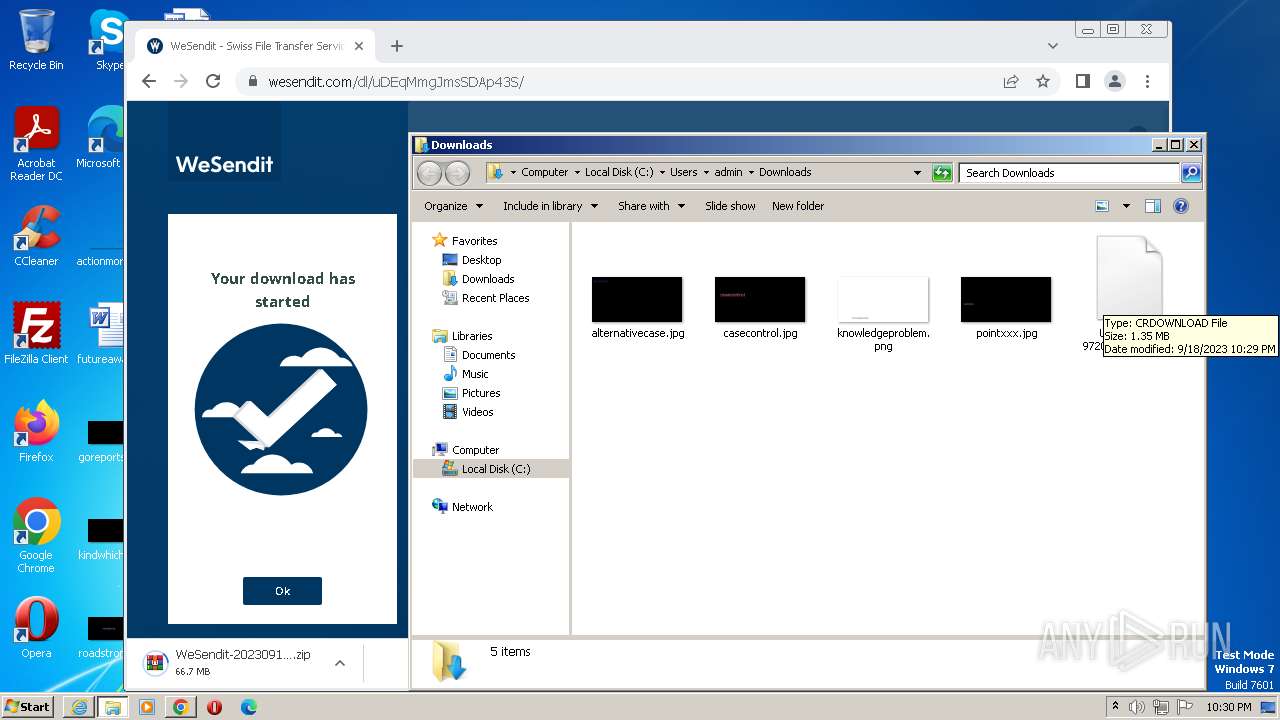
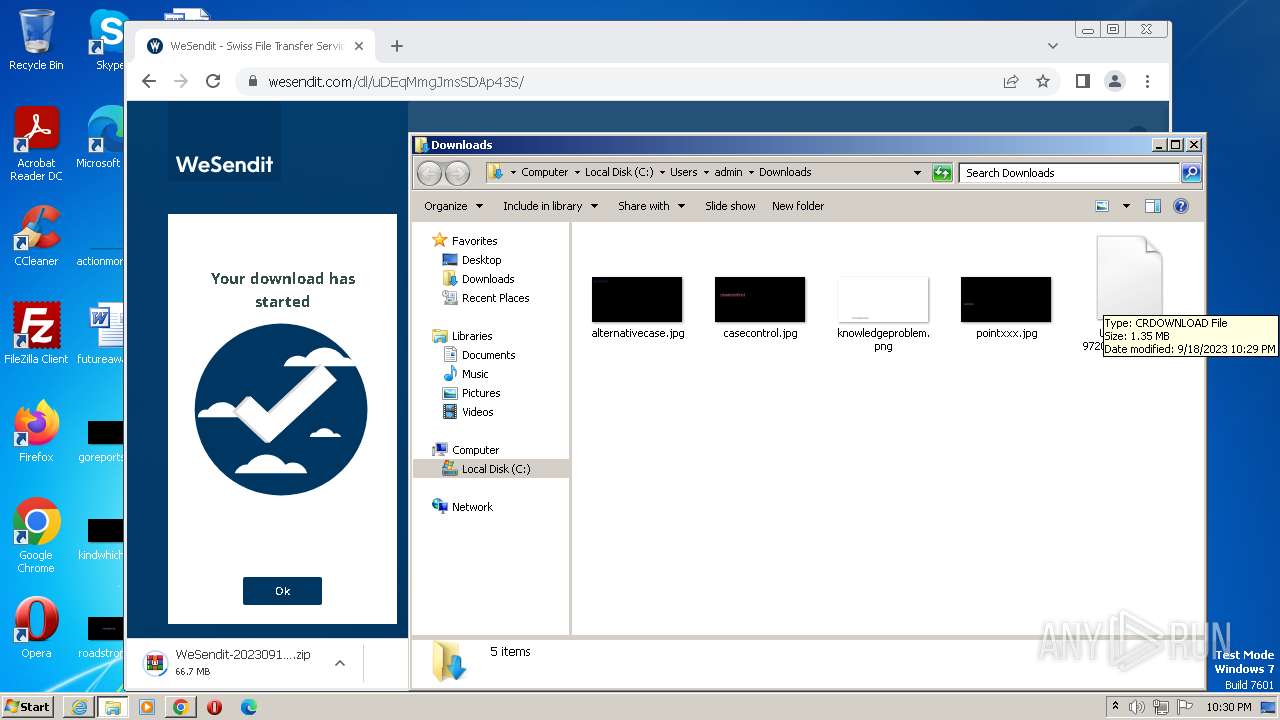
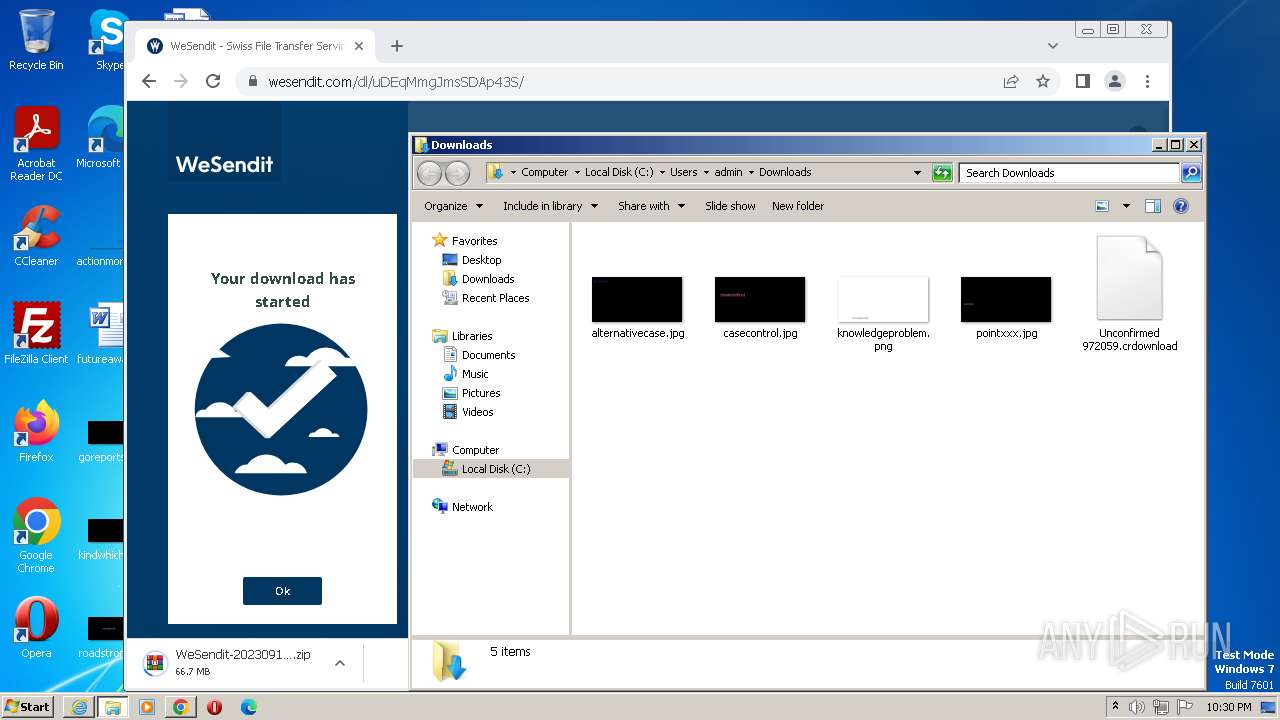
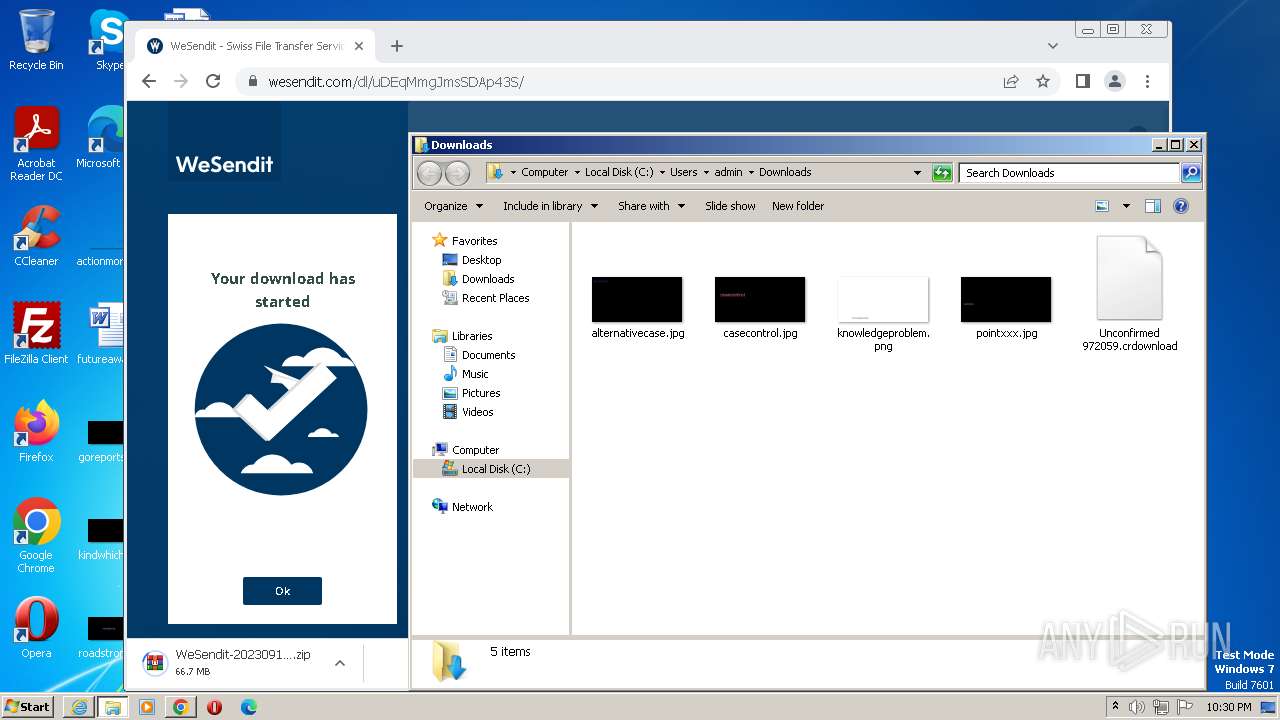
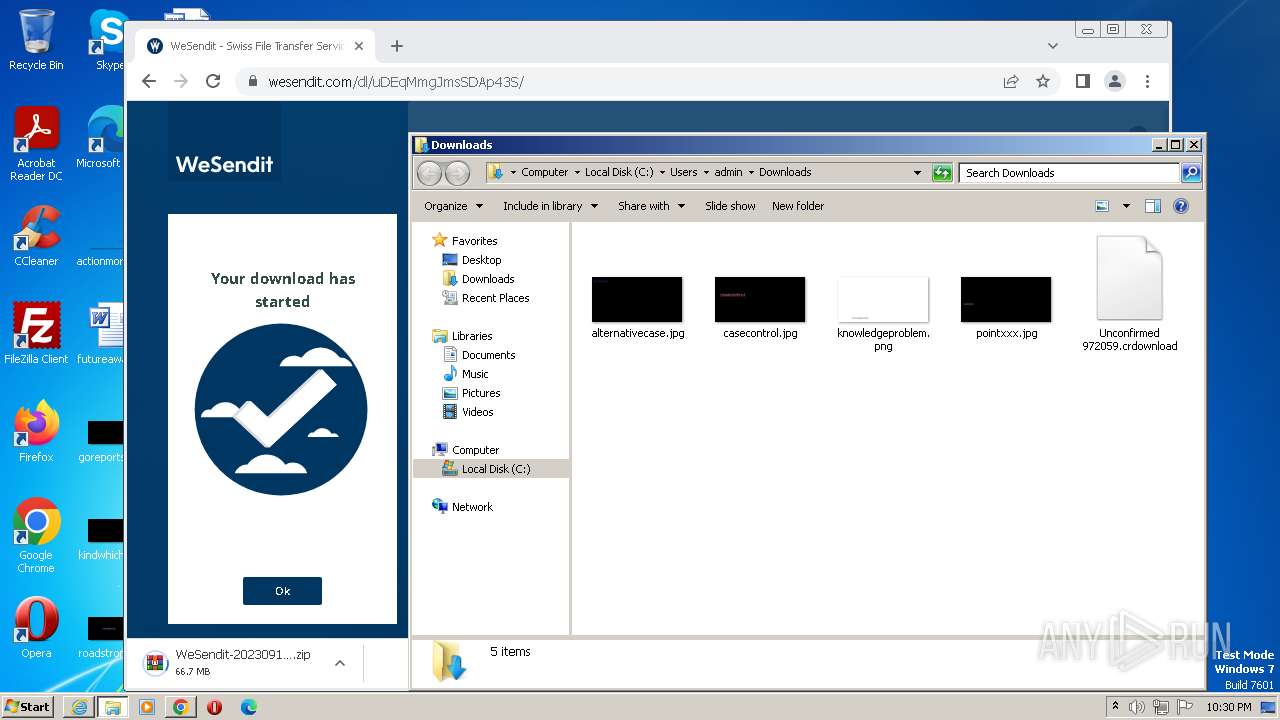
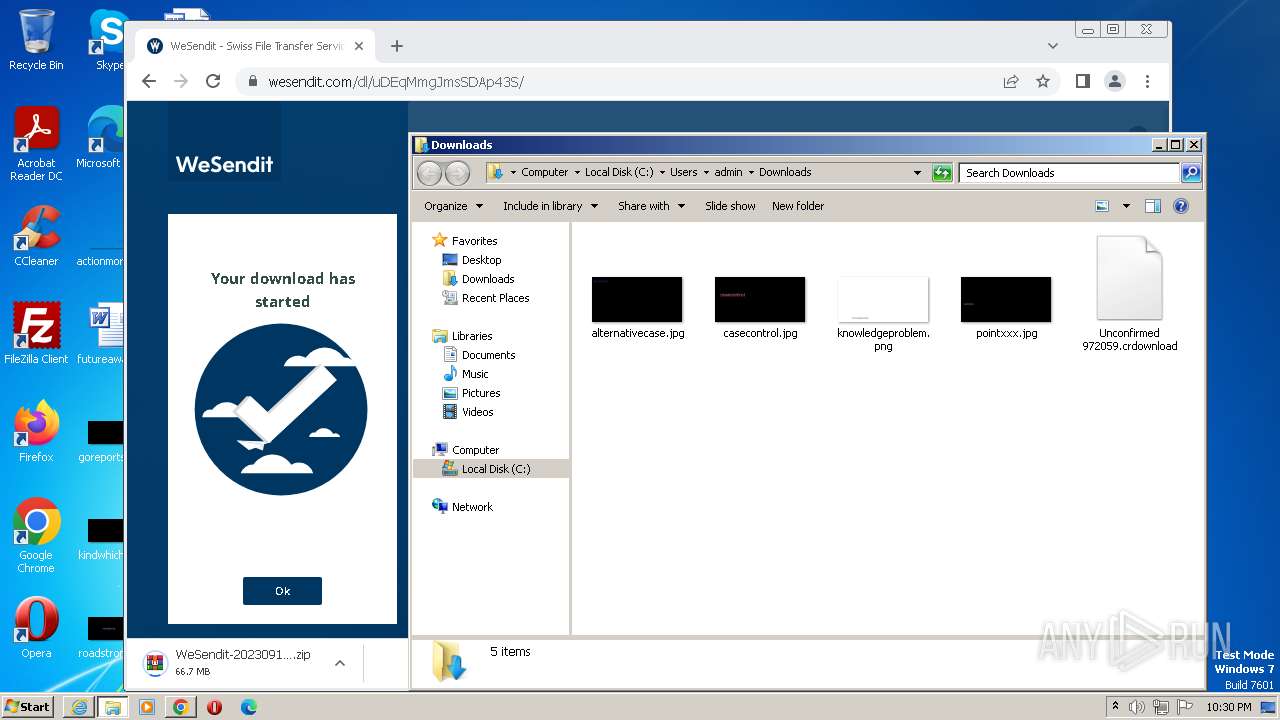
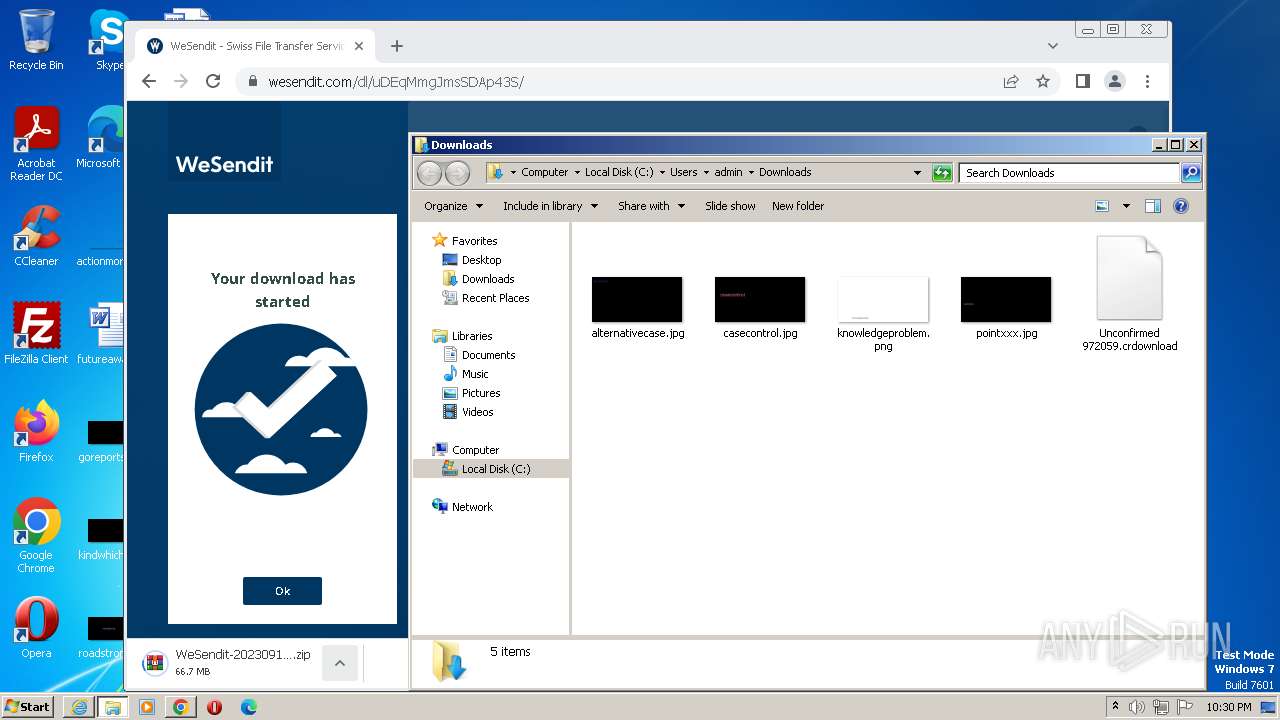
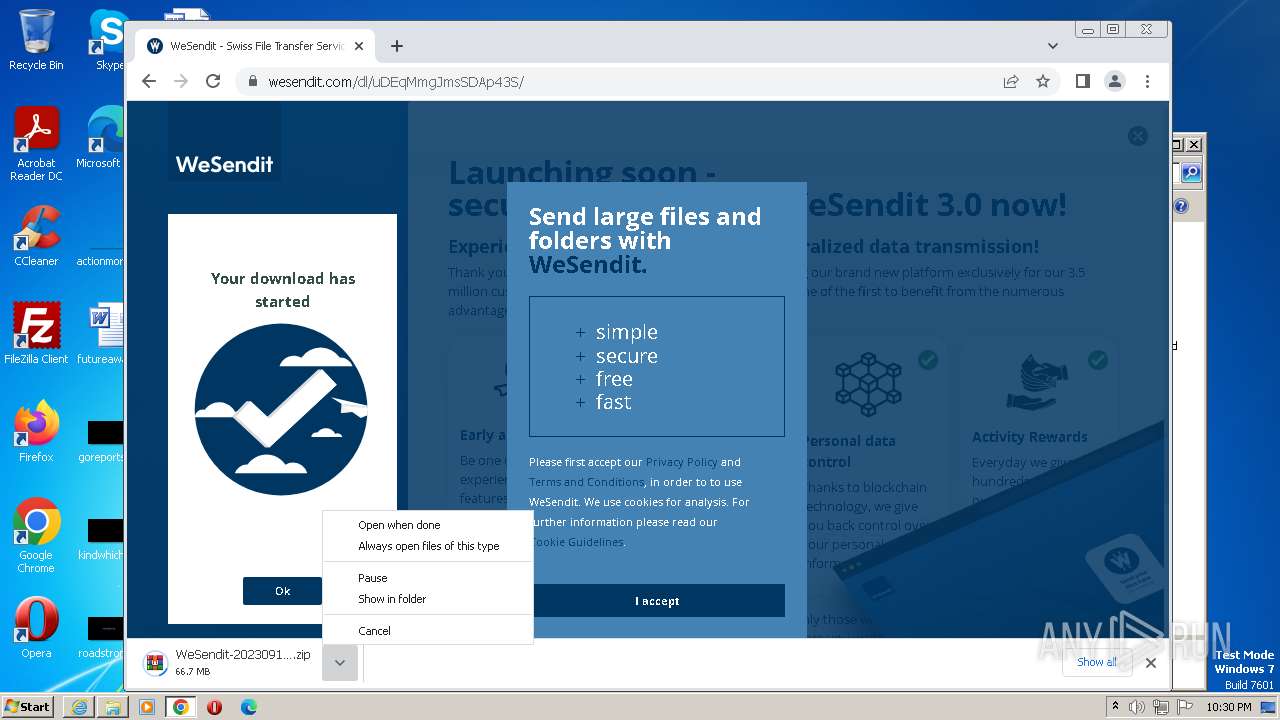
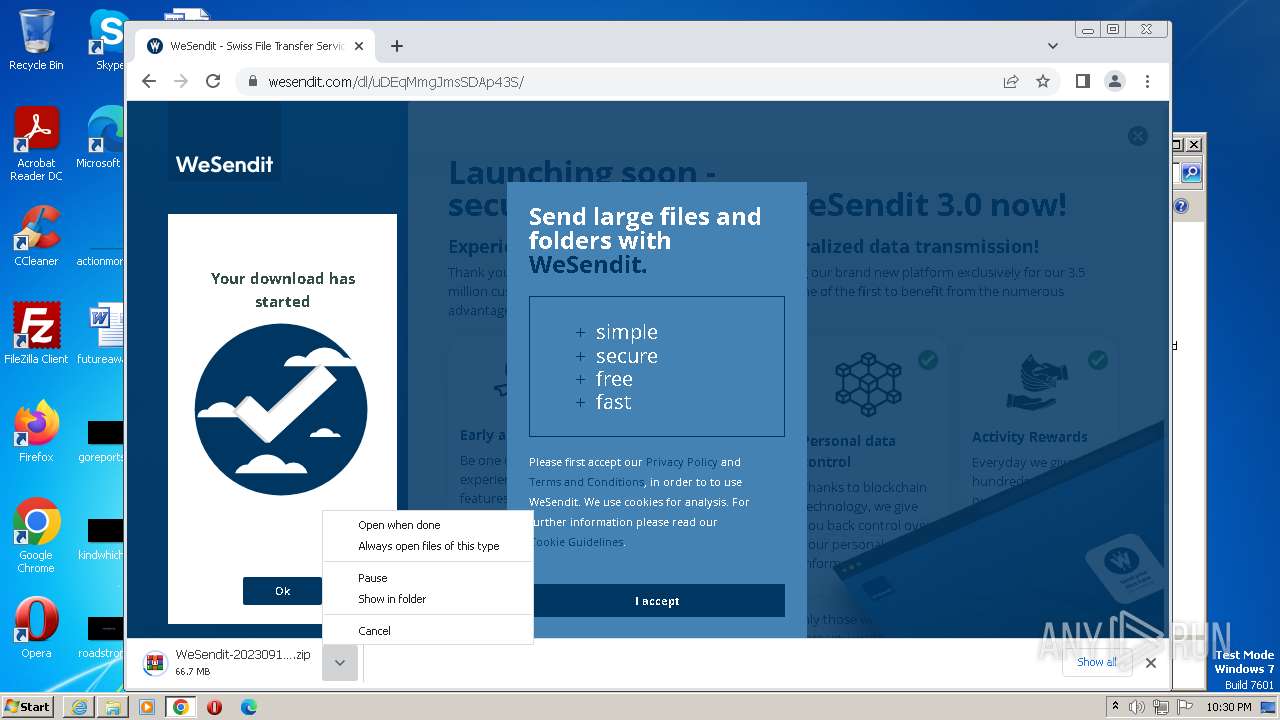
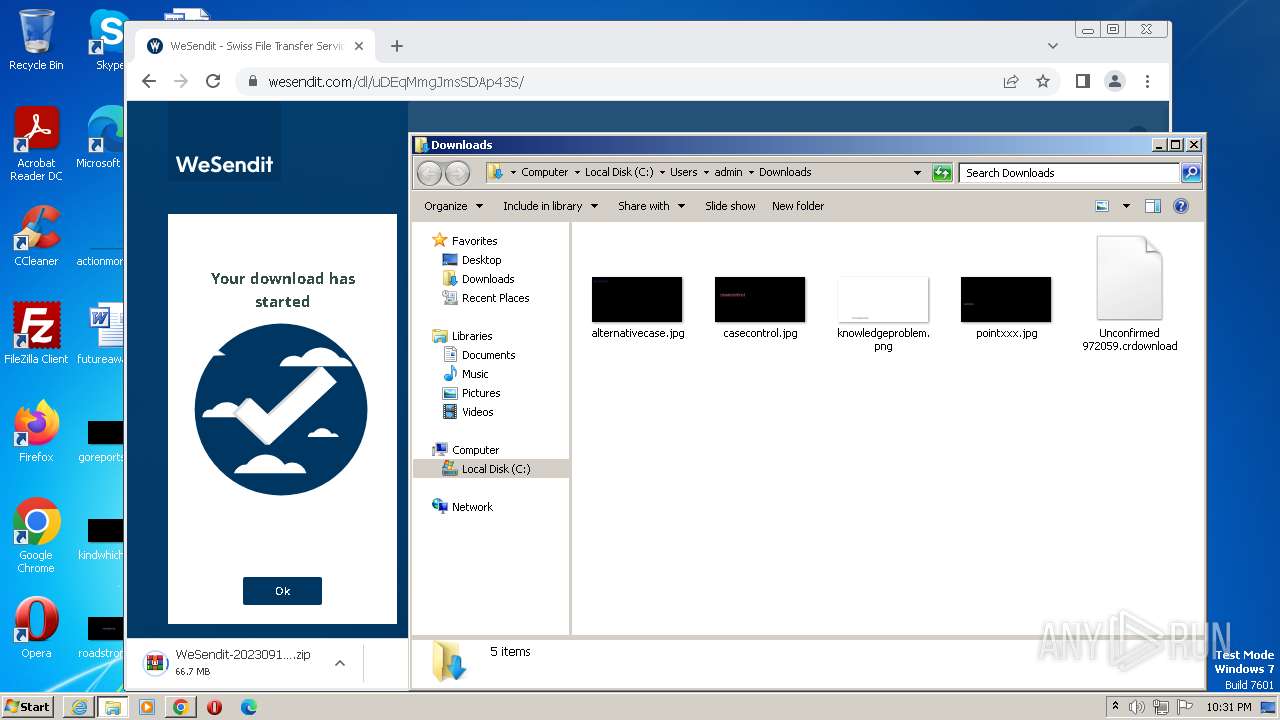
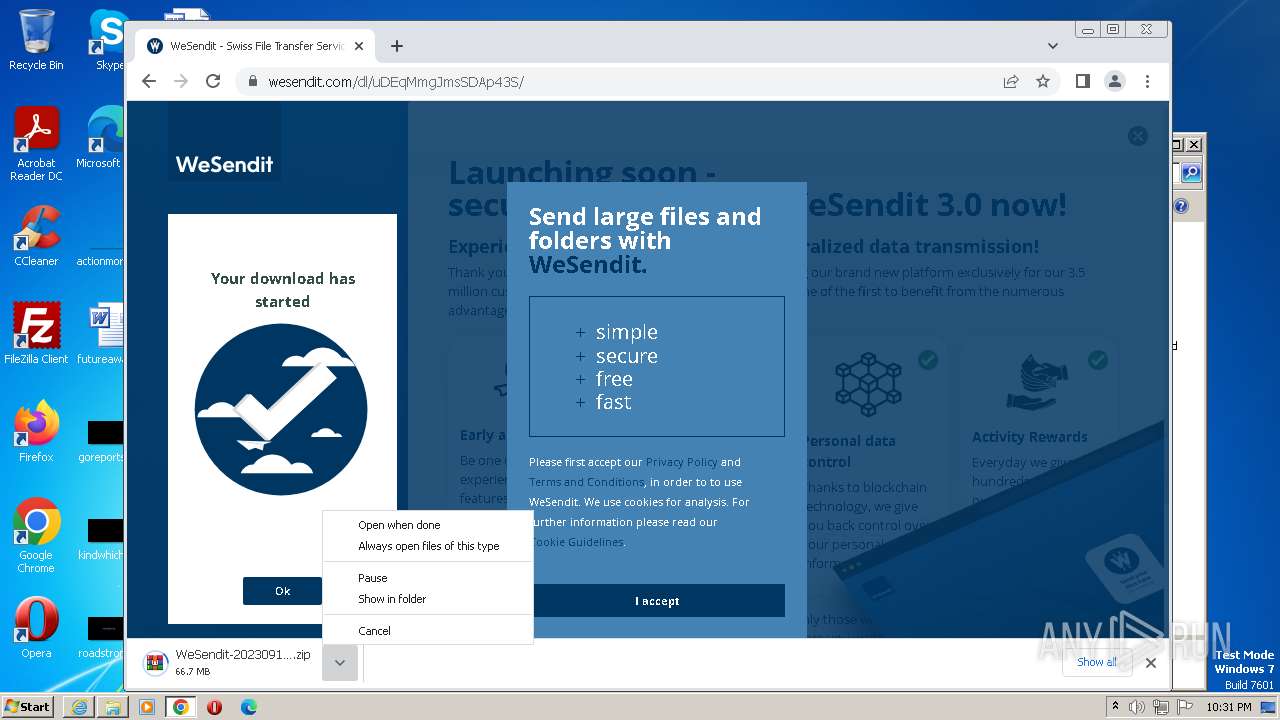
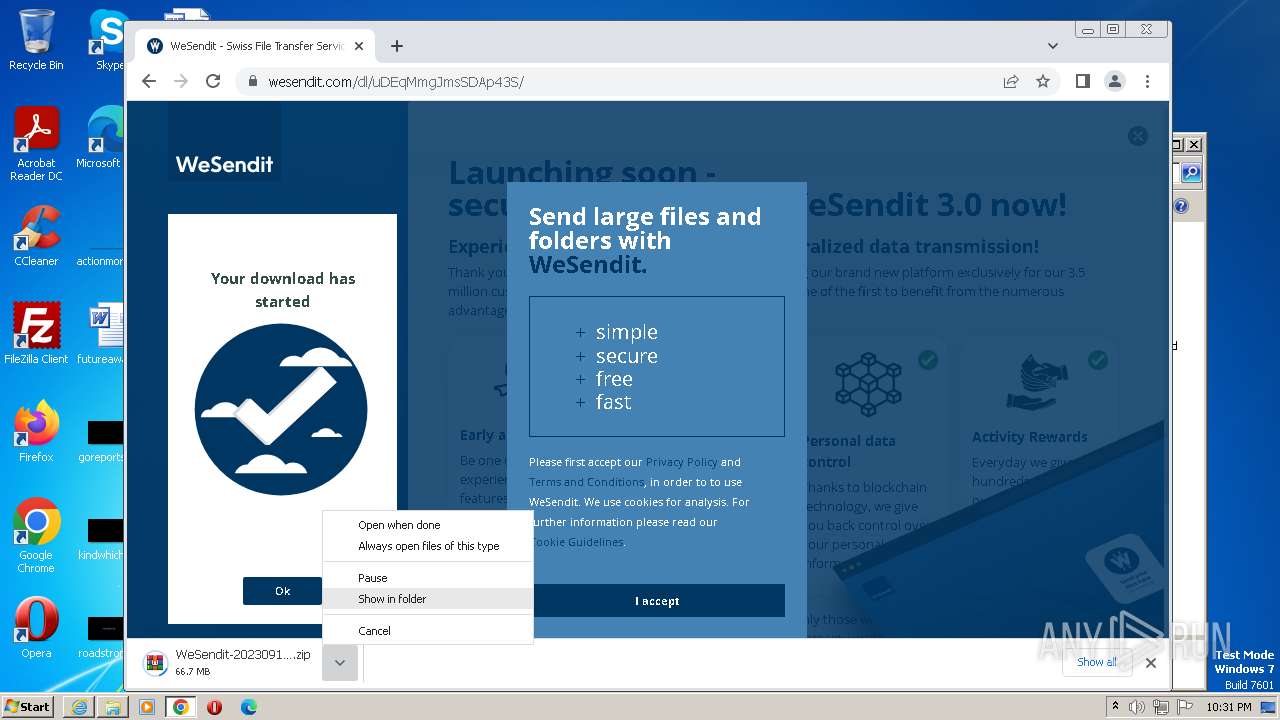
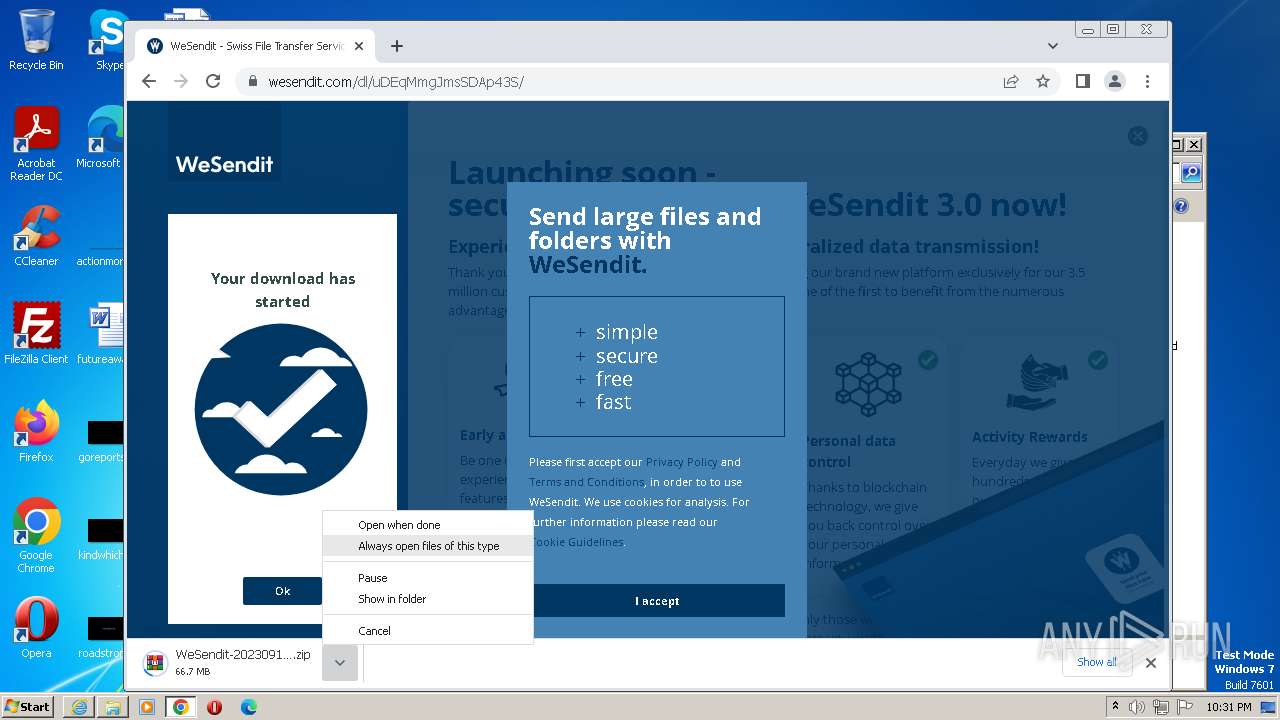
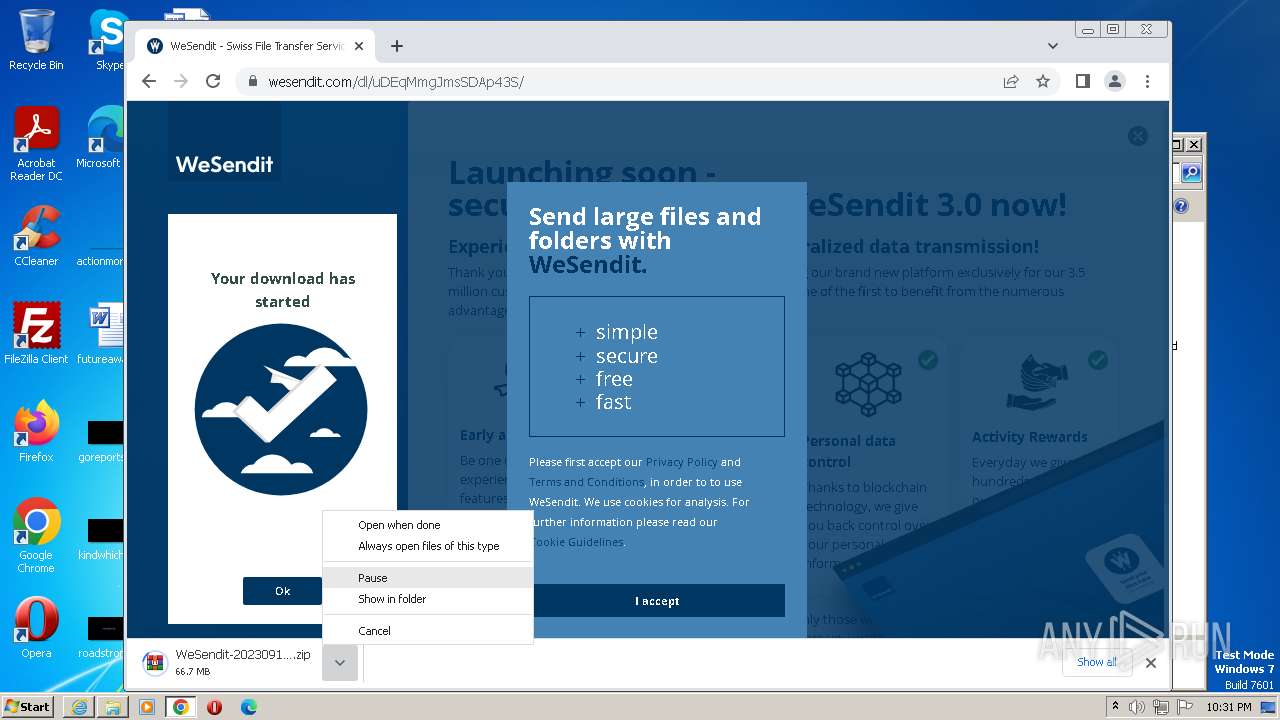
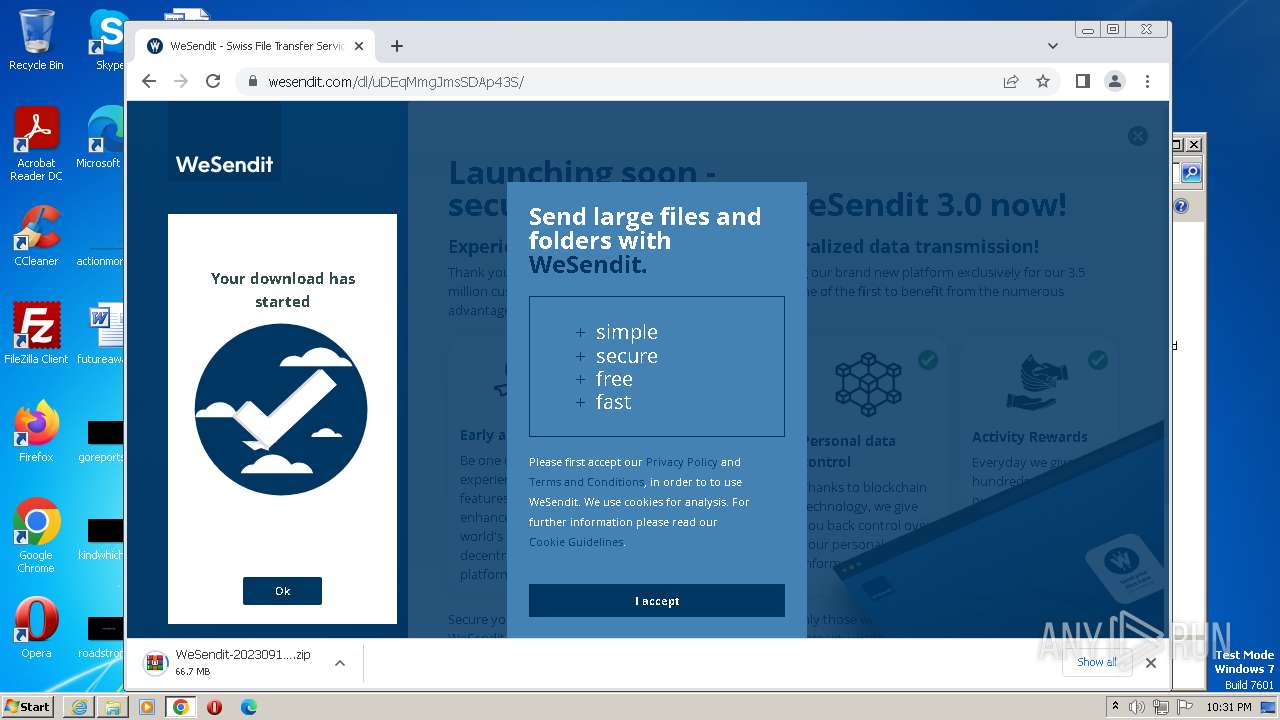
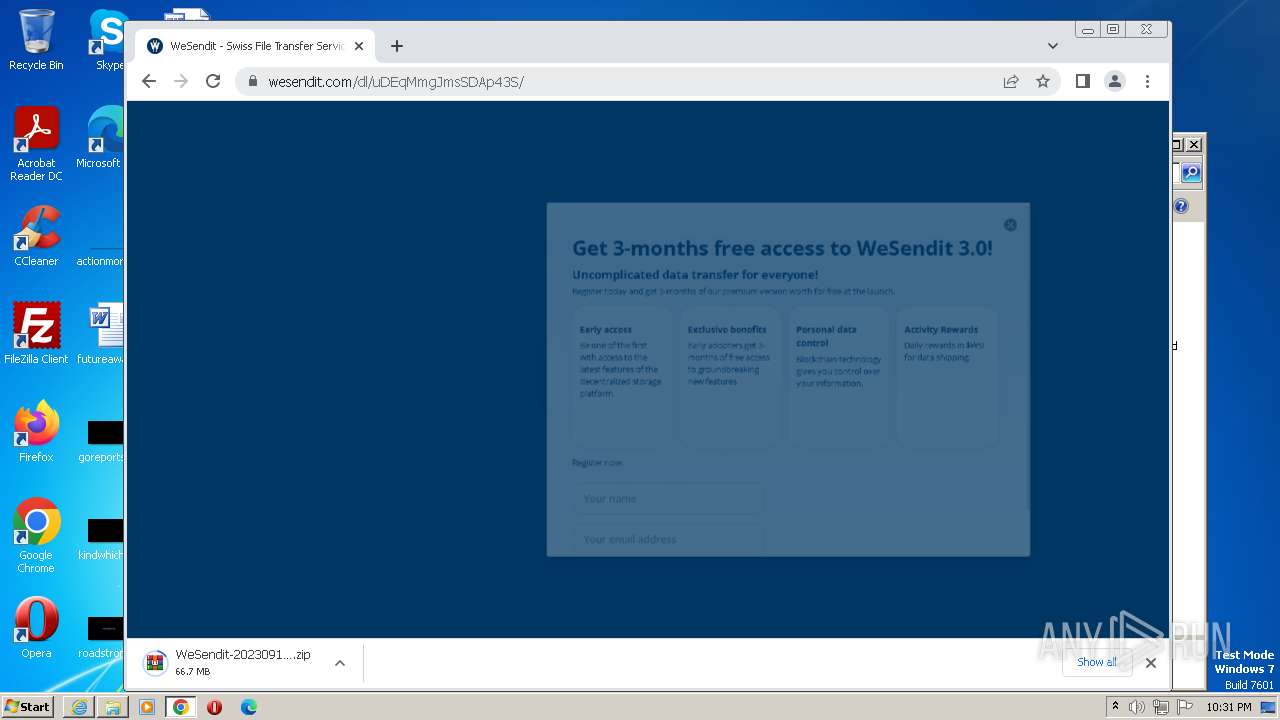
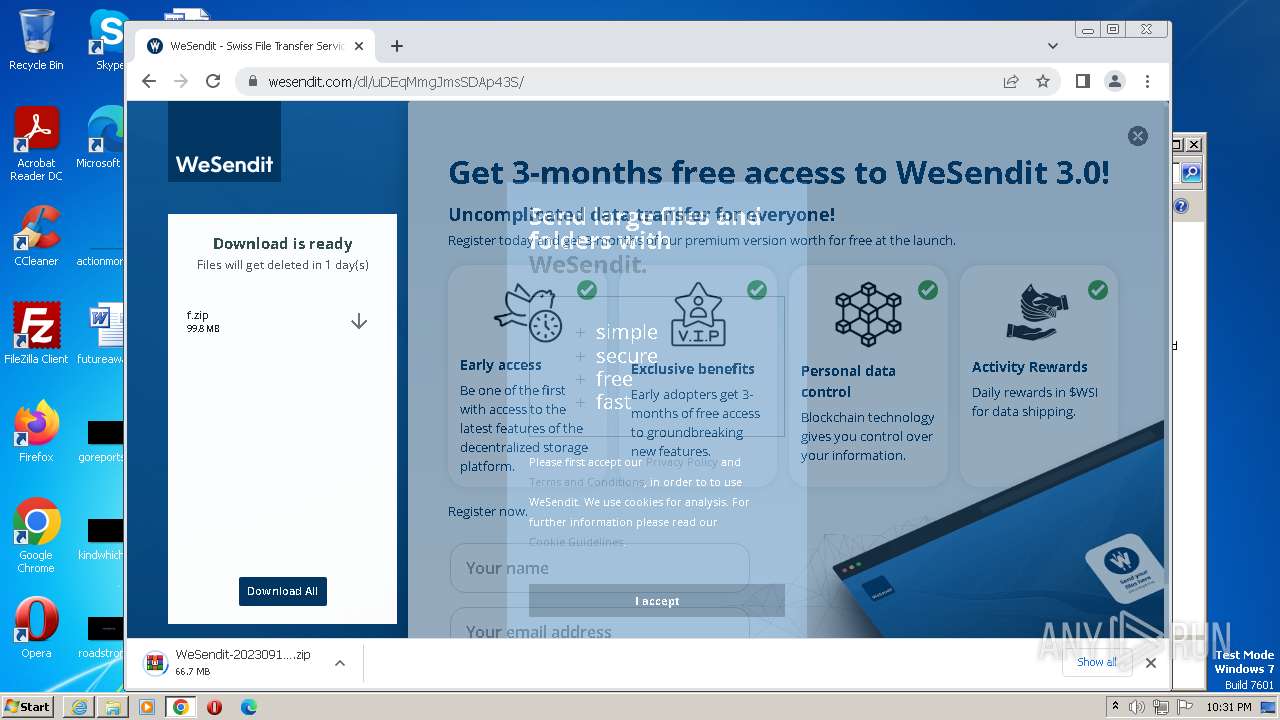
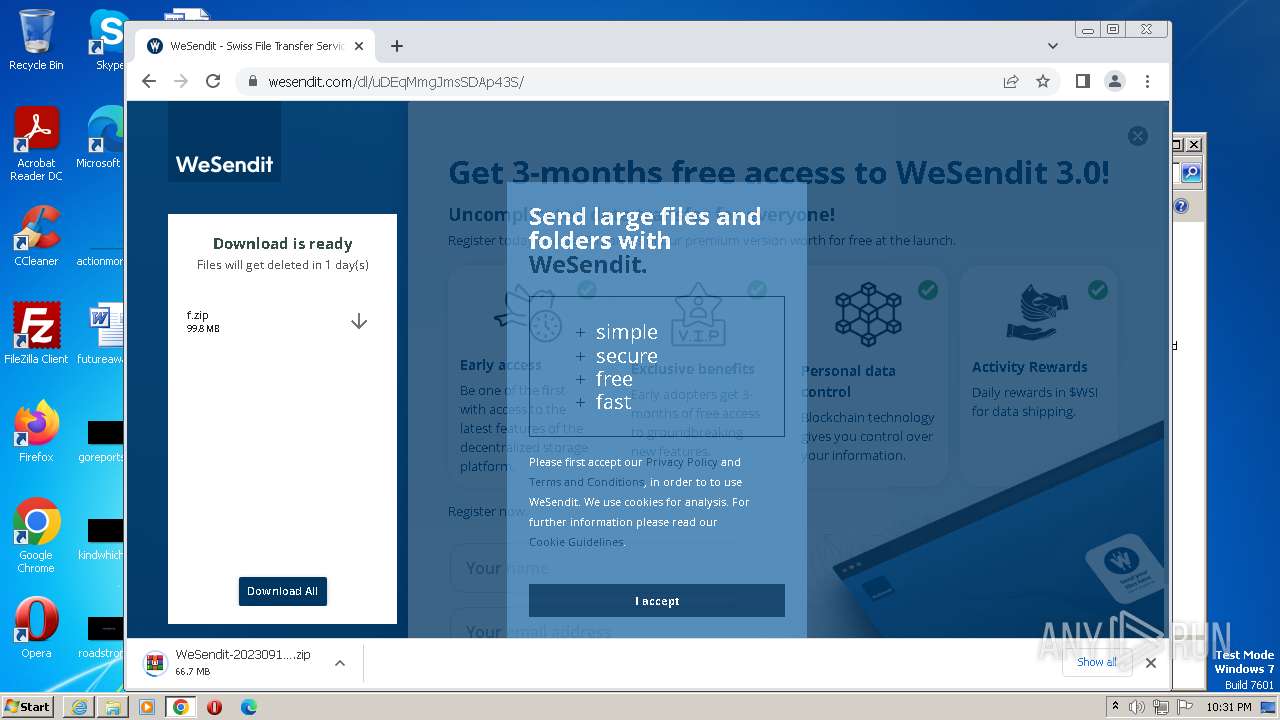
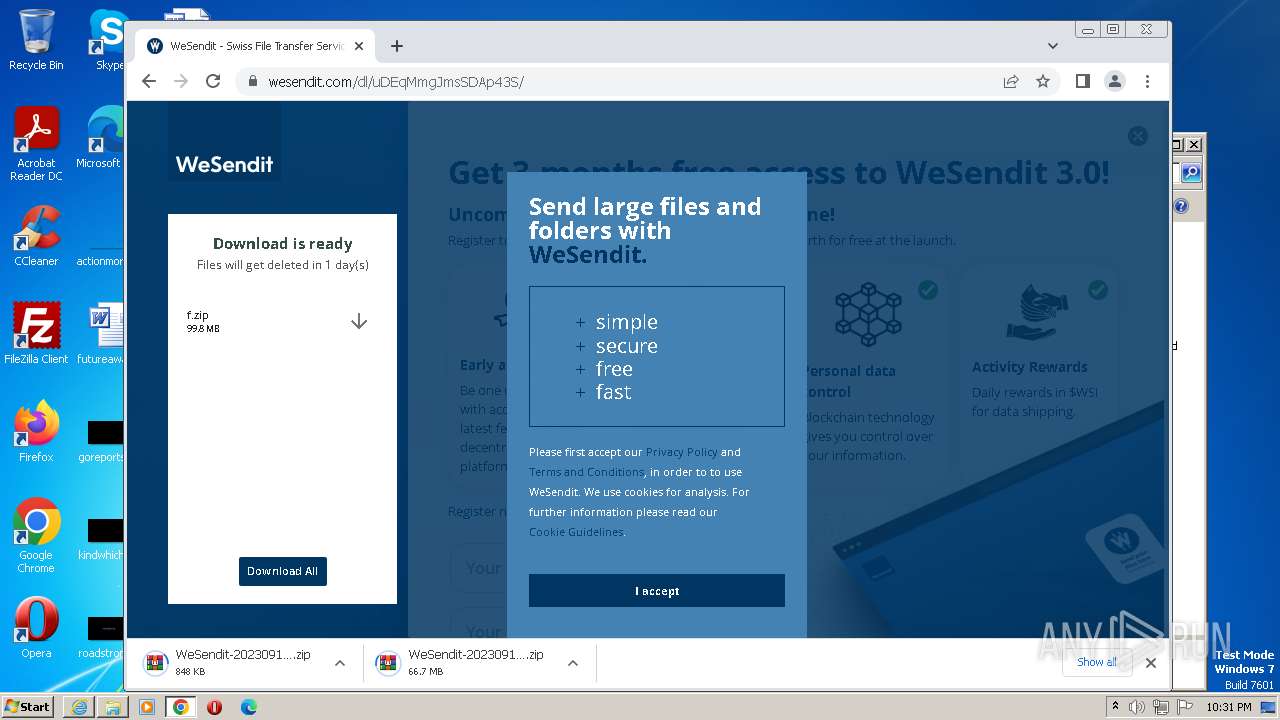
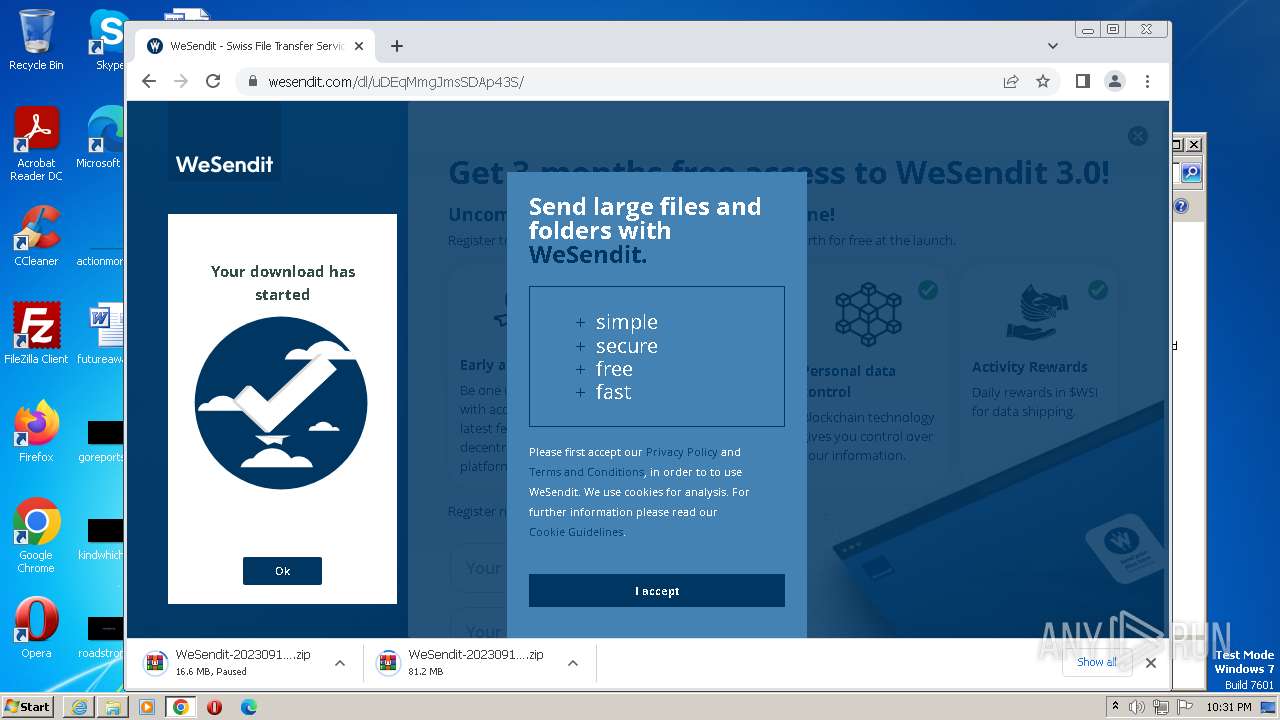
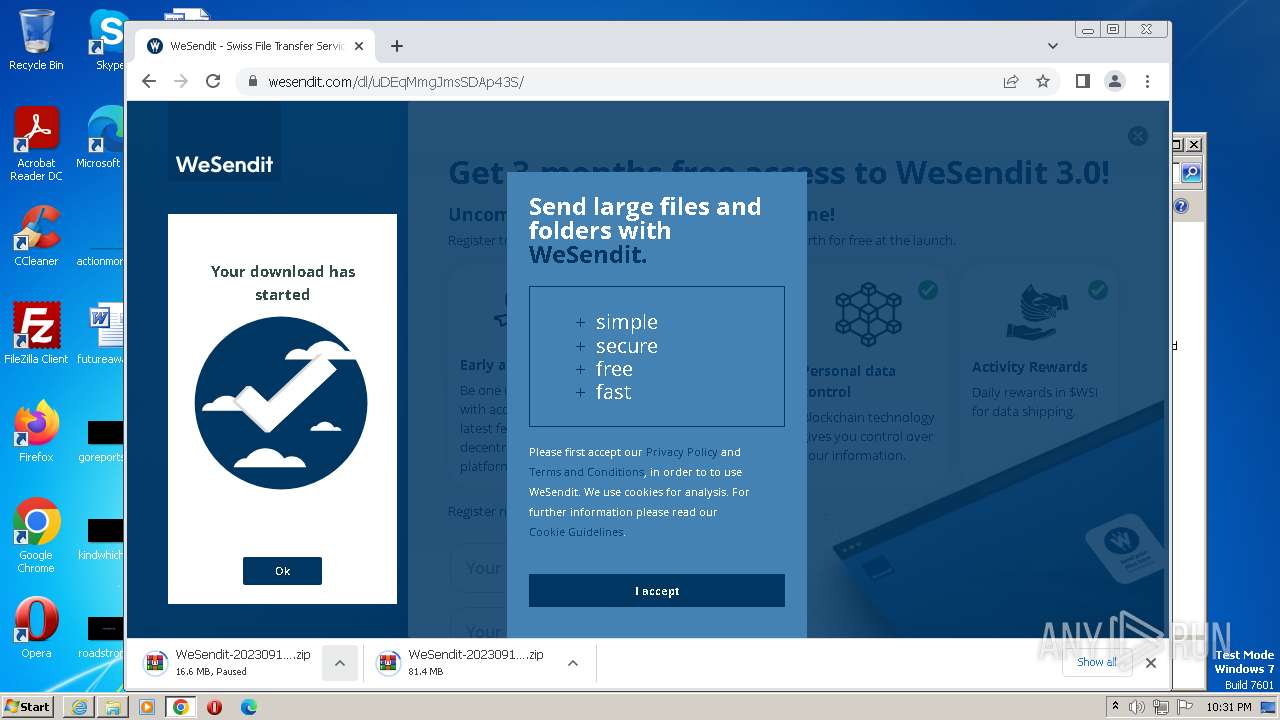
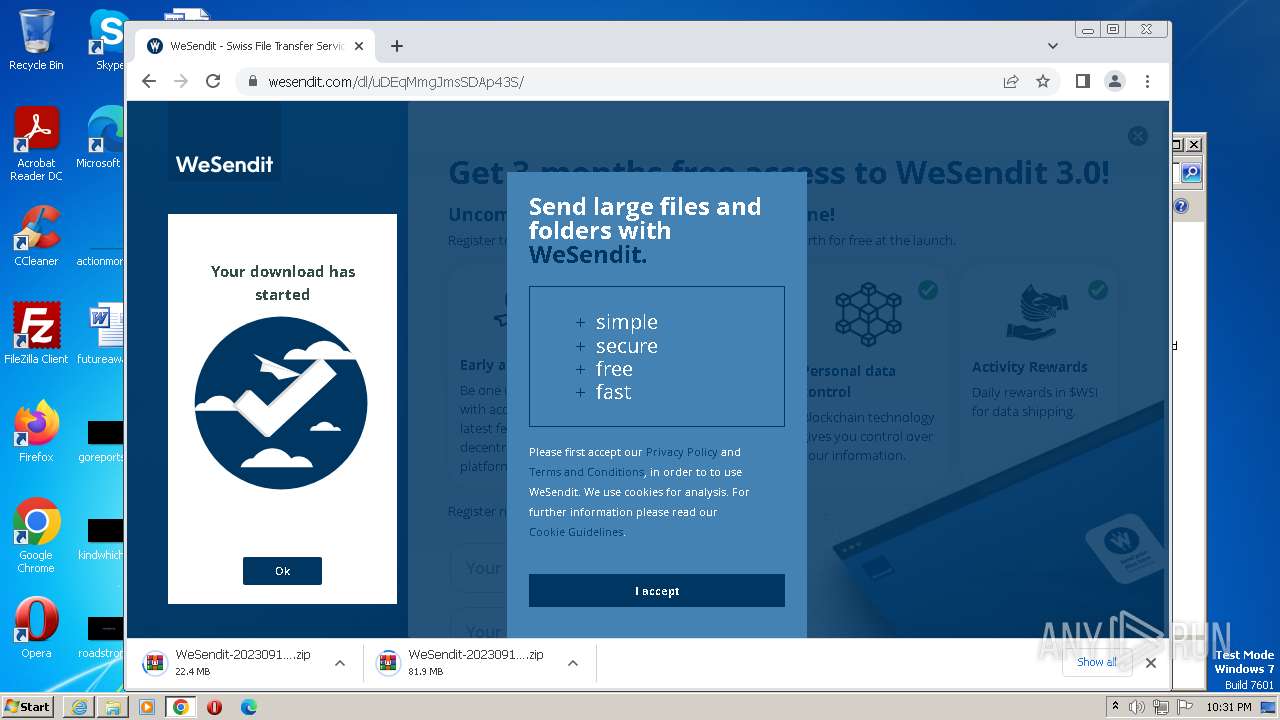
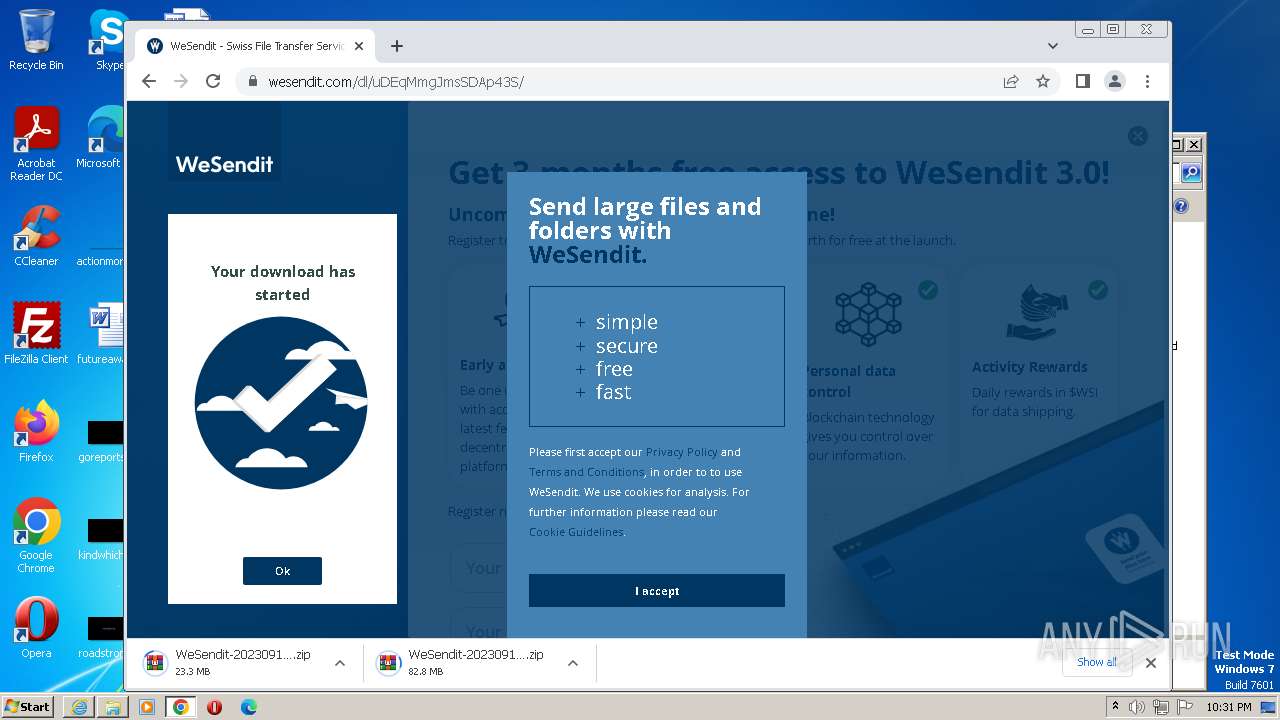
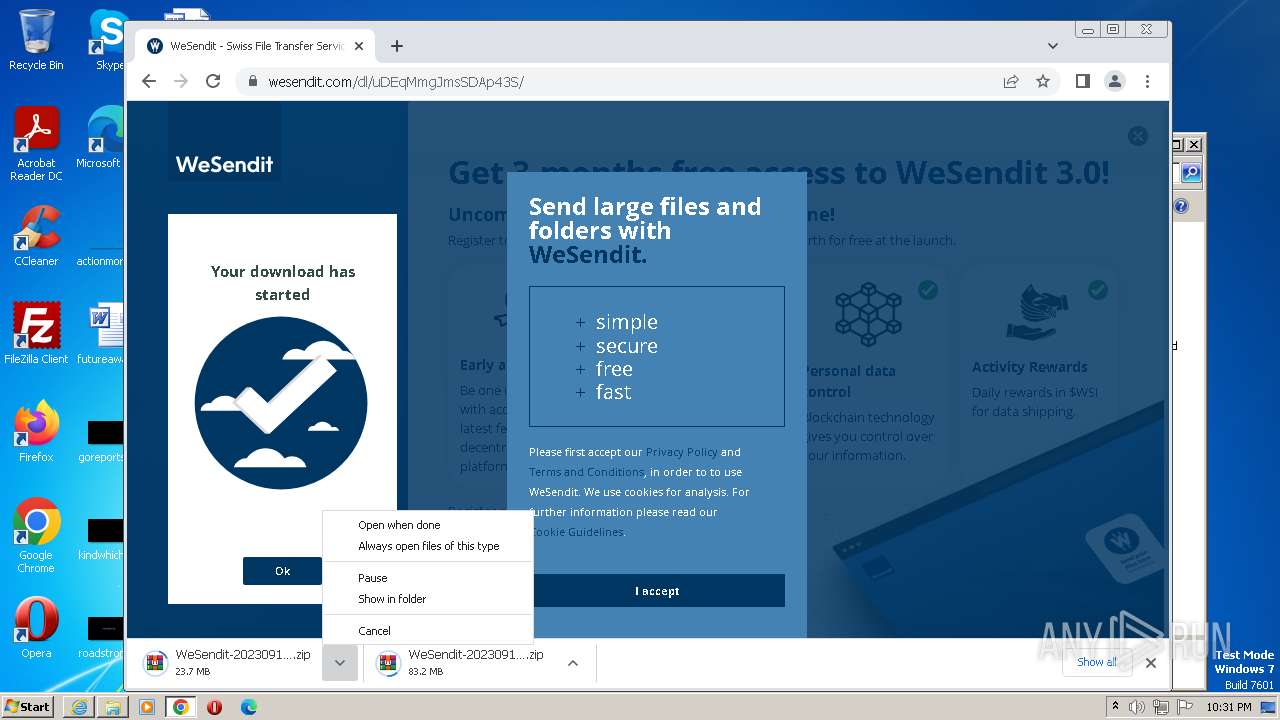
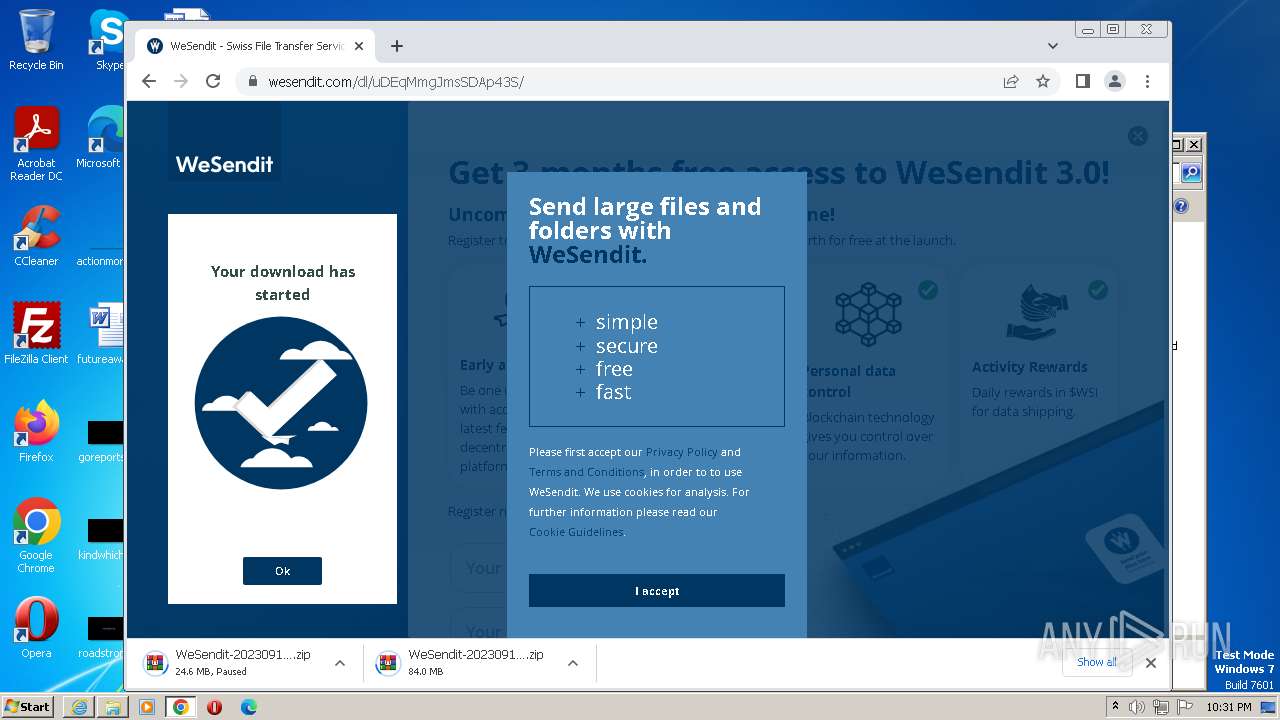
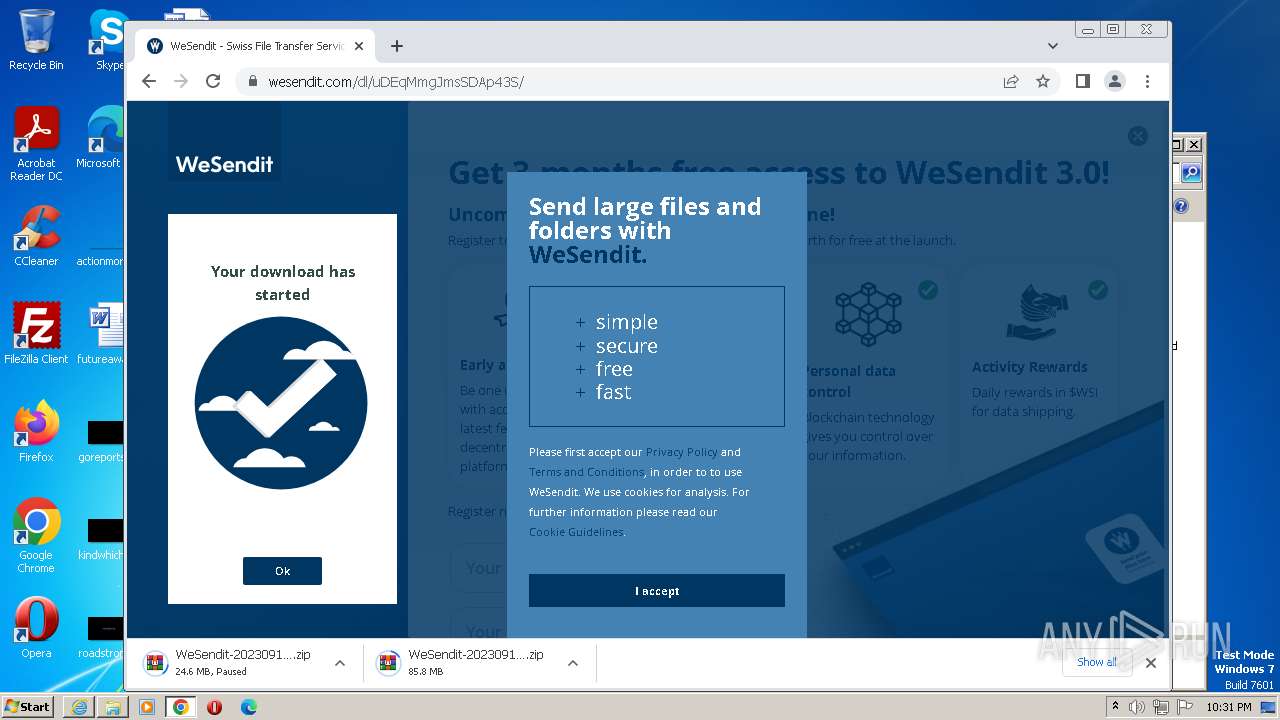
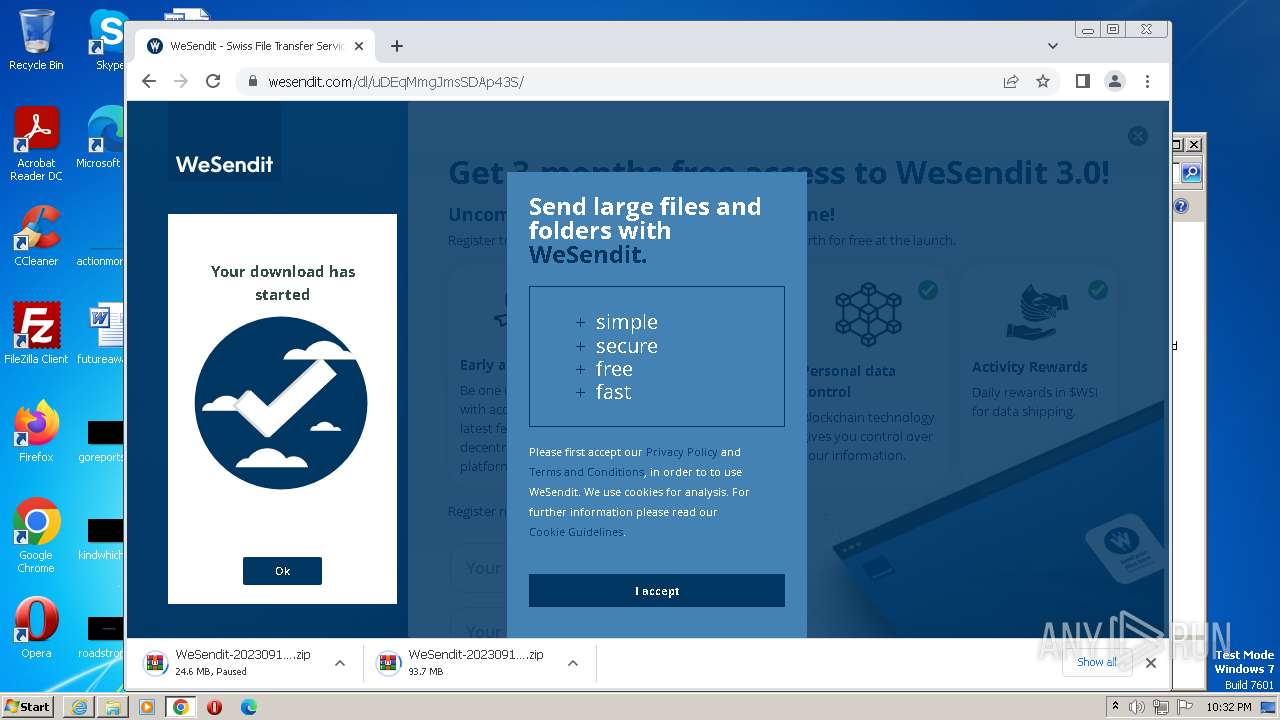
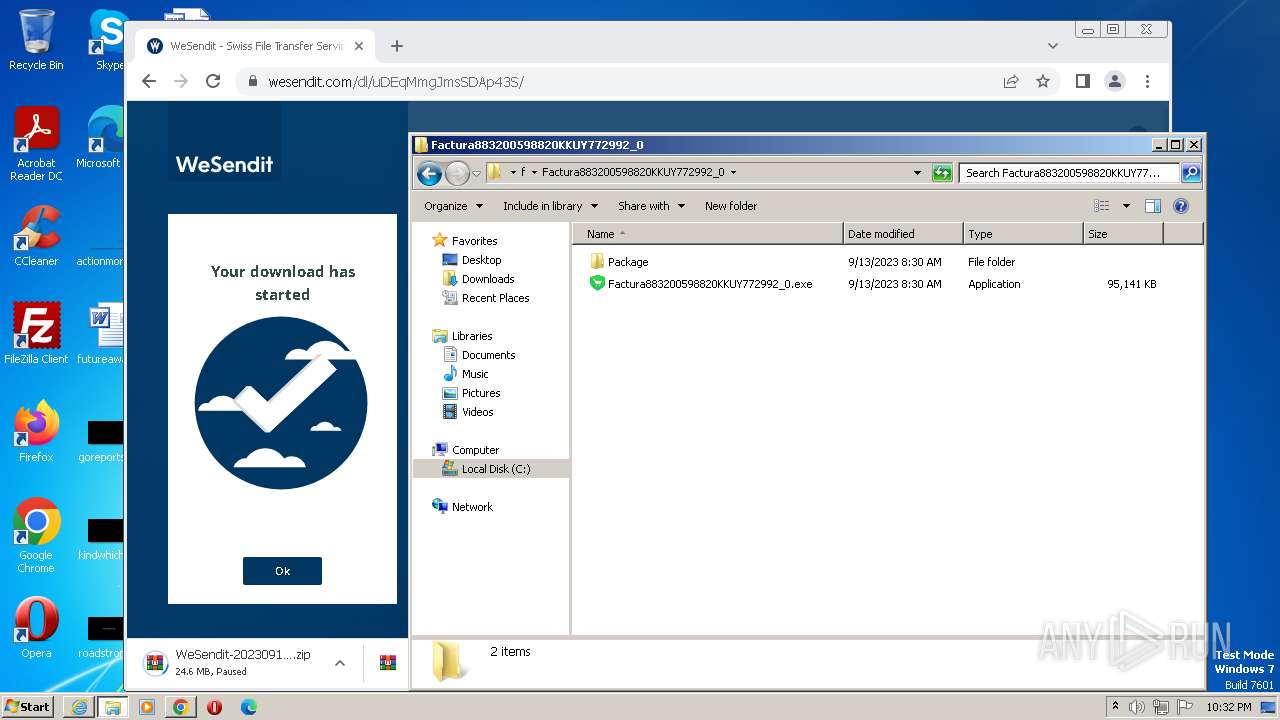
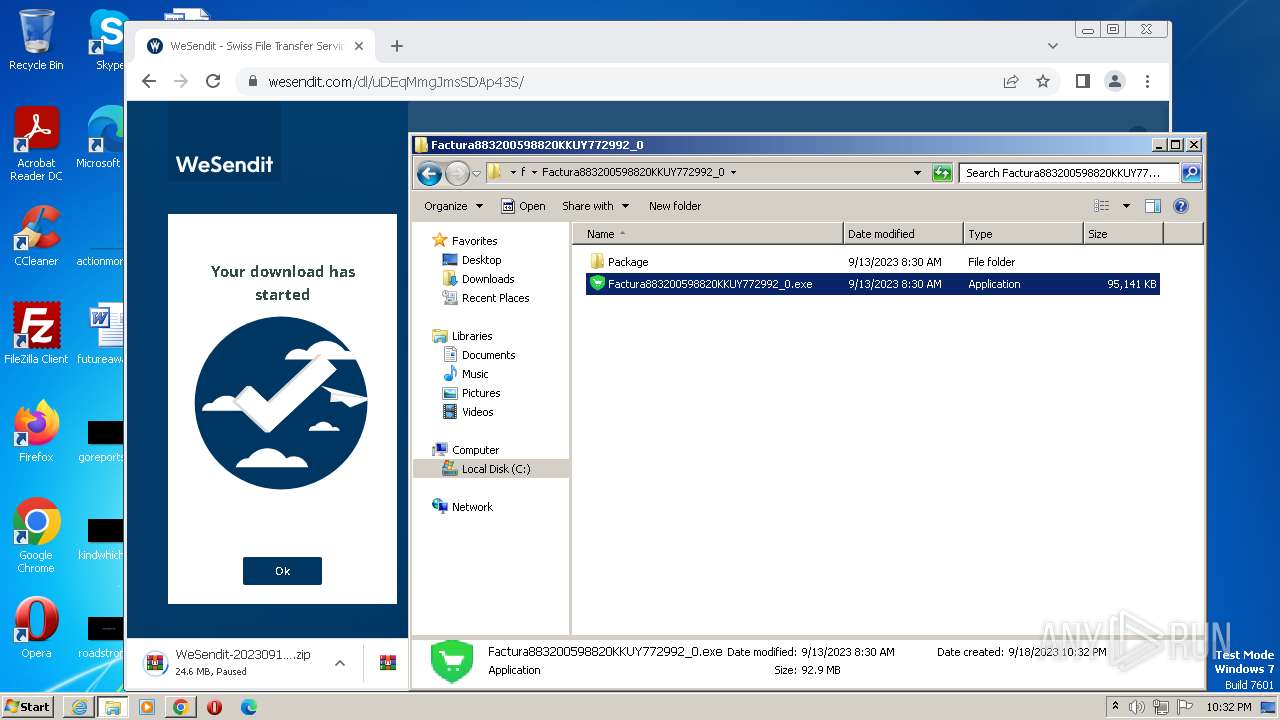
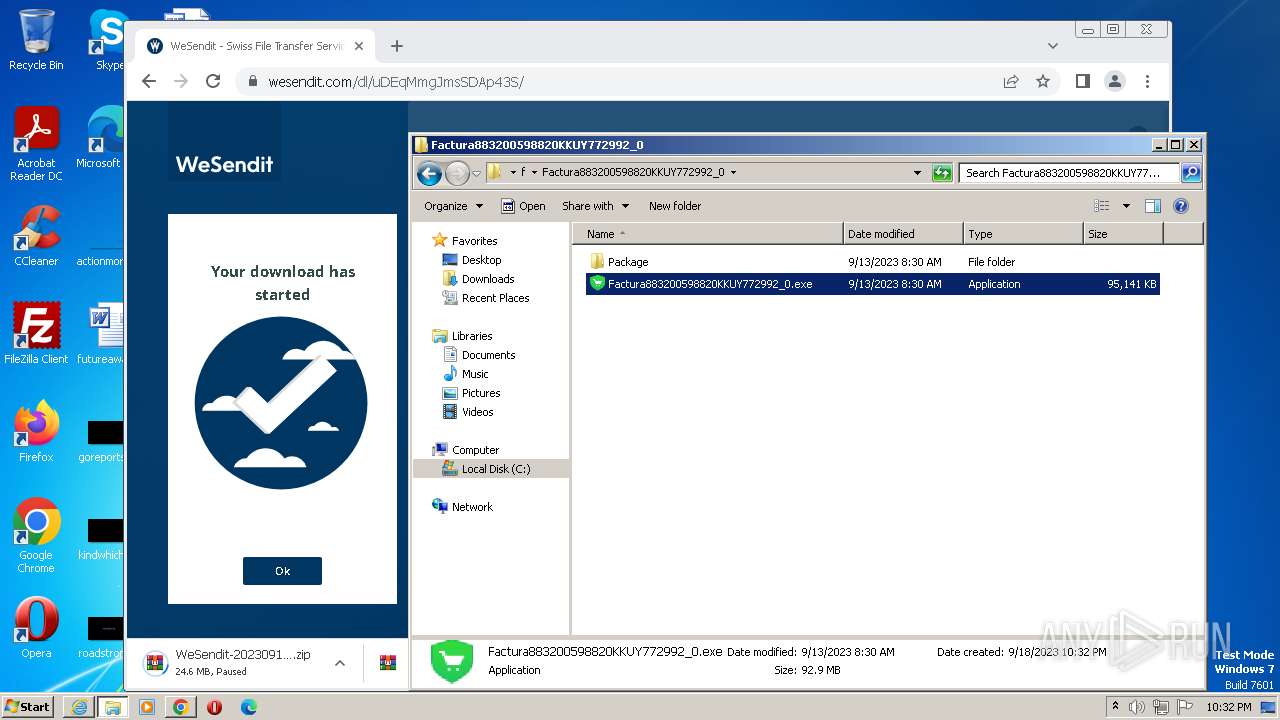
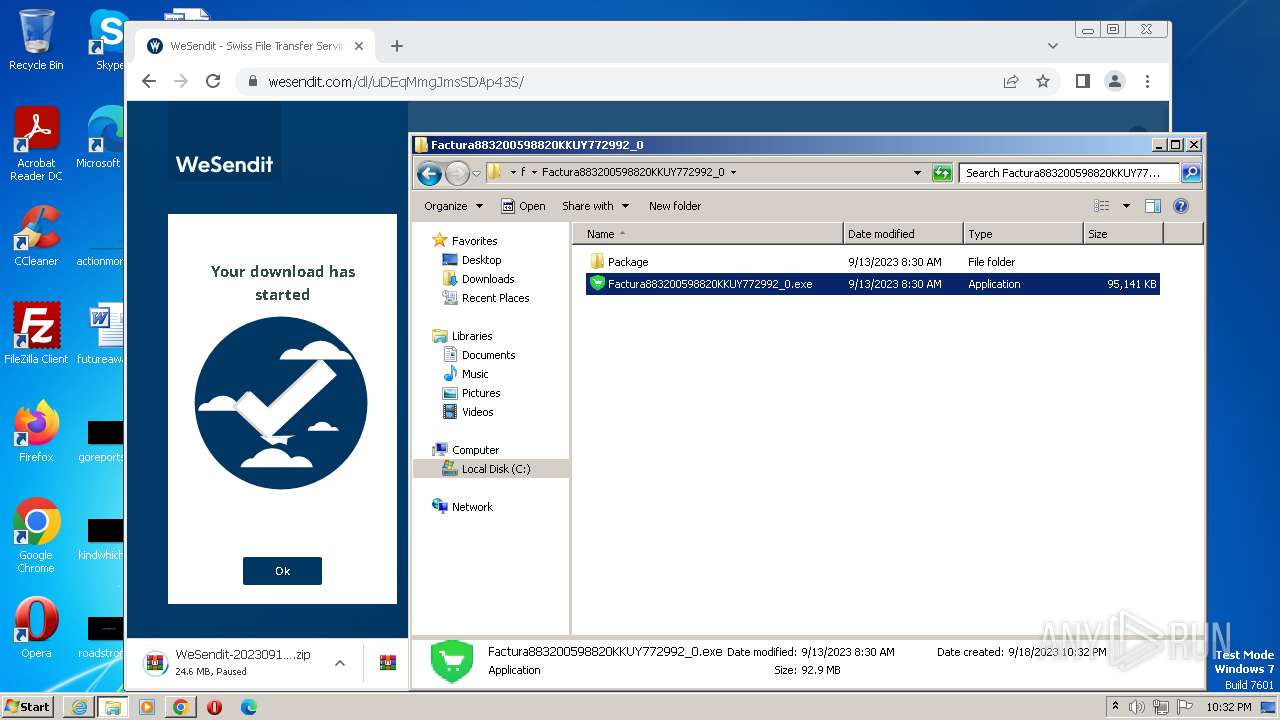
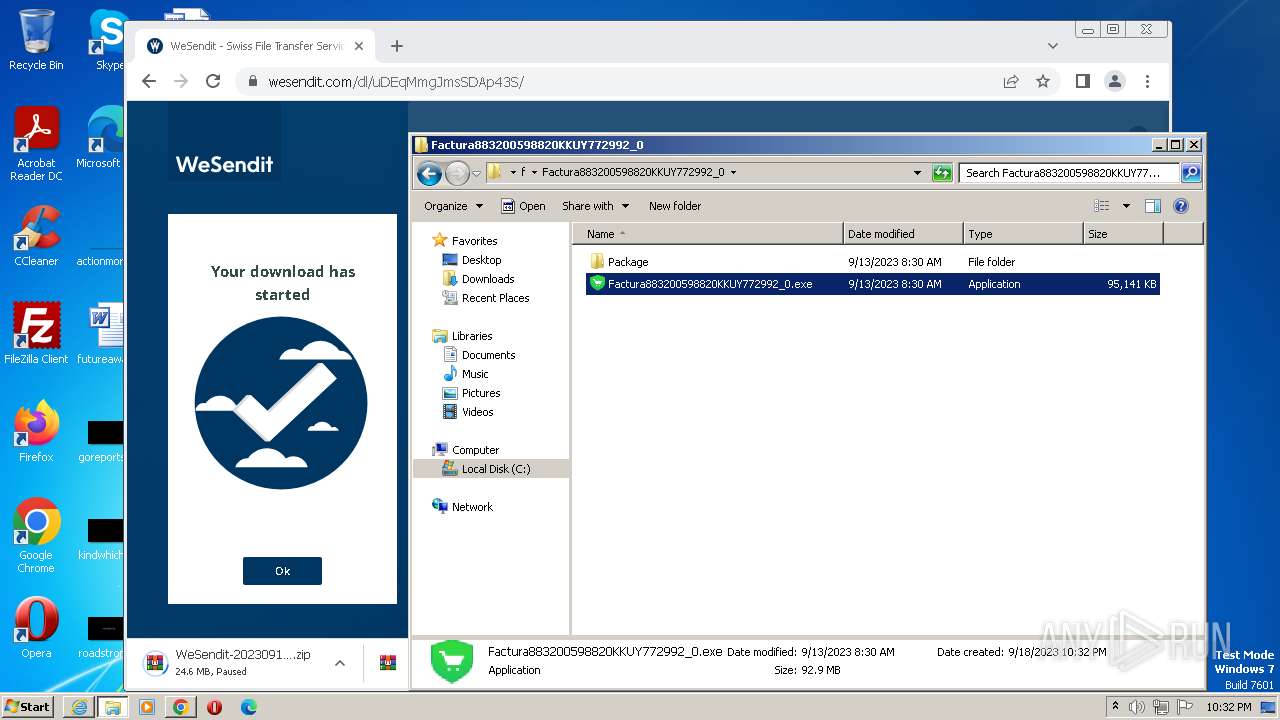
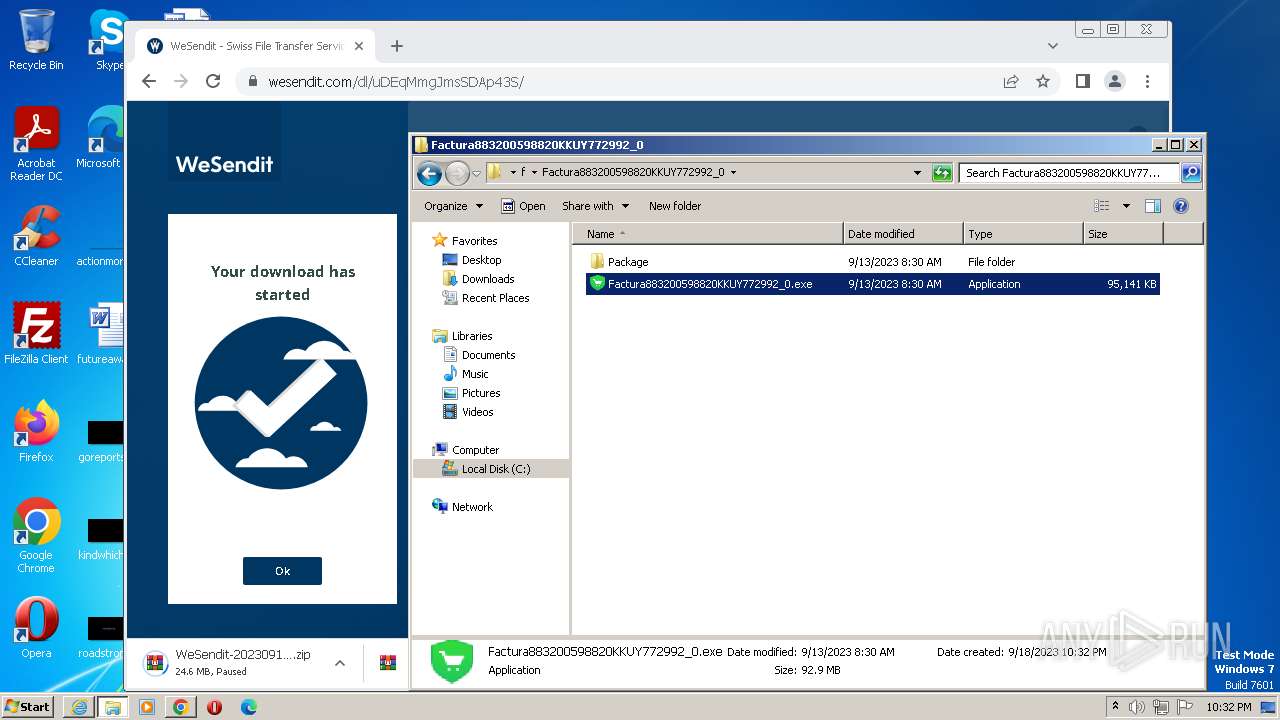
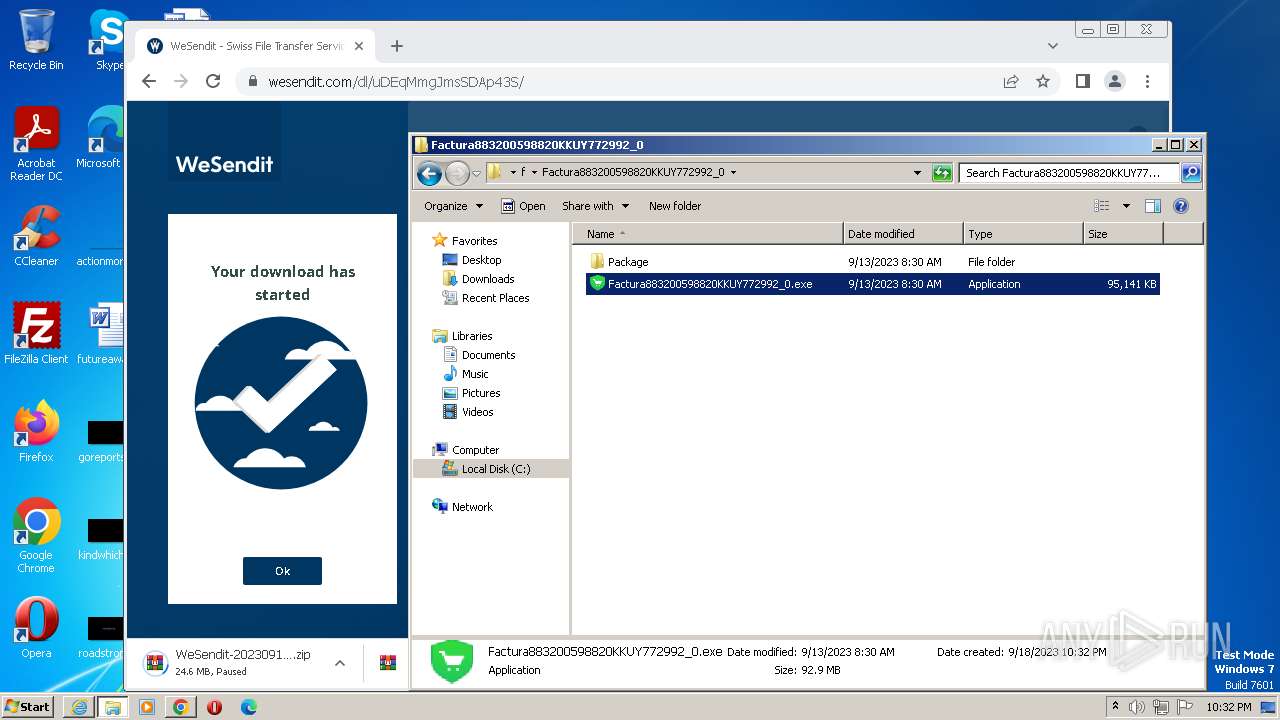
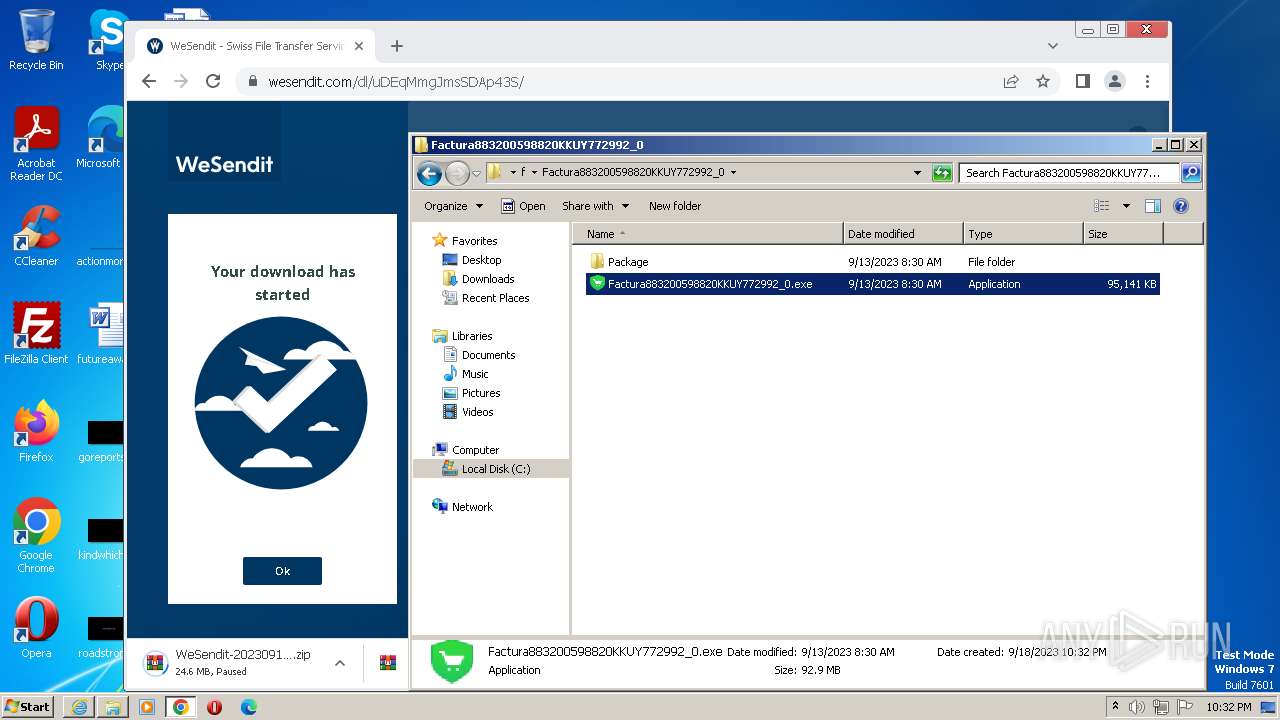
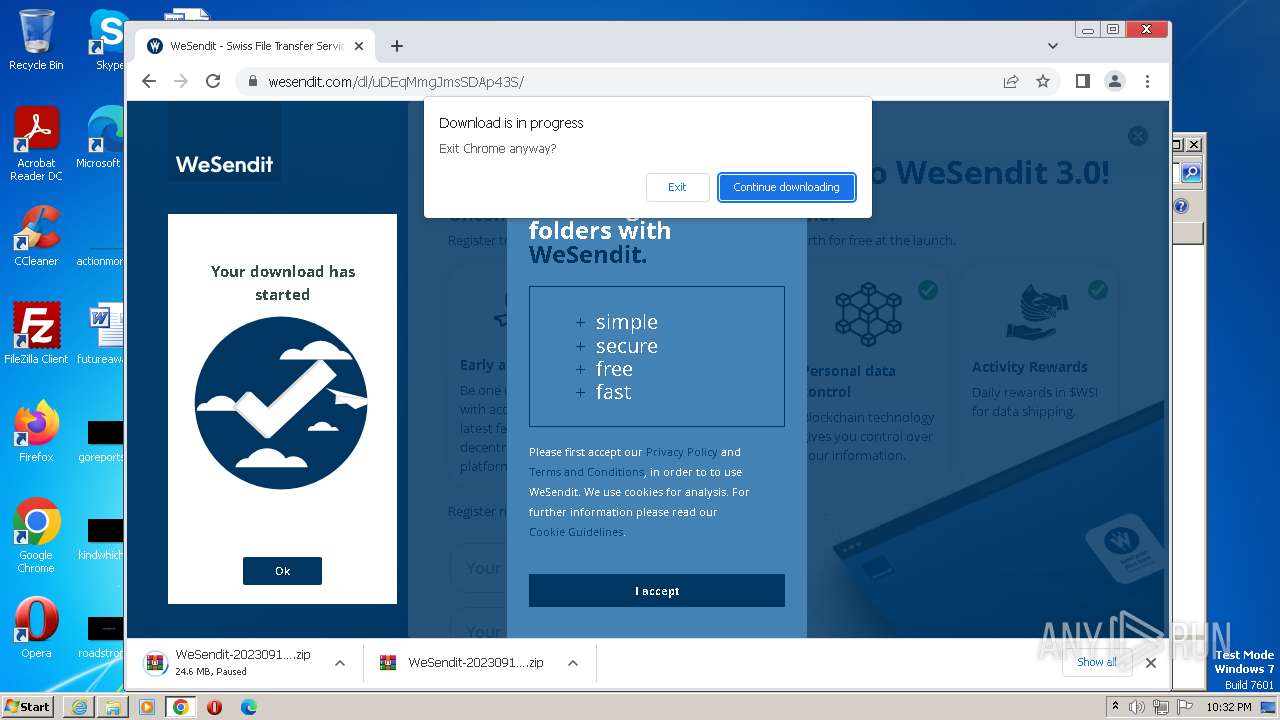
| URL: | https://wsi.li/dl/uDEqMmgJmsSDAp43S/ |
| Full analysis: | https://app.any.run/tasks/cd1a9e9d-da8e-406f-977c-b68f0f0a8310 |
| Verdict: | Malicious activity |
| Analysis date: | September 18, 2023, 21:28:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C3340C4B011EEDE8839C14E61781F60C |
| SHA1: | 7751EE353449EA66A82F45AB2EE002A64E214D63 |
| SHA256: | 91C02CA16B92096BDEB49C6589096B84D243B1833B00A19ABD83A66D503F22CB |
| SSDEEP: | 3:N8HMFSOsihcWn:2sFyihcWn |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads settings of System Certificates
- Factura883200598820KKUY772992_0.exe (PID: 2460)
Reads the Internet Settings
- Factura883200598820KKUY772992_0.exe (PID: 2460)
INFO
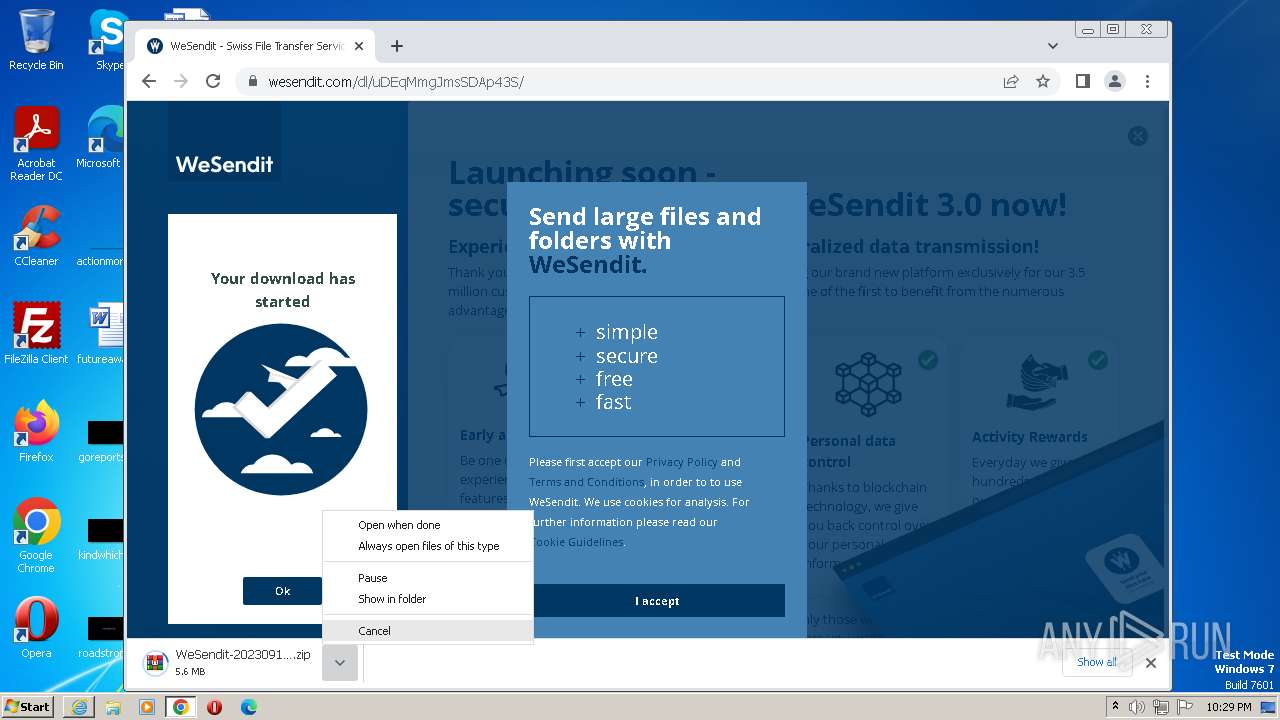
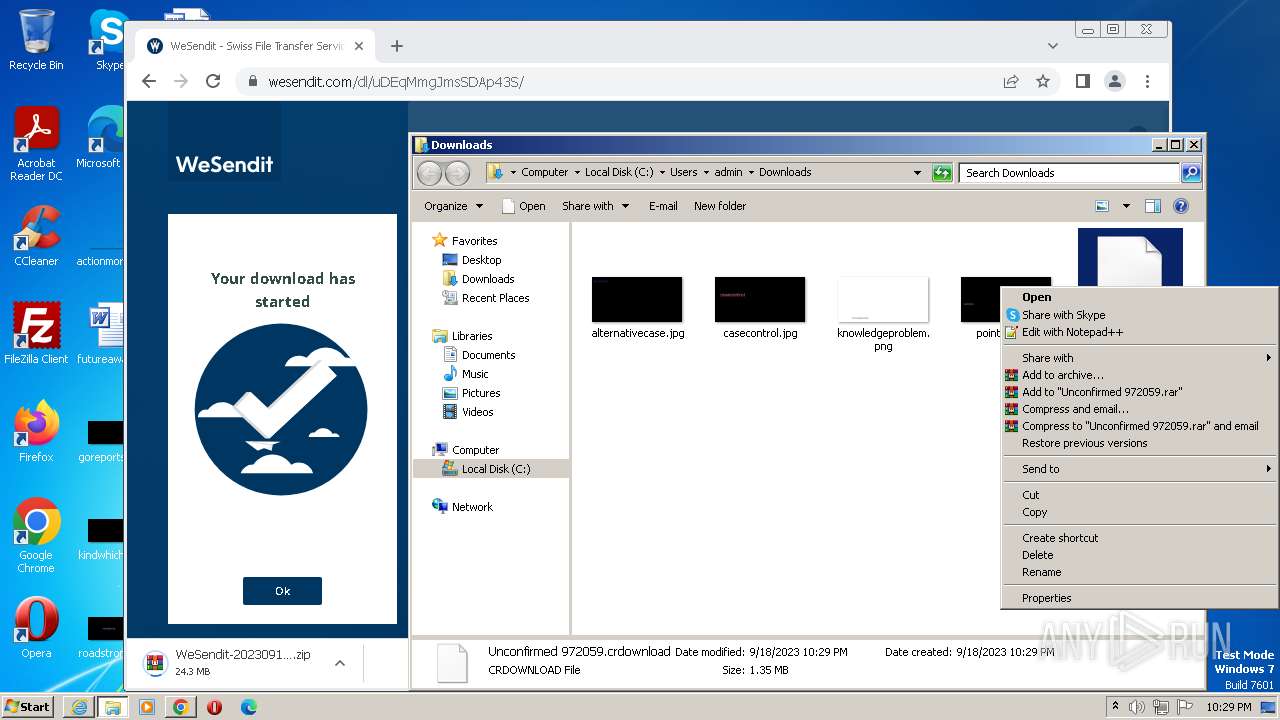
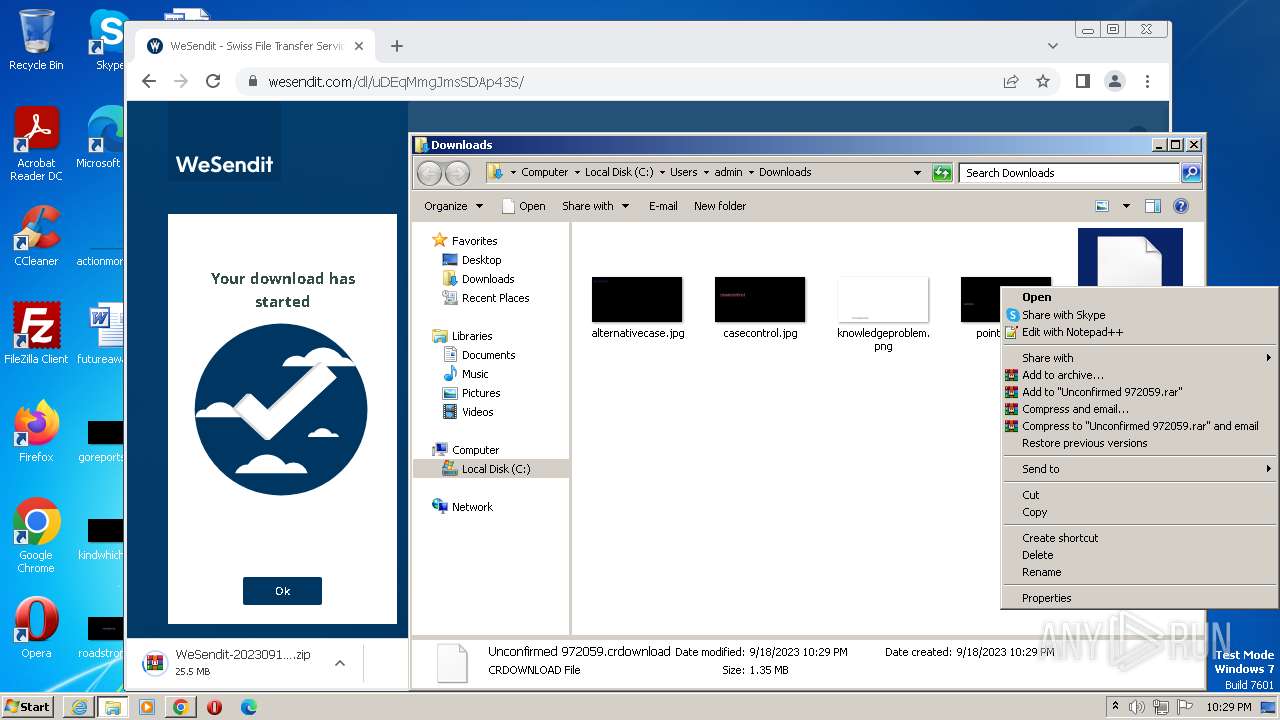
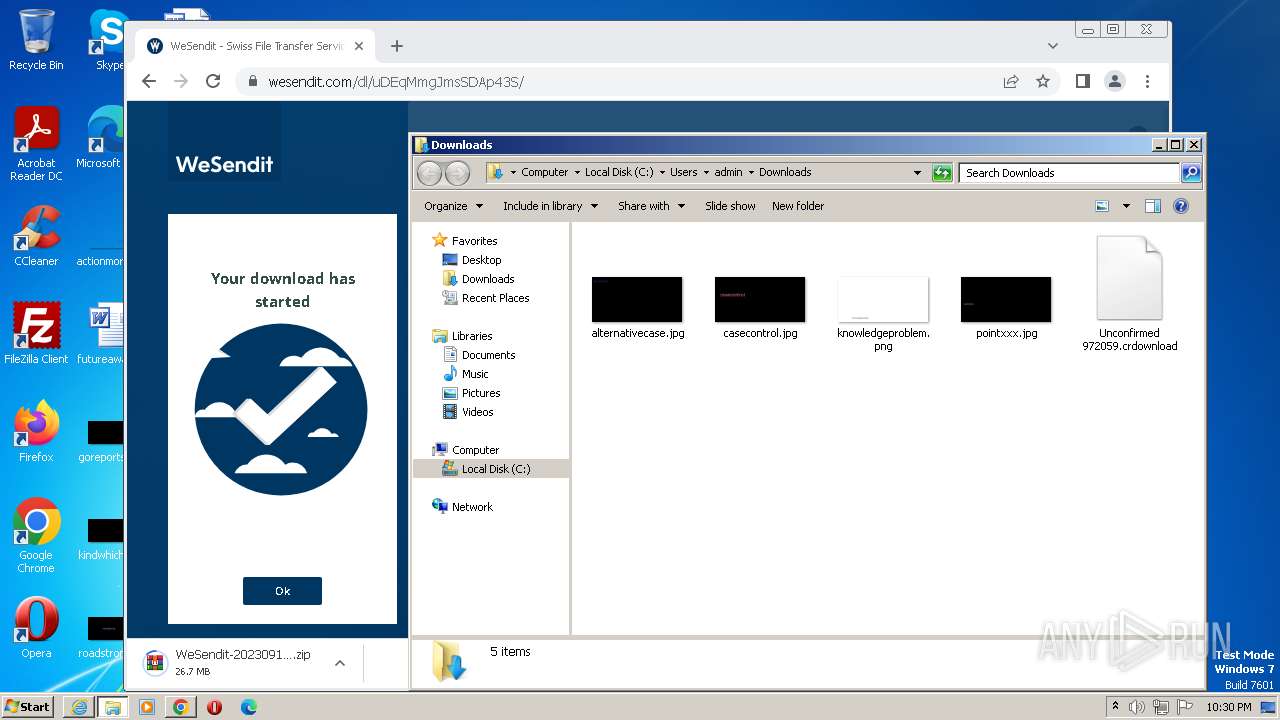
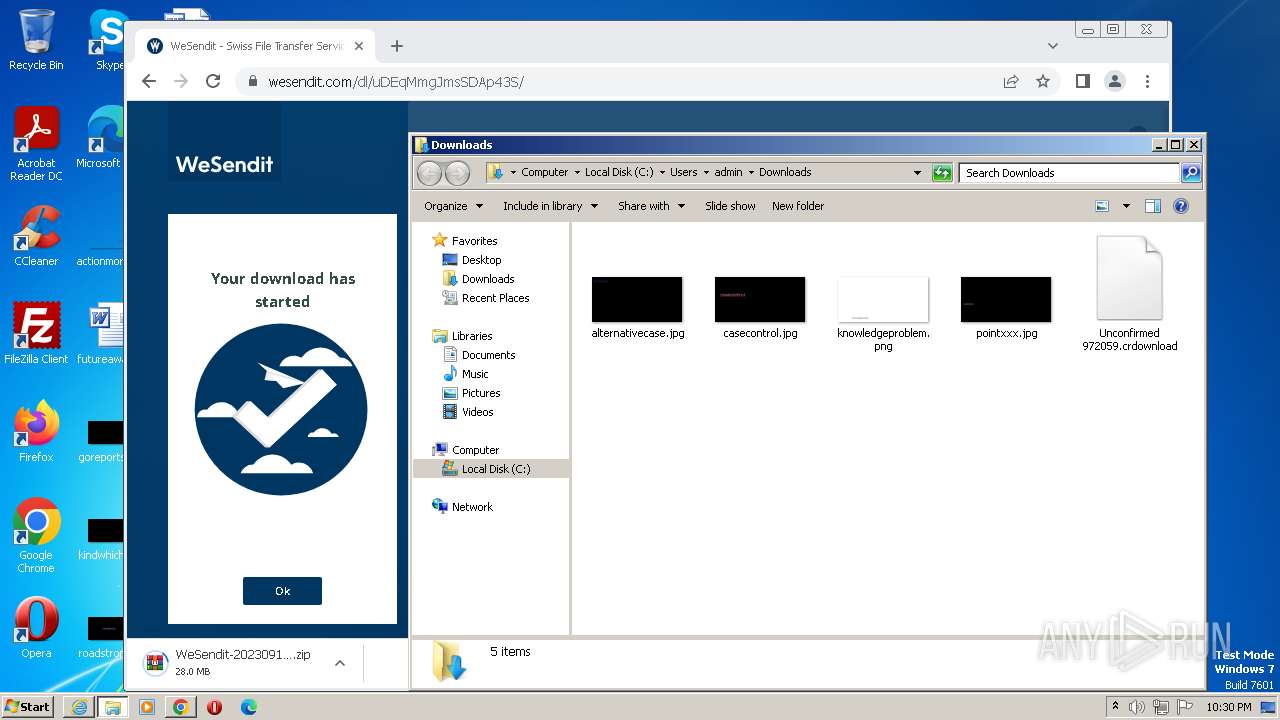
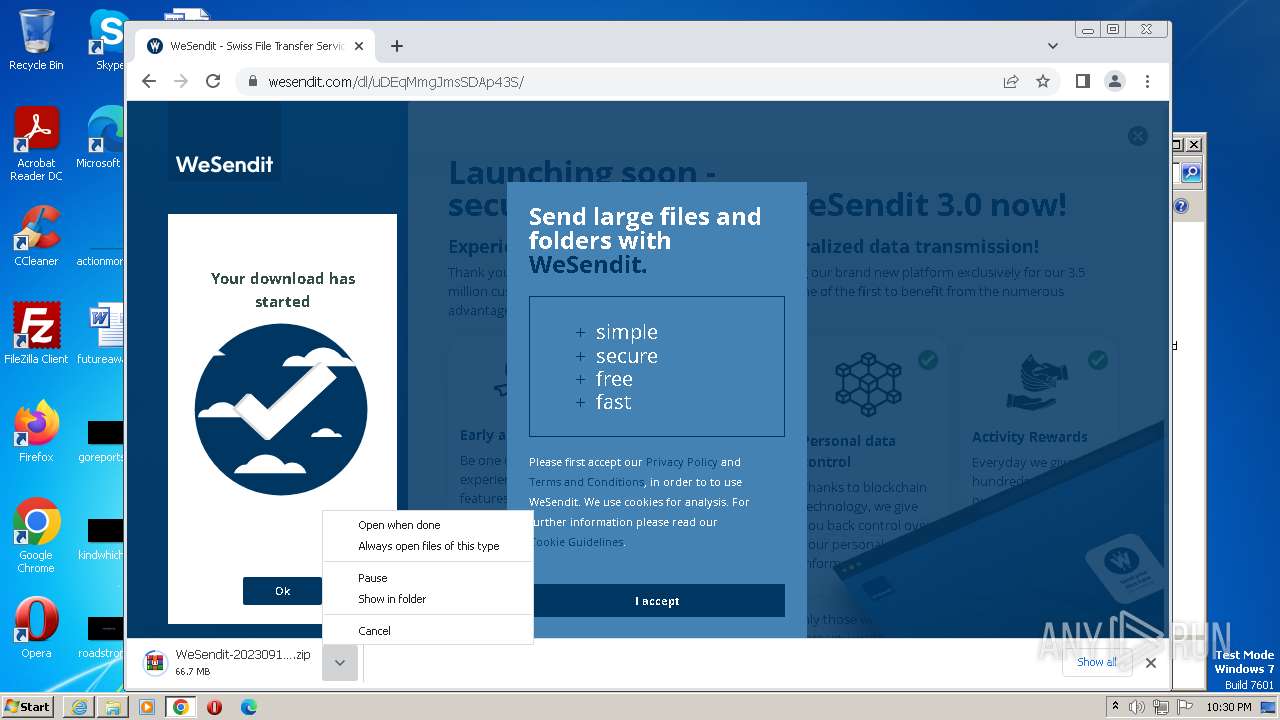
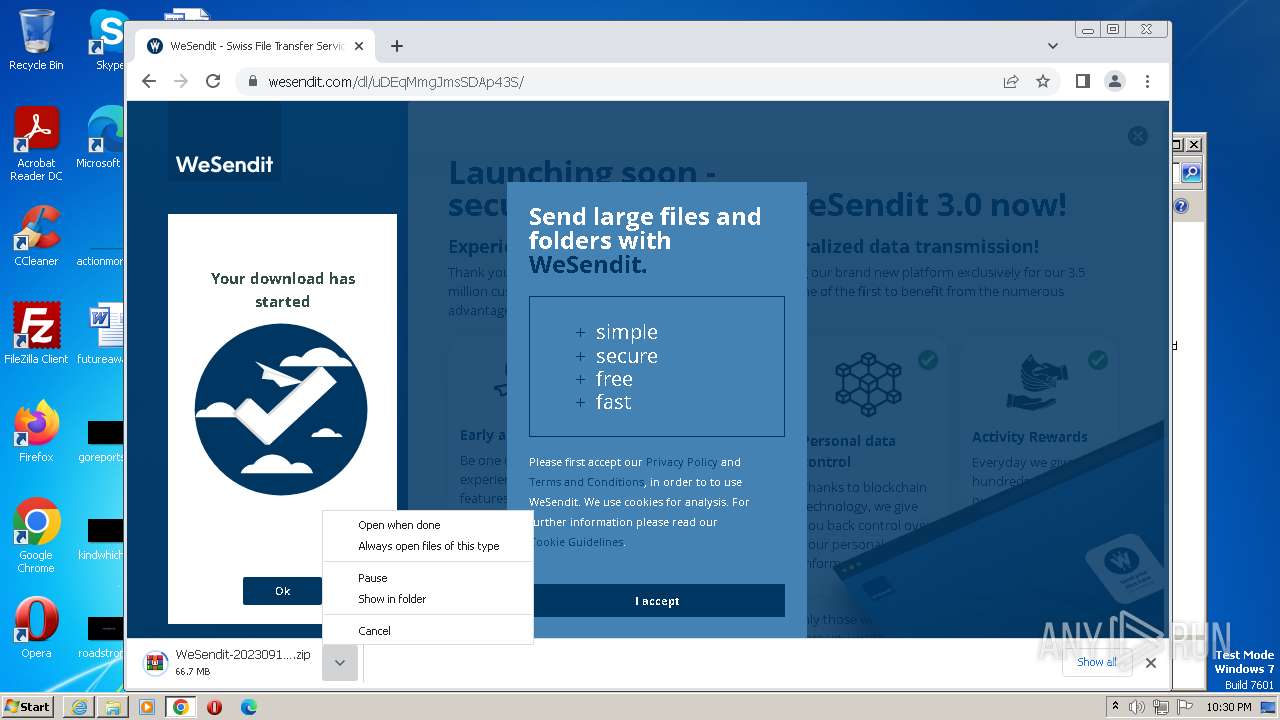
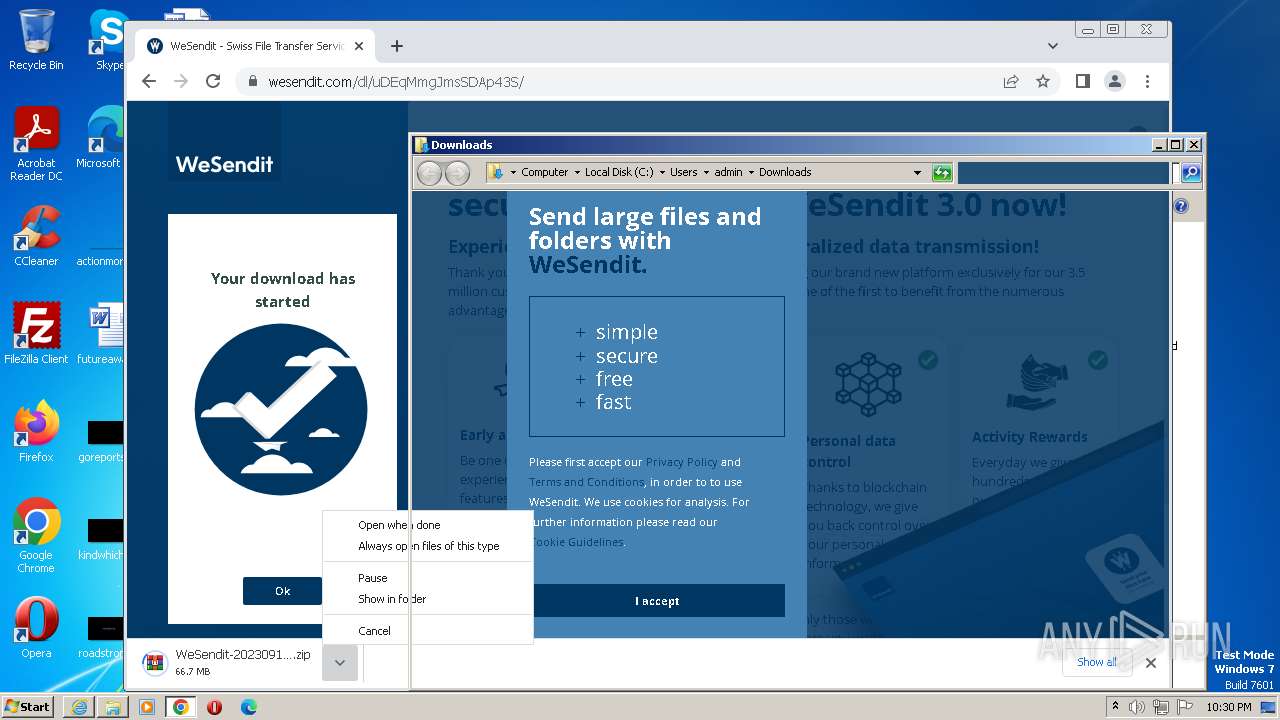
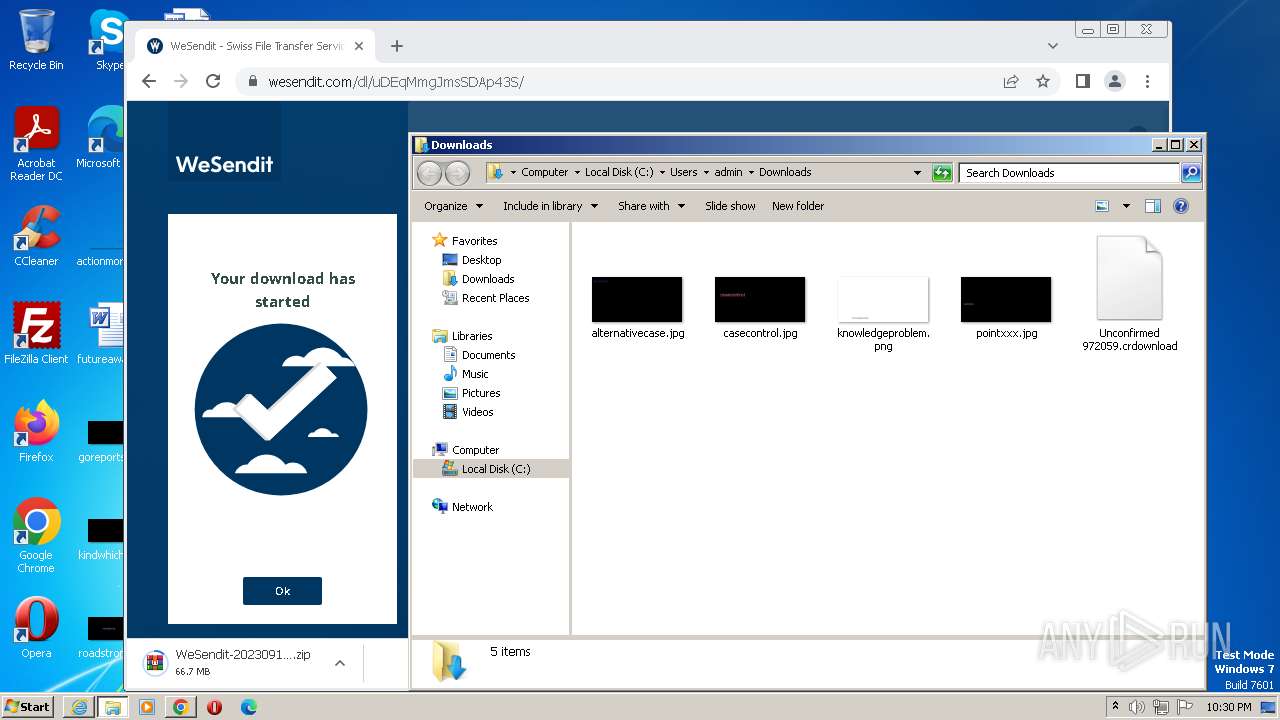
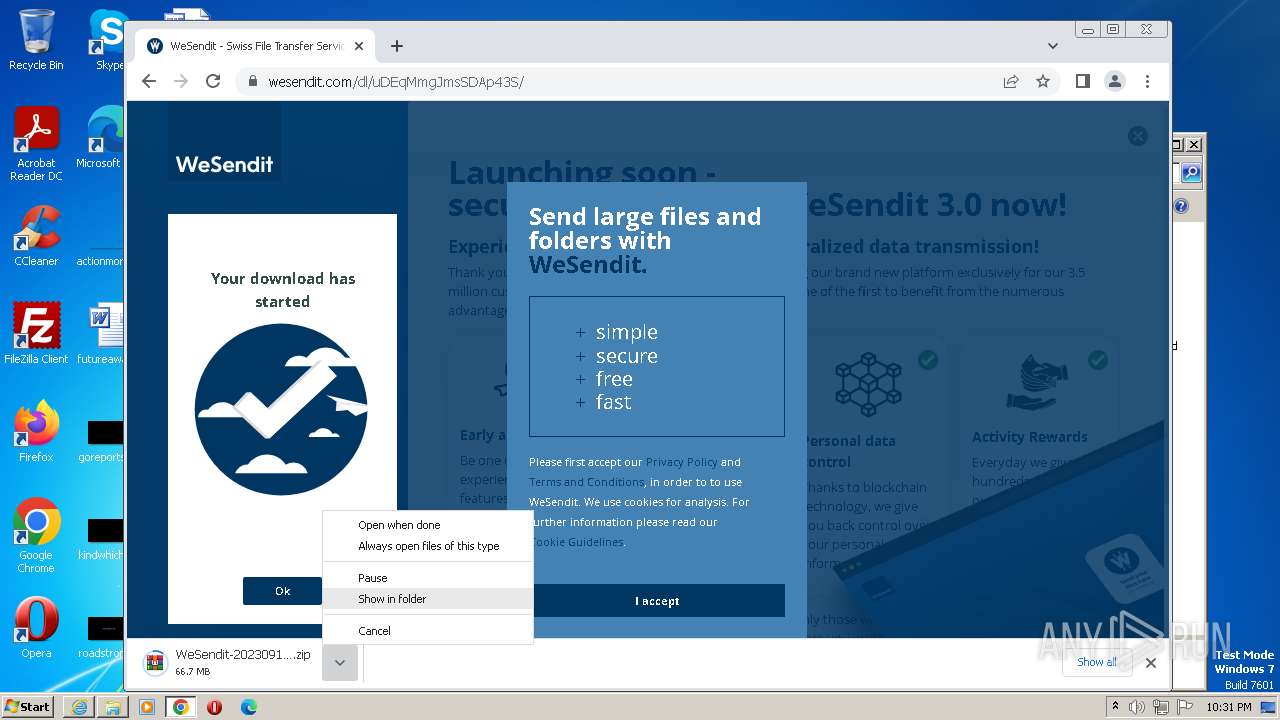
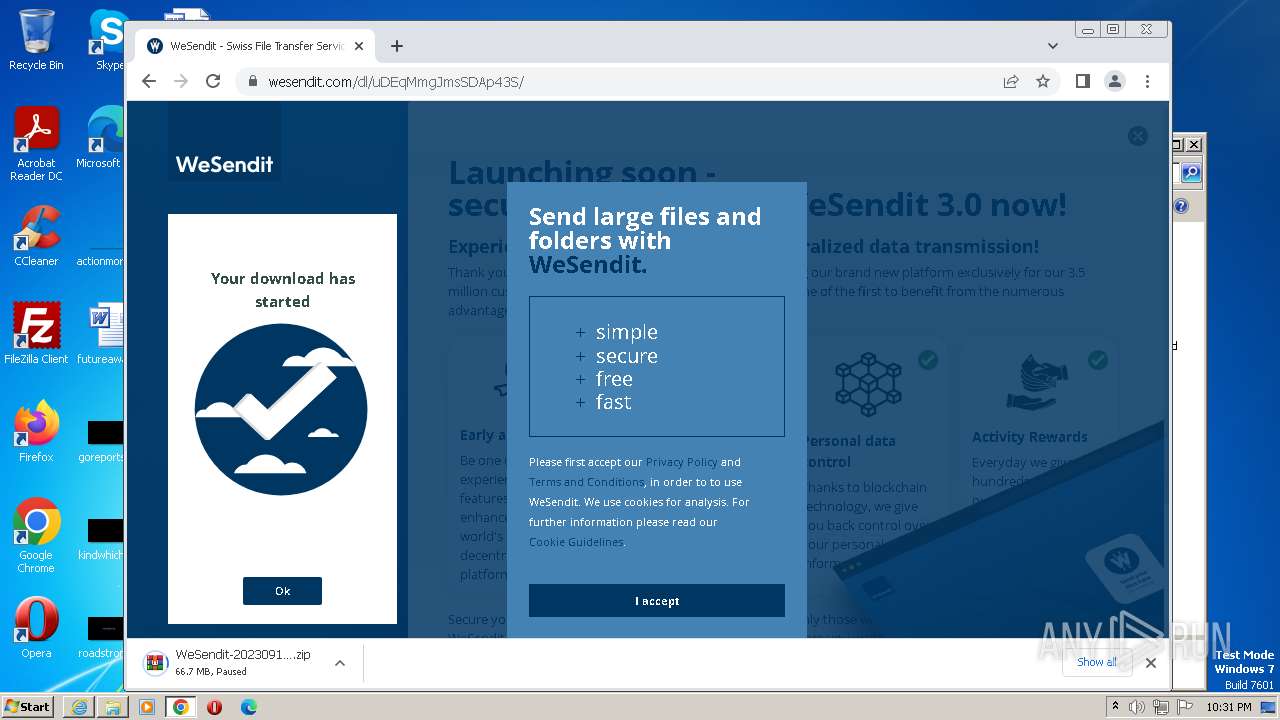
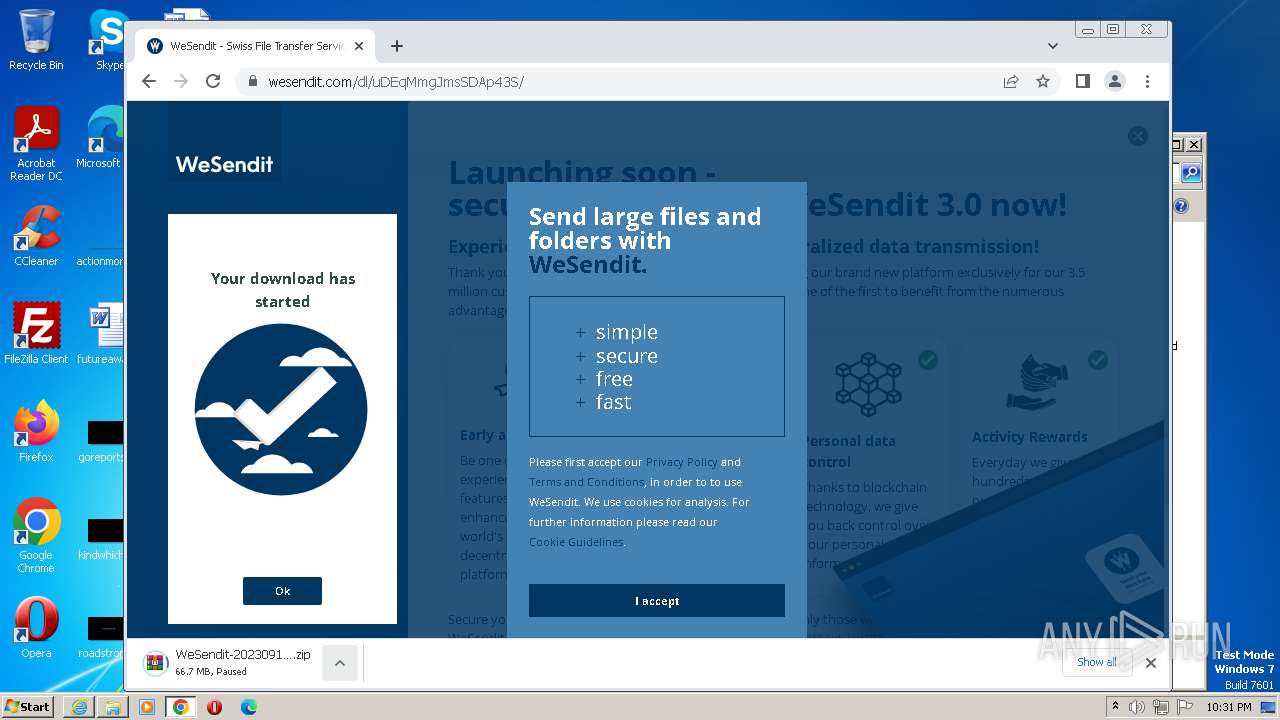
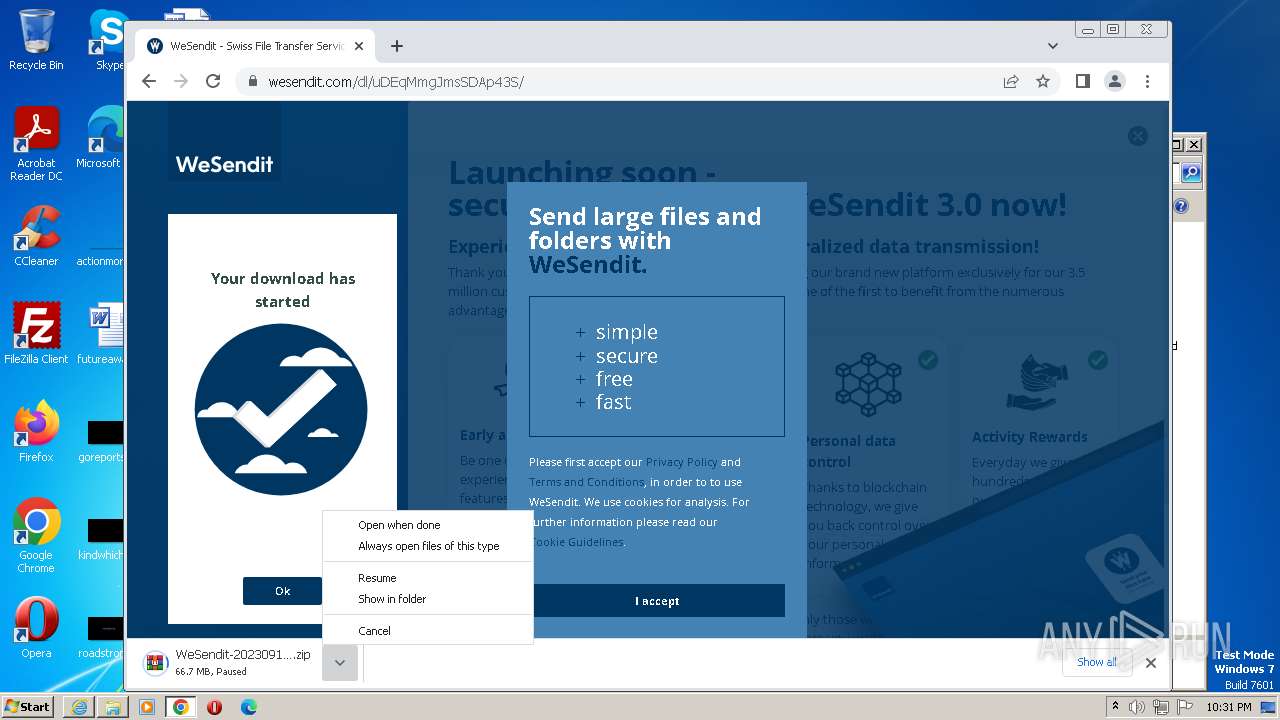
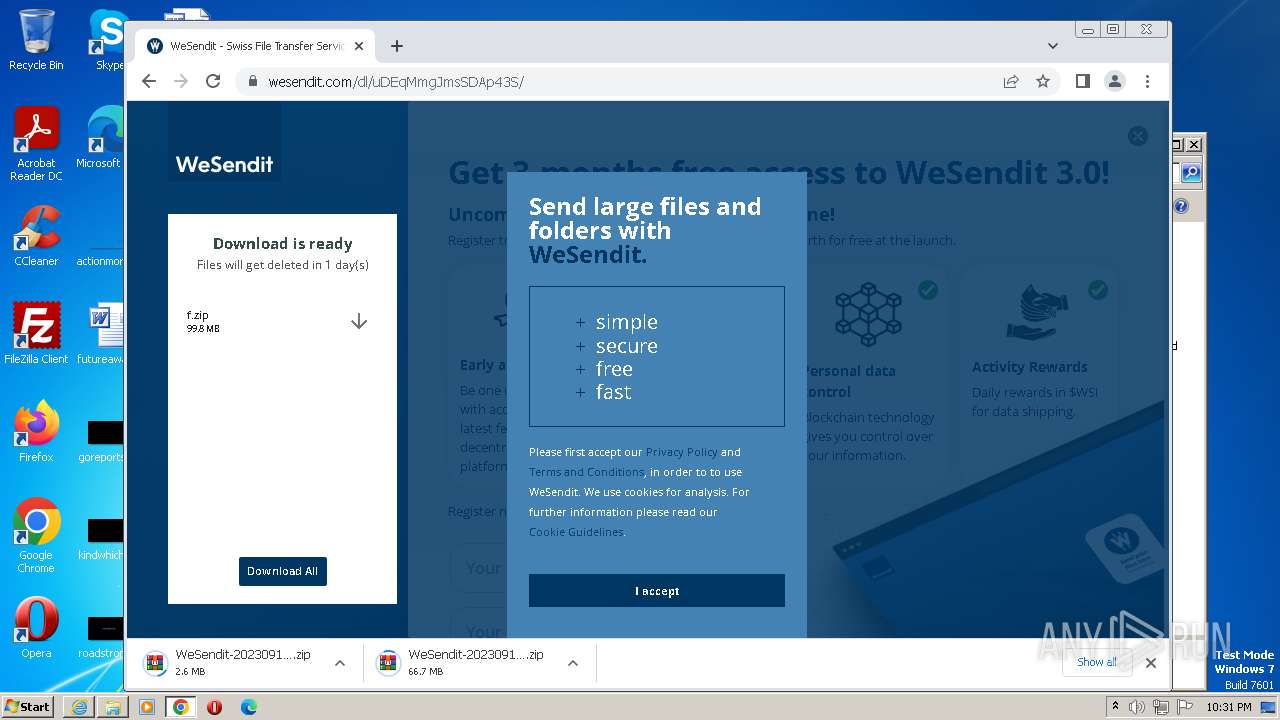
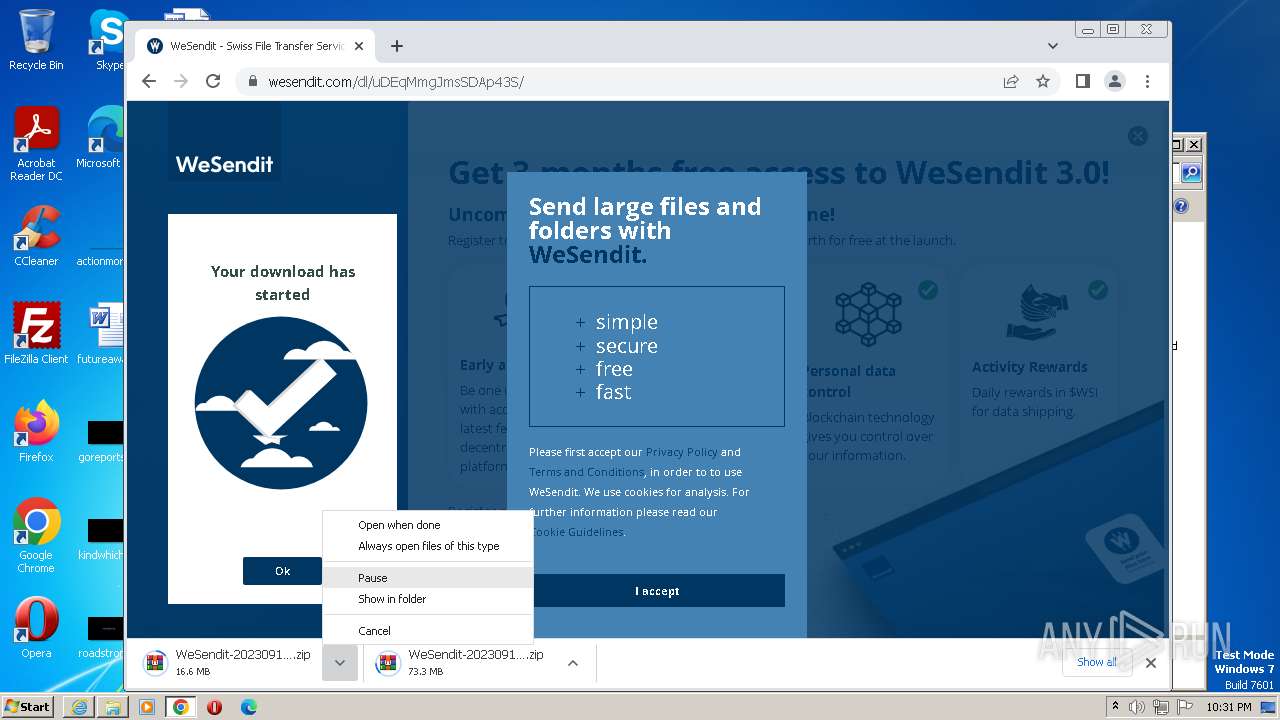
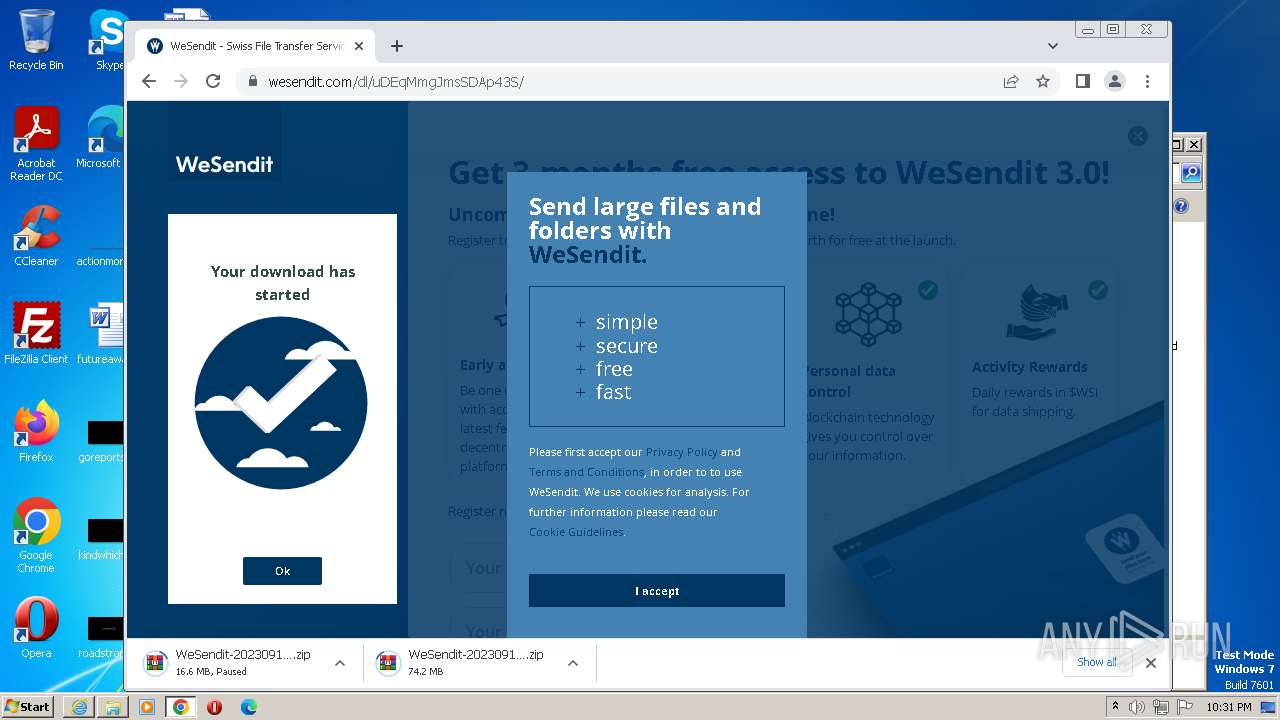
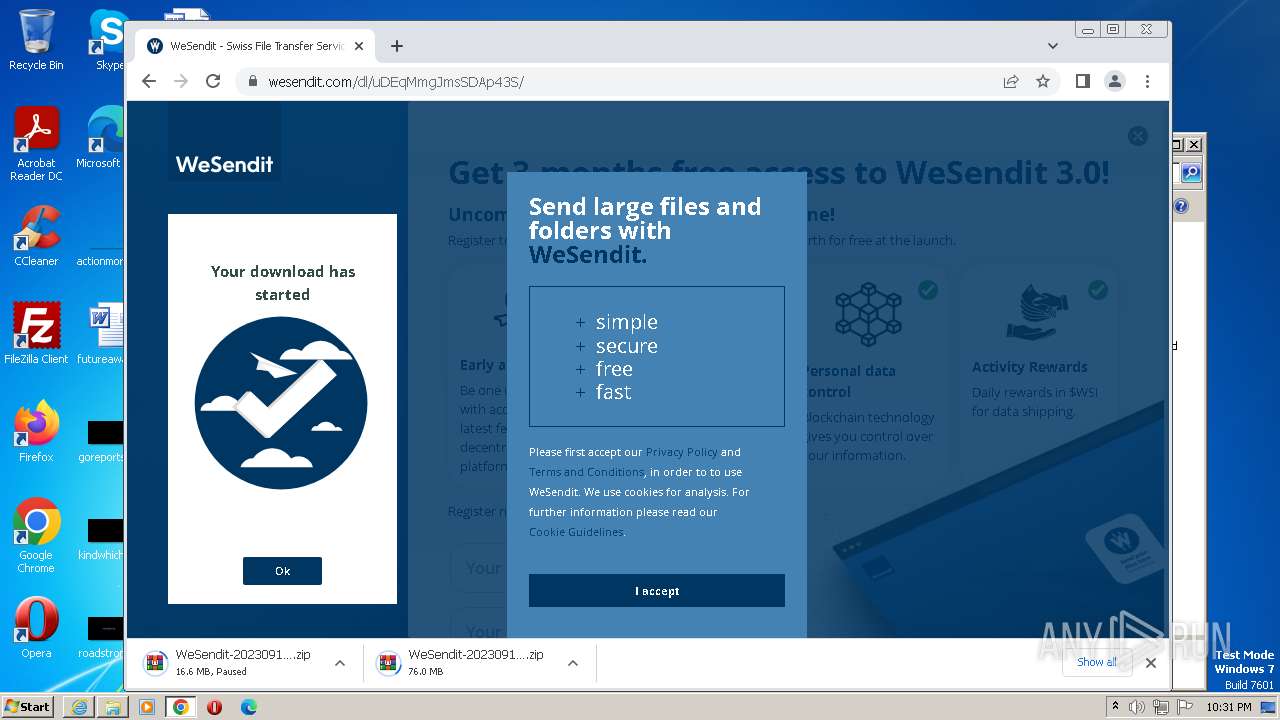
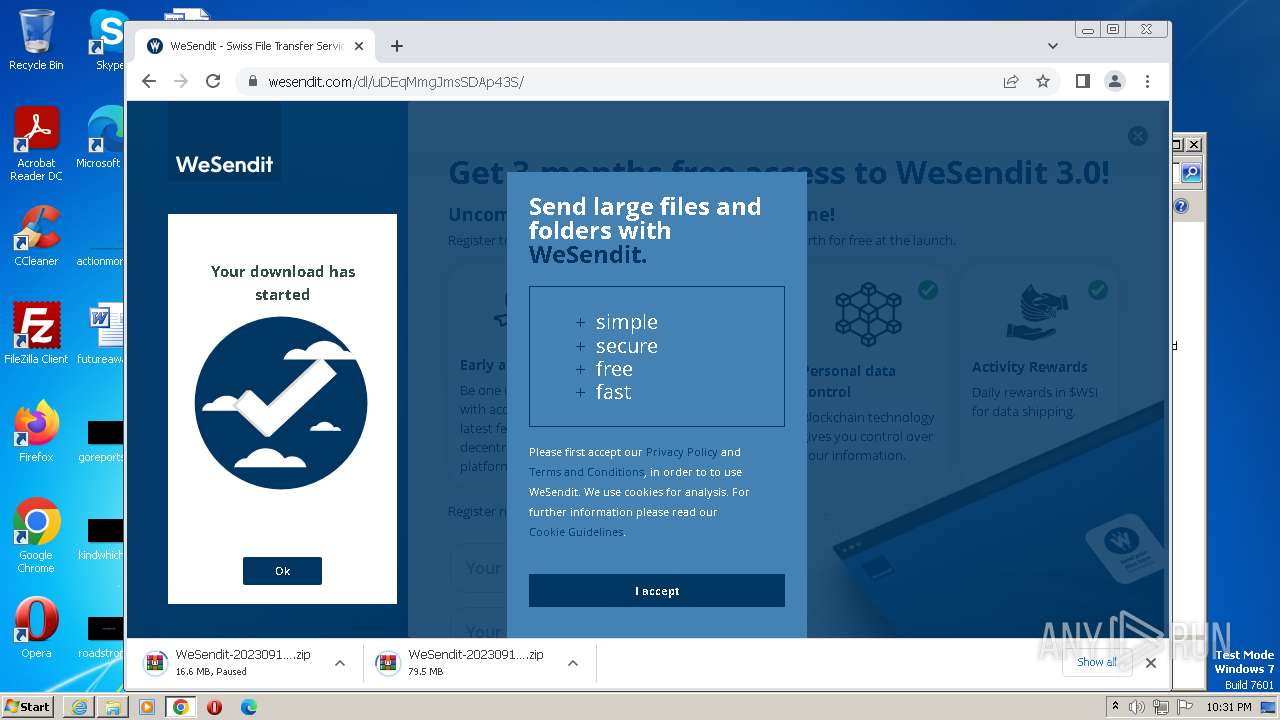
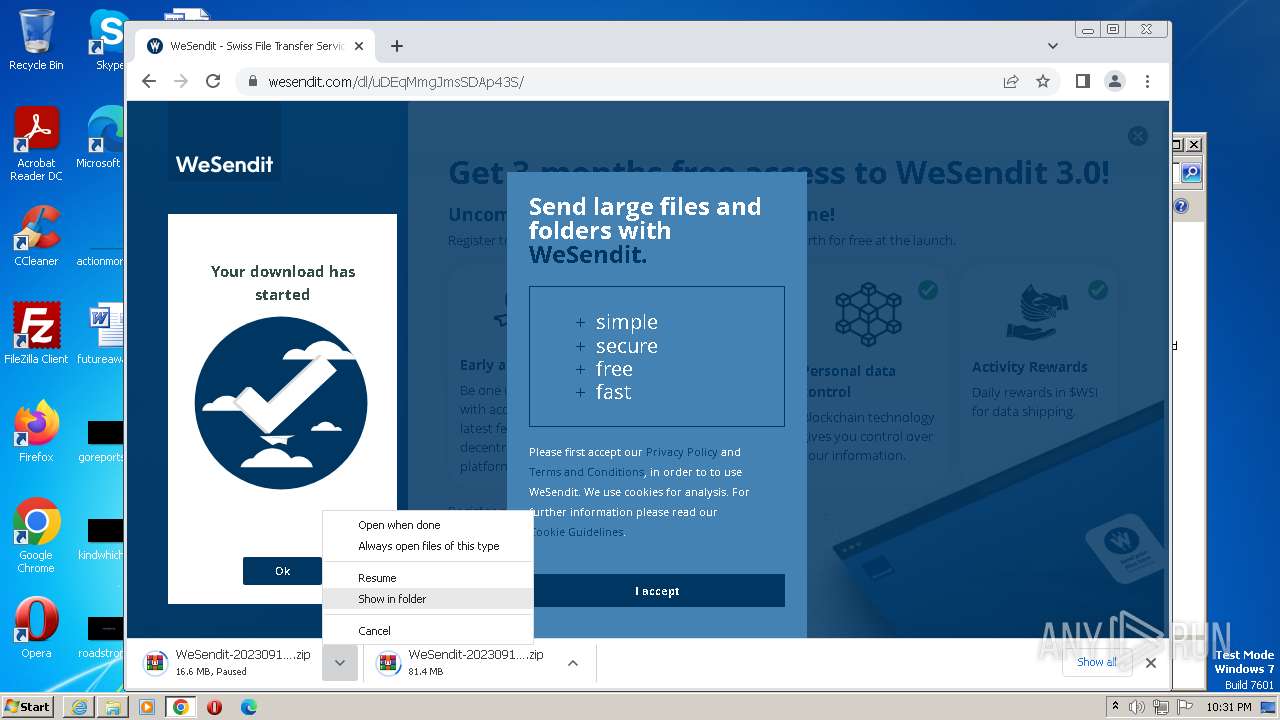
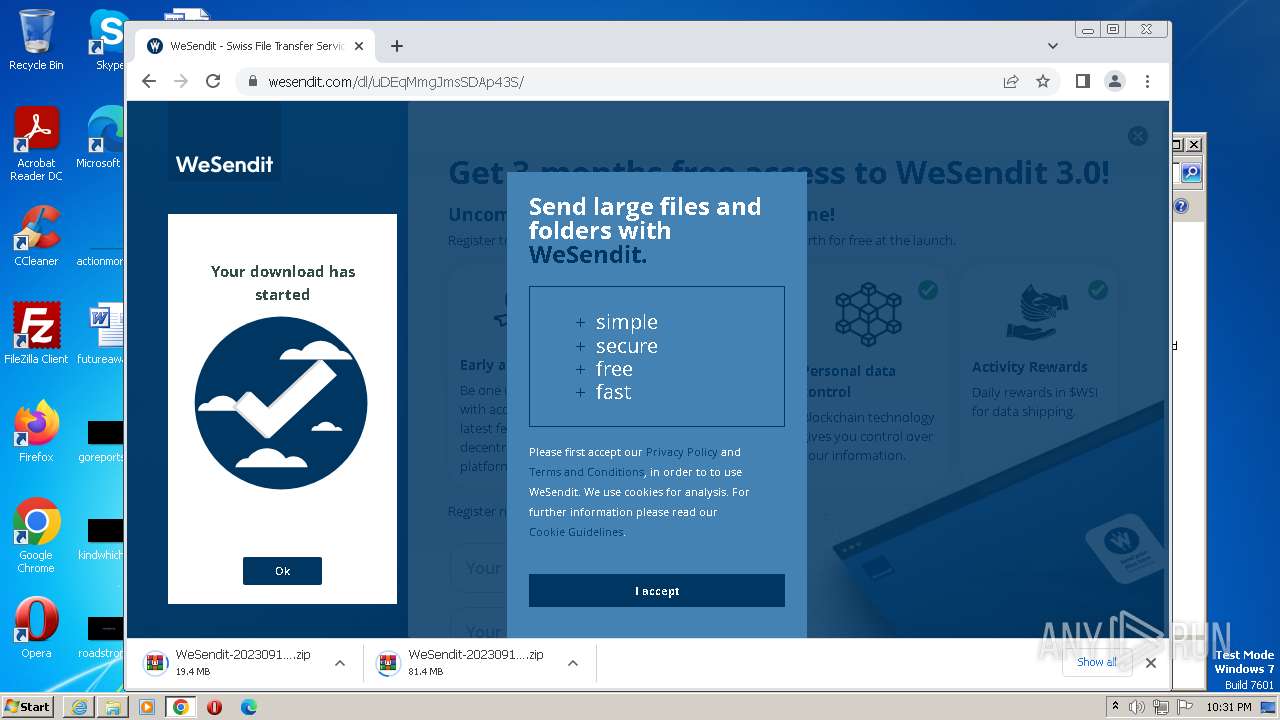
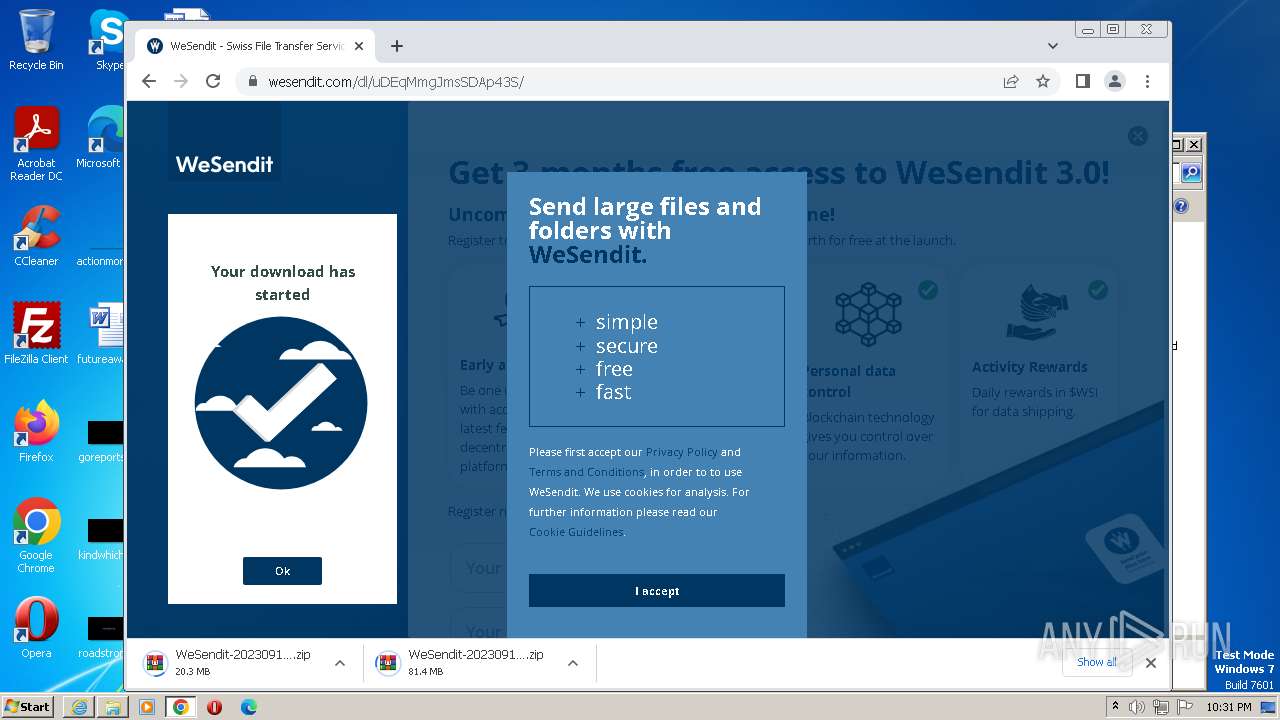
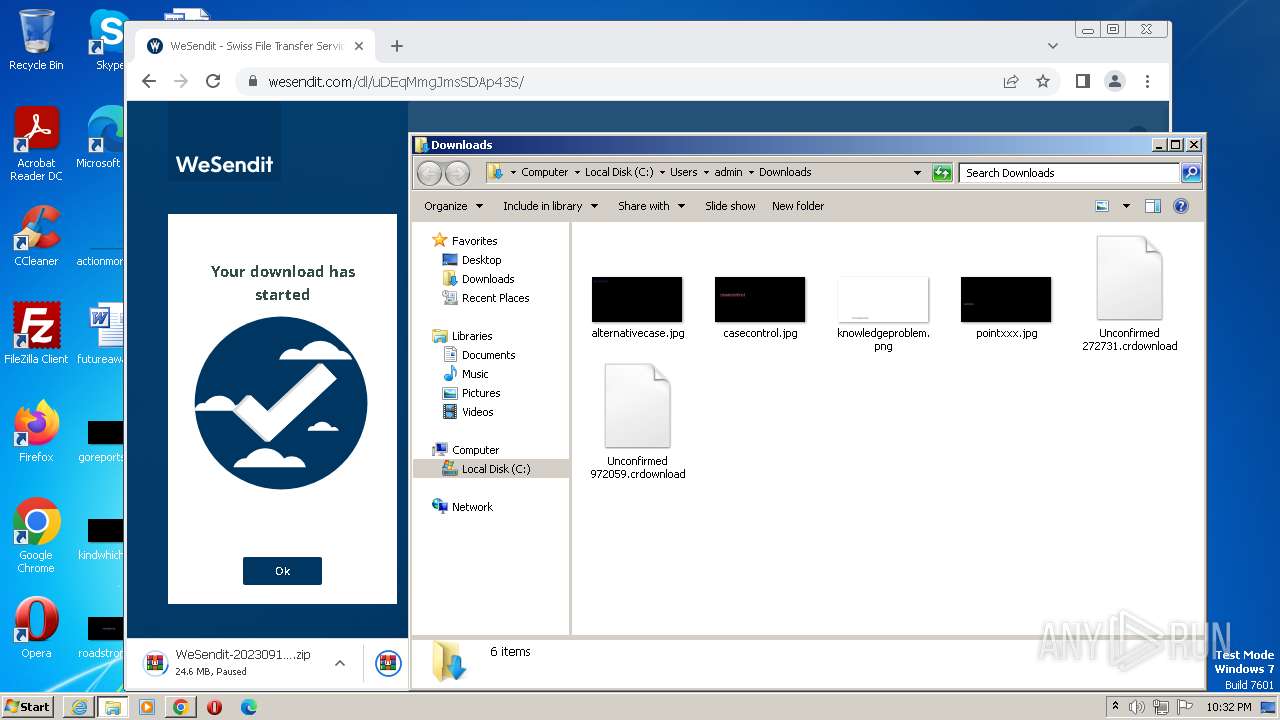
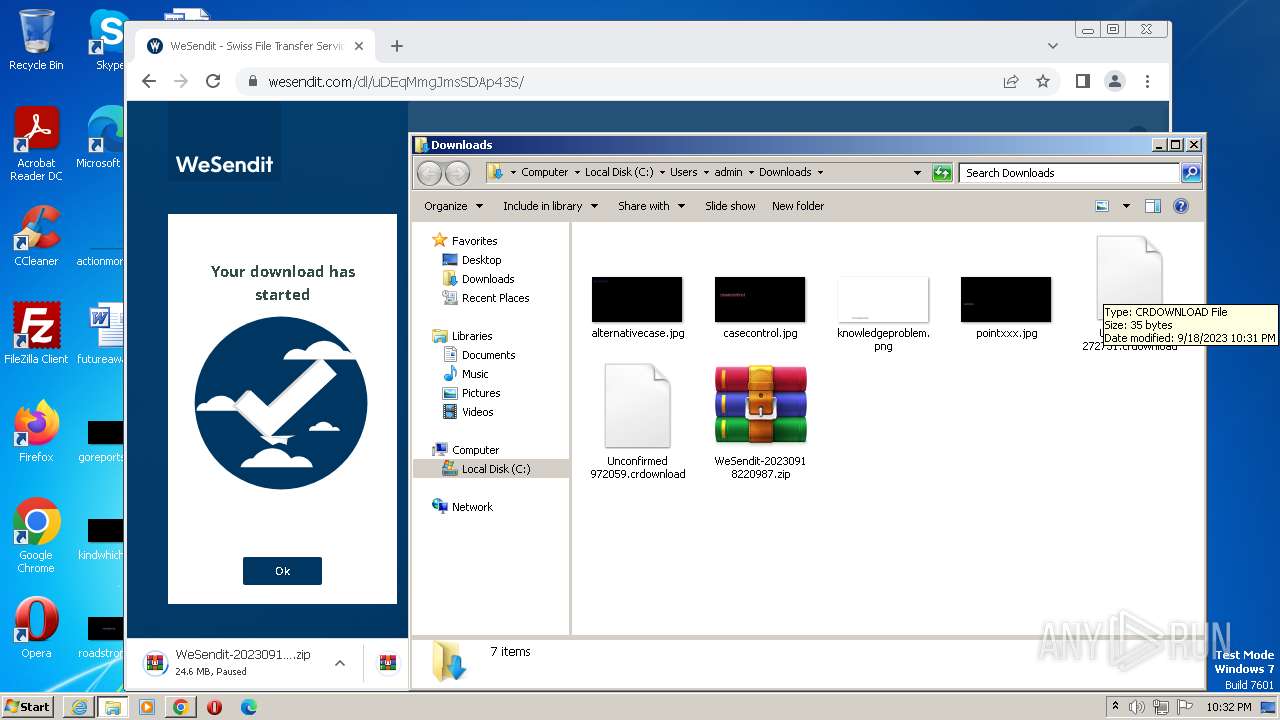
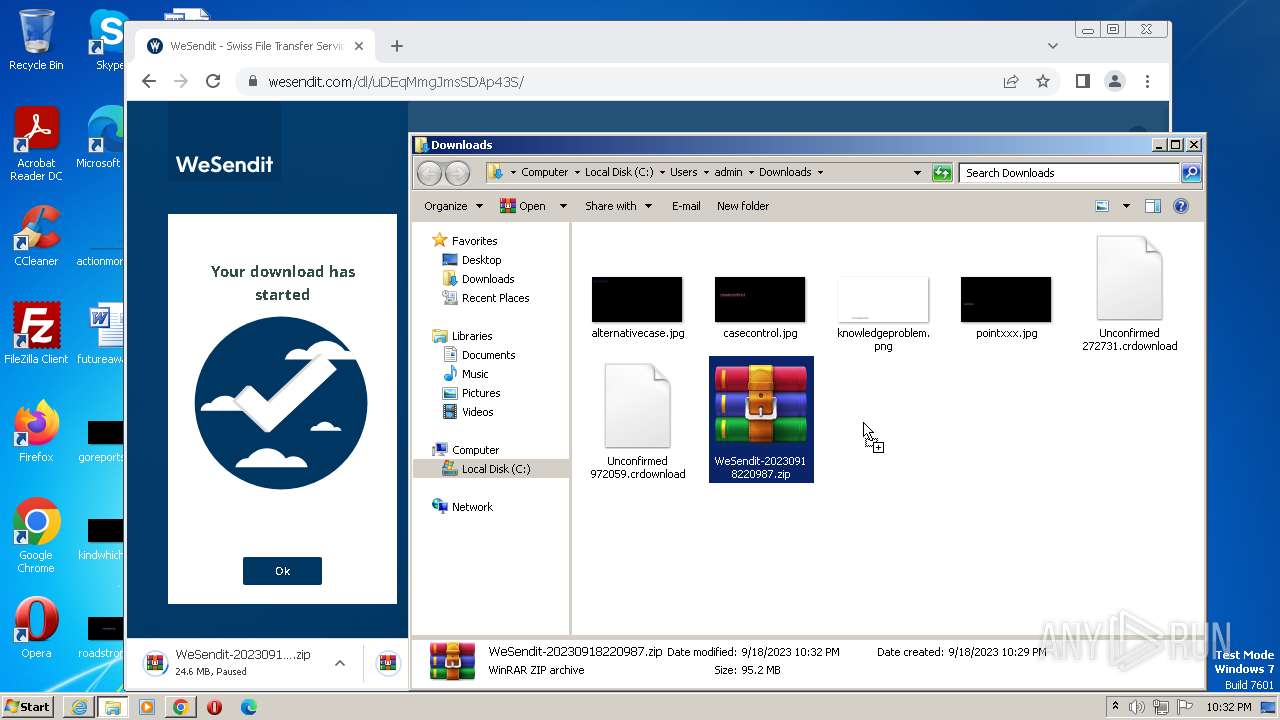
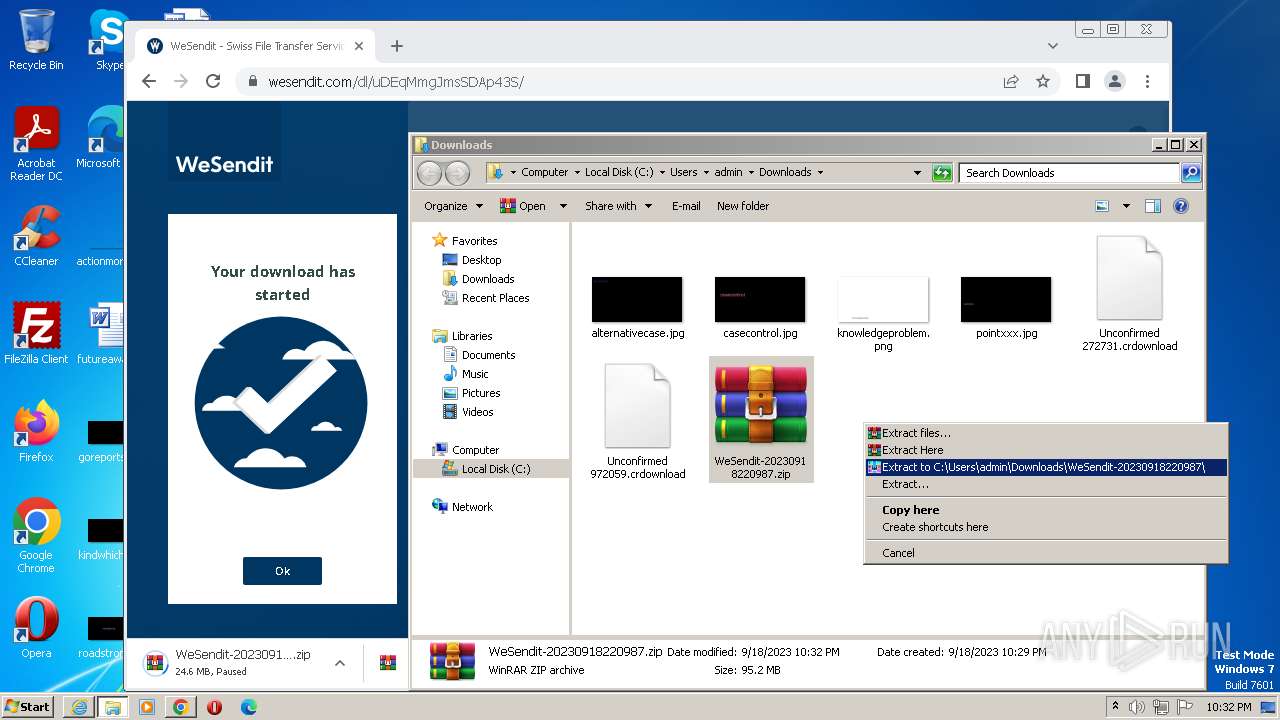
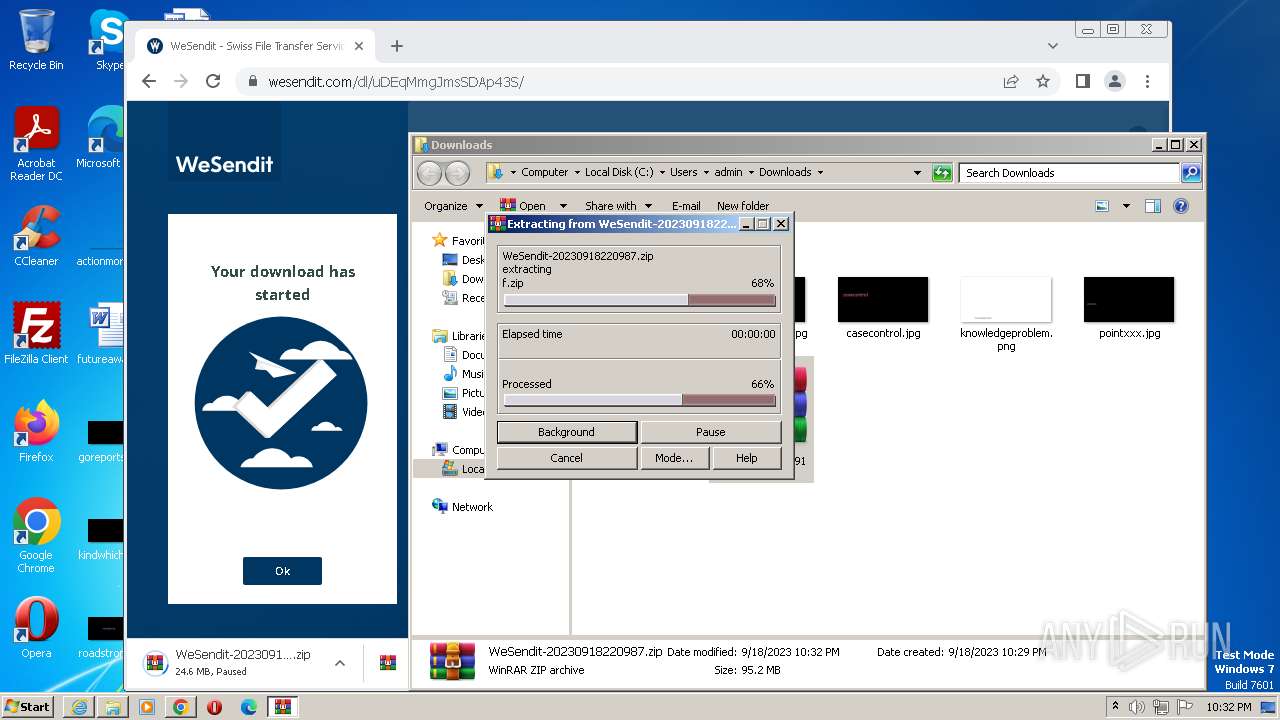
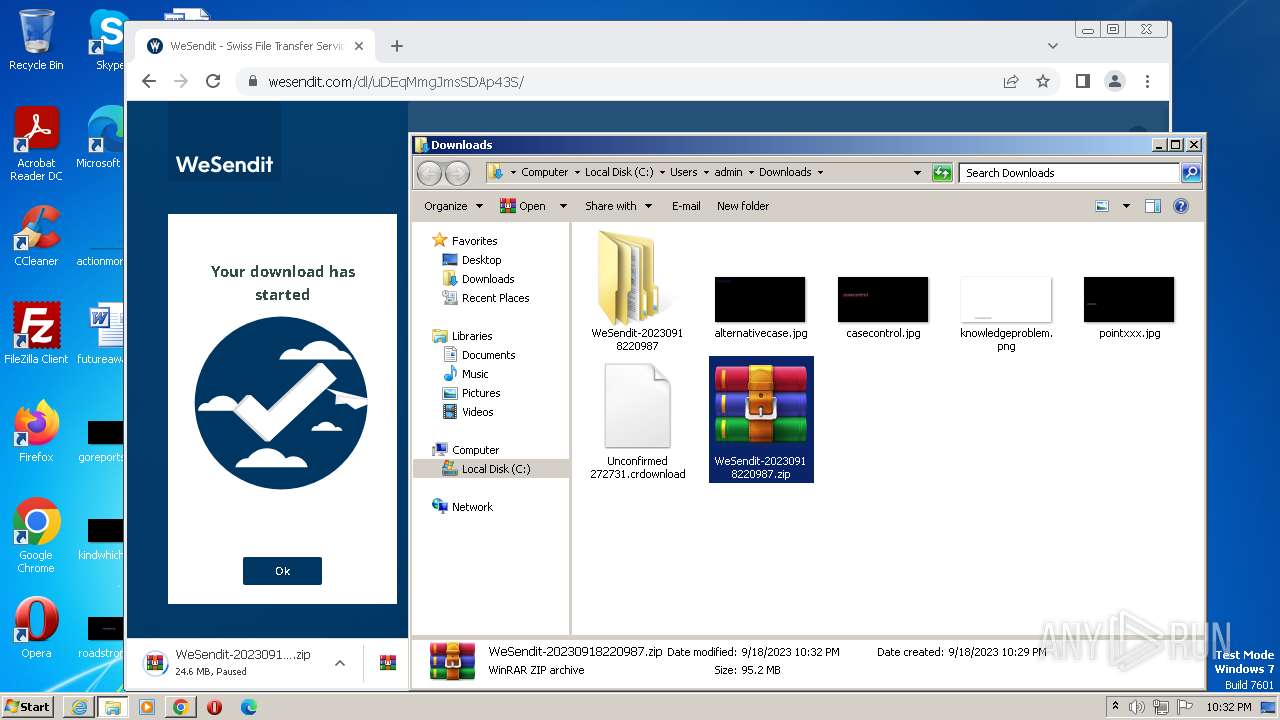
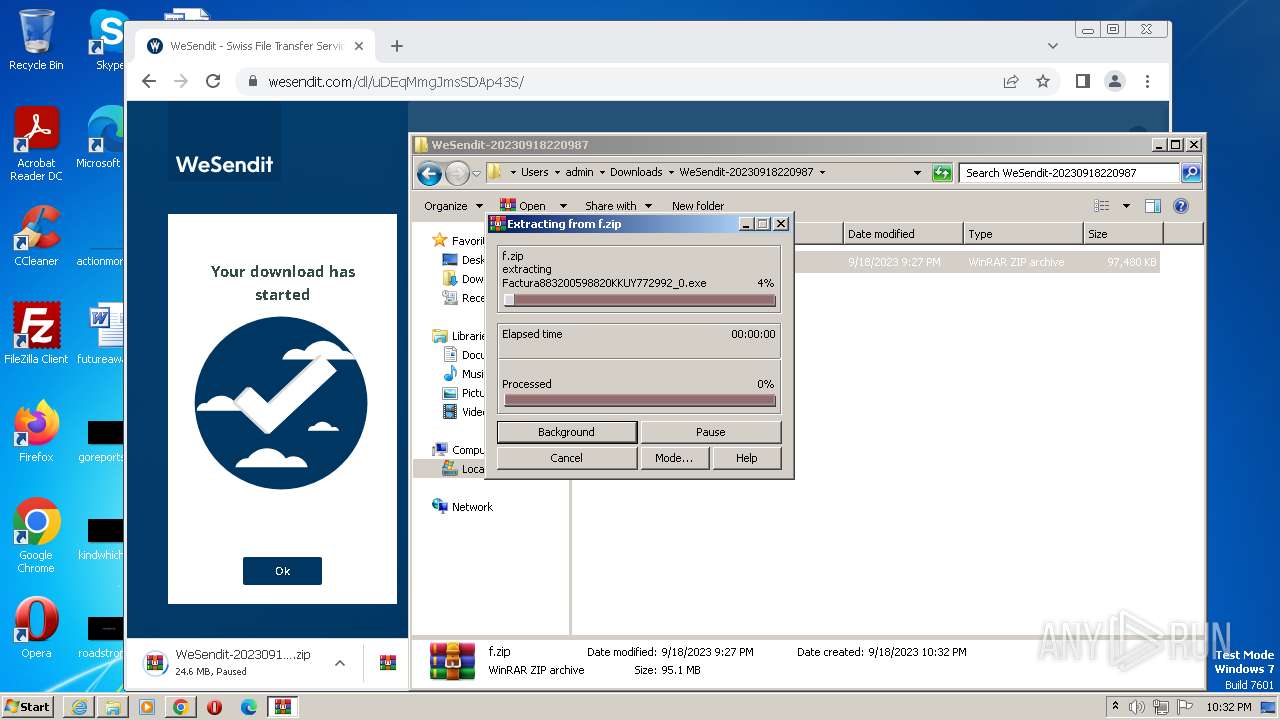
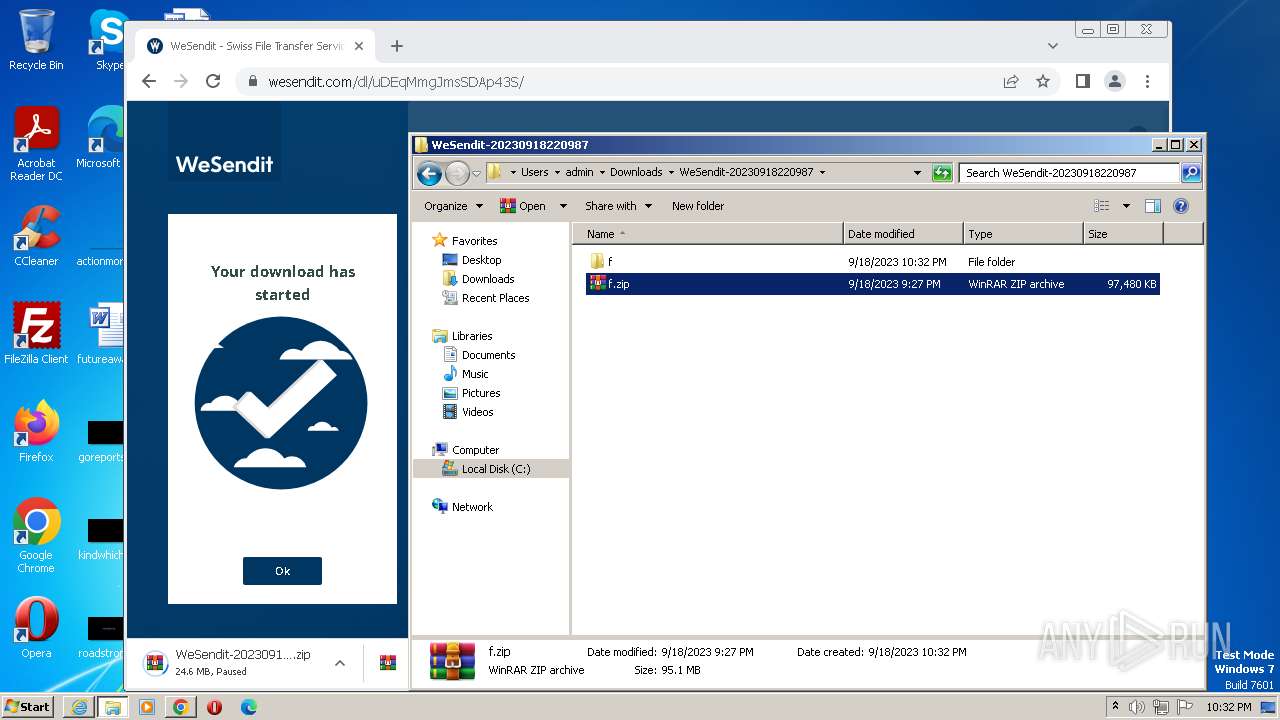
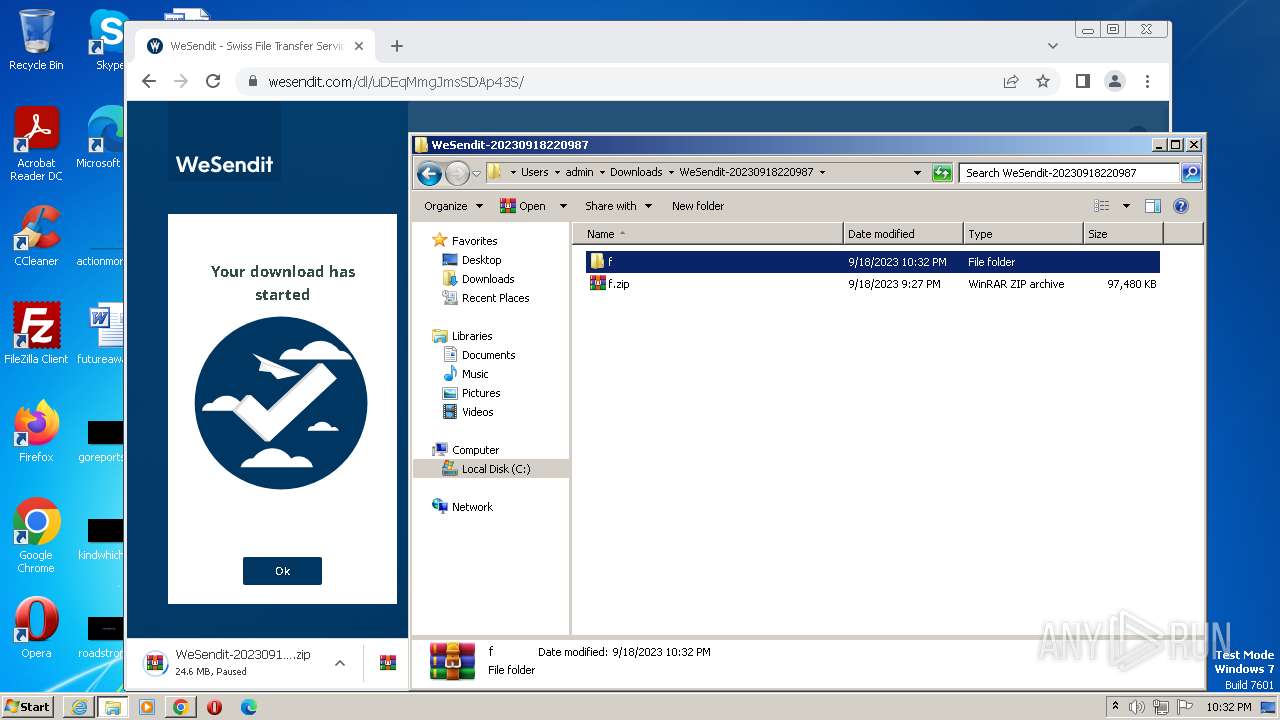
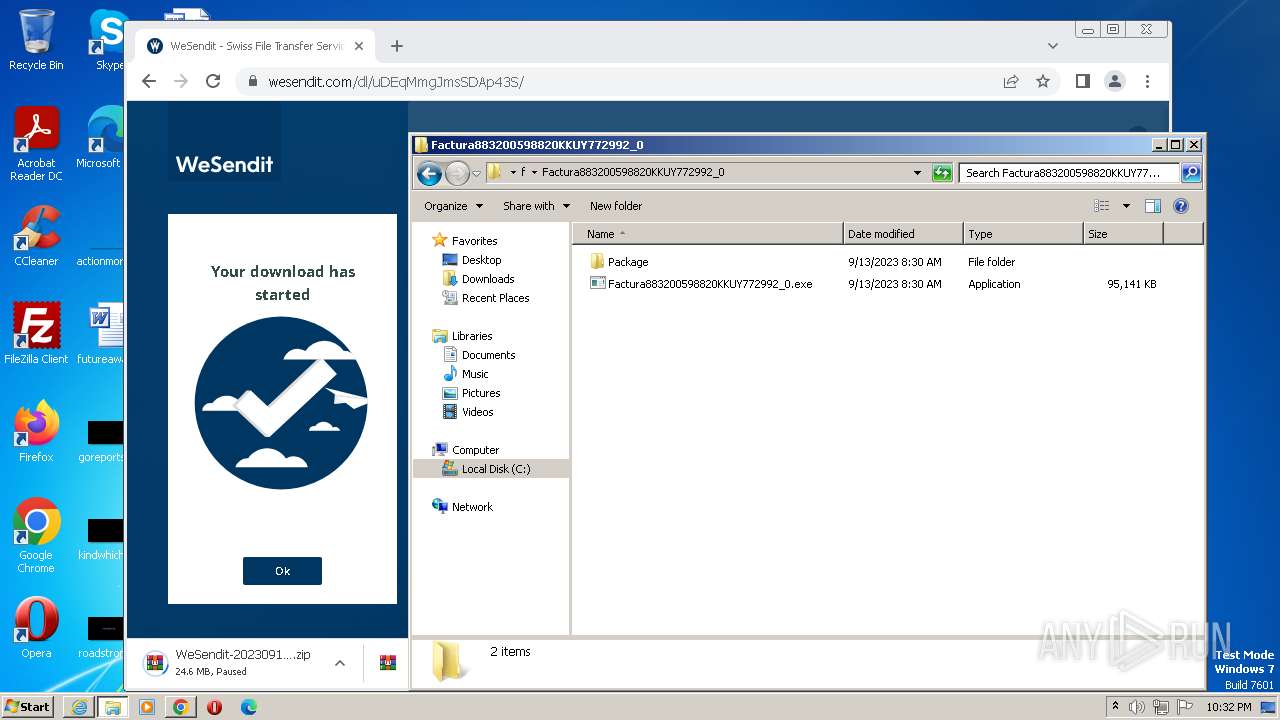
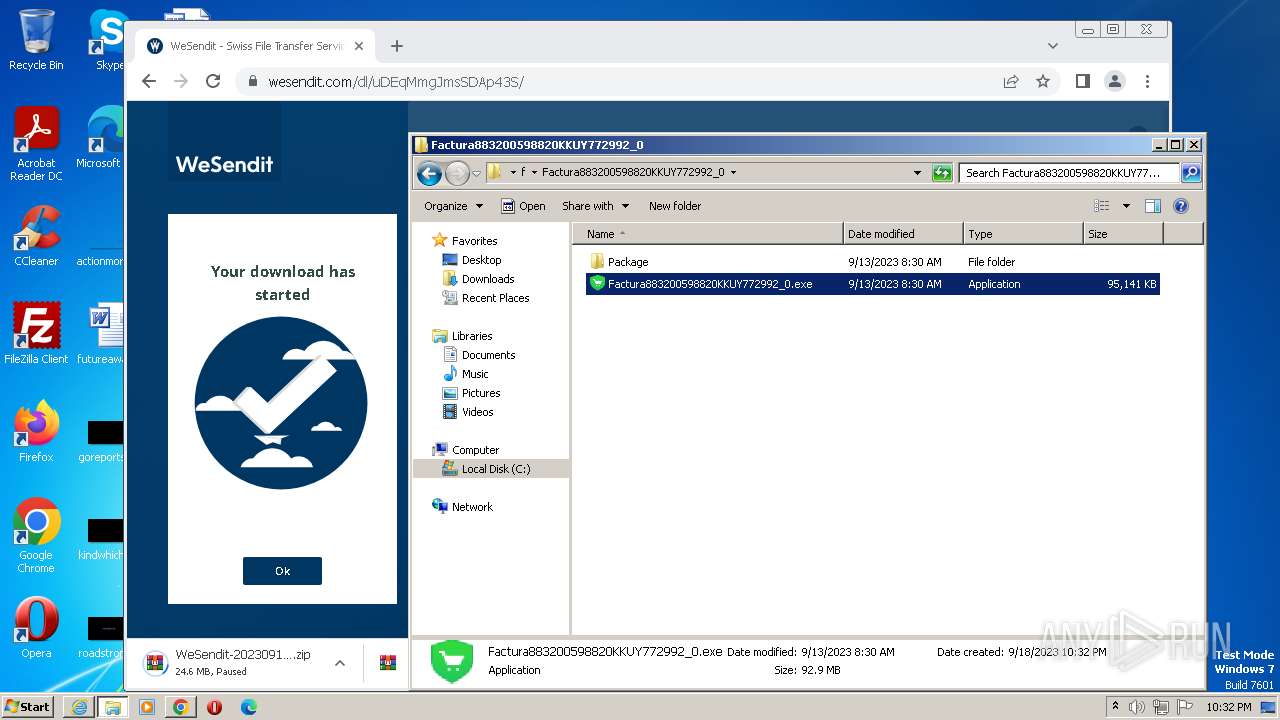
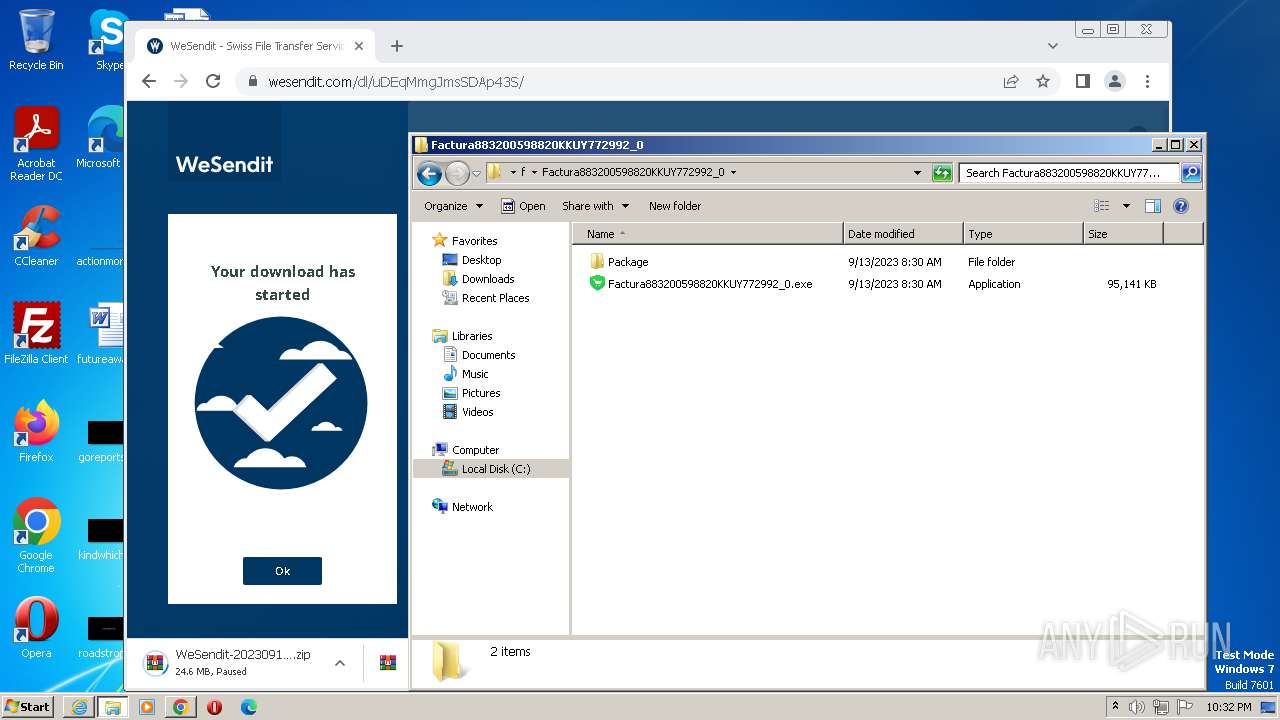
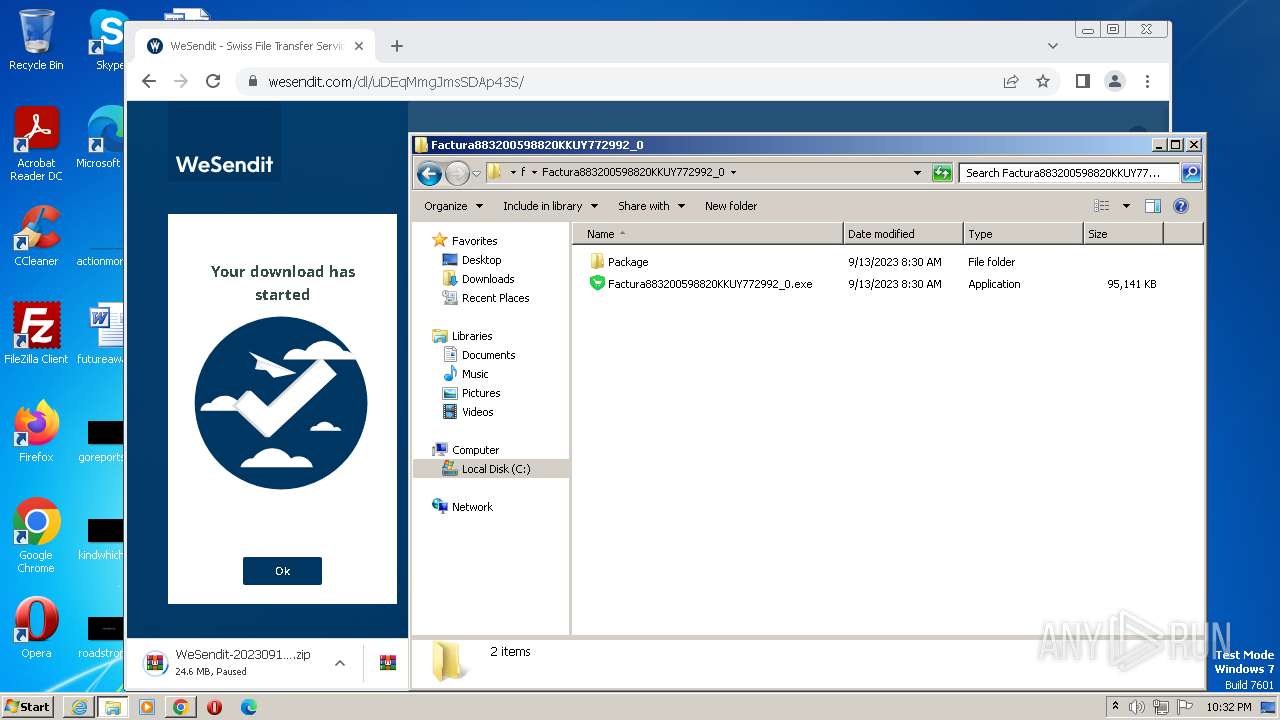
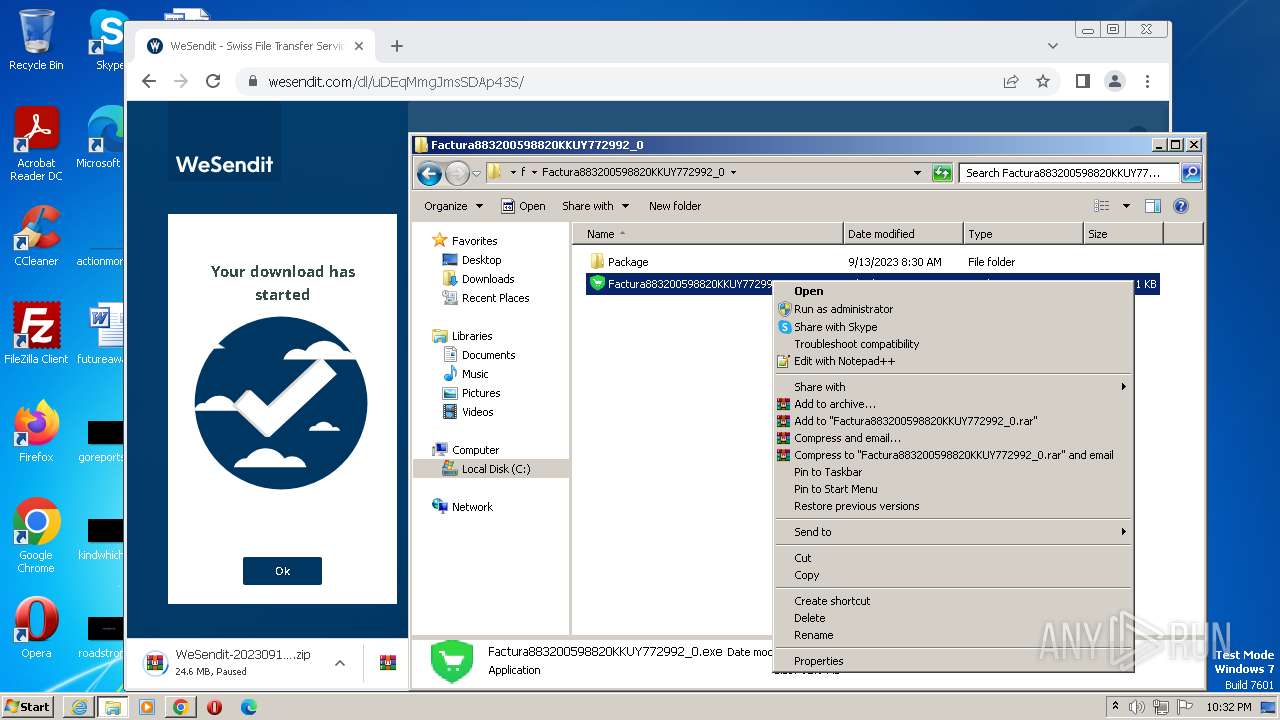
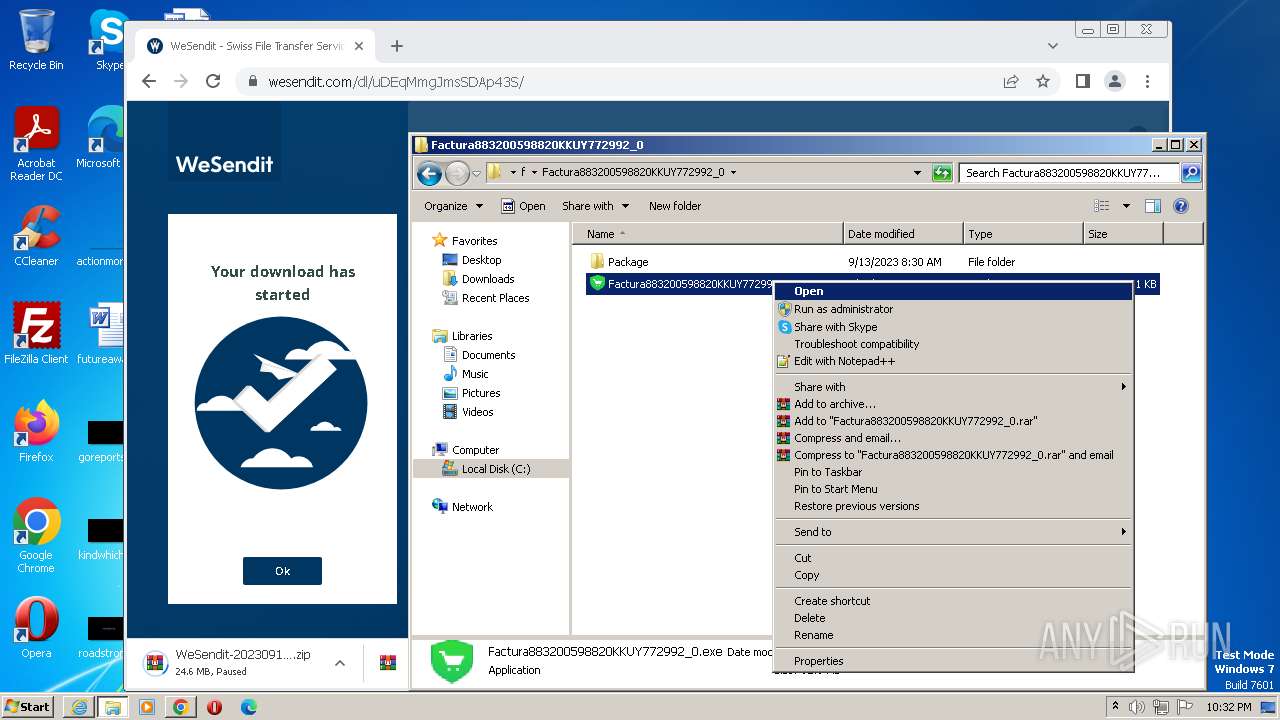
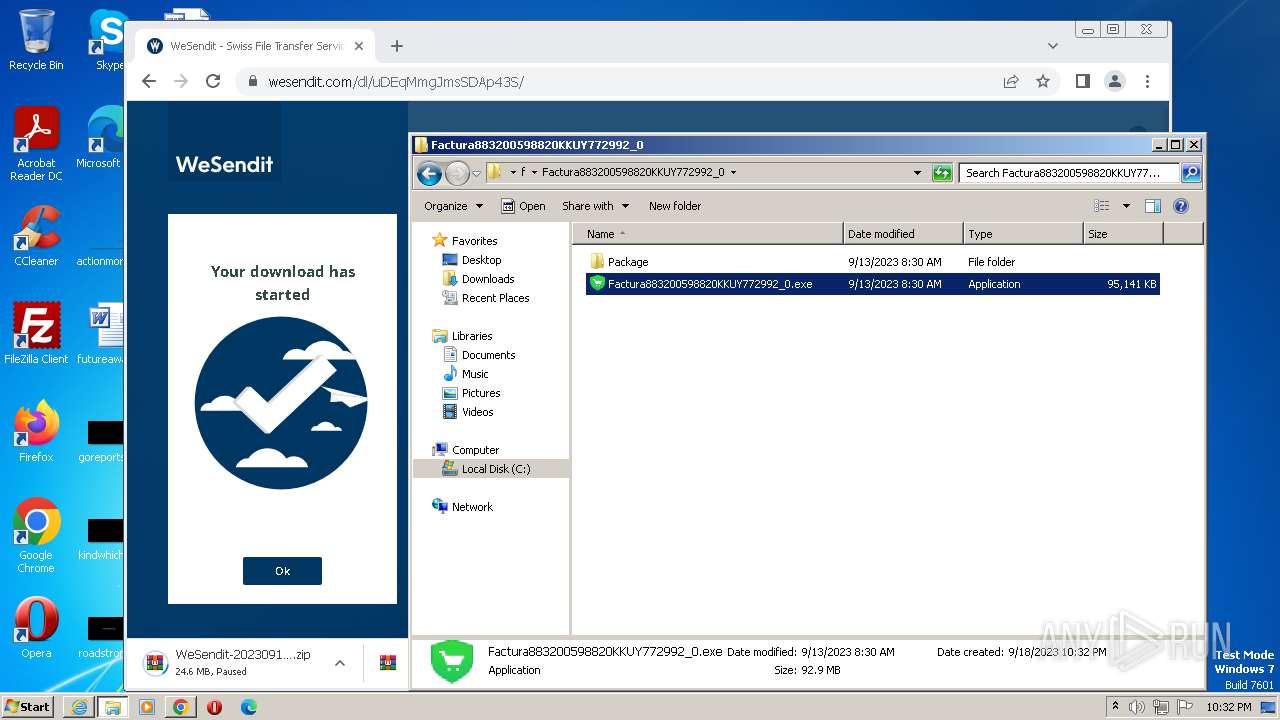
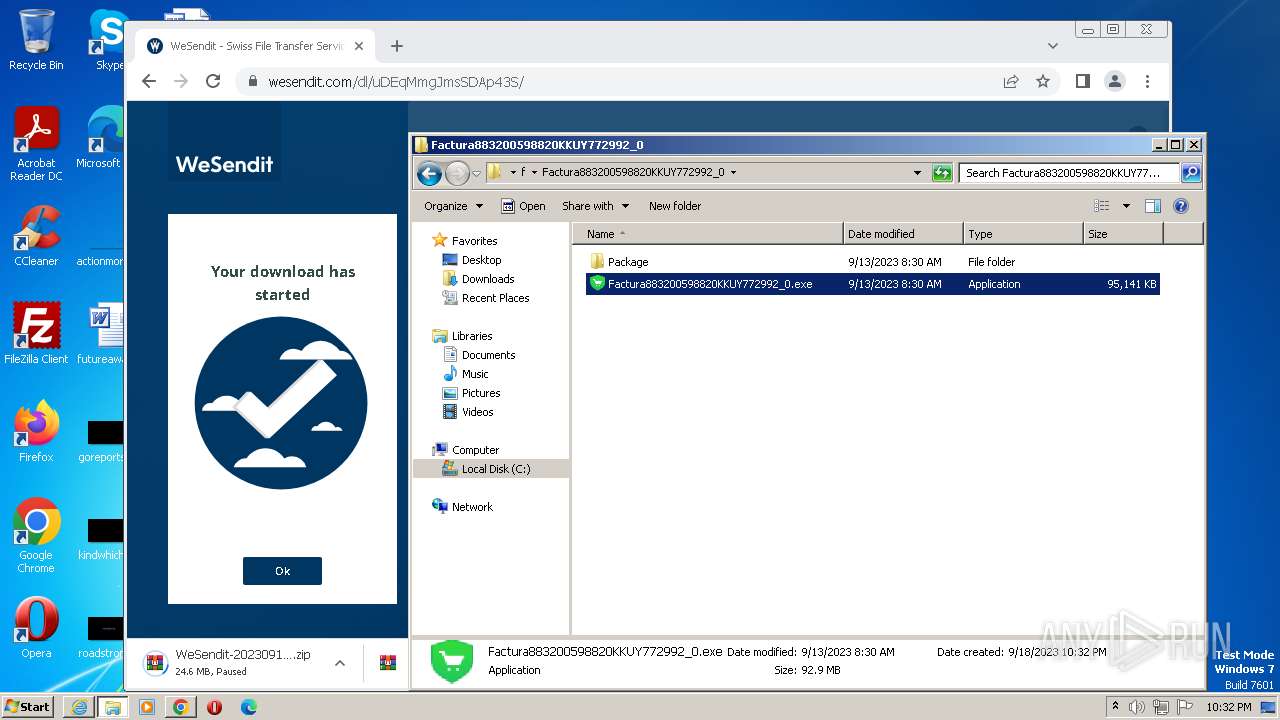
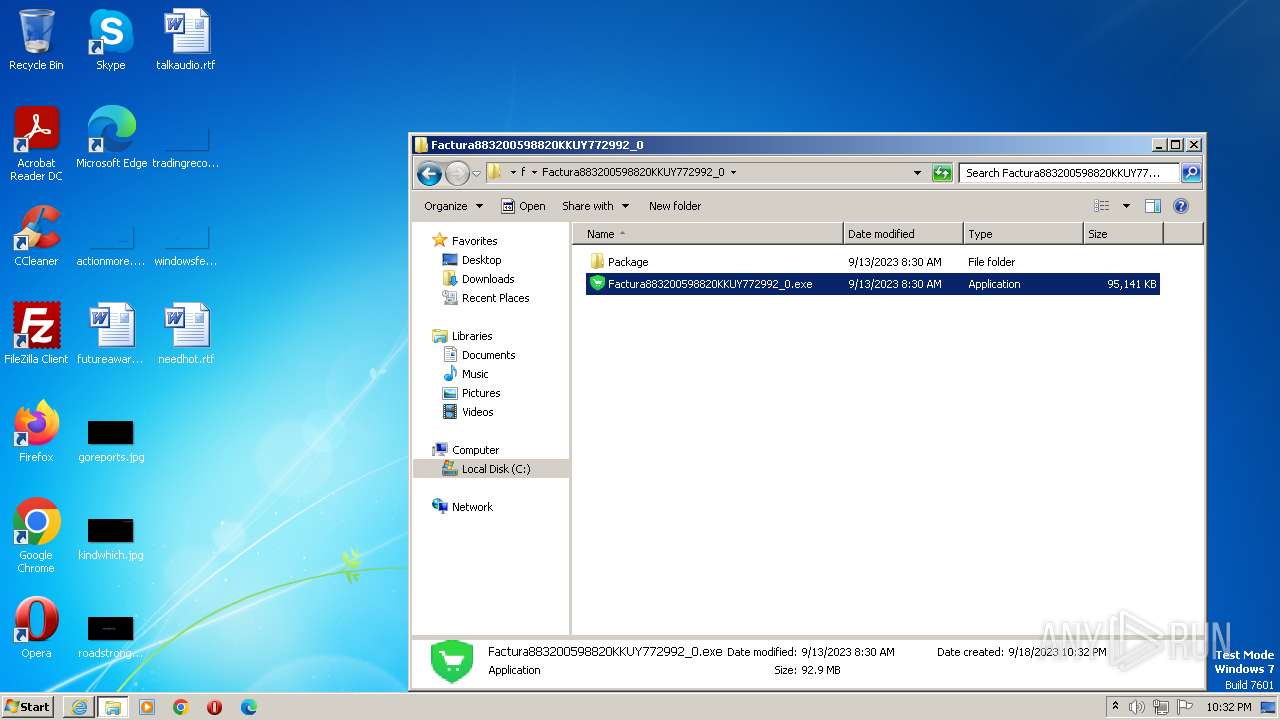
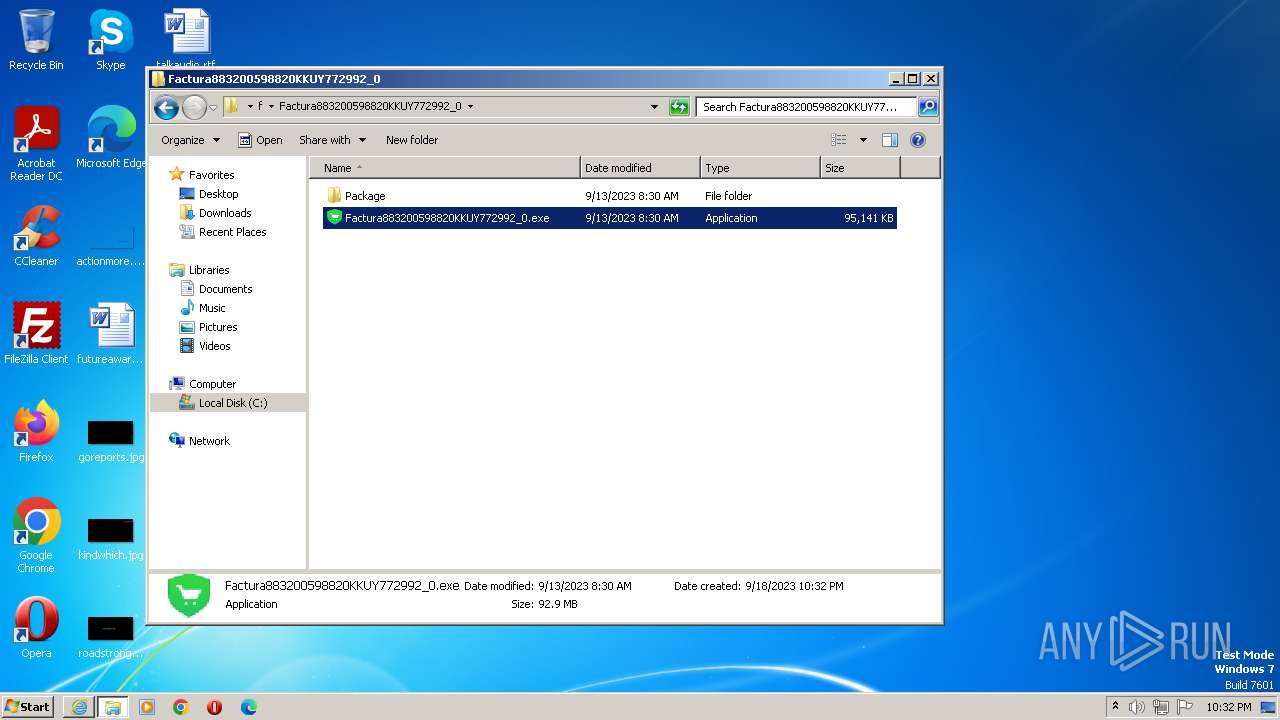
Manual execution by a user
- chrome.exe (PID: 3616)
- WinRAR.exe (PID: 1664)
- WinRAR.exe (PID: 3576)
- Factura883200598820KKUY772992_0.exe (PID: 2460)
- Factura883200598820KKUY772992_0.exe (PID: 2088)
- Factura883200598820KKUY772992_0.exe (PID: 3404)
Application launched itself
- iexplore.exe (PID: 996)
- chrome.exe (PID: 3616)
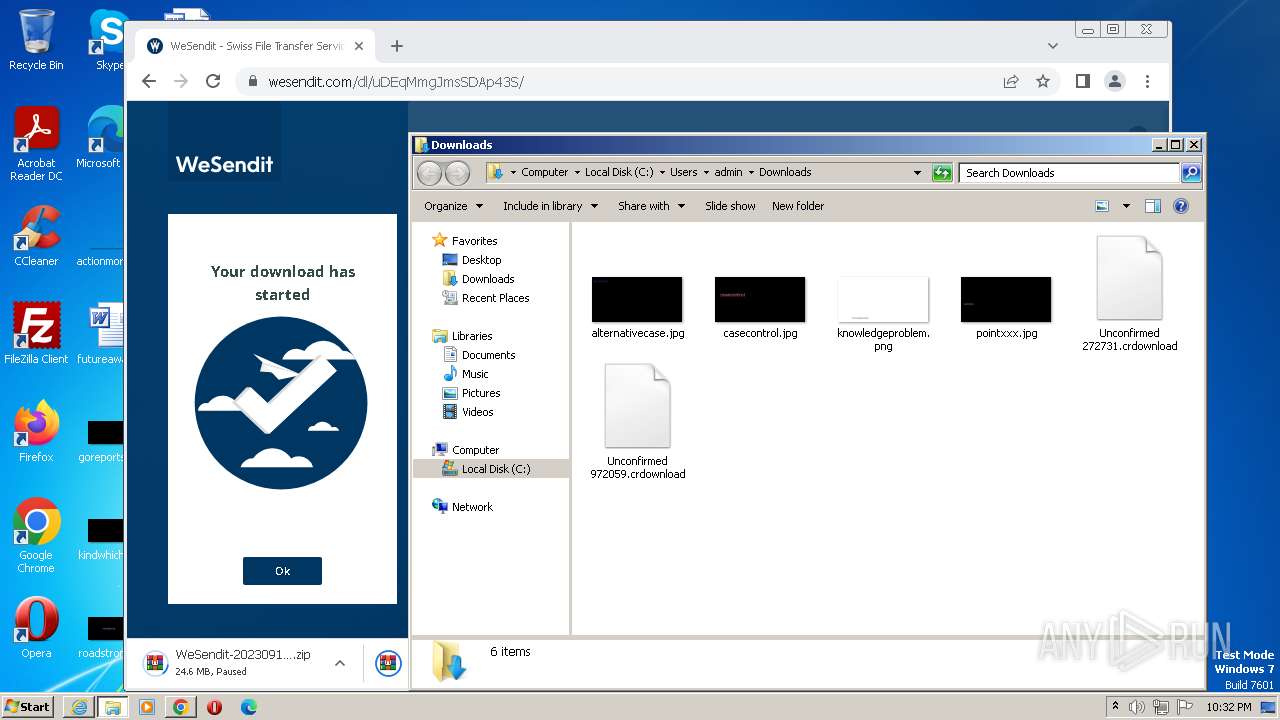
The process uses the downloaded file
- chrome.exe (PID: 3580)
- chrome.exe (PID: 3832)
- chrome.exe (PID: 3200)
- chrome.exe (PID: 2564)
- WinRAR.exe (PID: 1664)
Creates files or folders in the user directory
- Factura883200598820KKUY772992_0.exe (PID: 2460)
Checks supported languages
- Factura883200598820KKUY772992_0.exe (PID: 2460)
- Factura883200598820KKUY772992_0.exe (PID: 2088)
- Factura883200598820KKUY772992_0.exe (PID: 3404)
Reads the computer name
- Factura883200598820KKUY772992_0.exe (PID: 2460)
Reads the machine GUID from the registry
- Factura883200598820KKUY772992_0.exe (PID: 2460)
Create files in a temporary directory
- Factura883200598820KKUY772992_0.exe (PID: 2460)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
76
Monitored processes
31
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 900 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=12 --mojo-platform-channel-handle=2336 --field-trial-handle=1236,i,14409184210809088823,2444241897877441864,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=2376 --field-trial-handle=1236,i,14409184210809088823,2444241897877441864,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 996 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://wsi.li/dl/uDEqMmgJmsSDAp43S/" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1200 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1316 --field-trial-handle=1236,i,14409184210809088823,2444241897877441864,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1424 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:996 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3712 --field-trial-handle=1236,i,14409184210809088823,2444241897877441864,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
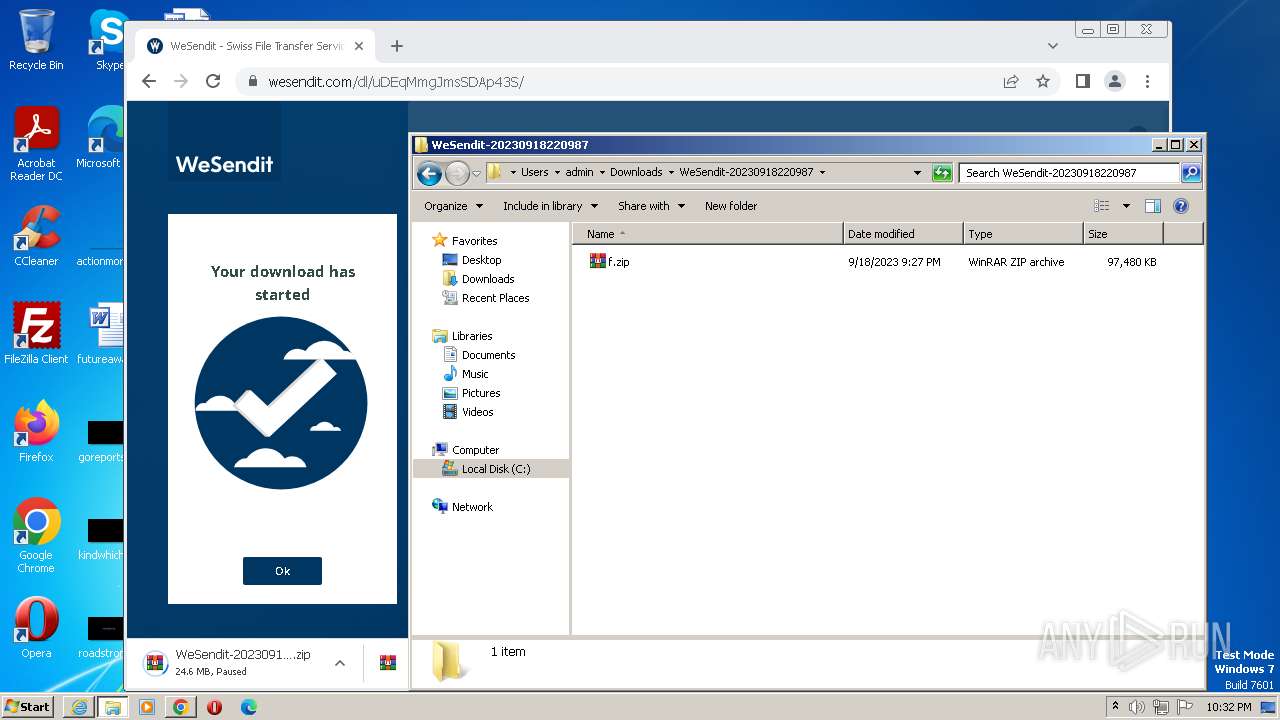
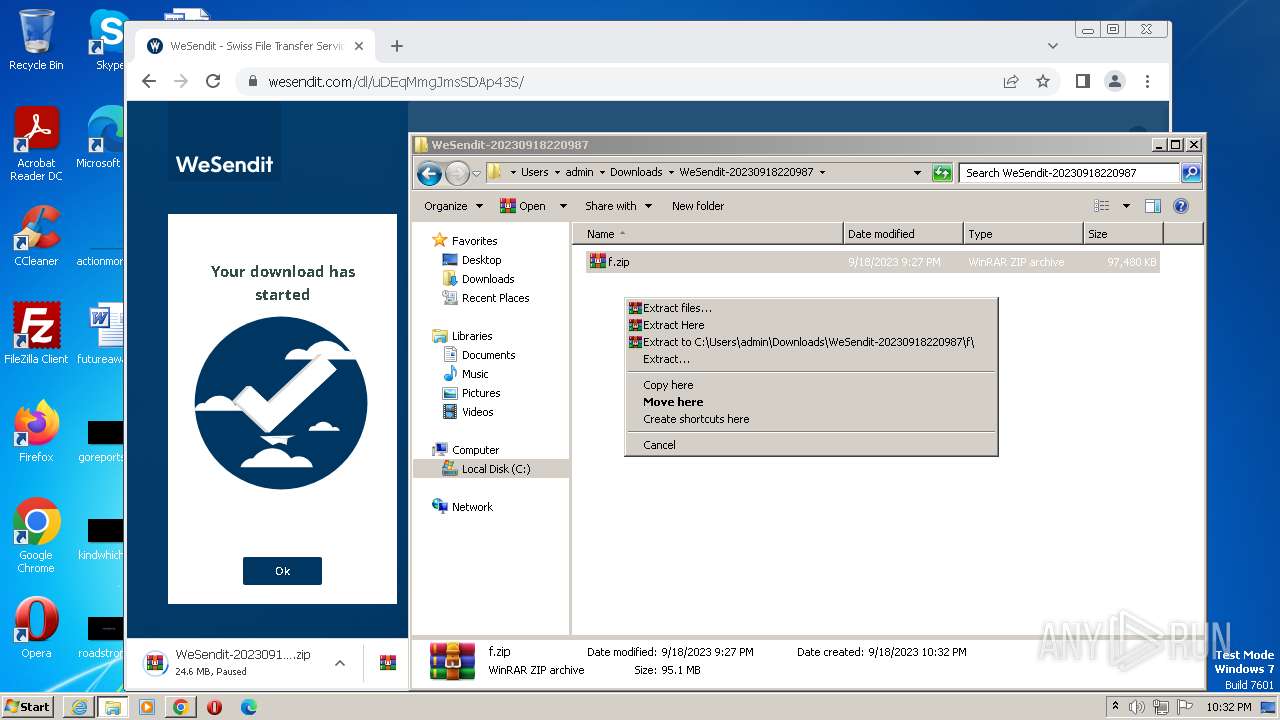
| 1664 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\WeSendit-20230918220987.zip" C:\Users\admin\Downloads\WeSendit-20230918220987\ | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3356 --field-trial-handle=1236,i,14409184210809088823,2444241897877441864,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2084 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --mojo-platform-channel-handle=3412 --field-trial-handle=1236,i,14409184210809088823,2444241897877441864,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2088 | "C:\Users\admin\Downloads\WeSendit-20230918220987\f\Factura883200598820KKUY772992_0\Factura883200598820KKUY772992_0.exe" | C:\Users\admin\Downloads\WeSendit-20230918220987\f\Factura883200598820KKUY772992_0\Factura883200598820KKUY772992_0.exe | — | explorer.exe | |||||||||||
User: admin Company: LULU Software Integrity Level: MEDIUM Description: Soda PDF Desktop 14 Installer Exit code: 0 Version: 14.0.241.2517 Modules
| |||||||||||||||
Total events
21 113
Read events
20 919
Write events
189
Delete events
5
Modification events
| (PID) Process: | (996) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (996) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (996) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (996) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (996) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (996) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (996) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (996) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (996) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (996) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
5
Suspicious files
177
Text files
119
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3616 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RFfc971.TMP | — | |
MD5:— | SHA256:— | |||
| 3616 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3616 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\80fcb1a6-4545-4df3-8798-107570467d30.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 1424 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:24BE8A92460B5B7A555B1DA559296958 | SHA256:77A3CFE6B7EB676AF438D5DE88C7EFCB6ABCC494E0B65DA90201969E6D79B2A3 | |||
| 3616 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RFfcaa9.TMP | text | |
MD5:561161B0FF5BCA89BF47F8AC972A7499 | SHA256:ECCA5CCFA0BEED7581B39FCE03D0FD3B694DF0F92BFFF780F702118AD51FC17D | |||
| 1424 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:C458177AA7F6A746C6ADA6F491147347 | SHA256:2C76B71683DD8999057253C82A0321ADCB7298B49C7622053C1C6BEC4D08AA98 | |||
| 3616 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:B806171F9E7C87423595645872D869B0 | SHA256:851A8D533BEBF6A69C5518375396E97463302C1E2031D04F8EB5851C5C82CEB9 | |||
| 3616 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old~RFfcba3.TMP | text | |
MD5:7C1C23F006788D107F8A01B852CC6701 | SHA256:9FA4E627077EDCBEC8AAA1ED2DD5538E630790893F88F02F1E9CC863E6A27848 | |||
| 3616 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:29B82603A20A26A3F99DB34525AF7448 | SHA256:9601A054A9C6AA6A65CEFAA229046476C1A089989FA6441DAD71D39F6794B980 | |||
| 3616 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RFfcb94.TMP | text | |
MD5:0917C6BFC618ACD47C1F53C7E7FFFF9C | SHA256:A5CAF56982DA7AE34B201E8609610786B4730371EF0812B7D418A2F9B73547BC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
167
DNS requests
115
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
868 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ackyowojwm6xpsge7iqqunu4farq_20230815.558564245.14/obedbbhbpmojnkanicioggnmelmoomoc_20230815.558564245.14_all_ENUS500000_ad6jojylf2dkpsjf5ulyv4jw54qq.crx3 | unknown | — | — | unknown |
1424 | iexplore.exe | GET | 200 | 142.251.141.35:80 | http://crl.pki.goog/gsr1/gsr1.crl | unknown | der | 1.70 Kb | unknown |
1424 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?49361a3f17fc7612 | unknown | compressed | 4.66 Kb | unknown |
996 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | unknown | der | 1.47 Kb | unknown |
1424 | iexplore.exe | GET | 200 | 104.18.14.101:80 | http://crl.sectigo.com/SectigoRSAOrganizationValidationSecureServerCA.crl | unknown | binary | 934 Kb | unknown |
1424 | iexplore.exe | GET | 200 | 104.18.15.101:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEBN9U5yqfDGppDNwGWiEeo0%3D | unknown | der | 2.18 Kb | unknown |
1424 | iexplore.exe | GET | 200 | 142.250.184.131:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | der | 1.41 Kb | unknown |
1424 | iexplore.exe | GET | 200 | 104.18.15.101:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | unknown | der | 1.42 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ackyowojwm6xpsge7iqqunu4farq_20230815.558564245.14/obedbbhbpmojnkanicioggnmelmoomoc_20230815.558564245.14_all_ENUS500000_ad6jojylf2dkpsjf5ulyv4jw54qq.crx3 | unknown | binary | 6.14 Kb | unknown |
1424 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | unknown | der | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1424 | iexplore.exe | 75.2.45.134:443 | wsi.li | AMAZON-02 | US | unknown |
1424 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | STACKPATH-CDN | US | whitelisted |
1424 | iexplore.exe | 104.18.15.101:80 | ocsp.comodoca.com | CLOUDFLARENET | — | unknown |
3284 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
996 | iexplore.exe | 92.123.104.60:443 | www.bing.com | Akamai International B.V. | DE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1424 | iexplore.exe | 104.18.14.101:80 | ocsp.comodoca.com | CLOUDFLARENET | — | unknown |
3616 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1200 | chrome.exe | 142.250.186.131:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
wsi.li |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
crl.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
crl.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |